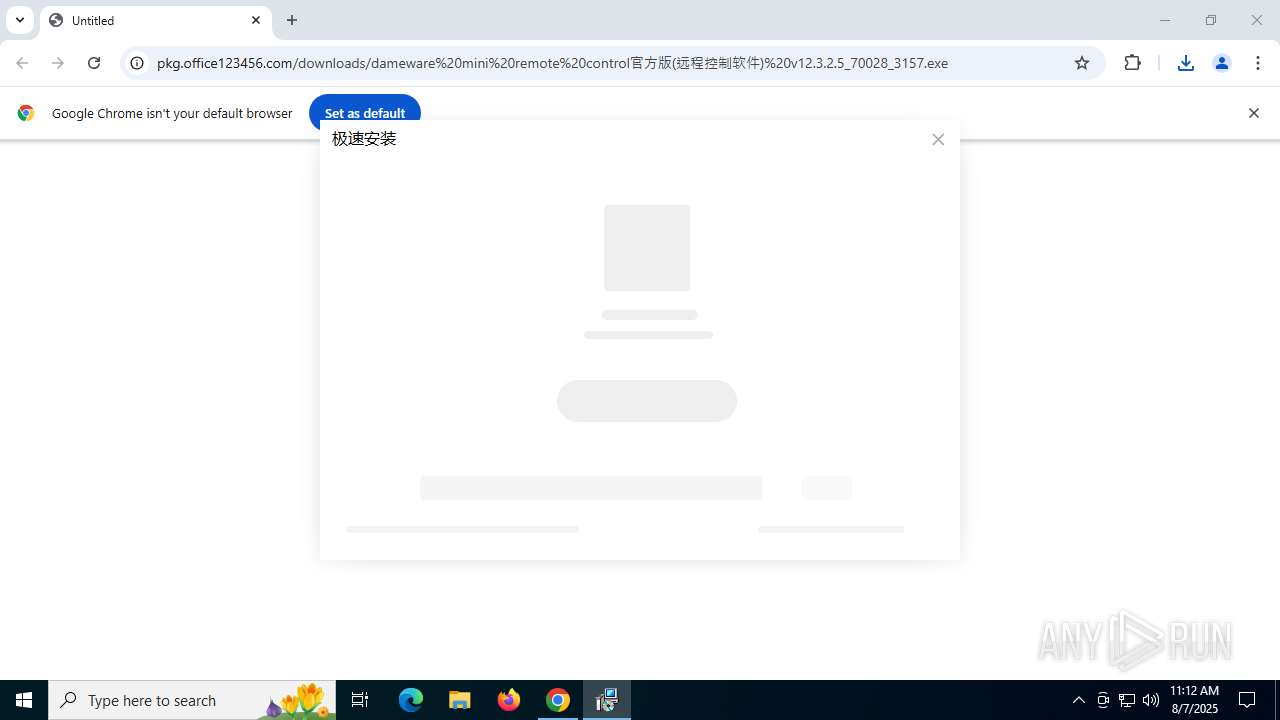
| URL: | https://pkg.office123456.com/downloads/dameware%20mini%20remote%20control%E5%AE%98%E6%96%B9%E7%89%88(%E8%BF%9C%E7%A8%8B%E6%8E%A7%E5%88%B6%E8%BD%AF%E4%BB%B6)%20v12.3.2.5_70028_3157.exe |
| Full analysis: | https://app.any.run/tasks/e4b99e78-6355-4e85-a187-3c61d34fa6fe |
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2025, 11:12:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | FCC28C1FAE4F63154BAA6C4DB0ADC544 |
| SHA1: | 3535EA21660BC45CE07F0DAE2B5857584B7531E2 |
| SHA256: | 9CC9BC8C32B288FA341C556B6B313C1C55415AD717E52A15CA8BE938E5EF2B53 |
| SSDEEP: | 3:N8KfRW6MXKyIuRNXrKRlXVGQCQApRRfFz1PRAgSAk4lMqAnjjAUAZA8LWzm/6TUC:2KM9ayIuRNbHJdRAgnVxWzkdC |
MALICIOUS
Changes Windows Defender settings
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
Adds path to the Windows Defender exclusion list
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
Registers / Runs the DLL via REGSVR32.EXE
- CapableZip.exe (PID: 6012)
- CapableClear.exe (PID: 2076)
SUSPICIOUS
Script adds exclusion path to Windows Defender
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
Searches for installed software
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- About.exe (PID: 7236)
- About.exe (PID: 5724)
- Capable.exe (PID: 3872)
- CapableService.exe (PID: 1324)
- CapableZip.exe (PID: 6012)
- CapableClear.exe (PID: 2076)
- CapableZipSer.exe (PID: 7360)
- Capable.exe (PID: 7268)
- CapableClearSer.exe (PID: 7356)
- About.exe (PID: 7616)
- About.exe (PID: 700)
- CapableZip.exe (PID: 4676)
- regsvr32.exe (PID: 7724)
- BKUt.exe (PID: 7740)
- About.exe (PID: 7864)
Creates/Modifies COM task schedule object
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- regsvr32.exe (PID: 7724)
- regsvr32.exe (PID: 7812)
- BKUt.exe (PID: 7740)
Starts POWERSHELL.EXE for commands execution
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
Reads security settings of Internet Explorer
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- Capable.exe (PID: 3872)
- CapableService.exe (PID: 1324)
- Capable.exe (PID: 7268)
- CapableClearSer.exe (PID: 7356)
- CapableZipSer.exe (PID: 7360)
- About.exe (PID: 5724)
- About.exe (PID: 7236)
- About.exe (PID: 7616)
- CapableClear.exe (PID: 2076)
- CapableZip.exe (PID: 6012)
- About.exe (PID: 7864)
The process creates files with name similar to system file names
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- Capable.exe (PID: 7268)
Executable content was dropped or overwritten
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- CapableZip.exe (PID: 6012)
- Capable.exe (PID: 7268)
Creates a software uninstall entry
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
Executes as Windows Service
- CapableService.exe (PID: 1324)
- CapableClearSer.exe (PID: 7356)
- CapableZipSer.exe (PID: 7360)
Application launched itself
- Capable.exe (PID: 3872)
- About.exe (PID: 5724)
- About.exe (PID: 7236)
- About.exe (PID: 7616)
INFO
Application launched itself
- chrome.exe (PID: 6128)
Creates files or folders in the user directory
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- CapableService.exe (PID: 1324)
- CapableZip.exe (PID: 6012)
- CapableZipSer.exe (PID: 7360)
- CapableClearSer.exe (PID: 7356)
- Capable.exe (PID: 7268)
- About.exe (PID: 7616)
- BKUt.exe (PID: 7740)
- About.exe (PID: 7864)
Reads the computer name
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- CapableService.exe (PID: 1324)
- About.exe (PID: 7236)
- About.exe (PID: 5724)
- Capable.exe (PID: 3872)
- CapableZip.exe (PID: 6012)
- CapableClear.exe (PID: 2076)
- CapableClearSer.exe (PID: 7356)
- CapableZipSer.exe (PID: 7360)
- Capable.exe (PID: 7268)
- About.exe (PID: 7616)
- About.exe (PID: 700)
- CapableZip.exe (PID: 4676)
- About.exe (PID: 7864)
- BKUt.exe (PID: 7740)
Checks supported languages
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- About.exe (PID: 5724)
- Capable.exe (PID: 3872)
- Capable.exe (PID: 7268)
- CapableService.exe (PID: 1324)
- About.exe (PID: 7236)
- CapableClear.exe (PID: 2076)
- CapableZip.exe (PID: 6012)
- About.exe (PID: 7616)
- About.exe (PID: 700)
- CapableZipSer.exe (PID: 7360)
- CapableClearSer.exe (PID: 7356)
- CapableZip.exe (PID: 4676)
- BKUt.exe (PID: 7740)
- About.exe (PID: 7864)
Checks proxy server information
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- Capable.exe (PID: 7268)
- About.exe (PID: 7616)
The sample compiled with chinese language support
- chrome.exe (PID: 6128)
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- Capable.exe (PID: 7268)
Reads the machine GUID from the registry
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- BKUt.exe (PID: 7740)
Process checks computer location settings
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- Capable.exe (PID: 3872)
- About.exe (PID: 7236)
- About.exe (PID: 5724)
- CapableClear.exe (PID: 2076)
- CapableZip.exe (PID: 6012)
- About.exe (PID: 7616)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7920)
Executable content was dropped or overwritten
- chrome.exe (PID: 6128)
Create files in a temporary directory
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- Capable.exe (PID: 7268)
The sample compiled with english language support
- dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe (PID: 7608)
- Capable.exe (PID: 7268)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7920)
Creates files in the program directory
- BKUt.exe (PID: 7740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
173
Monitored processes
35
Malicious processes
4
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 700 | "C:\Users\admin\AppData\Local\CapableWin\About.exe" -yjlcme=szcrF+o+PDdfuqEBwRQ6gA== | C:\Users\admin\AppData\Local\CapableWin\About.exe | — | About.exe | |||||||||||
User: admin Company: 北京华网智讯软件有限公司 Integrity Level: HIGH Description: About.exe Exit code: 0 Version: 4.0.2.250717 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1976,i,13664680832095932464,15412643379008404122,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1964 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1212 | "C:\Windows\System32\regsvr32.exe" /s "C:\Users\admin\AppData\Local\CapableWin\Tools\Capable-Clear\CapableDoc64.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | CapableClear.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\Users\admin\AppData\Local\CapableWin\CapableService.exe -jqjtsu | C:\Users\admin\AppData\Local\CapableWin\CapableService.exe | services.exe | ||||||||||||
User: SYSTEM Company: 北京华网智讯软件有限公司 Integrity Level: SYSTEM Description: CapableService.exe Version: 4.0.2.250717 Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\AppData\Local\CapableWin\Tools\Capable-Clear\CapableClear.exe" -bboyge=zOZTYFWppW9/+twjoaBilw== | C:\Users\admin\AppData\Local\CapableWin\Tools\Capable-Clear\CapableClear.exe | — | Capable.exe | |||||||||||
User: admin Company: 北京华网智讯软件有限公司 Integrity Level: HIGH Description: CapableClear.exe Exit code: 0 Version: 4.0.2.250717 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2284,i,13664680832095932464,15412643379008404122,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2356 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2668 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4548,i,13664680832095932464,15412643379008404122,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3872 | "C:\Users\admin\AppData\Local\CapableWin\Capable.exe" -yjlcme=uRllQV0FK9xObNn03GmrUg== | C:\Users\admin\AppData\Local\CapableWin\Capable.exe | — | dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | |||||||||||
User: admin Company: 北京华网智讯软件有限公司 Integrity Level: HIGH Description: 全能电脑助手 Exit code: 0 Version: 4.0.2.250717 Modules
| |||||||||||||||
| 4124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3068,i,13664680832095932464,15412643379008404122,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
18 495
Read events
18 271
Write events
212
Delete events
12
Modification events
| (PID) Process: | (6128) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6128) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6128) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6128) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6128) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7608) dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\CapableWin\mkey |
| Operation: | write | Name: | wsjevs |
Value: 0 | |||
| (PID) Process: | (7608) dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\CapableWin\mkey |
| Operation: | write | Name: | nezmtm |
Value: 70028 | |||
| (PID) Process: | (7608) dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\CapableWin\mkey |
| Operation: | write | Name: | htsfkq |
Value: C:\Users\admin\AppData\Local\CapableWin\ | |||
| (PID) Process: | (7608) dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\CapableWin\mkey |
| Operation: | write | Name: | ZfcVuBkI |
Value: dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | |||
| (PID) Process: | (7608) dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\CapableWin\mkey |
| Operation: | write | Name: | niohnr |
Value: 1754564873 | |||
Executable files
48
Suspicious files
21
Text files
43
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18cf61.TMP | — | |
MD5:— | SHA256:— | |||
| 6128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18cf70.TMP | — | |
MD5:— | SHA256:— | |||
| 6128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF18cf80.TMP | — | |
MD5:— | SHA256:— | |||
| 6128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF18cf90.TMP | — | |
MD5:— | SHA256:— | |||
| 6128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF18cf90.TMP | — | |
MD5:— | SHA256:— | |||
| 6128 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
69
DNS requests
39
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6240 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5556 | chrome.exe | GET | 200 | 142.250.185.78:80 | http://clients2.google.com/time/1/current?cup2key=8:kAEKG0ZFJC0tCl-h0zD_gdTAo-3JcAHeo61nLsm2j0g&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 106 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
7608 | dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | GET | 200 | 106.14.92.120:80 | http://jto.newtab123.com/dvi0vp/?d=nkNu5/fIxpgdAdMUN4TAObbMtuDPAzl20wCNLe6Htii4JMGfT9vC7vrhZhzIs7jr+LmRgYoRxF07RmZW9vDy+pTBwcGXS30aR+8avCsGqVybfAPaAShx0Ml8Qoehc53dXYEiHA97Dg+1/gbuANuPIEJagzADDdBsNhYjn+h5FaHpTQqz2UW7bvp4RNcY4BIuZIVHBspVq1exkgAFLg/gks6rJ8dZPWh7XZV/1GXLBtC6HLs+wf8o6Cn1ya7z7WY5&_=1754565158 | CN | — | — | unknown |
7608 | dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | GET | 200 | 106.14.92.120:80 | http://jto.newtab123.com/dvi0vp/?d=nkNu5/fIxpgdAdMUN4TAOdWEdTEZakBwz4rrzooOHG9wmbS7vn+zeiJnYbb0T2hTUEfiAA8bsbx7eaNR0NT0PH5Me1ljYFzOVia+N+5X9iF9vJ6b3YvZ+hoF0PCy0DoehvS6wiCL8Eq+BbyQrUPD369Oj3nFy/RWNv4fr7ASsDb6RZcPgxduB3eZqFi1e8mA9VuHvOPzyC0cMtvIFT6NsNvY0tQigZsN9nl1BTBx90SYiwLPIVhbfz6miTv2YZv4dj0LRgiHzCqJAdstPlAkRPJFE+3N3qsHWueOzXcod4pMIkQH1oTL+yXP7QepJOVPDRngus4c/WjbR9ZzfVw+c9Ry/Rtriegchb3lQSdv8Cx1mWz34m4TvbvXWD8mMA1RXDH6eGonDsRA0p8e0E/M7PFI/8KEi9Lpdzd/+YqV2Xp2Vg2bjktRU56smHKQ5Y1KD46iKoNT3UoC8BLGCdy3eVekQt9oNst4ItJKfa4giS4=&_=1754565158 | CN | — | — | unknown |
7608 | dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | GET | 200 | 168.235.193.153:80 | http://ott.newtab123.com/dvi0vp/cp/p/?p=b0FL9fZkGvdhJLphXdsUqw==&_=1754565158 | US | text | 143 b | unknown |
7608 | dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | GET | 200 | 168.235.193.153:80 | http://ott.newtab123.com/dvi0vp/tb/cf/?p=2C/ksDx6wUa8UmpfsYgNyVjSKk5gxCQJH3YMcA2x6NmENt01rcHcLT3p4uQhlnxM&_=1754565159 | US | text | 128 b | unknown |
7608 | dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | GET | 200 | 168.235.193.153:80 | http://ott.newtab123.com/dvi0vp/cp/cloud/?p=E/0xt/tLzGfe29WlF6bZScLSO9G5o1E+ESJ6nmQkFrR7sdpmNZ/BDb7STRxtAzpO2ftpvv6rVRJRE4JuPWBHWkjtQ1iwp2sRMWxqZEwt3OrNyqY7RgAsf6u5c/sjSDF0V8k3EVMvCA9Z5nJdYNVBY6DKrEDNRUAZ24skvat5Wsmd+NPUFRafF1LeLN3rqTleAilklaJQMtTqYcdh3TLEAk3ZR2rO7+54MokTq0sCDS0=&_=1754565159 | US | text | 1.50 Kb | unknown |
7608 | dameware mini remote control官方版(远程控制软件) v12.3.2.5_70028_3157.exe | GET | 200 | 106.14.92.120:80 | http://jto.newtab123.com/dvi0vp/?d=nkNu5/fIxpgdAdMUN4TAOdWEdTEZakBwz4rrzooOHG9wmbS7vn+zeiJnYbb0T2hTUEfiAA8bsbx7eaNR0NT0PH5Me1ljYFzOVia+N+5X9iF9vJ6b3YvZ+hoF0PCy0DoemaYAc3G6hMyDW9Xn+NG6X1tO99/EyOCRp77yNHsJ4mezGjZVHghlxWi0bv1dQQe7fWZ1VLAREyQ1tHA/gdb7PpWCFJcRylepDq3lc24luCgiWf9IUFw+RoHJml4z8WSG4MQhgKyUCTRyiC2ABYtjtFk5iZKGb+0F+qpcv53+jhY5dv6dmKAuZuECpXUleKQQBB+OKwJw38G+/4mecV2Ef/apr8Q0EJi+IURRtdD79SHRT+zSZudeJQRRwiTzK/cDOLzamd9OLXzA5LQwpstXDOaMECPMBALqxrfsImObjEz8P+n5qrM4aDGXgFuTHCU5nwei+9dEdRgFe87Ryq0a1bh/JwAnyhQv3JclQlu5x4E=&_=1754565166 | CN | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
472 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5556 | chrome.exe | 142.250.186.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
5556 | chrome.exe | 142.250.185.78:80 | clients2.google.com | GOOGLE | US | whitelisted |
5556 | chrome.exe | 142.250.102.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5556 | chrome.exe | 168.235.193.212:443 | pkg.office123456.com | — | US | whitelisted |
6128 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
pkg.office123456.com |
| unknown |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
BKUt.exe | CheckRegSZValue false - |
BKUt.exe | Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf\UserChoice |
BKUt.exe | |
BKUt.exe | CheckRegSZValue false - |
BKUt.exe | Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf\UserChoice |
BKUt.exe | |
BKUt.exe | CheckRegSZValue false - |
BKUt.exe | Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf\UserChoice |
BKUt.exe | |
BKUt.exe | CheckRegSZValue false - |