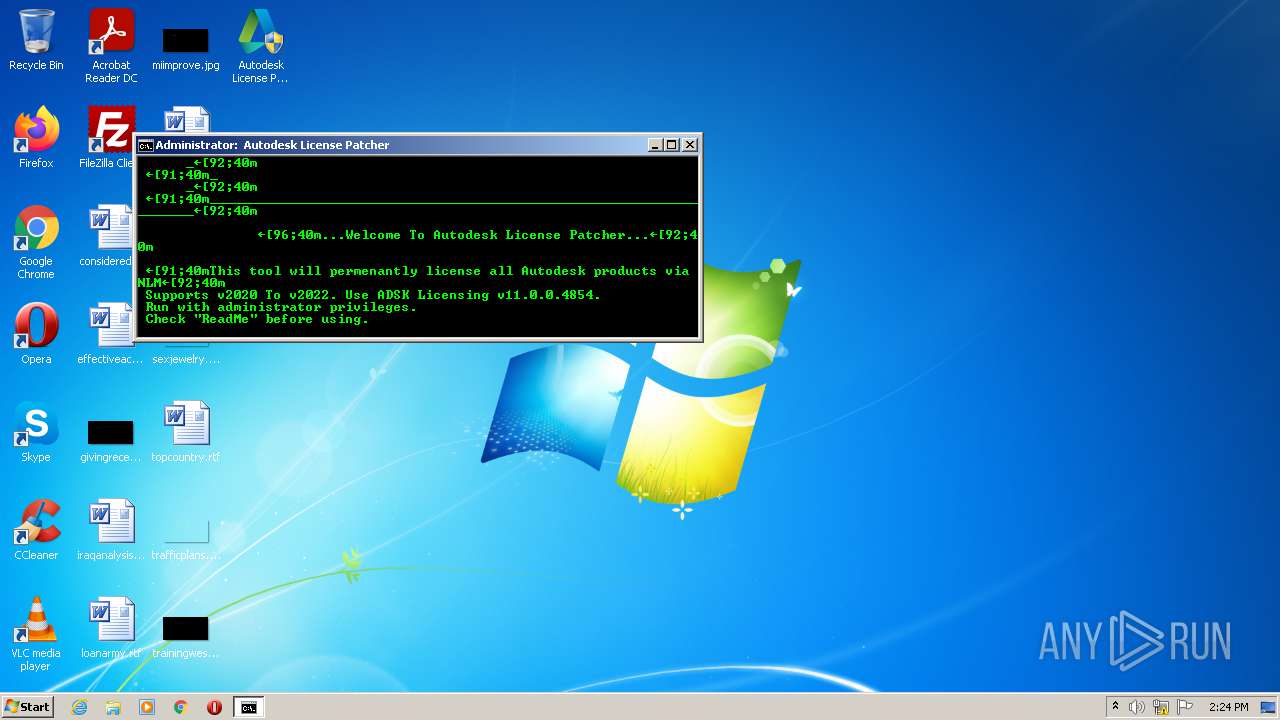
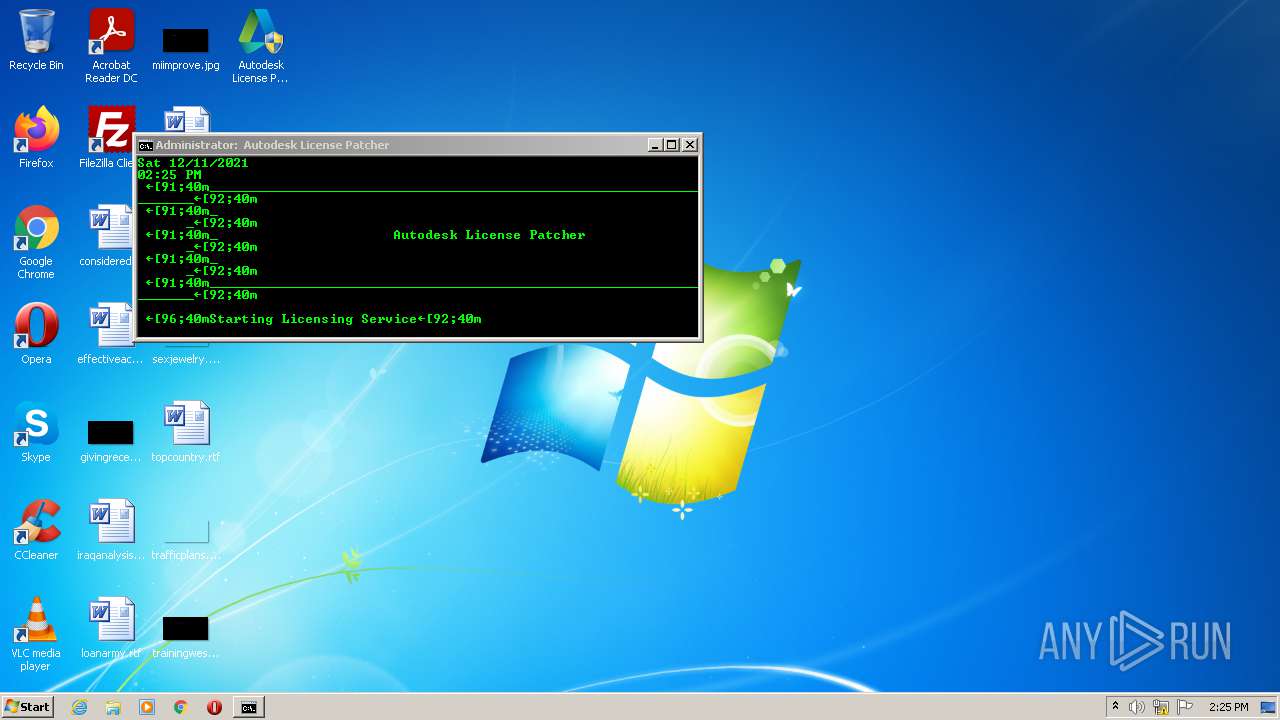
| File name: | Autodesk License Patcher Ultimate Installer.exe |
| Full analysis: | https://app.any.run/tasks/8b3debca-b283-46b4-a090-2e319f2e3d3c |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2021, 14:24:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A88F74305278474AEFA30EC8D89AC91B |
| SHA1: | 2D8FE3CAFB42E3D0264BBA4807345D8E4AA13BA3 |
| SHA256: | 9CBF4A9F365FA6E302CBEEFE79FBB060E3281C1D8266E7485E82E8F78B3B56BC |
| SSDEEP: | 196608:541dQ1VBoyux/oEwfopVuz6o/3MbzF/9sKpHqBjmKcuxEeiv22idXZ:CQ1VBoyuxjA0bzPsxrtEeivNSXZ |
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2380)
- cmd.exe (PID: 3196)
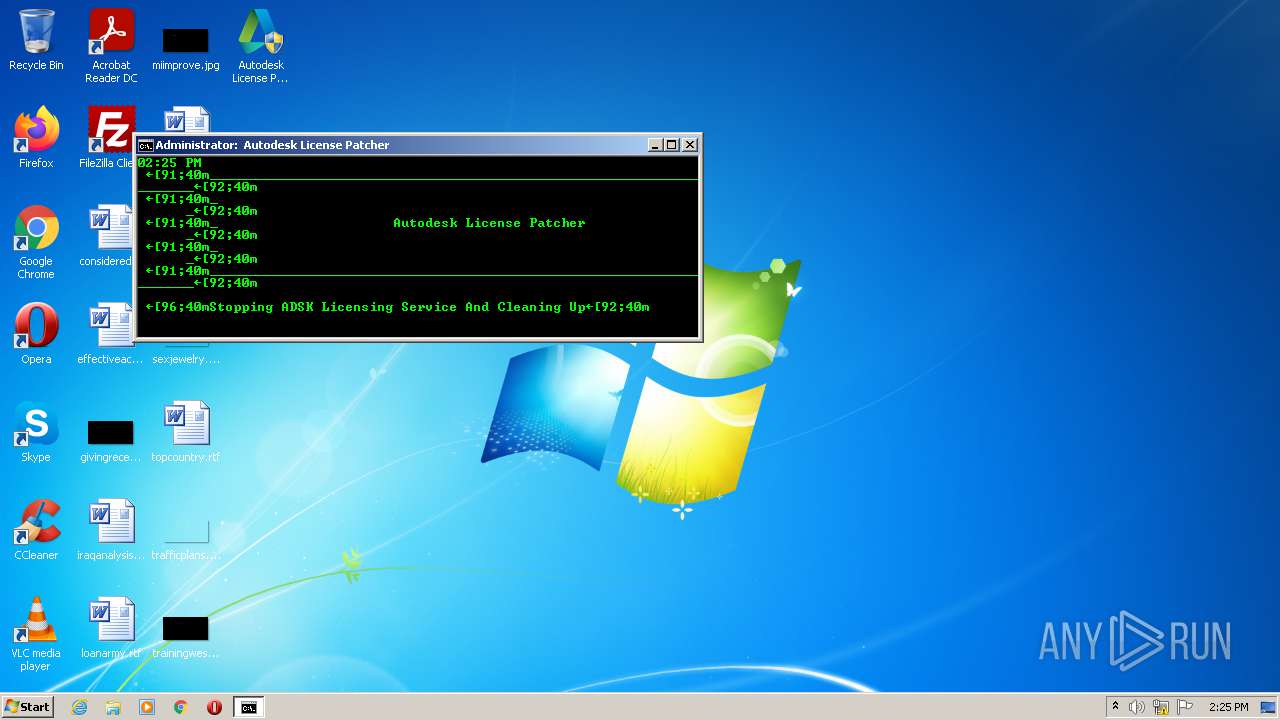
Starts NET.EXE for service management
- cmd.exe (PID: 2380)
- cmd.exe (PID: 3196)
Drops executable file immediately after starts
- Autodesk License Patcher Ultimate Installer.exe (PID: 2708)
- xcopy.exe (PID: 596)
- xcopy.exe (PID: 1008)
- xcopy.exe (PID: 2880)
- xcopy.exe (PID: 2208)
- xcopy.exe (PID: 2364)
Executes PowerShell scripts
- cmd.exe (PID: 2380)
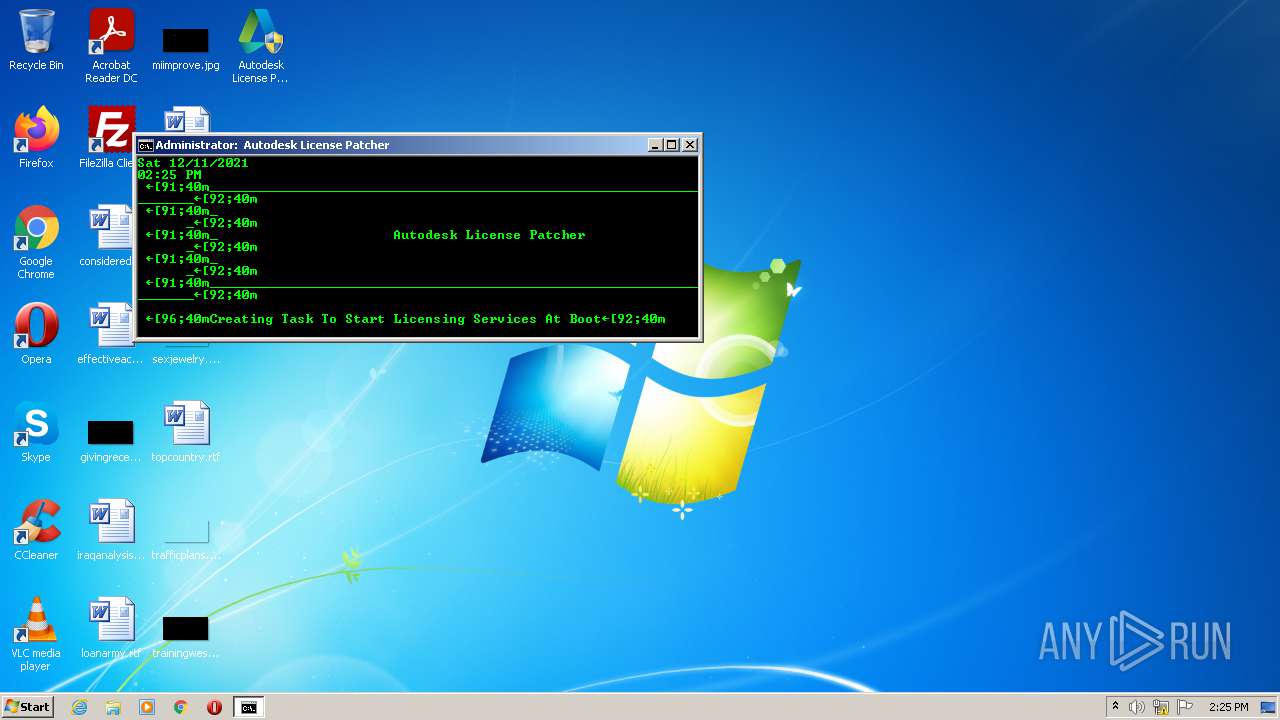
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2676)
- schtasks.exe (PID: 3012)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2380)
SUSPICIOUS
Reads the computer name
- Autodesk License Patcher Ultimate Installer.exe (PID: 2708)
- WMIC.exe (PID: 3884)
- powershell.exe (PID: 3424)
- WMIC.exe (PID: 2596)
- wscript.exe (PID: 2400)
Checks supported languages
- Autodesk License Patcher Ultimate Installer.exe (PID: 2708)
- chcp.com (PID: 3332)
- mode.com (PID: 3232)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 3284)
- cmd.exe (PID: 3876)
- WMIC.exe (PID: 2596)
- cmd.exe (PID: 452)
- WMIC.exe (PID: 3884)
- powershell.exe (PID: 3424)
- mode.com (PID: 1072)
- chcp.com (PID: 3268)
- wscript.exe (PID: 2400)
- cmd.exe (PID: 3196)
Starts application with an unusual extension
- cmd.exe (PID: 2380)
- cmd.exe (PID: 3196)
Starts CMD.EXE for commands execution
- Autodesk License Patcher Ultimate Installer.exe (PID: 2708)
- cmd.exe (PID: 2380)
- wscript.exe (PID: 2400)
Drops a file that was compiled in debug mode
- Autodesk License Patcher Ultimate Installer.exe (PID: 2708)
- xcopy.exe (PID: 596)
- xcopy.exe (PID: 2880)
- xcopy.exe (PID: 2208)
- xcopy.exe (PID: 2364)
Executable content was dropped or overwritten
- Autodesk License Patcher Ultimate Installer.exe (PID: 2708)
- xcopy.exe (PID: 1008)
- xcopy.exe (PID: 596)
- xcopy.exe (PID: 2880)
- xcopy.exe (PID: 2208)
- xcopy.exe (PID: 2364)
Drops a file with too old compile date
- Autodesk License Patcher Ultimate Installer.exe (PID: 2708)
- xcopy.exe (PID: 2880)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2380)
- cmd.exe (PID: 3196)
Executed as Windows Service
- msiexec.exe (PID: 2664)
Application launched itself
- cmd.exe (PID: 2380)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 452)
- cmd.exe (PID: 3876)
Starts SC.EXE for service management
- cmd.exe (PID: 2380)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2380)
Reads Environment values
- netsh.exe (PID: 1984)
- netsh.exe (PID: 2516)
- netsh.exe (PID: 1740)
- netsh.exe (PID: 3816)
- netsh.exe (PID: 3288)
- netsh.exe (PID: 3240)
- netsh.exe (PID: 1172)
- netsh.exe (PID: 3352)
- netsh.exe (PID: 2876)
- netsh.exe (PID: 2304)
- netsh.exe (PID: 3616)
- netsh.exe (PID: 2616)
- netsh.exe (PID: 1484)
- netsh.exe (PID: 3464)
- netsh.exe (PID: 2508)
- netsh.exe (PID: 276)
- netsh.exe (PID: 1808)
- netsh.exe (PID: 2416)
- netsh.exe (PID: 3352)
- netsh.exe (PID: 1444)
- netsh.exe (PID: 3184)
- netsh.exe (PID: 3196)
- netsh.exe (PID: 2720)
- netsh.exe (PID: 2616)
- netsh.exe (PID: 2952)
- netsh.exe (PID: 3288)
- netsh.exe (PID: 3464)
- netsh.exe (PID: 4012)
- netsh.exe (PID: 560)
Executes scripts
- cmd.exe (PID: 2380)
INFO
Checks supported languages
- PING.EXE (PID: 3360)
- PING.EXE (PID: 3672)
- net.exe (PID: 2796)
- net1.exe (PID: 2952)
- taskkill.exe (PID: 1888)
- taskkill.exe (PID: 3604)
- taskkill.exe (PID: 3848)
- taskkill.exe (PID: 2056)
- taskkill.exe (PID: 1132)
- taskkill.exe (PID: 2020)
- taskkill.exe (PID: 2468)
- taskkill.exe (PID: 2920)
- PING.EXE (PID: 3580)
- msiexec.exe (PID: 2664)
- xcopy.exe (PID: 1008)
- xcopy.exe (PID: 596)
- xcopy.exe (PID: 3416)
- xcopy.exe (PID: 1096)
- xcopy.exe (PID: 2780)
- taskkill.exe (PID: 584)
- msiexec.exe (PID: 3248)
- xcopy.exe (PID: 2208)
- PING.EXE (PID: 2796)
- xcopy.exe (PID: 2364)
- xcopy.exe (PID: 2880)
- PING.EXE (PID: 2880)
- HOSTNAME.EXE (PID: 3508)
- schtasks.exe (PID: 3012)
- PING.EXE (PID: 3688)
- sc.exe (PID: 3328)
- schtasks.exe (PID: 2676)
- netsh.exe (PID: 1984)
- netsh.exe (PID: 2516)
- netsh.exe (PID: 1740)
- netsh.exe (PID: 3816)
- netsh.exe (PID: 3240)
- netsh.exe (PID: 3352)
- netsh.exe (PID: 2876)
- netsh.exe (PID: 3288)
- netsh.exe (PID: 1172)
- netsh.exe (PID: 3464)
- netsh.exe (PID: 3616)
- netsh.exe (PID: 2508)
- netsh.exe (PID: 2616)
- netsh.exe (PID: 2304)
- netsh.exe (PID: 1484)
- netsh.exe (PID: 276)
- netsh.exe (PID: 1808)
- netsh.exe (PID: 2416)
- netsh.exe (PID: 3184)
- netsh.exe (PID: 3352)
- netsh.exe (PID: 1444)
- netsh.exe (PID: 3288)
- netsh.exe (PID: 2720)
- netsh.exe (PID: 3196)
- netsh.exe (PID: 2616)
- netsh.exe (PID: 4012)
- netsh.exe (PID: 2952)
- netsh.exe (PID: 3464)
- PING.EXE (PID: 3232)
- net.exe (PID: 1312)
- net1.exe (PID: 3688)
- PING.EXE (PID: 3828)
- netsh.exe (PID: 560)
- PING.EXE (PID: 3340)
- PING.EXE (PID: 2696)
- taskkill.exe (PID: 1092)
- taskkill.exe (PID: 3420)
- taskkill.exe (PID: 2520)
- taskkill.exe (PID: 336)
- taskkill.exe (PID: 3524)
- taskkill.exe (PID: 3376)
- net.exe (PID: 1492)
- net1.exe (PID: 4044)
- taskkill.exe (PID: 3468)
- taskkill.exe (PID: 2312)
- net.exe (PID: 4044)
- taskkill.exe (PID: 3456)
- net1.exe (PID: 3840)
Reads the computer name
- PING.EXE (PID: 3360)
- net1.exe (PID: 2952)
- PING.EXE (PID: 3672)
- taskkill.exe (PID: 3604)
- taskkill.exe (PID: 1888)
- taskkill.exe (PID: 3848)
- taskkill.exe (PID: 2468)
- taskkill.exe (PID: 2056)
- taskkill.exe (PID: 1132)
- taskkill.exe (PID: 2020)
- taskkill.exe (PID: 2920)
- msiexec.exe (PID: 3248)
- msiexec.exe (PID: 2664)
- PING.EXE (PID: 3580)
- taskkill.exe (PID: 584)
- PING.EXE (PID: 2796)
- PING.EXE (PID: 2880)
- HOSTNAME.EXE (PID: 3508)
- schtasks.exe (PID: 2676)
- schtasks.exe (PID: 3012)
- sc.exe (PID: 3328)
- PING.EXE (PID: 3688)
- netsh.exe (PID: 1984)
- netsh.exe (PID: 2516)
- netsh.exe (PID: 1740)
- netsh.exe (PID: 3288)
- netsh.exe (PID: 3240)
- netsh.exe (PID: 1172)
- netsh.exe (PID: 3816)
- netsh.exe (PID: 3352)
- netsh.exe (PID: 2876)
- netsh.exe (PID: 2304)
- netsh.exe (PID: 1484)
- netsh.exe (PID: 3464)
- netsh.exe (PID: 2508)
- netsh.exe (PID: 3616)
- netsh.exe (PID: 2616)
- netsh.exe (PID: 276)
- netsh.exe (PID: 1808)
- netsh.exe (PID: 2416)
- netsh.exe (PID: 3184)
- netsh.exe (PID: 1444)
- netsh.exe (PID: 3196)
- netsh.exe (PID: 3288)
- netsh.exe (PID: 2720)
- netsh.exe (PID: 3352)
- netsh.exe (PID: 2952)
- netsh.exe (PID: 2616)
- netsh.exe (PID: 560)
- PING.EXE (PID: 3232)
- net1.exe (PID: 3688)
- PING.EXE (PID: 3828)
- netsh.exe (PID: 4012)
- netsh.exe (PID: 3464)
- PING.EXE (PID: 2696)
- PING.EXE (PID: 3340)
- taskkill.exe (PID: 1092)
- taskkill.exe (PID: 3420)
- taskkill.exe (PID: 2520)
- taskkill.exe (PID: 3524)
- taskkill.exe (PID: 3376)
- net1.exe (PID: 4044)
- taskkill.exe (PID: 3468)
- taskkill.exe (PID: 336)
- taskkill.exe (PID: 2312)
- net1.exe (PID: 3840)
- taskkill.exe (PID: 3456)
Checks Windows Trust Settings
- powershell.exe (PID: 3424)
- wscript.exe (PID: 2400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:12:01 19:00:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201216 |
| InitializedDataSize: | 334848 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ec40 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Dec-2020 18:00:55 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 01-Dec-2020 18:00:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000310EA | 0x00031200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70808 |
.rdata | 0x00033000 | 0x0000A612 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22174 |
.data | 0x0003E000 | 0x00023728 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70882 |
.didat | 0x00062000 | 0x00000188 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29825 |
.rsrc | 0x00063000 | 0x00043CE0 | 0x00043E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.0129 |
.reloc | 0x000A7000 | 0x00002268 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55486 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26192 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.79487 | 1640 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 4.31213 | 744 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 4.72758 | 488 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 4.13528 | 296 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 4.94754 | 5672 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.11236 | 440 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
134
Monitored processes
94
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | netsh advfirewall firewall add rule name="AutodeskNLM" dir=out action=block profile=any program="\Autodesk Shared\AdskLicensing\Current\AdskLicensingAnalyticsClient\ADPClientService.exe" | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 336 | taskkill /F /IM "lmgrd.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 452 | C:\Windows\system32\cmd.exe /c wmic path Win32_NetworkAdapter where "PNPDeviceID like '%%PCI%%' AND AdapterTypeID='0'" get MacAddress,AdapterType | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 560 | netsh advfirewall firewall add rule name="AutodeskNLM" dir=out action=block profile=any program="\Autodesk Shared\Network License Manager\adskflex.exe" | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | taskkill /F /IM "lmtools.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 596 | xcopy "C:\AutodeskLicensePatcherInstaller\Files\NetworkLicenseManager\lmgrd.exe" "\Autodesk Shared\Network License Manager\" /Y /K /R /S /H /i | C:\Windows\system32\xcopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | xcopy "C:\AutodeskLicensePatcherInstaller\Files\NetworkLicenseManager\adskflex.exe" "\Autodesk Shared\Network License Manager\" /Y /K /R /S /H /i | C:\Windows\system32\xcopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | mode con: cols=70 lines=12 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | taskkill /F /IM "AdskLicensingAgent.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1096 | xcopy "C:\AutodeskLicensePatcherInstaller\Files\Service\Service.vbs" "\Autodesk Shared\Network License Manager\" /Y /K /R /S /H /i | C:\Windows\system32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
18 418
Read events
17 052
Write events
1 366
Delete events
0
Modification events
| (PID) Process: | (2708) Autodesk License Patcher Ultimate Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2708) Autodesk License Patcher Ultimate Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2708) Autodesk License Patcher Ultimate Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2708) Autodesk License Patcher Ultimate Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1984) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1984) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (1984) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (1984) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (1984) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (1984) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
Executable files
10
Suspicious files
2
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2708 | Autodesk License Patcher Ultimate Installer.exe | C:\AutodeskLicensePatcherInstaller\Files\NetworkLicenseManager\License.lic | text | |
MD5:201904E1798C04199B989D5D2679AF89 | SHA256:8C7EA9DF994FA92CF57DC2F624D3994901136520358960686128B6C27A39315D | |||
| 2708 | Autodesk License Patcher Ultimate Installer.exe | C:\AutodeskLicensePatcherInstaller\Files\PatchedFiles\AdskLicensingService.exe | executable | |
MD5:1B65133C259C89CC85374AAA37024A18 | SHA256:ADFB17162C1D1AFBEFBA639FDC0F9EE1A3FF93C728340F523FEEBBA156404404 | |||
| 2708 | Autodesk License Patcher Ultimate Installer.exe | C:\AutodeskLicensePatcherInstaller\Files\Service\Service.vbs | text | |
MD5:C578D9653B22800C3EB6B6A51219BBB8 | SHA256:20A98A7E6E137BB1B9BD5EF6911A479CB8EAC925B80D6DB4E70B19F62A40CCE2 | |||
| 2708 | Autodesk License Patcher Ultimate Installer.exe | C:\AutodeskLicensePatcherInstaller\Files\Service\Service.bat | text | |
MD5:BBE4DBEFCD6B3C7B5A120DD6D81AEDA1 | SHA256:78A08760D027EBF71756C5D906F849AC4C46FADD2EC713AB709FD289CEE447D9 | |||
| 2708 | Autodesk License Patcher Ultimate Installer.exe | C:\AutodeskLicensePatcherInstaller\Files\PatchedFiles\adlmint.dll | executable | |
MD5:B940DEA1BD3482983F696150F9D42CFA | SHA256:79308CEA626BF674AFEB3423EFD61EC2ADD6D6930AFECF19A32FA0EA4FE3EE37 | |||
| 2708 | Autodesk License Patcher Ultimate Installer.exe | C:\AutodeskLicensePatcherInstaller\Files\NetworkLicenseManager\adskflex.exe | executable | |
MD5:6BEFBECBECB1B7448DB57BC6E4682266 | SHA256:9798BF79AC945F3B7A53063E9F0D00D4A3D43C65ADDDBC853A3C3DE7534785F5 | |||
| 596 | xcopy.exe | C:\Autodesk Shared\Network License Manager\lmgrd.exe | executable | |
MD5:2B62942AC6D4BDF9233BB1D8DBCA59D9 | SHA256:C2EFADF435920E9CD4B02763D6DD430E342112185890239307D65814FF723AB9 | |||
| 1008 | xcopy.exe | C:\Autodesk Shared\Network License Manager\adskflex.exe | executable | |
MD5:6BEFBECBECB1B7448DB57BC6E4682266 | SHA256:9798BF79AC945F3B7A53063E9F0D00D4A3D43C65ADDDBC853A3C3DE7534785F5 | |||
| 3416 | xcopy.exe | C:\Autodesk Shared\Network License Manager\License.lic | text | |
MD5:201904E1798C04199B989D5D2679AF89 | SHA256:8C7EA9DF994FA92CF57DC2F624D3994901136520358960686128B6C27A39315D | |||
| 2880 | xcopy.exe | C:\Autodesk Shared\AdskLicensing\11.0.0.4854\AdskLicensingService\AdskLicensingService.exe | executable | |
MD5:1B65133C259C89CC85374AAA37024A18 | SHA256:ADFB17162C1D1AFBEFBA639FDC0F9EE1A3FF93C728340F523FEEBBA156404404 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report