| File name: | index.html |
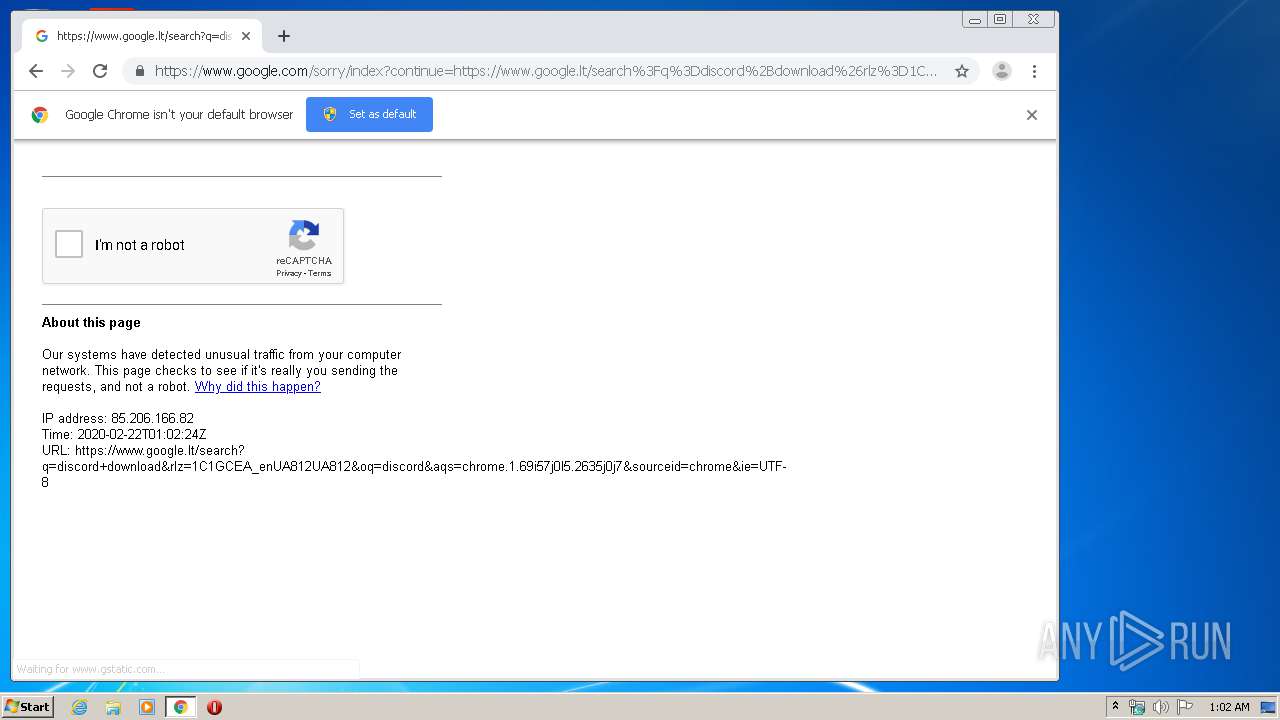
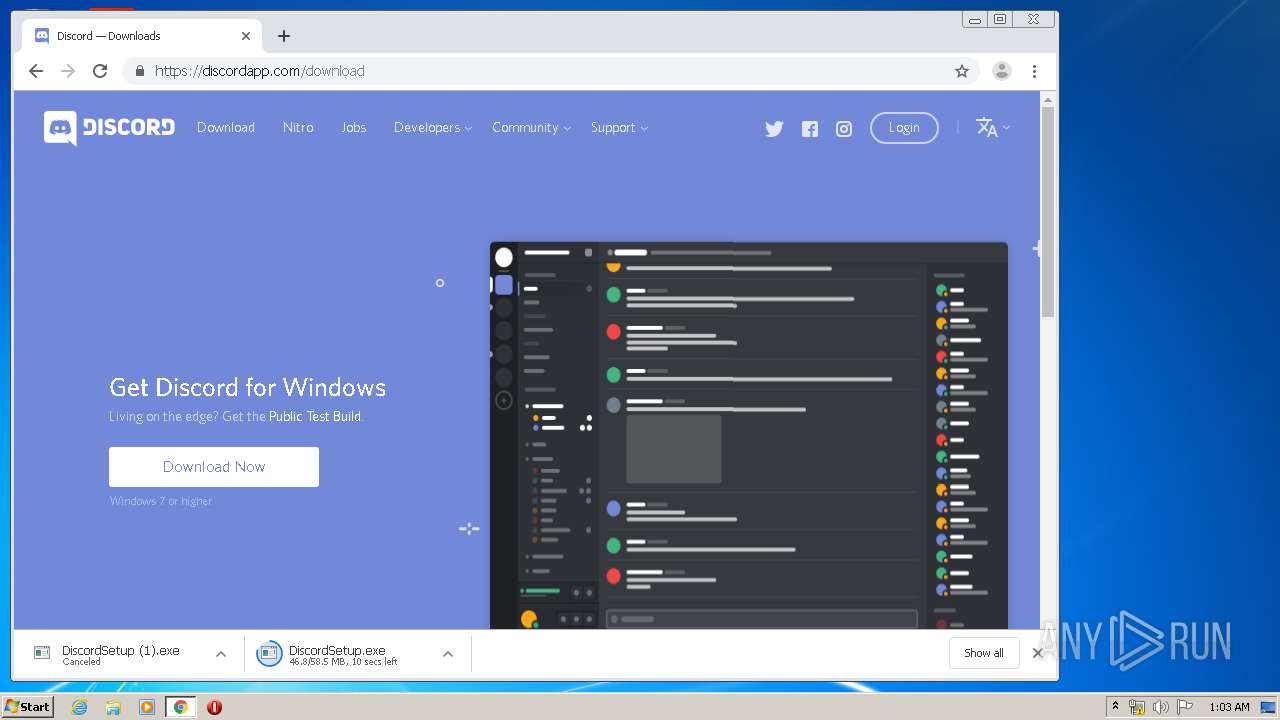
| Full analysis: | https://app.any.run/tasks/be4b4f36-9674-4b3c-901a-bf49624ba9fc |
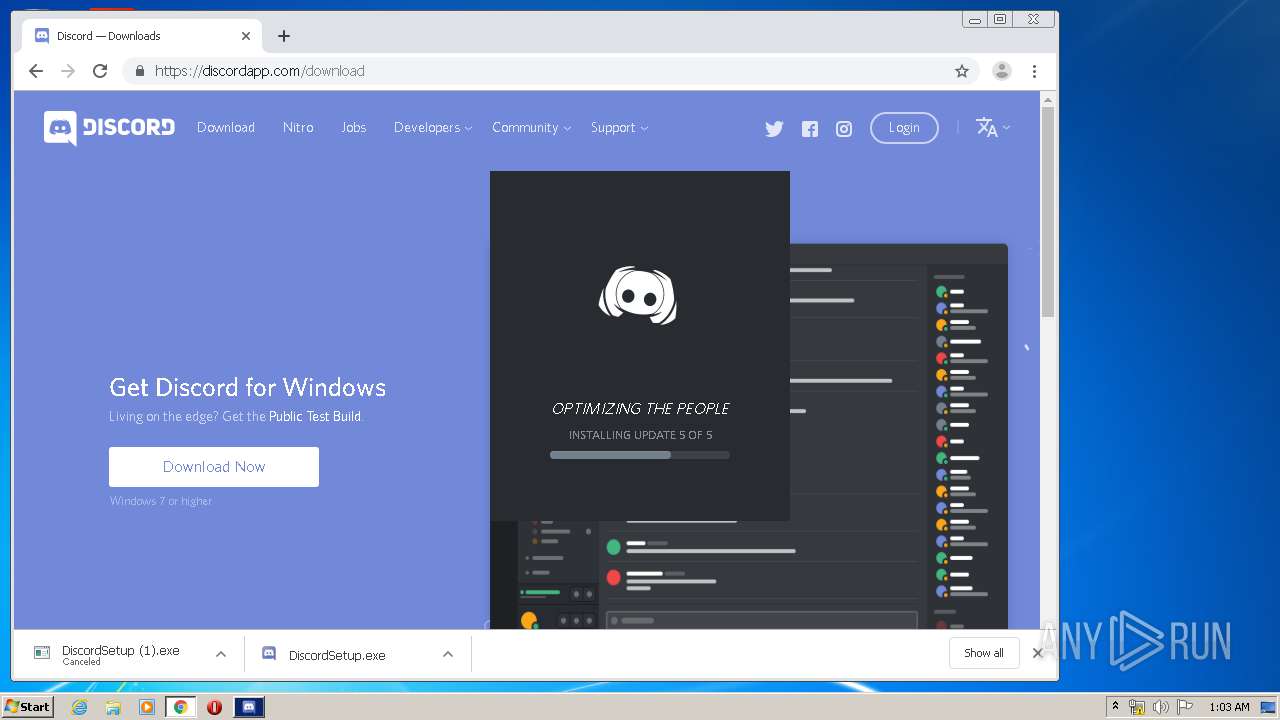
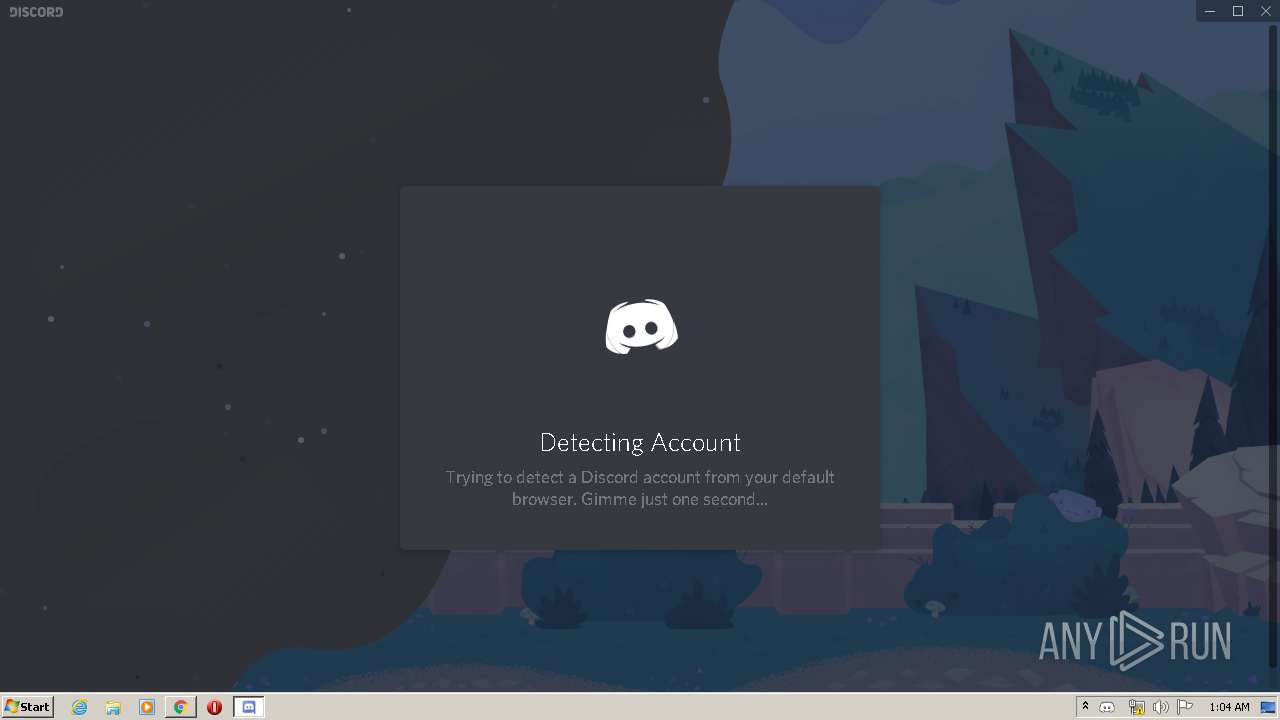
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 01:01:42 |
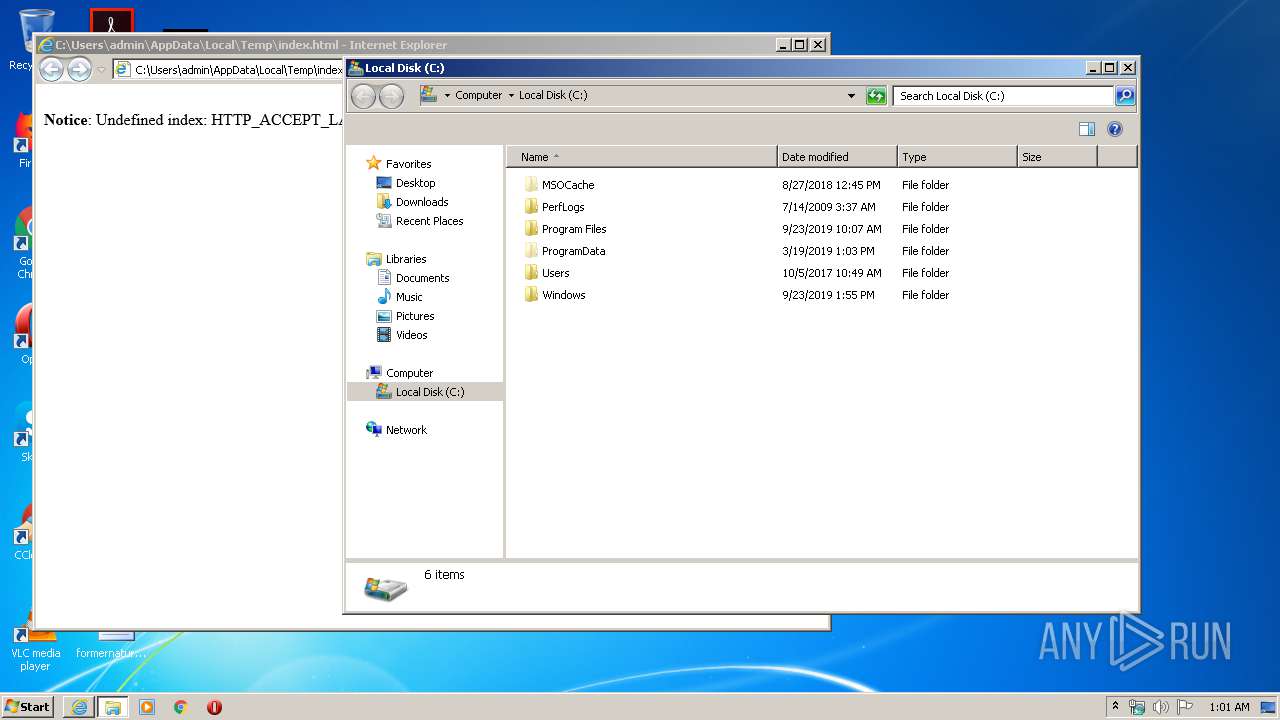
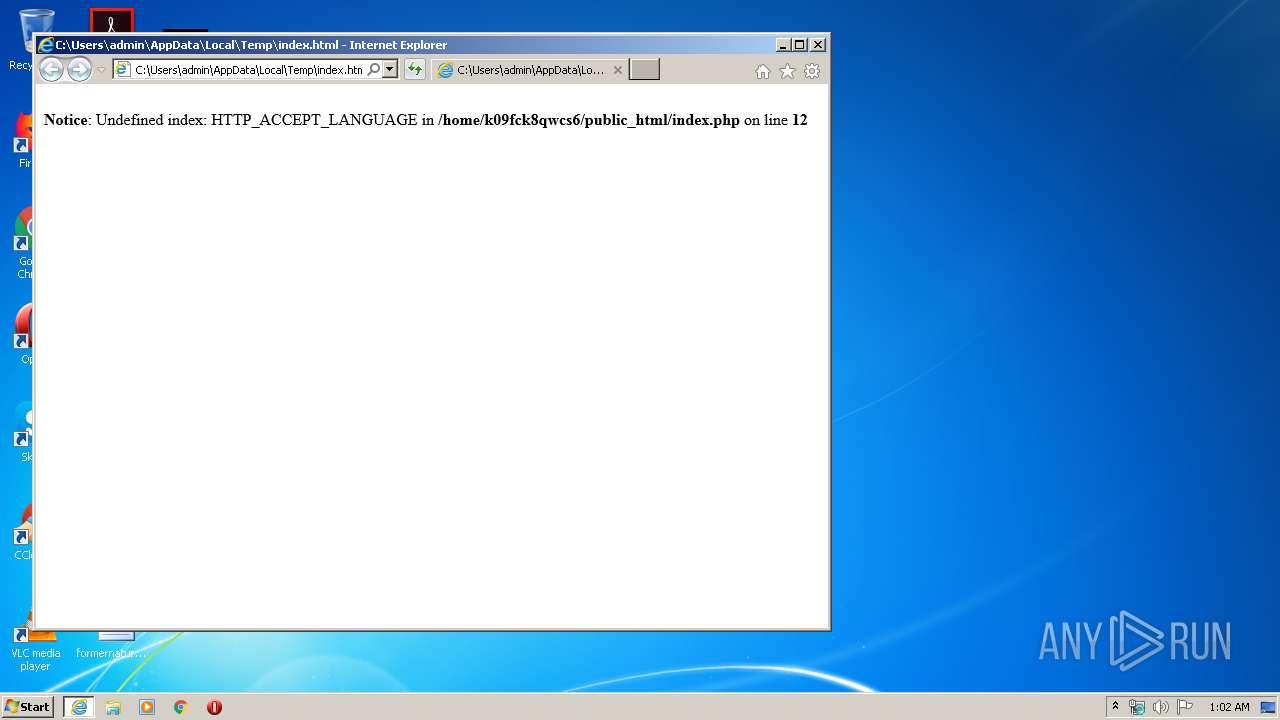
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text |
| MD5: | C71C03CB7B0E5D0BA2C46D83D2083028 |
| SHA1: | 6B69DA6BCF38C4FD69E9A90983C53726A04F3CA6 |
| SHA256: | 9CD0A4184294E5C264321388E4957D57D5A726182DA4BA3A5F46C2F405AFBF4E |
| SSDEEP: | 6:qTCgbhG3LkLBqWWXS462DPG12CH0725AGMRJViUK2Ewb:qTCgdG3LC1WXS4jy12CI25AGMxiUZb |
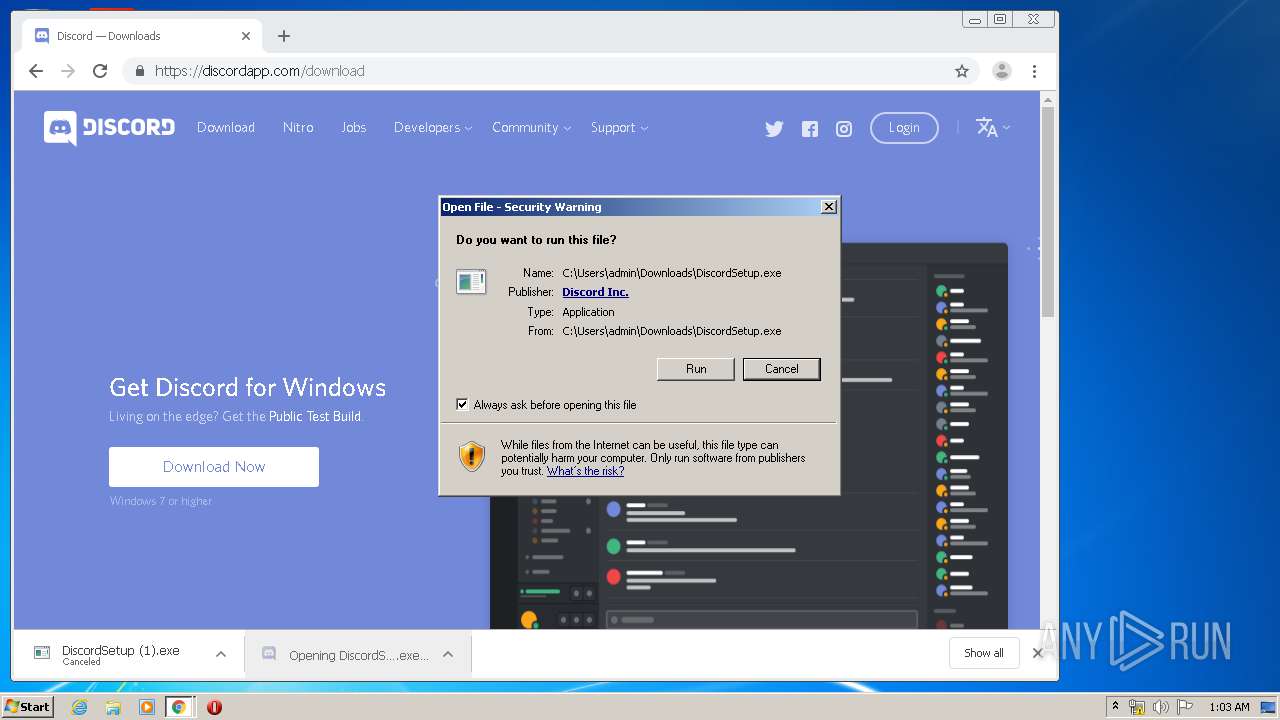
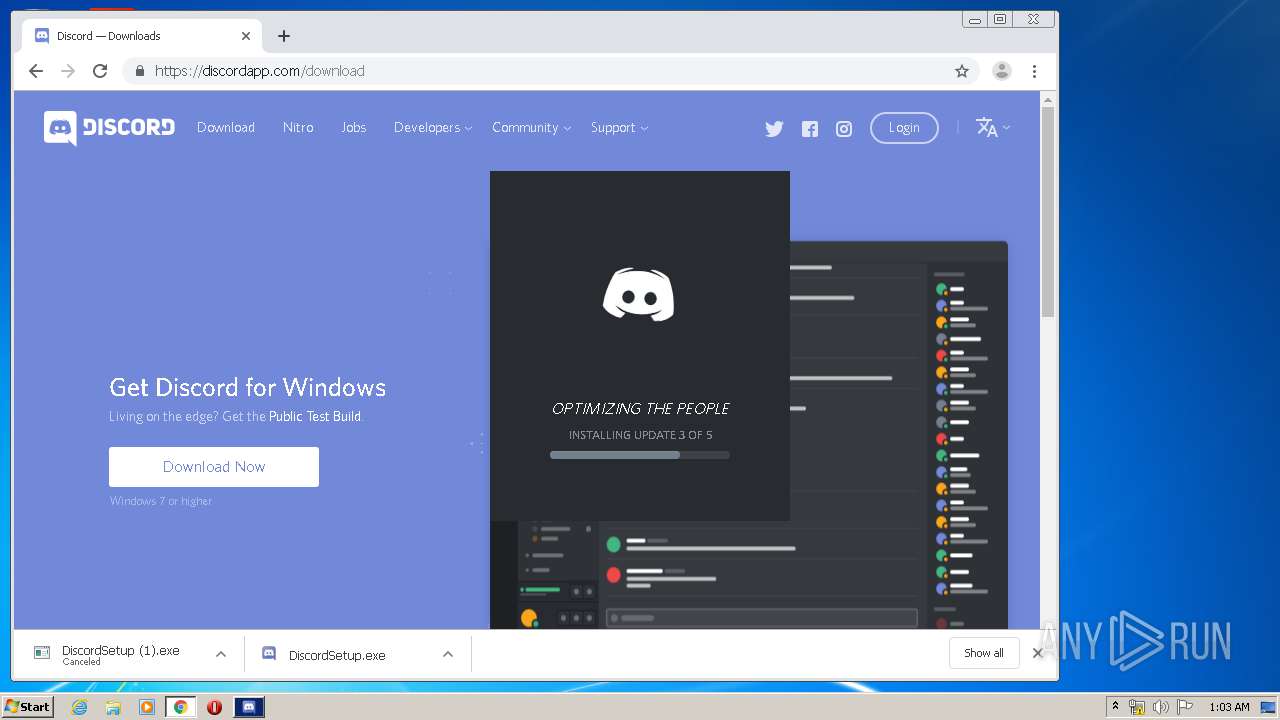
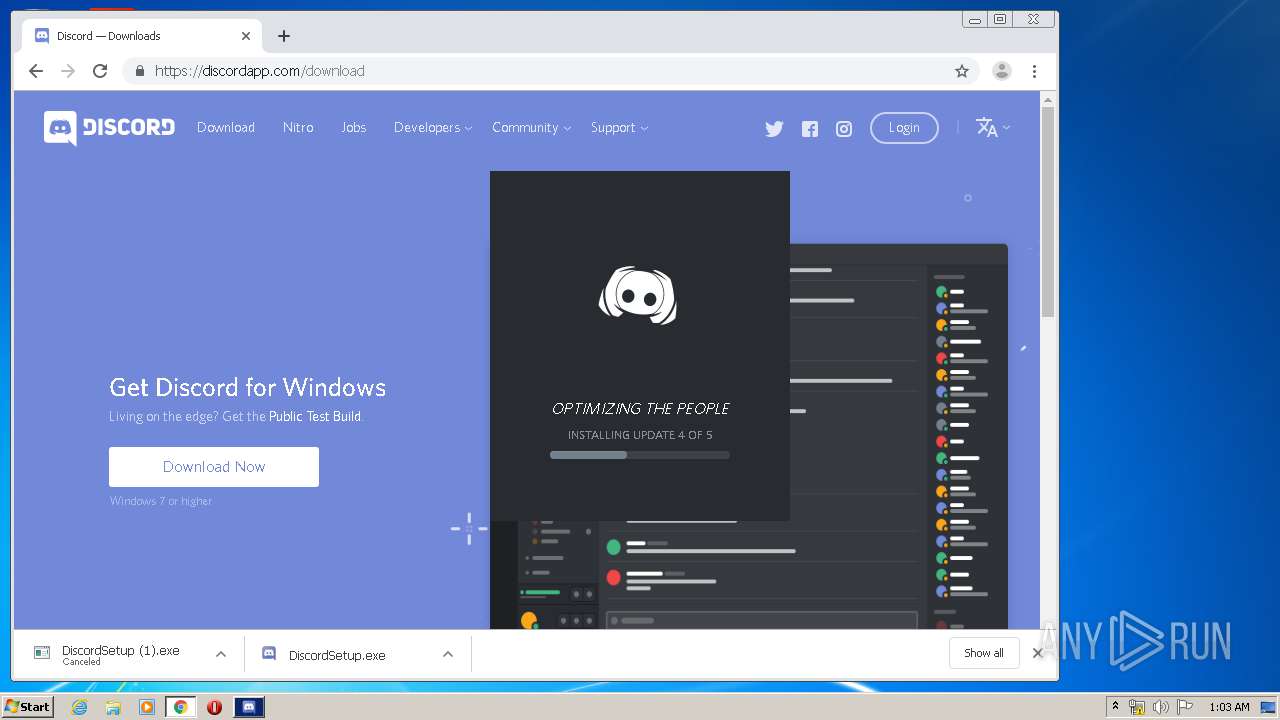
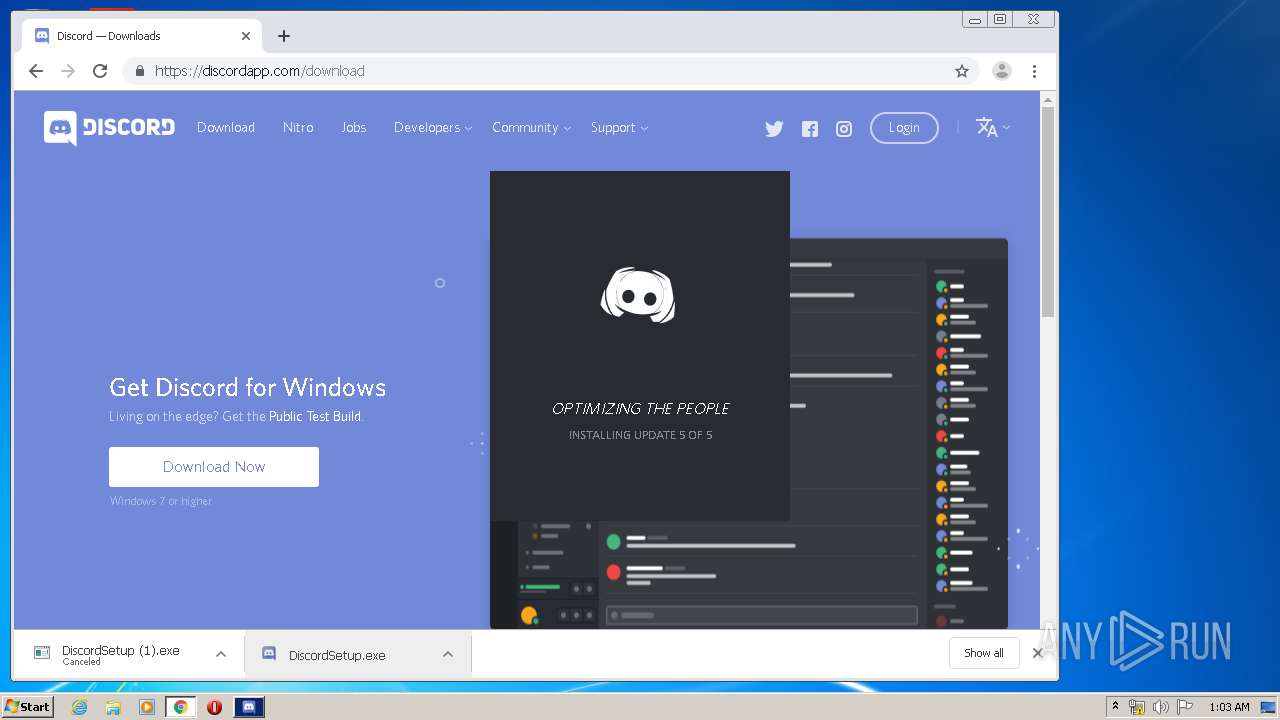
MALICIOUS
Application was dropped or rewritten from another process
- DiscordSetup.exe (PID: 3196)
- Squirrel.exe (PID: 348)
- Update.exe (PID: 792)
- Update.exe (PID: 2888)
- Update.exe (PID: 3844)
- Update.exe (PID: 3508)
Loads dropped or rewritten executable
- Discord.exe (PID: 3600)
- Discord.exe (PID: 3088)
- Discord.exe (PID: 2452)
- Discord.exe (PID: 2624)
- Discord.exe (PID: 3112)
- Discord.exe (PID: 2132)
- Discord.exe (PID: 2060)
- Discord.exe (PID: 952)
- Discord.exe (PID: 3512)
- Discord.exe (PID: 3876)
- Discord.exe (PID: 3384)
- Discord.exe (PID: 2412)
- Discord.exe (PID: 1708)
- Discord.exe (PID: 3796)
- Discord.exe (PID: 2764)
- Discord.exe (PID: 968)
- Discord.exe (PID: 3688)
Changes the autorun value in the registry
- reg.exe (PID: 3144)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 4048)
- DiscordSetup.exe (PID: 3196)
- Update.exe (PID: 792)
- Discord.exe (PID: 3112)
Modifies files in Chrome extension folder
- chrome.exe (PID: 4048)
Starts itself from another location
- Update.exe (PID: 792)
Application launched itself
- Discord.exe (PID: 3600)
- Discord.exe (PID: 2624)
- Discord.exe (PID: 3112)
- Discord.exe (PID: 2452)
- Discord.exe (PID: 1708)
Uses REG.EXE to modify Windows registry
- Discord.exe (PID: 3600)
Creates files in the user directory
- Update.exe (PID: 2888)
- Discord.exe (PID: 2452)
- Discord.exe (PID: 3112)
- Discord.exe (PID: 3512)
Modifies the open verb of a shell class
- reg.exe (PID: 3228)
Creates a software uninstall entry
- Update.exe (PID: 792)
Reads Environment values
- Update.exe (PID: 3844)
- Update.exe (PID: 3508)
Starts CMD.EXE for commands execution
- Discord.exe (PID: 3512)
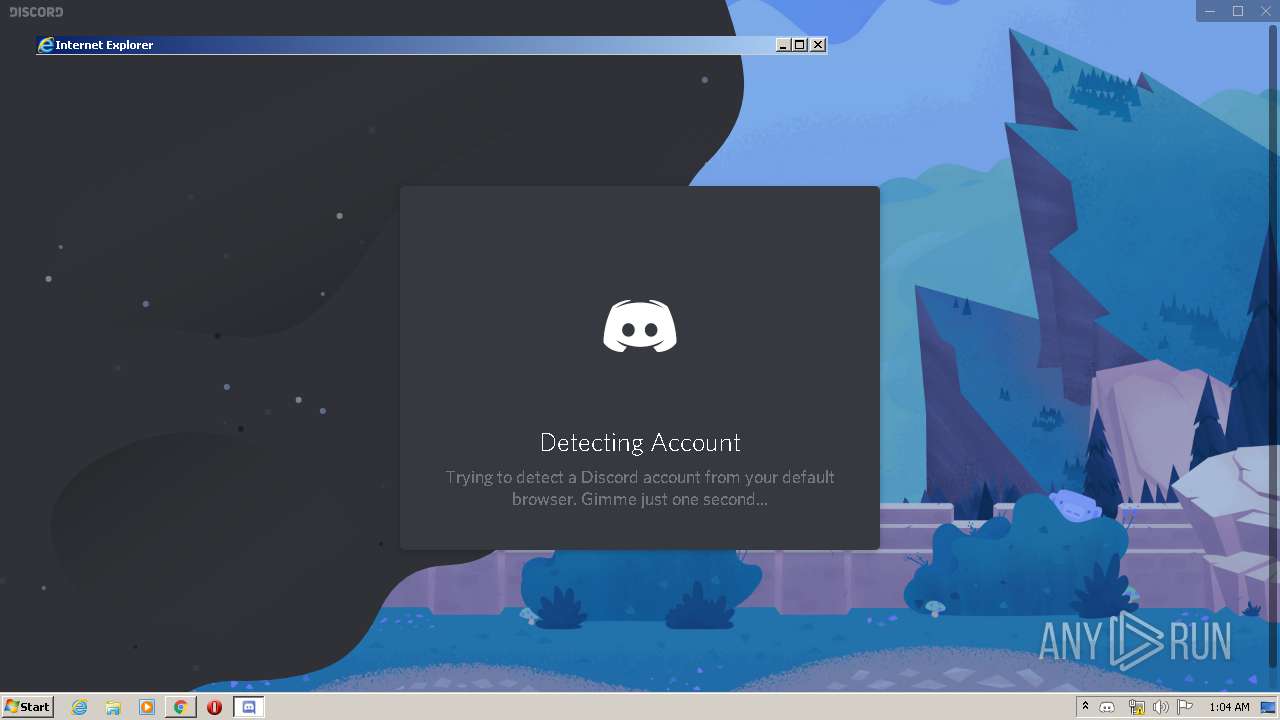
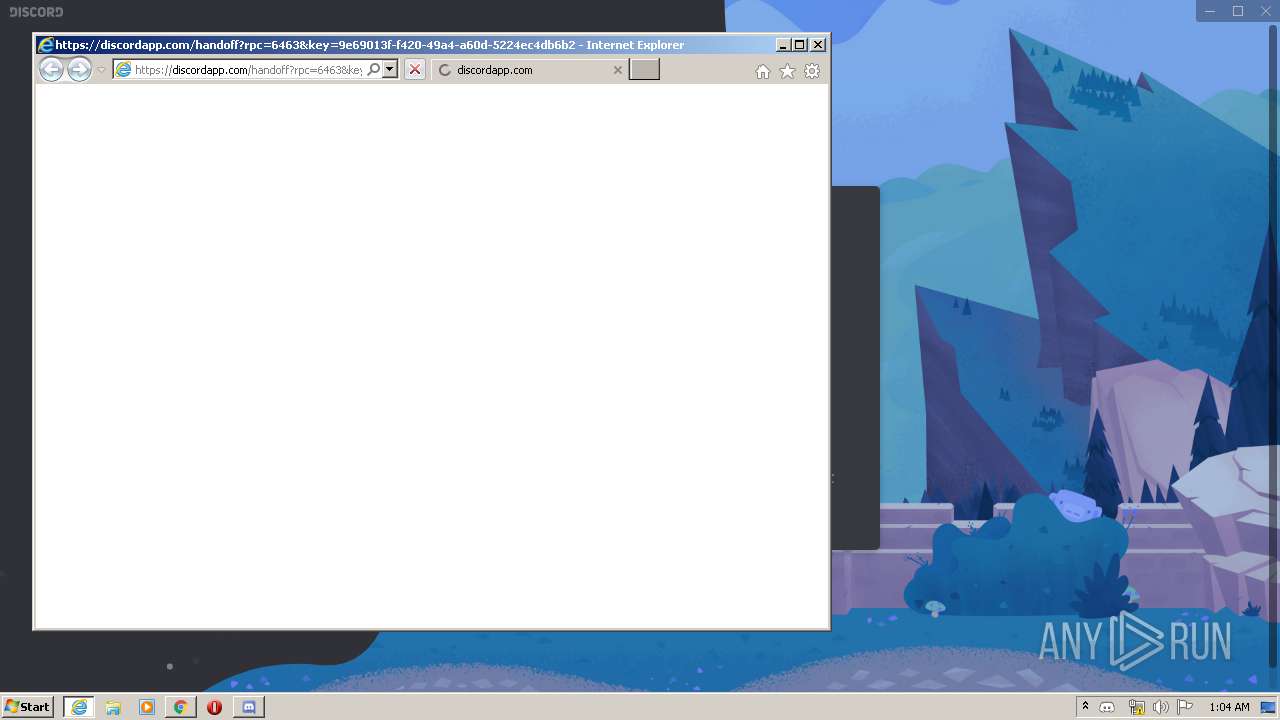
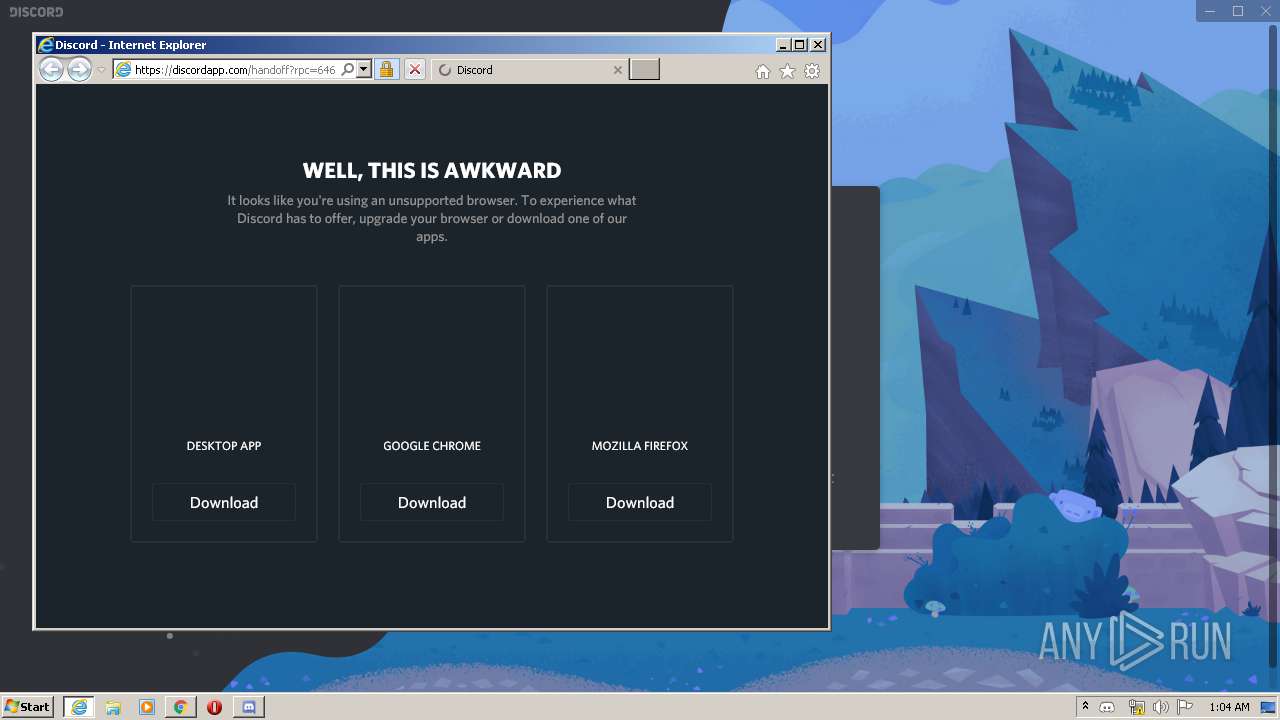
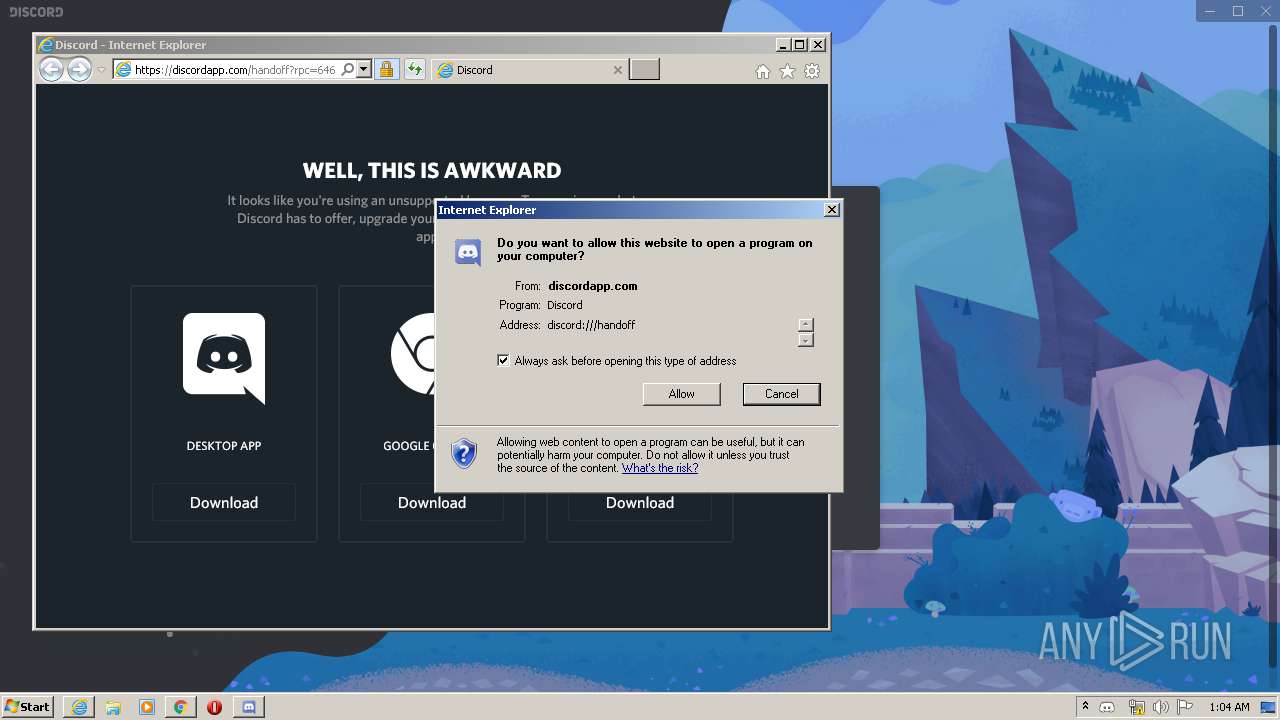
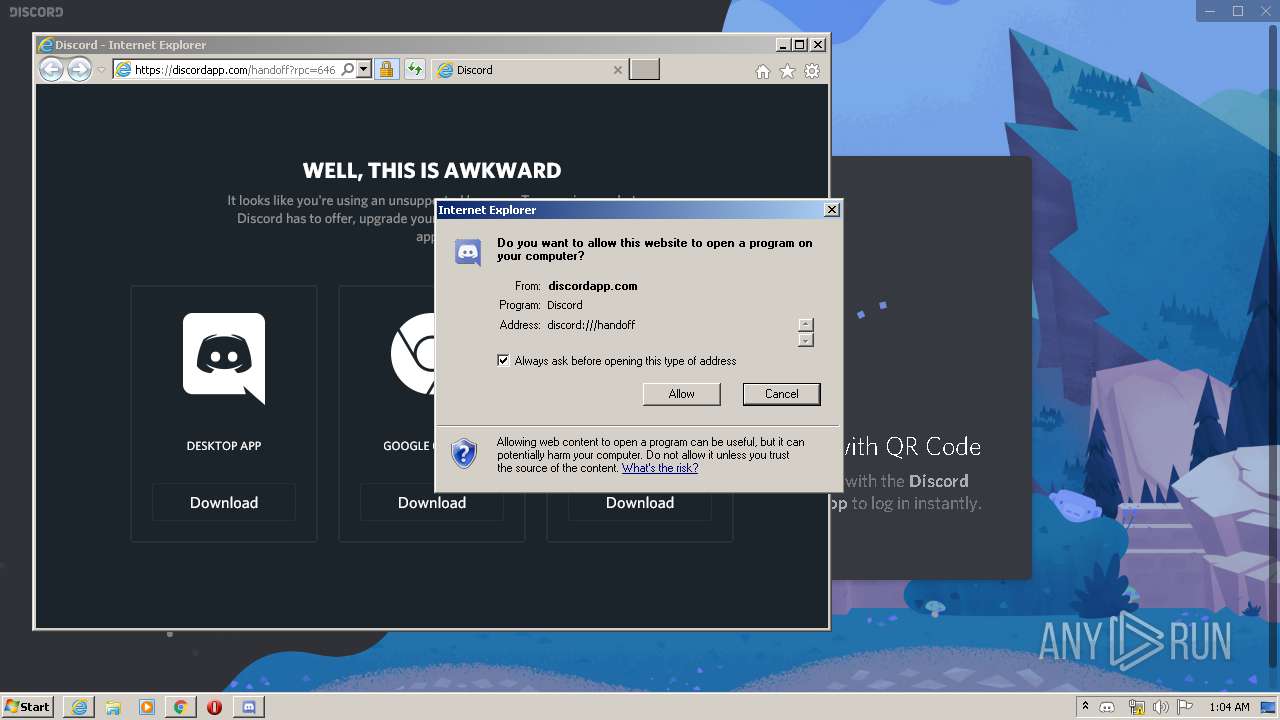
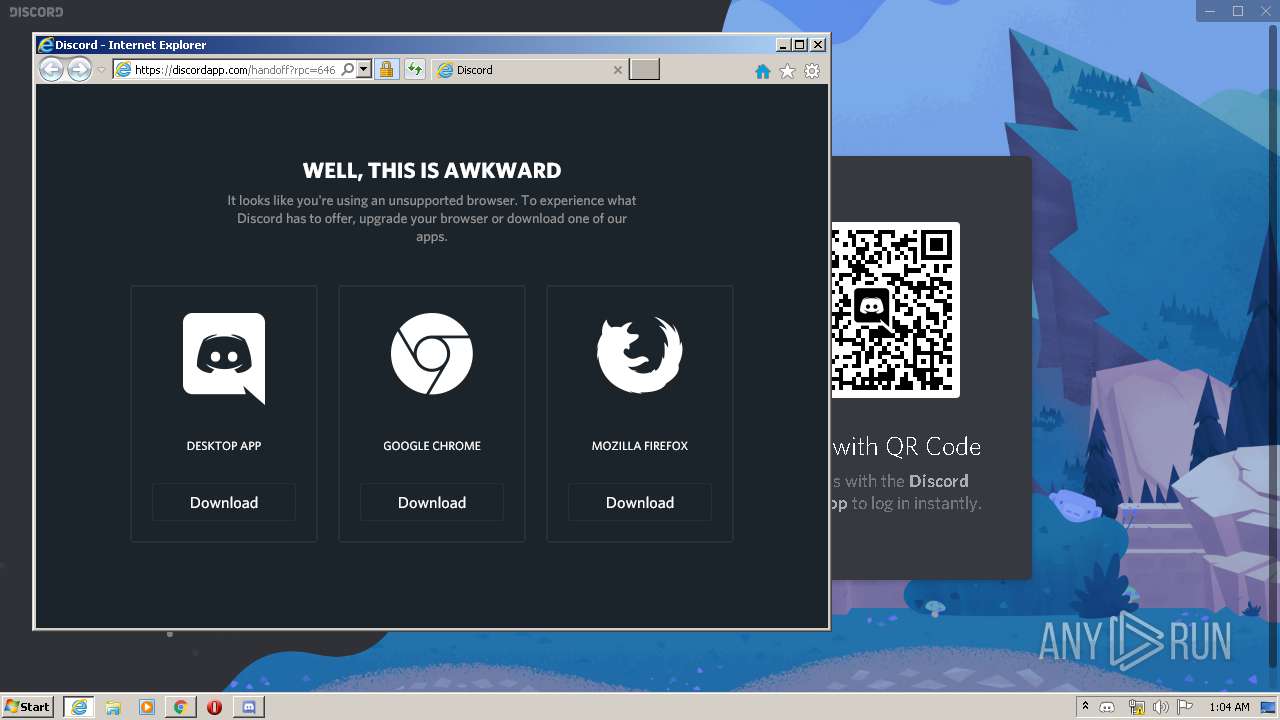
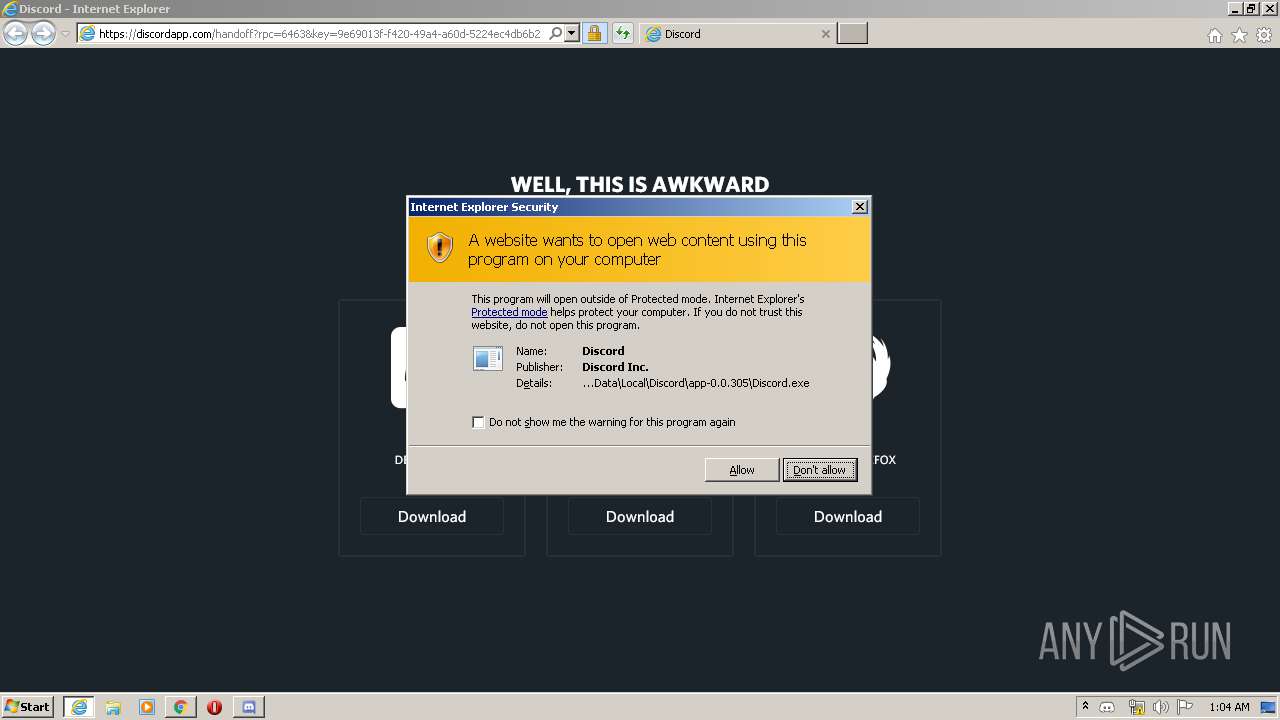
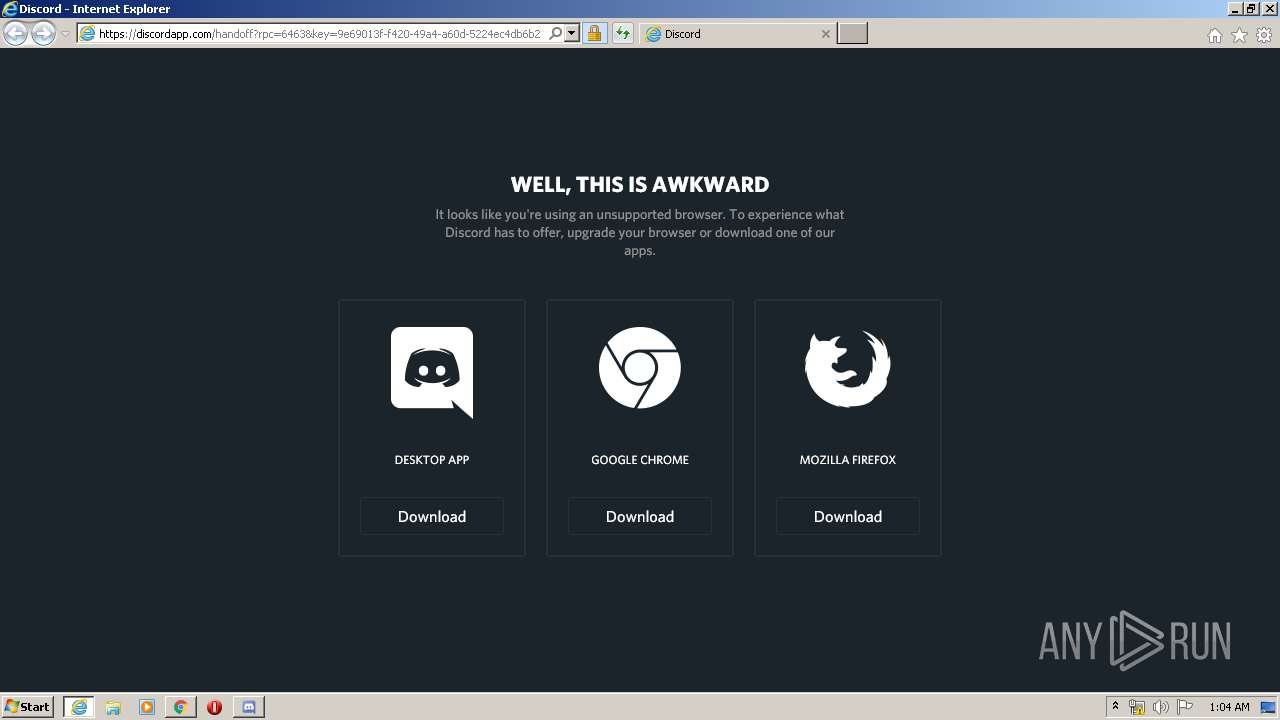
Starts Internet Explorer
- Discord.exe (PID: 3112)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2856)
- iexplore.exe (PID: 3740)
Reads internet explorer settings
- iexplore.exe (PID: 3504)
- iexplore.exe (PID: 1876)
Reads Internet Cache Settings
- iexplore.exe (PID: 2844)
- iexplore.exe (PID: 2856)
- chrome.exe (PID: 4048)
- iexplore.exe (PID: 1876)
- iexplore.exe (PID: 3740)
Application launched itself
- iexplore.exe (PID: 3504)
- chrome.exe (PID: 4048)
- iexplore.exe (PID: 2856)
- iexplore.exe (PID: 3740)
Reads the hosts file
- chrome.exe (PID: 4048)
- chrome.exe (PID: 2696)
- Discord.exe (PID: 2452)
- Discord.exe (PID: 3112)
- Discord.exe (PID: 3600)
- Discord.exe (PID: 1708)
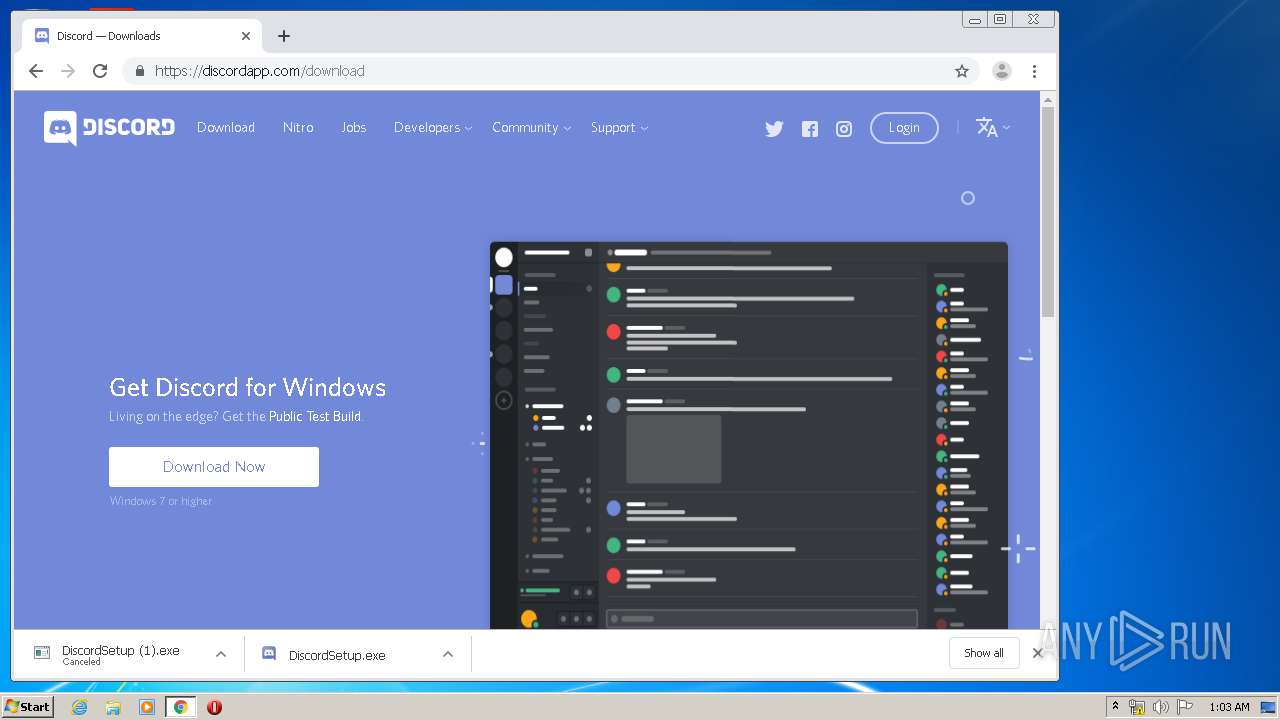
Manual execution by user
- chrome.exe (PID: 4048)
Reads settings of System Certificates
- chrome.exe (PID: 4048)
- chrome.exe (PID: 2696)
- iexplore.exe (PID: 2856)
- iexplore.exe (PID: 1876)
- iexplore.exe (PID: 3740)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1876)
Creates files in the user directory
- iexplore.exe (PID: 1876)
- iexplore.exe (PID: 3740)
Changes settings of System certificates
- iexplore.exe (PID: 2856)
- iexplore.exe (PID: 3740)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2856)
- iexplore.exe (PID: 3740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
118
Monitored processes
69
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Users\admin\AppData\Local\Discord\app-0.0.305\Squirrel.exe" --updateSelf=C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | C:\Users\admin\AppData\Local\Discord\app-0.0.305\Squirrel.exe | — | Update.exe | |||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 4294967295 Version: 1.1.1.0 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,17345928665436654335,2427945480675629373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4740985135553340507 --mojo-platform-channel-handle=4460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,17345928665436654335,2427945480675629373,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12878000199275675074 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4596 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe" --install . | C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | DiscordSetup.exe | ||||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 1.1.1.0 Modules
| |||||||||||||||
| 952 | "C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --force-color-profile=srgb --enable-features=SharedArrayBuffer --service-pipe-token=6353747778290529796 --lang=en-US --app-user-model-id=com.squirrel.Discord.Discord --app-path="C:\Users\admin\AppData\Local\Discord\app-0.0.305\resources\app.asar" --node-integration=true --webview-tag=true --no-sandbox --background-color=#fff --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6353747778290529796 --renderer-client-id=4 --mojo-platform-channel-handle=1372 /prefetch:1 | C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe | — | Discord.exe | |||||||||||
User: admin Company: Discord Inc. Integrity Level: MEDIUM Description: Discord Exit code: 0 Version: 0.0.305 Modules
| |||||||||||||||
| 968 | C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe --reporter-url=https://sentry.io/api/146342/minidump/?sentry_key=384ce4413de74fe0be270abe03b2b35a --application-name=Discord "--crashes-directory=C:\Users\admin\AppData\Local\Temp\Discord Crashes" --v=1 | C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe | Discord.exe | ||||||||||||
User: admin Company: Discord Inc. Integrity Level: MEDIUM Description: Discord Exit code: 2 Version: 0.0.305 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,17345928665436654335,2427945480675629373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7154476177727890113 --mojo-platform-channel-handle=3692 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
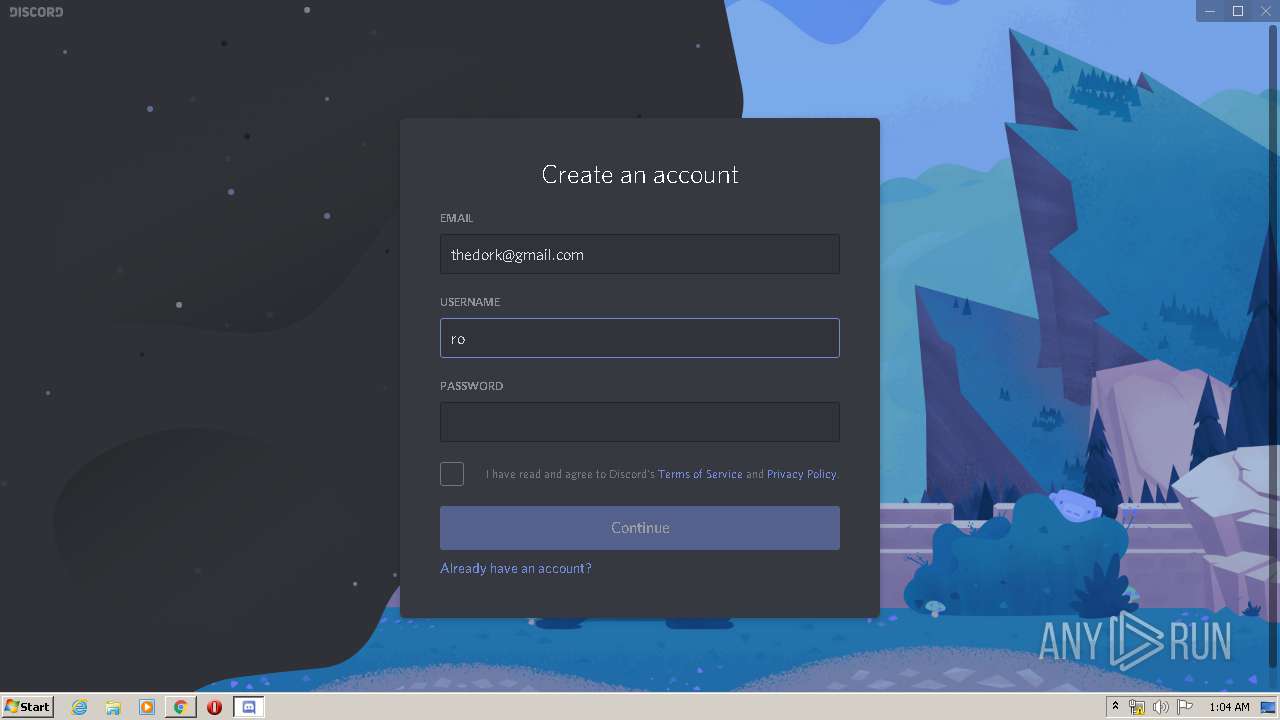
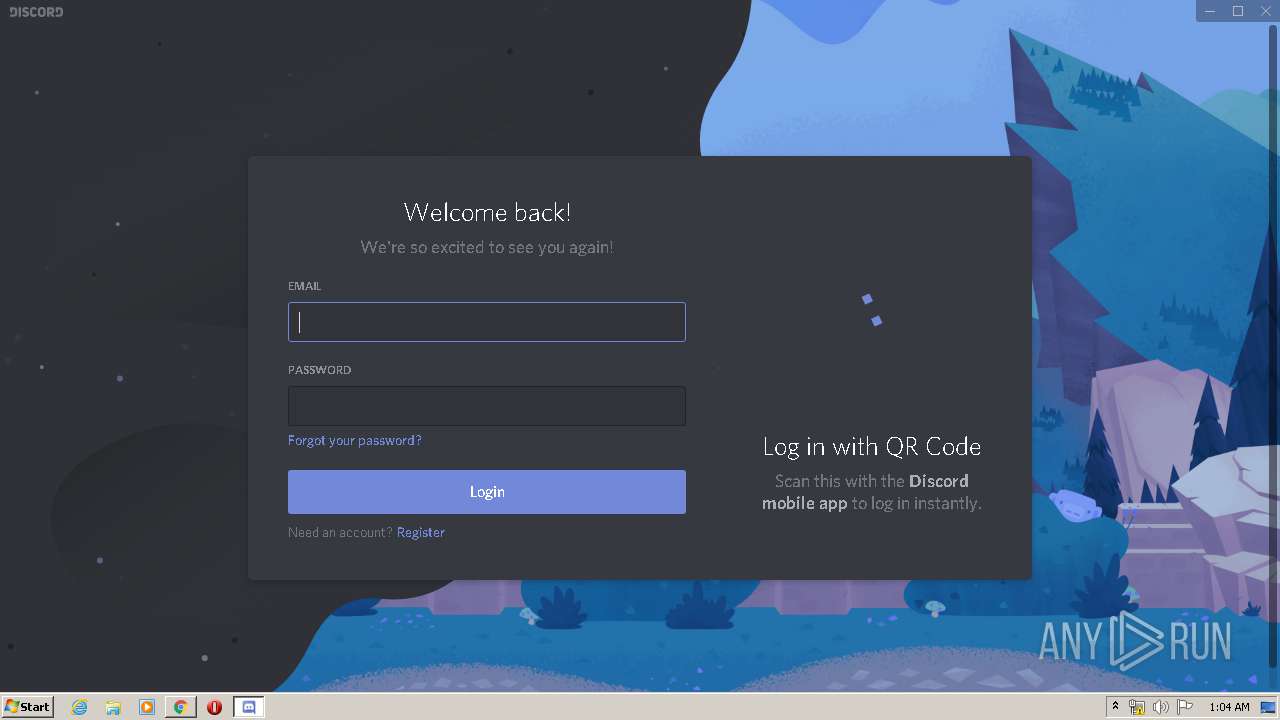
| 1708 | "C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe" --url -- "discord:///handoff" | C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe | — | iexplore.exe | |||||||||||
User: admin Company: Discord Inc. Integrity Level: MEDIUM Description: Discord Exit code: 0 Version: 0.0.305 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3740 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,17345928665436654335,2427945480675629373,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6771903461076913837 --mojo-platform-channel-handle=3160 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
17 772
Read events
4 668
Write events
8 817
Delete events
4 287
Modification events
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3216239786 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30796059 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
46
Suspicious files
152
Text files
1 186
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0EC79BF2E7D745B3.TMP | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF795F72E16BD39ED2.TMP | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF025D6FD21CA2737D.TMP | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC43DEE1CEAB6AB09.TMP | — | |
MD5:— | SHA256:— | |||
| 4048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E507D97-FD0.pma | — | |
MD5:— | SHA256:— | |||
| 4048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c78a442c-9786-493c-b9e8-6b9a44881690.tmp | — | |
MD5:— | SHA256:— | |||
| 4048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{F5083D85-550E-11EA-972D-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 4048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
98
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1876 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | US | der | 471 b | whitelisted |
2696 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 520 b | whitelisted |
1876 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 312 b | whitelisted |
1876 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | US | der | 471 b | whitelisted |
1876 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEESdv3pClq0bcSaWGwue8Dw%3D | US | der | 279 b | whitelisted |
2696 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 515 b | whitelisted |
1876 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 312 b | whitelisted |
1876 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEESdv3pClq0bcSaWGwue8Dw%3D | US | der | 279 b | whitelisted |
2856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2856 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2696 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.18.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.22.14:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2696 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2696 | chrome.exe | 216.58.205.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 87.245.200.147:80 | r8---sn-gxuog0-n8vl.gvt1.com | RETN Limited | RU | whitelisted |
2696 | chrome.exe | 172.217.23.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
Threats
Process | Message |
|---|---|
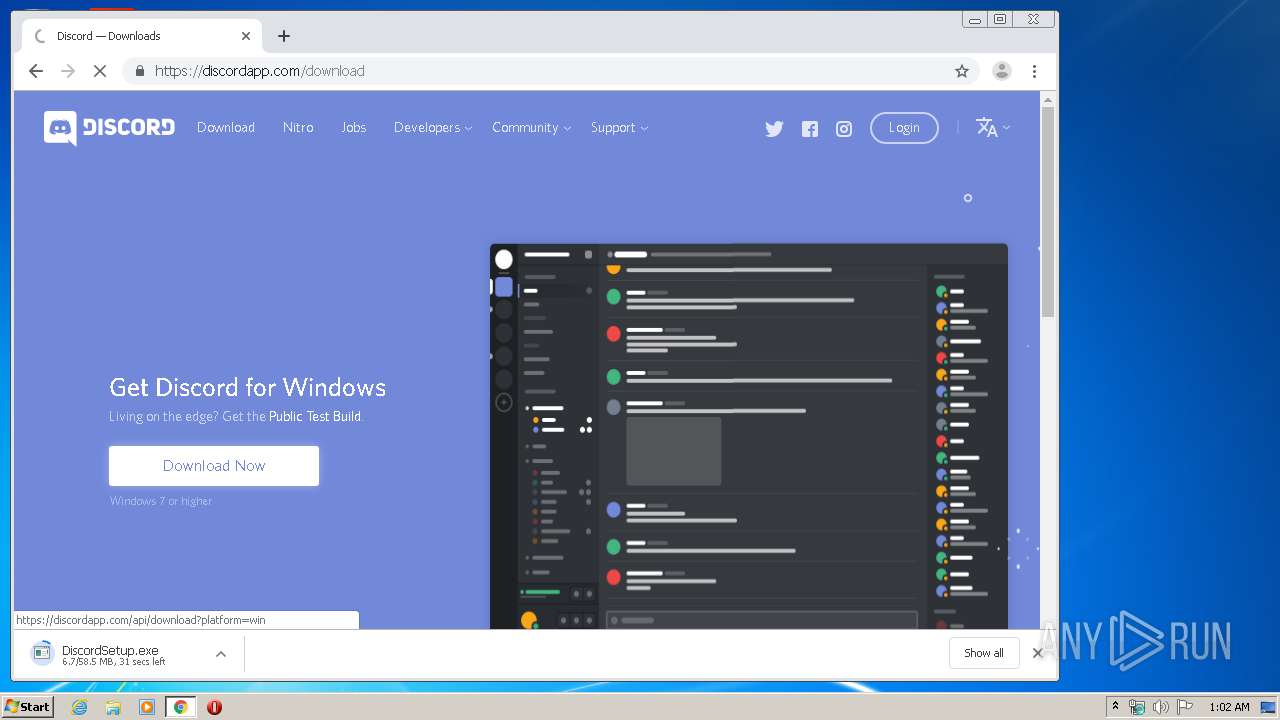
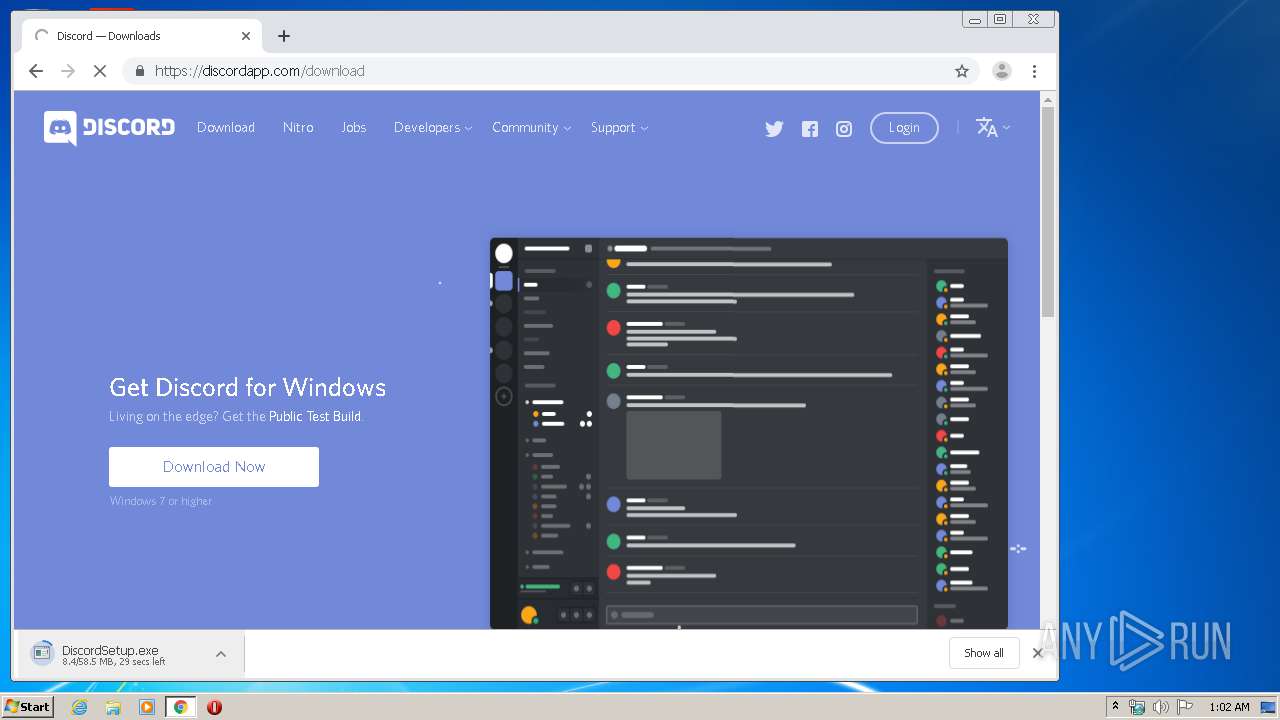
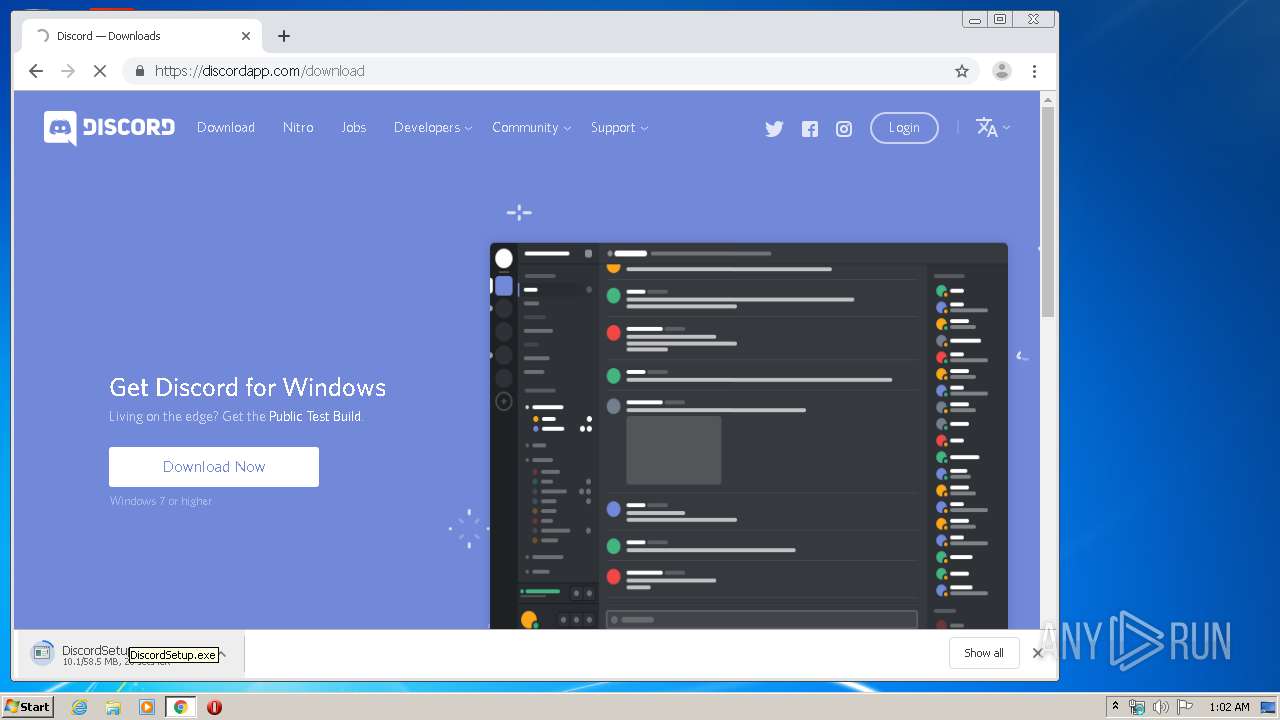
DiscordSetup.exe | Start up installer: |
DiscordSetup.exe | Elevated process: ?
|
DiscordSetup.exe | Want standard install |
Discord.exe | [3384:2552:0222/010401.701:VERBOSE1:crash_service_main.cc(81)] Session start. cmdline is [--reporter-url=https://sentry.io/api/146342/minidump/?sentry_key=384ce4413de74fe0be270abe03b2b35a --application-name=Discord "--crashes-directory=C:\Users\admin\AppData\Local\Temp\Discord Crashes" --v=1]
|
Discord.exe | [3384:2552:0222/010401.702:VERBOSE1:crash_service.cc(279)] checkpoint is C:\Users\admin\AppData\Local\Temp\Discord Crashes\crash_checkpoint.txt
server is https://sentry.io/api/146342/minidump/?sentry_key=384ce4413de74fe0be270abe03b2b35a
maximum 128 reports/day
reporter is electron-crash-service
|
Discord.exe | [3384:2552:0222/010401.702:VERBOSE1:crash_service.cc(147)] window handle is 00070246
|
Discord.exe | [3384:2552:0222/010401.702:VERBOSE1:crash_service_main.cc(95)] Ready to process crash requests
|
Discord.exe | [3384:3152:0222/010401.702:VERBOSE1:crash_service.cc(309)] client start. pid = 3112
|
Discord.exe | [3384:2552:0222/010401.702:VERBOSE1:crash_service.cc(275)] pipe name is \\.\pipe\Discord Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\Discord Crashes
|
Discord.exe | [3384:3152:0222/010546.332:VERBOSE1:crash_service.cc(309)] client start. pid = 3112
|