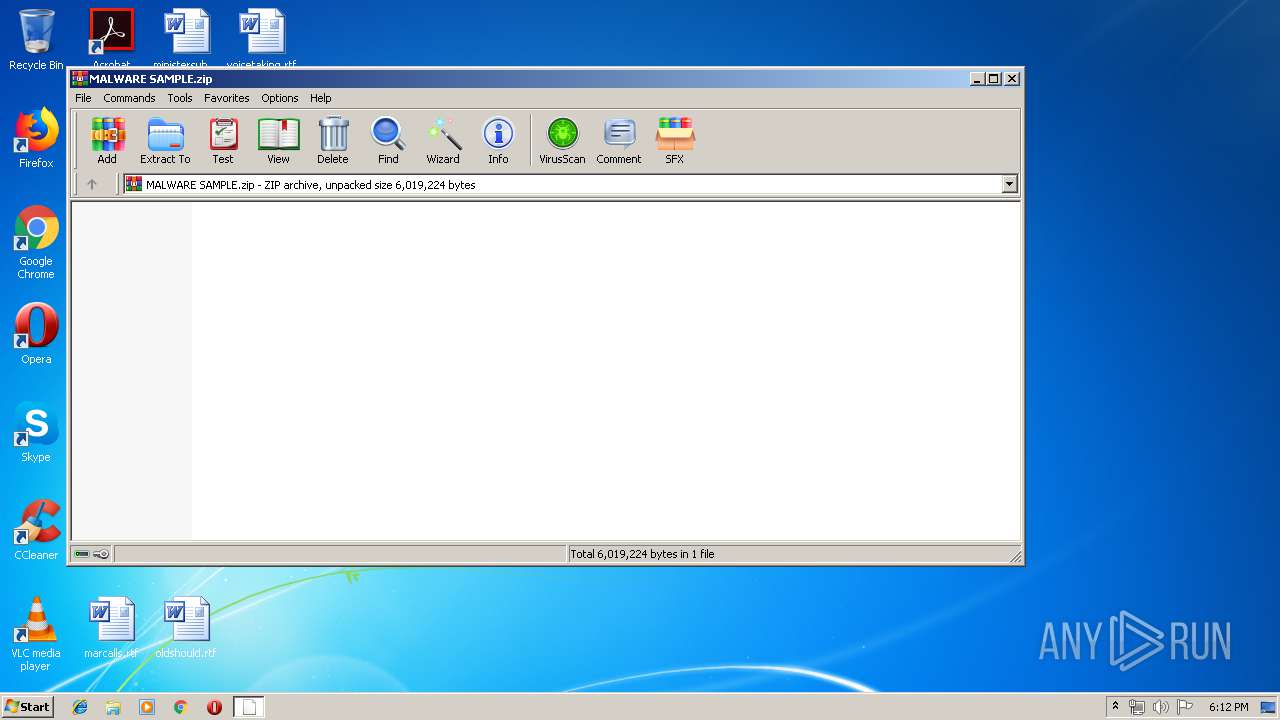
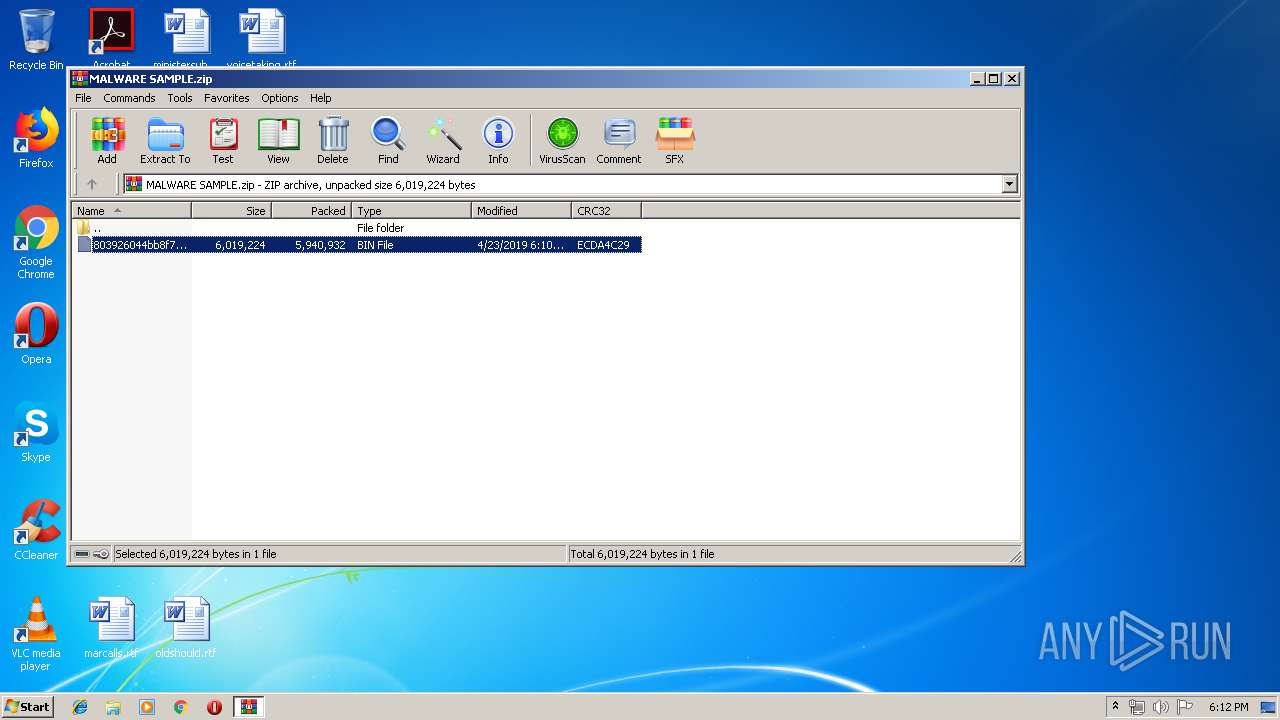
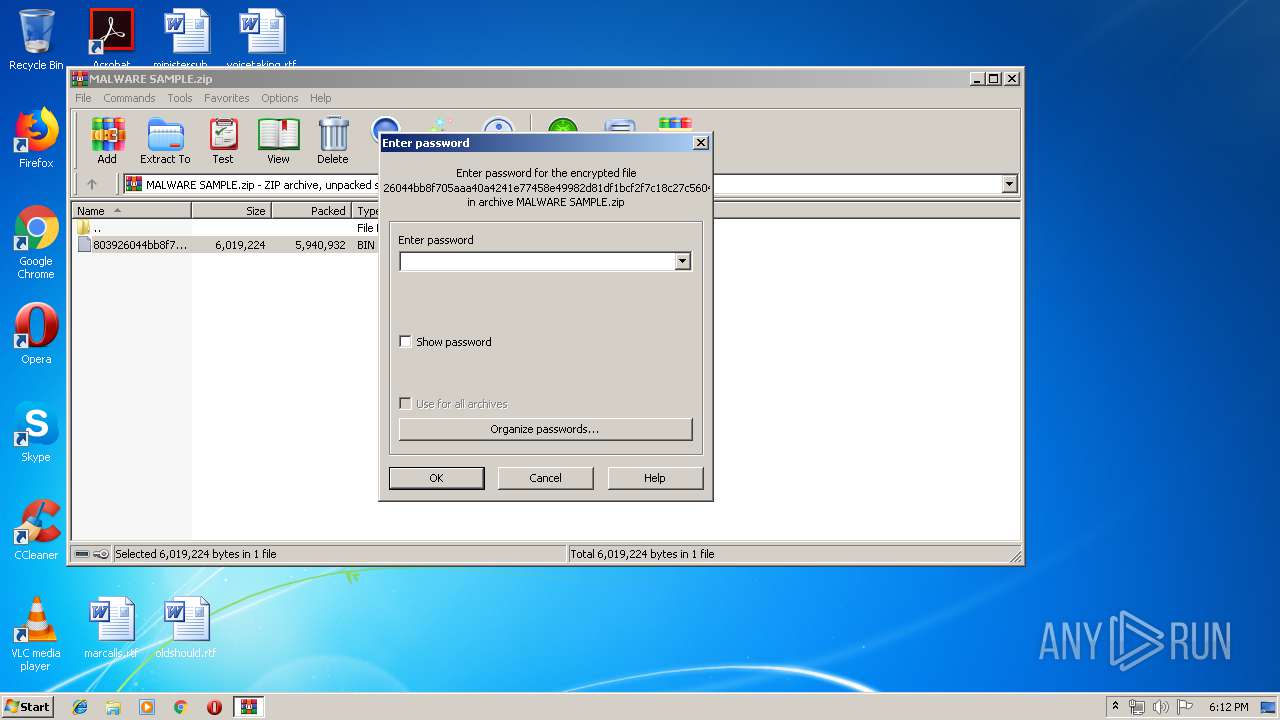
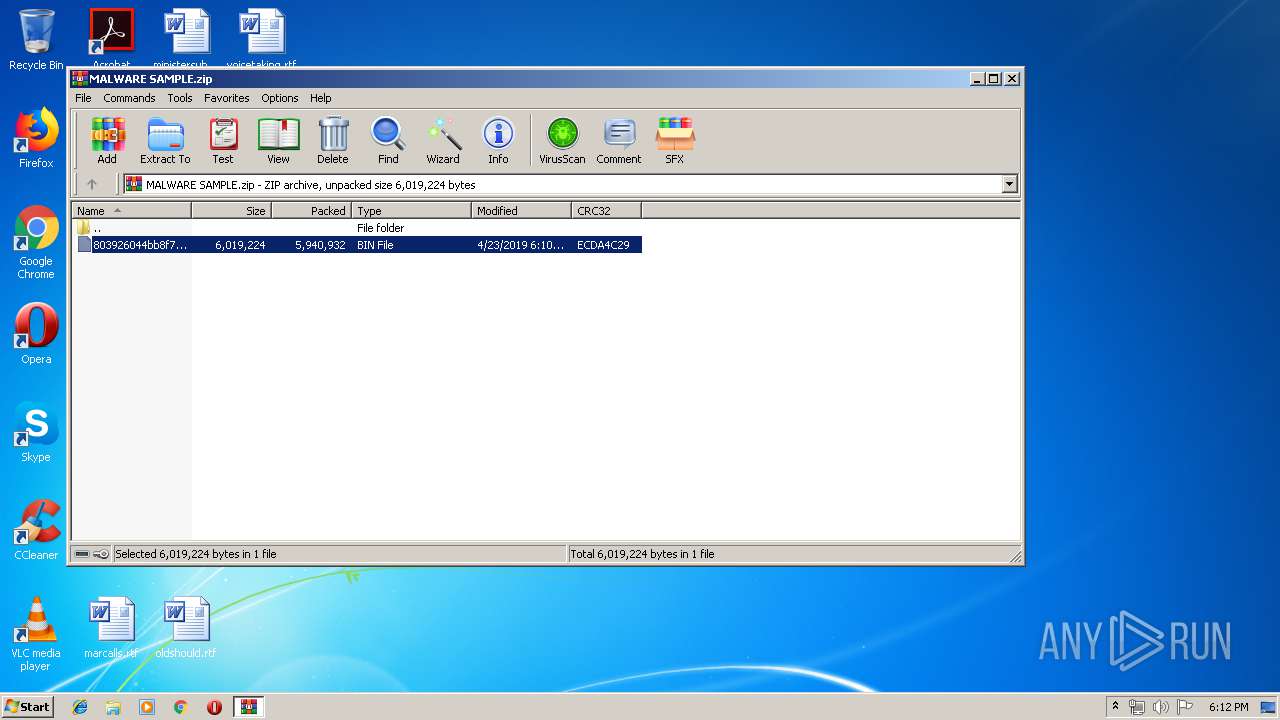
| File name: | MALWARE SAMPLE.zip |
| Full analysis: | https://app.any.run/tasks/da451280-a1d1-4dff-9bbd-a9d73cf1584f |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 17:12:00 |
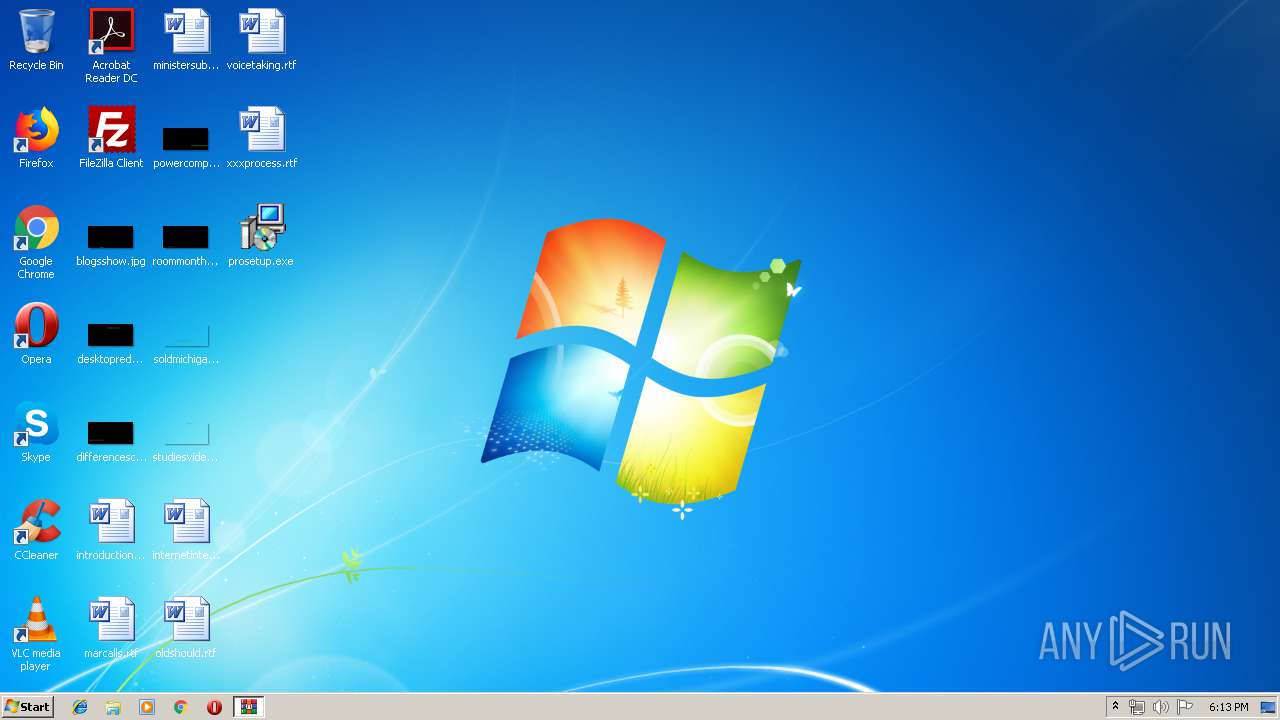
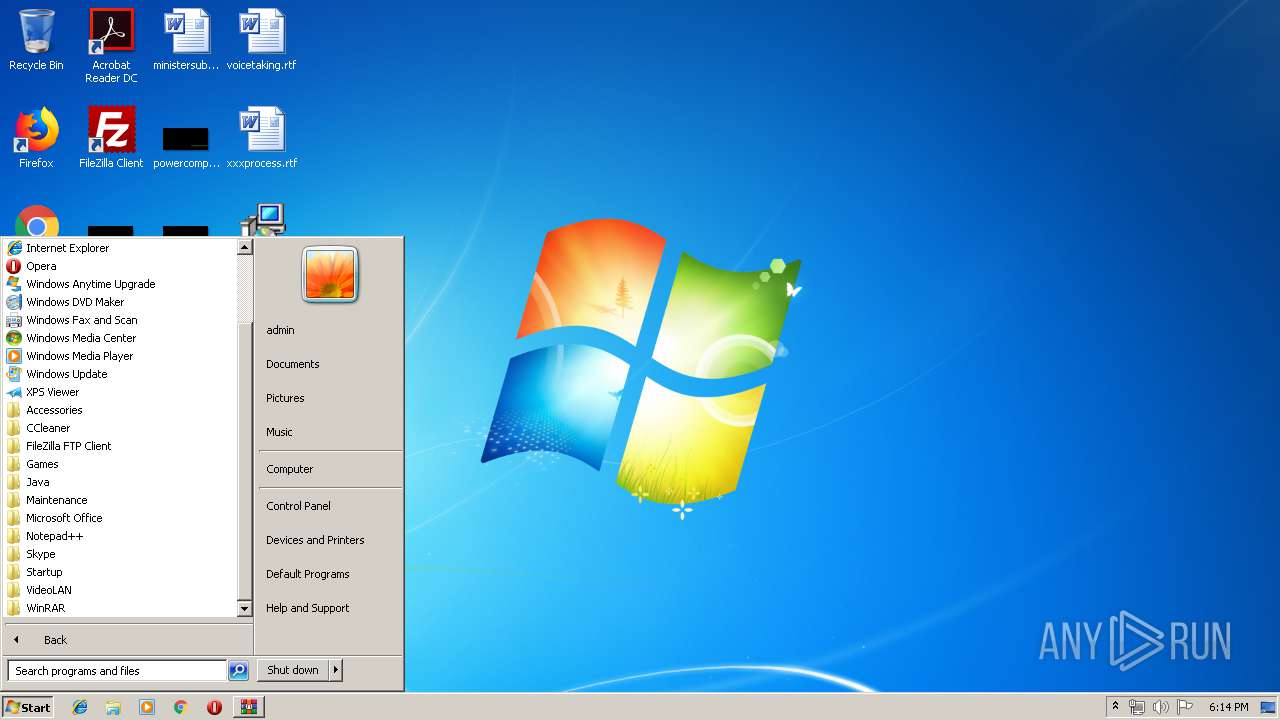
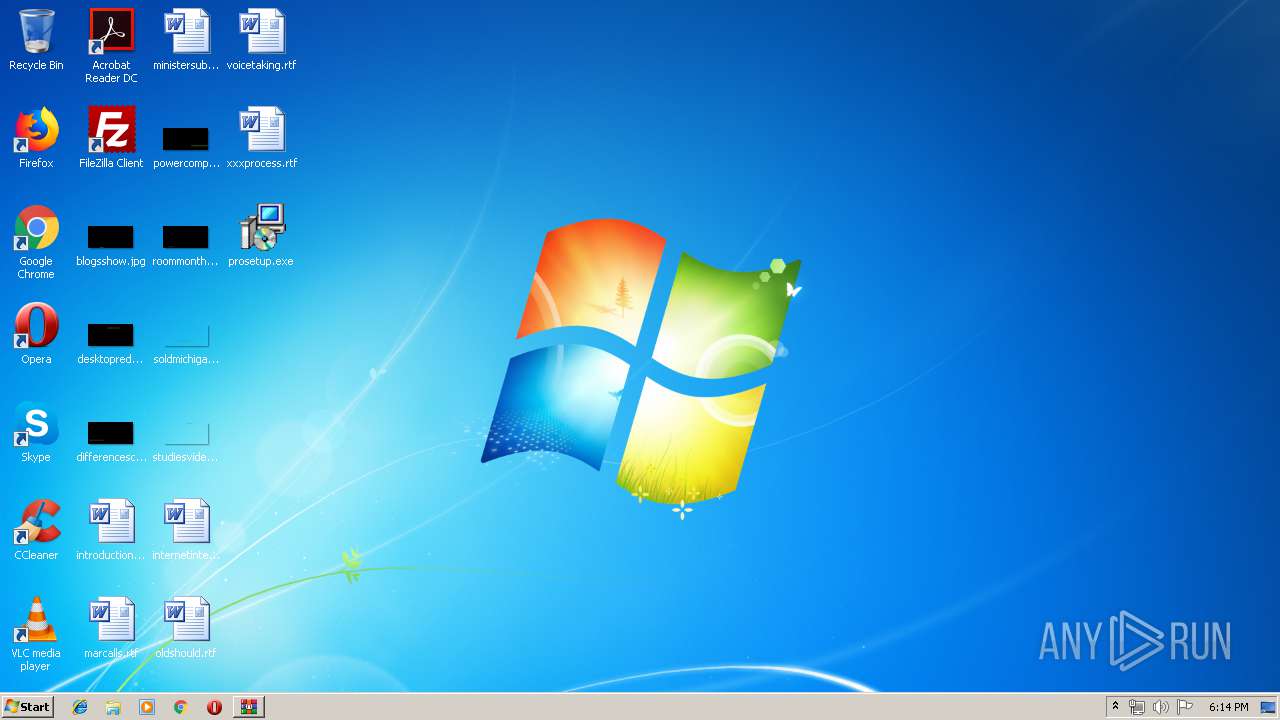
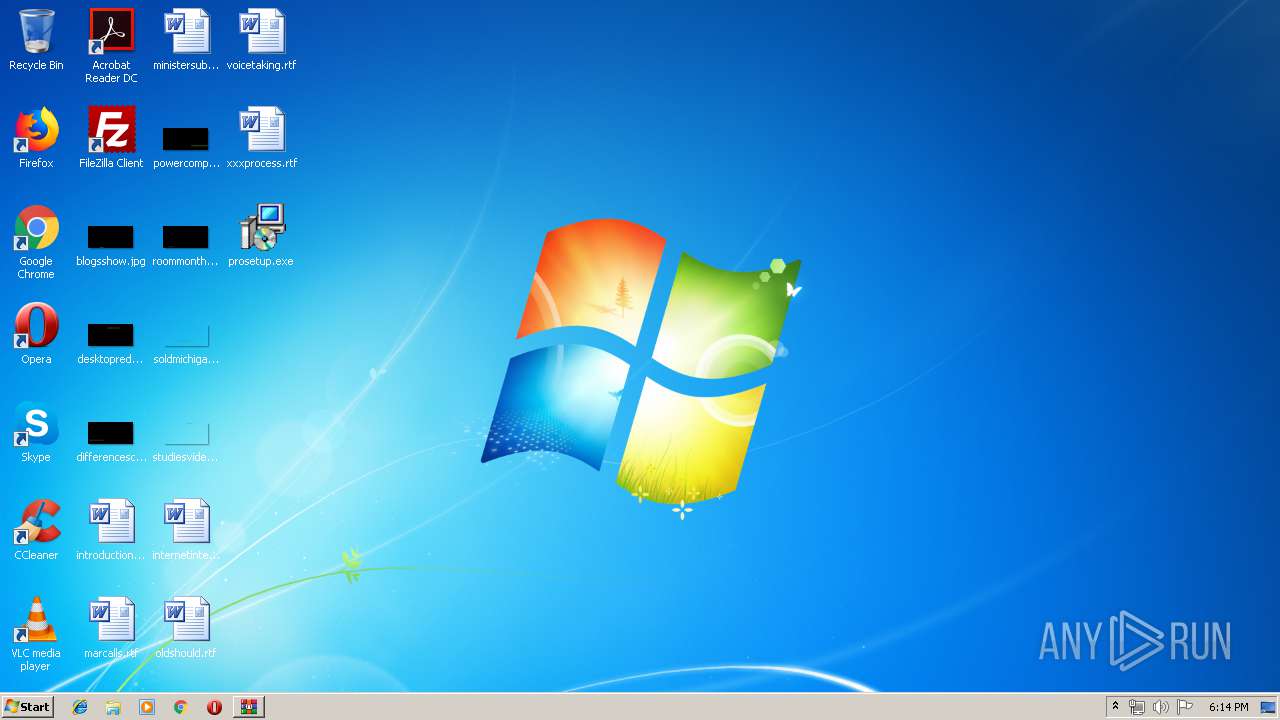
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 63AD2ABF3E28FDE3BFC0DDABA5E64FE8 |
| SHA1: | A1540727B7031B2115ADA810E6A952ABF0BFB55E |
| SHA256: | 9CDDF34E362169B42E7173E54143B54F88295EE19EDB680842DC772DD27D8324 |
| SSDEEP: | 98304:HFv9J4/jStTlbt6k5qsx31GPlE0urH9YWfv/8B4bLOlEfW9hKYTd2yS:lLojStTVt6kvQPlE3dYWfSTKAdNS |
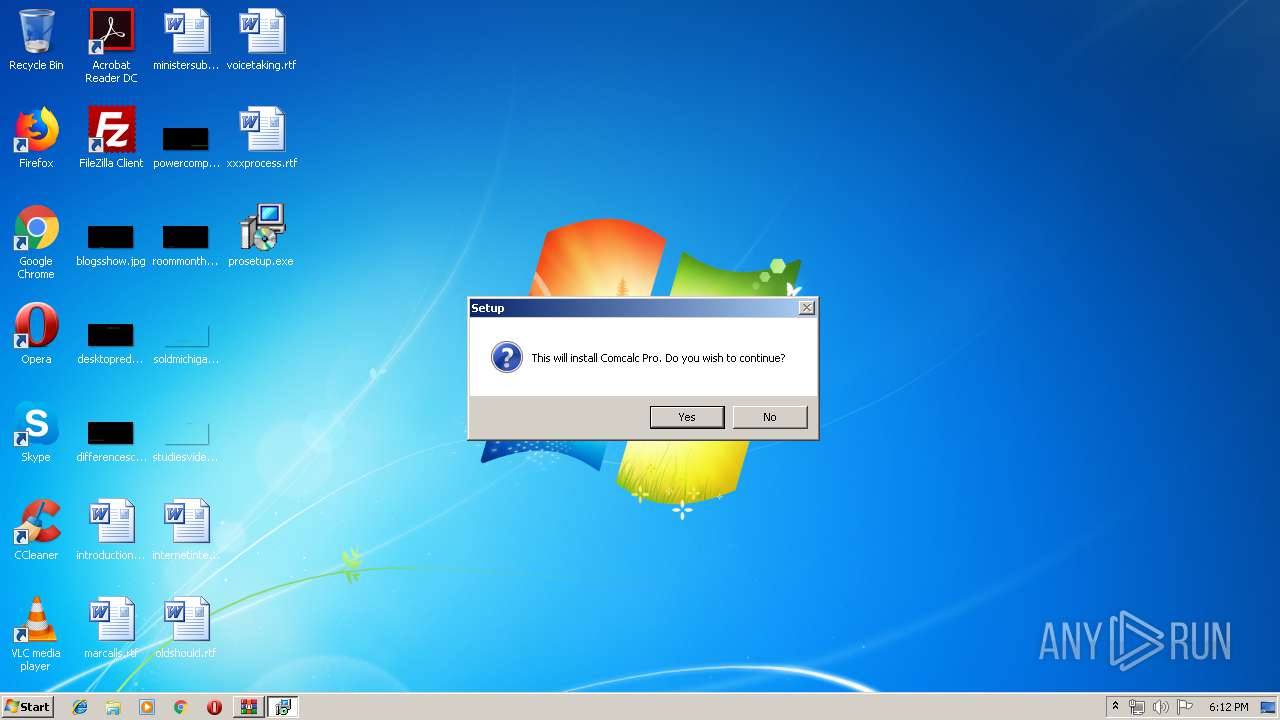
MALICIOUS
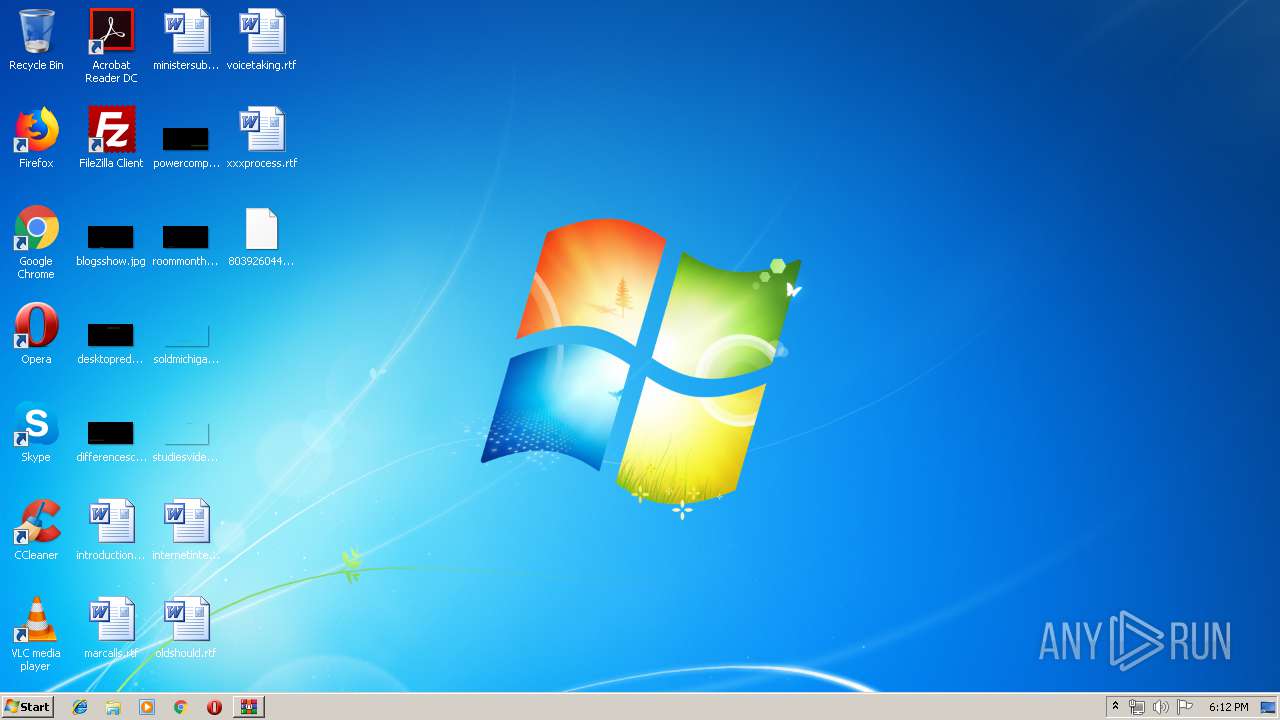
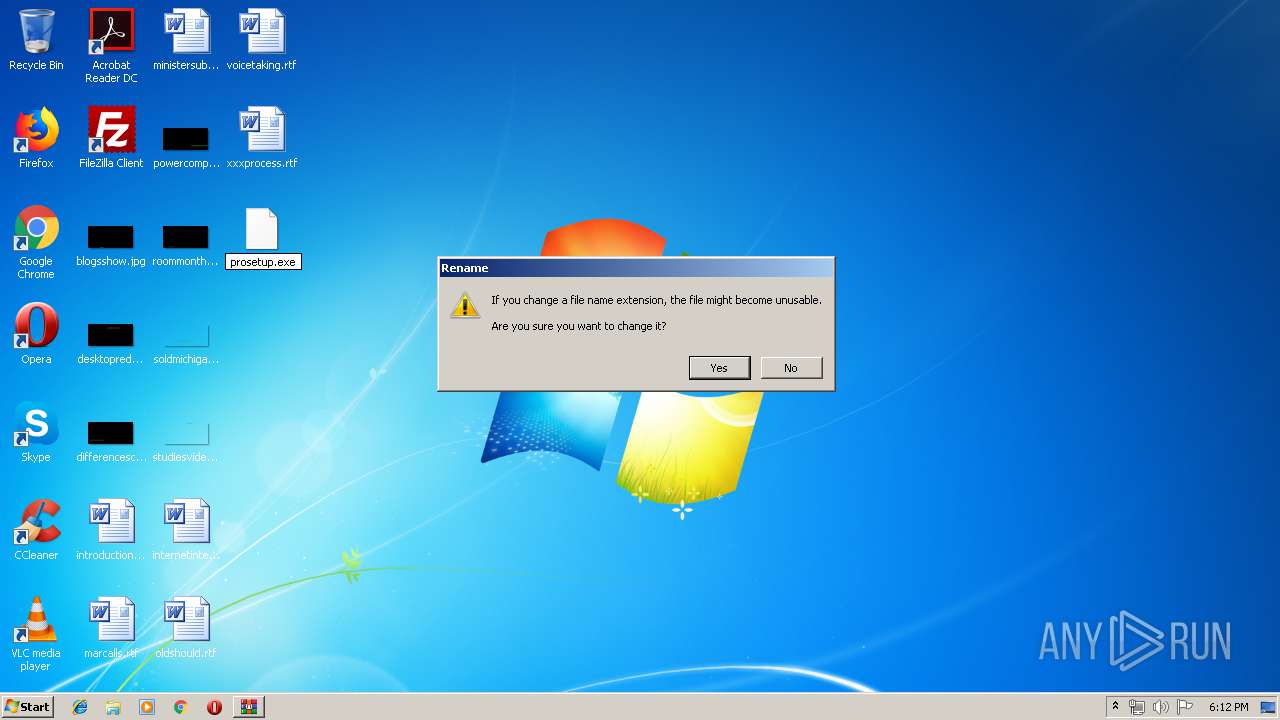
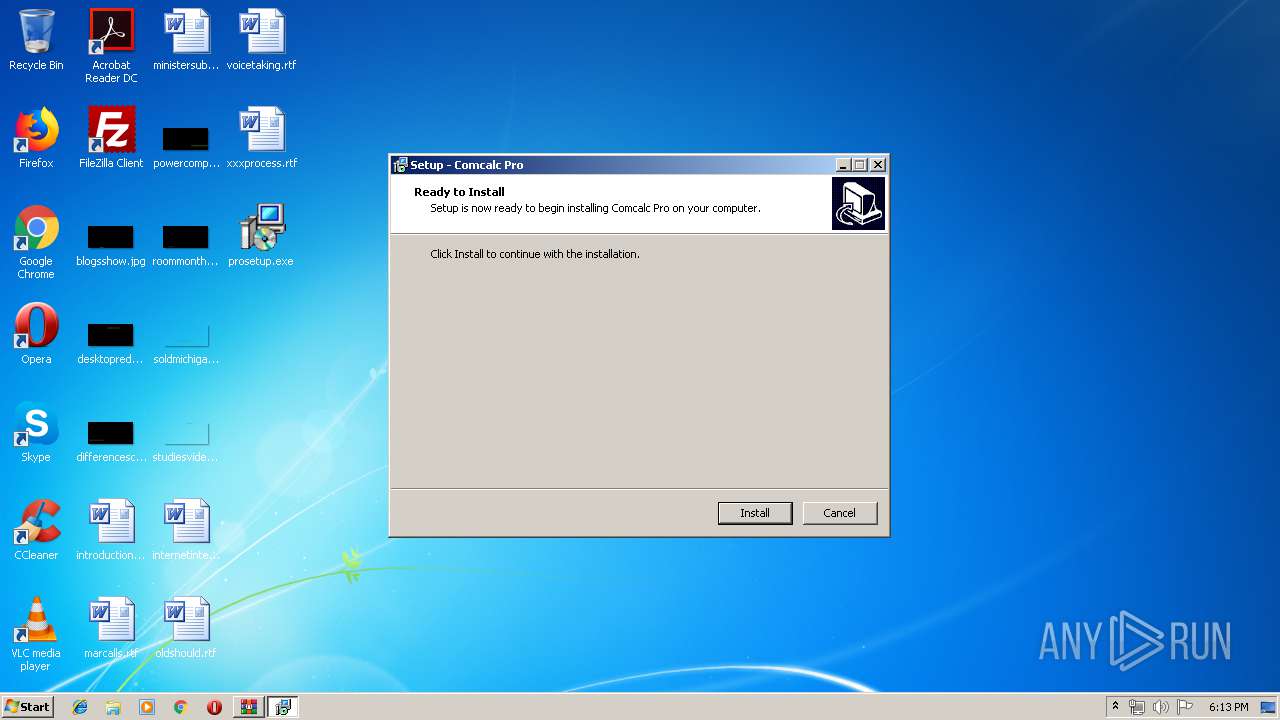
Application was dropped or rewritten from another process
- prosetup.exe (PID: 3040)
- prosetup.exe (PID: 3400)
- prosetup.exe (PID: 4048)
- prosetup.exe (PID: 2844)
SUSPICIOUS
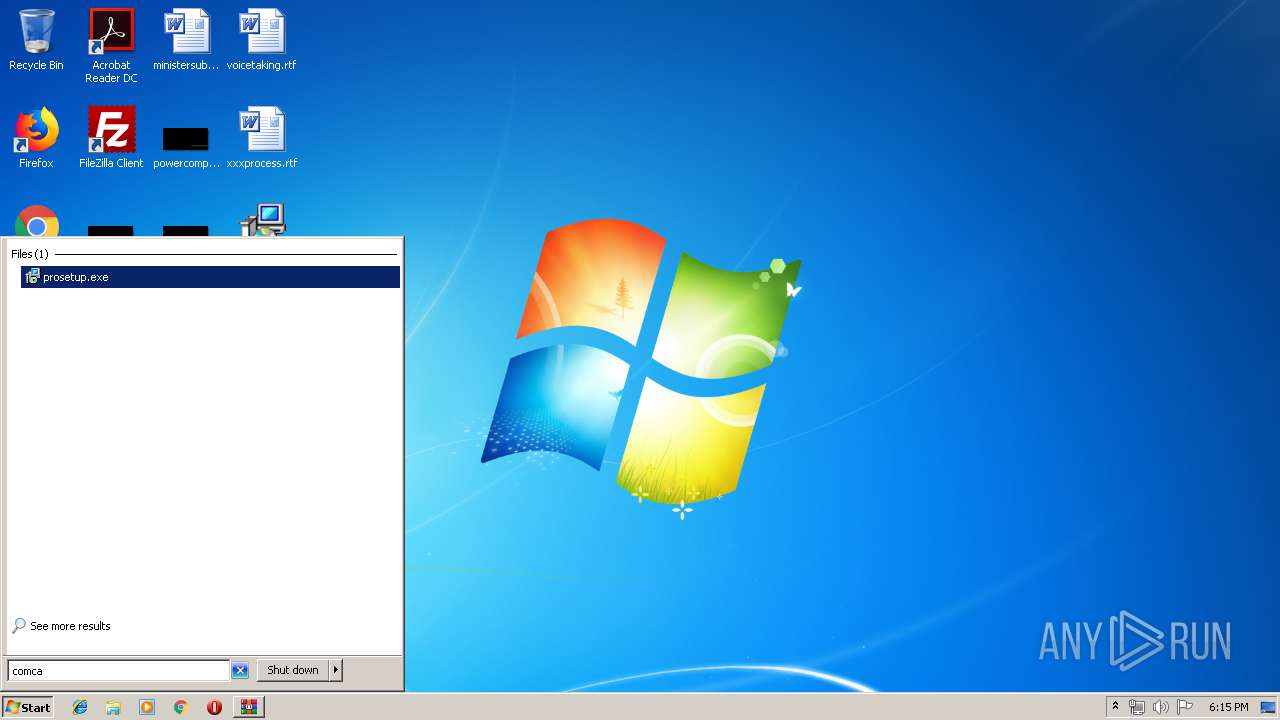
Executable content was dropped or overwritten
- prosetup.exe (PID: 3040)
- prosetup.exe (PID: 3400)
- prosetup.tmp (PID: 3424)
- WinRAR.exe (PID: 2584)
Reads Windows owner or organization settings
- prosetup.tmp (PID: 3424)
Reads the Windows organization settings
- prosetup.tmp (PID: 3424)
INFO
Application was dropped or rewritten from another process
- prosetup.tmp (PID: 3352)
- prosetup.tmp (PID: 2132)
- prosetup.tmp (PID: 3424)
- prosetup.tmp (PID: 3364)
Application launched itself
- chrome.exe (PID: 3716)
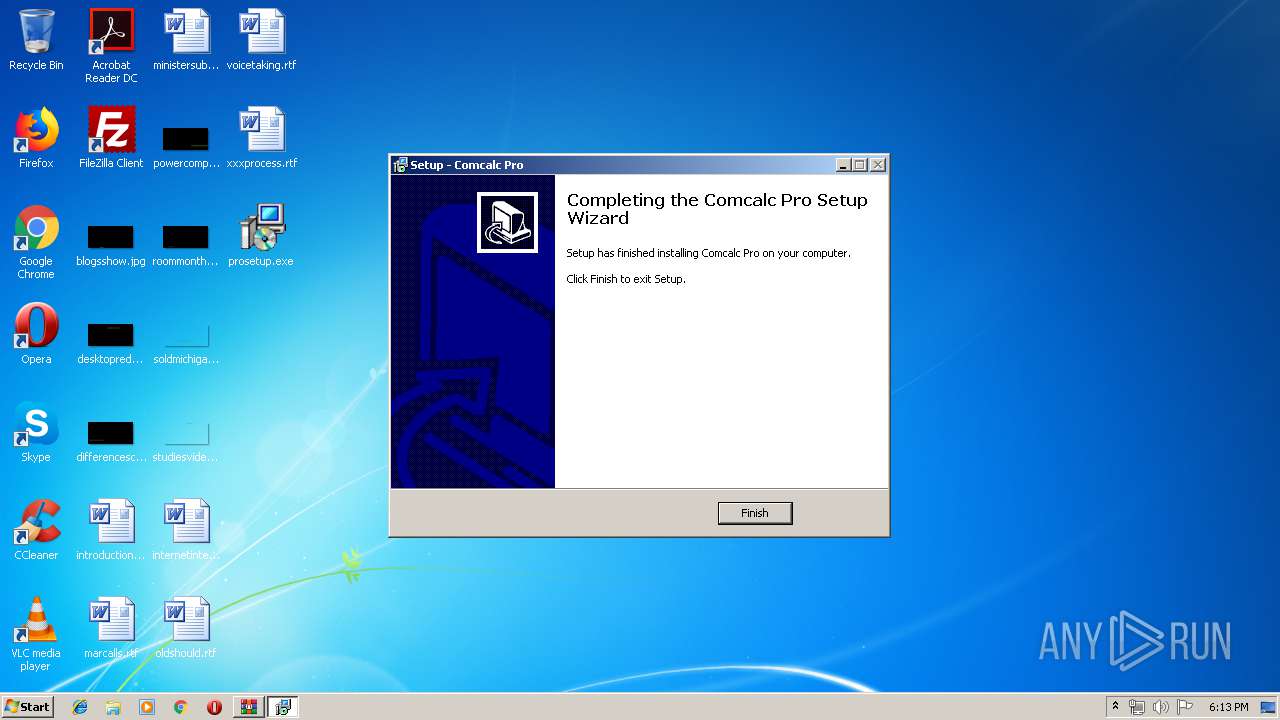
Creates a software uninstall entry
- prosetup.tmp (PID: 3424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:23 17:10:28 |
| ZipCRC: | 0xecda4c29 |
| ZipCompressedSize: | 5940932 |
| ZipUncompressedSize: | 6019224 |
| ZipFileName: | 803926044bb8f705aaa40a4241e77458e49982d81df1bcf2f7c18c27c56043d2.bin |
Total processes
59
Monitored processes
21
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3728 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\AppData\Local\Temp\is-LAOK4.tmp\prosetup.tmp" /SL5="$C0174,5632756,121344,C:\Users\admin\Desktop\prosetup.exe" | C:\Users\admin\AppData\Local\Temp\is-LAOK4.tmp\prosetup.tmp | — | prosetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,17825858674652163047,14998237240822486490,131072 --enable-features=PasswordImport --service-pipe-token=17612436192533074915 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17612436192533074915 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,17825858674652163047,14998237240822486490,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17056014272893411614 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17056014272893411614 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3664 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
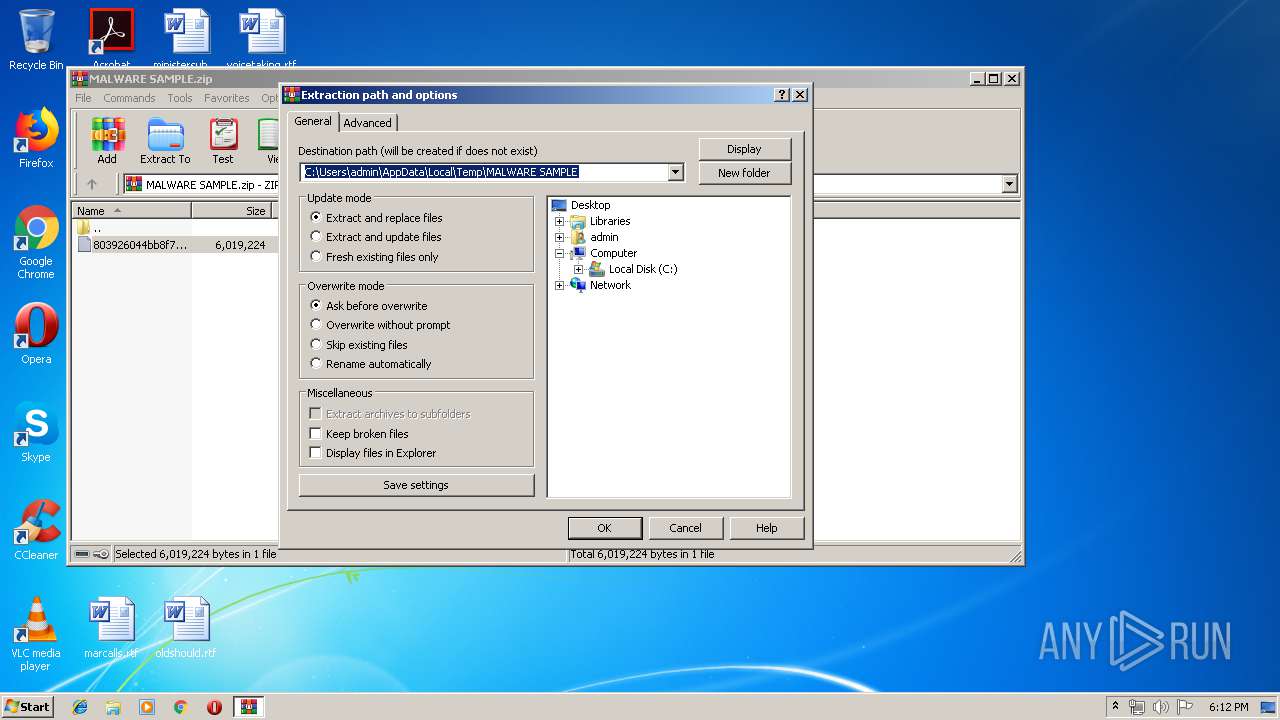
| 2584 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MALWARE SAMPLE.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,17825858674652163047,14998237240822486490,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10918507980621477547 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10918507980621477547 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,17825858674652163047,14998237240822486490,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10422270157403428296 --mojo-platform-channel-handle=948 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
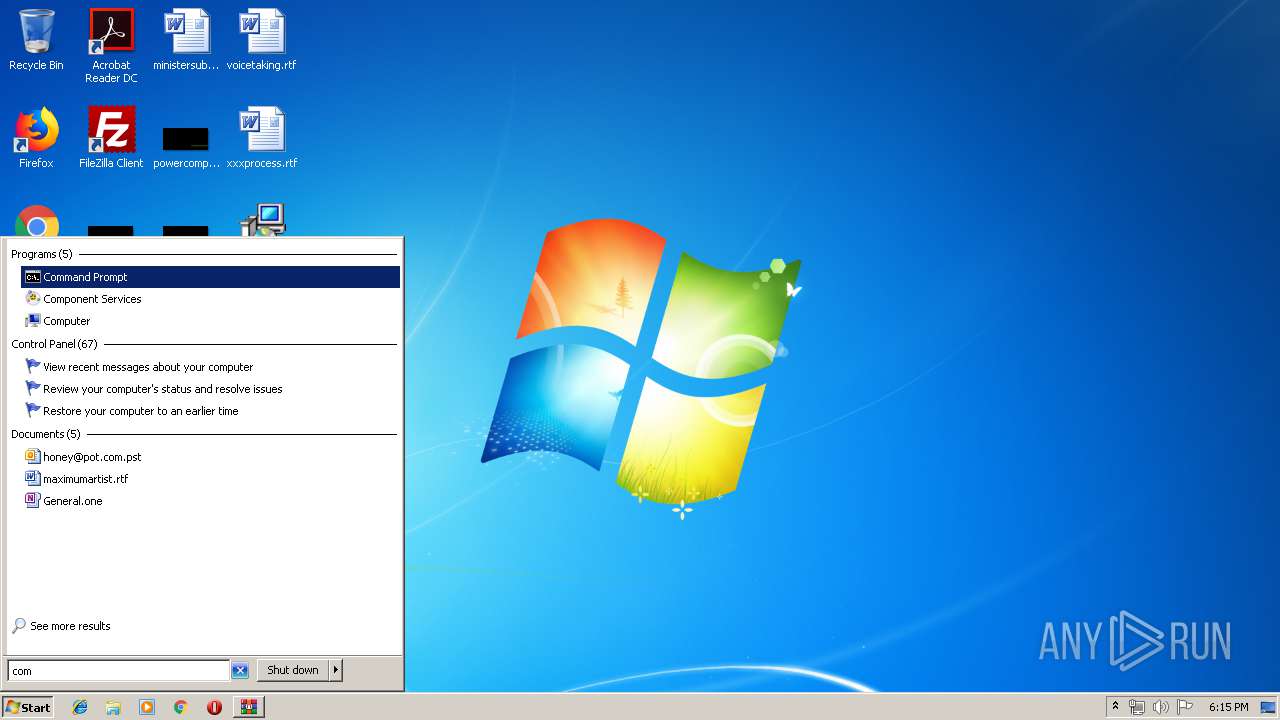
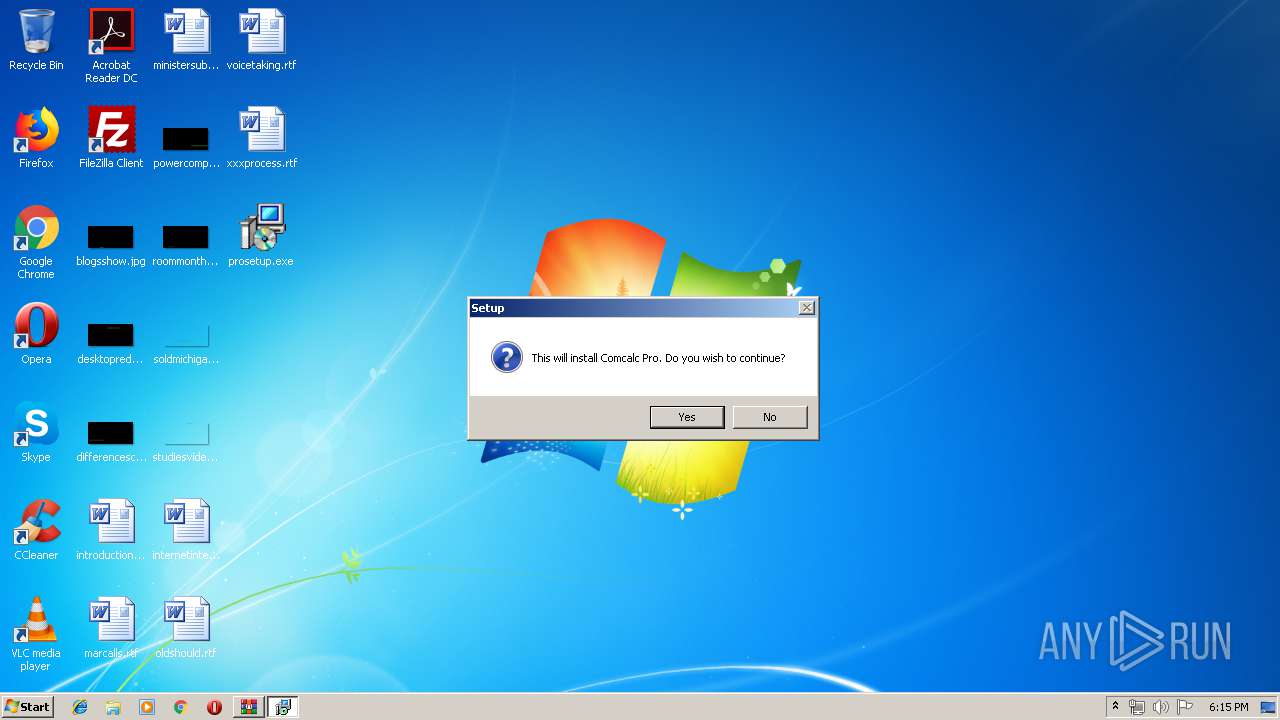
| 2844 | "C:\Users\admin\Desktop\prosetup.exe" | C:\Users\admin\Desktop\prosetup.exe | — | explorer.exe | |||||||||||
User: admin Company: Automated Power Systems (Asys) Pty Ltd Integrity Level: MEDIUM Description: Comcalc Pro Setup Exit code: 0 Version: 3.6.7 Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,17825858674652163047,14998237240822486490,131072 --enable-features=PasswordImport --service-pipe-token=15831042411335802296 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15831042411335802296 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3040 | "C:\Users\admin\Desktop\prosetup.exe" | C:\Users\admin\Desktop\prosetup.exe | explorer.exe | ||||||||||||
User: admin Company: Automated Power Systems (Asys) Pty Ltd Integrity Level: MEDIUM Description: Comcalc Pro Setup Exit code: 0 Version: 3.6.7 Modules
| |||||||||||||||
Total events
673
Read events
567
Write events
96
Delete events
10
Modification events
| (PID) Process: | (2584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2584) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MALWARE SAMPLE.zip | |||
| (PID) Process: | (2584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
6
Suspicious files
59
Text files
81
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3424 | prosetup.tmp | C:\Comcalc Pro\is-VPNU3.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | prosetup.tmp | C:\Comcalc Pro\is-93AJ3.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | prosetup.tmp | C:\Comcalc Pro\is-SIFNE.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | prosetup.tmp | C:\Comcalc Pro\is-DTOLD.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | prosetup.tmp | C:\Comcalc Pro\is-G3PKG.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | prosetup.tmp | C:\Comcalc Pro\Drawings\is-5NBU8.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | prosetup.tmp | C:\Comcalc Pro\Drawings\is-6QIM8.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | prosetup.tmp | C:\Comcalc Pro\Drawings\is-S0KIG.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | prosetup.tmp | C:\Comcalc Pro\Drawings\is-SP6KT.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | prosetup.tmp | C:\Comcalc Pro\Drawings\is-4KKB6.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
18
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3716 | chrome.exe | GET | — | 87.245.198.13:80 | http://r2---sn-gxuog0-axqe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=91.221.66.140&mm=28&mn=sn-gxuog0-axqe&ms=nvh&mt=1556039507&mv=u&pl=23&shardbypass=yes | RU | — | — | whitelisted |
3716 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 510 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3716 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3716 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
3716 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3716 | chrome.exe | 216.58.207.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3716 | chrome.exe | 216.58.206.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
3716 | chrome.exe | 87.245.198.13:80 | r2---sn-gxuog0-axqe.gvt1.com | RETN Limited | RU | whitelisted |
3716 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3716 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3716 | chrome.exe | 172.217.22.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3716 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.de |
| whitelisted |
fonts.googleapis.com |
| whitelisted |