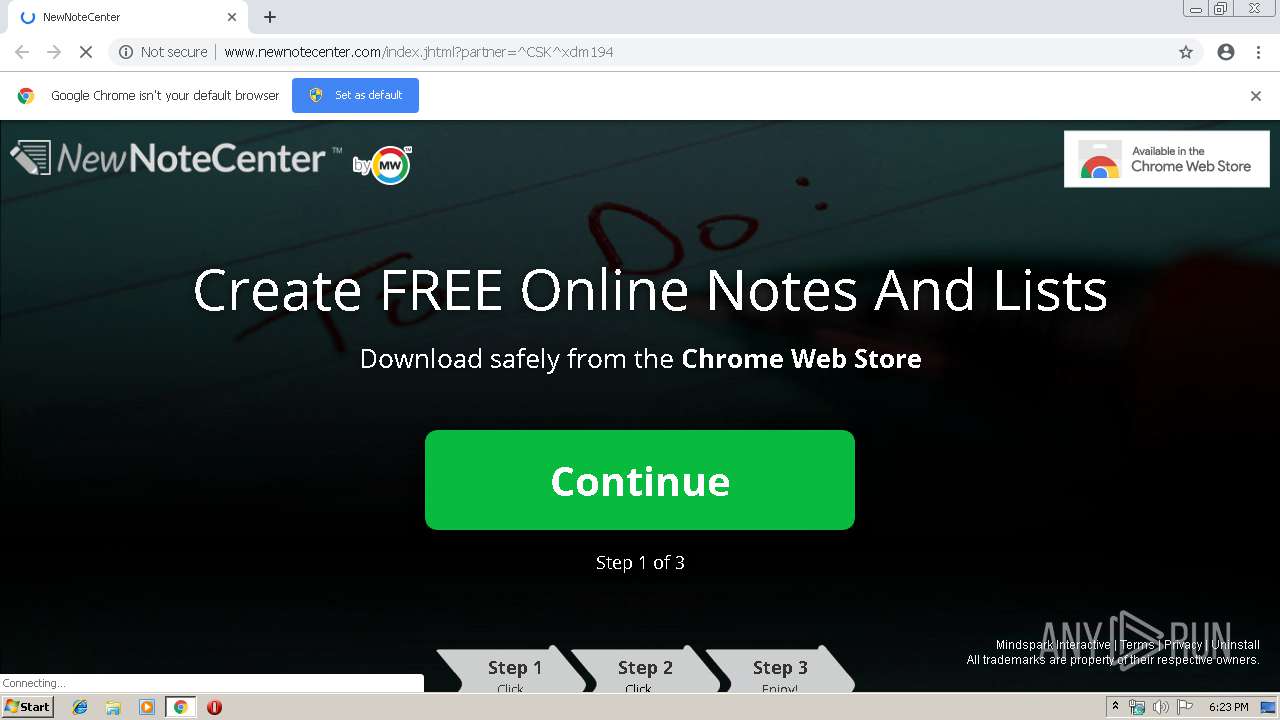
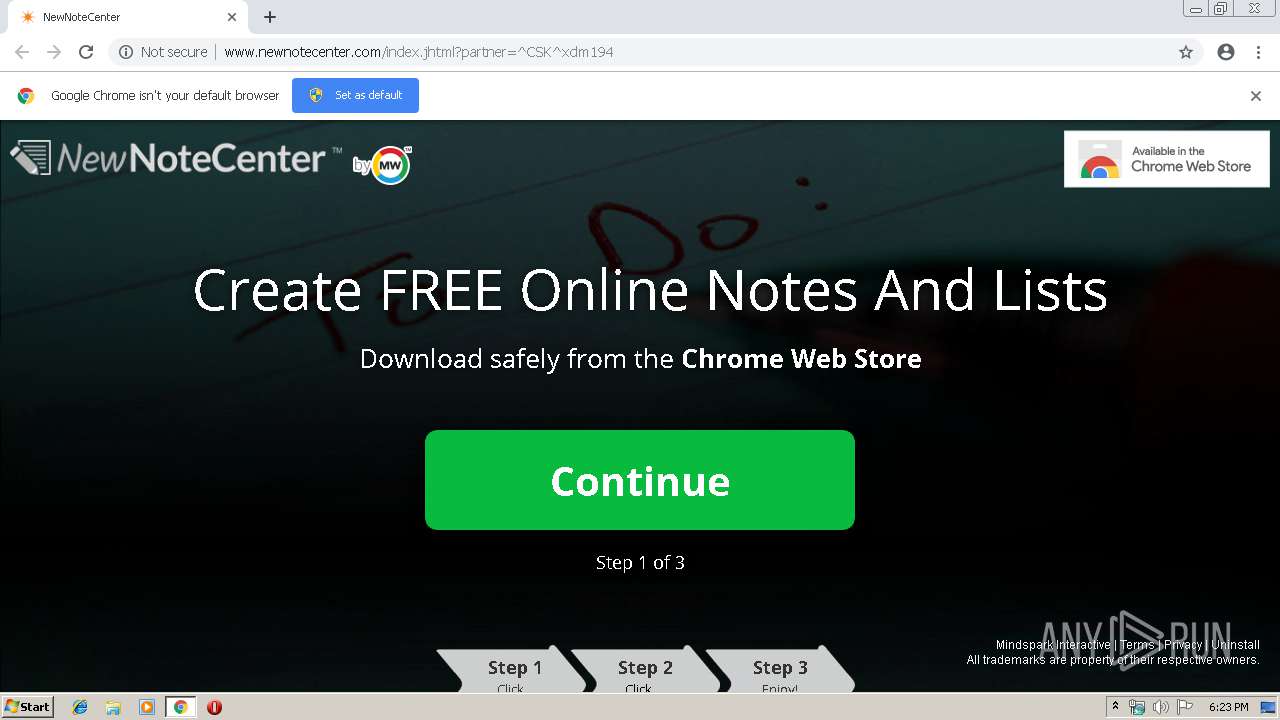
| URL: | http://www.newnotecenter.com/index.jhtml?partner=^CSK^xdm194 |
| Full analysis: | https://app.any.run/tasks/1b76a60d-8f3c-4d79-a224-09cdb75a2029 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 17:22:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | ECDB17ED08E874E33FA9B1F8EB14BCE6 |
| SHA1: | 9854646F1AA8ACCC9B0D76C2B931017CC4B3D69E |
| SHA256: | 9CAD56CFAC7E52861074F7711475F49083FC09F16C3DC6029468B982BF2616DA |
| SSDEEP: | 3:N1KJS404iA6GKbBUUVEXR0xg:Cc40Z5BUUuXWg |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2816)
INFO
Application launched itself
- chrome.exe (PID: 2816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --service-pipe-token=10861114725197286248 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10861114725197286248 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --service-pipe-token=11288740897435971458 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11288740897435971458 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1692 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17023308769242842767 --mojo-platform-channel-handle=4556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13927537341083777549 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13927537341083777549 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --service-pipe-token=6170257844413139568 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6170257844413139568 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2820 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://www.newnotecenter.com/index.jhtml?partner=^CSK^xdm194 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=18365695593966178434 --mojo-platform-channel-handle=4648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6806888849885908518 --mojo-platform-channel-handle=4648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,14153359556614846771,5797823042694672624,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12633345130580451948 --mojo-platform-channel-handle=4600 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
546
Read events
474
Write events
68
Delete events
4
Modification events
| (PID) Process: | (2680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2816-13200686594370125 |
Value: 259 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
23
Text files
124
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2ecec5eb-d372-4c6f-a821-a5077eb4c180.tmp | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
30
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2816 | chrome.exe | GET | 204 | 35.244.218.203:80 | http://www.newnotecenter.com/anemone.jhtml?anxuu=1A17E7DC-A1A8-4592-8FEB-BD12513A33F1&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T00%3A00%3A00Z&anxsn=prod-dlp-europe-west1-0kwg&anxu=http%3A%2F%2Fwww.newnotecenter.com%2Findex.jhtml&anxl=en-US&anxlv=1556212996135&anxsq=3&present=false&anxe=ToolbarDetect&anxr=941070903 | US | — | — | whitelisted |
2816 | chrome.exe | GET | 204 | 35.244.218.203:80 | http://www.newnotecenter.com/anemone.jhtml?anxuu=1A17E7DC-A1A8-4592-8FEB-BD12513A33F1&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T00%3A00%3A00Z&anxsn=prod-dlp-europe-west1-0kwg&anxu=http%3A%2F%2Fwww.newnotecenter.com%2Findex.jhtml&anxl=en-US&anxlv=1556212996177&anxsq=4&page=SplashPage&action=userconnection&downLink=10&effectiveType=4g&anxe=DLPInfo&anxr=259618957 | US | — | — | whitelisted |
2816 | chrome.exe | GET | 200 | 104.111.214.175:80 | http://ak.staticimgfarm.com/images/webtooltab/ttdetect-2/prd/ttDetectUtil.js | NL | text | 3.81 Kb | whitelisted |
2816 | chrome.exe | GET | 200 | 35.244.218.203:80 | http://www.newnotecenter.com/static/cws/audio.js | US | text | 649 b | whitelisted |
2816 | chrome.exe | GET | 200 | 35.244.218.203:80 | http://www.newnotecenter.com/index.jhtml?partner=^CSK^xdm194 | US | html | 42.9 Kb | whitelisted |
2816 | chrome.exe | GET | 204 | 35.244.218.203:80 | http://www.newnotecenter.com/anemone.jhtml?anxuu=1A17E7DC-A1A8-4592-8FEB-BD12513A33F1&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T00%3A00%3A00Z&anxsn=prod-dlp-europe-west1-0kwg&anxu=http%3A%2F%2Fwww.newnotecenter.com%2Findex.jhtml&anxl=en-US&anxlv=1556212996125&anxrd=none&anxrp=-&anxrk=-&anxrm=-&anxrb=-&anxrc=-&anxrs=-&anxsq=1&anxi=AF5935BF-C352-427F-9217-3D42077BB96F&anxe=backFill&anxr=1960984746 | US | compressed | 649 b | whitelisted |
2816 | chrome.exe | GET | 200 | 35.244.218.203:80 | http://newnotecenter.dl.myway.com/localStorage.jhtml | US | html | 2.20 Kb | whitelisted |
2816 | chrome.exe | GET | 200 | 104.111.214.175:80 | http://ak.imgfarm.com/images/download/chrome/overlay_bl_2.png | NL | image | 18.7 Kb | whitelisted |
2816 | chrome.exe | GET | 204 | 35.244.218.203:80 | http://www.newnotecenter.com/anemone.jhtml?anxuu=1A17E7DC-A1A8-4592-8FEB-BD12513A33F1&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T00%3A00%3A00Z&anxsn=prod-dlp-europe-west1-0kwg&anxu=http%3A%2F%2Fwww.newnotecenter.com%2Findex.jhtml&anxl=en-US&anxlv=1556213017218&anxsq=5&cookiesEnabled=1&pageLoad=21584&anxe=SplashLanding&anxr=1411832663 | US | compressed | 649 b | whitelisted |
2816 | chrome.exe | GET | 200 | 104.111.214.175:80 | http://ak.imgfarm.com/images/download/spokesperson/html5/audio/newrvid_33017_01_take01.mp3 | NL | mp3 | 66.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2816 | chrome.exe | 172.217.16.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2816 | chrome.exe | 104.111.214.175:443 | ak.staticimgfarm.com | Akamai International B.V. | NL | whitelisted |
2816 | chrome.exe | 104.111.214.175:80 | ak.staticimgfarm.com | Akamai International B.V. | NL | whitelisted |
2816 | chrome.exe | 2.18.232.251:80 | akz.imgfarm.com | Akamai International B.V. | — | whitelisted |
— | — | 35.244.218.203:80 | www.newnotecenter.com | — | US | whitelisted |
— | — | 104.111.214.175:80 | ak.staticimgfarm.com | Akamai International B.V. | NL | whitelisted |
2816 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2816 | chrome.exe | 172.217.21.194:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2816 | chrome.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2816 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.newnotecenter.com |
| whitelisted |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ak.staticimgfarm.com |
| whitelisted |
ak.imgfarm.com |
| whitelisted |
akz.imgfarm.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
newnotecenter.dl.myway.com |
| whitelisted |
newnotecenter.dl.tb.ask.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2816 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |