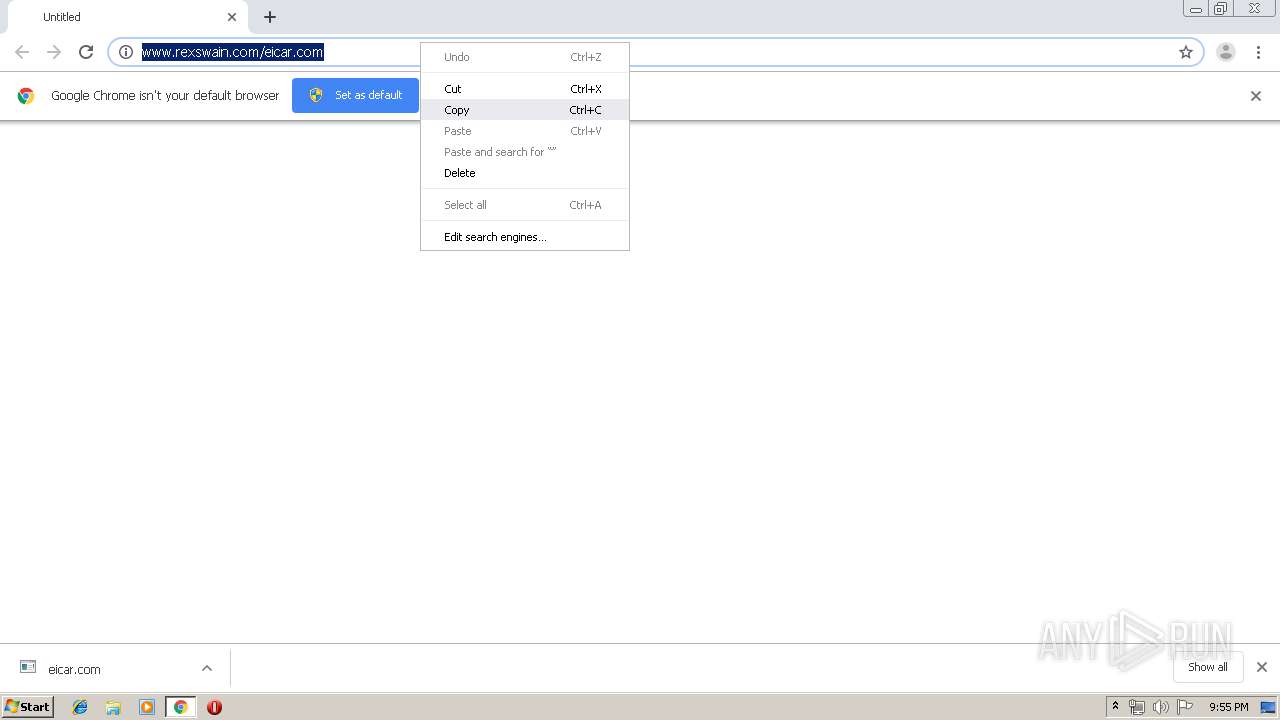
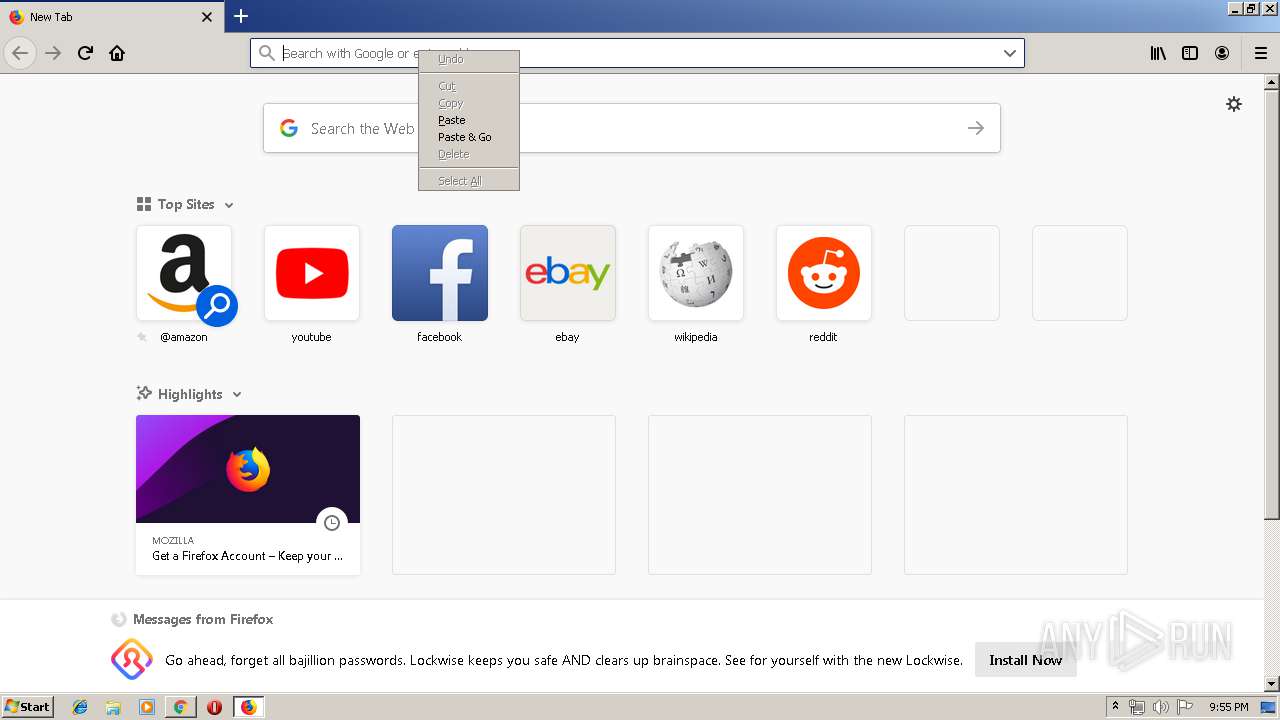
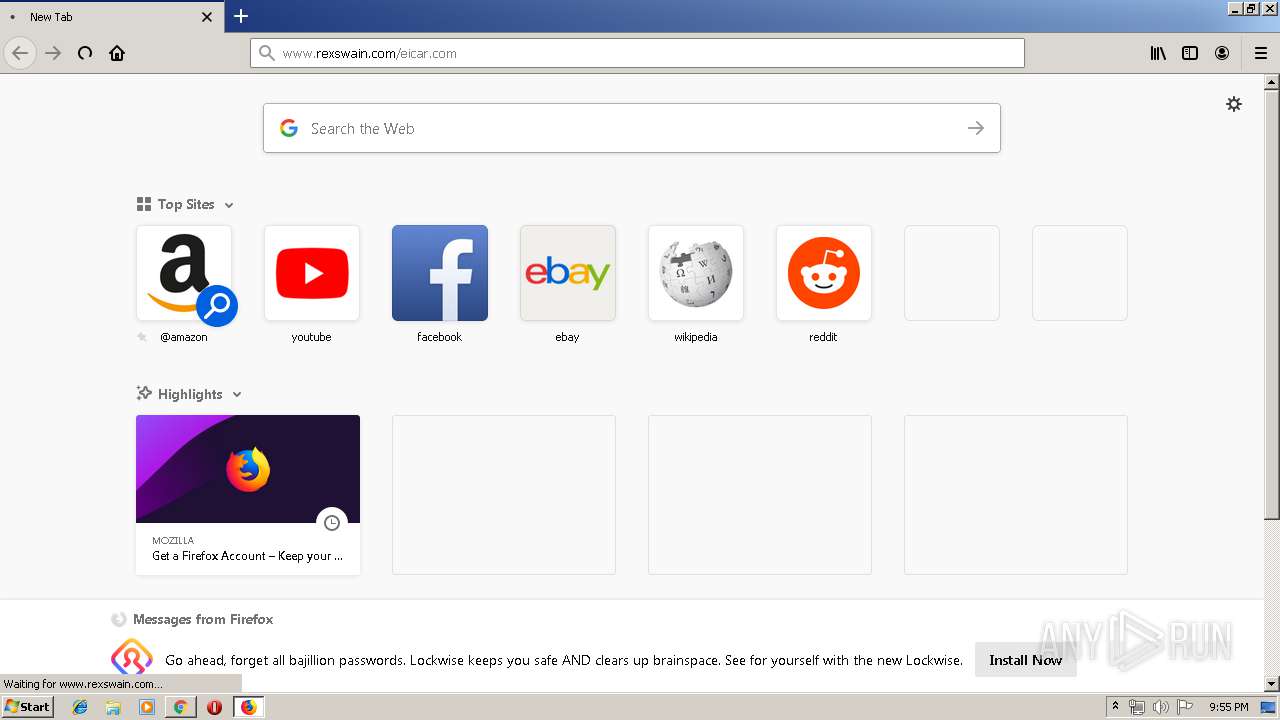
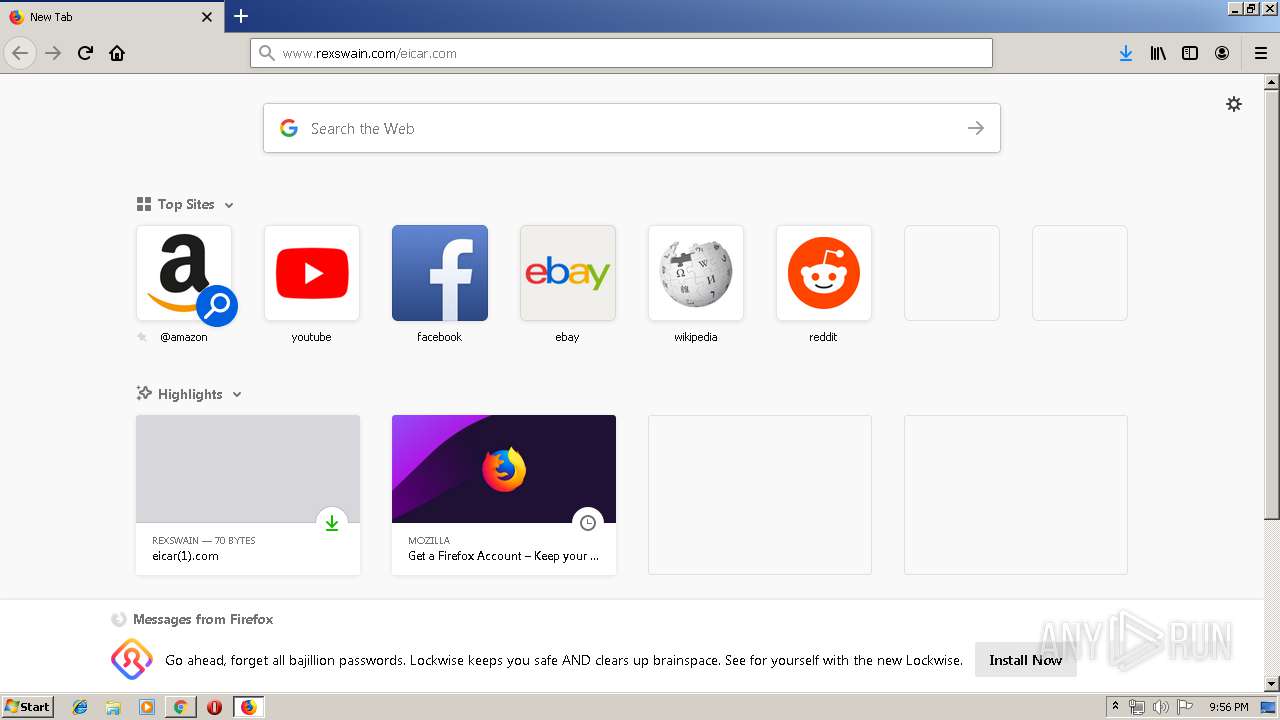
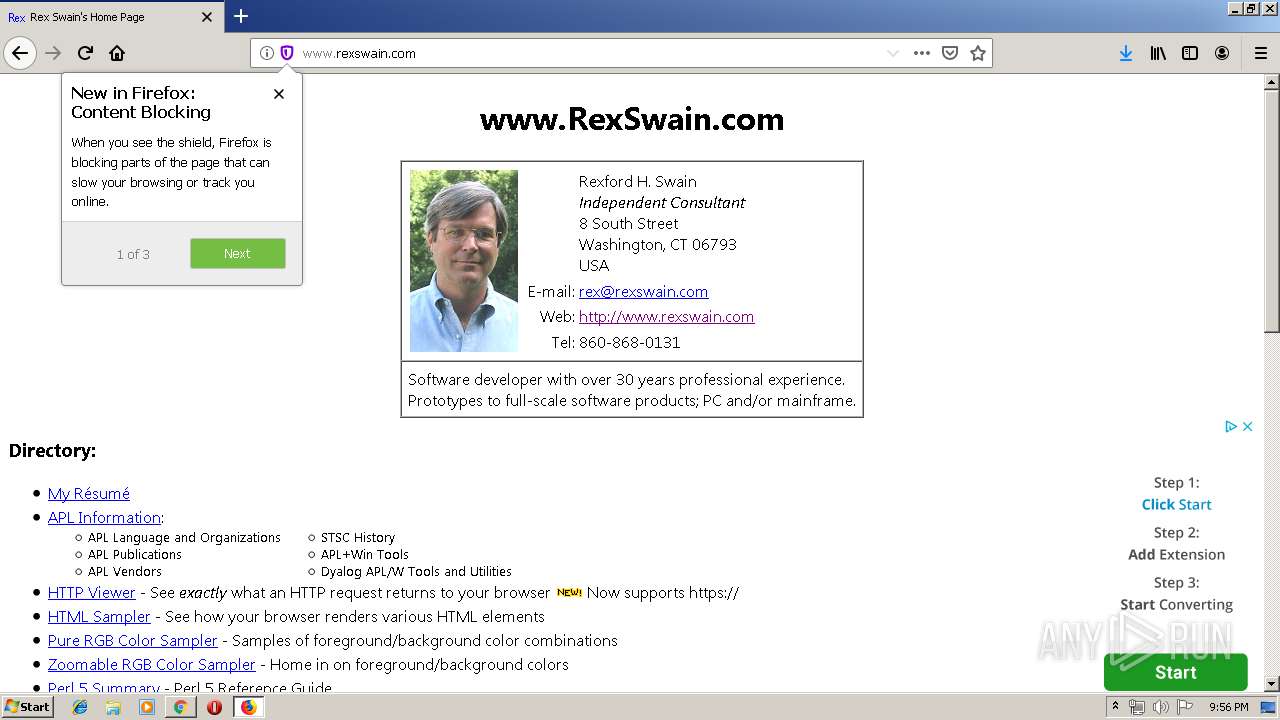
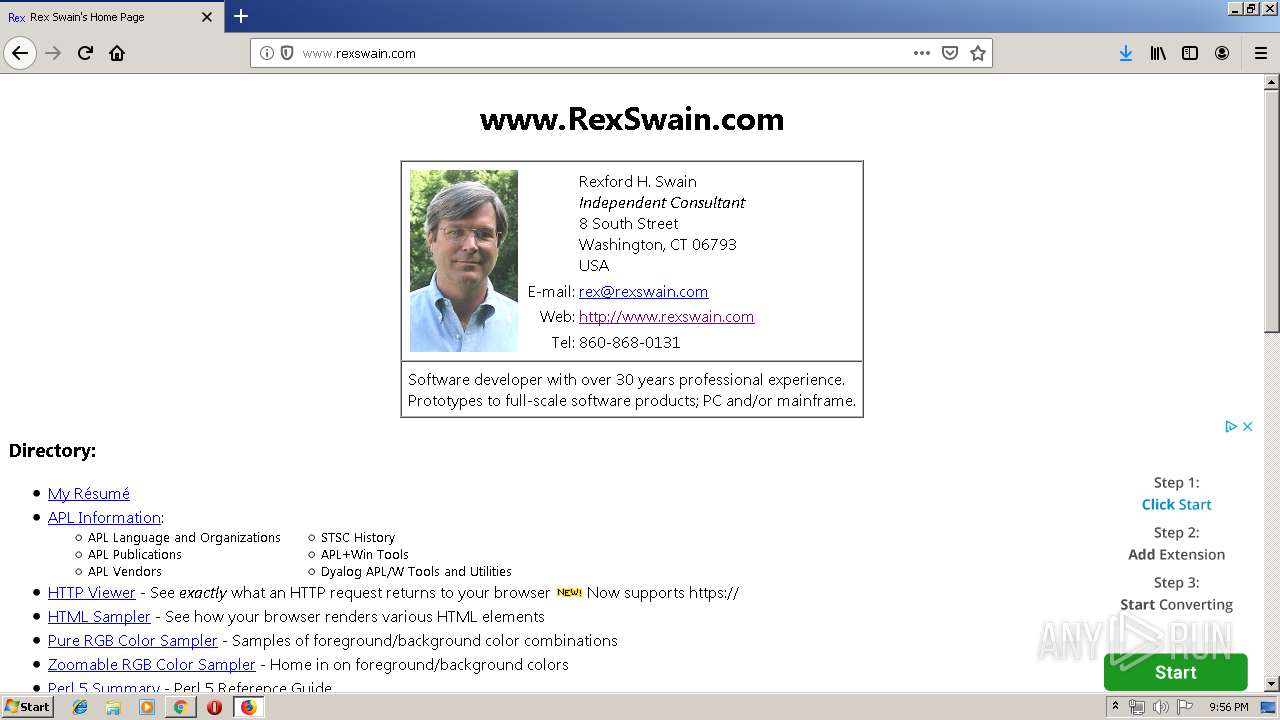
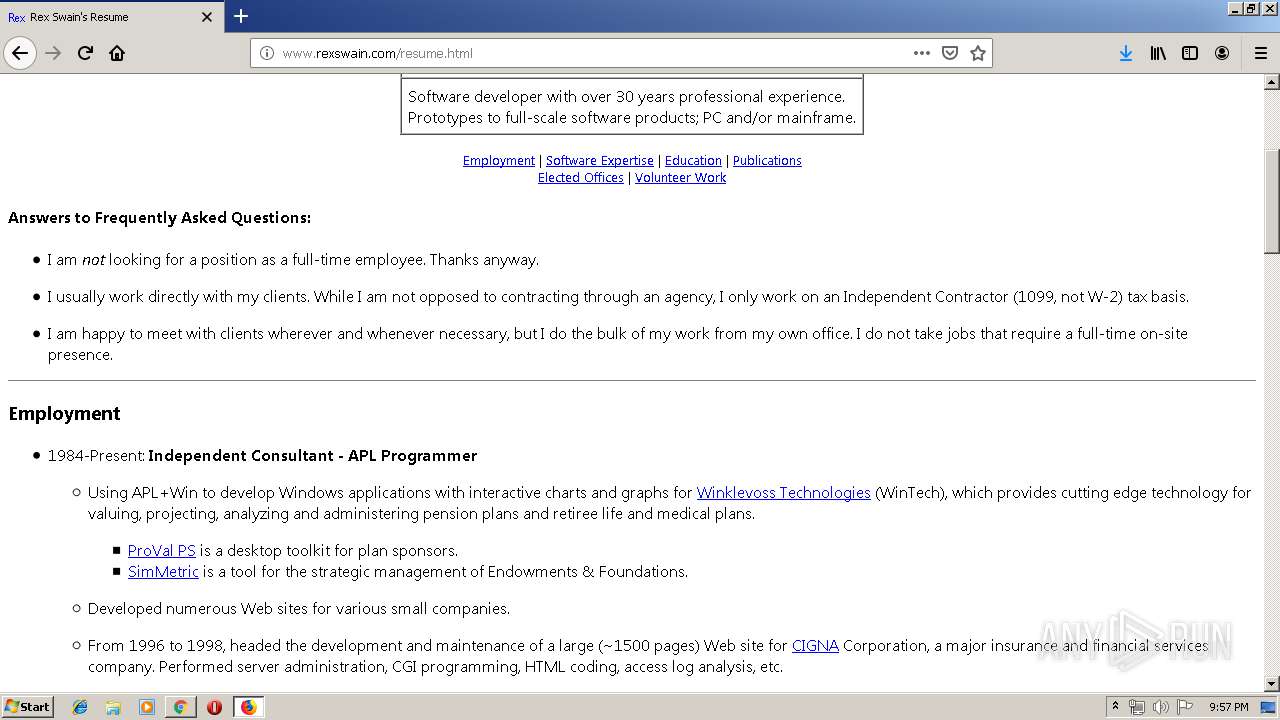
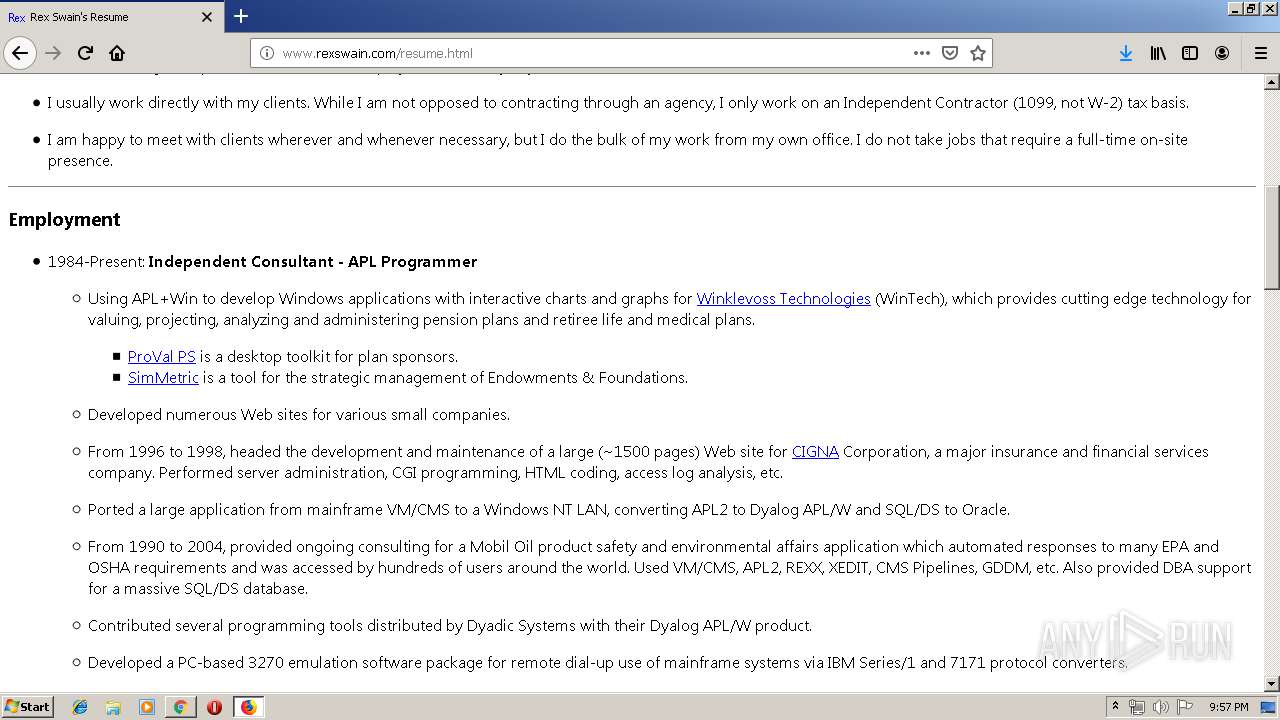
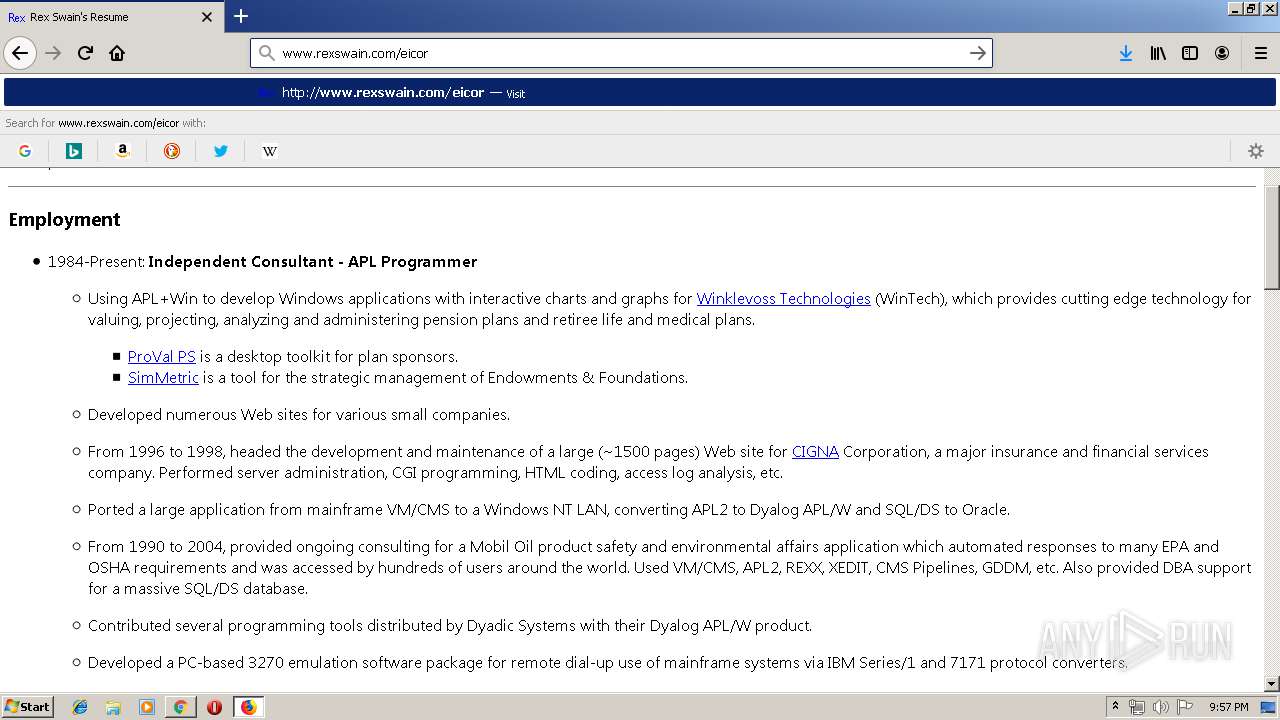
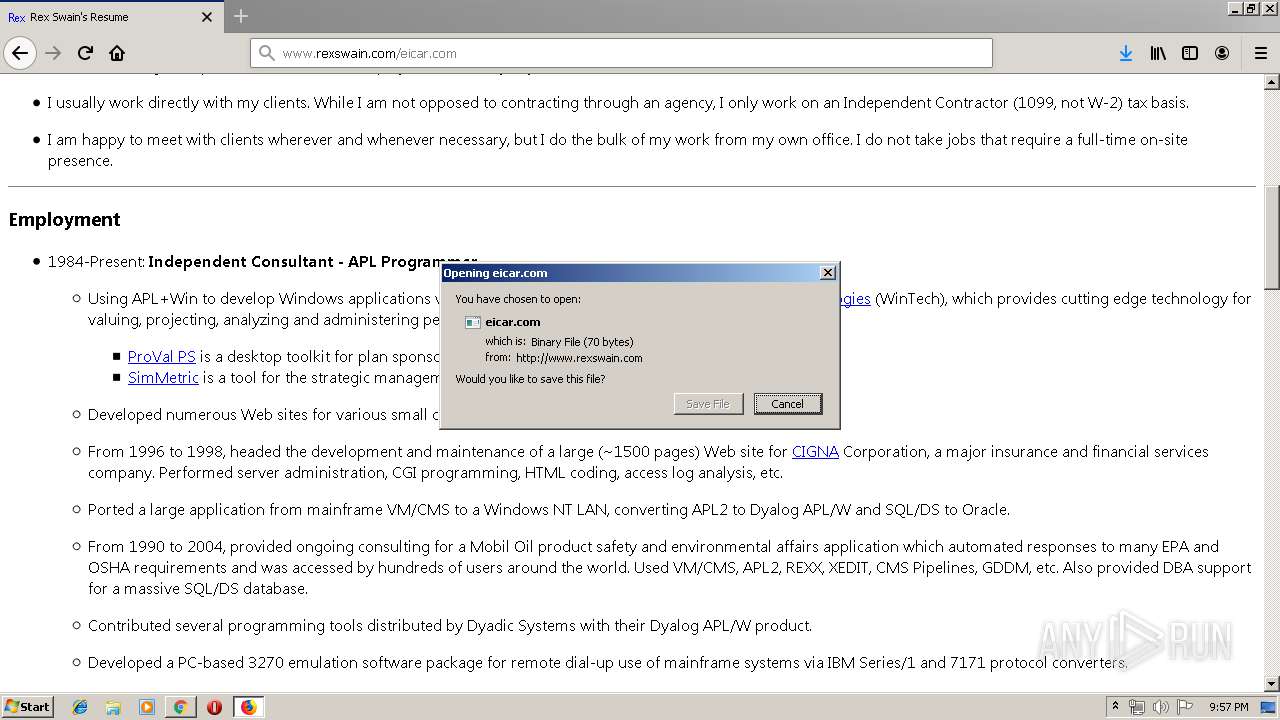
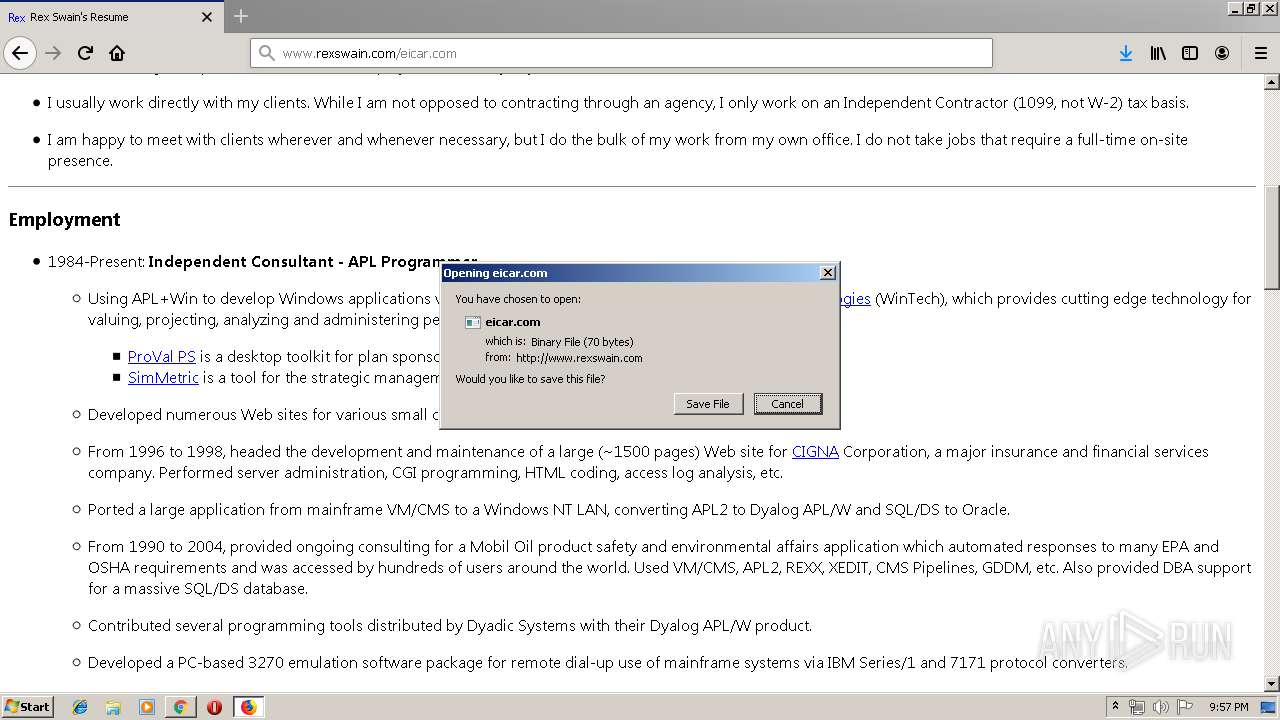
| URL: | http://www.rexswain.com/eicar.com |
| Full analysis: | https://app.any.run/tasks/a1a59616-9b2b-4704-b3a5-a2b8e6c6b7f8 |
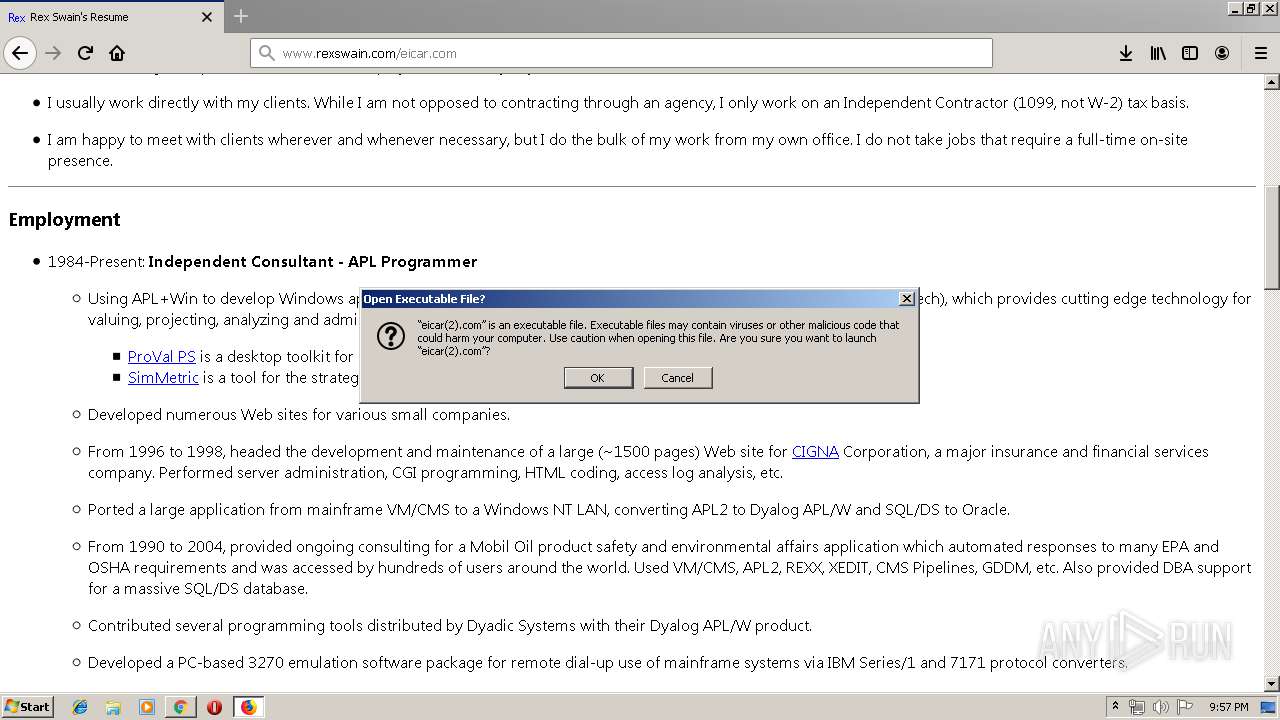
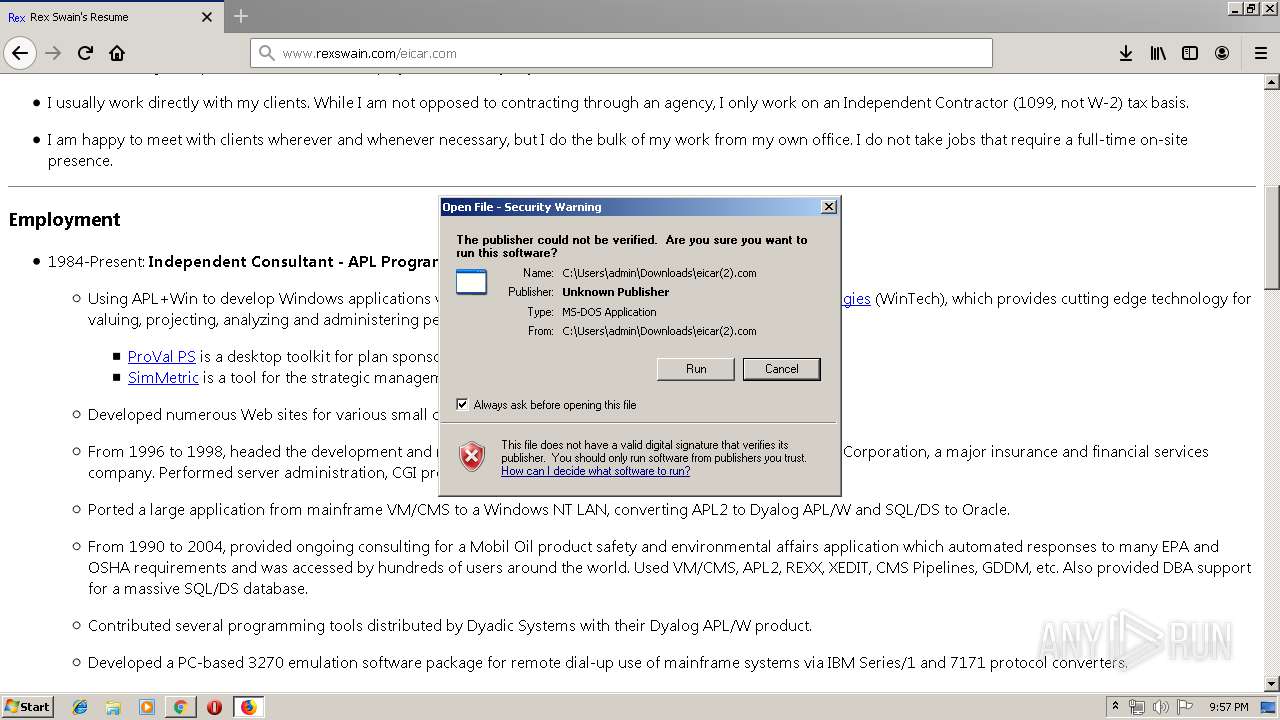
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 20:54:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 47882C9B45098FBCA4D1FF0A4A5CD6B7 |
| SHA1: | C35CF13AD5208D518A05FF2995E61E32C615CEE4 |
| SHA256: | 9CC52E067E5F52009B30B96D7F7E3DDF00CB634E25D3A44D9FFA13D5CB94F58E |
| SSDEEP: | 3:N1KJS4QLRyKweZI:Cc4QL0KweZI |
MALICIOUS
No malicious indicators.SUSPICIOUS
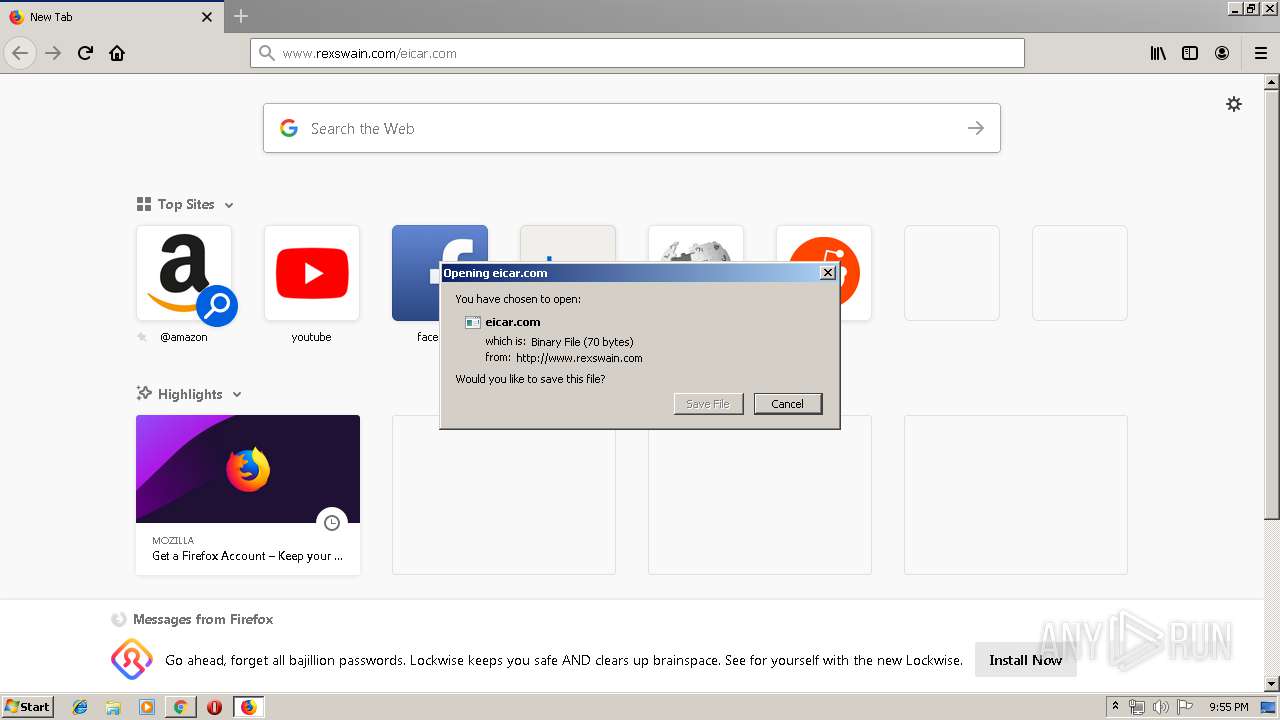
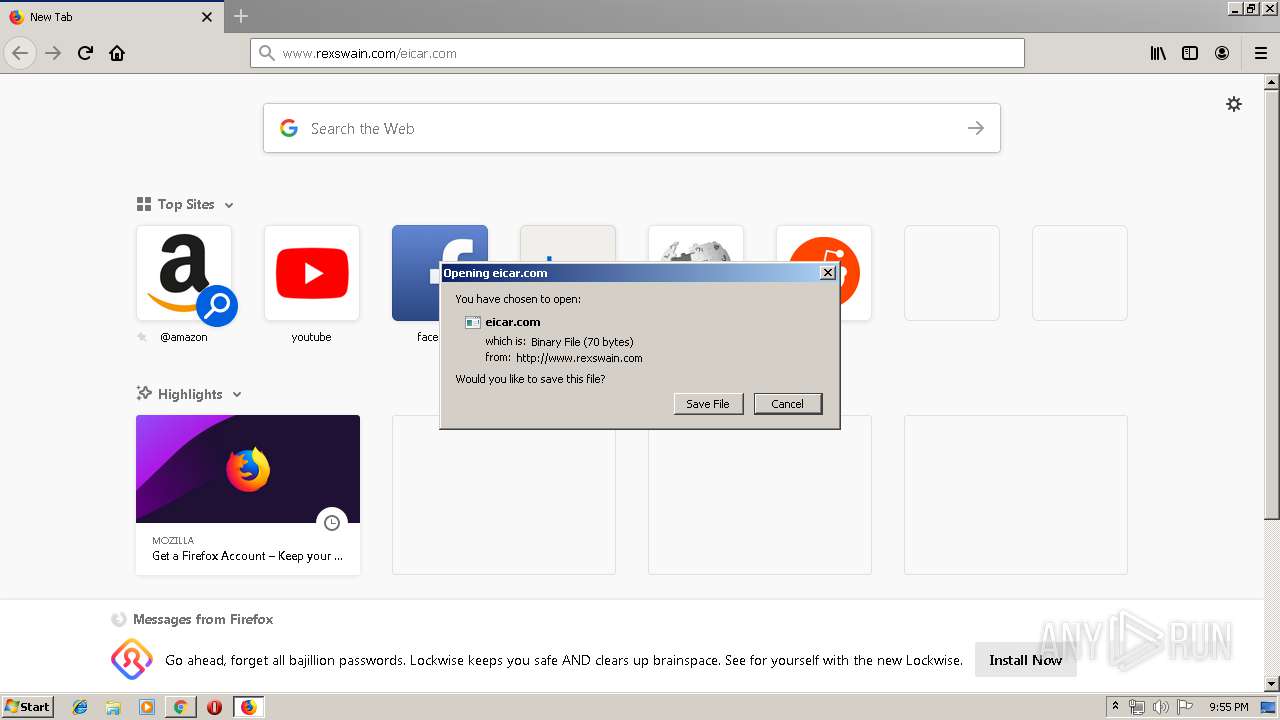
Executable content was dropped or overwritten
- firefox.exe (PID: 1176)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1568)
Executes application which crashes
- firefox.exe (PID: 1176)
INFO
Application launched itself
- chrome.exe (PID: 1568)
- firefox.exe (PID: 2620)
- firefox.exe (PID: 1176)
Reads Internet Cache Settings
- chrome.exe (PID: 1568)
Manual execution by user
- firefox.exe (PID: 2620)
Reads CPU info
- firefox.exe (PID: 1176)
Creates files in the user directory
- firefox.exe (PID: 1176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,1582926331875655820,8594875852970815209,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10327201611035406208 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3960 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,1582926331875655820,8594875852970815209,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5777494037461602694 --mojo-platform-channel-handle=2084 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,1582926331875655820,8594875852970815209,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4673585730624013961 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1176.13.2093327084\699581910" -childID 2 -isForBrowser -prefsHandle 2720 -prefMapHandle 2724 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1176 "\\.\pipe\gecko-crash-server-pipe.1176" 2740 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,1582926331875655820,8594875852970815209,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5801853484461424183 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.rexswain.com/eicar.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1176.0.1861739972\260044622" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1176 "\\.\pipe\gecko-crash-server-pipe.1176" 1160 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,1582926331875655820,8594875852970815209,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8051315922387840524 --mojo-platform-channel-handle=912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,1582926331875655820,8594875852970815209,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13780293067142435642 --mojo-platform-channel-handle=880 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 218
Read events
2 130
Write events
84
Delete events
4
Modification events
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1568-13210203296857625 |
Value: 259 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
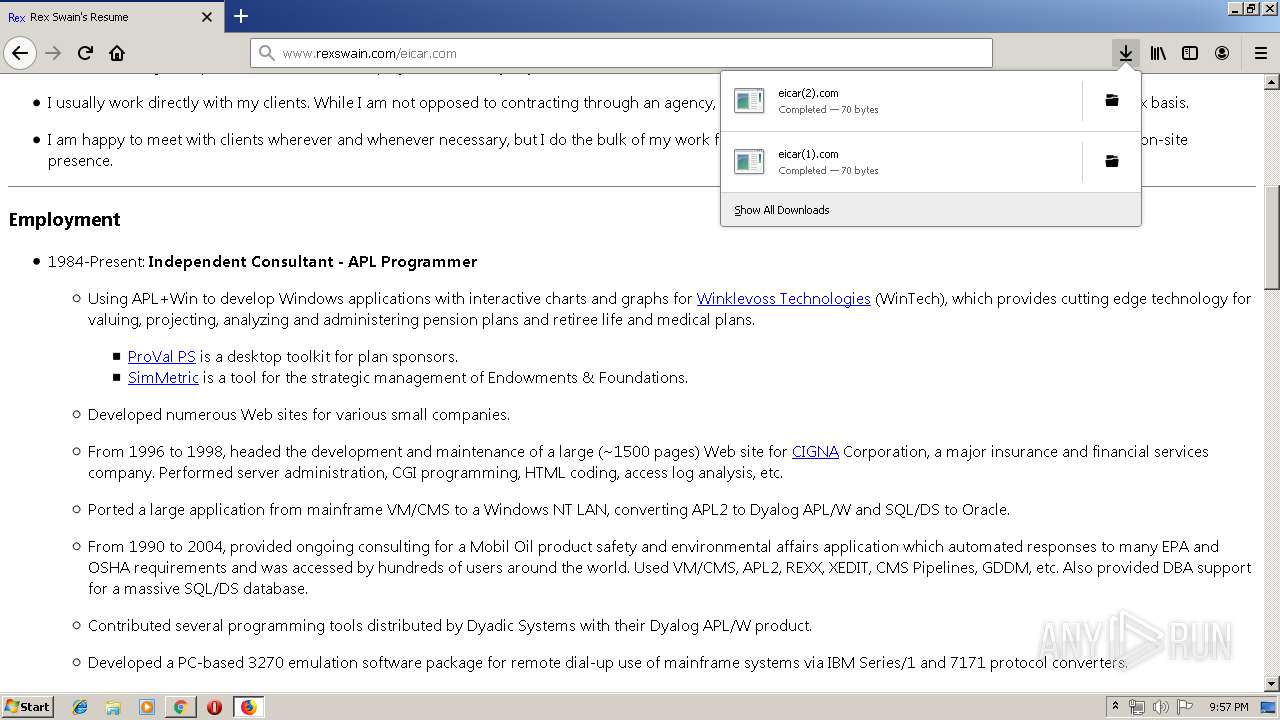
Executable files
2
Suspicious files
107
Text files
225
Unknown types
65
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0ce31cce-b616-4a1d-953f-ed3044309332.tmp | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF378e79.TMP | text | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF378e88.TMP | text | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF378eb7.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
60
DNS requests
144
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
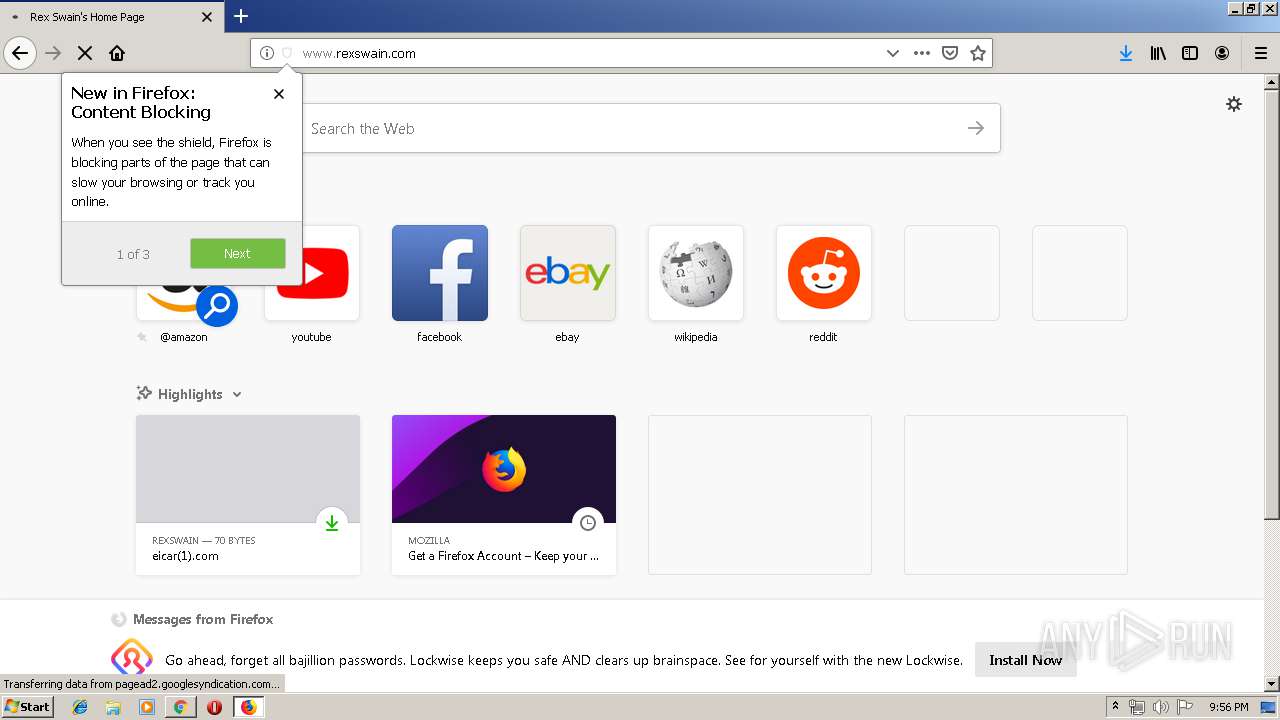
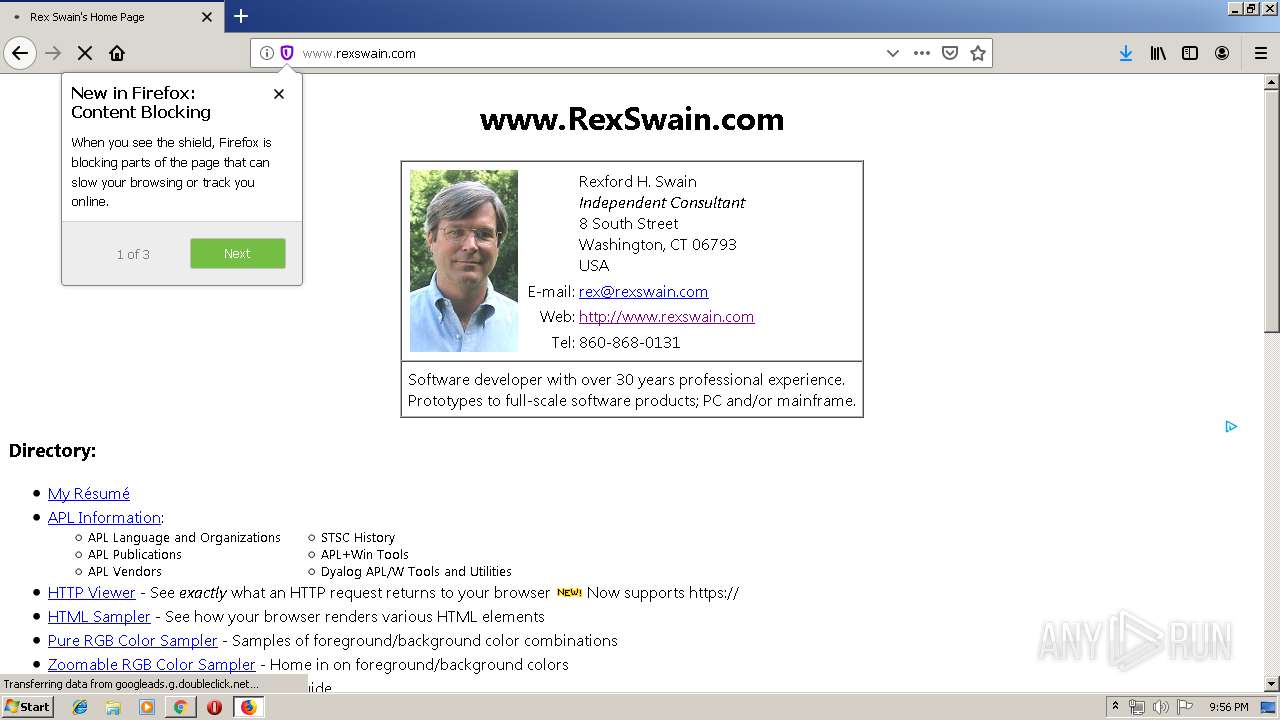
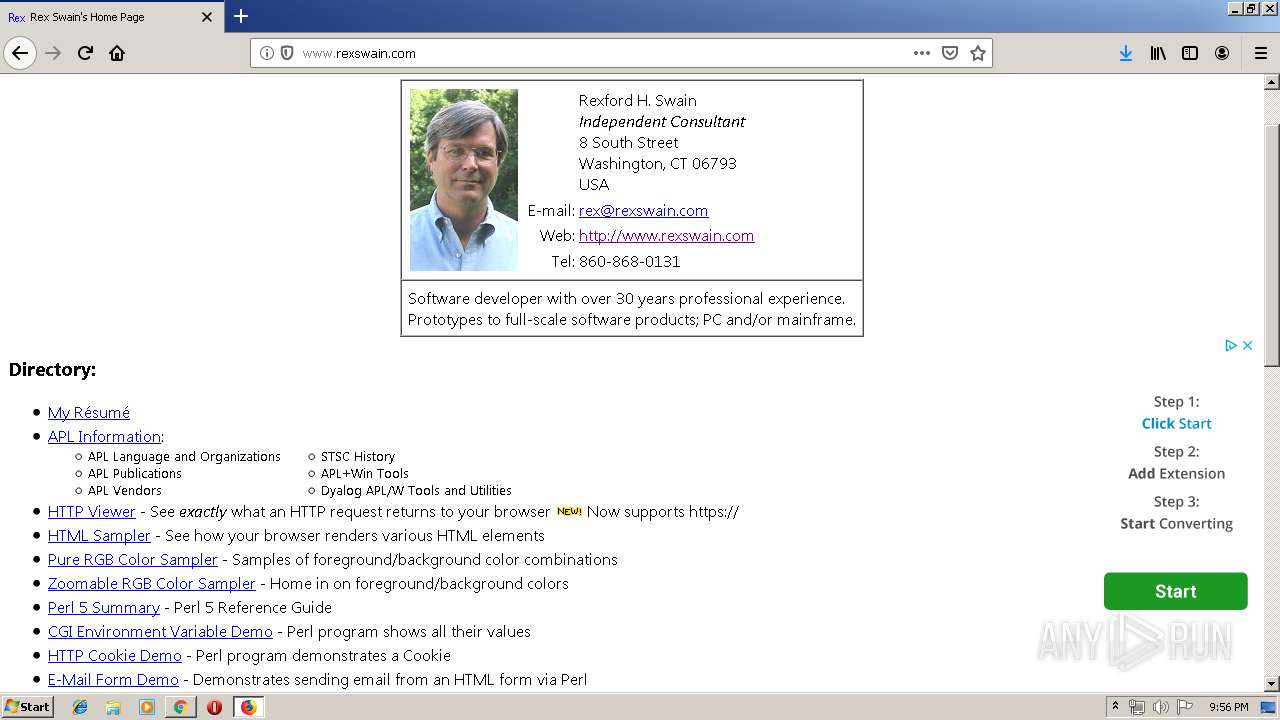
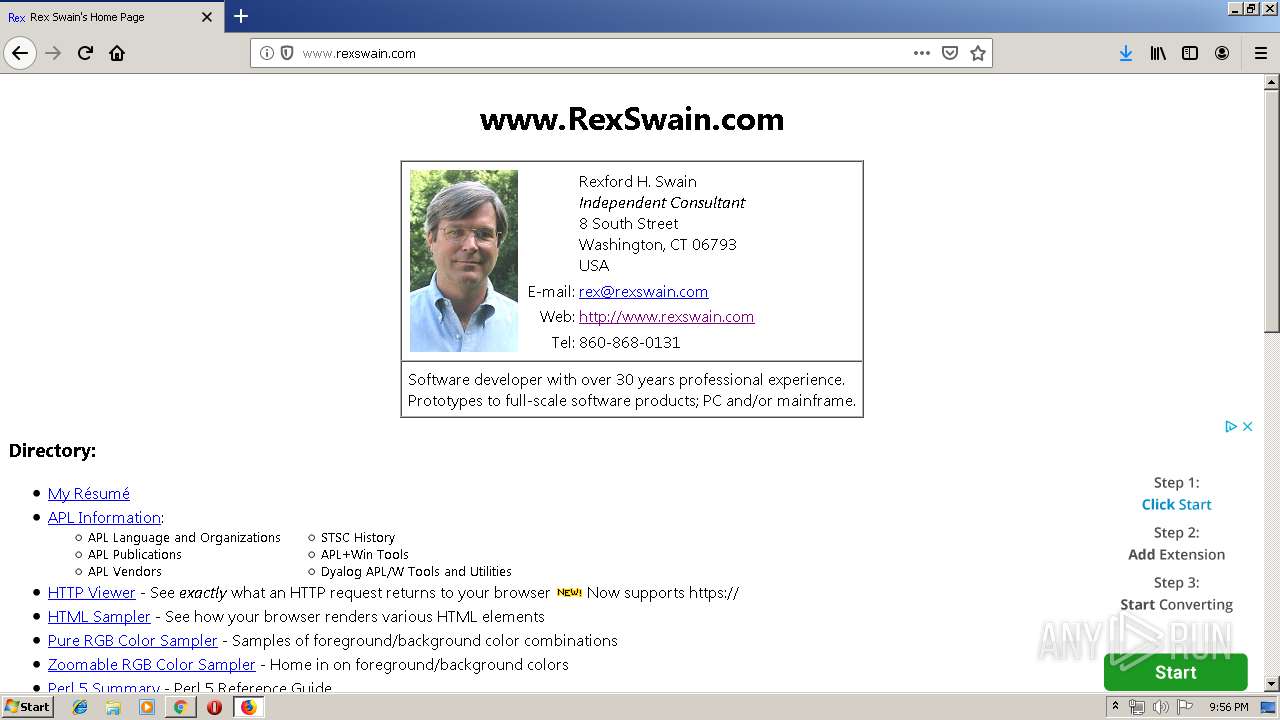
1176 | firefox.exe | GET | 200 | 205.134.250.164:80 | http://www.rexswain.com/normal.css | US | text | 217 b | suspicious |
1176 | firefox.exe | GET | 200 | 205.134.250.164:80 | http://www.rexswain.com/ | US | html | 5.58 Kb | suspicious |
1176 | firefox.exe | GET | 200 | 205.134.250.164:80 | http://www.rexswain.com/cgi-bin/countrex.cgi?index | US | image | 1.84 Kb | suspicious |
1176 | firefox.exe | POST | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
1176 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1176 | firefox.exe | POST | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
1176 | firefox.exe | GET | 200 | 205.134.250.164:80 | http://www.rexswain.com/rexc03.gif | US | image | 17.4 Kb | suspicious |
1176 | firefox.exe | POST | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
1176 | firefox.exe | GET | 200 | 216.58.207.66:80 | http://pagead2.googlesyndication.com/pagead/show_ads.js | US | text | 24.6 Kb | whitelisted |
1176 | firefox.exe | POST | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3992 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3992 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
1176 | firefox.exe | 52.43.169.220:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1176 | firefox.exe | 99.86.1.62:443 | snippets.cdn.mozilla.net | AT&T Services, Inc. | US | unknown |
1176 | firefox.exe | 34.208.208.167:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1176 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1176 | firefox.exe | 34.211.97.204:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1176 | firefox.exe | 172.217.16.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1176 | firefox.exe | 172.217.16.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1176 | firefox.exe | 13.35.253.45:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.rexswain.com |
| suspicious |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |