| File name: | 9ce42177bafe552495b8329726bb4acfcb5f9e886377a2e76fb901fa01ae407c.ps1 |
| Full analysis: | https://app.any.run/tasks/a9f19df4-35e6-4020-a32a-ecc483aa7586 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 08:41:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (1828), with CR line terminators |
| MD5: | CB0FE0FE3A20381A4A894216EEF11D0E |
| SHA1: | A03742D37684DF4EC933277E8200E2FB8EB634DB |
| SHA256: | 9CE42177BAFE552495B8329726BB4ACFCB5F9E886377A2E76FB901FA01AE407C |
| SSDEEP: | 48:tBhMFfZtHUuiDnPHybtrYN+8K9Kzba7DuUaIMakwTDREZWWvlFbyRc+/+8h8QHFn:tB0fZt0BPSiN6+1UaI98WWvlFS/XH2g |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7416)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 5260)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7892)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 7416)
- wscript.exe (PID: 7900)
Changes the autorun value in the registry
- reg.exe (PID: 7964)
SUSPICIOUS
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 7416)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7940)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 7416)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7416)
Application launched itself
- powershell.exe (PID: 7416)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 7416)
- wscript.exe (PID: 7900)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 5260)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7416)
- wscript.exe (PID: 7900)
The process executes via Task Scheduler
- wscript.exe (PID: 7900)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7900)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7416)
Connects to unusual port
- powershell.exe (PID: 7416)
INFO
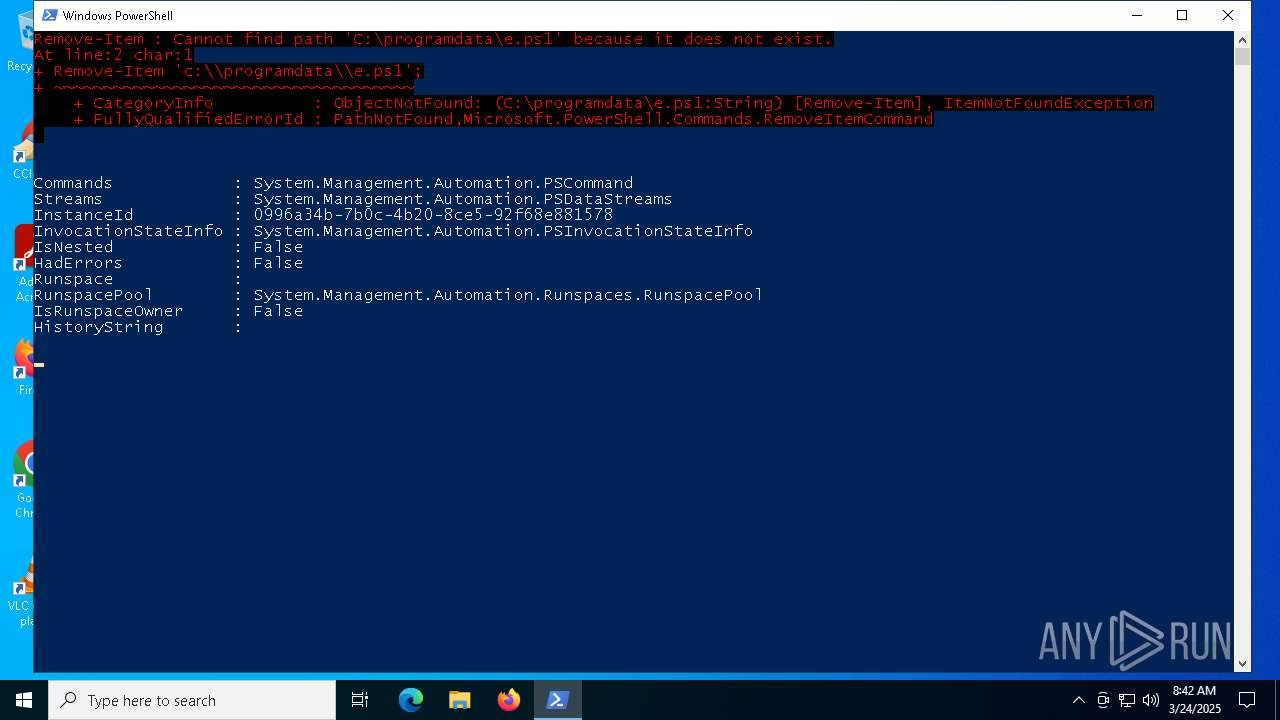
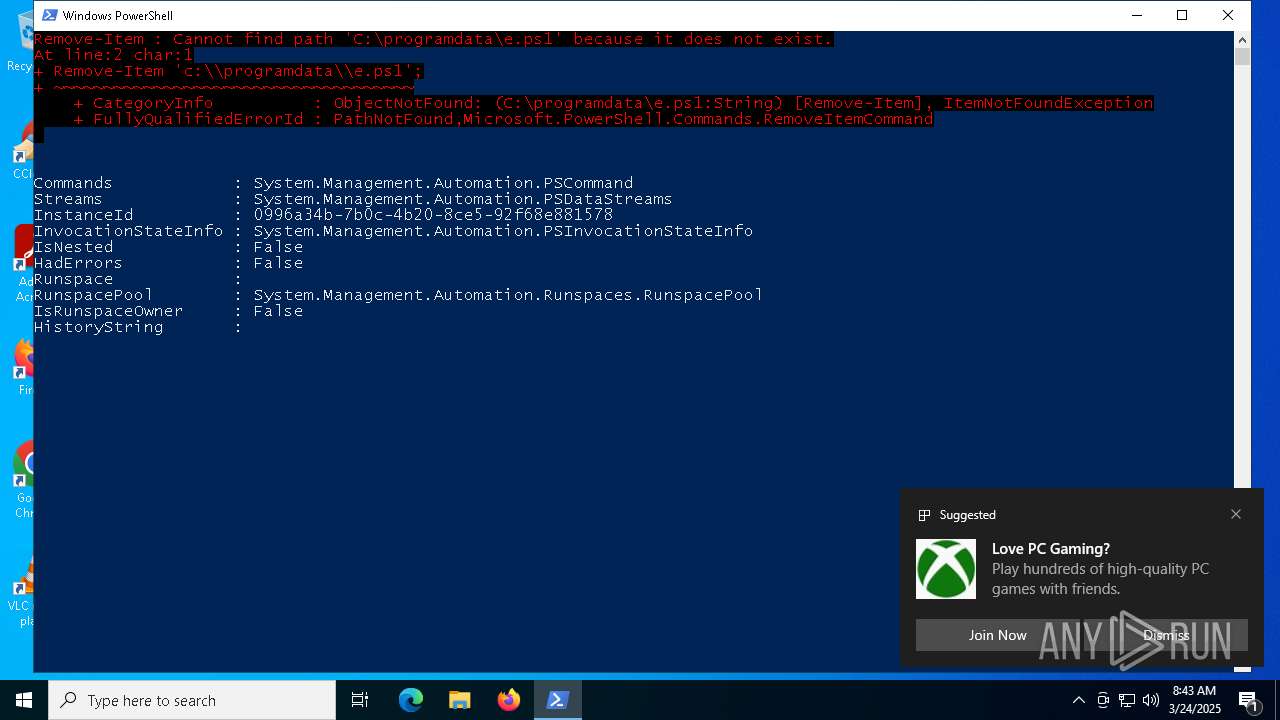
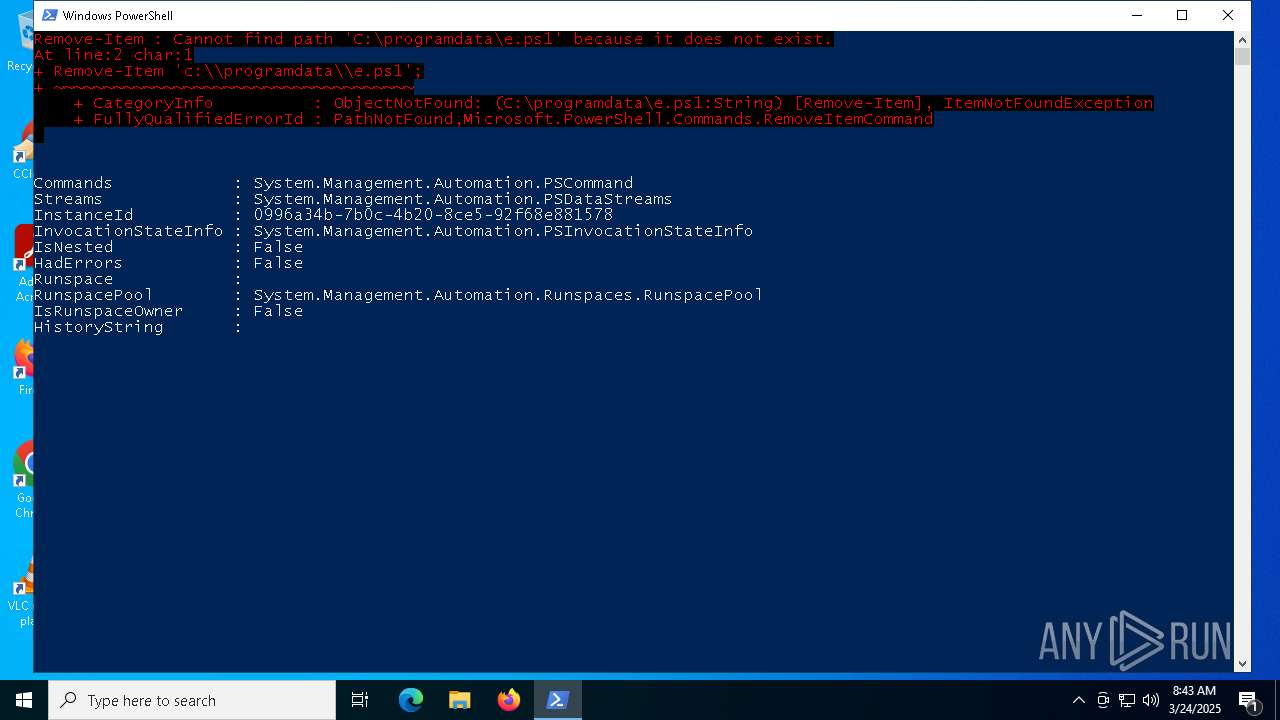
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7416)
Autorun file from Task Scheduler
- cmd.exe (PID: 7892)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7416)
Disables trace logs
- powershell.exe (PID: 7416)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 5260)
Checks proxy server information
- powershell.exe (PID: 7988)
- BackgroundTransferHost.exe (PID: 2656)
- powershell.exe (PID: 5260)
- powershell.exe (PID: 7416)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 5260)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7184)
- BackgroundTransferHost.exe (PID: 3676)
- BackgroundTransferHost.exe (PID: 2656)
- BackgroundTransferHost.exe (PID: 5176)
- BackgroundTransferHost.exe (PID: 1568)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 2656)
- slui.exe (PID: 7544)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 2656)
Checks supported languages
- ShellExperienceHost.exe (PID: 7728)
Creates files in the program directory
- powershell.exe (PID: 7416)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
20
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1568 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2656 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3676 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5176 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5260 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass -c " Invoke-Expression (Get-Content C:\\ProgramData\\AN9385.tmp);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7184 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7416 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\9ce42177bafe552495b8329726bb4acfcb5f9e886377a2e76fb901fa01ae407c.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7508 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 141
Read events
34 122
Write events
19
Delete events
0
Modification events
| (PID) Process: | (7964) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | GUpdate2 |
Value: c:\\windows\\system32\\wscript.exe //b //e:javascript C:\\ProgramData\\26545.tmp | |||
| (PID) Process: | (7184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2656) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2656) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2656) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3676) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3676) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3676) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
10
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2656 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\fbe15640-276f-415e-a333-dbdff5fd82a4.down_data | — | |
MD5:— | SHA256:— | |||
| 7416 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:0D918A5A31D2B1CC8EF0889828878745 | SHA256:2E122964C93666B0084E621D5CCE0A2A64C808F0510011292A16A5603ACA0273 | |||
| 7416 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10bac6.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7416 | powershell.exe | C:\ProgramData\26545.tmp | binary | |
MD5:62C9992BD4A3F06C305DE0ADCEA5CCBE | SHA256:EC78B61A5F54805BBDFFD69D57CE76DB41D1ADBB85C544688769EACF29D928CB | |||
| 7416 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_q5x5eore.4ct.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7416 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hkd02h5x.ac5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7416 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:C904B83F3EB6B36C24B175843EAE2F18 | SHA256:AE9C3B418FC314078AEA3B8FE77670BDBD72E127D1DAE886D031A73C2074B64F | |||
| 2656 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\dfbc4b3a-34ad-4681-9c74-dee9c15e1331.up_meta_secure | binary | |
MD5:6E4F5BF8F2D33FD67F71D5A2D2EDD59E | SHA256:81AB866919D922A9147E73E57B94A73EDF5FDD81D1BD083F6683FE83560BAF05 | |||
| 7416 | powershell.exe | C:\ProgramData\AN9385.tmp | text | |
MD5:9DEC4DA0B28AF8CBAD99611AE6C3E8D3 | SHA256:A1376496406895A00D9009B36A6E1073553F3198502A71D33D7438E68914261A | |||
| 8108 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vvikunhh.rpd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
55
DNS requests
20
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
5008 | SIHClient.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5008 | SIHClient.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5008 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5008 | SIHClient.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
5008 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 162.125.72.15:443 | https://ucc5e5838f94556bf9d7f324386d.dl.dropboxusercontent.com/cd/0/get/CmfRaeVmZlKd-NfFx755th-ZTVUoL8LtPfcF4CiasXbwsLKaXt5bjhiAlNnSzK56baSViLU9VrUeE3s1iFjV-jRwPaKJfxvA2y0dMLpTvF6knGEqSR5BNKfPC96Y7lIkpxFQno8n48P76cZohbnD-fP6/file?dl=1 | unknown | compressed | 4.67 Kb | whitelisted |
— | — | POST | 400 | 20.190.159.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | GET | 200 | 172.217.16.202:443 | https://www.googleapis.com/drive/v3/files?q=name+contains+'eee'+and+not+fullText+contains+'result'+and+mimeType+!=+'application/vnd.google-apps.folder' | unknown | binary | 75 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7416 | powershell.exe | 64.20.59.148:8855 | — | IS-AS-1 | US | unknown |
7416 | powershell.exe | 162.125.72.18:443 | www.dropbox.com | DROPBOX | US | whitelisted |
7416 | powershell.exe | 162.125.72.15:443 | ucc5e5838f94556bf9d7f324386d.dl.dropboxusercontent.com | DROPBOX | US | whitelisted |
7988 | powershell.exe | 142.250.186.138:443 | www.googleapis.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.dropbox.com |
| whitelisted |
ucc5e5838f94556bf9d7f324386d.dl.dropboxusercontent.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |