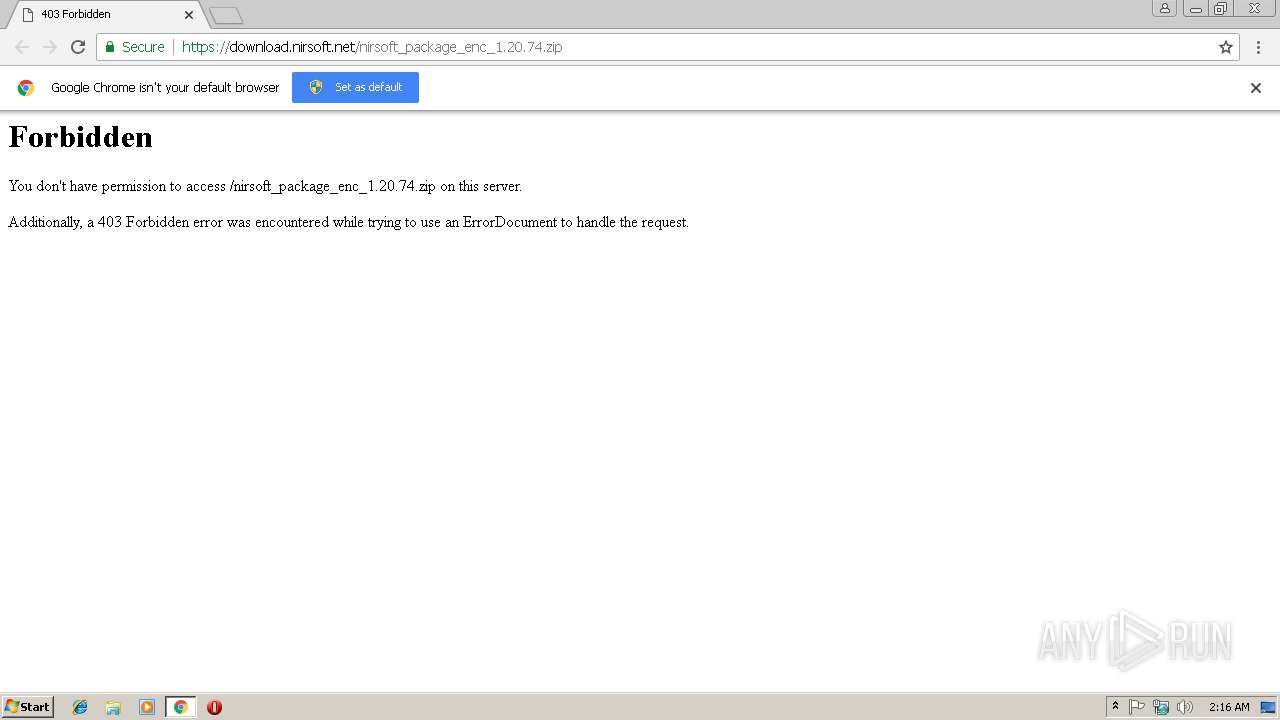
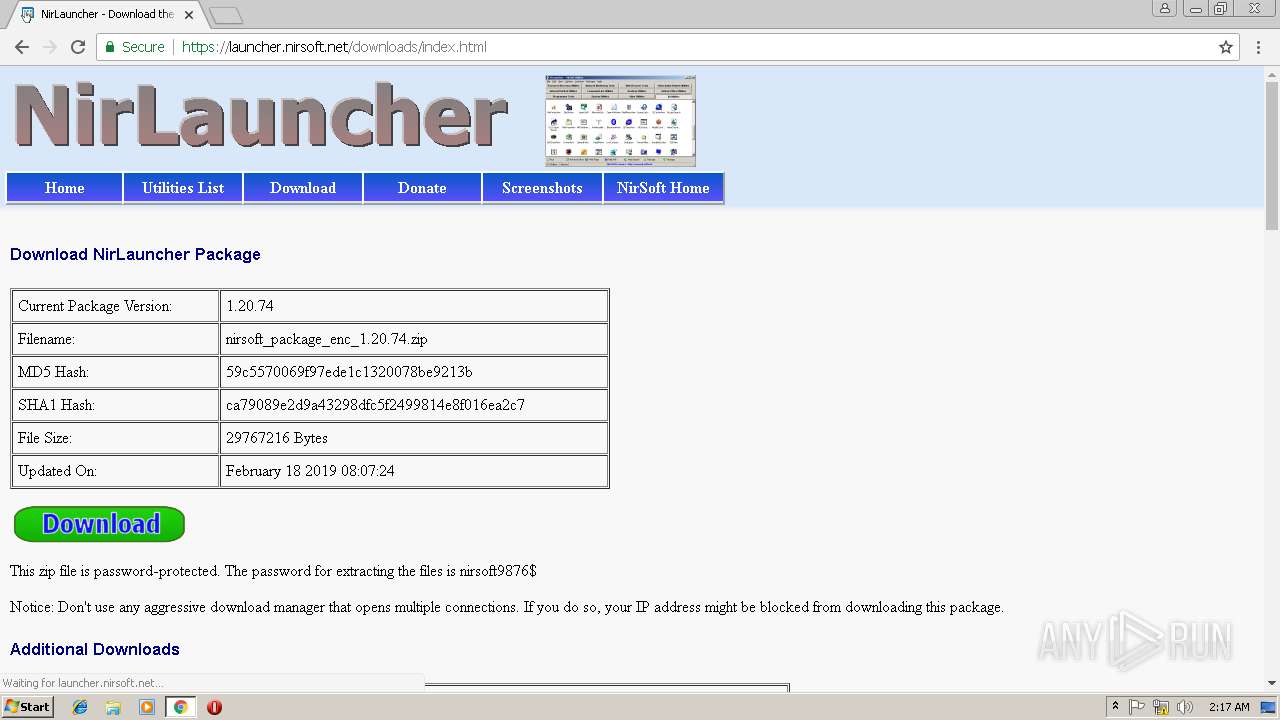
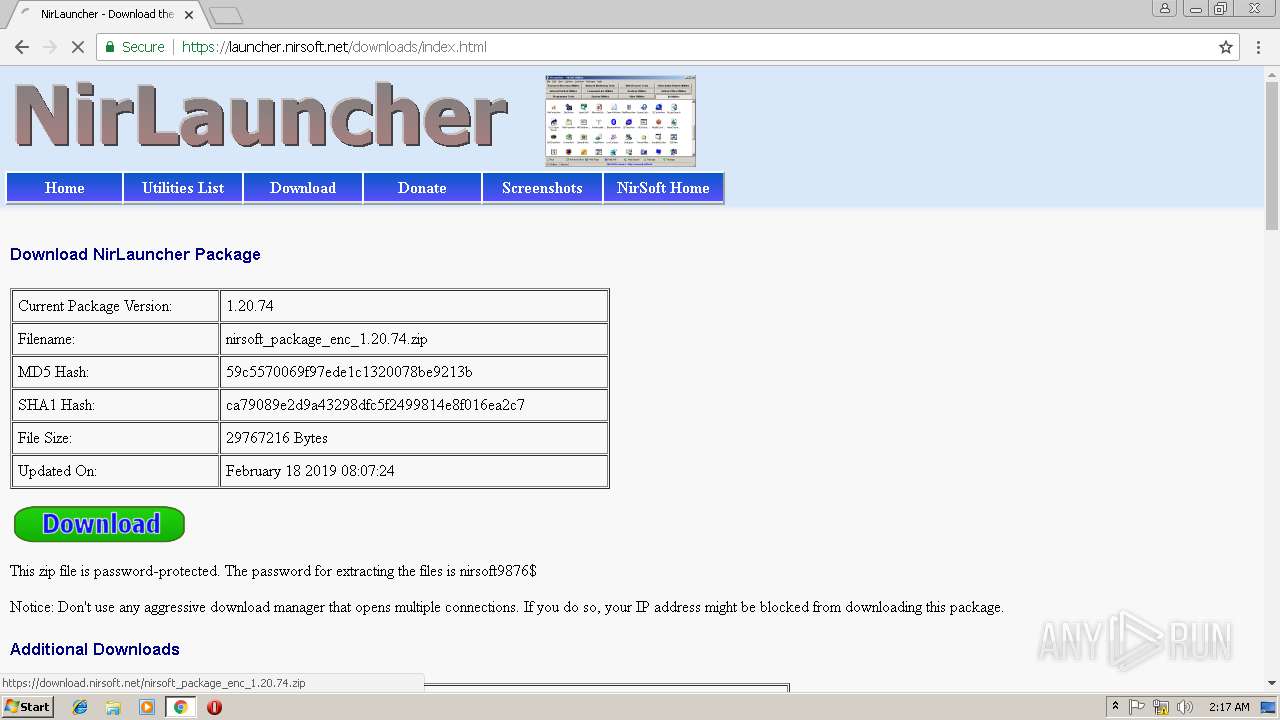
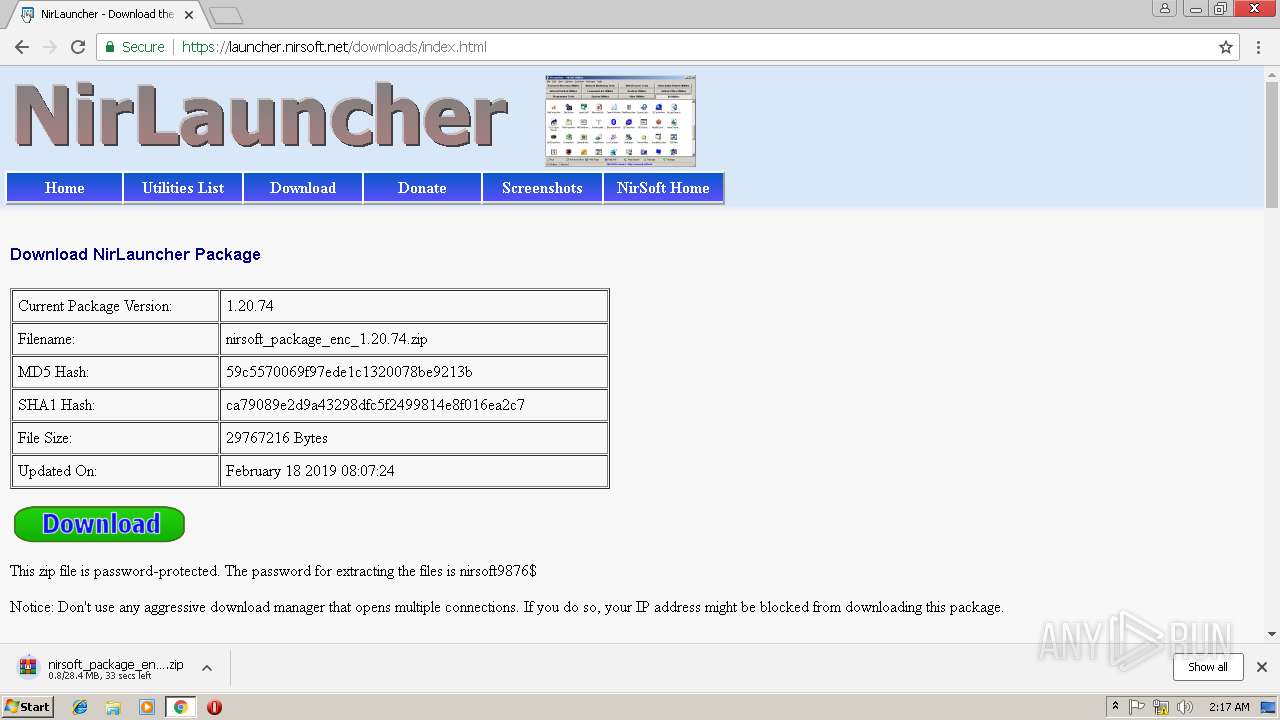
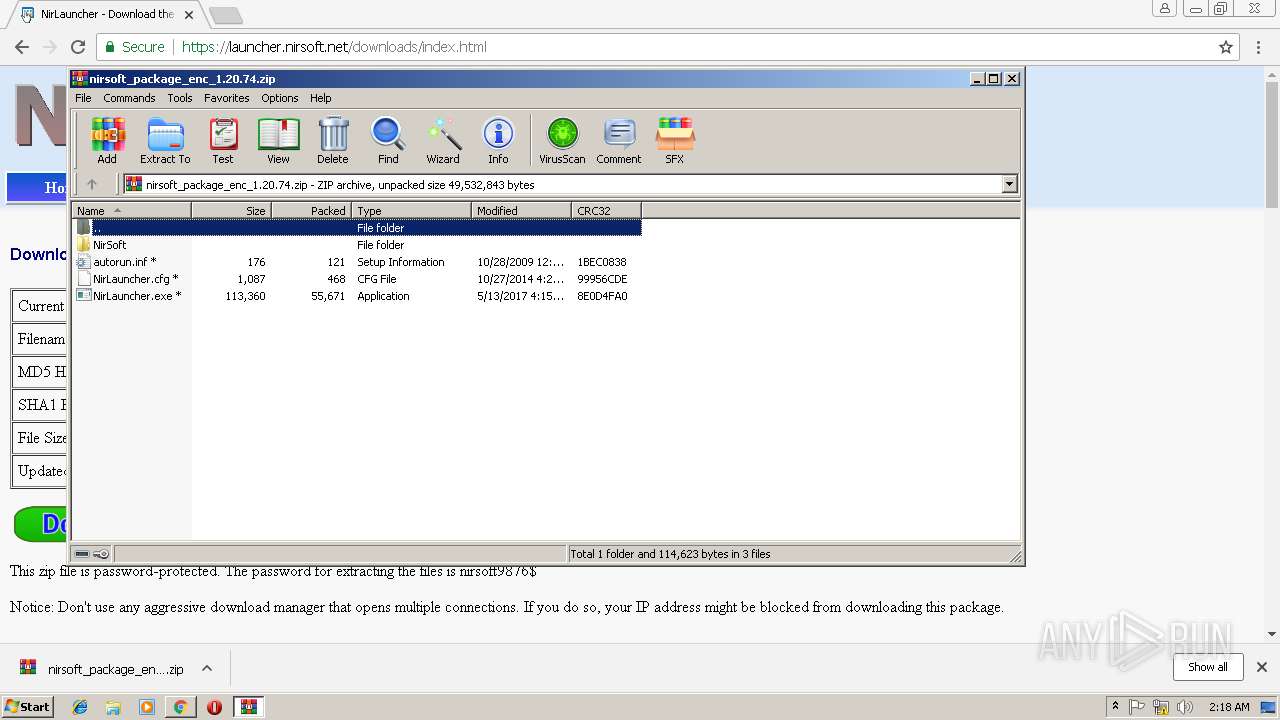
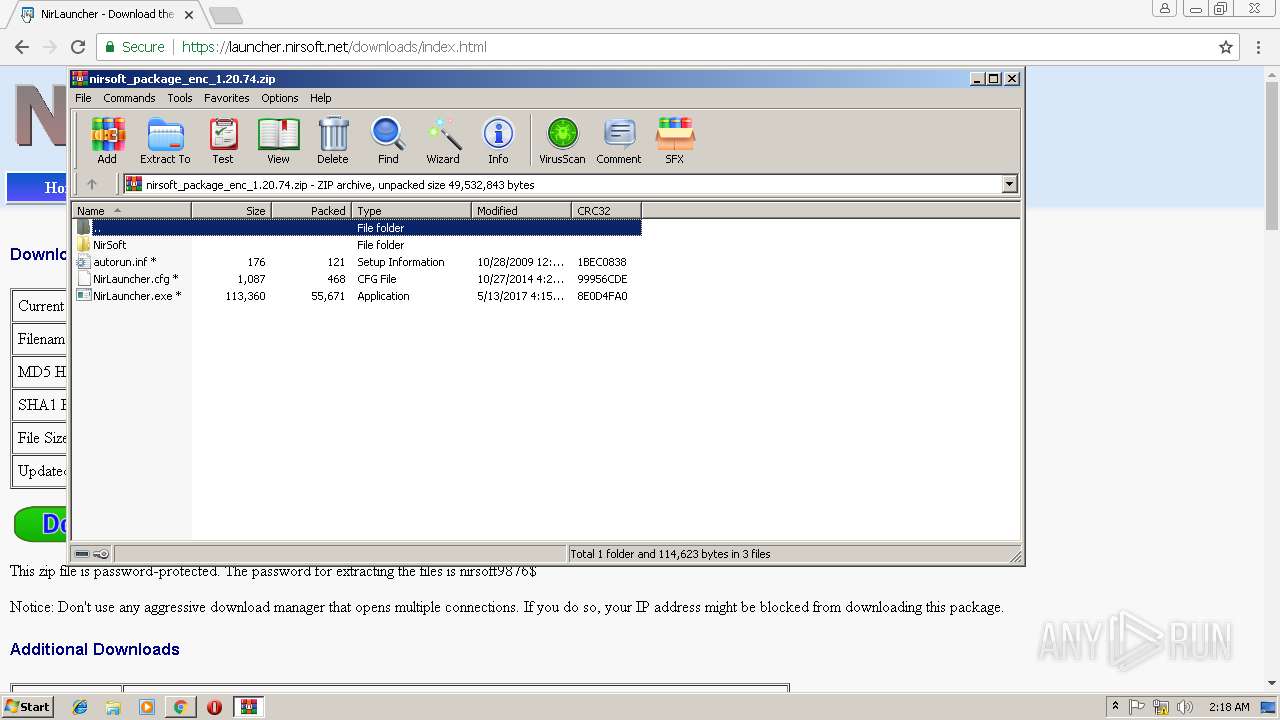
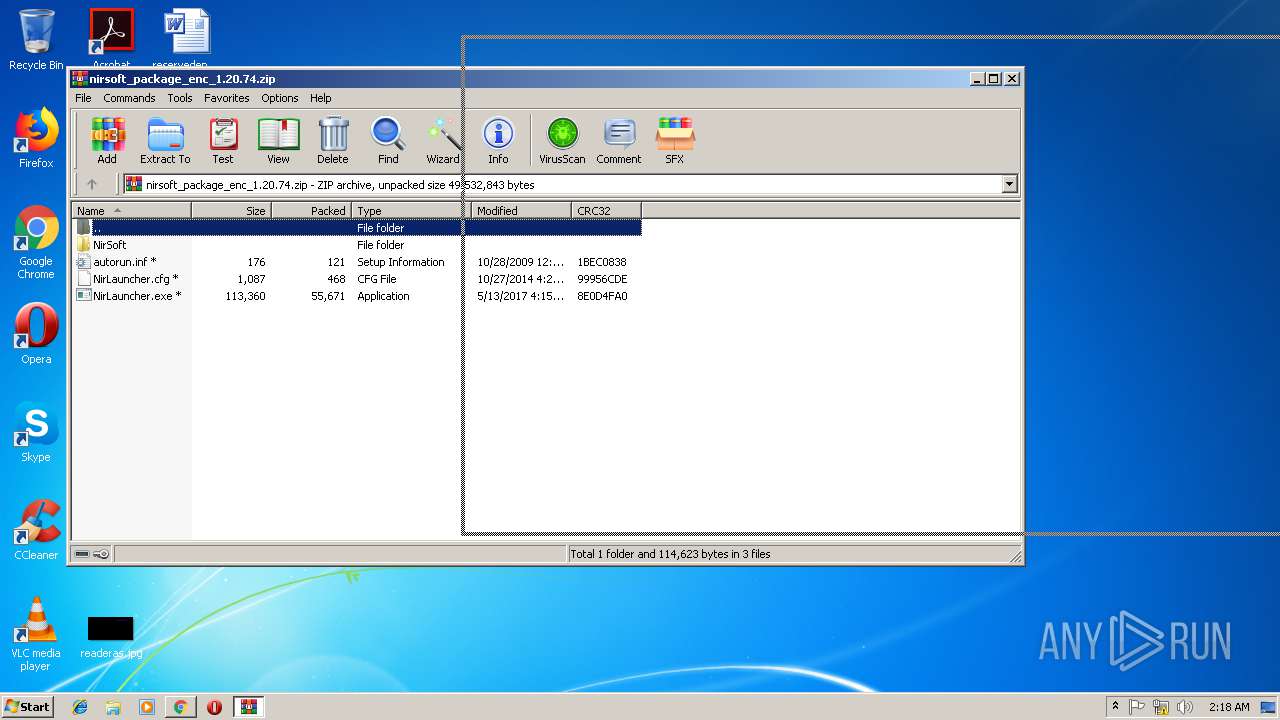
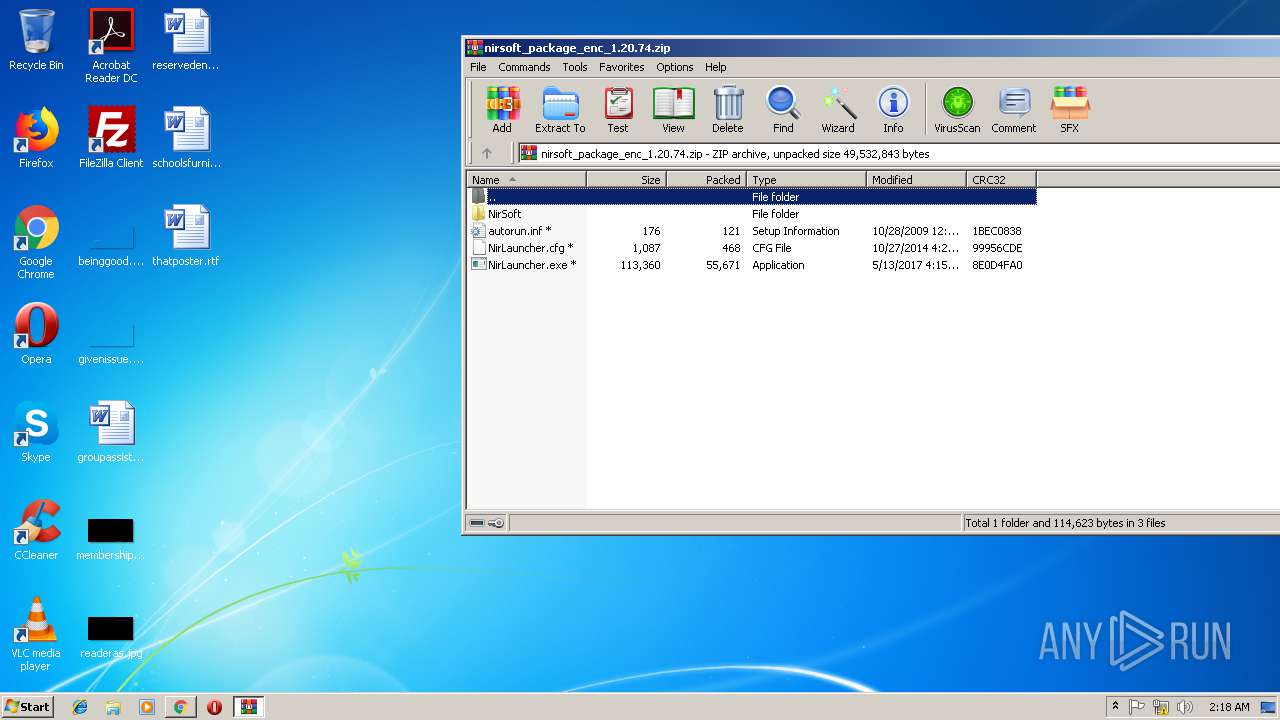
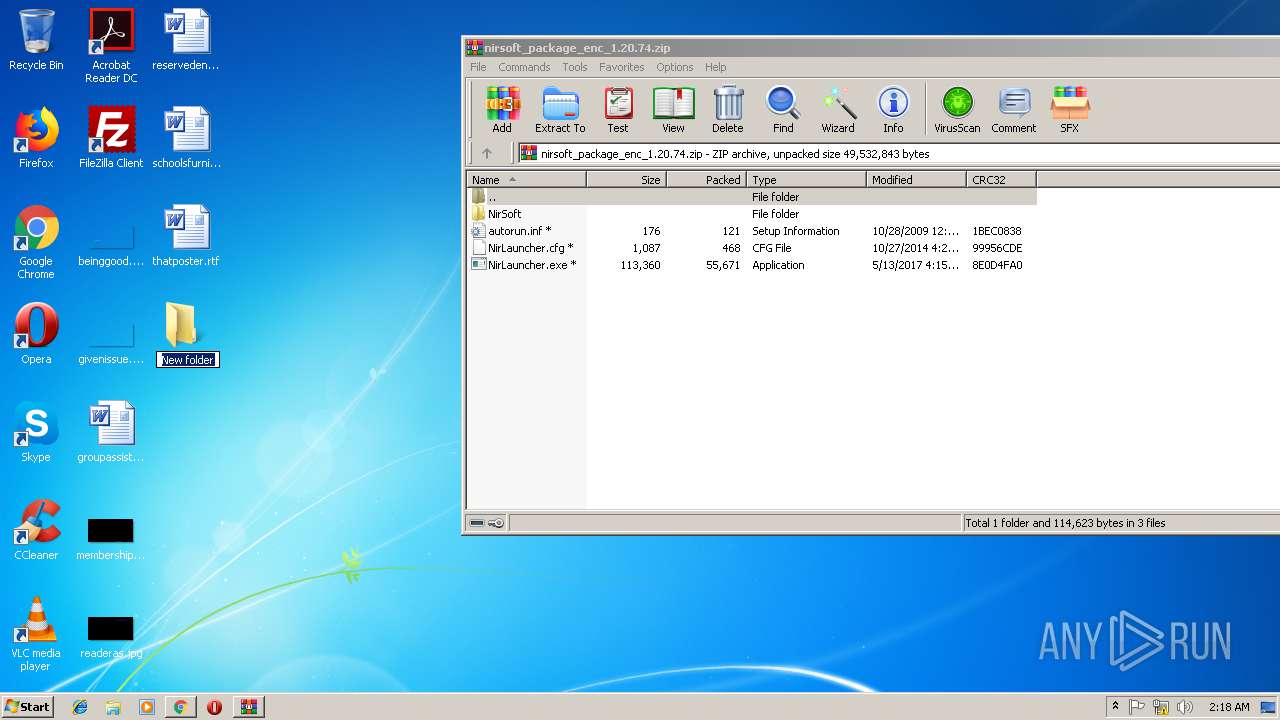
| URL: | https://download.nirsoft.net/nirsoft_package_enc_1.20.74.zip |
| Full analysis: | https://app.any.run/tasks/e515adc5-c1f6-462e-a9d3-d673972d4d03 |
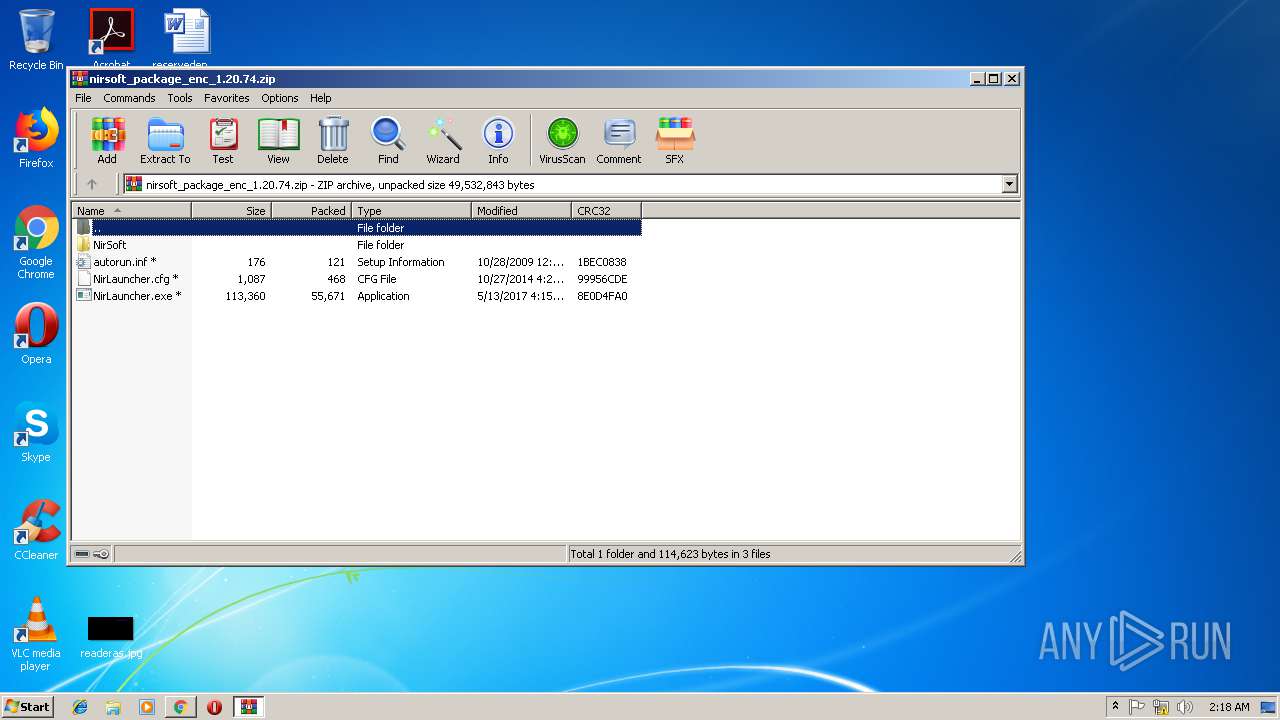
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2019, 02:16:10 |
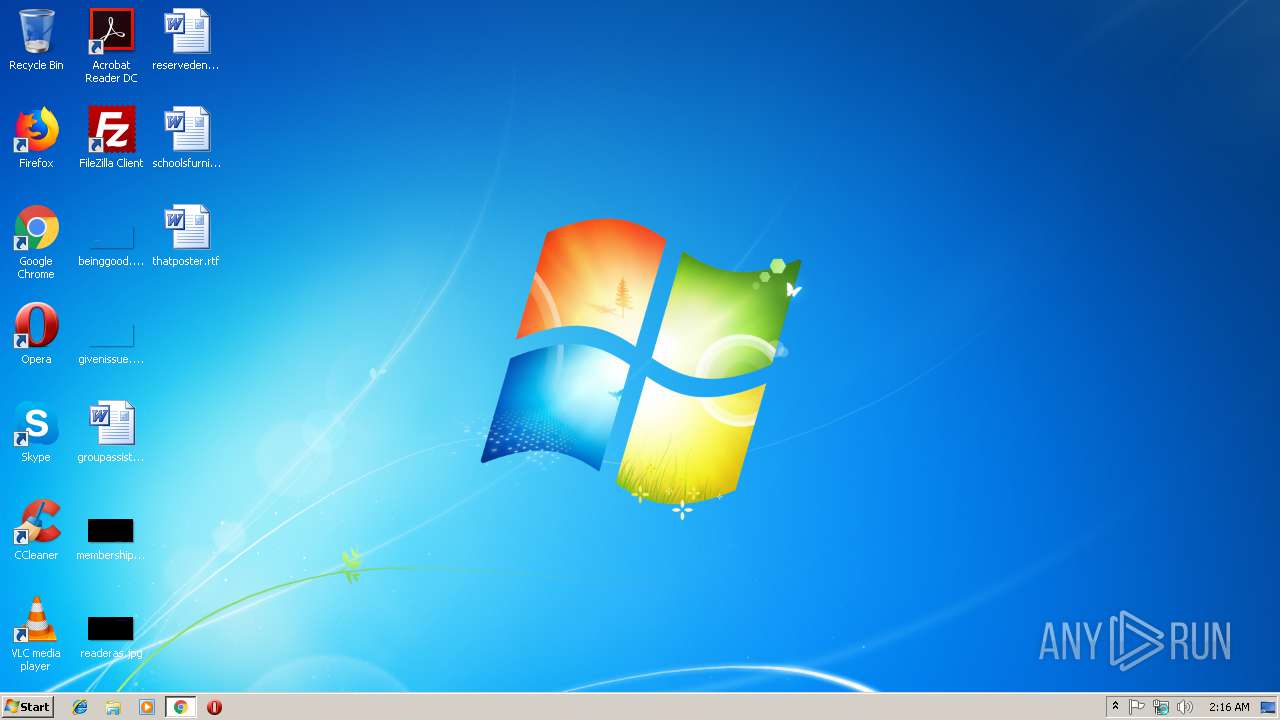
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0A92E1362418A97714A7F5991AE111B9 |
| SHA1: | 58AD3654F8B2D73525FC4AA4C75A41DF64966901 |
| SHA256: | 9CAEB425C1DD48431CE8DDAC5EEA671C6518D32D2872F07D694D887772ED7B12 |
| SSDEEP: | 3:N8SEl4XRRe37xoc:2SK+s9t |
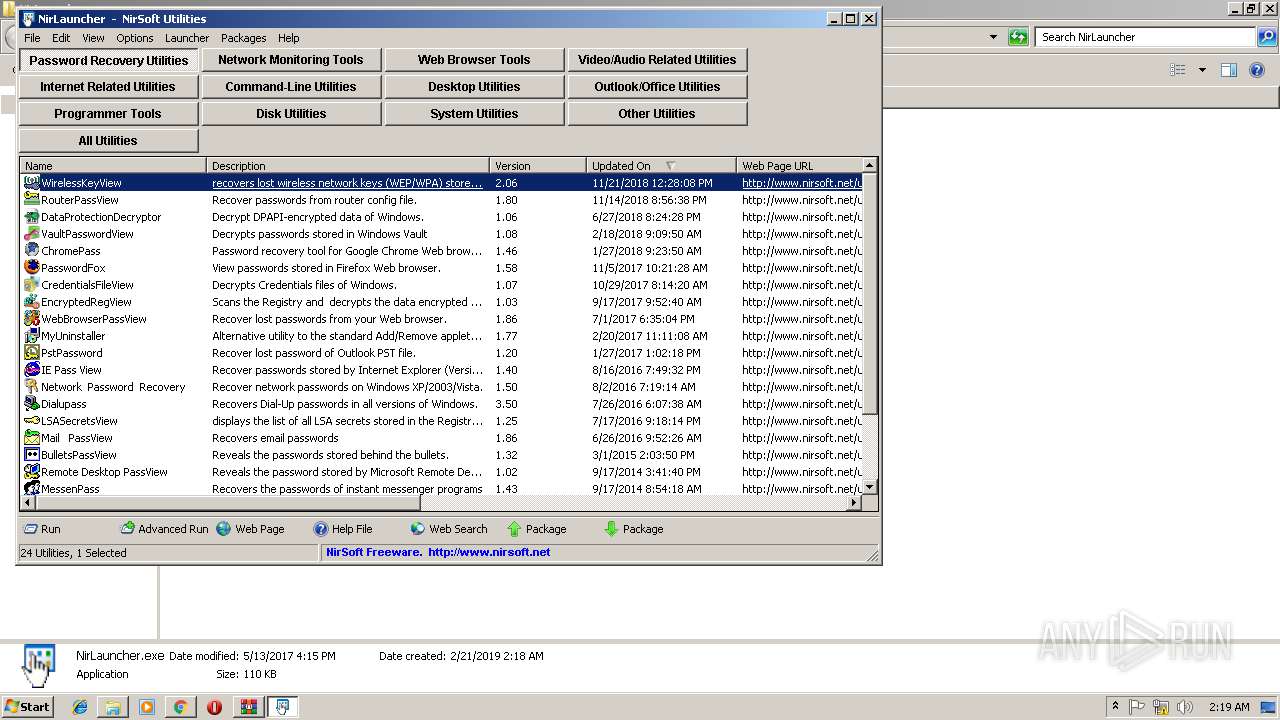
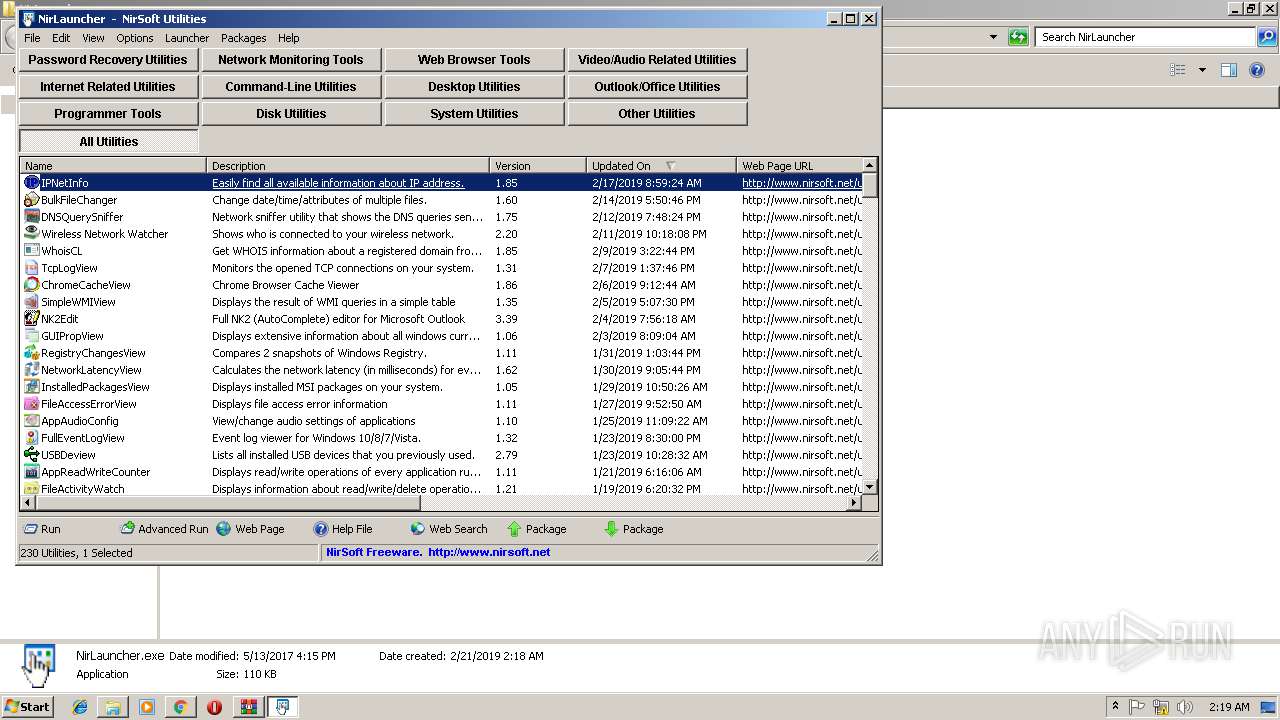
MALICIOUS
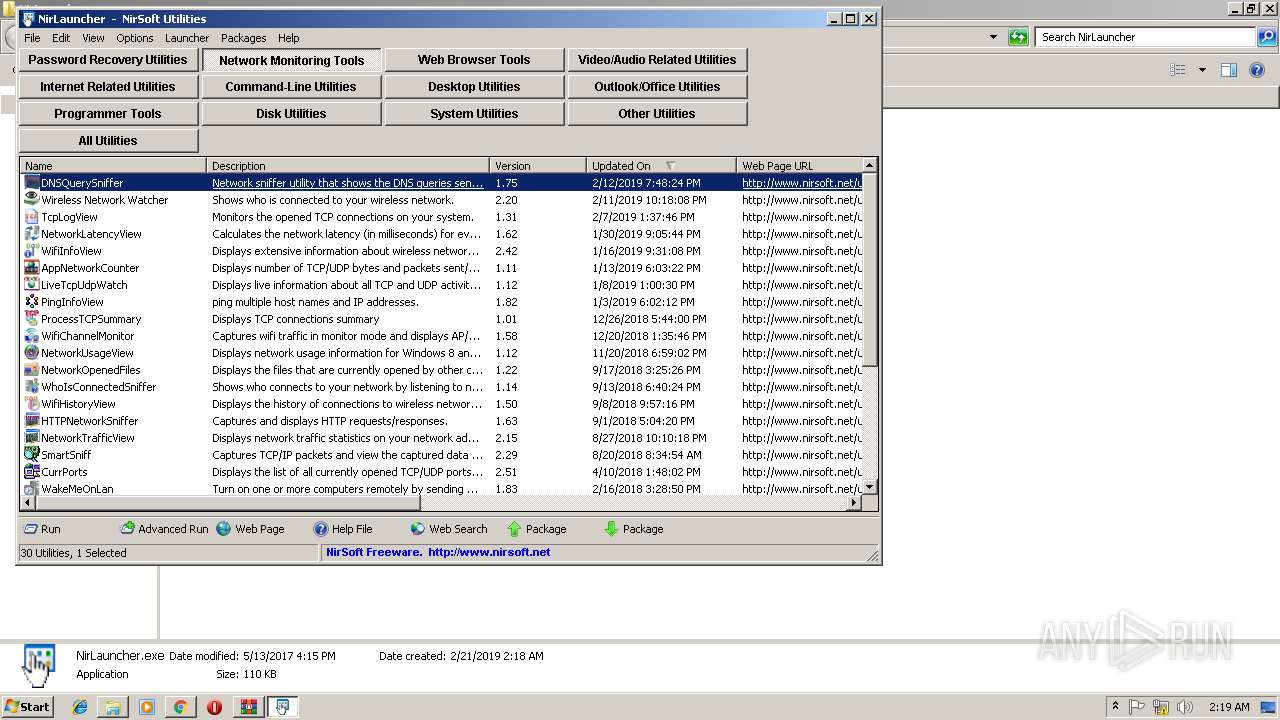
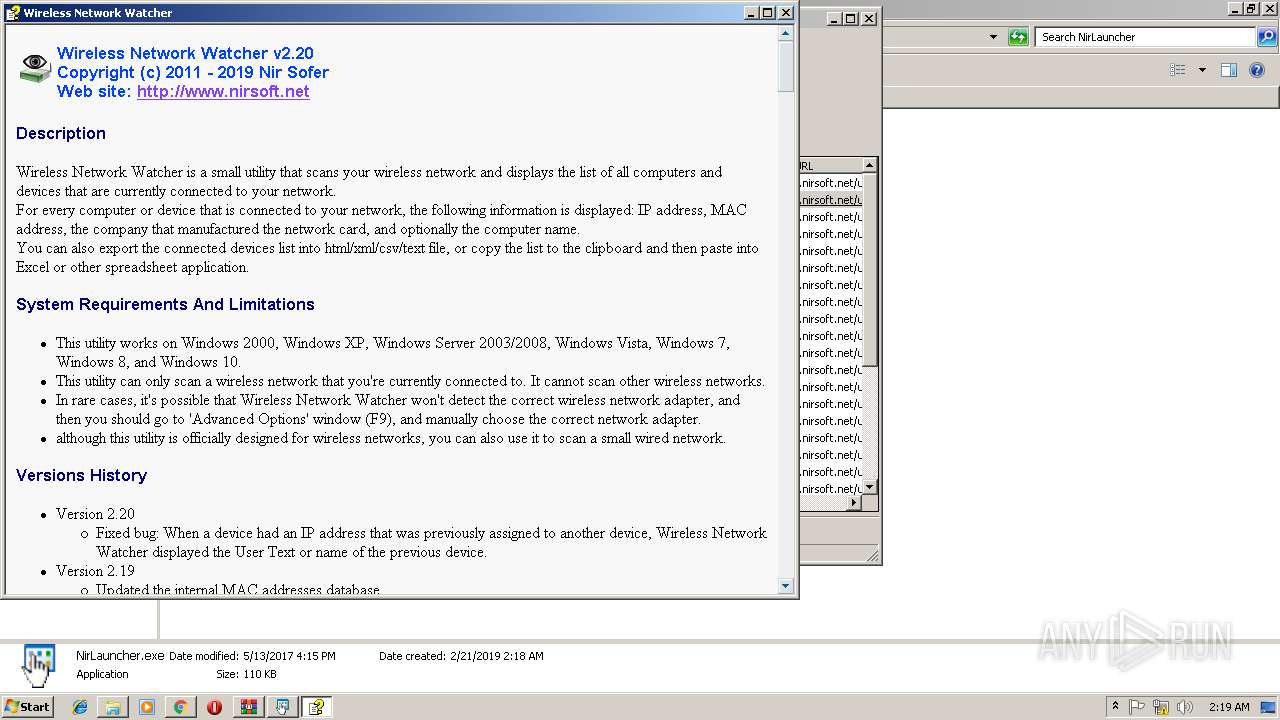
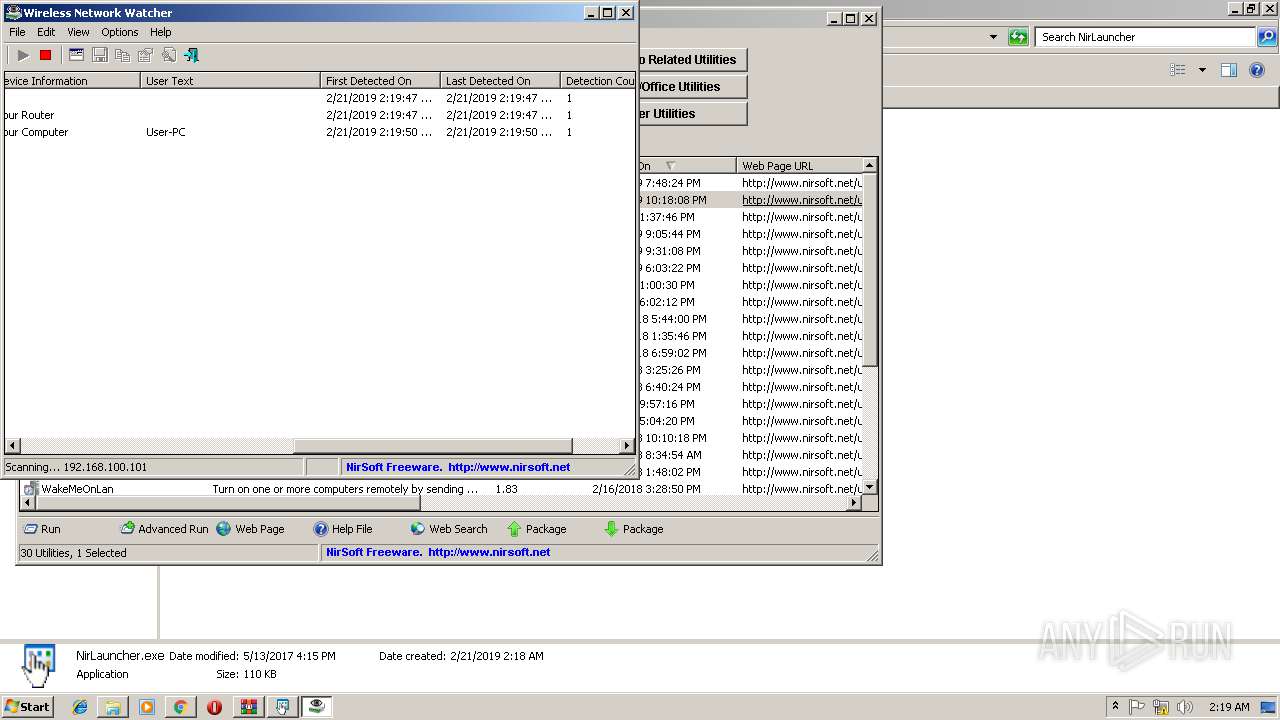
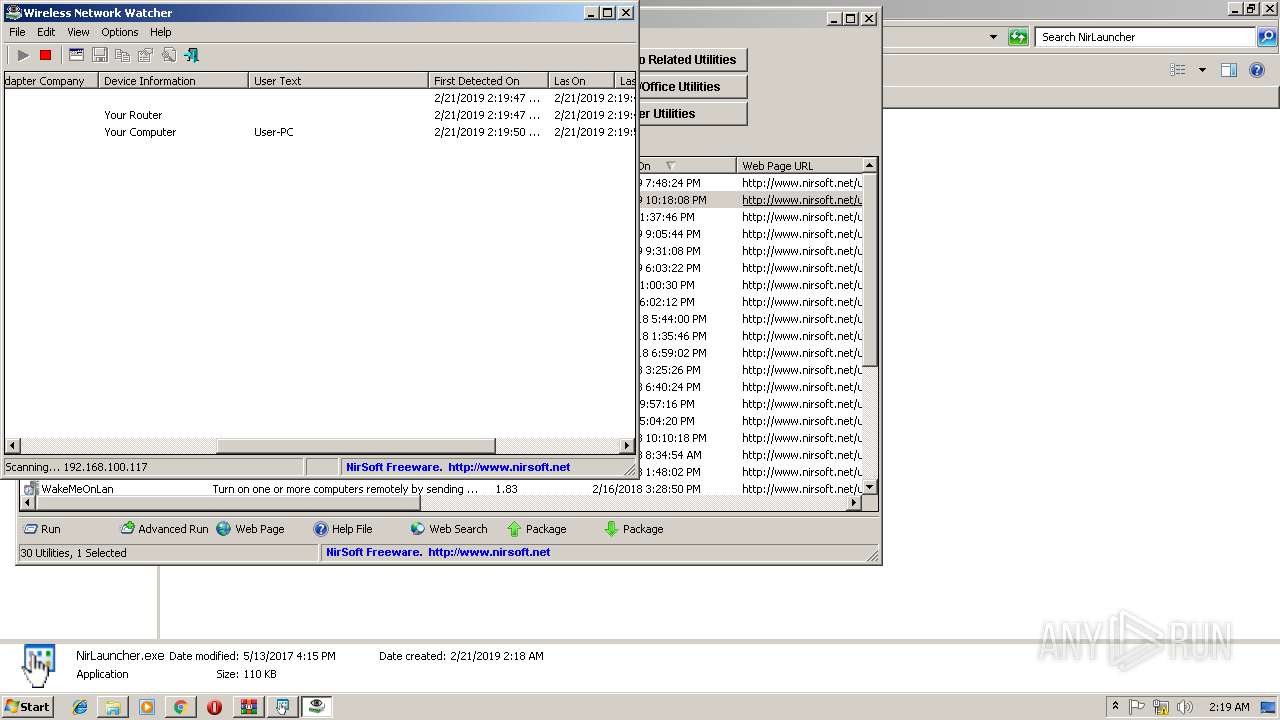
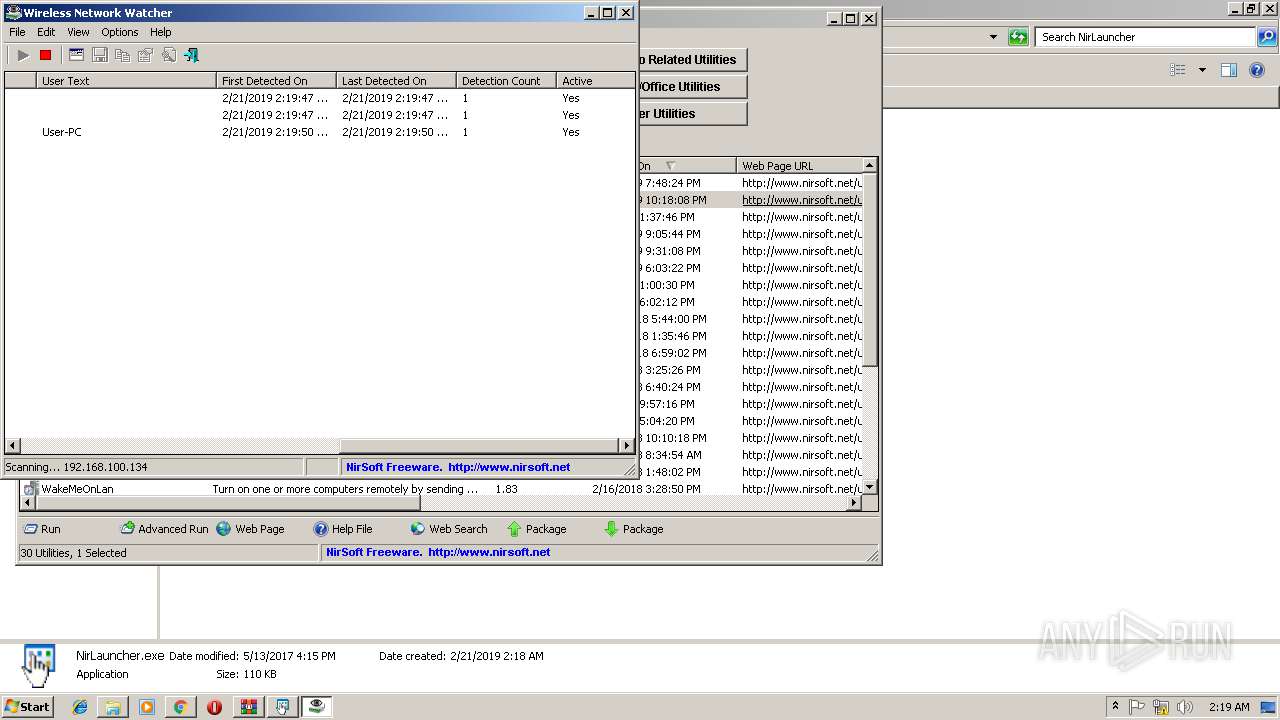
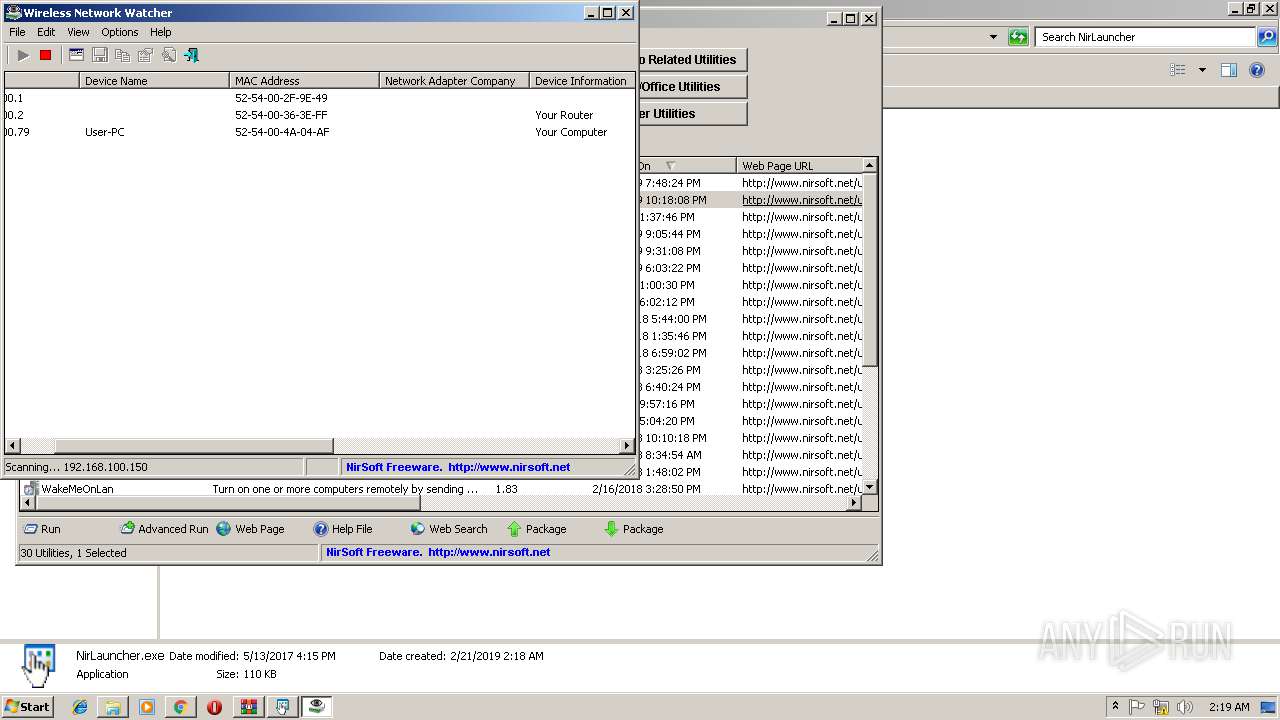
Application was dropped or rewritten from another process
- WirelessKeyView.exe (PID: 3004)
- WirelessKeyView.exe (PID: 3636)
- WNetWatcher.exe (PID: 3124)
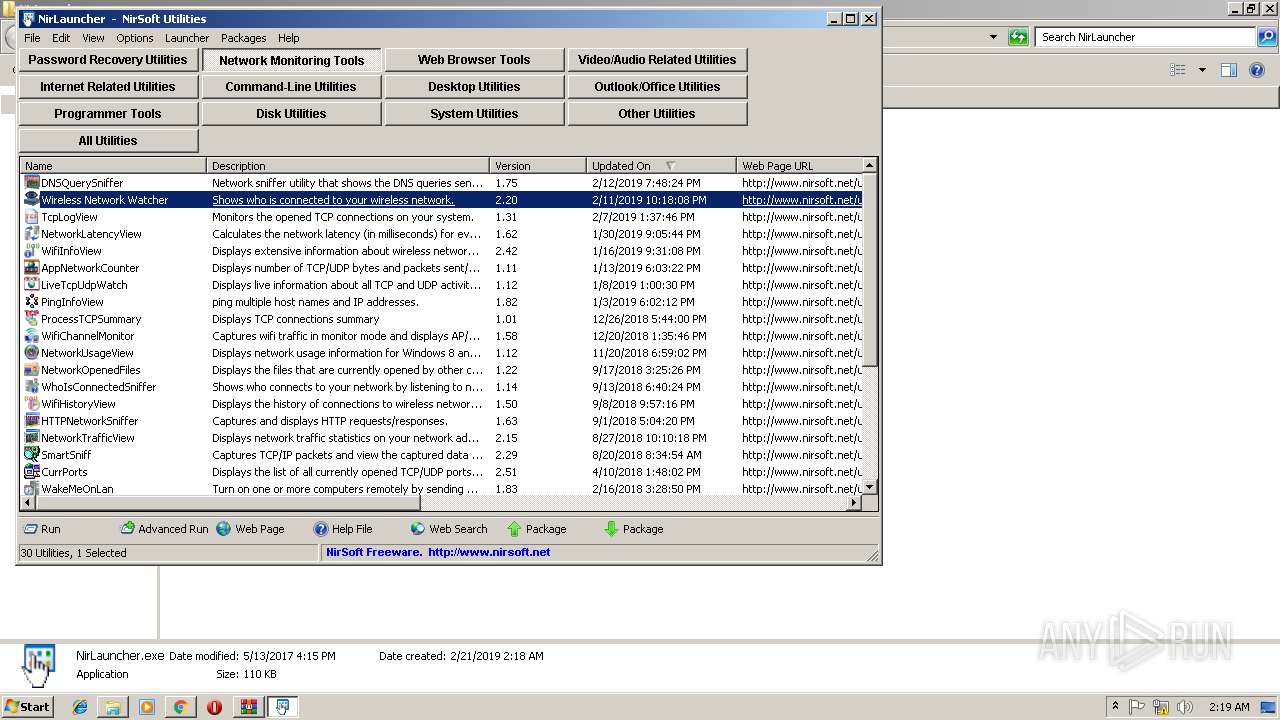
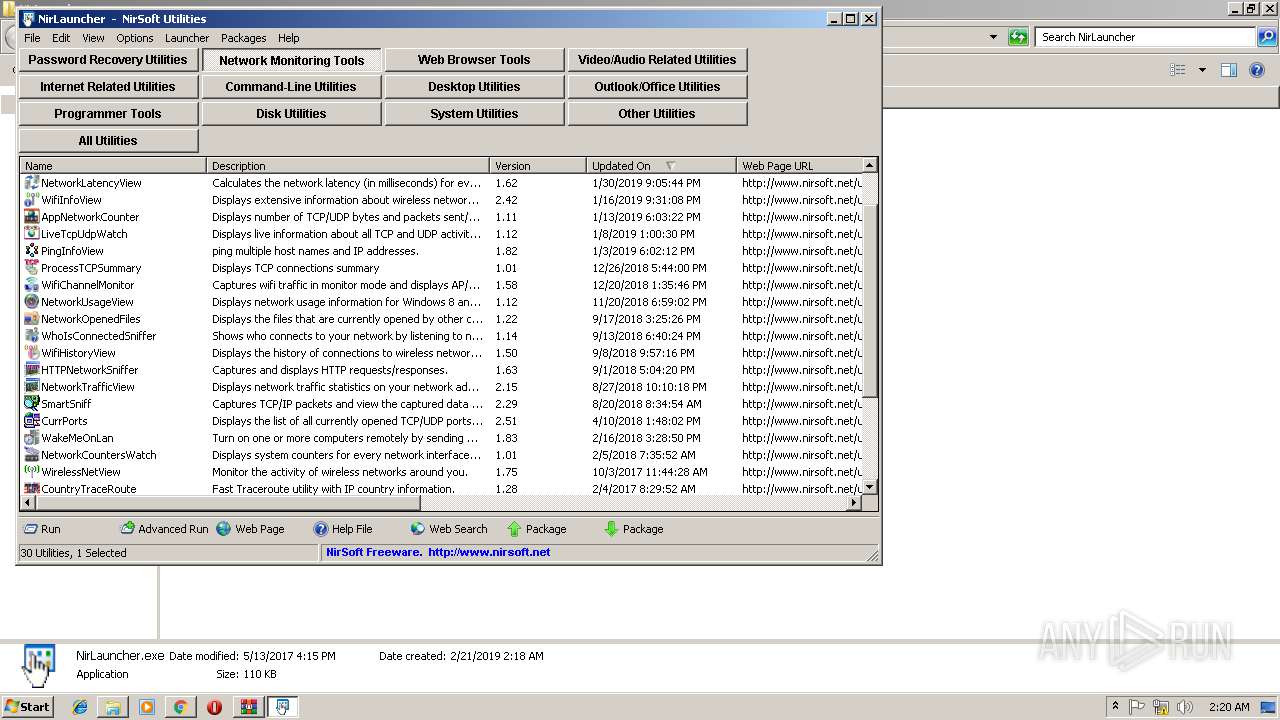
- NirLauncher.exe (PID: 3436)
- WirelessKeyView.exe (PID: 1236)
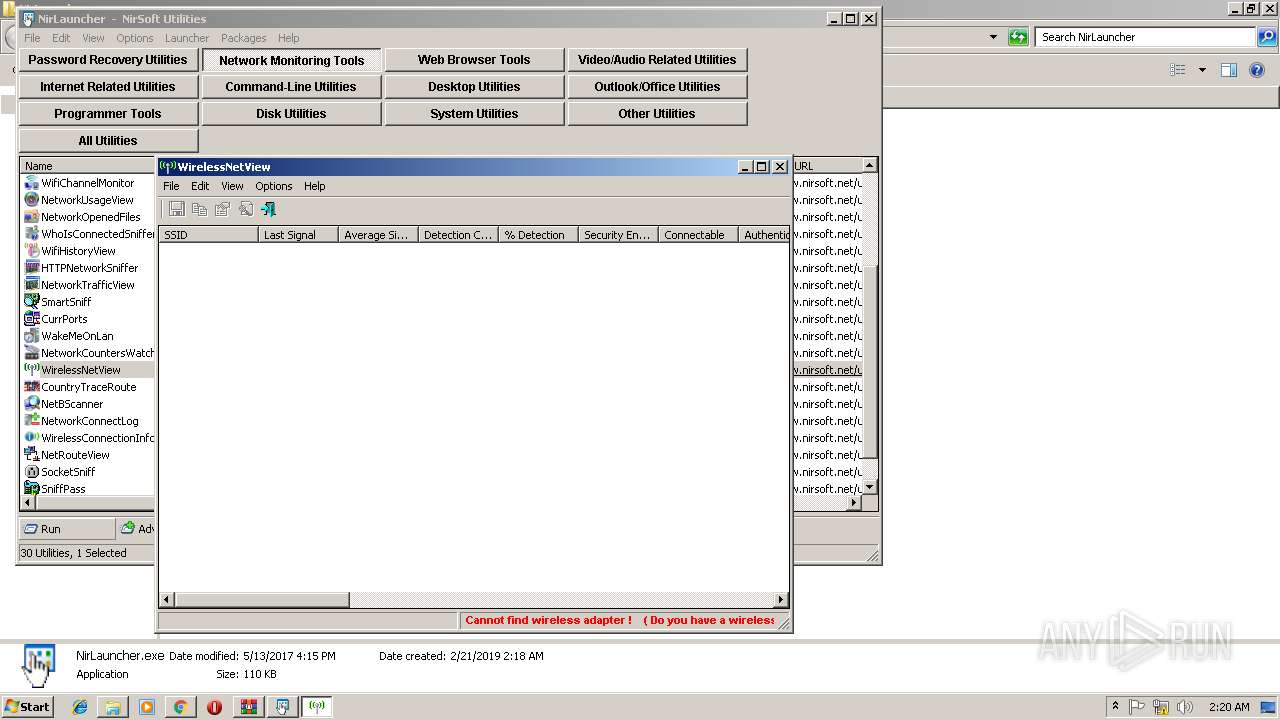
- WirelessNetView.exe (PID: 3816)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2888)
SUSPICIOUS
Reads internet explorer settings
- hh.exe (PID: 2816)
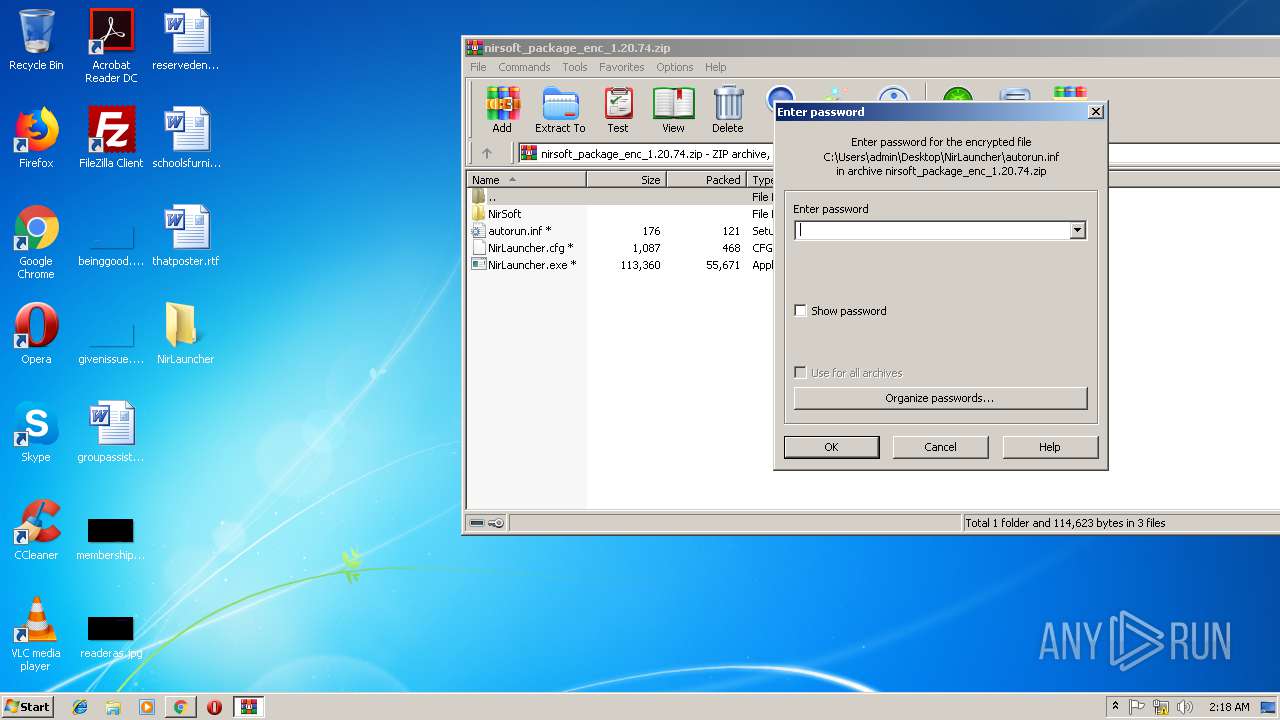
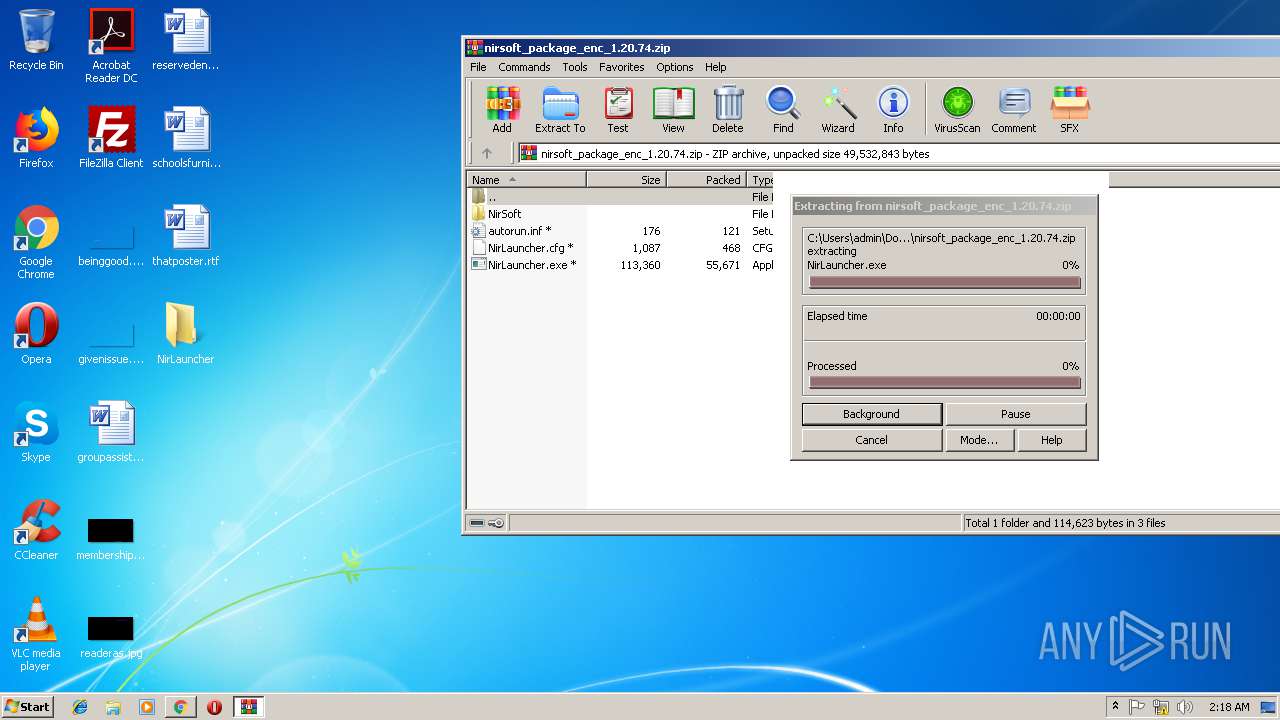
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2412)
INFO
Application launched itself
- chrome.exe (PID: 3540)
Reads Internet Cache Settings
- chrome.exe (PID: 3540)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
22
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1236 | "C:\Users\admin\Desktop\NirLauncher\NirSoft\WirelessKeyView.exe" /GetKeys WirelessKeyView001F4F51 | C:\Users\admin\Desktop\NirLauncher\NirSoft\WirelessKeyView.exe | WirelessKeyView.exe | ||||||||||||
User: SYSTEM Company: NirSoft Integrity Level: SYSTEM Description: Extracts wireless keys stored by Windows Exit code: 0 Version: 2.06 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,7358489227563244169,12394431903020360121,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=8593F8F35E58DC355323114D3D5705DE --mojo-platform-channel-handle=968 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,7358489227563244169,12394431903020360121,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=CE551A474866F14A9F00ACF3B9D6FD49 --mojo-platform-channel-handle=3476 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,7358489227563244169,12394431903020360121,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=516E5DD4B41D95559CF7BB806BE546B4 --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6feb00b0,0x6feb00c0,0x6feb00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
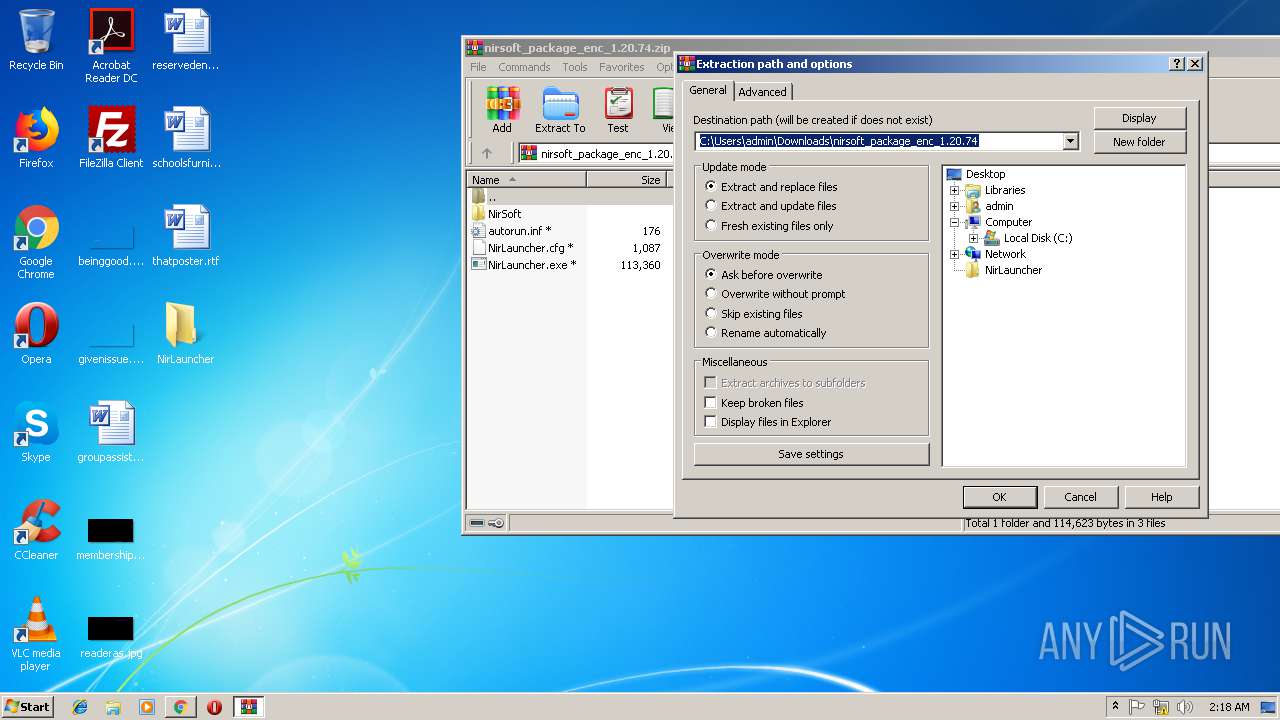
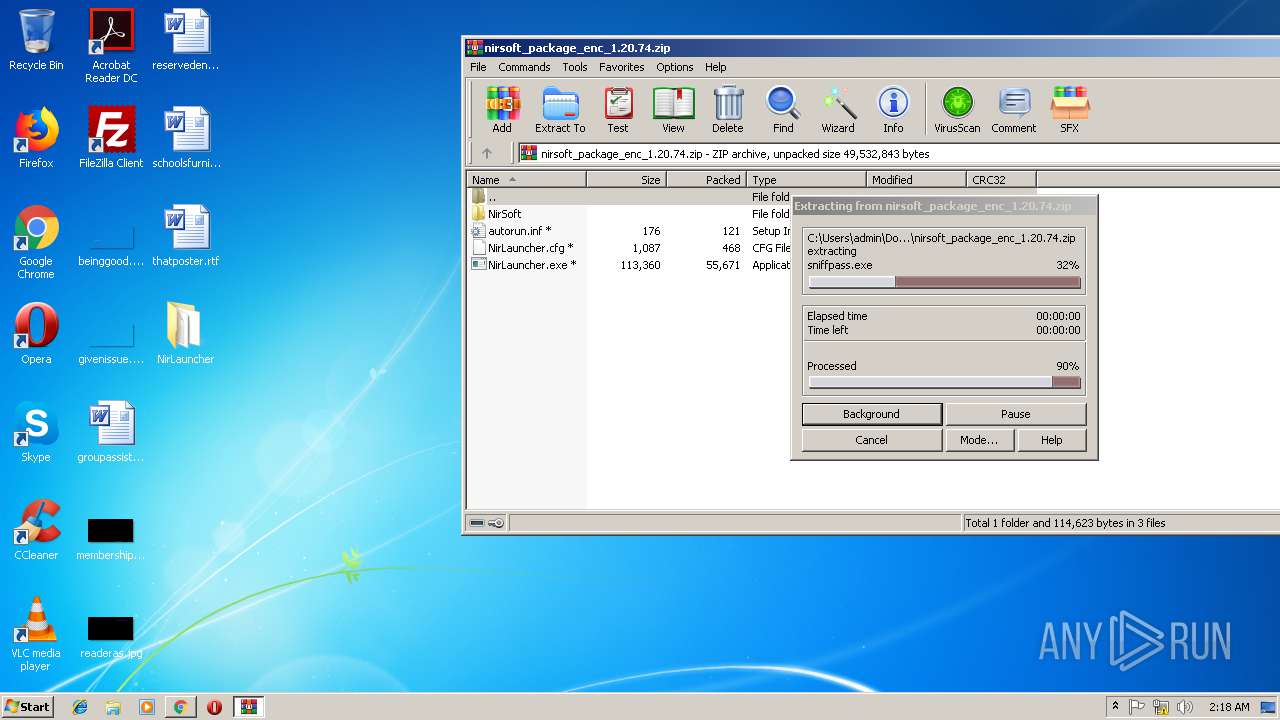
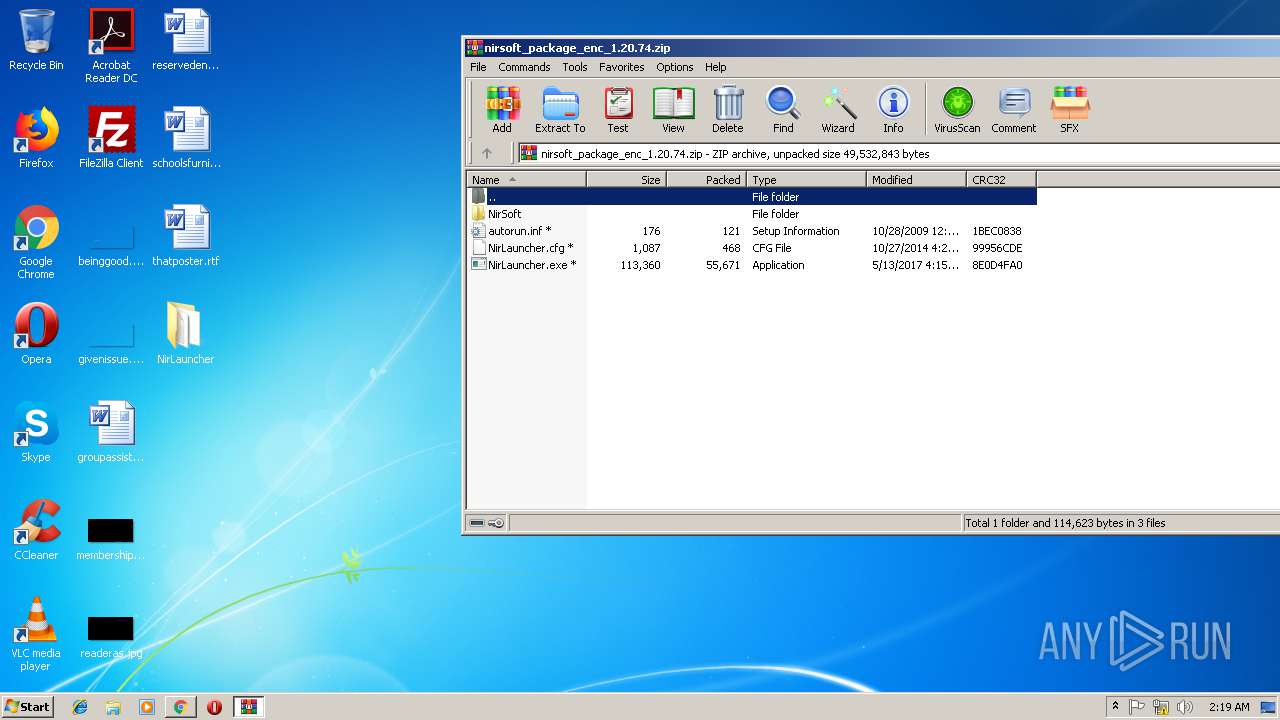
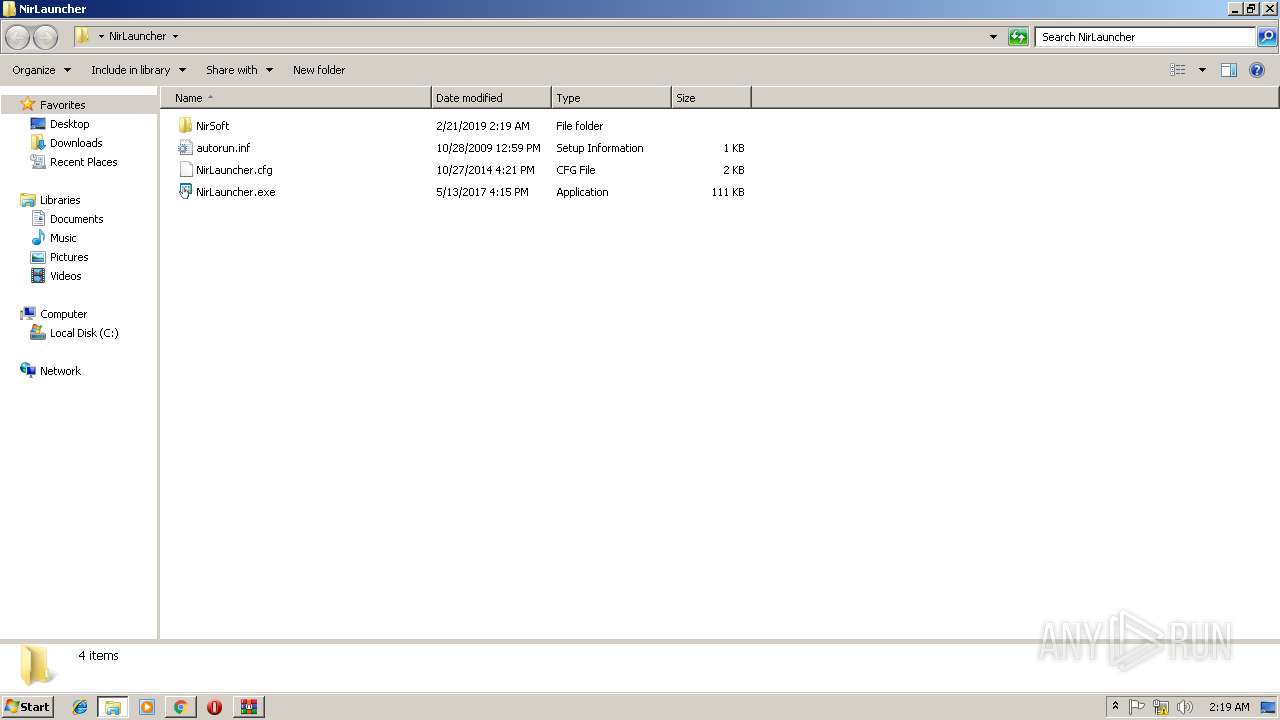
| 2412 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\nirsoft_package_enc_1.20.74.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2816 | "C:\Windows\hh.exe" C:\Users\admin\Desktop\NirLauncher\NirSoft\WNetWatcher.chm | C:\Windows\hh.exe | — | NirLauncher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2888 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe7_ Global\UsGthrCtrlFltPipeMssGthrPipe7 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,7358489227563244169,12394431903020360121,131072 --enable-features=PasswordImport --service-pipe-token=577D5794034B17475C079DB864CEBE5B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=577D5794034B17475C079DB864CEBE5B --renderer-client-id=4 --mojo-platform-channel-handle=1896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
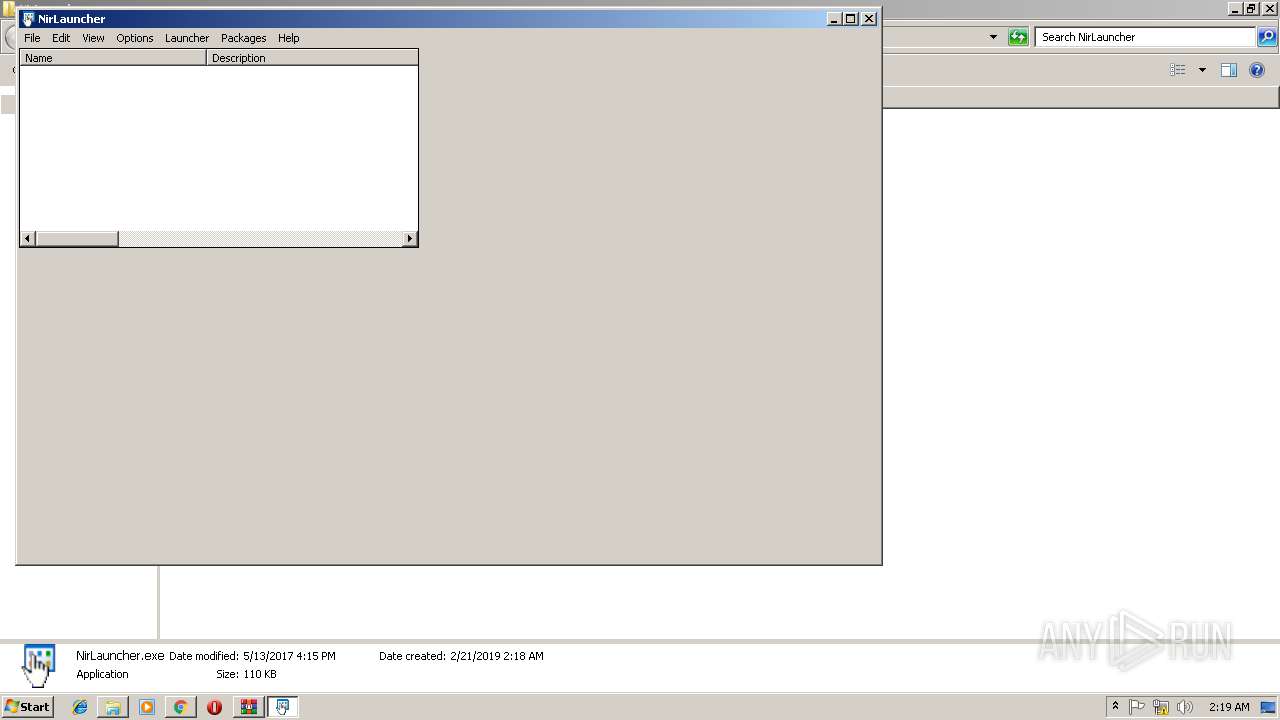
| 3004 | "C:\Users\admin\Desktop\NirLauncher\NirSoft\WirelessKeyView.exe" | C:\Users\admin\Desktop\NirLauncher\NirSoft\WirelessKeyView.exe | — | NirLauncher.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Extracts wireless keys stored by Windows Exit code: 3221226540 Version: 2.06 Modules
| |||||||||||||||
Total events
1 790
Read events
1 708
Write events
79
Delete events
3
Modification events
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3540-13195188985917500 |
Value: 259 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3540-13195188985917500 |
Value: 259 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
351
Suspicious files
62
Text files
265
Unknown types
230
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f5be564f-133c-4618-9f7f-cee17226846f.tmp | — | |
MD5:— | SHA256:— | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3ba0f59d-5b37-40bd-9a04-ddad4388edb6.tmp | — | |
MD5:— | SHA256:— | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1ae38b.TMP | text | |
MD5:92BE6B127E72365885AD4C3FB6534EE2 | SHA256:54302A2573ACC775720E7DB0AD85873276713302B4F72596A8DCC44B01C70E51 | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model | binary | |
MD5:33EE2CBF9AF5DB8AF82579A588224E98 | SHA256:6F0B1138BCF40CB883A88A02F6477AC70E17EBE245981CF39D40C8D38ED2E19F | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:C10EBD4DB49249EFC8D112B2920D5F73 | SHA256:90A1B994CAFE902F22A88A22C0B6CC9CB5B974BF20F8964406DD7D6C9B8867D1 | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:EDD71DD3BADE6CD69FF623E1CCF7012D | SHA256:BEFEA596B4676CCF7CC37EA8048044BFA0556C8931D76FDEEB693D20264E50D6 | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF1ae3ba.TMP | text | |
MD5:1AA66EFDB743FB0A8DCC1CD79B0B6542 | SHA256:28D56532CCED7375A2A1C7731E57C1A1C2EC1AC9827F3E5BEEE7F8069A5F87DD | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
61
DNS requests
33
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3540 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
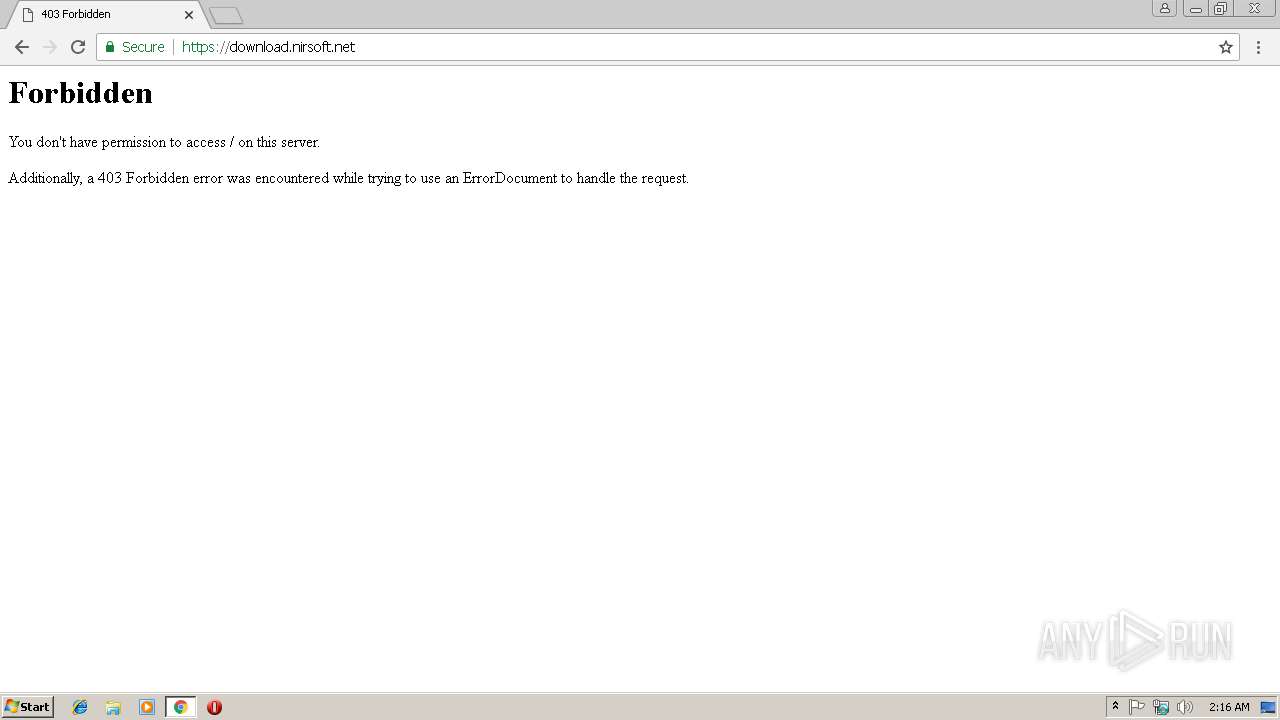
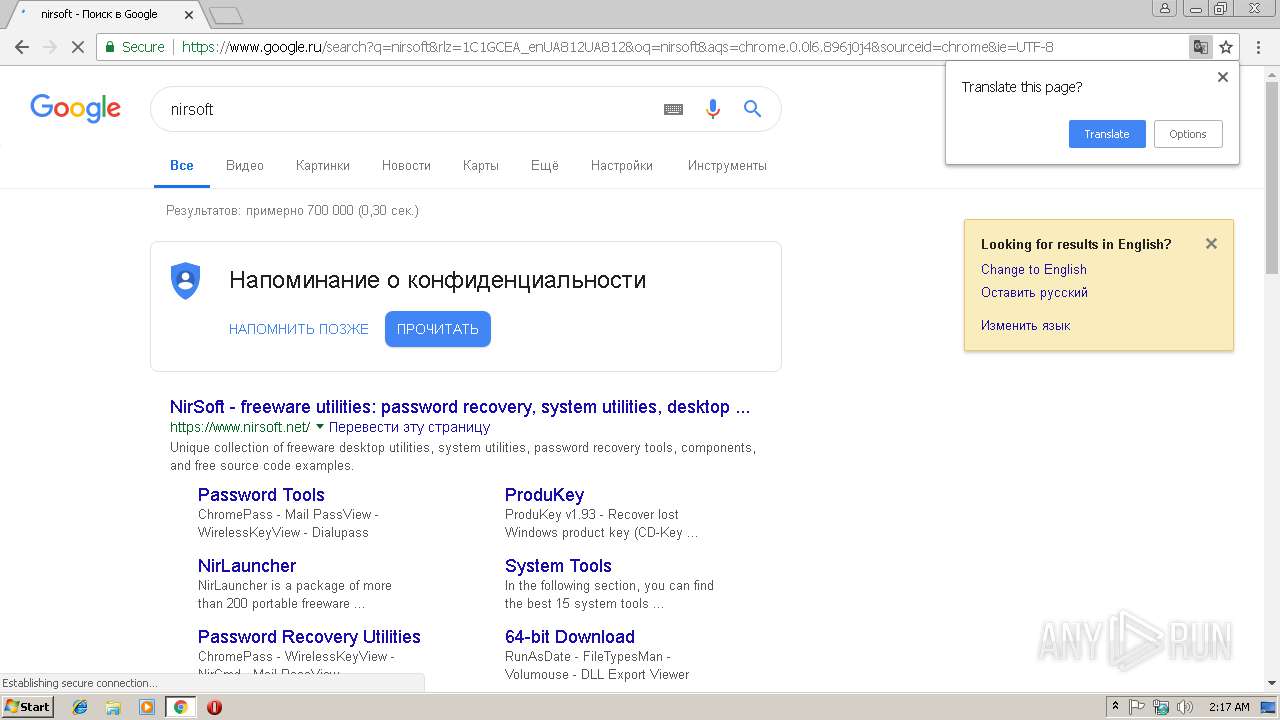
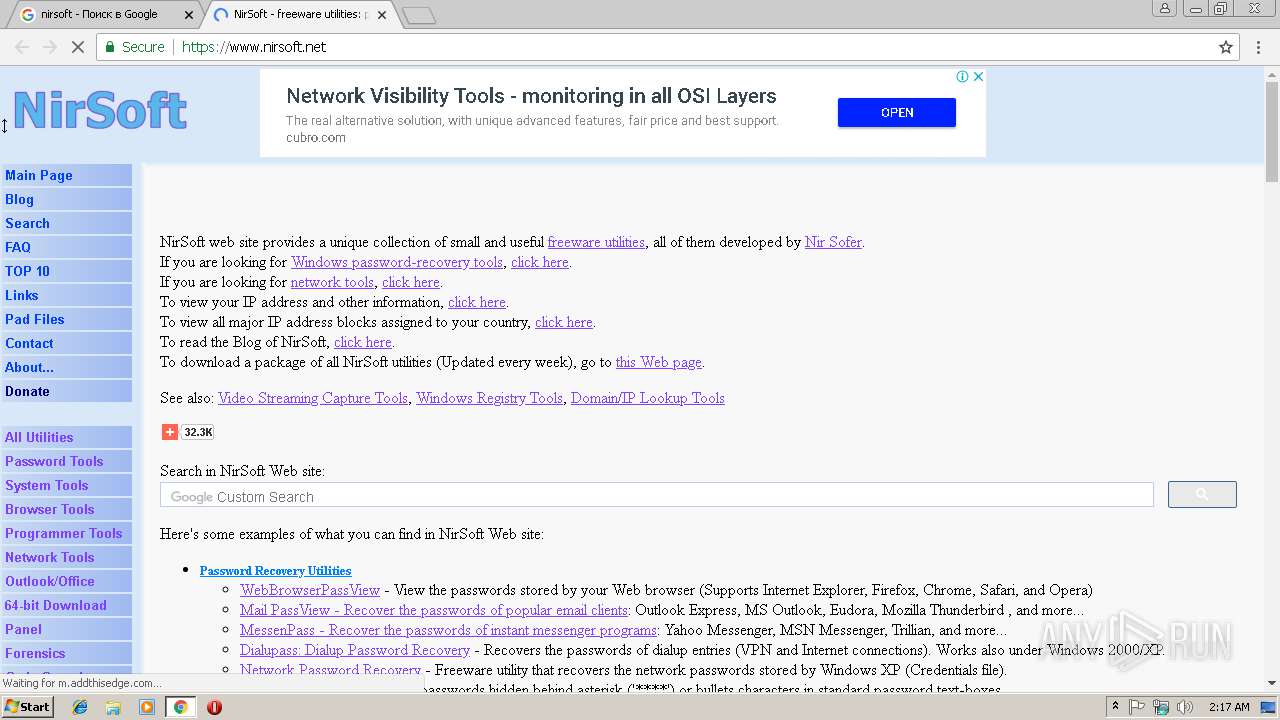
3540 | chrome.exe | 138.128.181.26:443 | download.nirsoft.net | HostDime.com, Inc. | US | suspicious |
3540 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.22.74:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.22.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.22.110:443 | consent.google.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 216.58.207.78:443 | apis.google.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 216.58.205.226:443 | adservice.google.ru | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
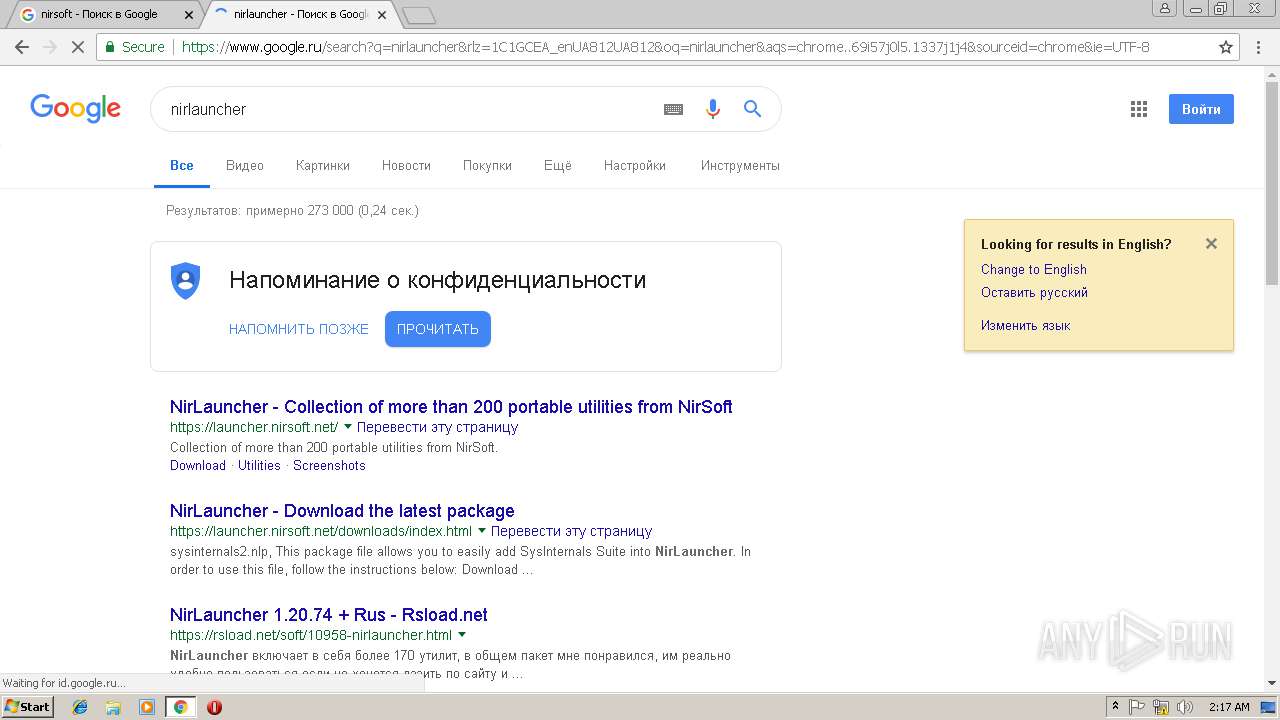
download.nirsoft.net |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
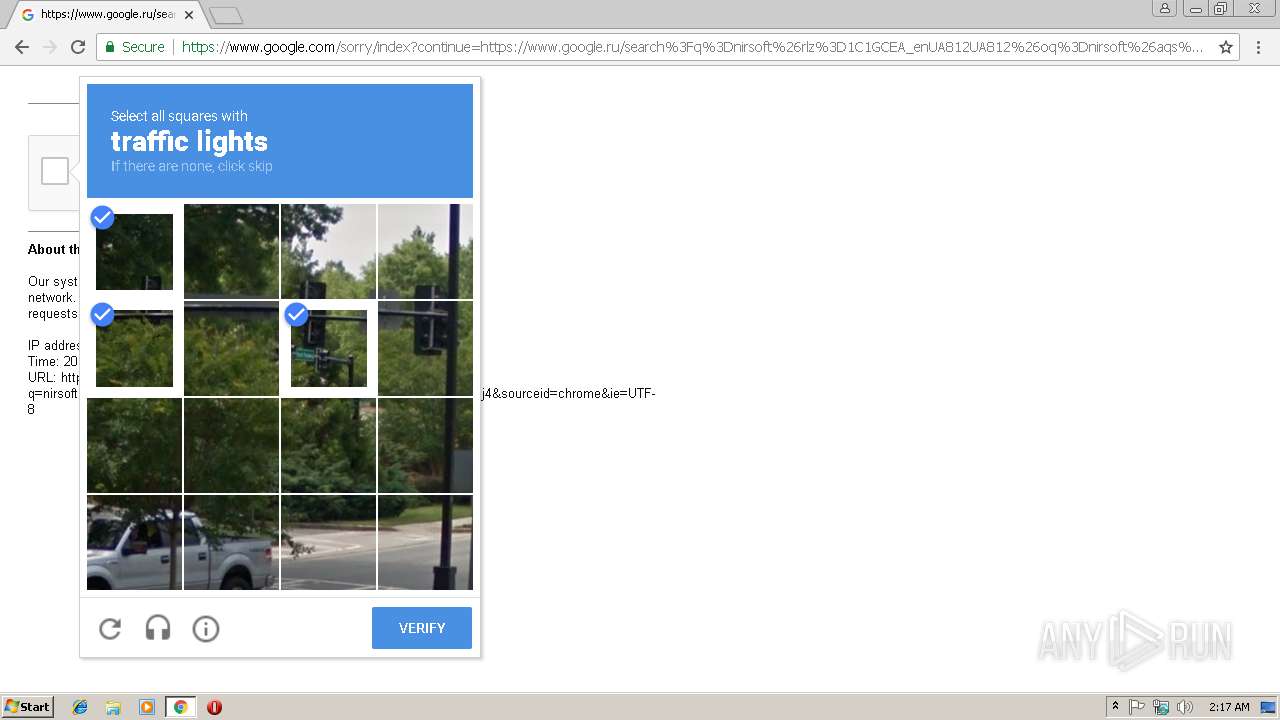
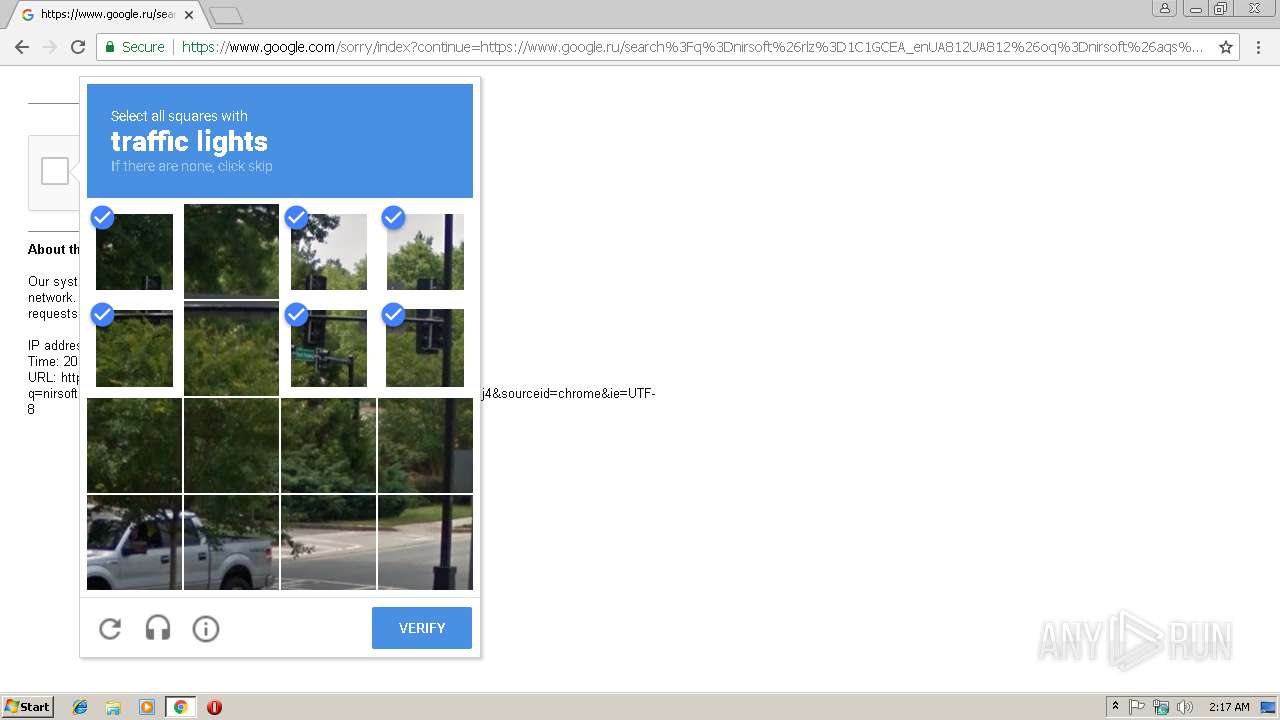
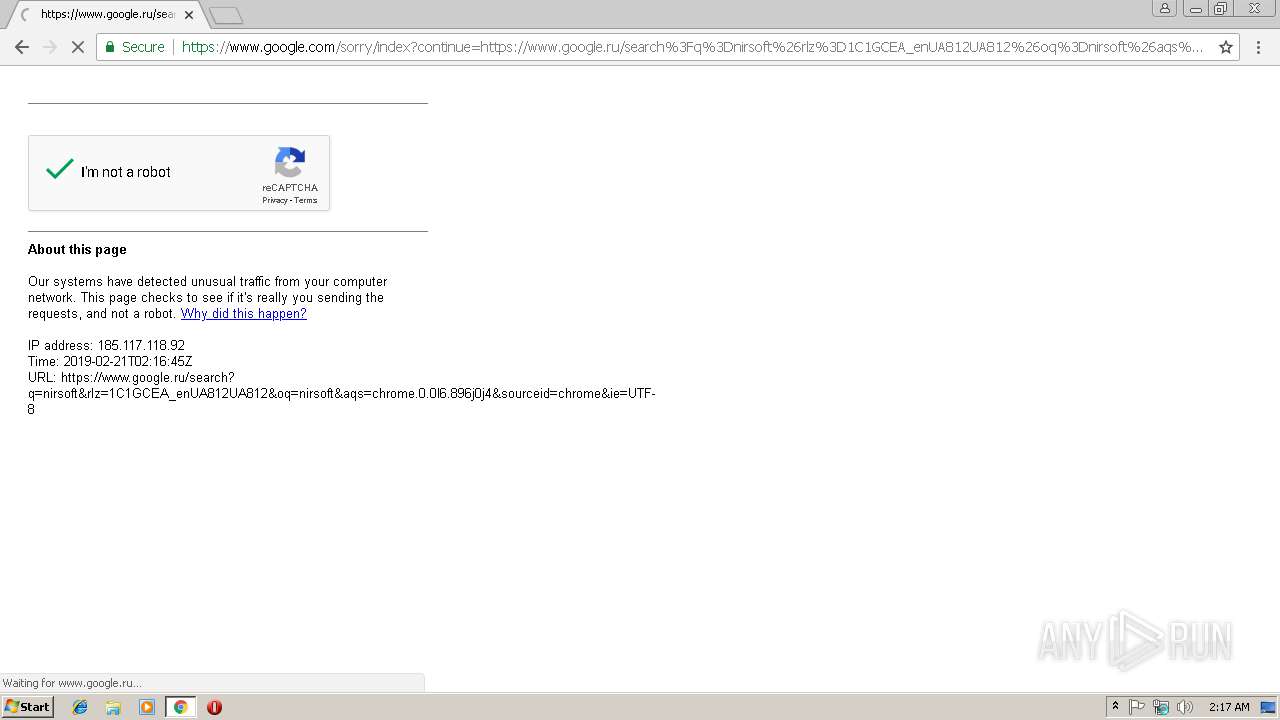
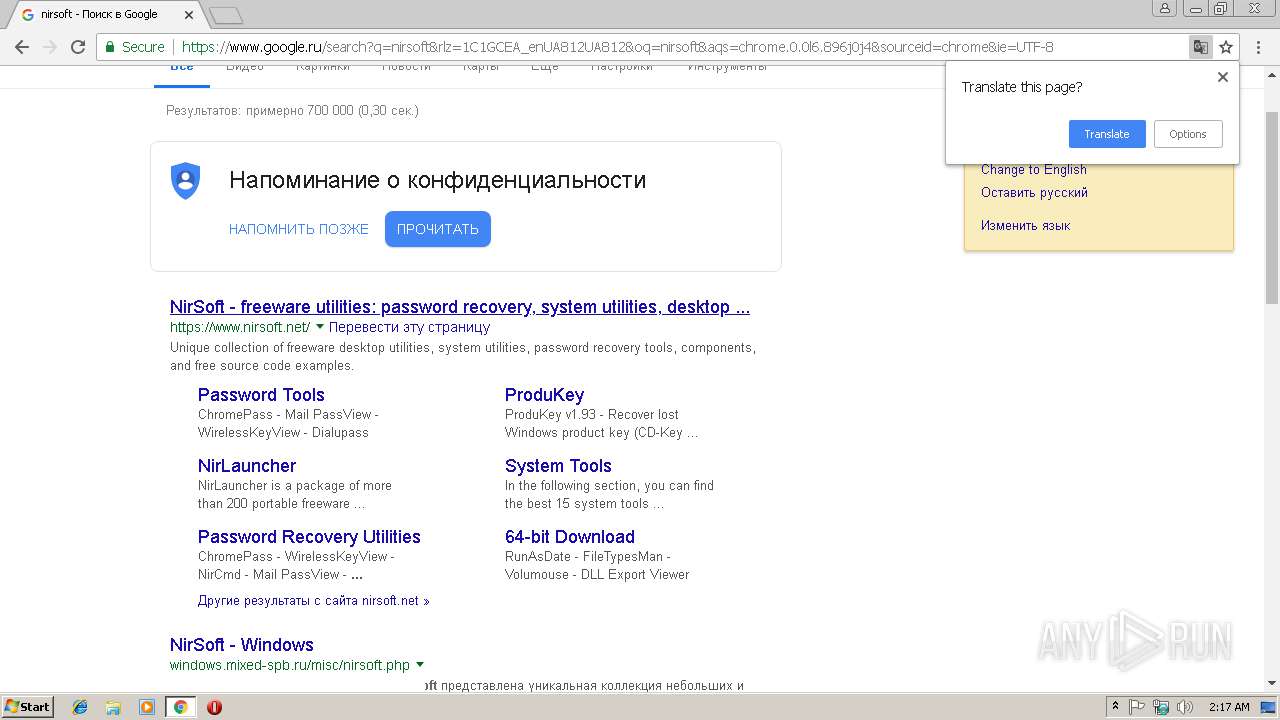
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
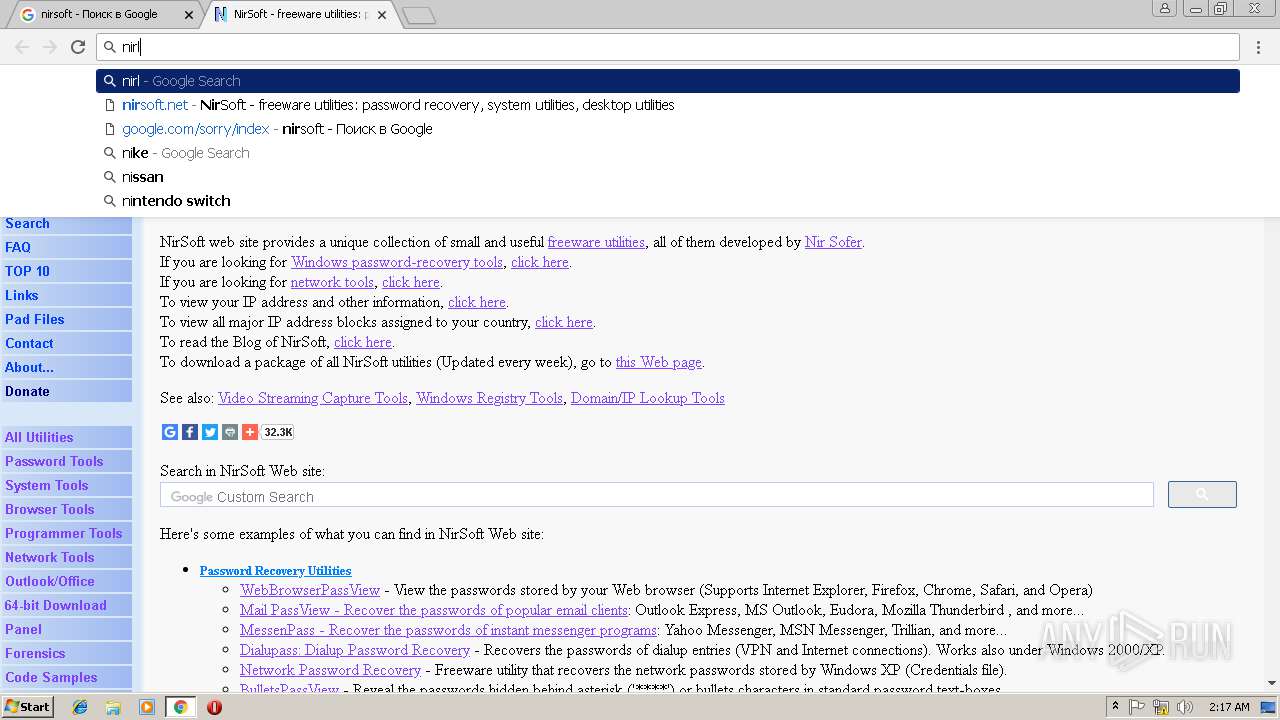
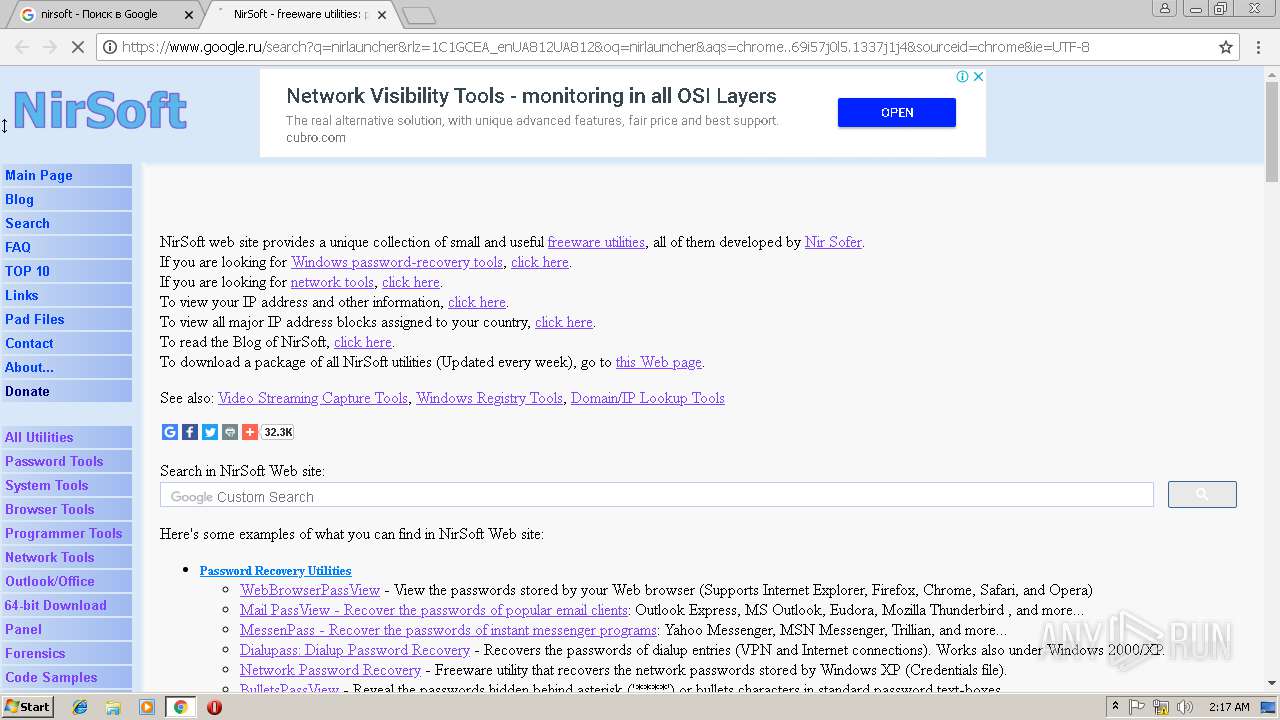
www.google.ru |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
consent.google.com |
| shared |
translate.googleapis.com |
| whitelisted |