| File name: | Upgrade.exe |
| Full analysis: | https://app.any.run/tasks/640ba708-db2e-43c8-8052-24816f6b3ab9 |
| Verdict: | No threats detected |
| Analysis date: | October 28, 2020, 05:28:39 |
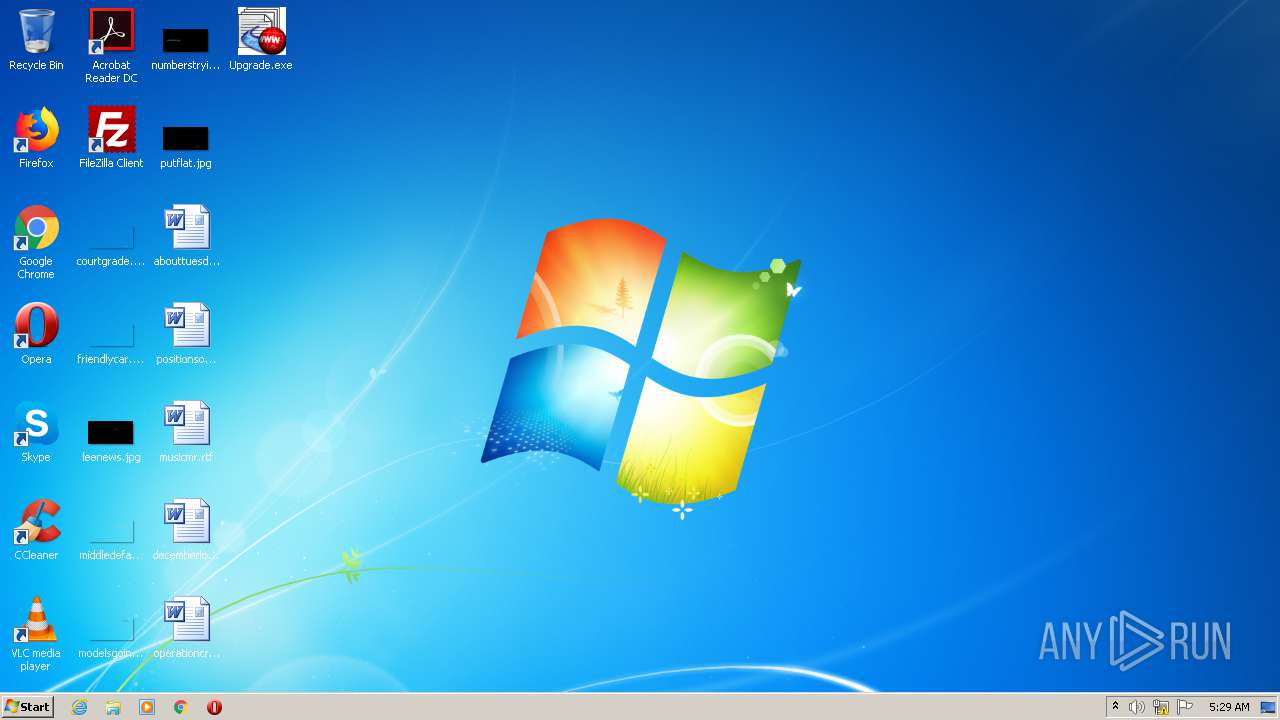
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 75D078CB41A527D534C7BEC1557195E1 |
| SHA1: | 3E36DEAE6BEE8E7EBED2DD0F4E2269FDC3353F17 |
| SHA256: | 9CAAB47074FA7CCD0B87E5EA92372301B18EA56783A67E07FDF96956B761FC31 |
| SSDEEP: | 6144:B0O6mTegl9Q2S02Ys4HJxdMN1zRuWXlZ:L6mTeg02/pL7MN1zRuW |
MALICIOUS
Changes settings of System certificates
- Upgrade.exe (PID: 2636)
SUSPICIOUS
Reads Internet Cache Settings
- Upgrade.exe (PID: 2636)
Adds / modifies Windows certificates
- Upgrade.exe (PID: 2636)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:11:14 15:49:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 159744 |
| InitializedDataSize: | 94208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbb1a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.4 |
| ProductVersionNumber: | 1.0.0.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Honest Technology |
| FileDescription: | honestech Product Agent Upgrader |
| FileVersion: | 1, 0, 0, 4 |
| InternalName: | honestech Product Agent Upgrader |
| LegalCopyright: | Copyright (C) 2007 |
| LegalTrademarks: | - |
| OriginalFileName: | Upgrade.EXE |
| PrivateBuild: | - |
| ProductName: | honestech Product Agent Upgrader |
| ProductVersion: | 1, 0, 0, 4 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Nov-2007 14:49:34 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Honest Technology |
| FileDescription: | honestech Product Agent Upgrader |
| FileVersion: | 1, 0, 0, 4 |
| InternalName: | honestech Product Agent Upgrader |
| LegalCopyright: | Copyright (C) 2007 |
| LegalTrademarks: | - |
| OriginalFilename: | Upgrade.EXE |
| PrivateBuild: | - |
| ProductName: | honestech Product Agent Upgrader |
| ProductVersion: | 1, 0, 0, 4 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 14-Nov-2007 14:49:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000261E2 | 0x00027000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53635 |
.rdata | 0x00028000 | 0x00009074 | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.47753 |
.data | 0x00032000 | 0x00008528 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.26856 |
.rsrc | 0x0003B000 | 0x000030B0 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.3324 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.37099 | 980 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.02695 | 308 | UNKNOWN | Korean - Korea | RT_CURSOR |
3 | 2.74274 | 180 | UNKNOWN | Korean - Korea | RT_CURSOR |
7 | 2.05112 | 78 | UNKNOWN | English - United States | RT_STRING |
128 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
3841 | 4.01751 | 102 | UNKNOWN | Korean - Korea | RT_STRING |
3842 | 1.33387 | 44 | UNKNOWN | Korean - Korea | RT_STRING |
3843 | 4.55941 | 158 | UNKNOWN | Korean - Korea | RT_STRING |
3857 | 5.45025 | 708 | UNKNOWN | Korean - Korea | RT_STRING |
3858 | 4.80034 | 370 | UNKNOWN | Korean - Korea | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
OLEPRO32.DLL |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINSPOOL.DRV |
Total processes
35
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2636 | "C:\Users\admin\Desktop\Upgrade.exe" | C:\Users\admin\Desktop\Upgrade.exe | explorer.exe | ||||||||||||
User: admin Company: Honest Technology Integrity Level: MEDIUM Description: honestech Product Agent Upgrader Exit code: 0 Version: 1, 0, 0, 4 Modules
| |||||||||||||||
Total events
93
Read events
68
Write events
23
Delete events
2
Modification events
| (PID) Process: | (2636) Upgrade.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2636) Upgrade.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2636) Upgrade.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2636) Upgrade.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2636) Upgrade.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2636) Upgrade.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2636) Upgrade.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2636) Upgrade.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2636) Upgrade.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\47BEABC922EAE80E78783462A79F45C254FDE68B |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000803ABC22C1E6FB8D9B3B274A321B9A010F00000001000000200000003560E45B41E46B8F36537025D1D5BC02D9652A10645B0EFF69E8B6A52191F33503000000010000001400000047BEABC922EAE80E78783462A79F45C254FDE68B1D000000010000001000000070253FBCBDE32A014D38C1993098AD991400000001000000140000003A9A8507106728B6EFF6BD05416E20C194DA0FDE62000000010000002000000045140B3247EB9CC8C5B4F0D7B53091F73292089E6E5A63E2749DD3ACA9198EDA53000000010000002500000030233021060B6086480186FD6D0107170330123010060A2B0601040182373C0101030200C00B000000010000005200000047006F00200044006100640064007900200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F007200690074007900200013202000470032000000090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030306082B0601050507030406082B06010505070308060A2B0601040182370A030406082B0601050507030606082B0601050507030719000000010000001000000021D008B47B7A2A81C8435903DED424C92000000001000000C9030000308203C5308202ADA003020102020100300D06092A864886F70D01010B0500308183310B30090603550406130255533110300E060355040813074172697A6F6E61311330110603550407130A53636F74747364616C65311A3018060355040A1311476F44616464792E636F6D2C20496E632E3131302F06035504031328476F20446164647920526F6F7420436572746966696361746520417574686F72697479202D204732301E170D3039303930313030303030305A170D3337313233313233353935395A308183310B30090603550406130255533110300E060355040813074172697A6F6E61311330110603550407130A53636F74747364616C65311A3018060355040A1311476F44616464792E636F6D2C20496E632E3131302F06035504031328476F20446164647920526F6F7420436572746966696361746520417574686F72697479202D20473230820122300D06092A864886F70D01010105000382010F003082010A0282010100BF716208F1FA5934F71BC918A3F7804958E9228313A6C52043013B84F1E685499F27EAF6841B4EA0B4DB7098C73201B1053E074EEEF4FA4F2F593022E7AB19566BE28007FCF316758039517BE5F935B6744EA98D8213E4B63FA90383FAA2BE8A156A7FDE0BC3B6191405CAEAC3A804943B467C320DF3006622C88D696D368C1118B7D3B21C60B438FA028CCED3DD4607DE0A3EEB5D7CC87CFBB02B53A4926269512505611A44818C2CA9439623DFAC3A819A0E29C51CA9E95D1EB69E9E300A39CEF18880FB4B5DCC32EC85624325340256270191B43B702A3F6EB1E89C88017D9FD4F9DB536D609DBF2CE758ABB85F46FCCEC41B033C09EB49315C6946B3E0470203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604143A9A8507106728B6EFF6BD05416E20C194DA0FDE300D06092A864886F70D01010B0500038201010099DB5D79D5F99759670361F17E3B0631752DA1208E4F6587B4F7A69CBCD8E92FD0DB5AEECF748C73B43842DA057BF80275B8FDA5B1D7AEF6D7DE13CB53107E8A46D197FAB72E2B11AB90B02780F9E89F5AE9379FABE4DF6CB385179D3DD9244F799135D65F04EB8083AB9A022DB510F4D890C7047340ED7225A0A99FEC9EAB68129957C68F123A09A4BD44FD061537C19BE432A3ED38E8D864F32C7E14FC02EA9FCDFF076817DB2290382D7A8DD154F169E35F33CA7A3D7B0AE3CA7F5F39E5E275BAC5761833CE2CF02F4CADF7B1E7CE4FA8C49B4A5406C57F7DD5080FE21CFE7E17B8AC5EF6D416B243090C4DF6A76BB4998465CA7A88E2E244BE5CF7EA1CF5 | |||
| (PID) Process: | (2636) Upgrade.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\47BEABC922EAE80E78783462A79F45C254FDE68B |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
4
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2636 | Upgrade.exe | C:\Users\admin\AppData\Local\Temp\Cab73D0.tmp | — | |
MD5:— | SHA256:— | |||
| 2636 | Upgrade.exe | C:\Users\admin\AppData\Local\Temp\Tar73D1.tmp | — | |
MD5:— | SHA256:— | |||
| 2636 | Upgrade.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C5FD5BF0CE6372B1CAFE381FD0BC969C | binary | |
MD5:— | SHA256:— | |||
| 2636 | Upgrade.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C5FD5BF0CE6372B1CAFE381FD0BC969C | der | |
MD5:— | SHA256:— | |||
| 2636 | Upgrade.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\upgradeagent[1].htm | html | |
MD5:— | SHA256:— | |||
| 2636 | Upgrade.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 2636 | Upgrade.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
| 2636 | Upgrade.exe | C:\Users\admin\AppData\Local\Temp\Info.xml | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2636 | Upgrade.exe | GET | 200 | 192.124.249.41:80 | http://crl.godaddy.com/gdroot.crl | US | der | 429 b | whitelisted |
2636 | Upgrade.exe | GET | 301 | 104.238.111.75:80 | http://www.honestech.com/upgrade/upgradeagent.asp | US | html | 173 b | whitelisted |
2636 | Upgrade.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2636 | Upgrade.exe | 104.238.111.75:80 | www.honestech.com | GoDaddy.com, LLC | US | unknown |
2636 | Upgrade.exe | 192.124.249.24:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2636 | Upgrade.exe | 104.238.111.75:443 | www.honestech.com | GoDaddy.com, LLC | US | unknown |
2636 | Upgrade.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.honestech.com |
| unknown |
ocsp.godaddy.com |
| whitelisted |
crl.godaddy.com |
| whitelisted |