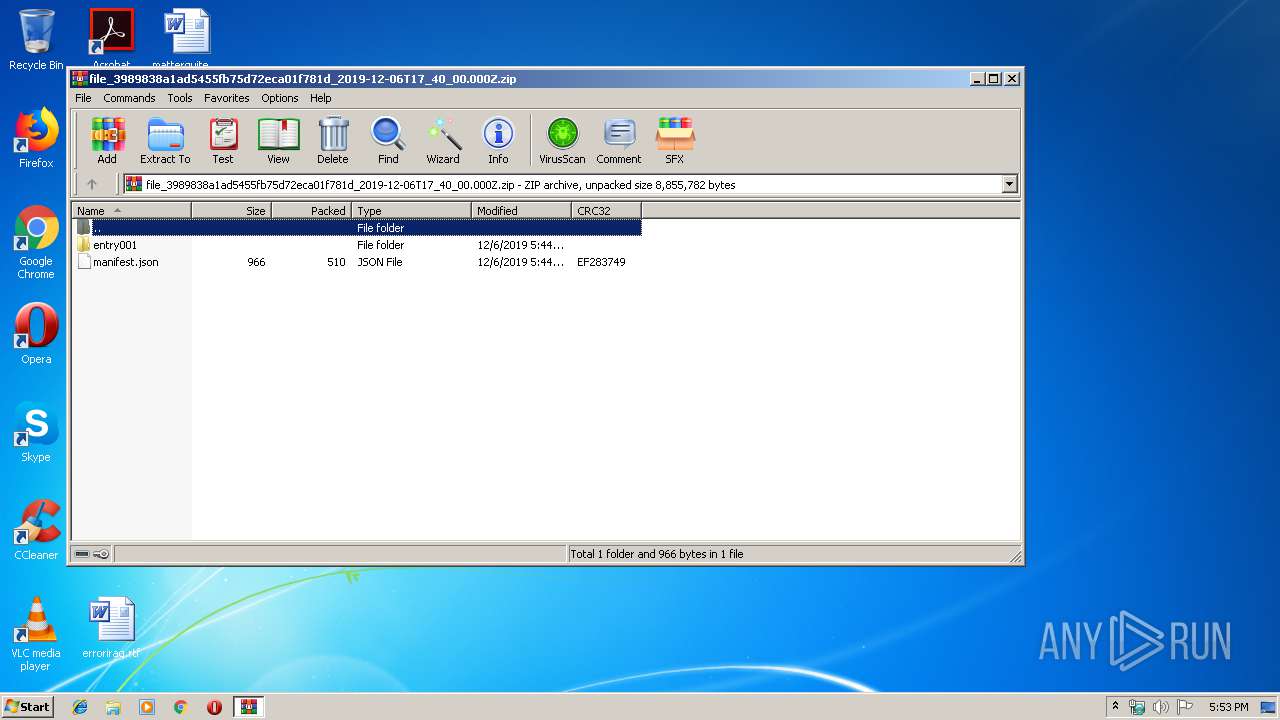
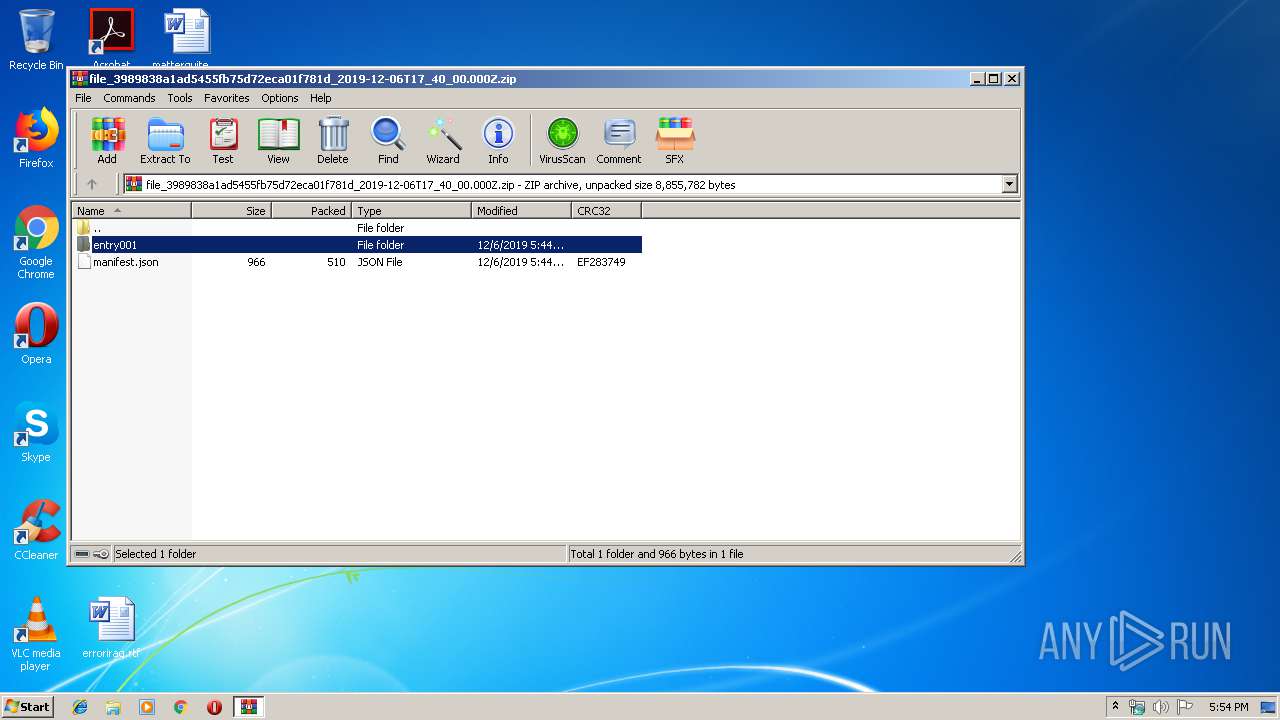
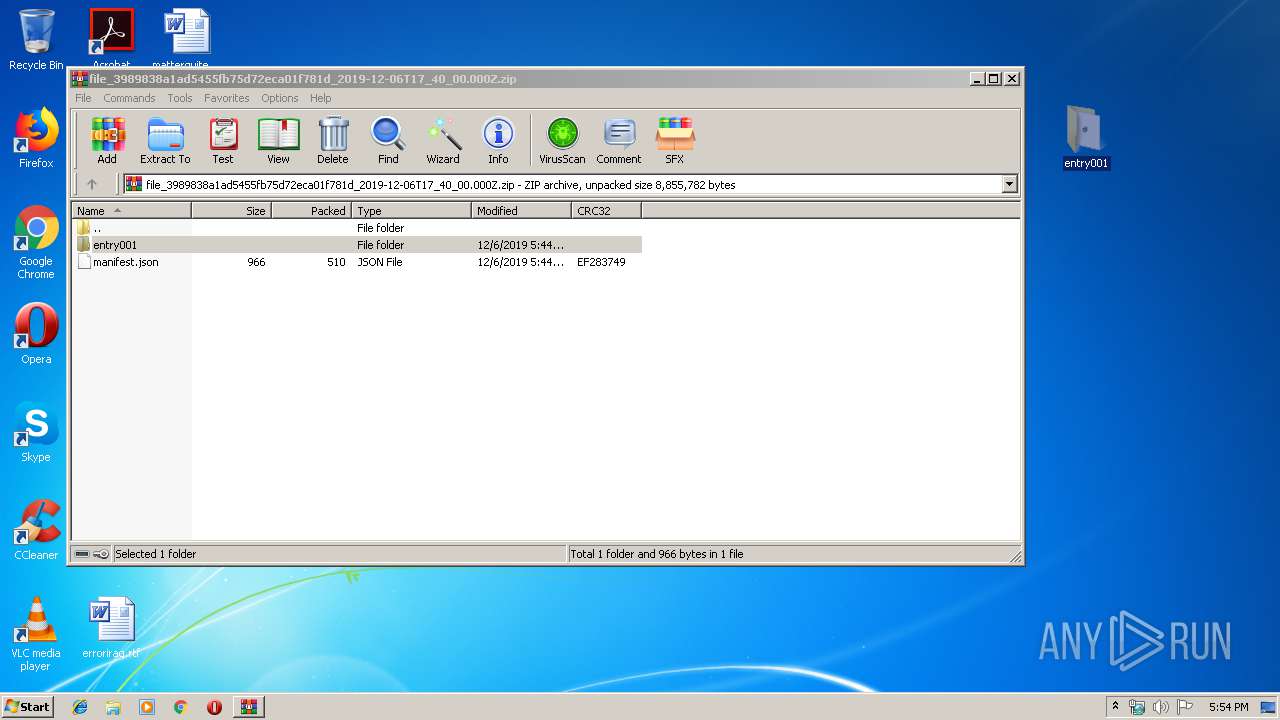
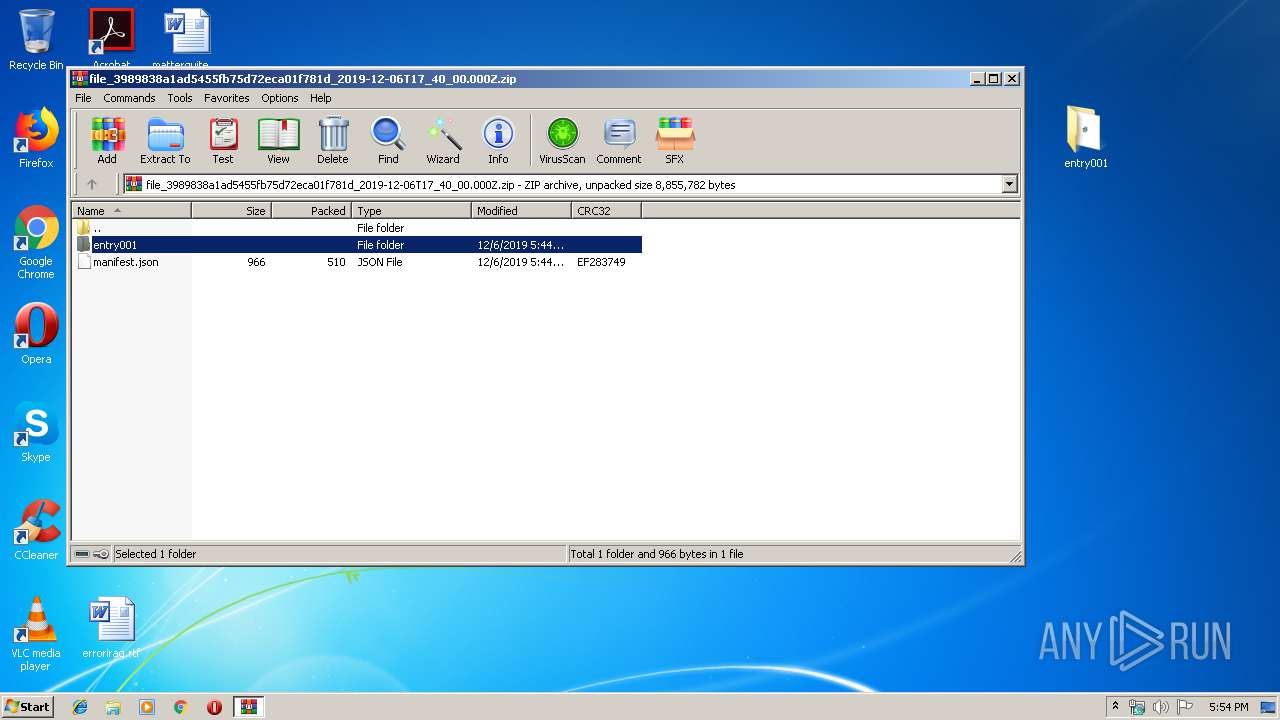
| File name: | file_3989838a1ad5455fb75d72eca01f781d_2019-12-06T17_40_00.000Z.zip |
| Full analysis: | https://app.any.run/tasks/f6db5786-cc60-4bd9-ba96-cc0a14d8b6b5 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 17:53:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
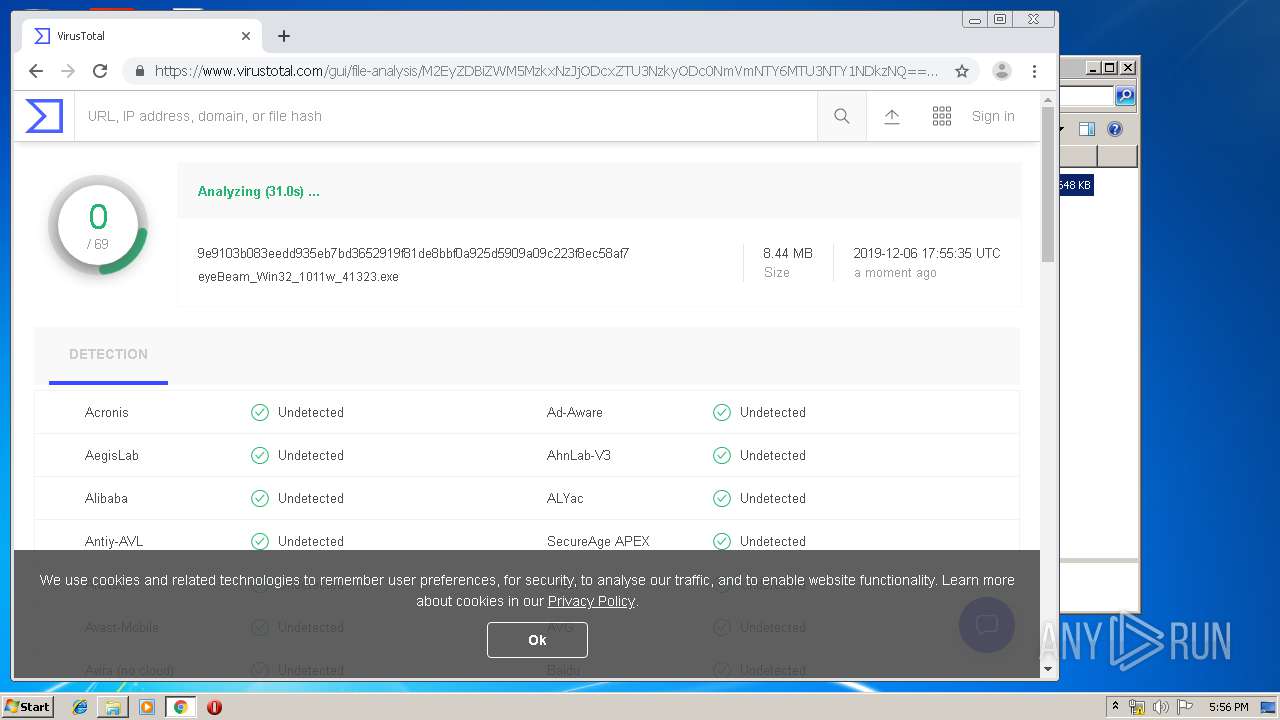
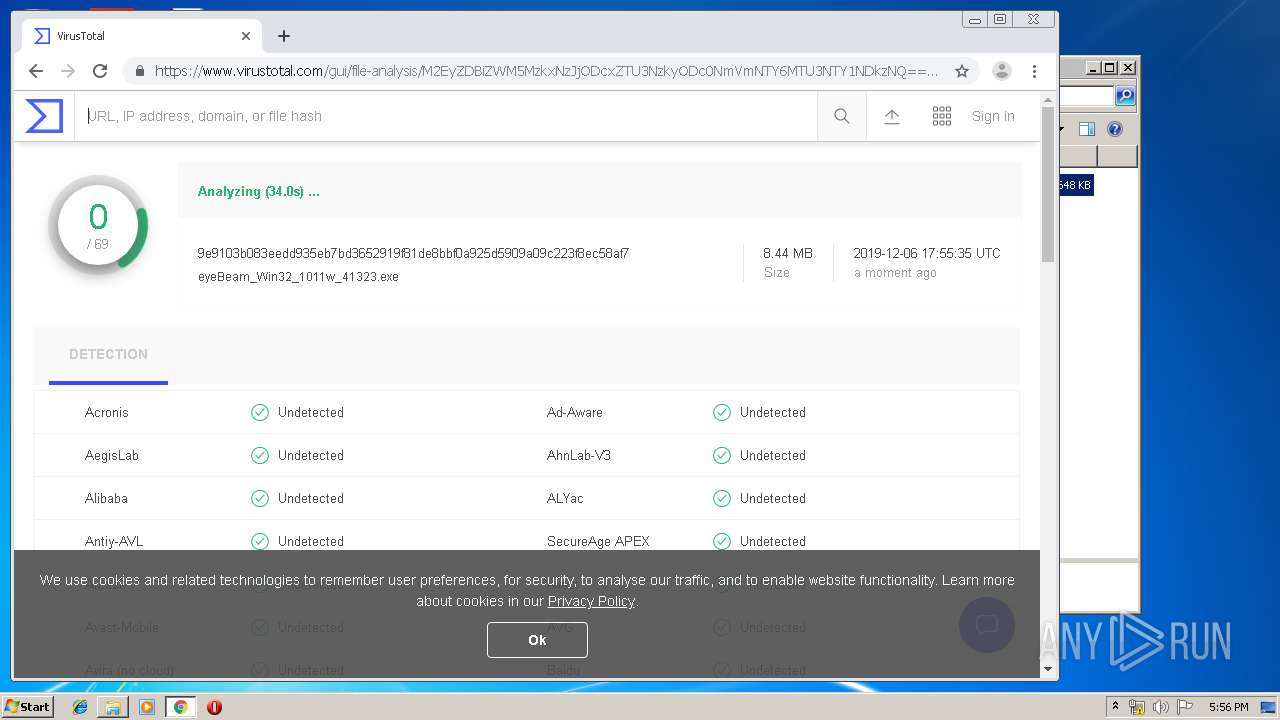
| MD5: | 34544B7793D8B8E40AAD0BCB6FD46672 |
| SHA1: | 6F4B2A2875B442CC6BF01A108694DE7872C7062F |
| SHA256: | 9CB828410A128E11C0917B71A33AD1DA218A52A99CFAE2274A3FE65C0CED327A |
| SSDEEP: | 196608:hGo9XS/ZBf2Jz/k+Ef+x+ZXGLxl6XO9/A8Lp8UjgBD0sipRHmLj:hGsSLK/h4++XL8ljpsi7mX |
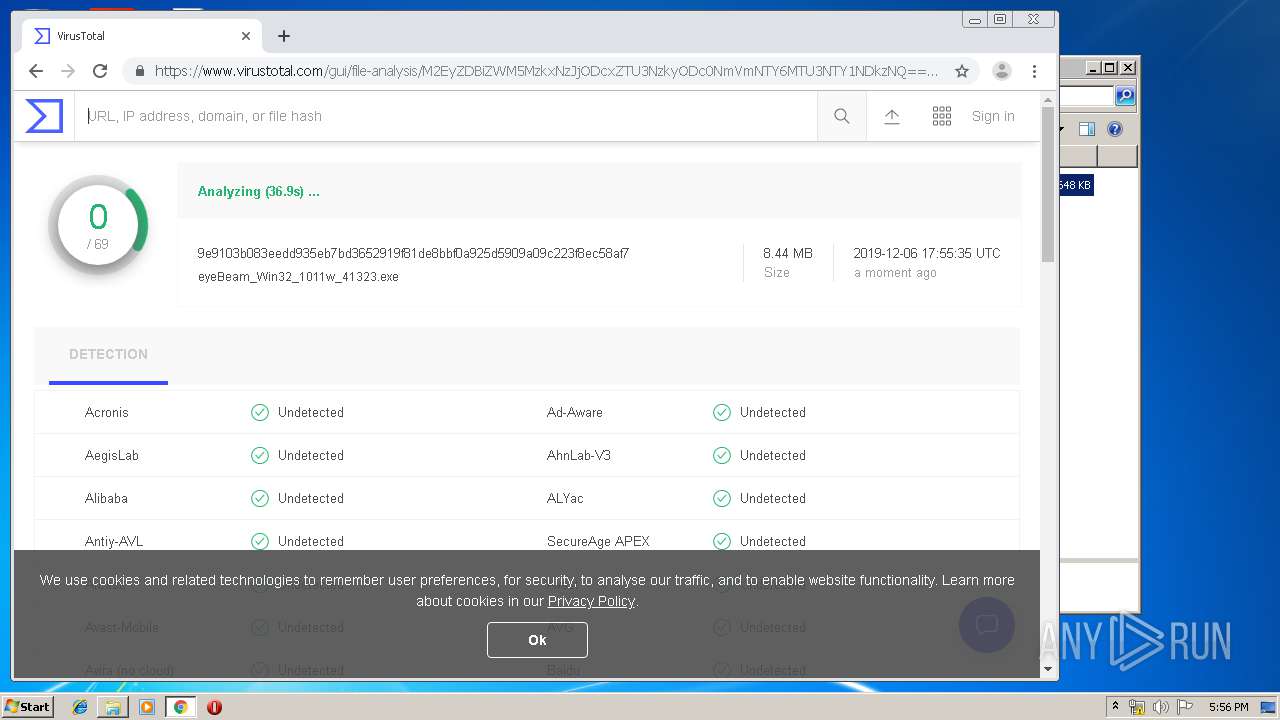
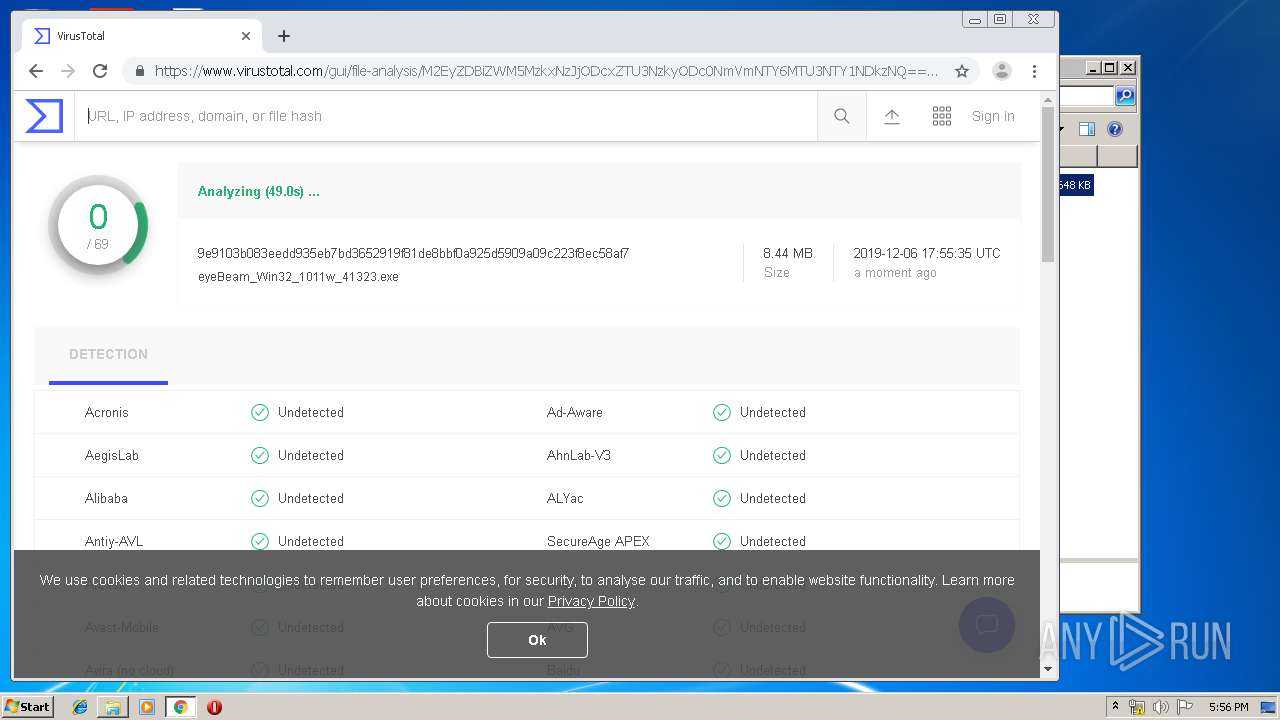
MALICIOUS
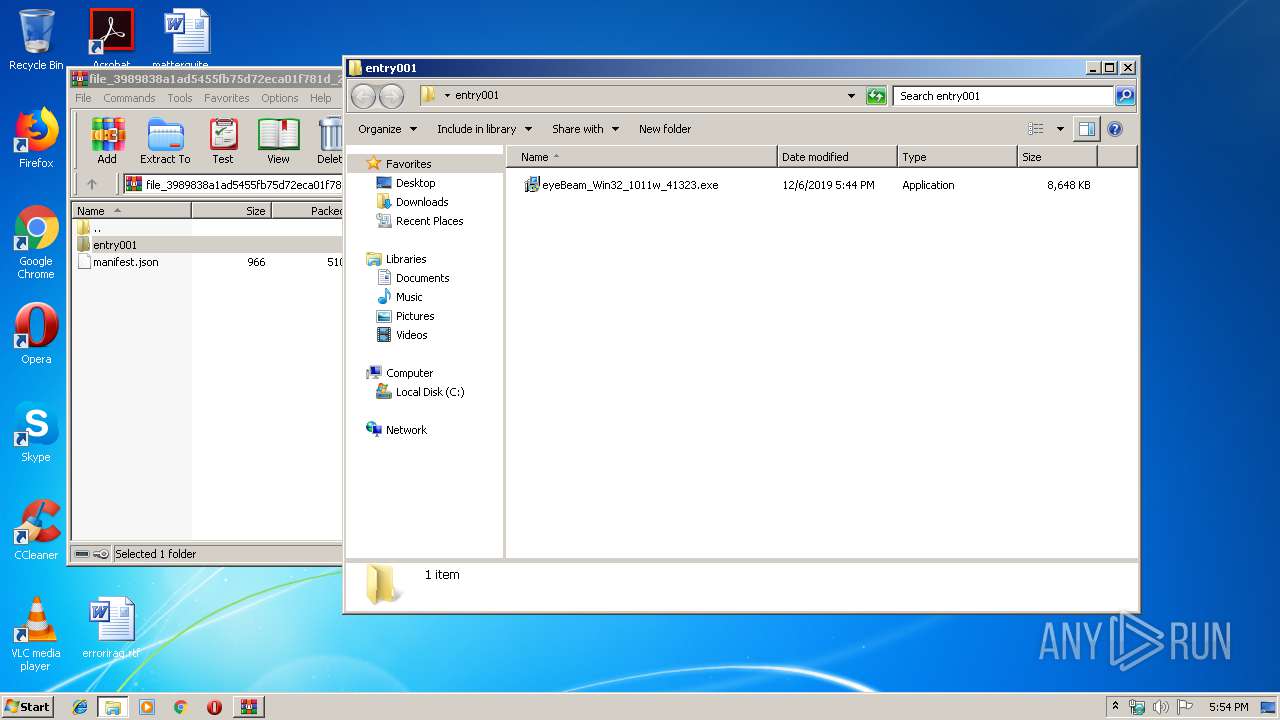
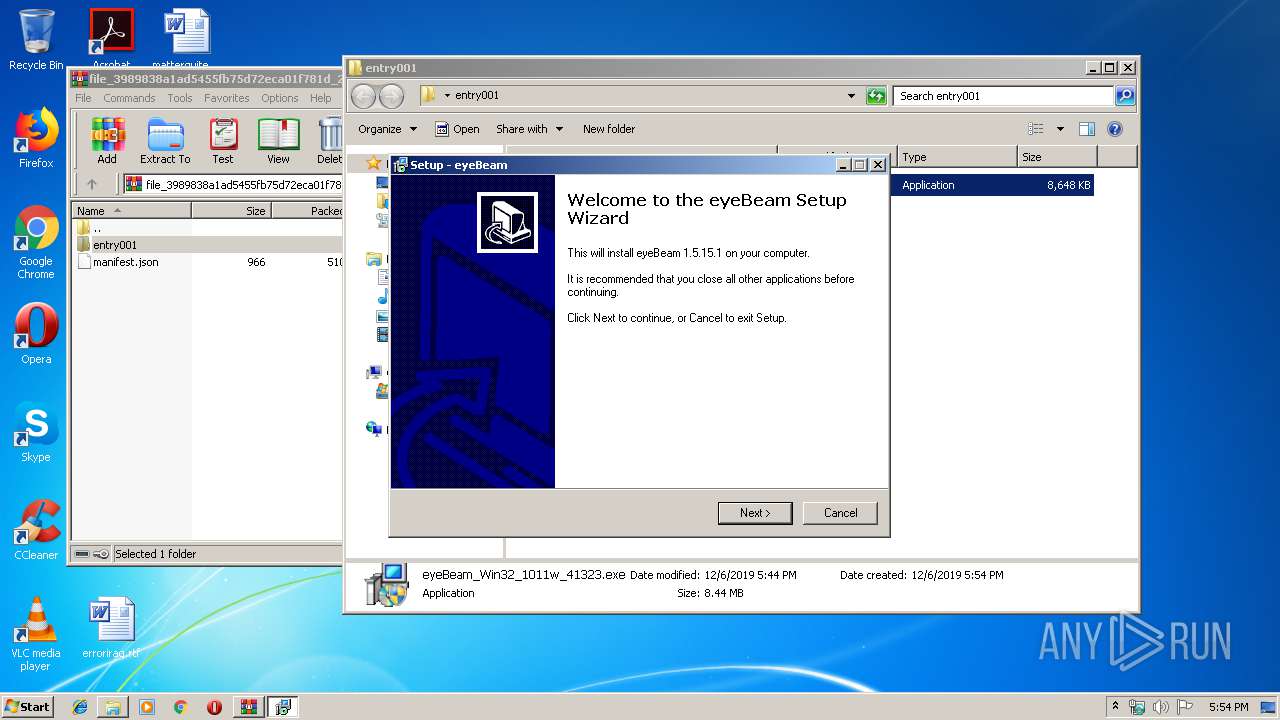
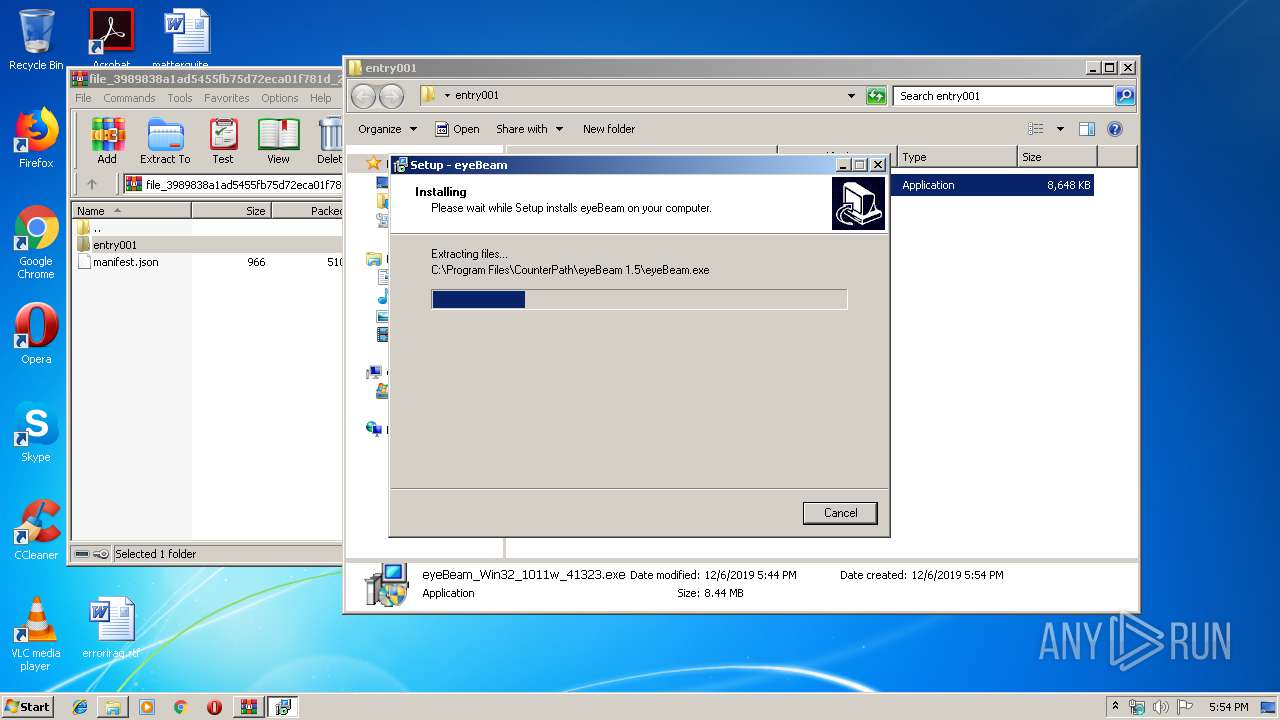
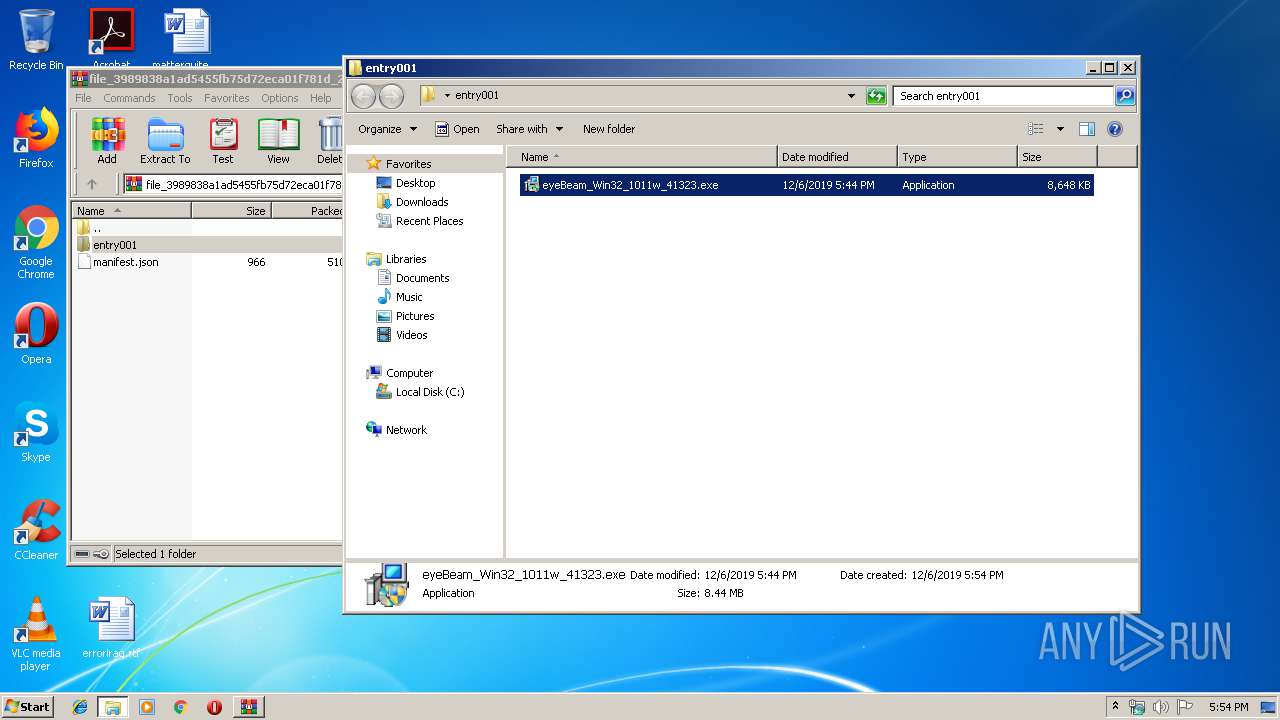
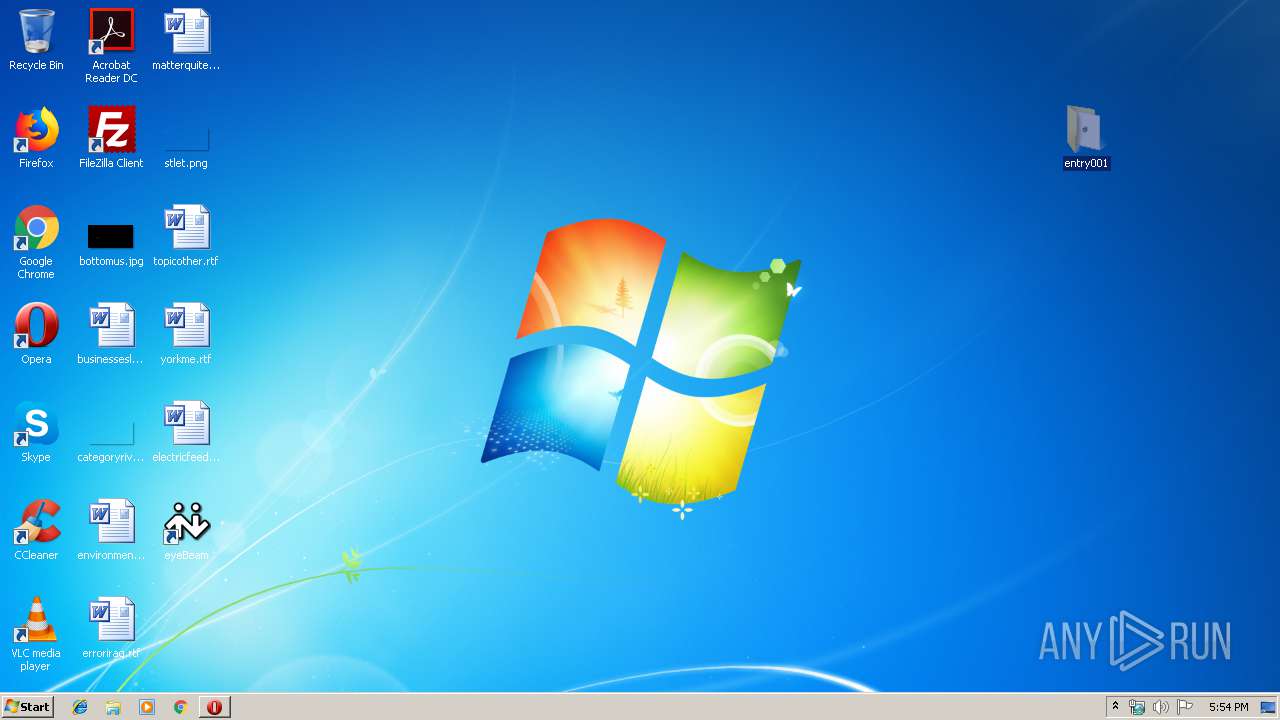
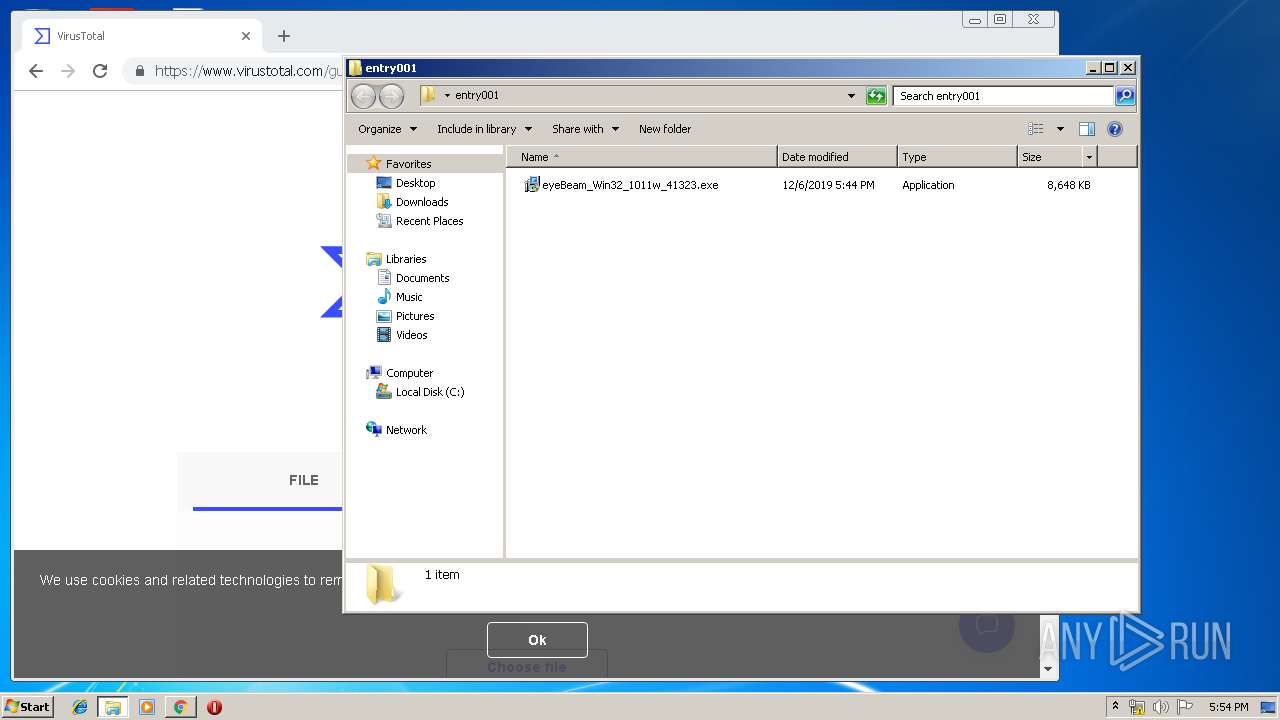
Application was dropped or rewritten from another process
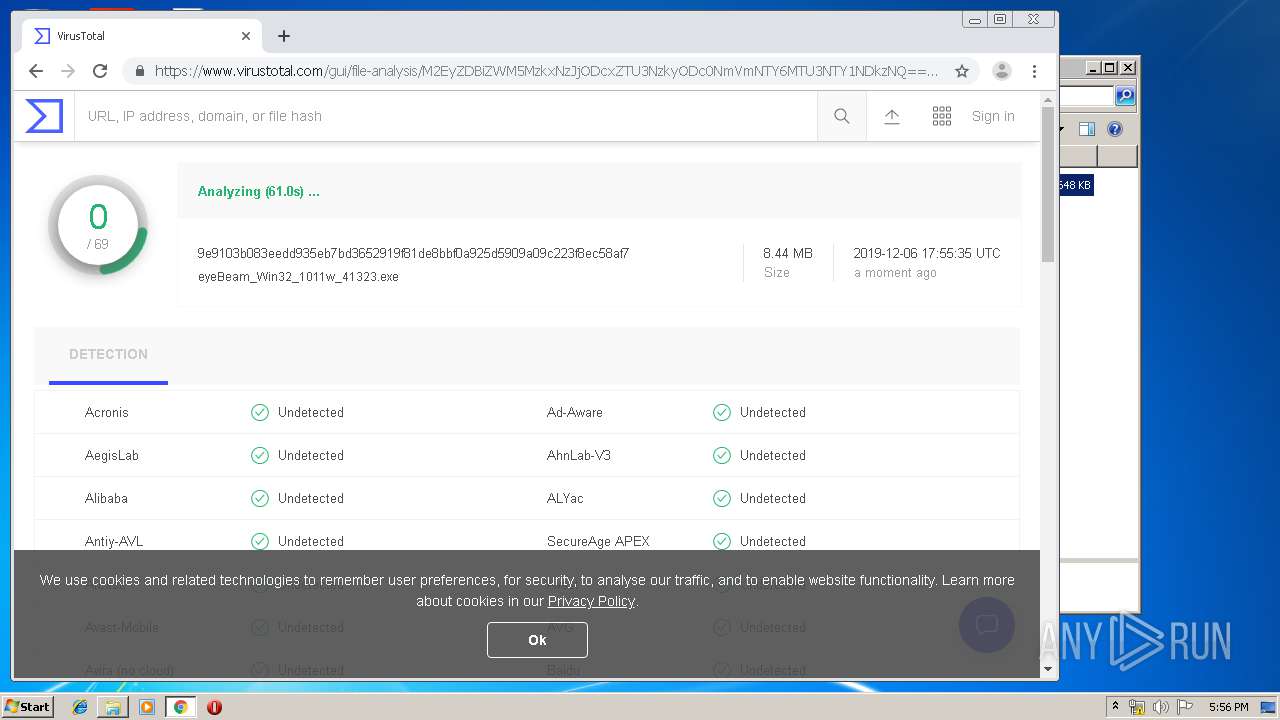
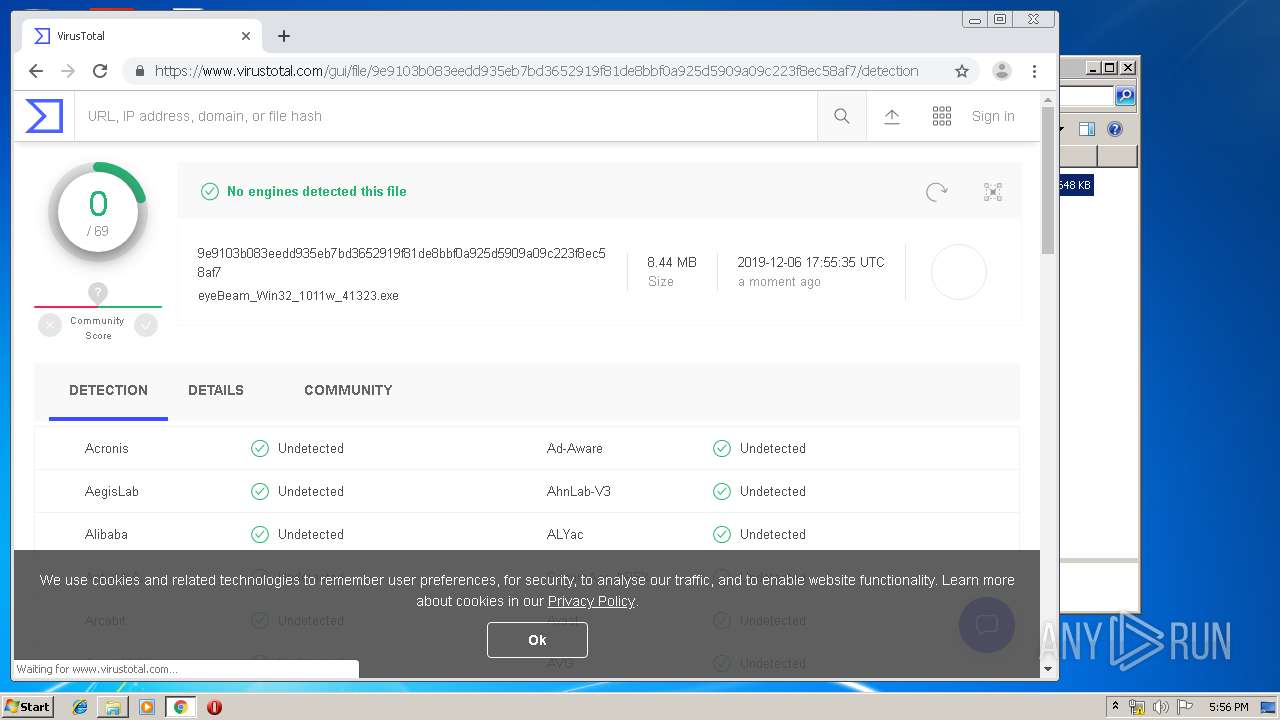
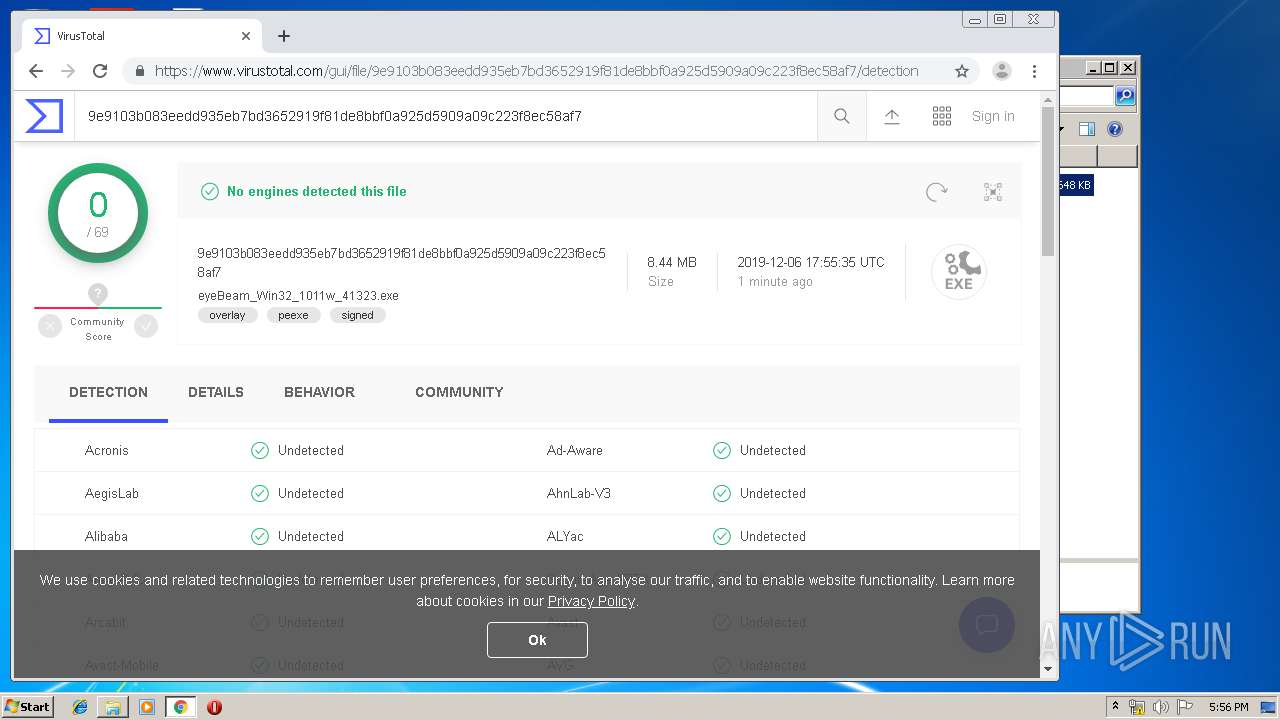
- eyeBeam_Win32_1011w_41323.exe (PID: 2416)
- eyeBeam_Win32_1011w_41323.exe (PID: 3328)
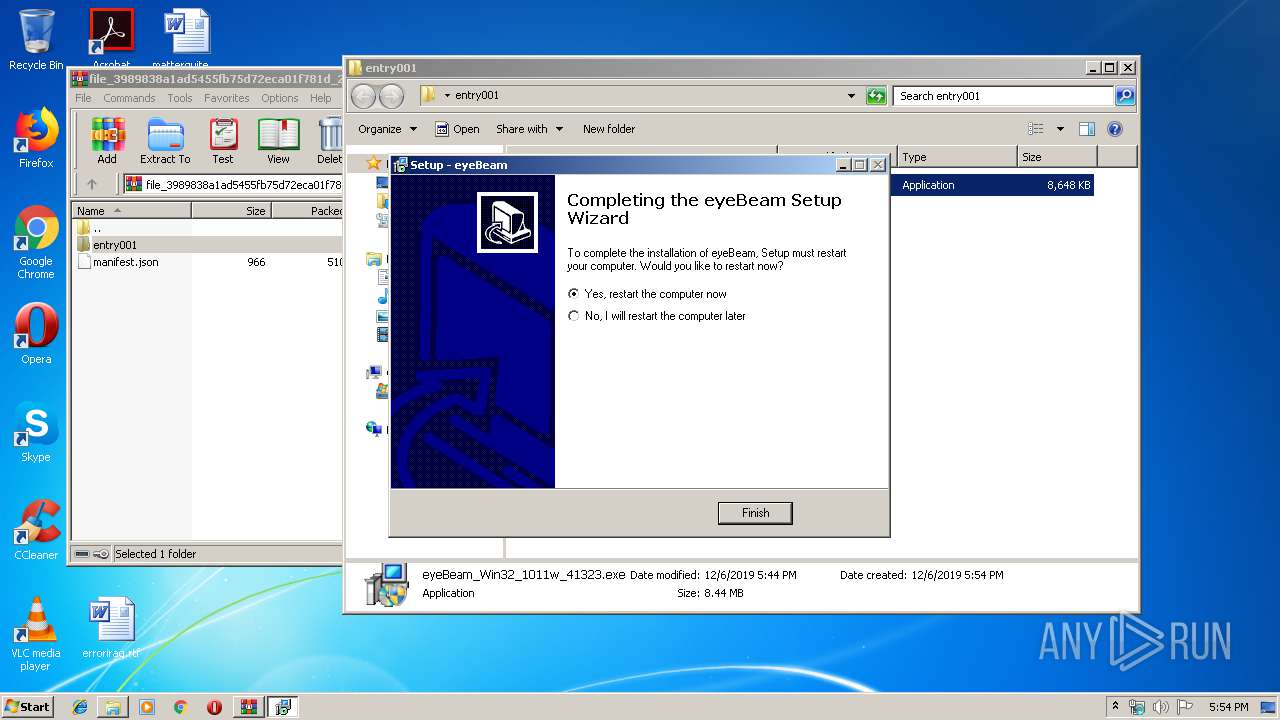
Changes the autorun value in the registry
- is-CENKQ.tmp (PID: 3972)
SUSPICIOUS
Executable content was dropped or overwritten
- is-CENKQ.tmp (PID: 3972)
- eyeBeam_Win32_1011w_41323.exe (PID: 2416)
- WinRAR.exe (PID: 2716)
Creates files in the Windows directory
- is-CENKQ.tmp (PID: 3972)
Modifies files in Chrome extension folder
- chrome.exe (PID: 992)
Modifies the open verb of a shell class
- is-CENKQ.tmp (PID: 3972)
INFO
Creates files in the program directory
- is-CENKQ.tmp (PID: 3972)
Creates a software uninstall entry
- is-CENKQ.tmp (PID: 3972)
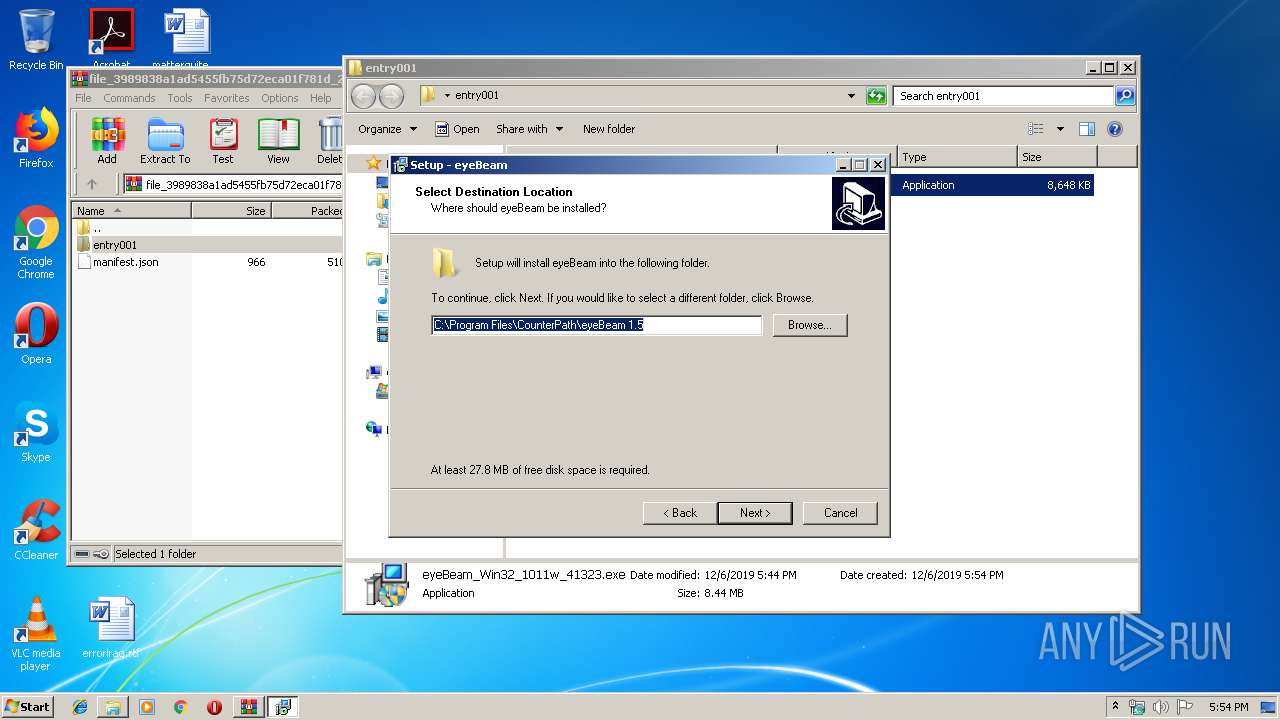
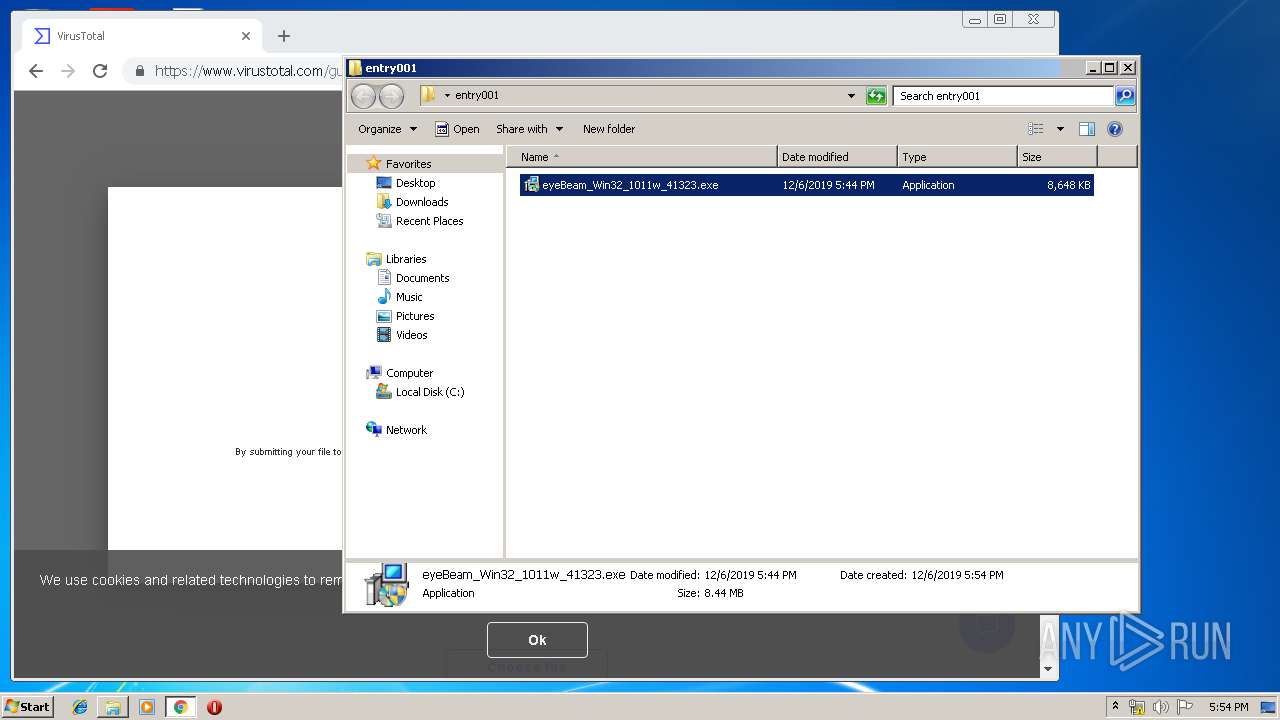
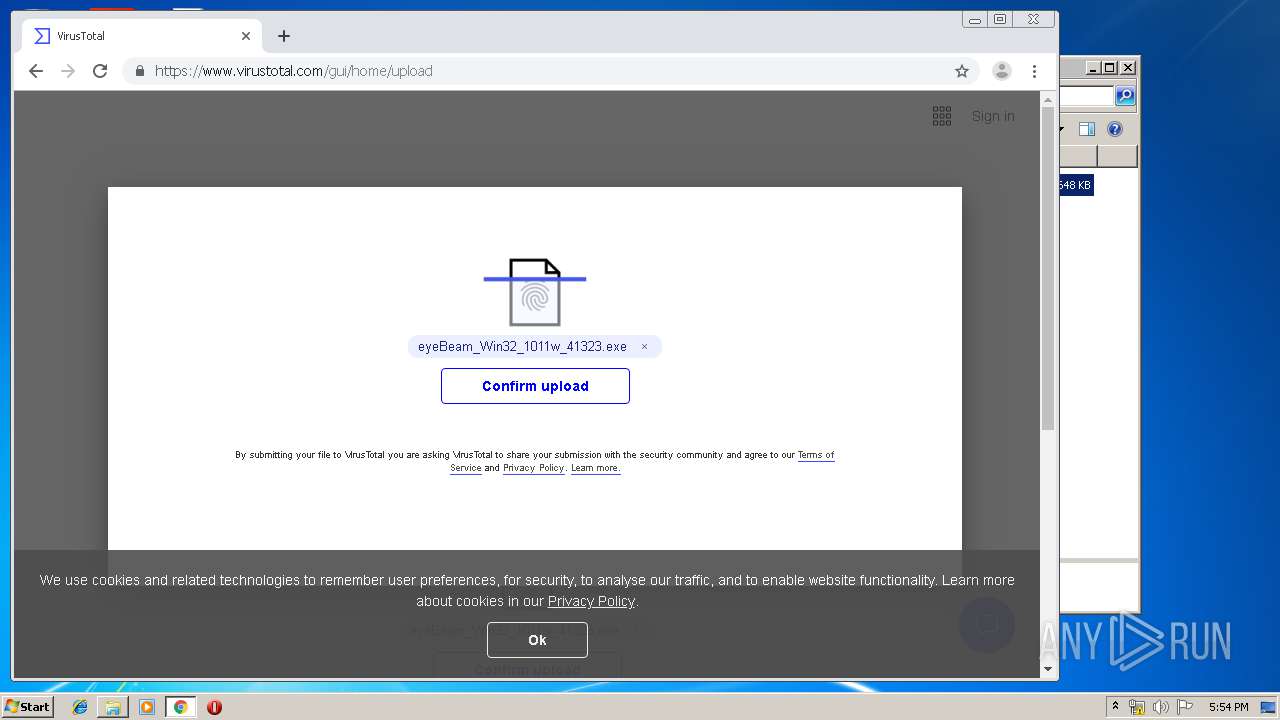
Manual execution by user
- eyeBeam_Win32_1011w_41323.exe (PID: 3328)
- eyeBeam_Win32_1011w_41323.exe (PID: 2416)
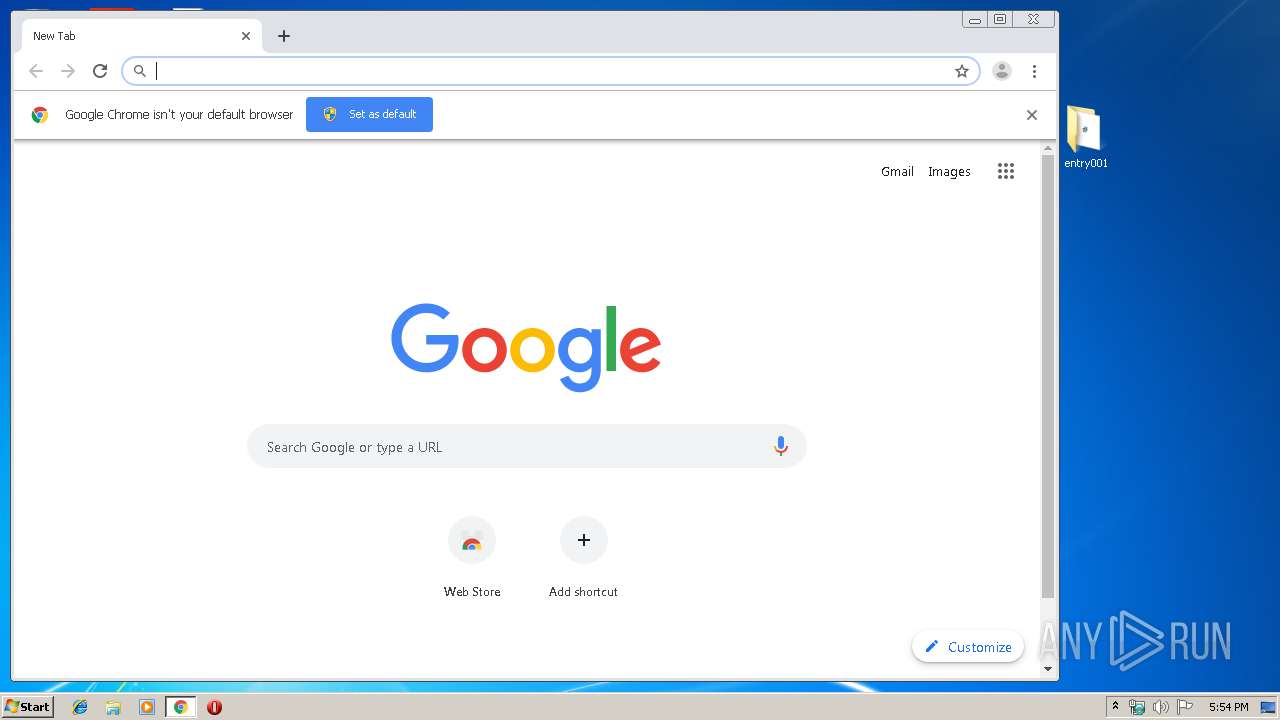
- chrome.exe (PID: 992)
Reads the hosts file
- chrome.exe (PID: 2204)
- chrome.exe (PID: 992)
Loads dropped or rewritten executable
- is-CENKQ.tmp (PID: 3972)
Application launched itself
- chrome.exe (PID: 992)
Application was dropped or rewritten from another process
- is-CENKQ.tmp (PID: 3972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | None |
| ZipModifyDate: | 2019:12:06 17:44:01 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | entry001/ |
Total processes
76
Monitored processes
36
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16796762708728983454,4020627738588851062,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2757485770772405082 --mojo-platform-channel-handle=3816 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16796762708728983454,4020627738588851062,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16492073565666942786 --mojo-platform-channel-handle=4060 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16796762708728983454,4020627738588851062,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=561061797257148213 --mojo-platform-channel-handle=3452 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,16796762708728983454,4020627738588851062,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9277186051991656390 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,16796762708728983454,4020627738588851062,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18083523831595454216 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16796762708728983454,4020627738588851062,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1004756529306136712 --mojo-platform-channel-handle=3284 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,16796762708728983454,4020627738588851062,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13025635306596146178 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16796762708728983454,4020627738588851062,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=317820339635094122 --mojo-platform-channel-handle=3432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16796762708728983454,4020627738588851062,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1299634440952165491 --mojo-platform-channel-handle=3576 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 479
Read events
1 327
Write events
147
Delete events
5
Modification events
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\file_3989838a1ad5455fb75d72eca01f781d_2019-12-06T17_40_00.000Z.zip | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
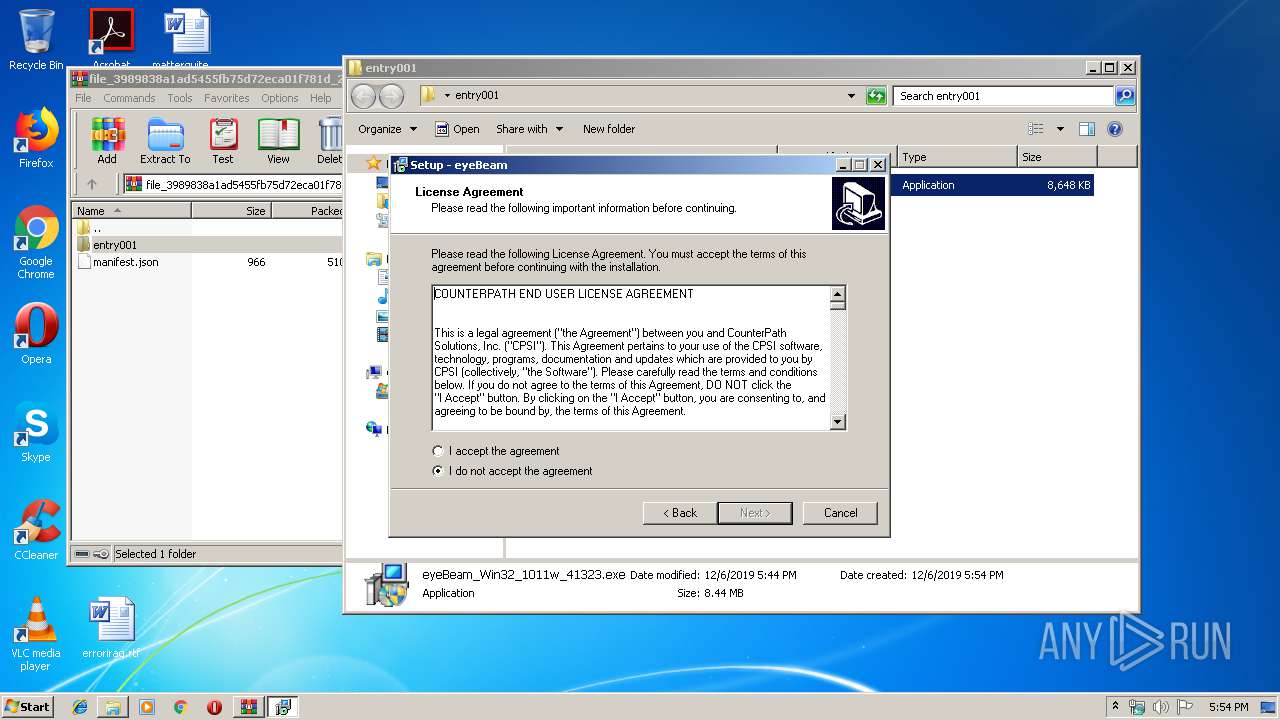
| (PID) Process: | (3972) is-CENKQ.tmp | Key: | HKEY_CURRENT_USER\Software\EBInstaller |
| Operation: | write | Name: | InstallerName |
Value: eyeBeam_Win32_1011w_41323.exe | |||
| (PID) Process: | (3972) is-CENKQ.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | eyeBeam SIP Client |
Value: "C:\Program Files\CounterPath\eyeBeam 1.5\eyeBeam.exe" | |||
Executable files
25
Suspicious files
61
Text files
320
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | is-CENKQ.tmp | C:\Program Files\CounterPath\eyeBeam 1.5\is-PVJ1H.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | is-CENKQ.tmp | C:\Program Files\CounterPath\eyeBeam 1.5\is-9RIMC.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | is-CENKQ.tmp | C:\Program Files\CounterPath\eyeBeam 1.5\is-84R1Q.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | is-CENKQ.tmp | C:\Program Files\CounterPath\eyeBeam 1.5\is-BGVBA.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | is-CENKQ.tmp | C:\Program Files\CounterPath\eyeBeam 1.5\is-6R1BU.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | is-CENKQ.tmp | C:\Program Files\CounterPath\eyeBeam 1.5\is-L9I5C.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | is-CENKQ.tmp | C:\Program Files\CounterPath\eyeBeam 1.5\is-RTFJR.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | is-CENKQ.tmp | C:\Program Files\CounterPath\eyeBeam 1.5\is-1GQ8F.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | is-CENKQ.tmp | C:\Program Files\CounterPath\eyeBeam 1.5\is-RKCCP.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | is-CENKQ.tmp | C:\Program Files\CounterPath\eyeBeam 1.5\is-2PVKL.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
30
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
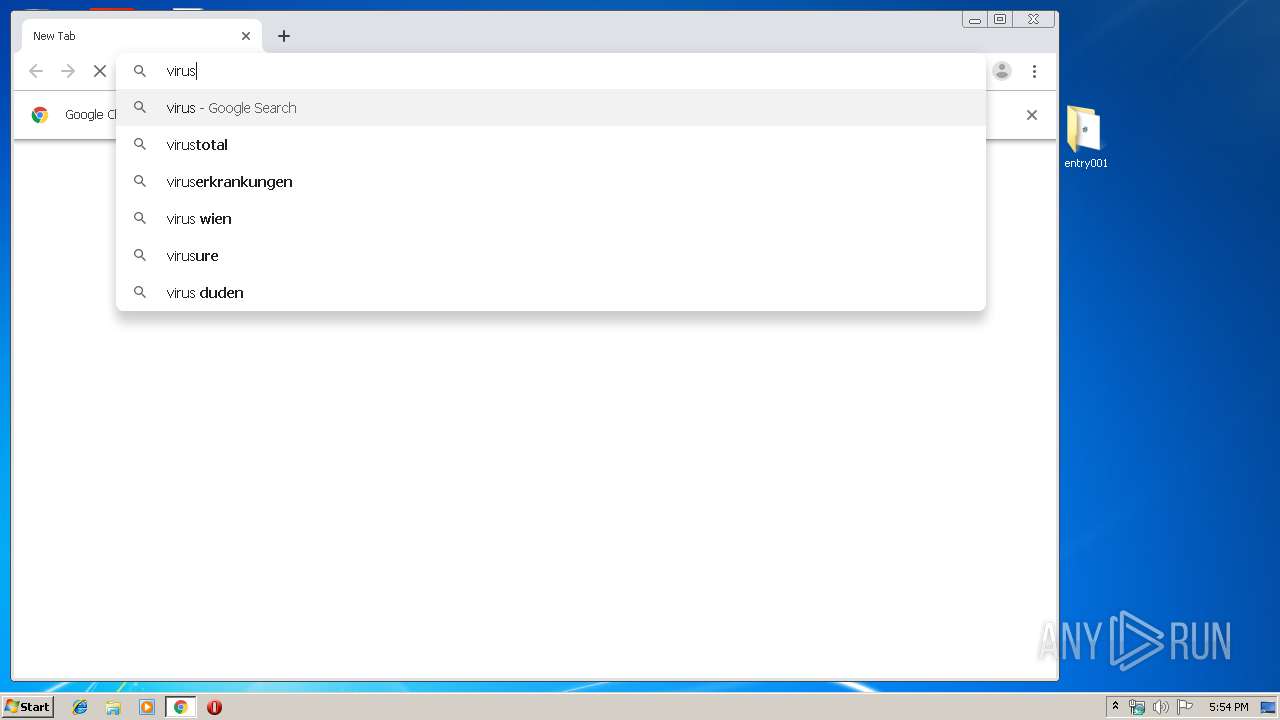
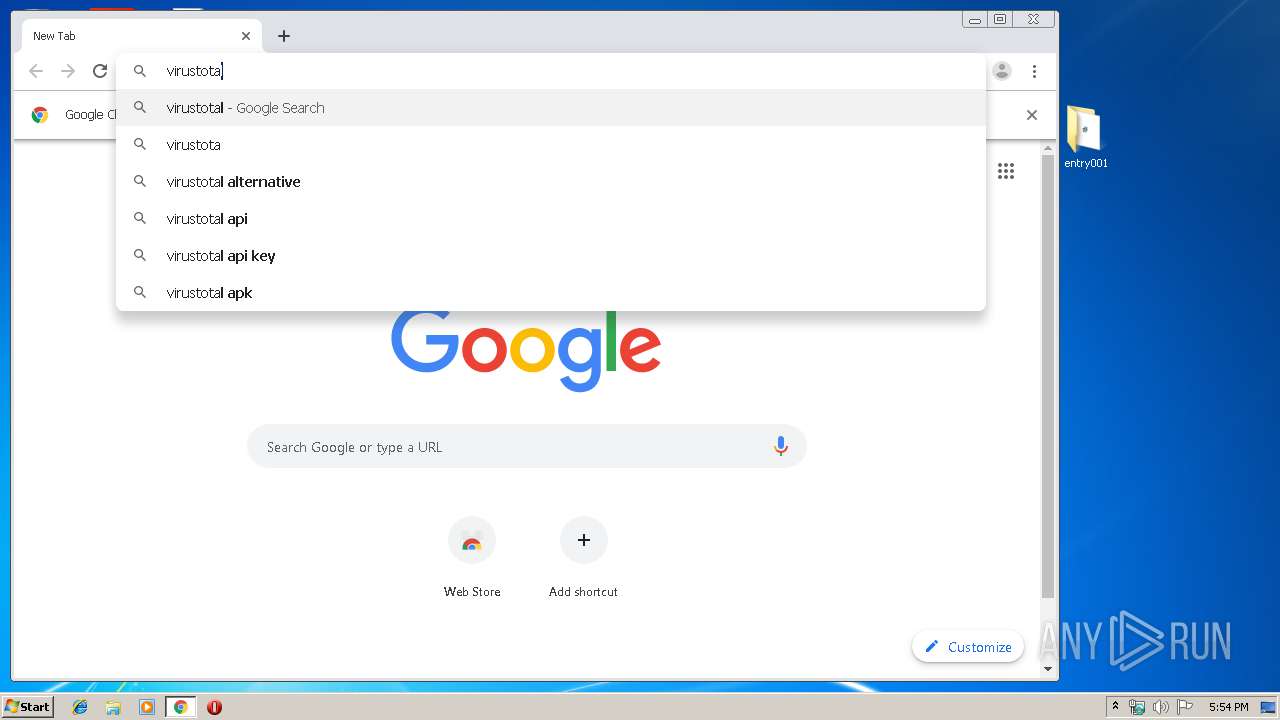
2204 | chrome.exe | GET | 302 | 216.239.32.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
2204 | chrome.exe | GET | 200 | 185.180.12.141:80 | http://r2---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.183.107.227&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1575654801&mv=m&mvi=1&pl=24&shardbypass=yes | AT | crx | 293 Kb | whitelisted |
2204 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 529 b | whitelisted |
2204 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 534 b | whitelisted |
2204 | chrome.exe | GET | 200 | 185.180.12.140:80 | http://r1---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.107.227&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1575654801&mv=m&mvi=0&pl=24&shardbypass=yes | AT | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2204 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2204 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2204 | chrome.exe | 172.217.22.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2204 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2204 | chrome.exe | 172.217.22.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2204 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2204 | chrome.exe | 172.217.23.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2204 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
2204 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |