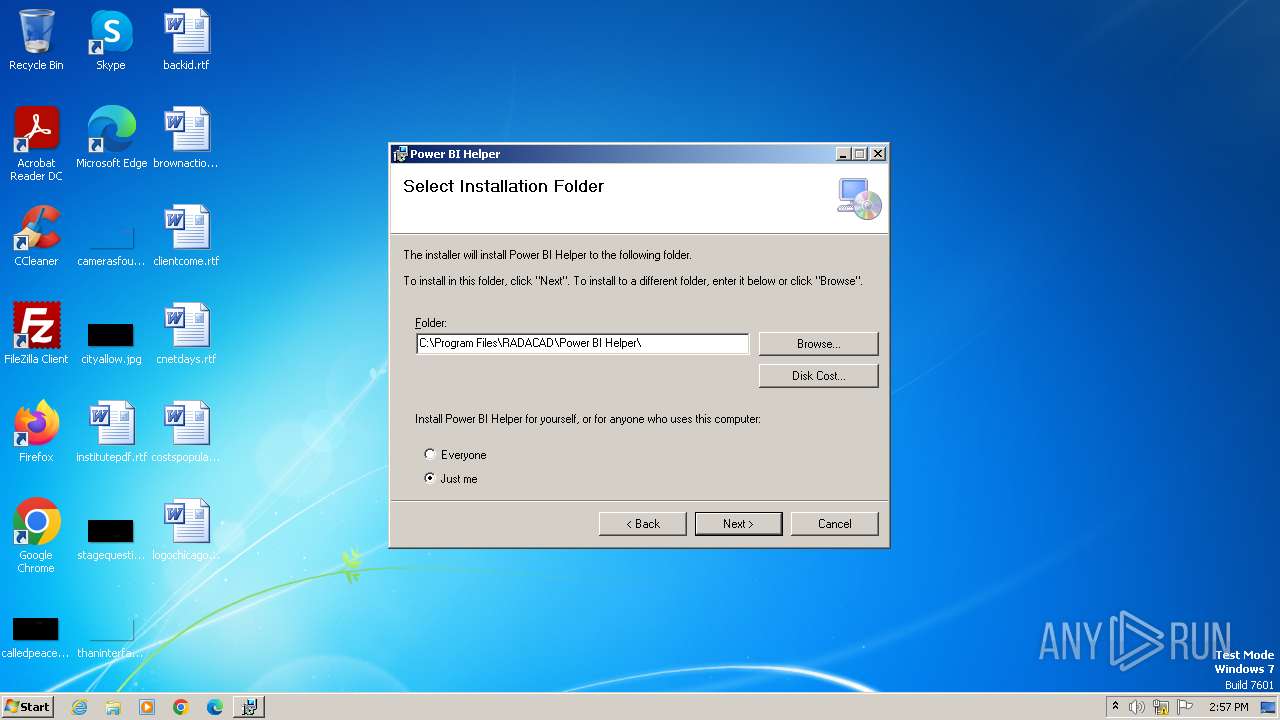
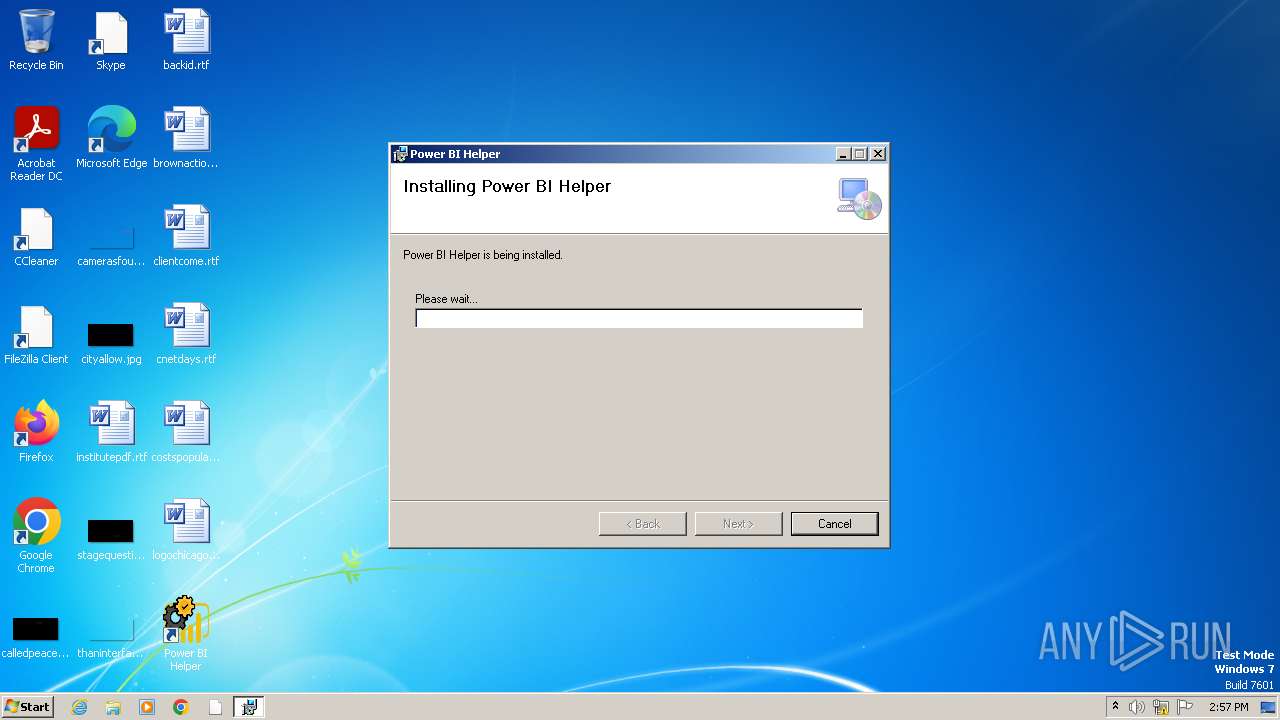
| File name: | Setup_Power_BI_Helperv12.3.msi |
| Full analysis: | https://app.any.run/tasks/58108e9e-aa71-4f71-a413-a07428b8e971 |
| Verdict: | Malicious activity |
| Analysis date: | May 13, 2024, 13:57:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Create Time/Date: Mon Jun 21 07:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1252, Template: Intel;1033, Number of Pages: 200, Revision Number: {29BB91B7-9C1B-4AC3-95D0-0063B92B5721}, Title: Setup Power BI Helper, Author: RADACAD, Number of Words: 2, Last Saved Time/Date: Mon Jun 28 04:03:48 2021, Last Printed: Mon Jun 28 04:03:48 2021 |
| MD5: | 5C1FB0E92511D099C661F122CBF9F657 |
| SHA1: | 7CD7229FC974FFB797C5A48F3009C3E15E12E79F |
| SHA256: | 9CBC9C06E2399568712E7F2139508EE1EA22933FF468C33AA41DE6513CC6149F |
| SSDEEP: | 98304:4j0el1egv3bv3/v3XFawUflw3mOdeRJ5gCaSROOyGjEpwoQUVgV2TUNHoNC13ZW7:LY0R/oX8mR |
MALICIOUS
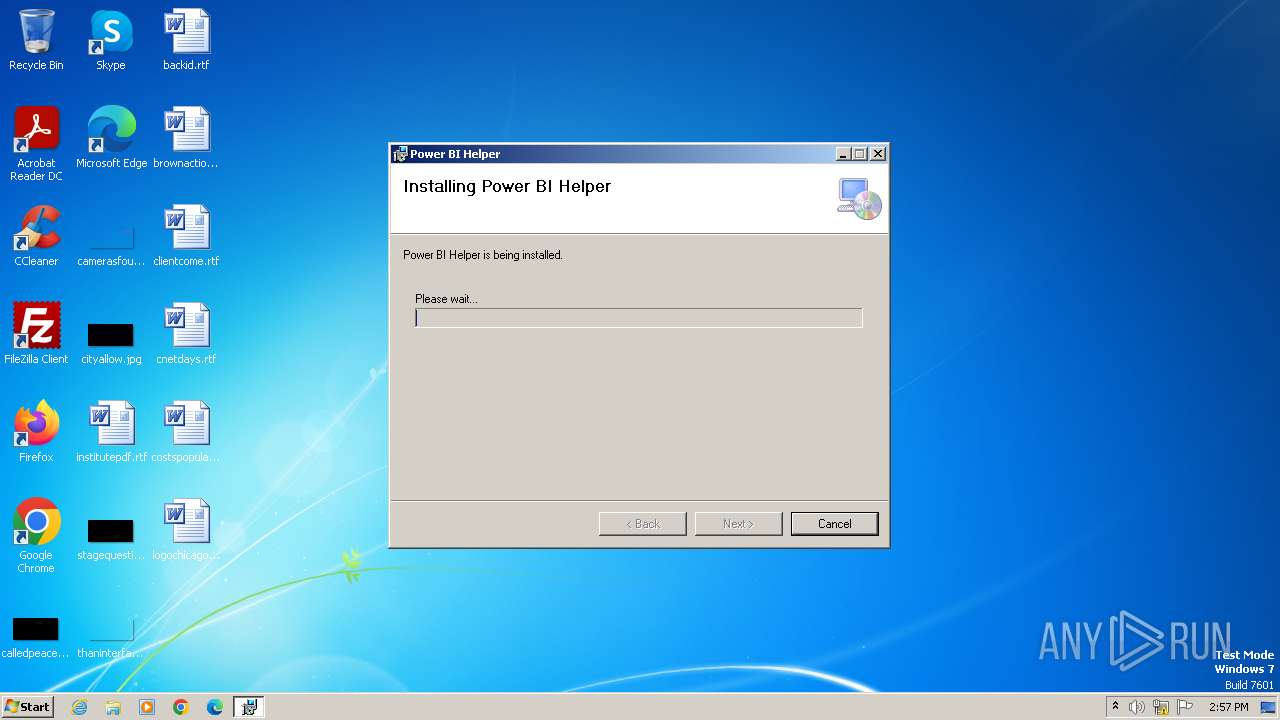
Drops the executable file immediately after the start
- msiexec.exe (PID: 3968)
- msiexec.exe (PID: 4016)
SUSPICIOUS
Process drops legitimate windows executable
- msiexec.exe (PID: 3968)
- msiexec.exe (PID: 4016)
Executes as Windows Service
- VSSVC.exe (PID: 1120)
Checks Windows Trust Settings
- msiexec.exe (PID: 4016)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4016)
The process creates files with name similar to system file names
- msiexec.exe (PID: 4016)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 580)
INFO
Checks supported languages
- msiexec.exe (PID: 4016)
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 2068)
- msiexec.exe (PID: 580)
Reads the software policy settings
- msiexec.exe (PID: 3968)
- msiexec.exe (PID: 4016)
Reads the computer name
- msiexec.exe (PID: 4016)
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 2068)
- msiexec.exe (PID: 580)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4016)
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 2068)
- msiexec.exe (PID: 580)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3968)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3968)
- msiexec.exe (PID: 4016)
Create files in a temporary directory
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 4016)
- msiexec.exe (PID: 2068)
Application launched itself
- msiexec.exe (PID: 4016)
Creates files or folders in the user directory
- msiexec.exe (PID: 4016)
Creates a software uninstall entry
- msiexec.exe (PID: 4016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (90.2) |
|---|---|---|
| .msp | | | Windows Installer Patch (8.4) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
| Pages: | 200 |
| RevisionNumber: | {29BB91B7-9C1B-4AC3-95D0-0063B92B5721} |
| Title: | Setup Power BI Helper |
| Subject: | - |
| Author: | RADACAD |
| Keywords: | - |
| Comments: | - |
| Words: | 2 |
| ModifyDate: | 2021:06:28 04:03:48 |
| LastPrinted: | 2021:06:28 04:03:48 |
Total processes
40
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | C:\Windows\system32\MsiExec.exe -Embedding 35A2F3B6719685D3C06C9C1CCE857D2D E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1120 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | C:\Windows\system32\MsiExec.exe -Embedding CFAF6FD0155F51F4DC385CC1D986E147 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\Setup_Power_BI_Helperv12.3.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4016 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4060 | C:\Windows\system32\MsiExec.exe -Embedding D043C1122705A41727A78EC04DB2BA71 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
11 964
Read events
11 415
Write events
529
Delete events
20
Modification events
| (PID) Process: | (3968) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4016) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000CA40B87D3DA5DA01B00F000038080000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000CA40B87D3DA5DA01B00F000038080000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 75 | |||
| (PID) Process: | (4016) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000BA0F8A7E3DA5DA01B00F000038080000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000014728C7E3DA5DA01B00F0000E8070000E80300000100000000000000000000007533668F9B99C64DB66399535A48C6B30000000000000000 | |||
| (PID) Process: | (1120) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C836917E3DA5DA016004000090060000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1120) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C836917E3DA5DA016004000084080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1120) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C836917E3DA5DA016004000060030000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1120) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C836917E3DA5DA016004000034030000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
132
Suspicious files
7
Text files
8
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4016 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{8f663375-999b-4dc6-b663-99535a48c6b3}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 4016 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4016 | msiexec.exe | C:\Windows\Installer\109646.msi | — | |
MD5:— | SHA256:— | |||
| 4016 | msiexec.exe | C:\Windows\Installer\MSI9BA6.tmp | executable | |
MD5:9945F10135A4C7214FA5605C21E5DE9B | SHA256:9F3B0F3AF4BFA061736935BAB1D50ED2581358DDC9A9C0DB22564ACED1A1807C | |||
| 3968 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI3F7D.tmp | executable | |
MD5:9945F10135A4C7214FA5605C21E5DE9B | SHA256:9F3B0F3AF4BFA061736935BAB1D50ED2581358DDC9A9C0DB22564ACED1A1807C | |||
| 4016 | msiexec.exe | C:\Program Files\RADACAD\Power BI Helper\System.Diagnostics.Tools.dll | executable | |
MD5:7D6677BD3F07DF4BBB6630A286F05F9A | SHA256:ADF05606FB2695C58F575873F4D75E05DCAB8BEB7D8F34507017D600DD8FFBC6 | |||
| 4016 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF308FBD5267181928.TMP | gmc | |
MD5:7937779A5C2ED28B7F93C77E6C864AD1 | SHA256:F6D0B85516A562D56DF28AC5CFACE5D045ADB52A15F79A1233EFBC5FE8E4054F | |||
| 4016 | msiexec.exe | C:\Program Files\RADACAD\Power BI Helper\System.Resources.ResourceManager.dll | executable | |
MD5:D13247D55E701B1D9BEC5F82254B4D6F | SHA256:1818D46656A2C4CF9EB93F04F0E58BF762A59F7319C92F0FBCF3D58E132193F1 | |||
| 4016 | msiexec.exe | C:\Windows\Installer\109647.ipi | binary | |
MD5:F9EE48E5D9E61369099278BA78F79D38 | SHA256:4CEB88D493C4D25287AC6FFFCF89DF38F168A7E977217F18240E52E550EDA5DD | |||
| 2068 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CFG9B86.tmp | xml | |
MD5:84F2F872035A2B2007494208AC3B98C4 | SHA256:F5BA88B4A9928B710C9DBF757F0C4DEE5BC6B6A56985D5BFEBA8620C8AE65B6C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |