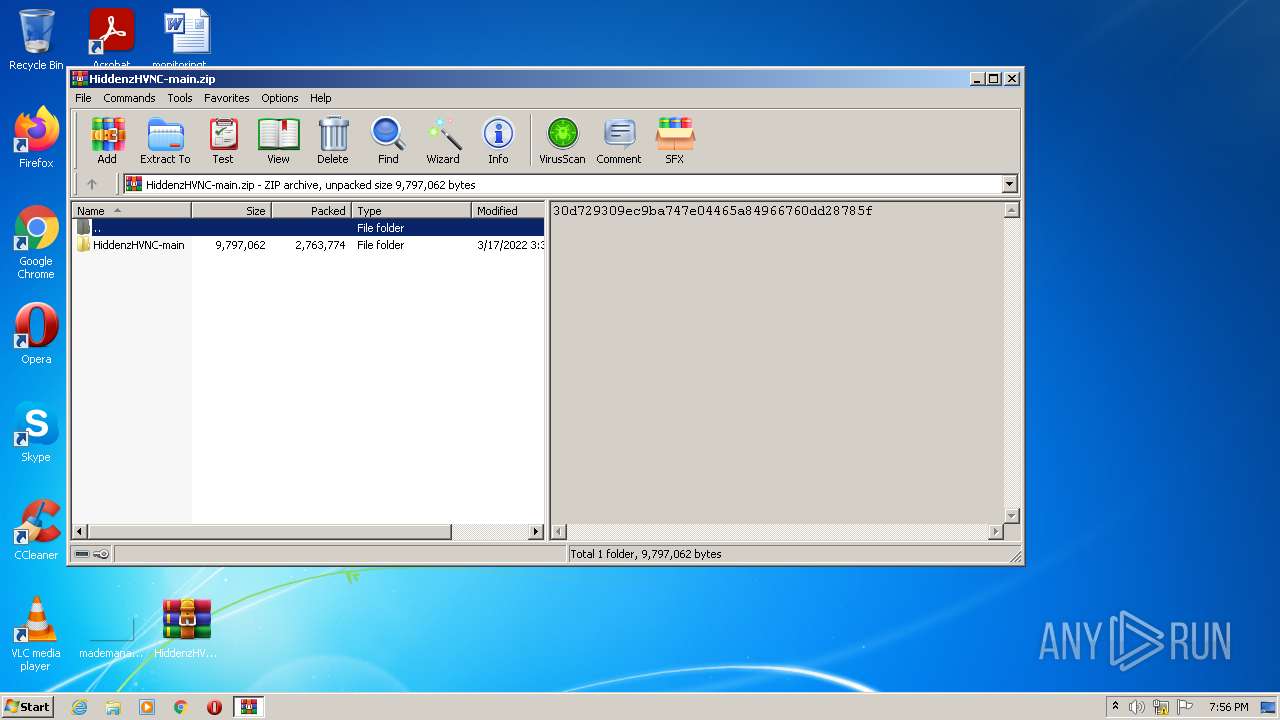
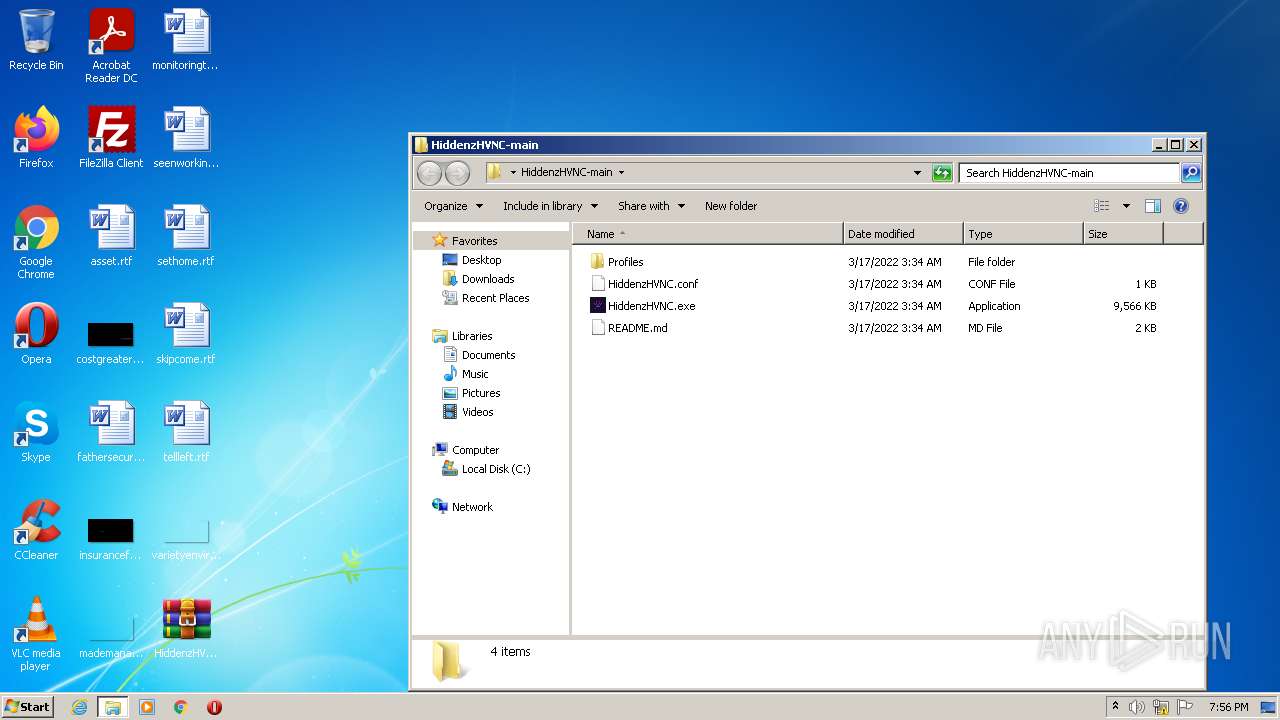
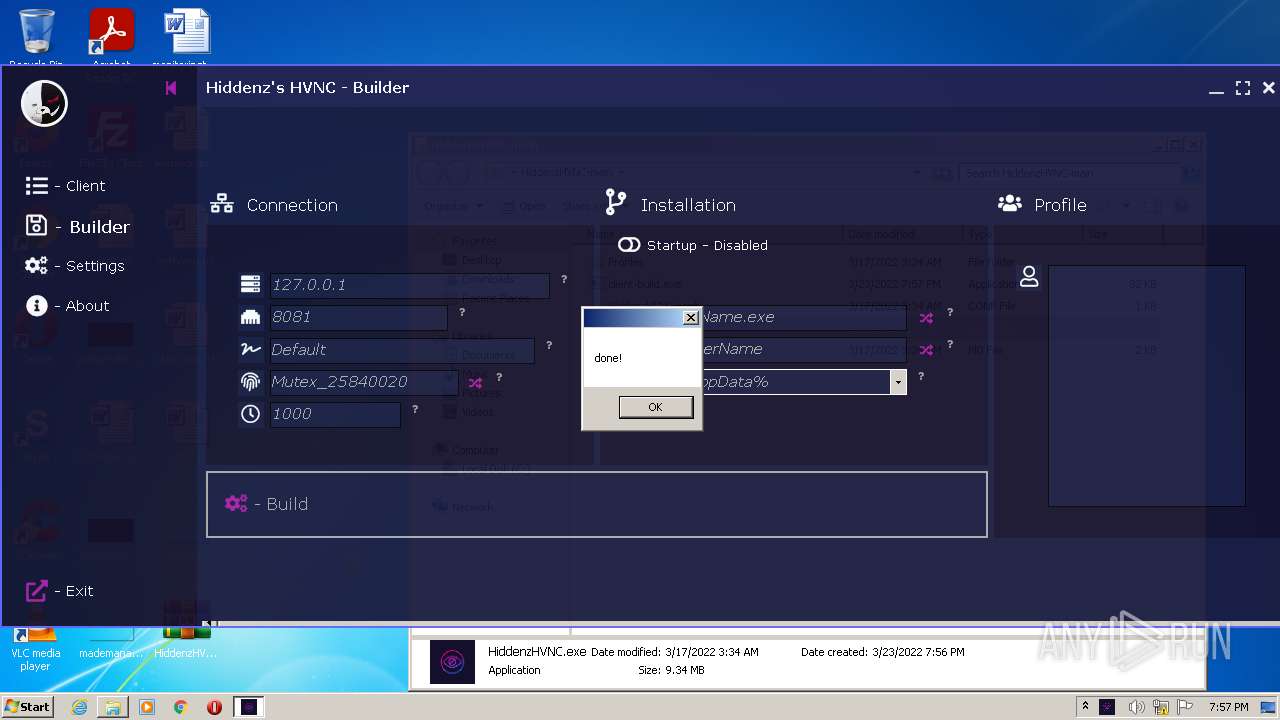
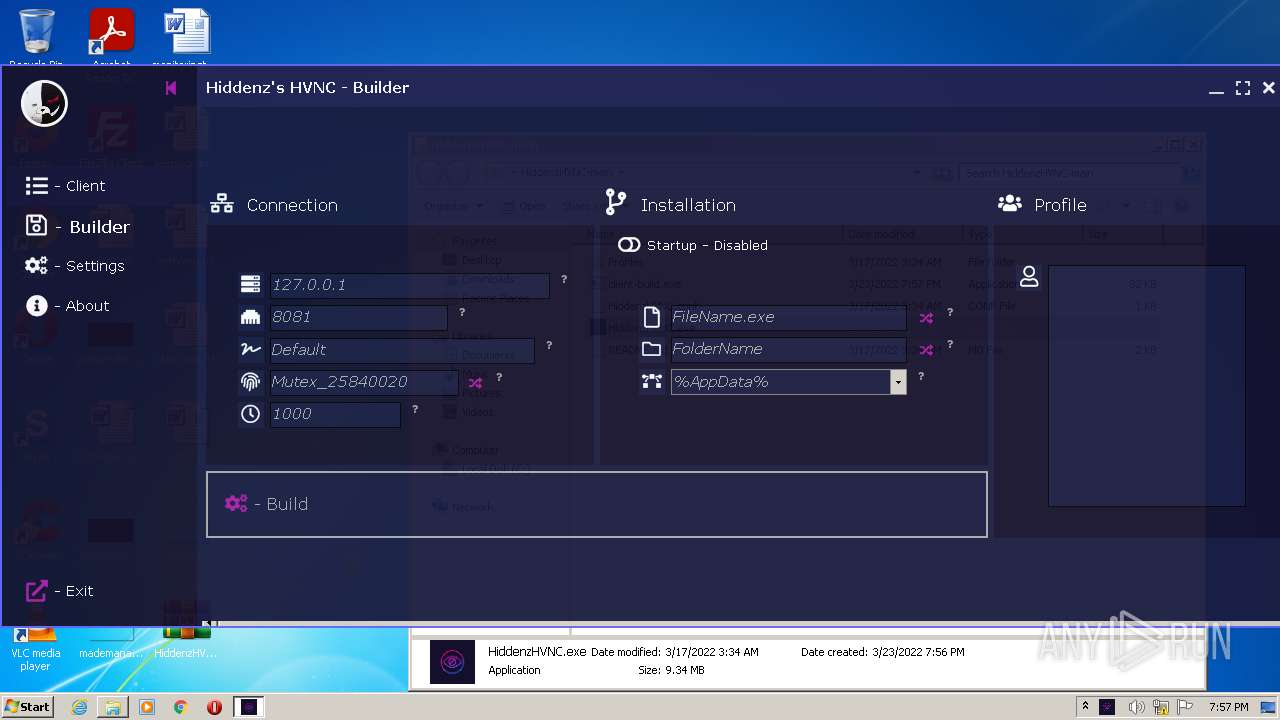
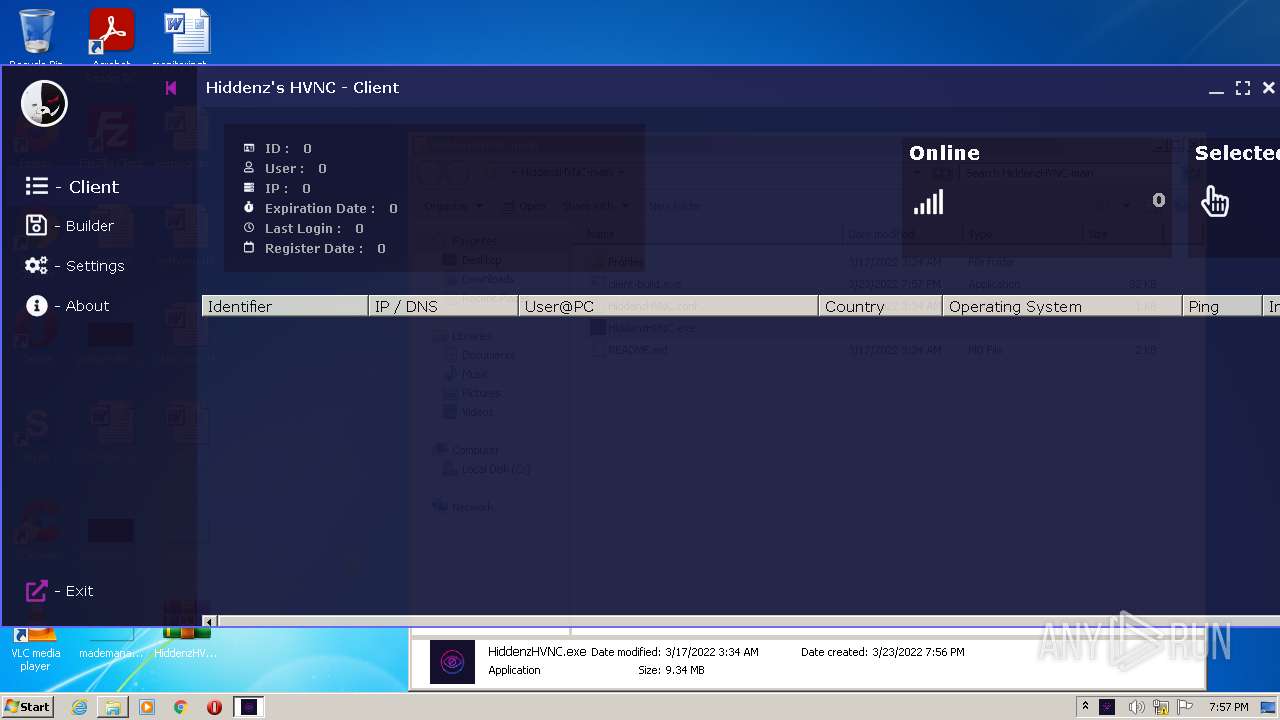
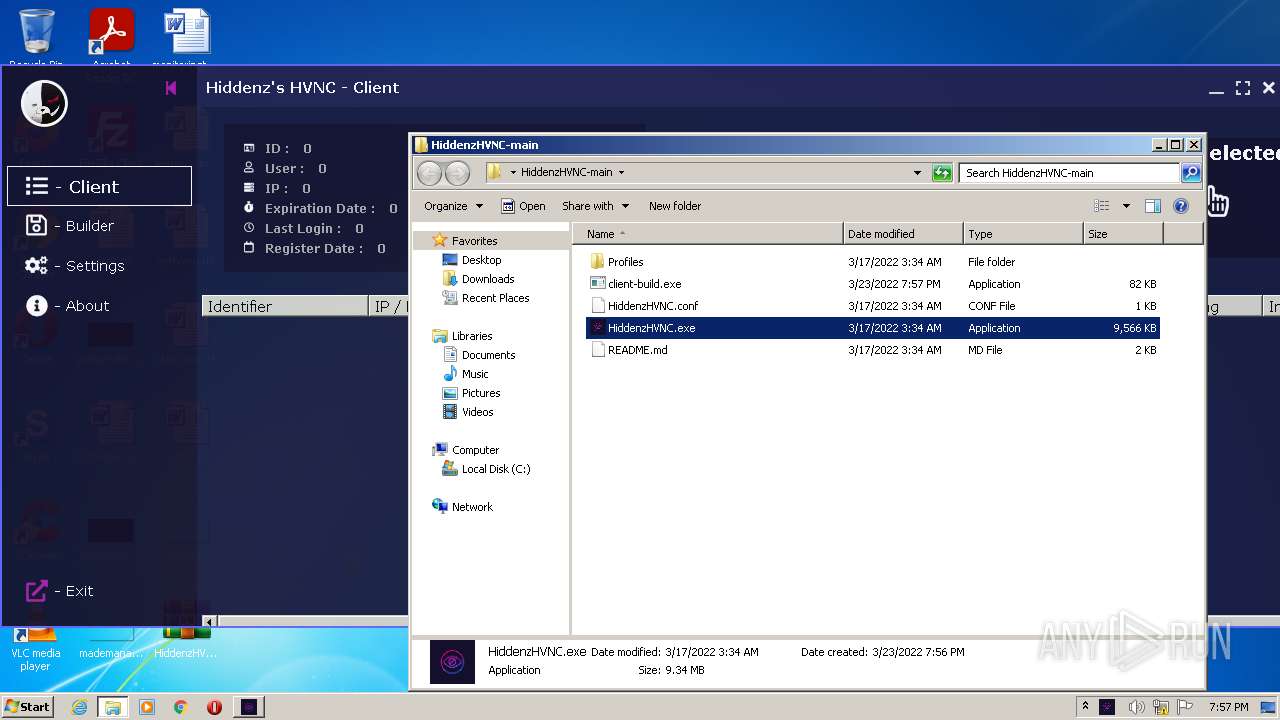
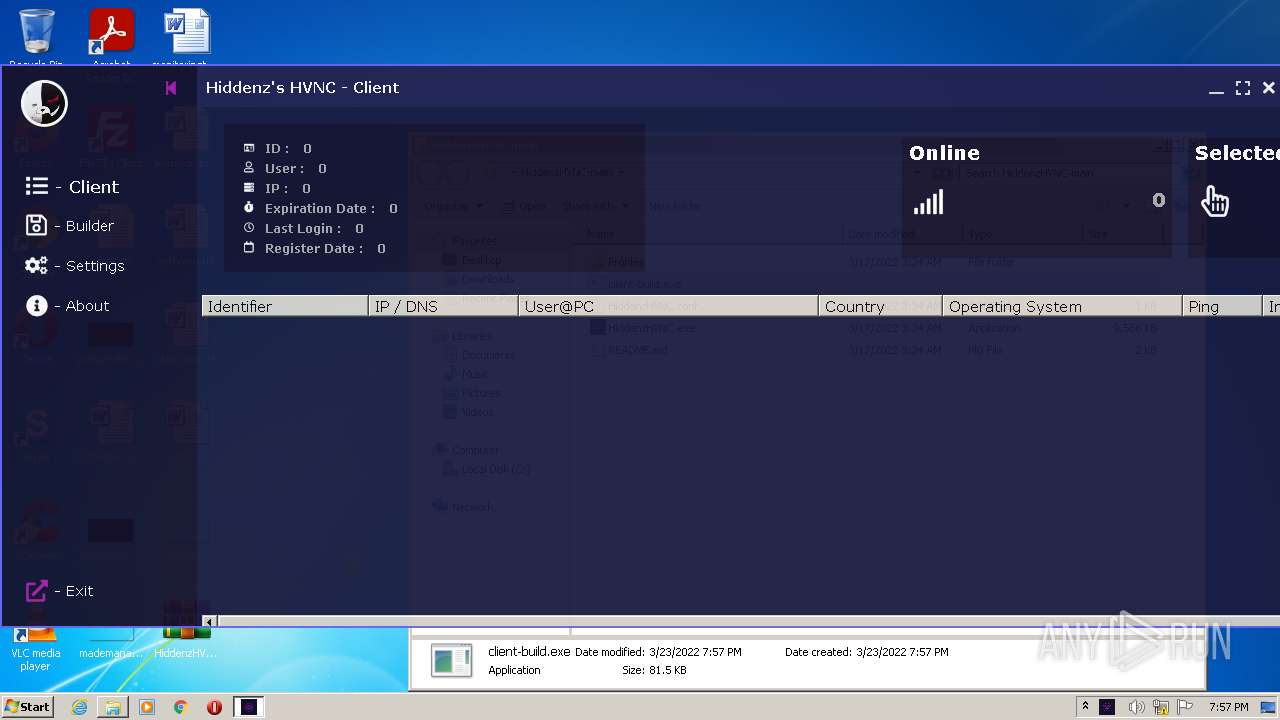
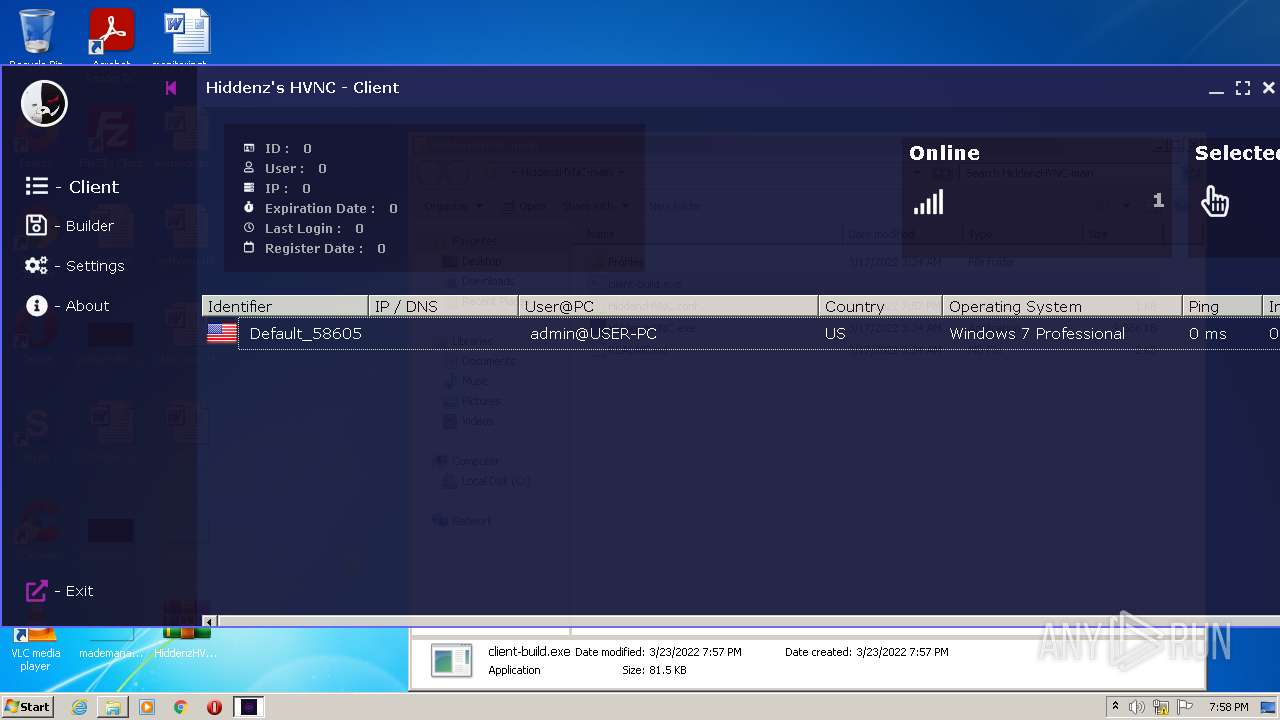
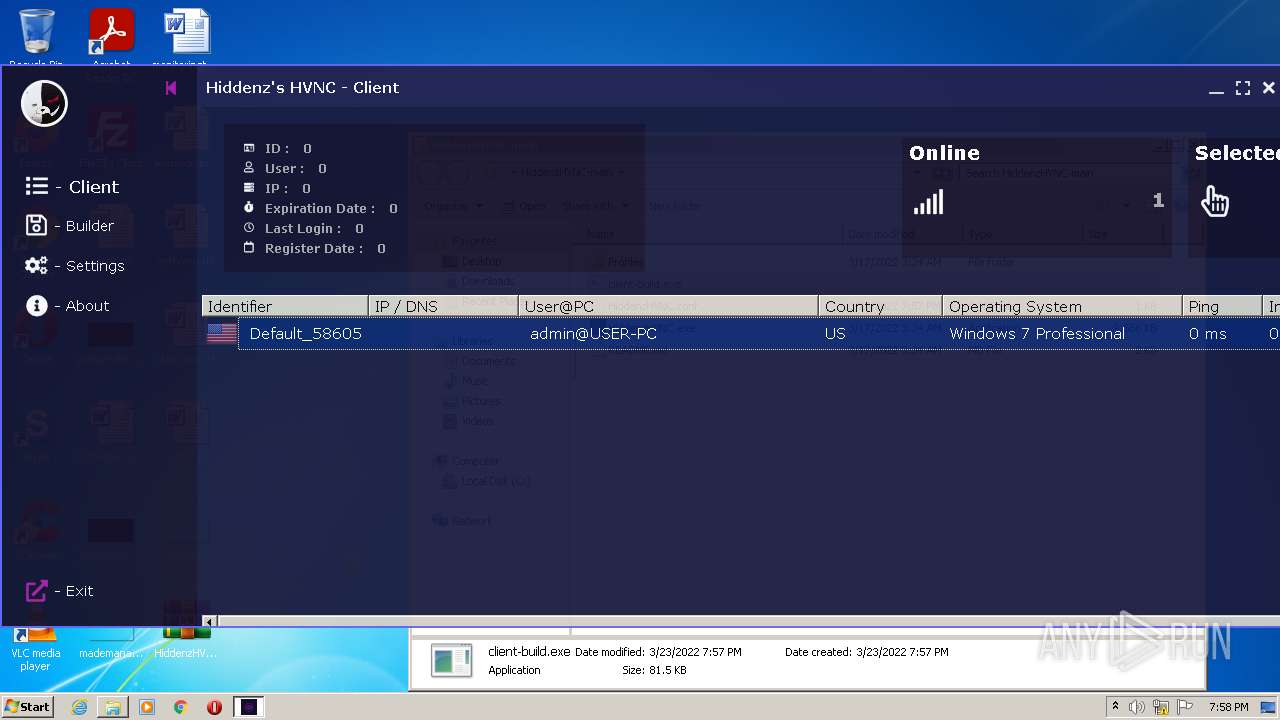
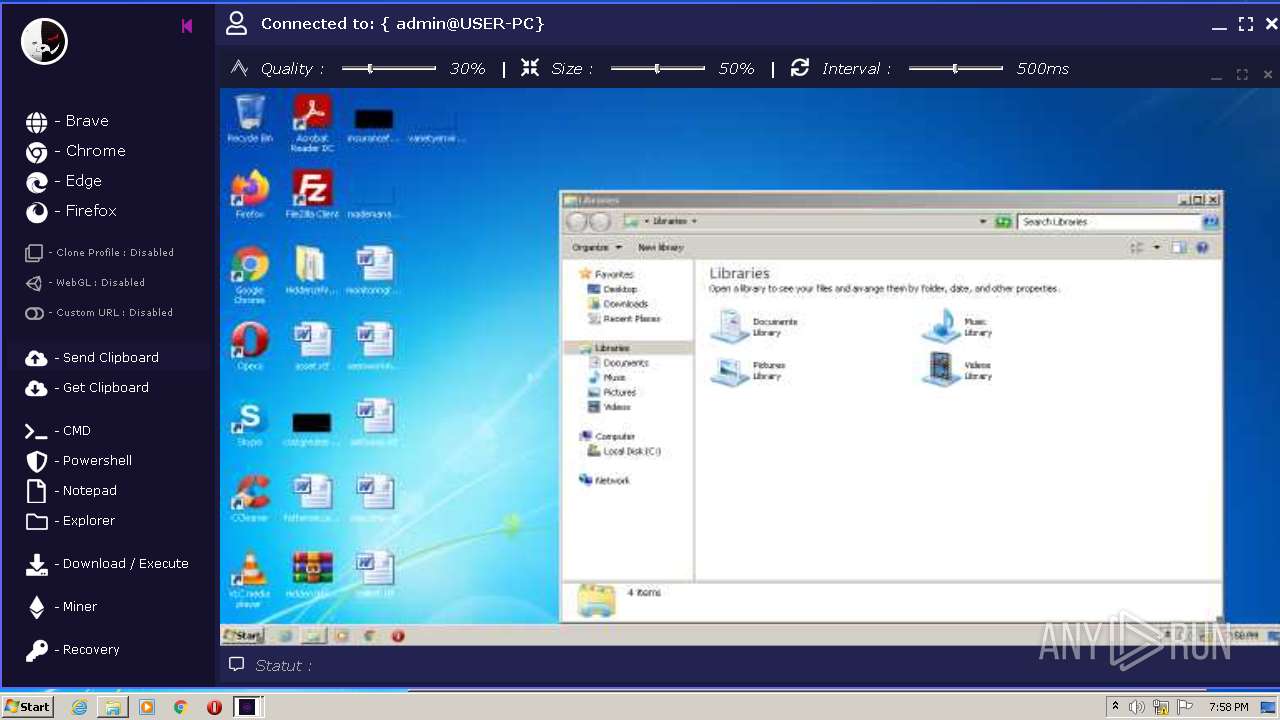
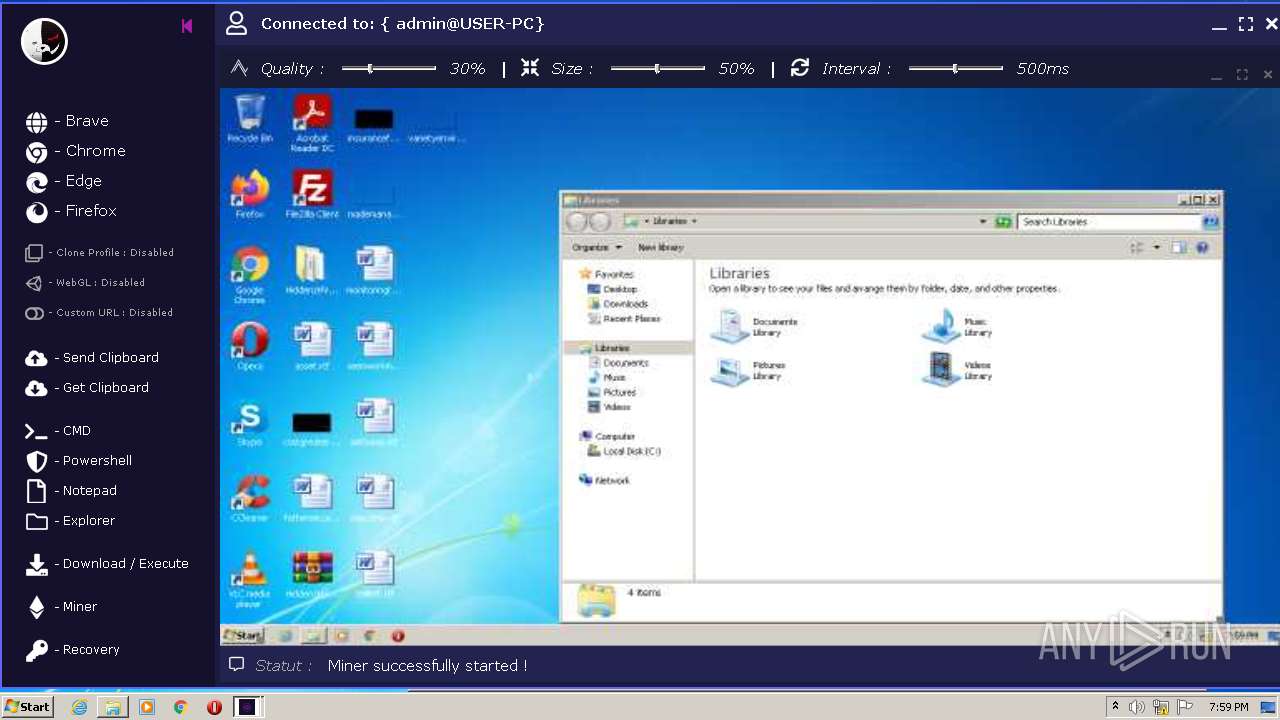
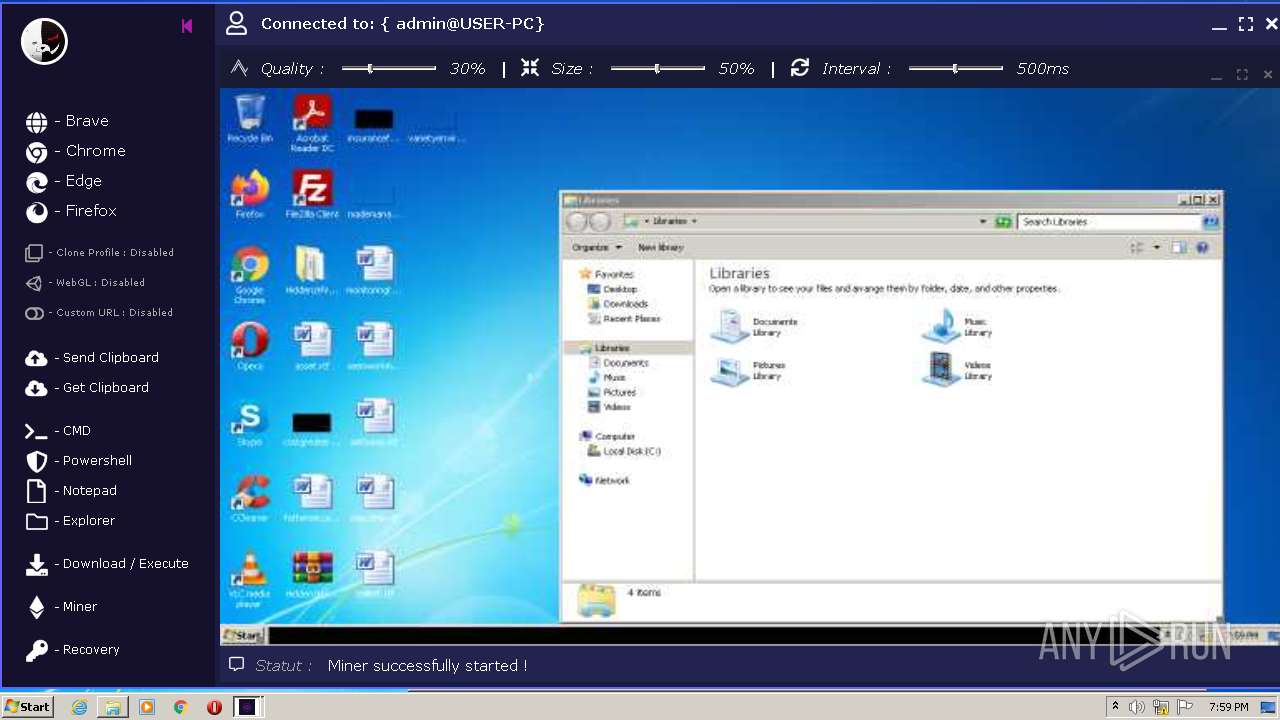
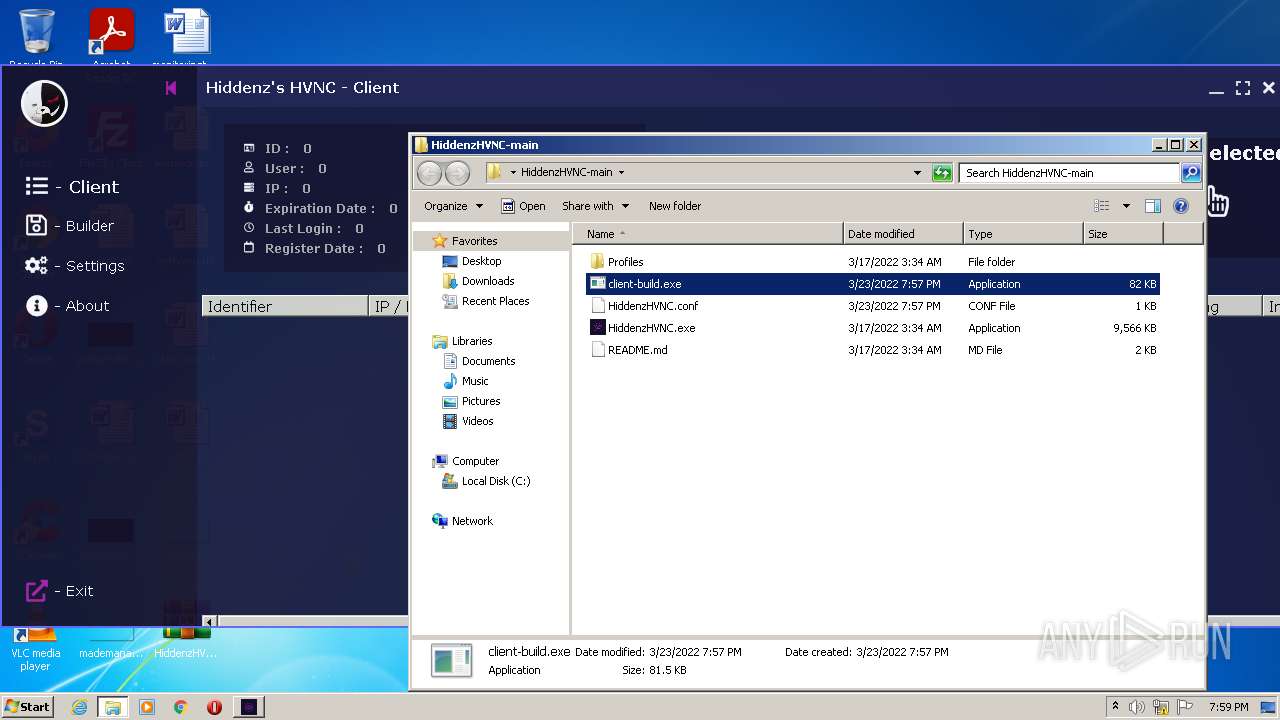
| File name: | HiddenzHVNC-main.zip |
| Full analysis: | https://app.any.run/tasks/02dbdbc4-03c6-42be-bbe9-52c4b84ef278 |
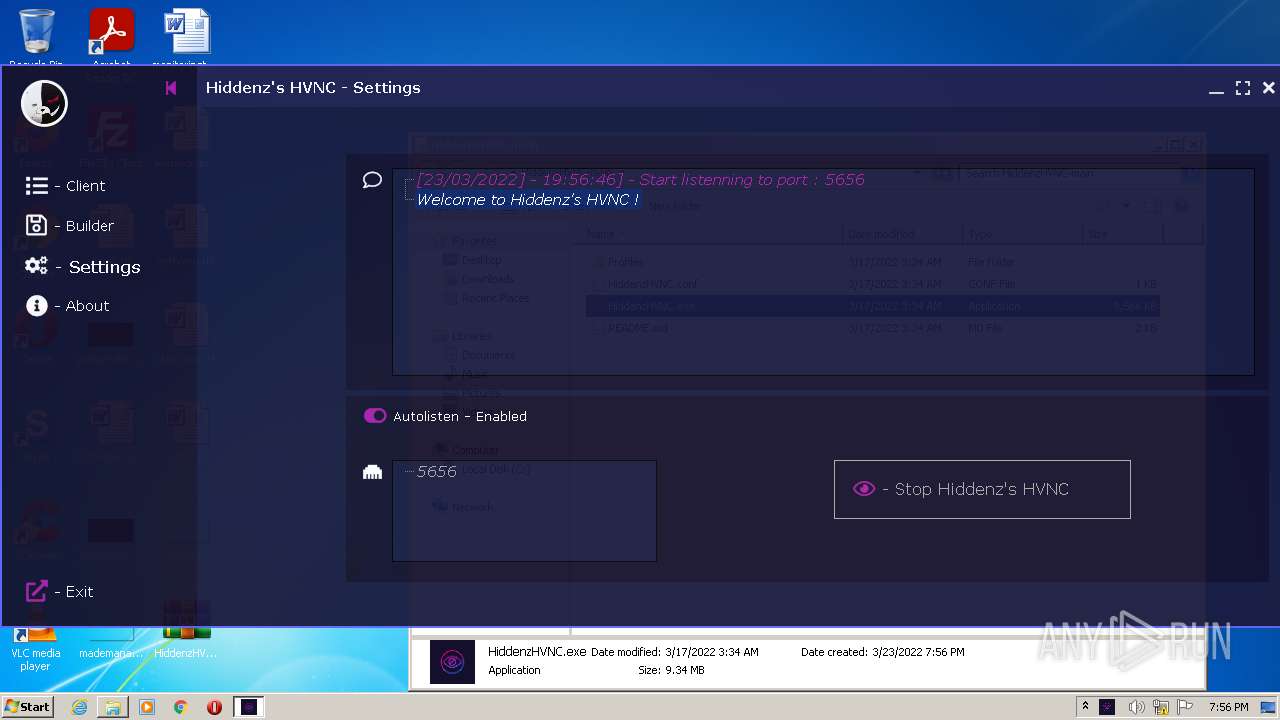
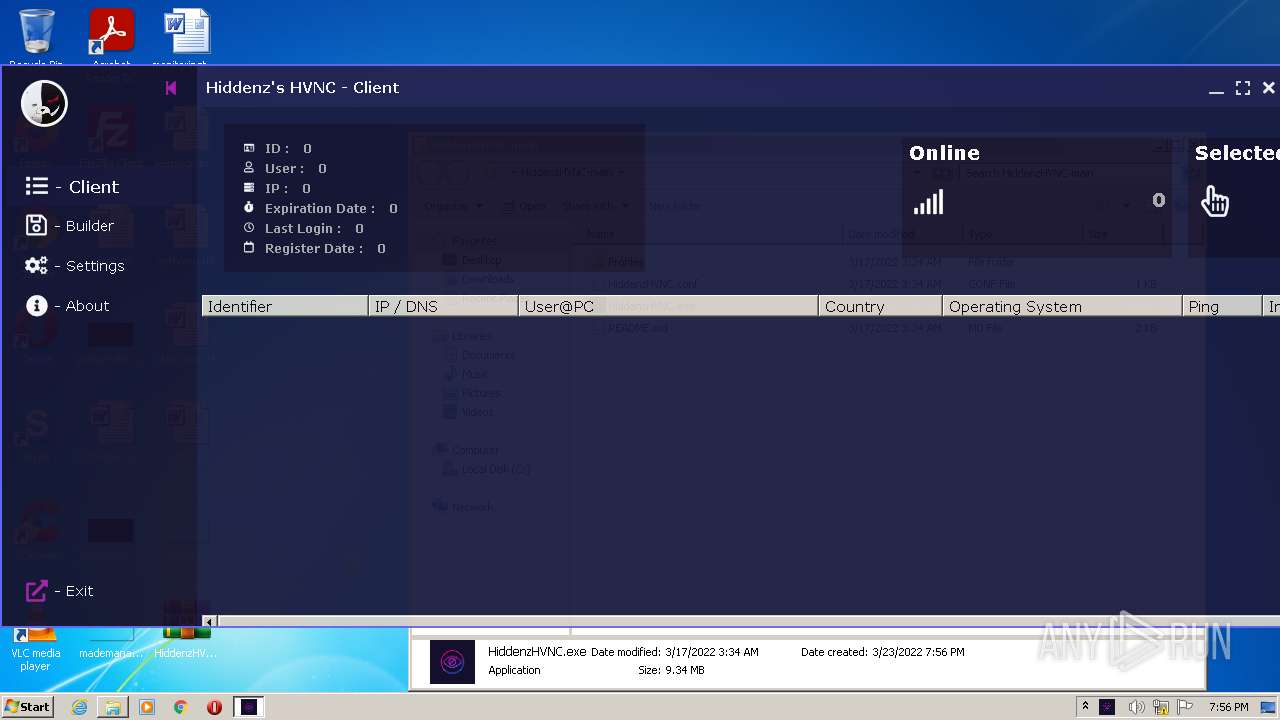
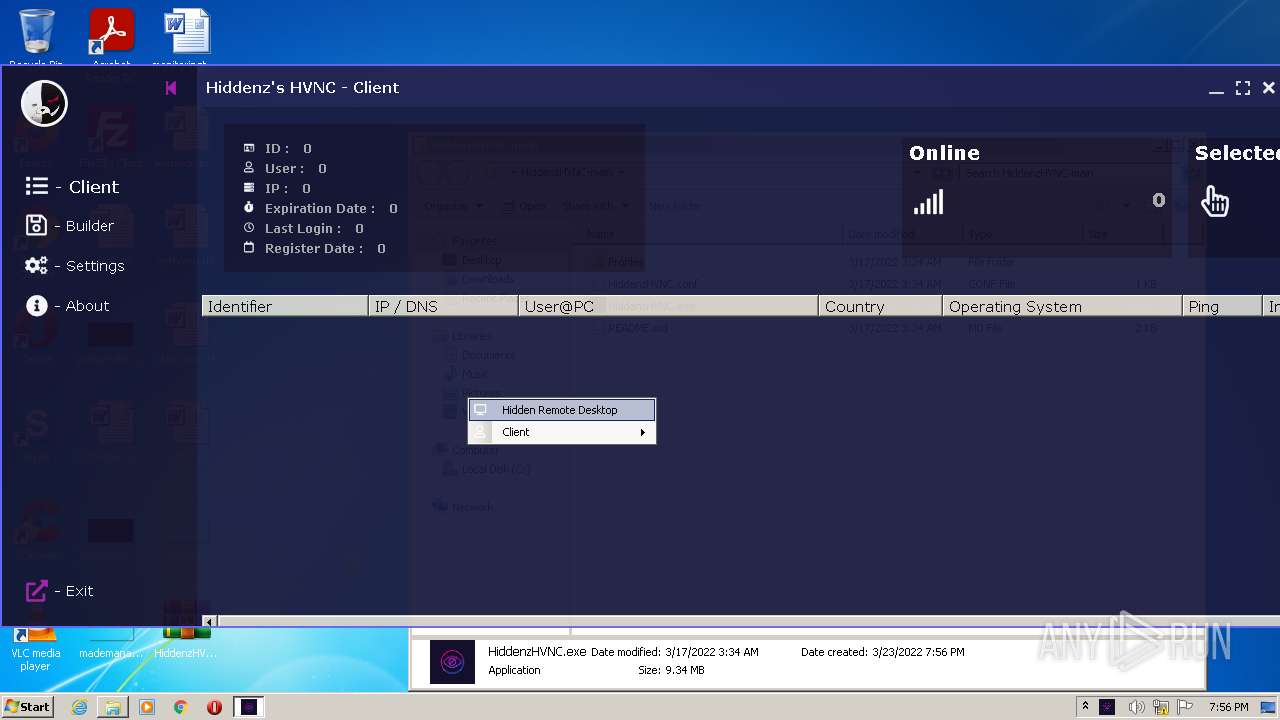
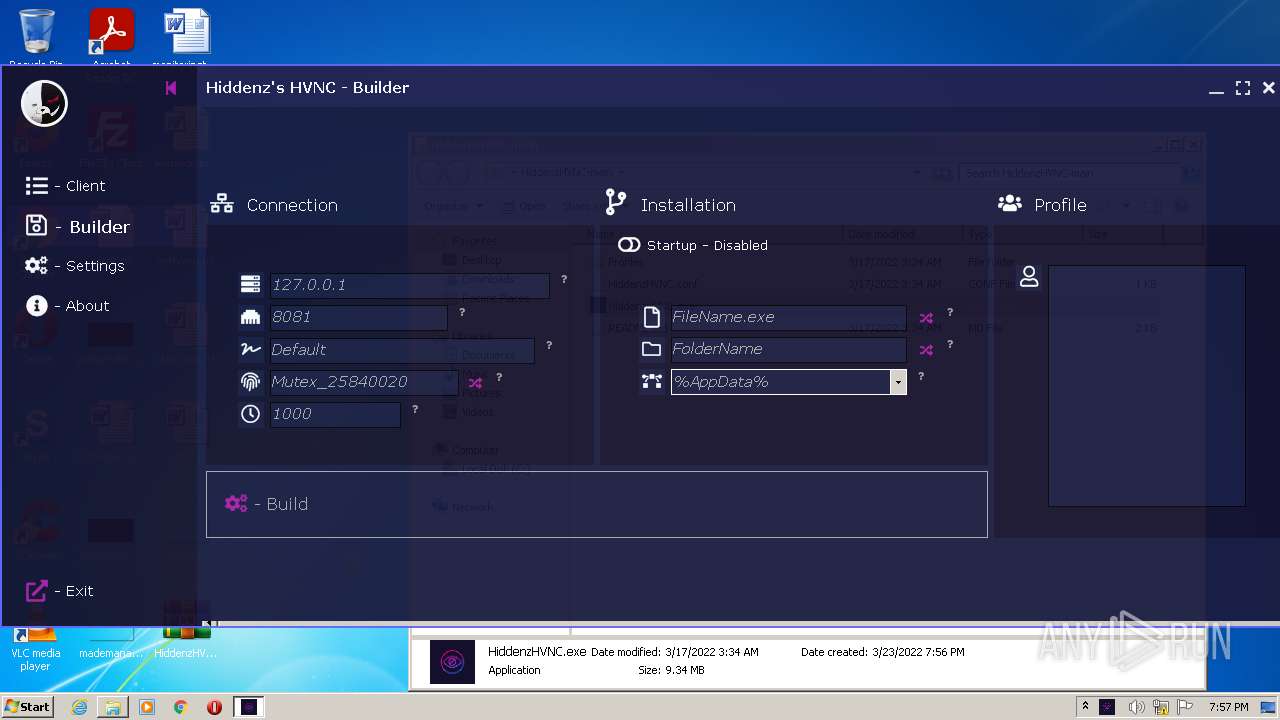
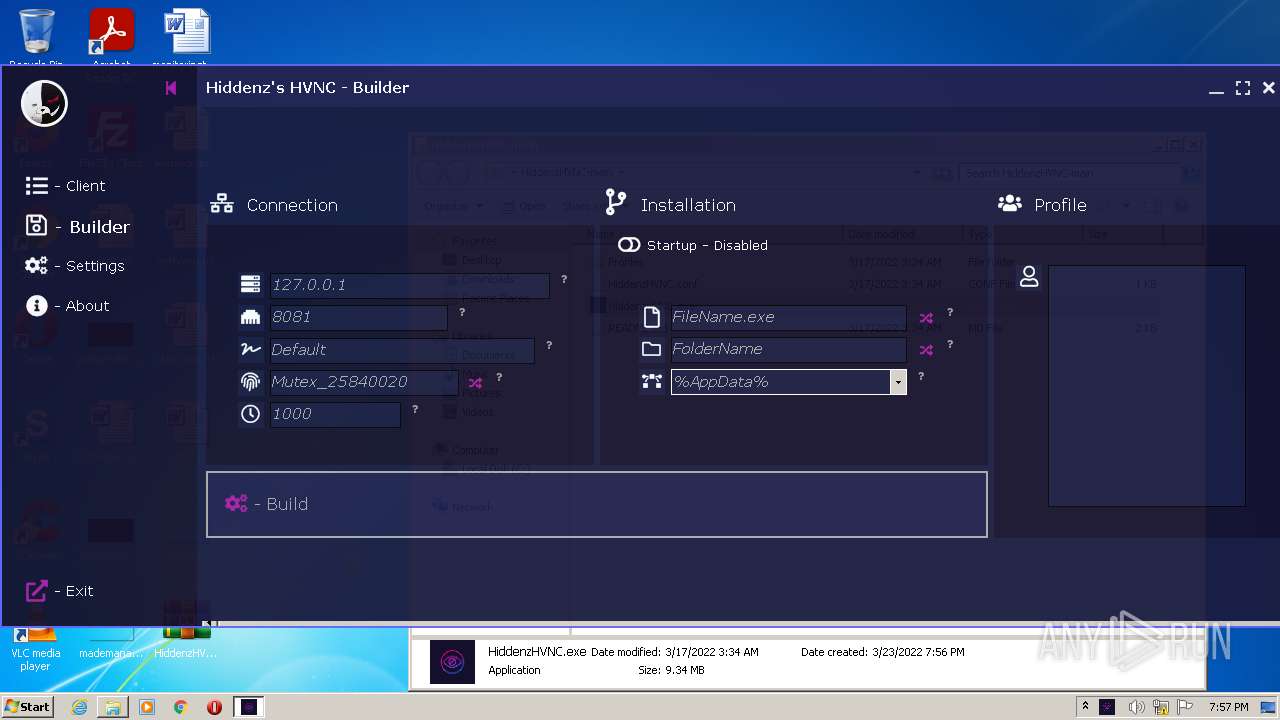
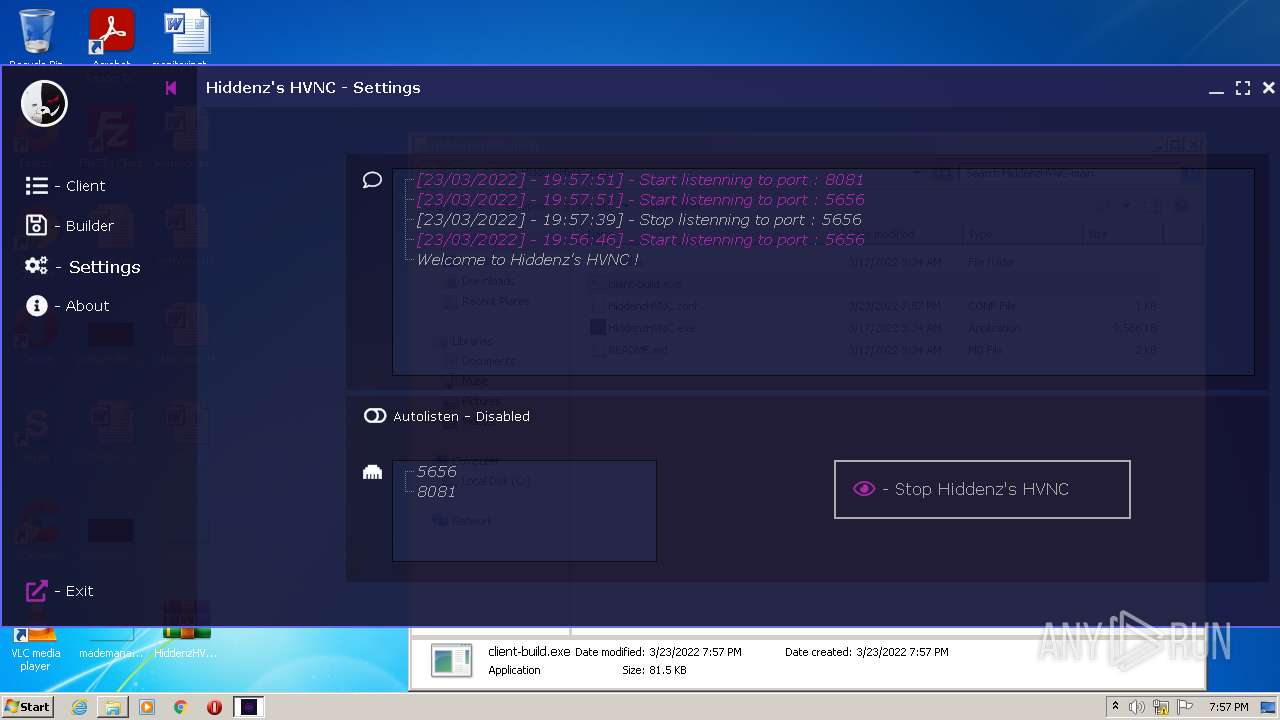
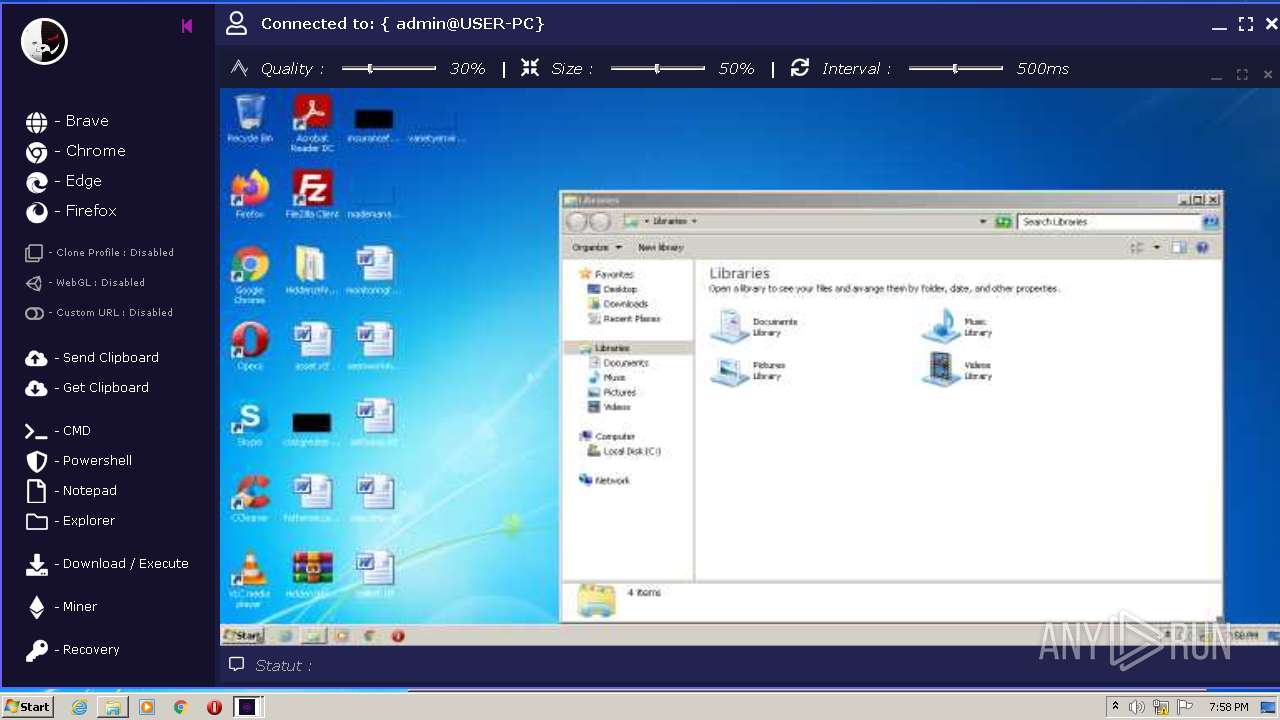
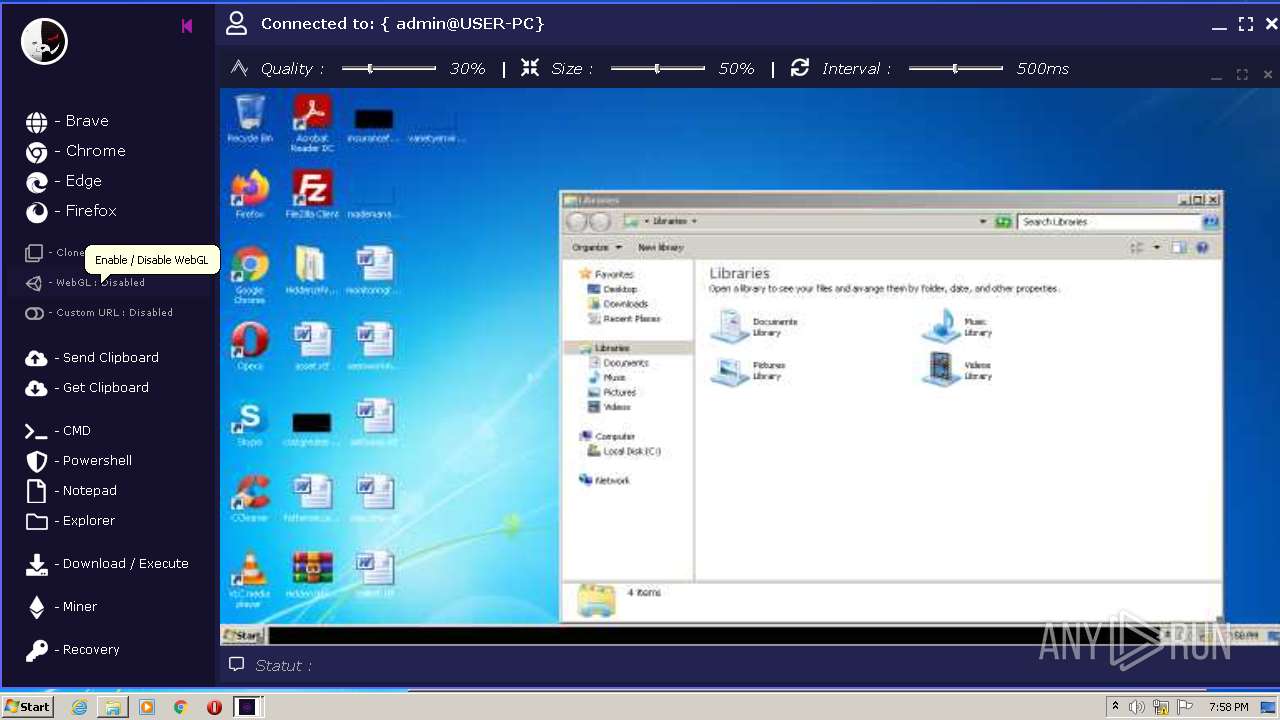
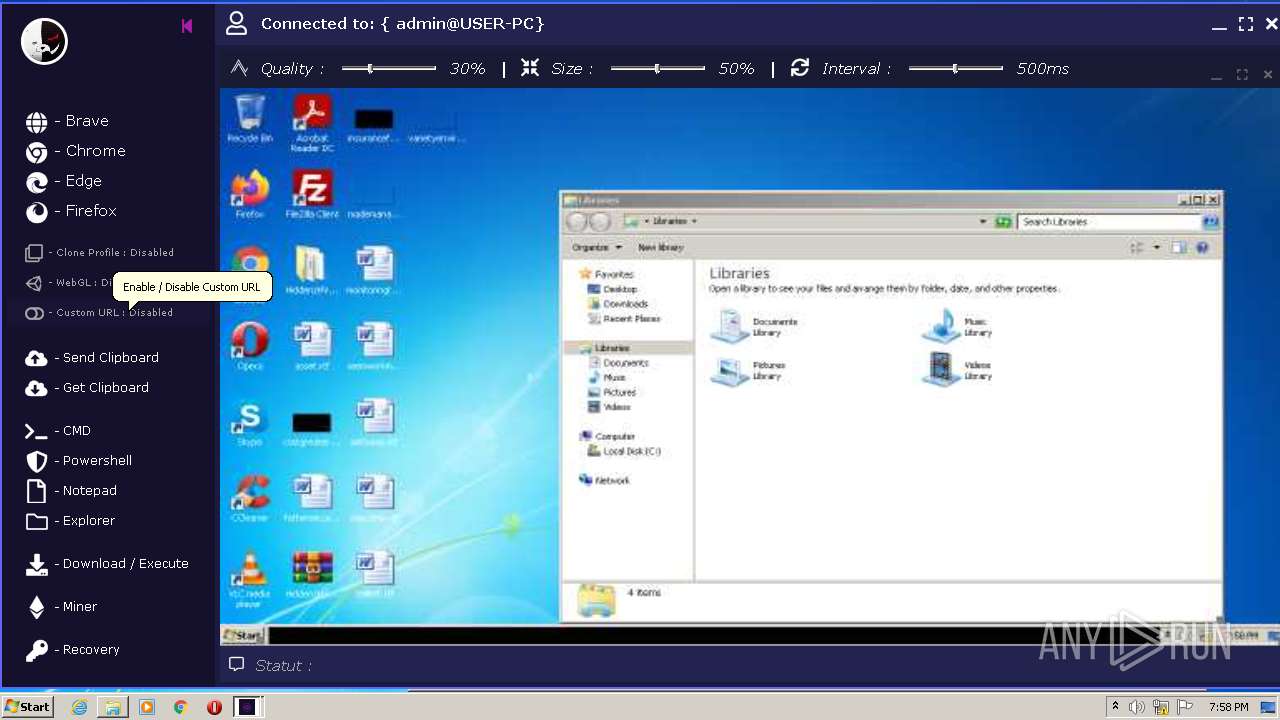
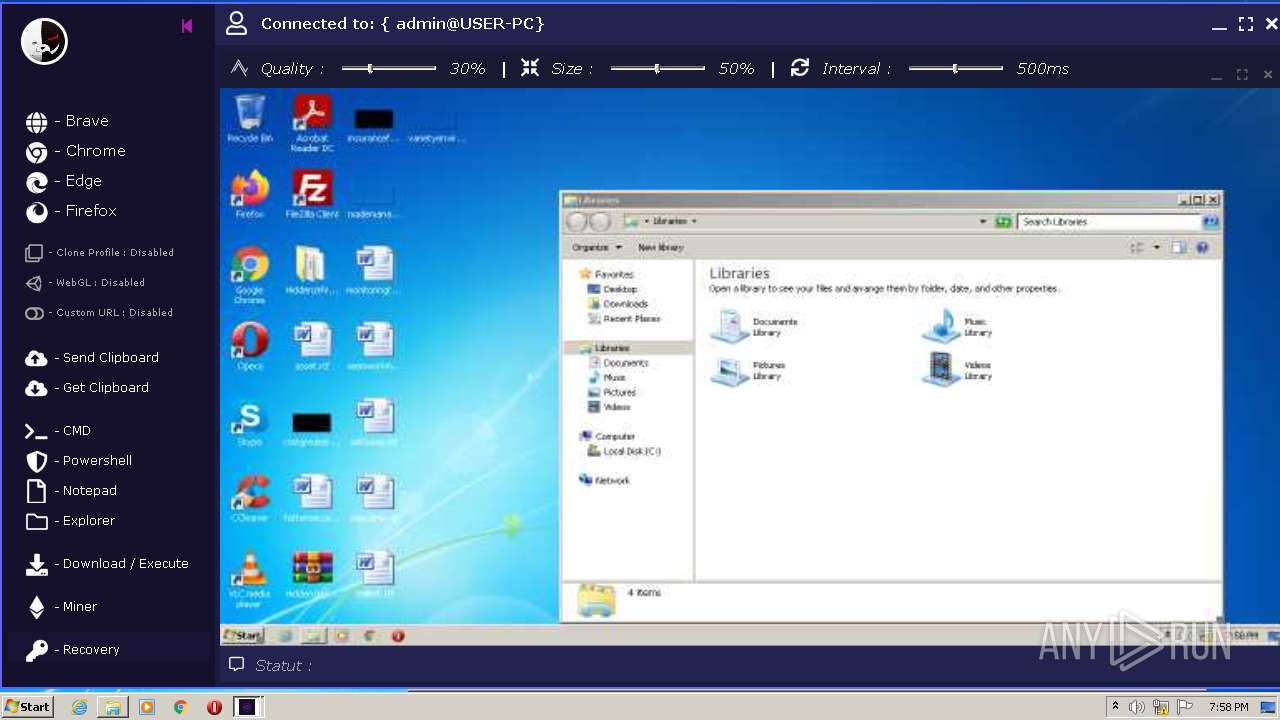
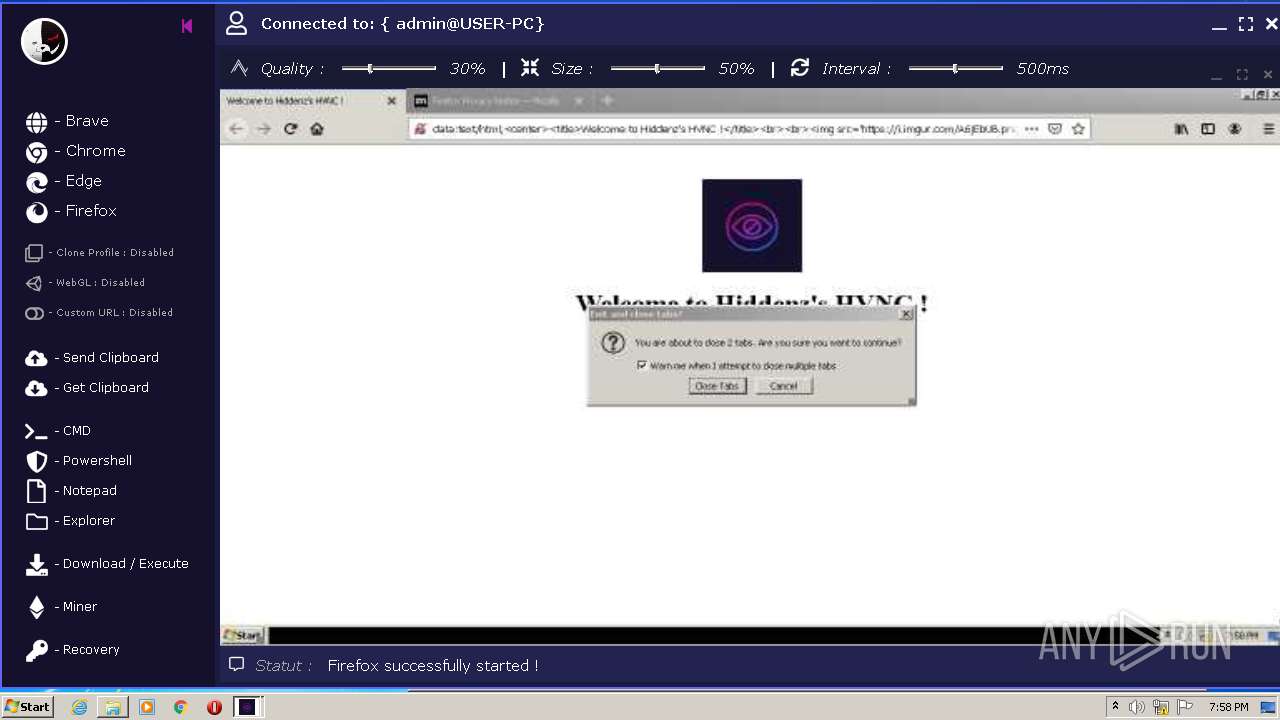
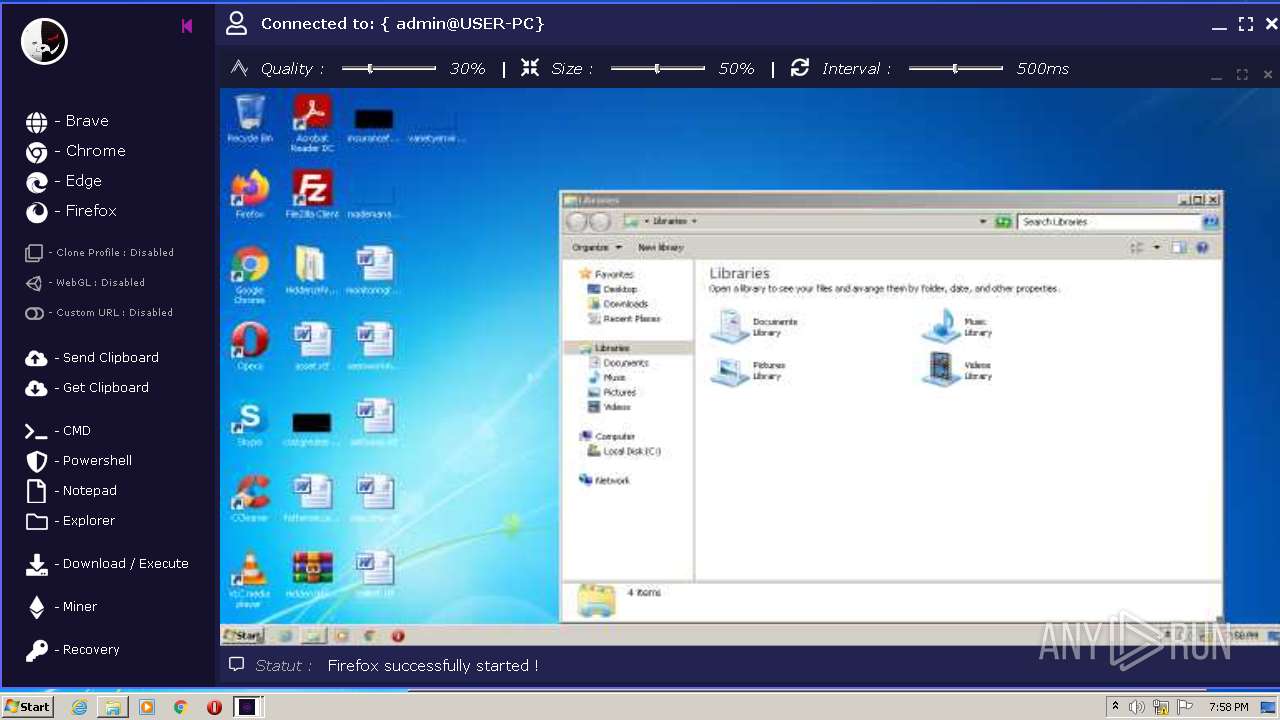
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
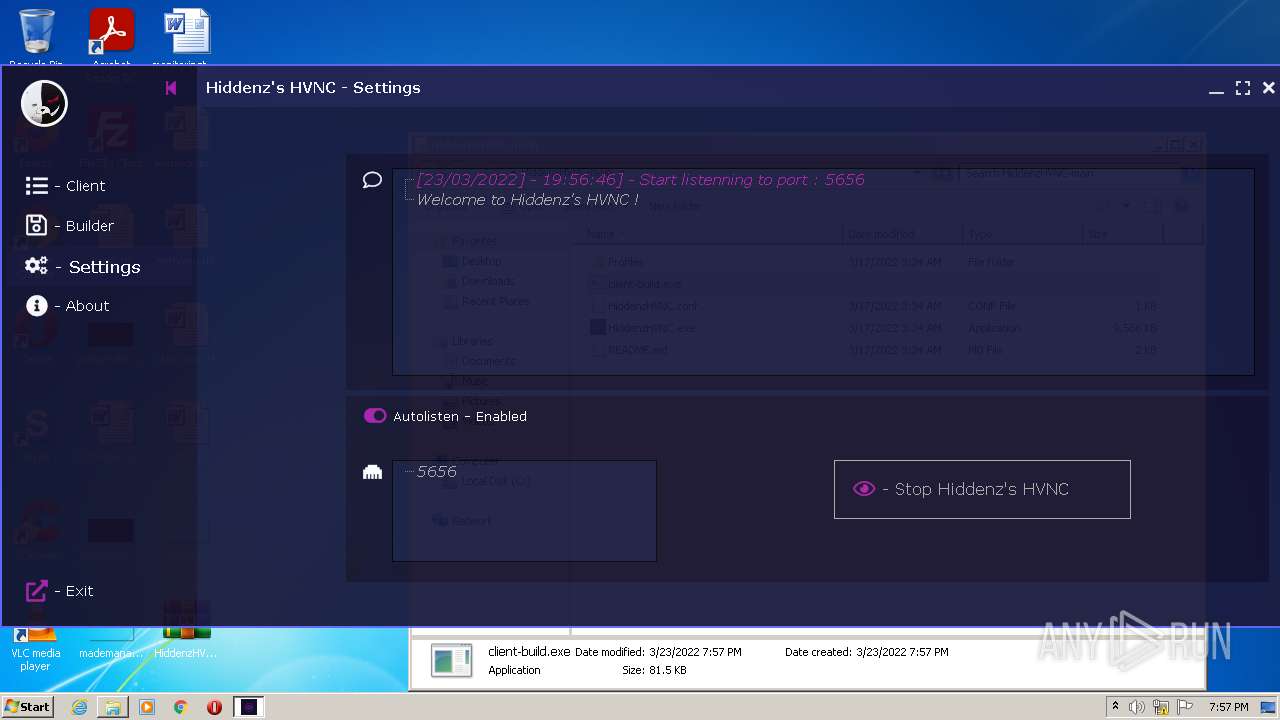
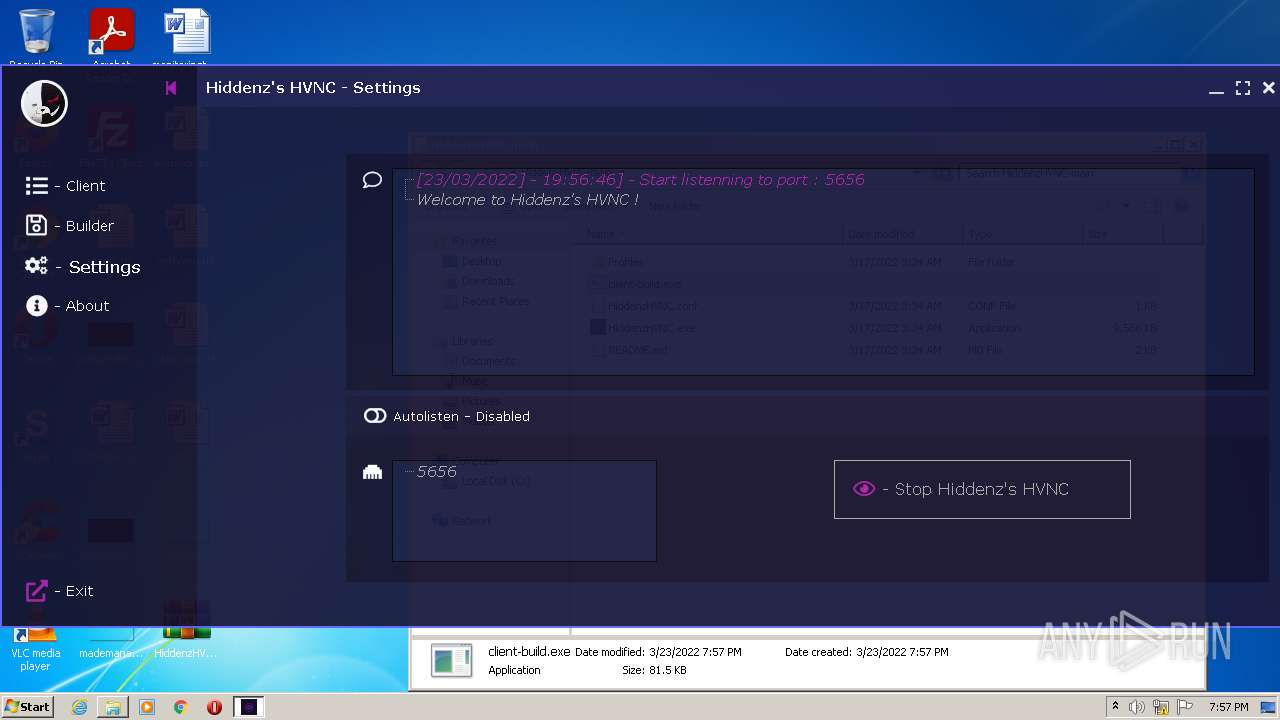
| Analysis date: | March 23, 2022, 19:56:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | C919B3E18F963C41FE39C52C642F327B |
| SHA1: | DF8CB5CEF91F81507BA647AAF8A79379E63F9FB1 |
| SHA256: | 9C96CF41F61F0B8E99371A2B0DE0BBC138BACA42E5203899E604AC358C9B9979 |
| SSDEEP: | 49152:/q/3ENTUyuUm9OCoxkObfq2+062Apvc7QbIxfegQTbi+BuAMw6ngS8up4SPCOEUm:HVUyfm9pdPh2A60MYXe+BuAhFSbQOEUm |
MALICIOUS
Application was dropped or rewritten from another process
- HiddenzHVNC.exe (PID: 3996)
- client-build.exe (PID: 2768)
- client-build.exe (PID: 2472)
Loads the Task Scheduler COM API
- explorer.exe (PID: 3816)
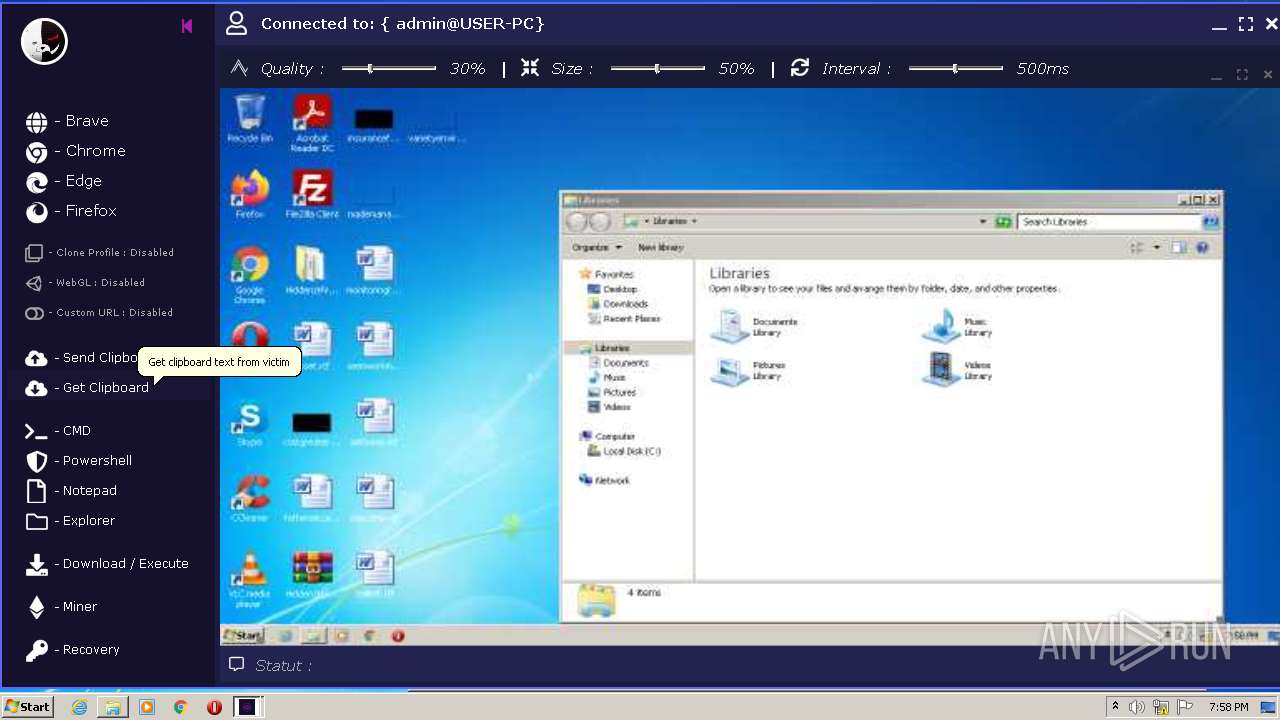
Actions looks like stealing of personal data
- pingsender.exe (PID: 896)
- pingsender.exe (PID: 3556)
- cvtres.exe (PID: 2512)
- pingsender.exe (PID: 3812)
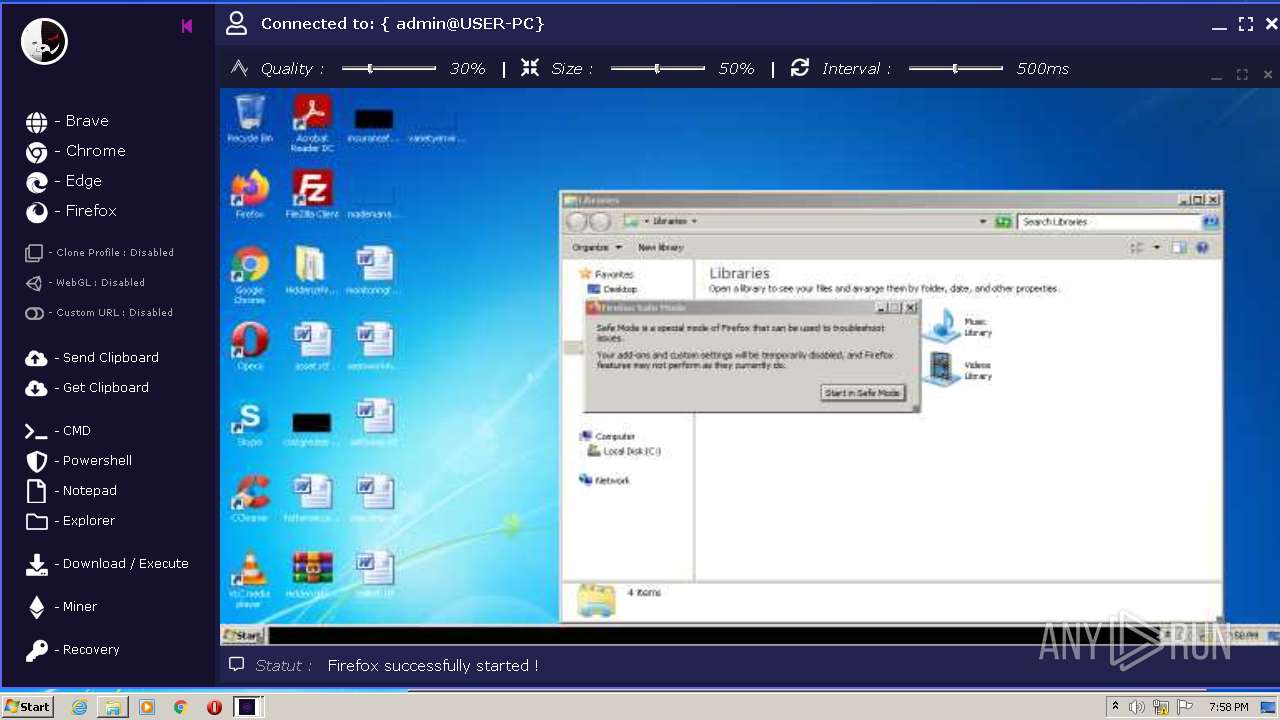
Steals credentials from Web Browsers
- pingsender.exe (PID: 896)
- pingsender.exe (PID: 3556)
- pingsender.exe (PID: 3812)
- cvtres.exe (PID: 2512)
Stealing of credential data
- cvtres.exe (PID: 2512)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 960)
- HiddenzHVNC.exe (PID: 3996)
- cvtres.exe (PID: 2512)
- client-build.exe (PID: 2768)
- client-build.exe (PID: 2472)
- cvtres.exe (PID: 3268)
- pingsender.exe (PID: 896)
- pingsender.exe (PID: 3556)
- pingsender.exe (PID: 3812)
Checks supported languages
- WinRAR.exe (PID: 960)
- client-build.exe (PID: 2768)
- HiddenzHVNC.exe (PID: 3996)
- cvtres.exe (PID: 2512)
- client-build.exe (PID: 2472)
- cvtres.exe (PID: 3268)
- pingsender.exe (PID: 896)
- pingsender.exe (PID: 3556)
- pingsender.exe (PID: 3812)
- cmd.exe (PID: 1252)
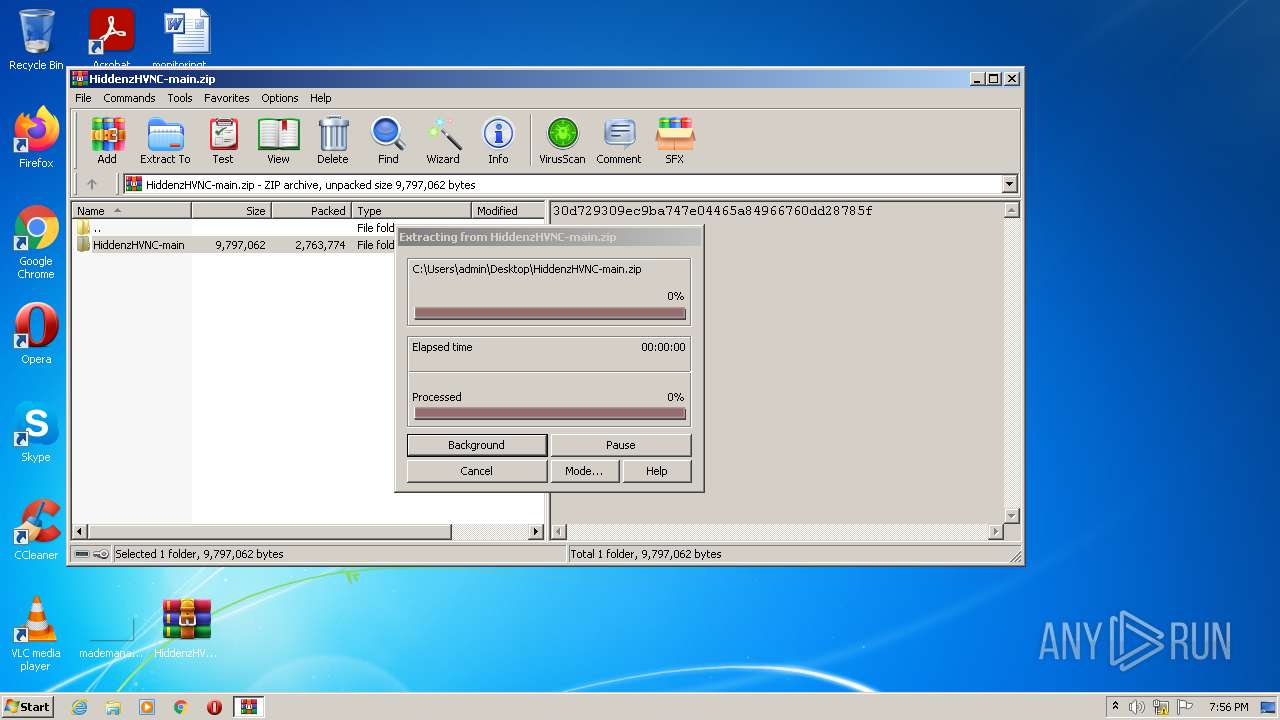
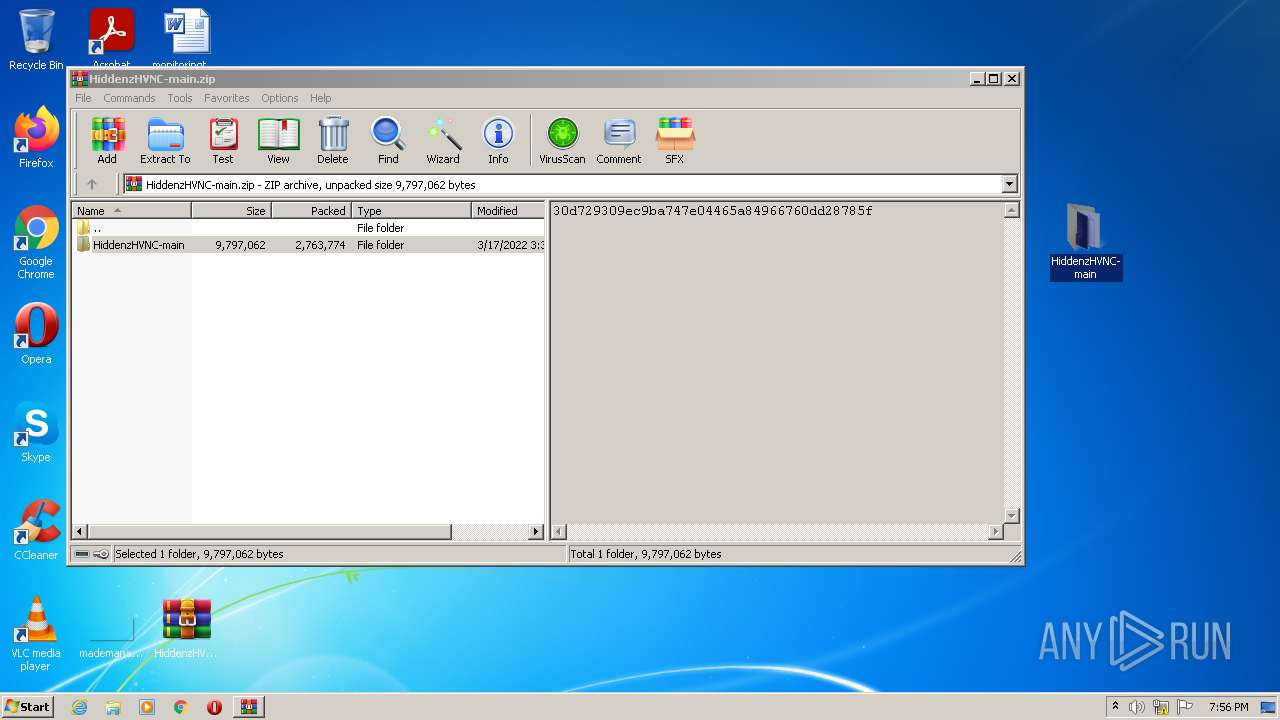
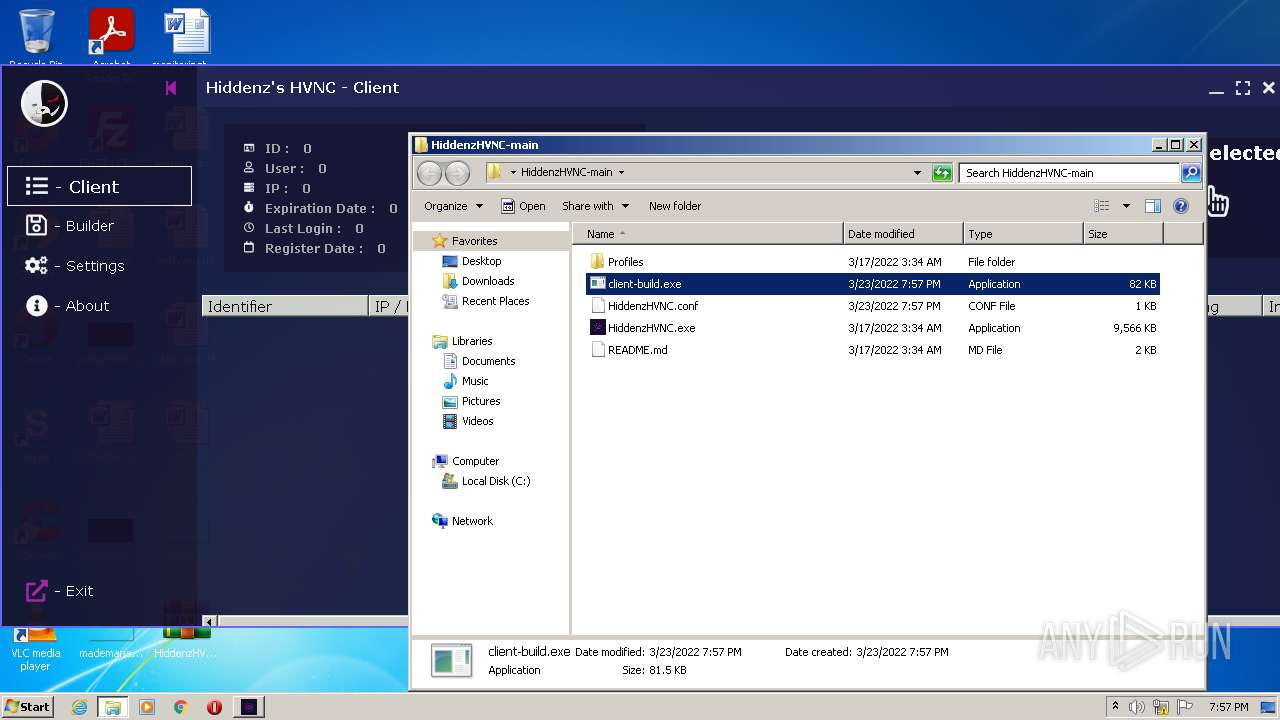
Executable content was dropped or overwritten
- WinRAR.exe (PID: 960)
- HiddenzHVNC.exe (PID: 3996)
- cvtres.exe (PID: 2512)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 960)
- HiddenzHVNC.exe (PID: 3996)
Reads the date of Windows installation
- explorer.exe (PID: 3816)
Reads Environment values
- cvtres.exe (PID: 2512)
Creates files in the user directory
- cvtres.exe (PID: 2512)
Checks for external IP
- cvtres.exe (PID: 2512)
Reads default file associations for system extensions
- explorer.exe (PID: 3816)
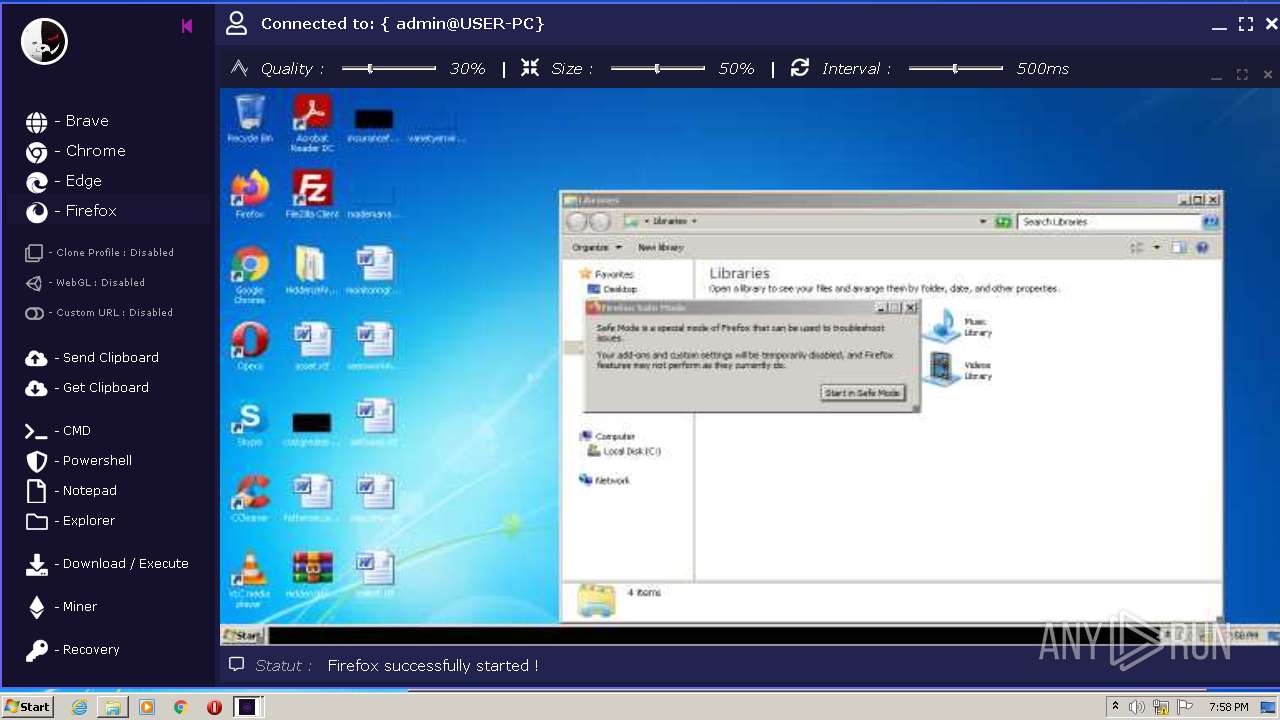
Loads DLL from Mozilla Firefox
- pingsender.exe (PID: 896)
- pingsender.exe (PID: 3556)
- pingsender.exe (PID: 3812)
- cvtres.exe (PID: 2512)
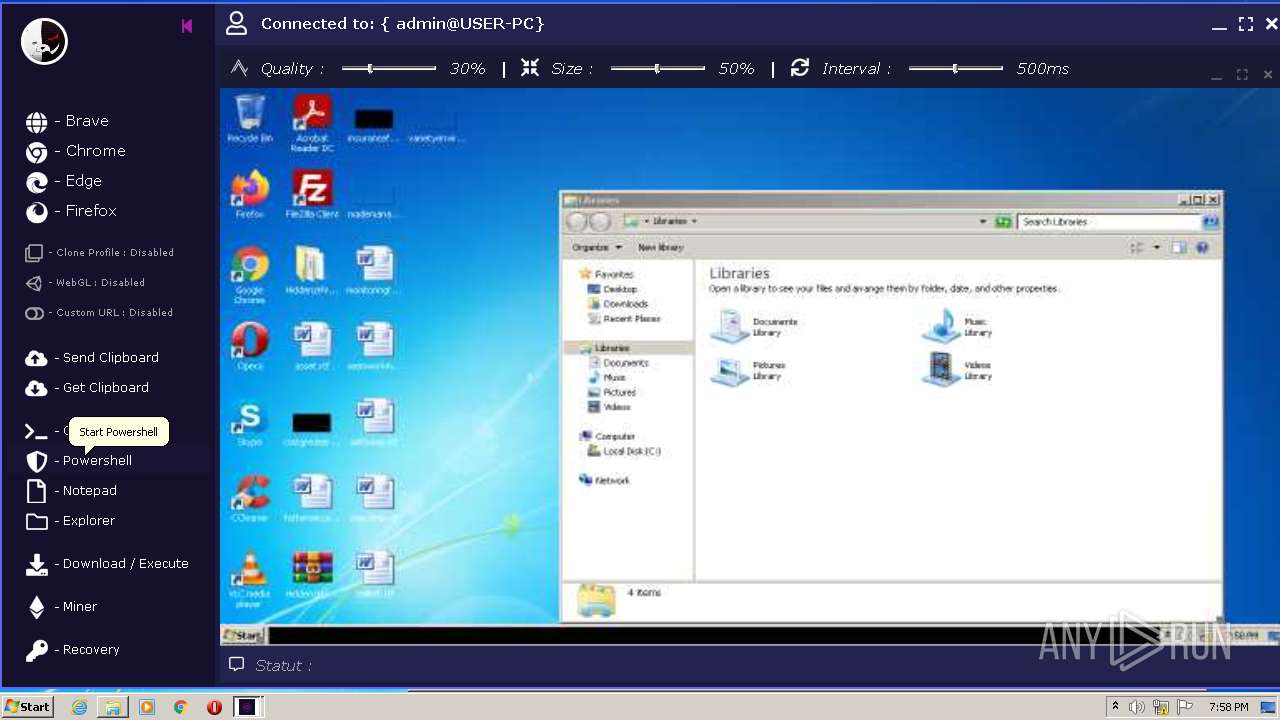
Starts CMD.EXE for commands execution
- cvtres.exe (PID: 2512)
INFO
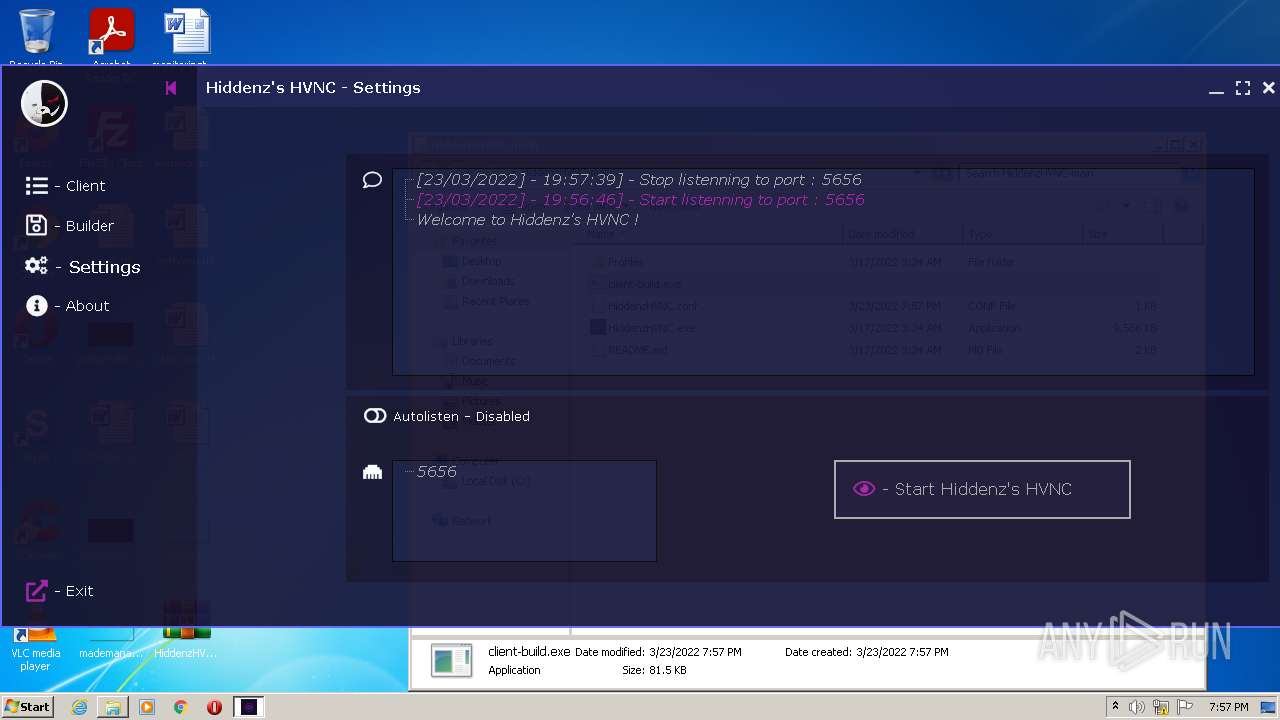
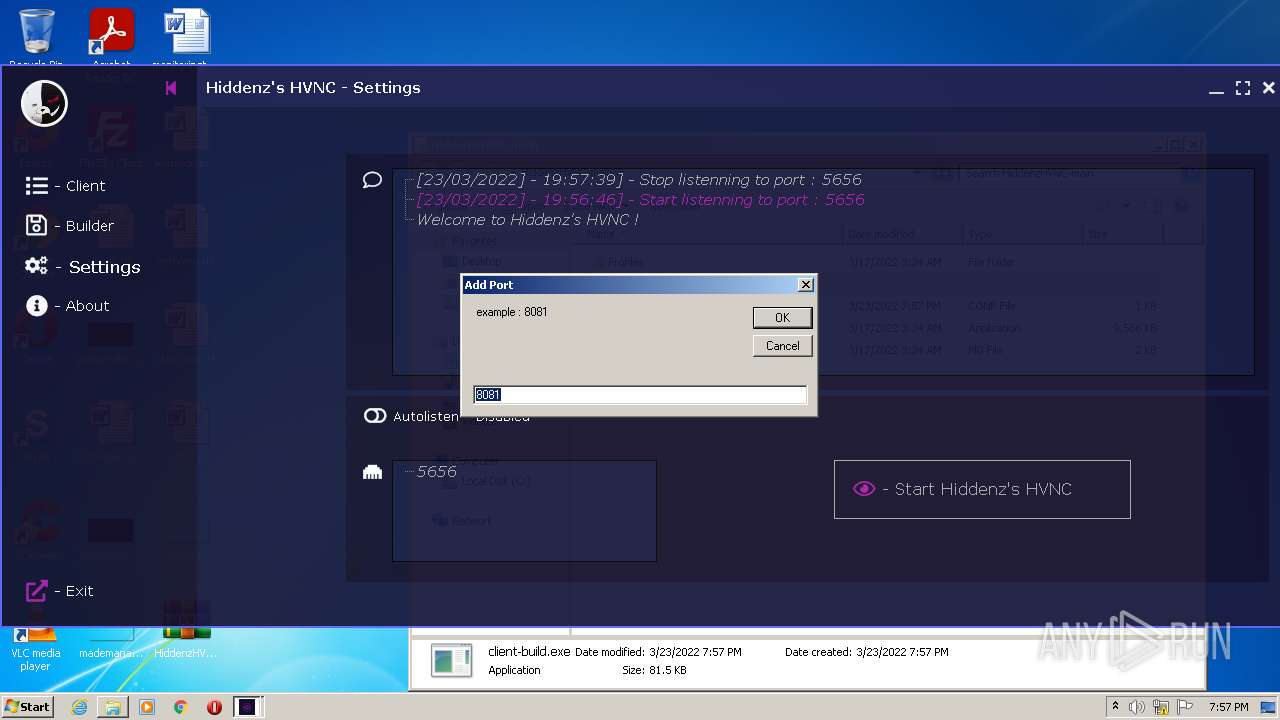
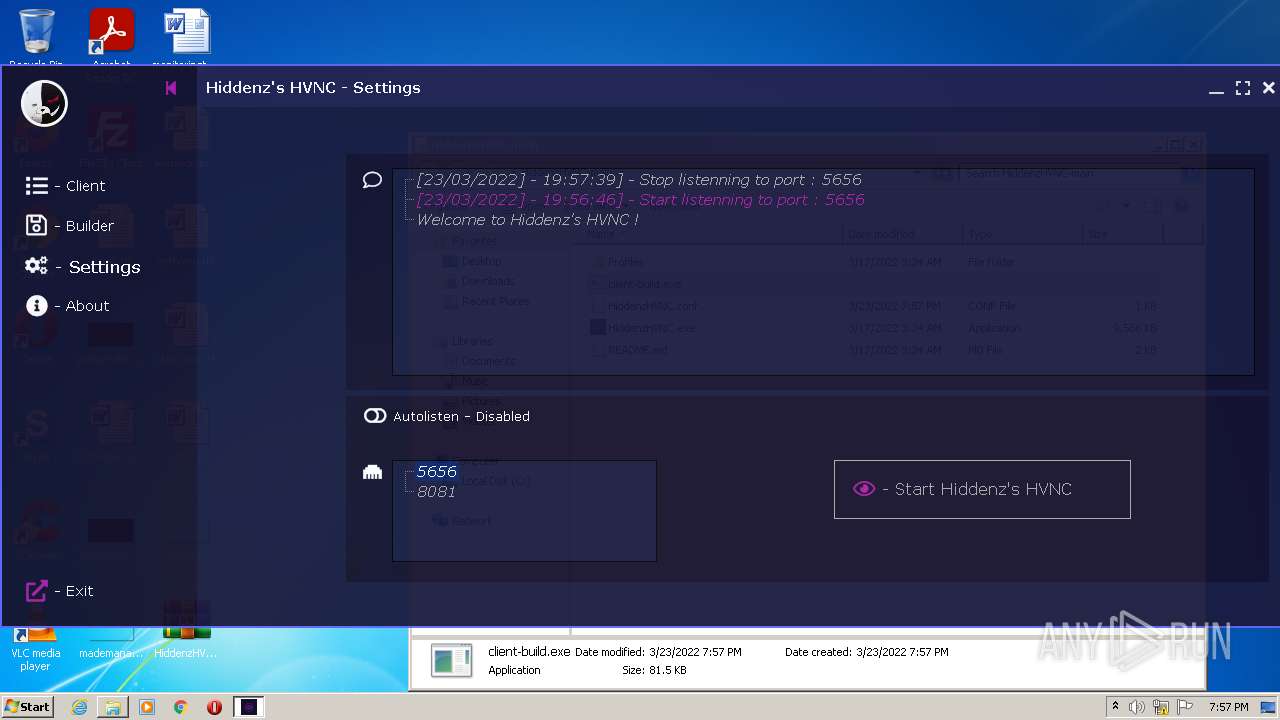
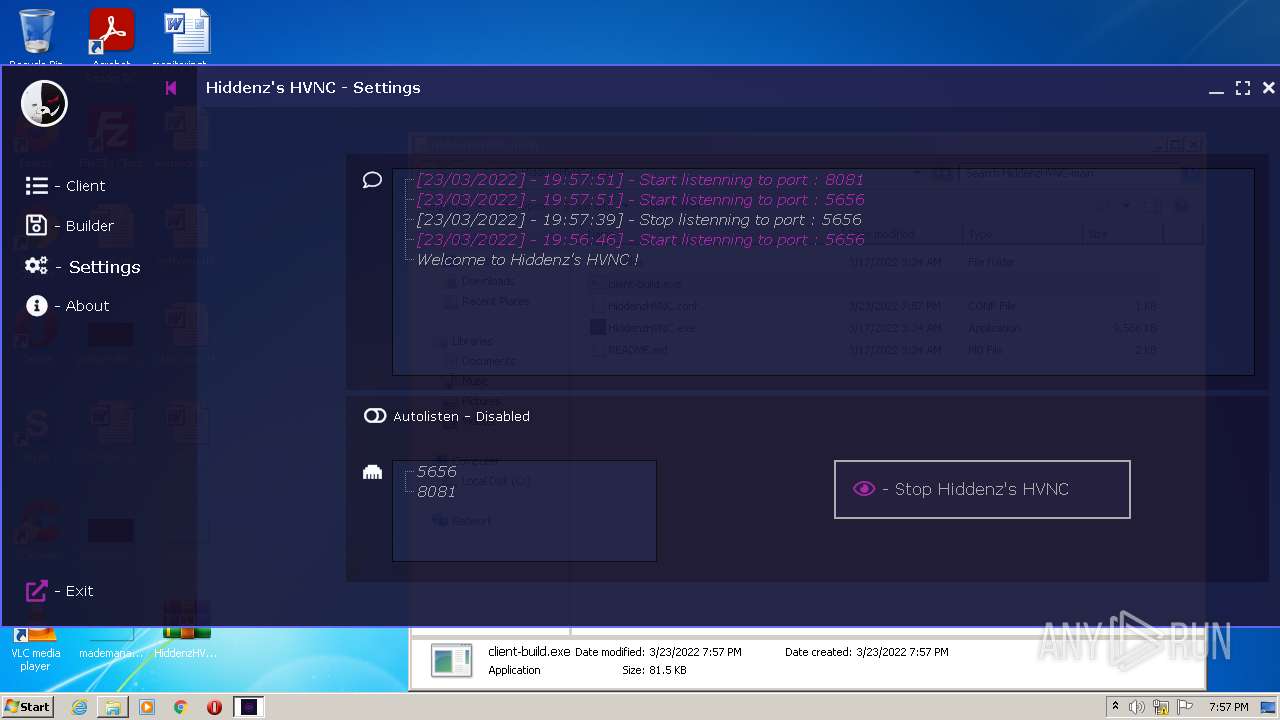
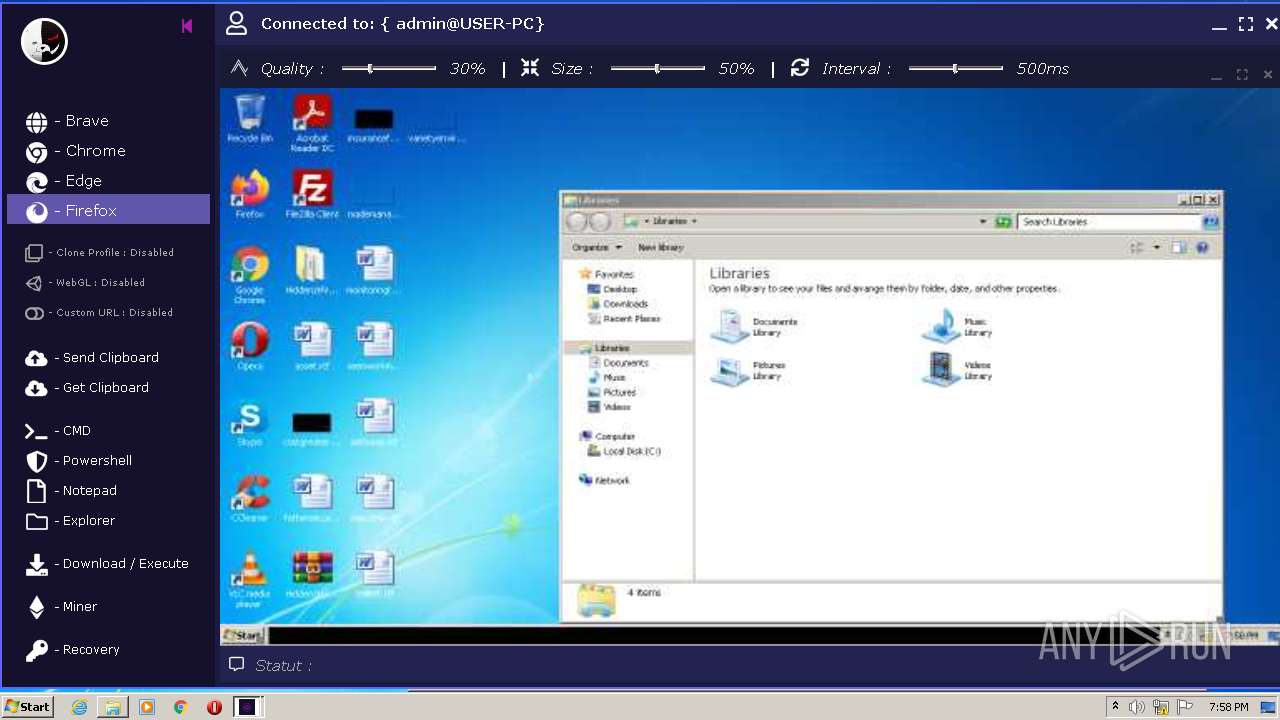
Manual execution by user
- HiddenzHVNC.exe (PID: 3996)
- client-build.exe (PID: 2768)
- client-build.exe (PID: 2472)
Reads the computer name
- explorer.exe (PID: 3816)
- explorer.exe (PID: 2872)
- firefox.exe (PID: 2500)
- firefox.exe (PID: 3588)
- firefox.exe (PID: 2664)
- firefox.exe (PID: 3140)
- firefox.exe (PID: 2708)
- firefox.exe (PID: 1568)
Checks supported languages
- explorer.exe (PID: 3816)
- explorer.exe (PID: 2872)
- firefox.exe (PID: 3032)
- firefox.exe (PID: 2500)
- firefox.exe (PID: 3588)
- firefox.exe (PID: 2664)
- firefox.exe (PID: 3140)
- firefox.exe (PID: 1568)
- firefox.exe (PID: 2708)
Reads CPU info
- firefox.exe (PID: 2500)
Application launched itself
- firefox.exe (PID: 3032)
- firefox.exe (PID: 2500)
Creates files in the program directory
- firefox.exe (PID: 2500)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2500)
Reads the date of Windows installation
- firefox.exe (PID: 2500)
Creates files in the user directory
- firefox.exe (PID: 2500)
Checks Windows Trust Settings
- pingsender.exe (PID: 3556)
- pingsender.exe (PID: 896)
- pingsender.exe (PID: 3812)
Reads settings of System Certificates
- pingsender.exe (PID: 3556)
- pingsender.exe (PID: 896)
- pingsender.exe (PID: 3812)
- cvtres.exe (PID: 2512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | HiddenzHVNC-main/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2022:03:16 20:34:26 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
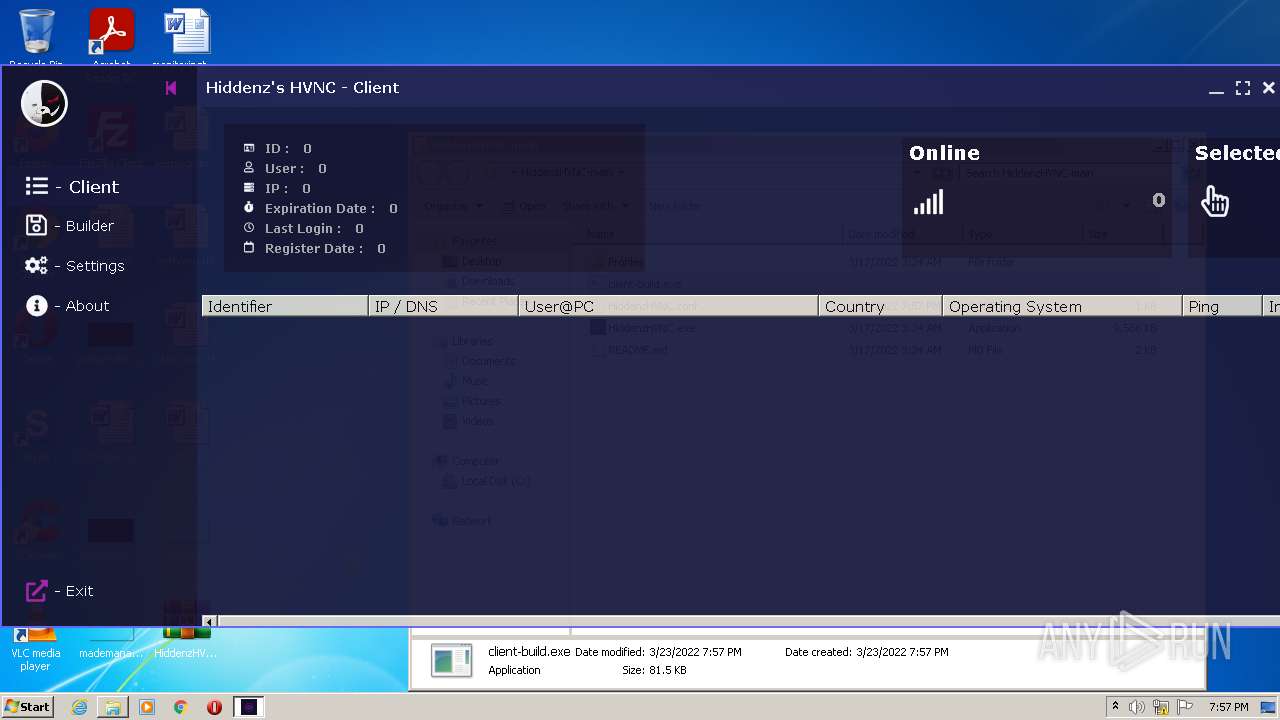
Total processes
66
Monitored processes
19
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/0349ec46-1925-48a7-8f98-b6e7028fe287/new-profile/Firefox/83.0/release/20201112153044?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\Waluigi\saved-telemetry-pings\0349ec46-1925-48a7-8f98-b6e7028fe287 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 960 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\HiddenzHVNC-main.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
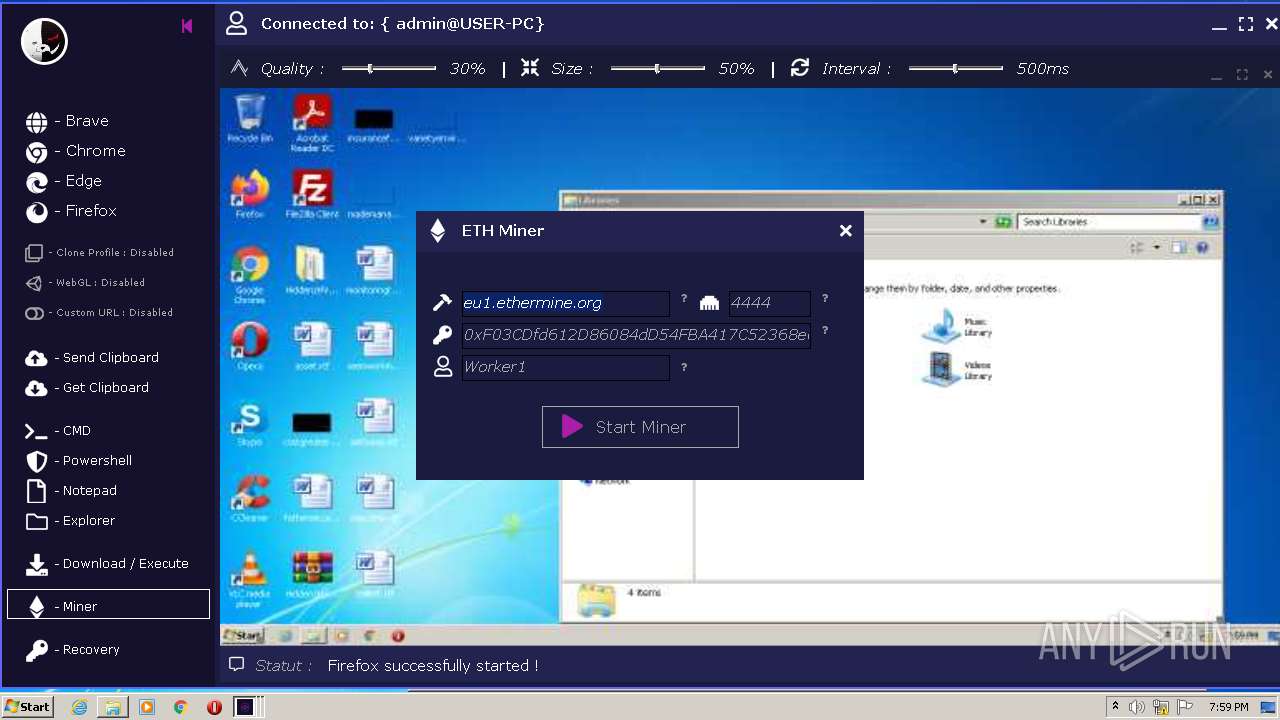
| 1252 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\RQ73BU.exe -P stratum://0xF03CDfd612D86084dD54FBA417C52368e0b20031.5CFY3:Worker1x@eu1.ethermine.org:4444 | C:\Windows\System32\cmd.exe | — | cvtres.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2500.18.993585881\1526709822" -childID 4 -isForBrowser -prefsHandle 4388 -prefMapHandle 4384 -prefsLen 8954 -prefMapSize 229247 -safeMode -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2500 "\\.\pipe\gecko-crash-server-pipe.2500" 4192 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
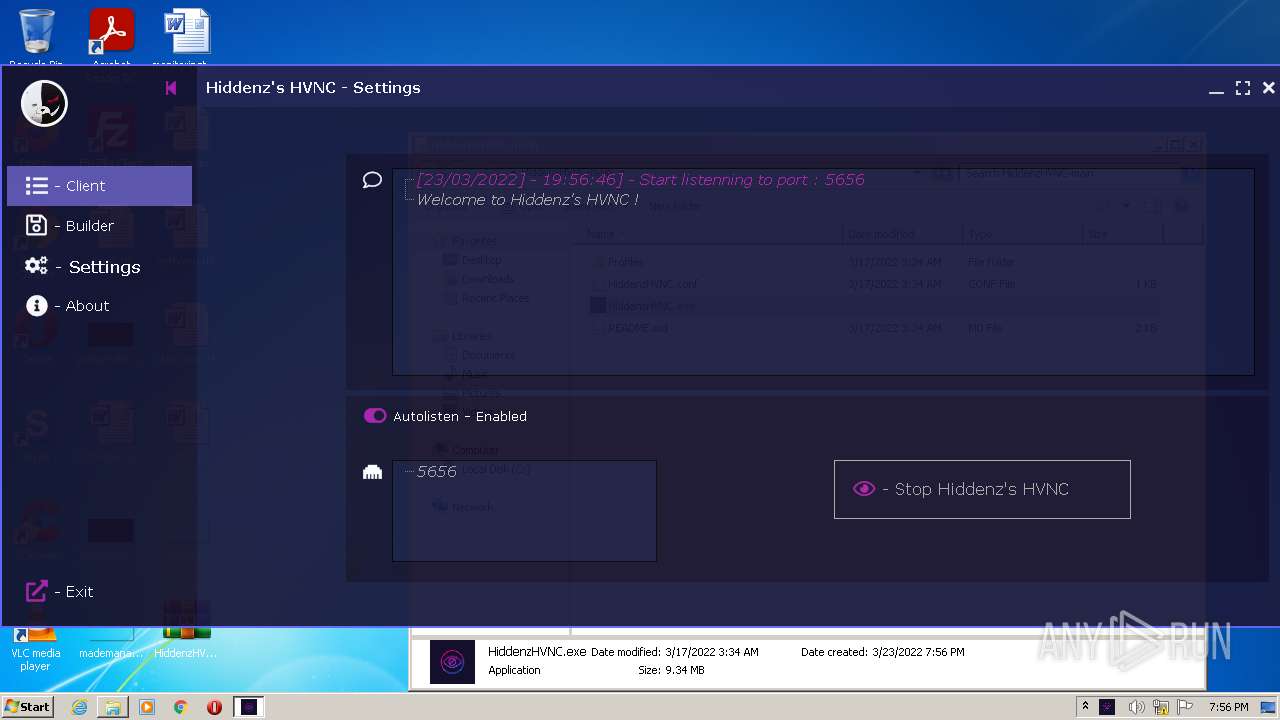
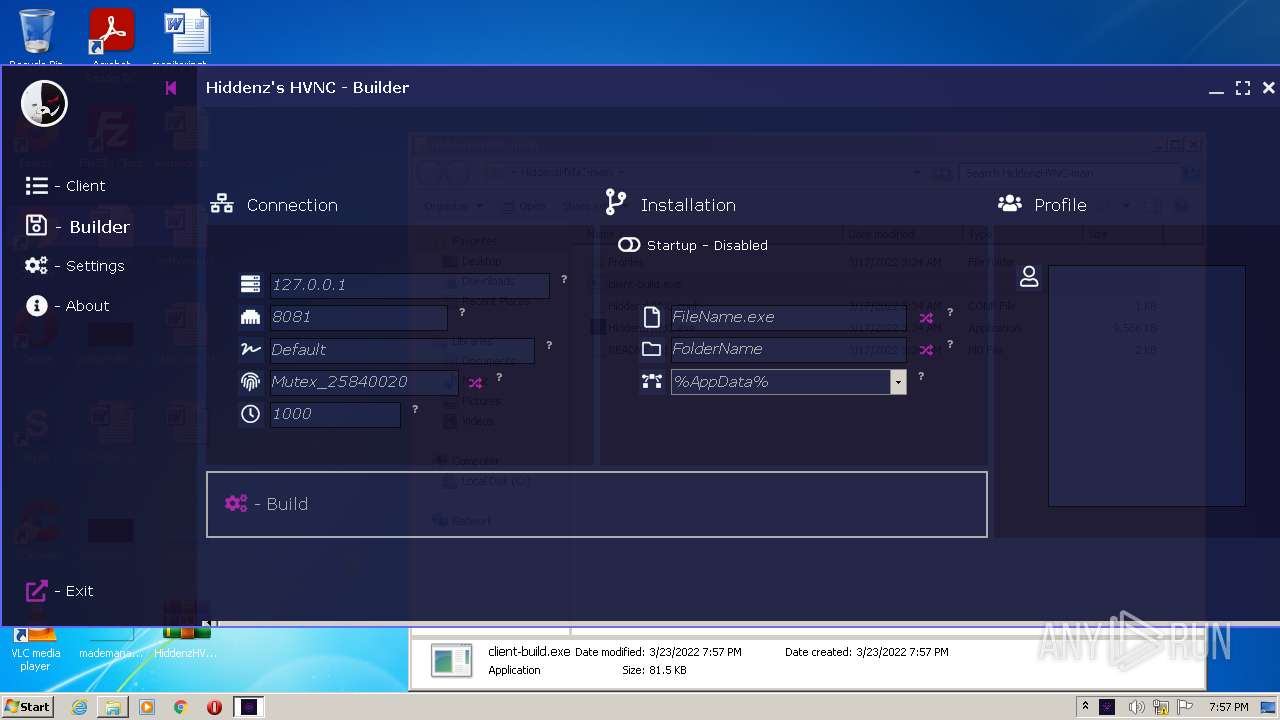
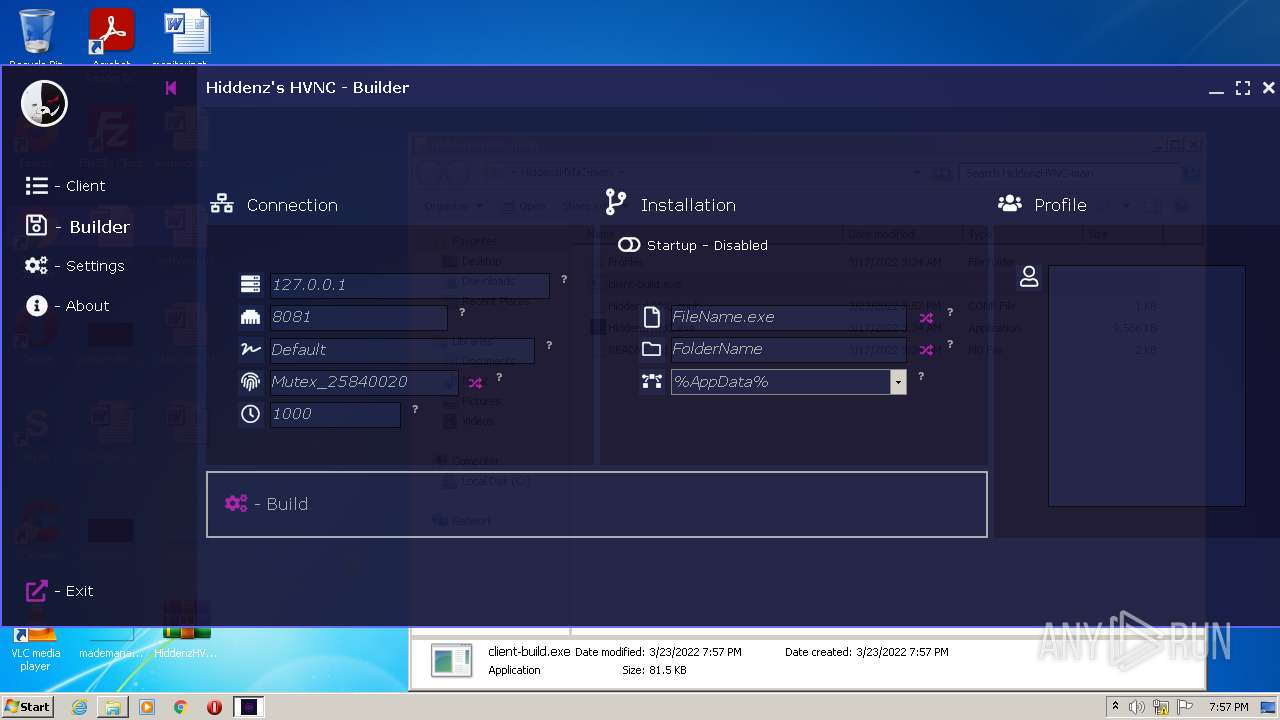
| 2472 | "C:\Users\admin\Desktop\HiddenzHVNC-main\client-build.exe" | C:\Users\admin\Desktop\HiddenzHVNC-main\client-build.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
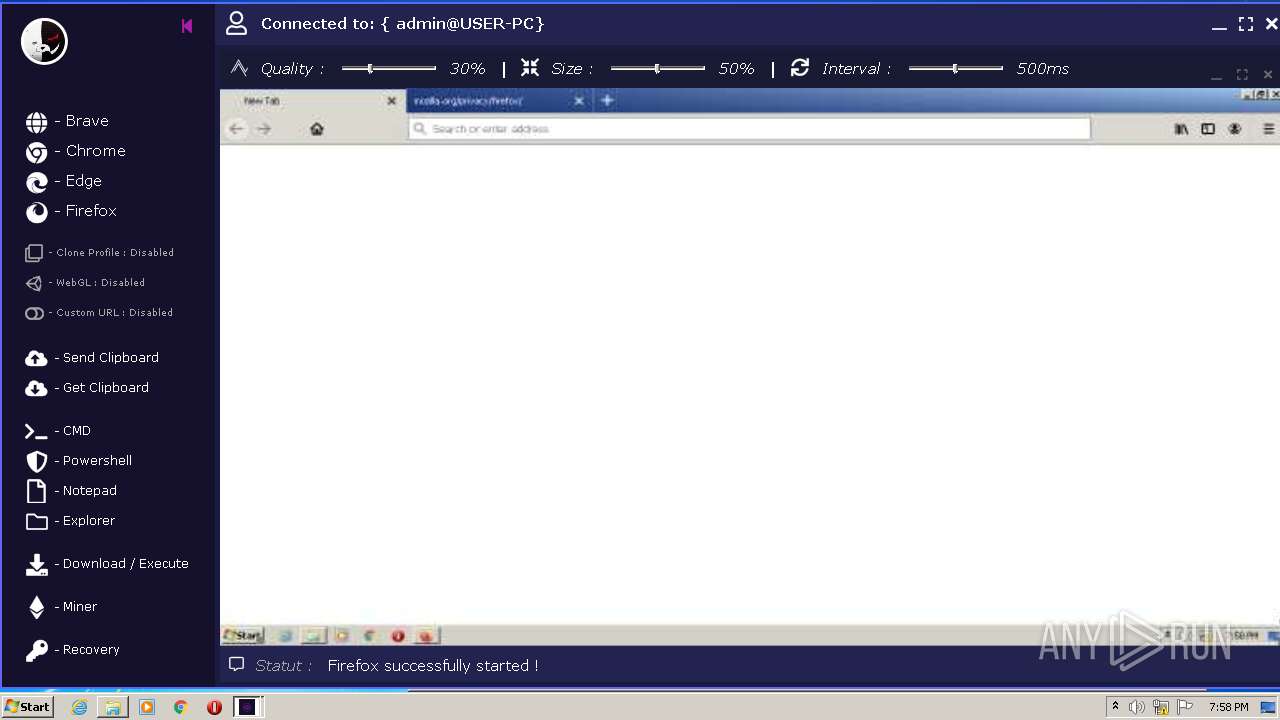
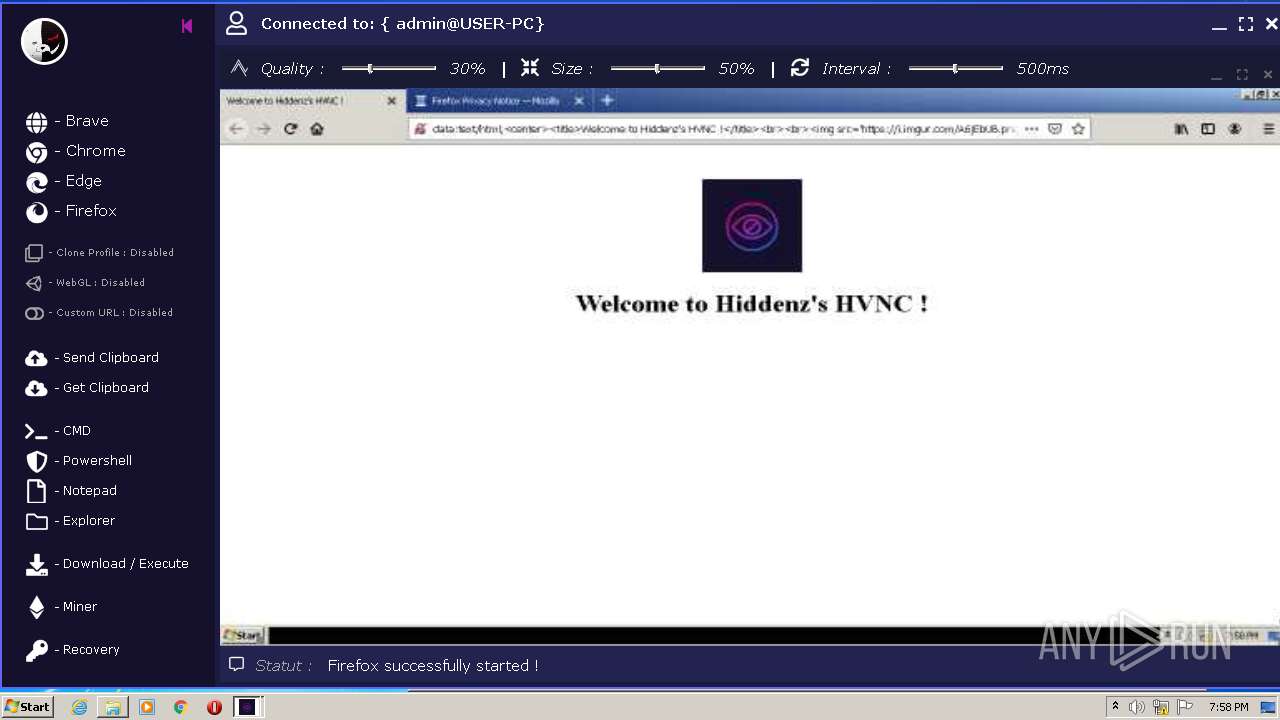
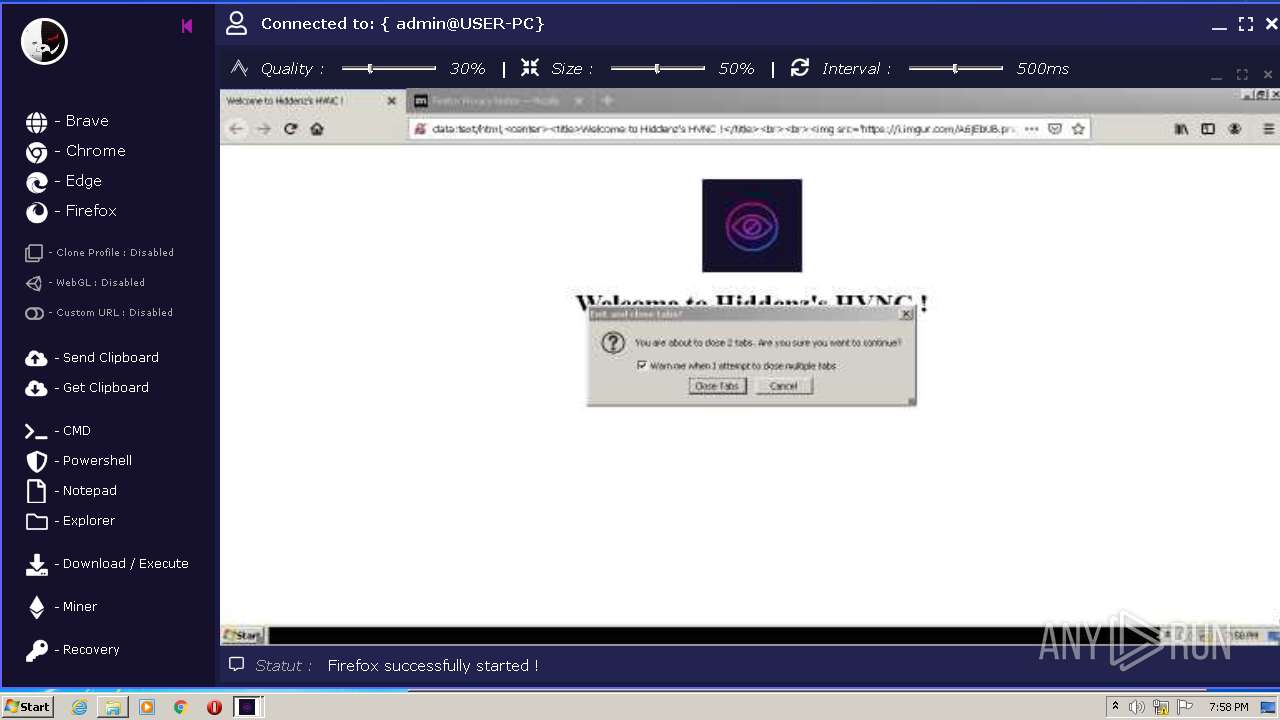
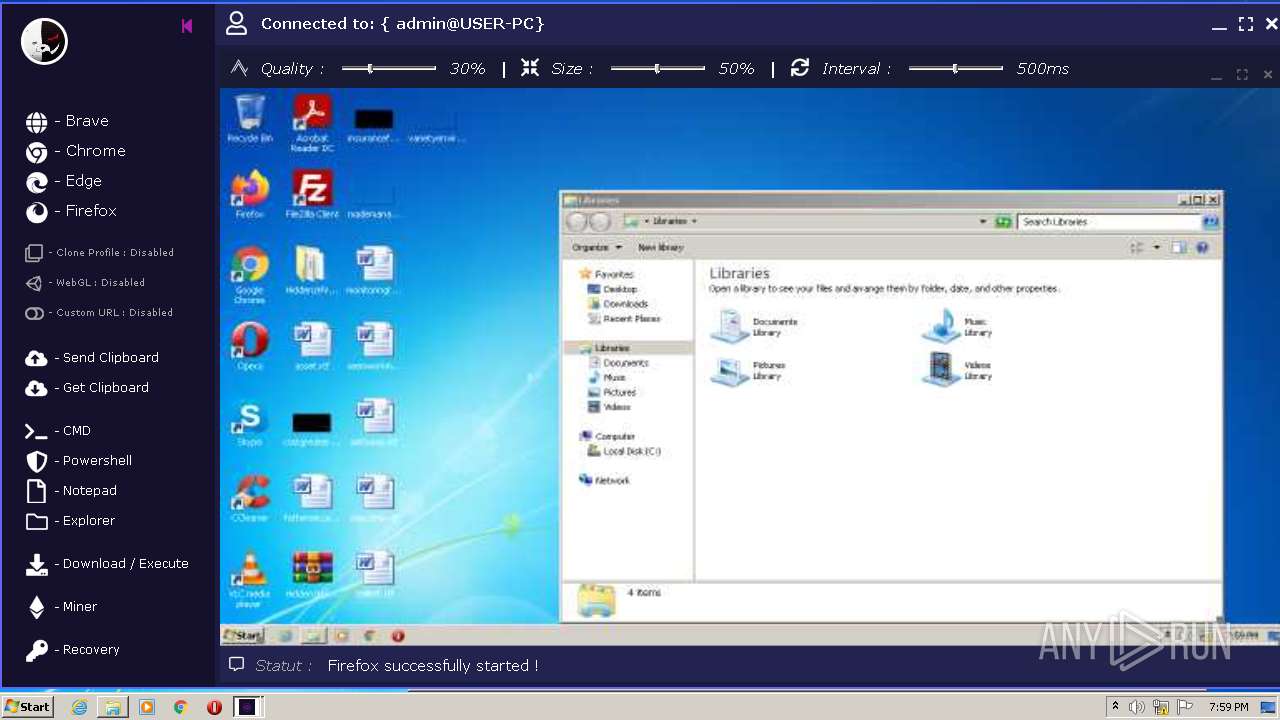
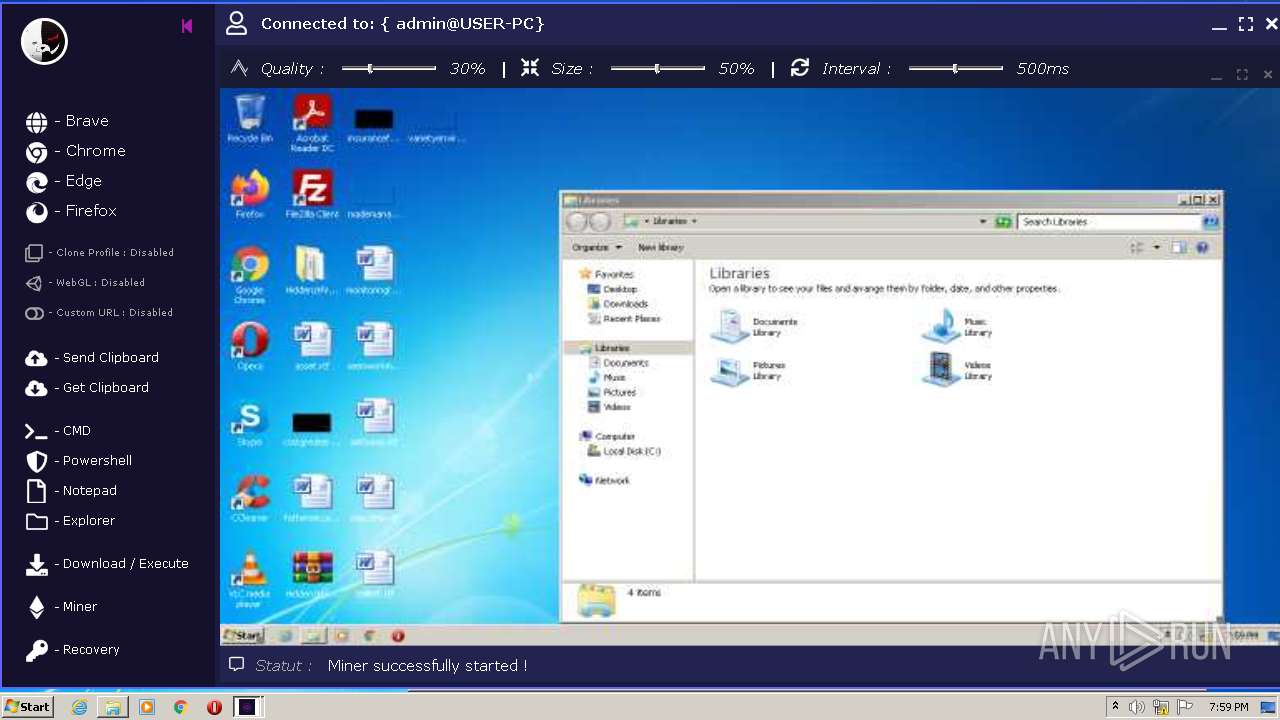
| 2500 | "C:\Program Files\Mozilla Firefox\firefox.exe" -new-window "data:text/html,<center><title>Welcome to Hiddenz's HVNC !</title><br><br><img src='https://i.imgur.com/A6jEbUB.png'><br><h1><font color='black'>Welcome to Hiddenz's HVNC !</font></h1></center>" -safe-mode -no-remote -profile C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\Waluigi | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2512 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | client-build.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft� Resource File To COFF Object Conversion Utility Exit code: 2147943401 Version: 12.00.51209.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2500.6.1675066717\1983759042" -childID 2 -isForBrowser -prefsHandle 2220 -prefMapHandle 2216 -prefsLen 140 -prefMapSize 229247 -safeMode -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2500 "\\.\pipe\gecko-crash-server-pipe.2500" 1224 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2500.24.1185498733\650244936" -childID 5 -isForBrowser -prefsHandle 3576 -prefMapHandle 4136 -prefsLen 9743 -prefMapSize 229247 -safeMode -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2500 "\\.\pipe\gecko-crash-server-pipe.2500" 3904 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2768 | "C:\Users\admin\Desktop\HiddenzHVNC-main\client-build.exe" | C:\Users\admin\Desktop\HiddenzHVNC-main\client-build.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
47 995
Read events
47 687
Write events
305
Delete events
3
Modification events
| (PID) Process: | (960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (960) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\HiddenzHVNC-main.zip | |||
| (PID) Process: | (960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
165
Text files
109
Unknown types
63
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | cvtres.exe | C:\Users\admin\AppData\Roaming\RegisterDate | text | |
MD5:— | SHA256:— | |||
| 3996 | HiddenzHVNC.exe | C:\Users\admin\Desktop\HiddenzHVNC-main\dymc1apj.newcfg | xml | |
MD5:— | SHA256:— | |||
| 3996 | HiddenzHVNC.exe | C:\Users\admin\Desktop\HiddenzHVNC-main\shvkk2ix.newcfg | xml | |
MD5:— | SHA256:— | |||
| 960 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa960.5433\HiddenzHVNC-main\HiddenzHVNC.conf | xml | |
MD5:93A58F0C377CE9B8C3B492D49AF020F6 | SHA256:D82E6A73A4C5CAB008DB92AF235C5AAD57A7A61DBAE27062C834B78A835C5D62 | |||
| 2500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\Waluigi\cookies.sqlite-journal | binary | |
MD5:— | SHA256:— | |||
| 3996 | HiddenzHVNC.exe | C:\Users\admin\Desktop\HiddenzHVNC-main\l2likmsl.newcfg | xml | |
MD5:— | SHA256:— | |||
| 2500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\Waluigi\prefs.js | text | |
MD5:— | SHA256:— | |||
| 2500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\Waluigi\permissions.sqlite-journal | binary | |
MD5:— | SHA256:— | |||
| 2500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\Waluigi\prefs-1.js | text | |
MD5:— | SHA256:— | |||
| 2500 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\Waluigi\extensions.json | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
40
DNS requests
101
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2500 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2500 | firefox.exe | POST | 200 | 92.123.194.91:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
2500 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2500 | firefox.exe | POST | 200 | 92.123.194.91:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
896 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2500 | firefox.exe | POST | 200 | 108.156.253.168:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
2500 | firefox.exe | POST | 200 | 108.156.253.168:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
2500 | firefox.exe | POST | 200 | 92.123.194.91:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
2500 | firefox.exe | POST | 200 | 92.123.194.91:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
2500 | firefox.exe | POST | 200 | 92.123.194.91:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2512 | cvtres.exe | 132.226.247.73:80 | checkip.dyndns.org | Oracle Corporation | US | malicious |
2500 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
2500 | firefox.exe | 108.157.3.185:443 | www.mozilla.org | — | US | unknown |
2500 | firefox.exe | 143.204.98.33:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
2500 | firefox.exe | 151.101.112.193:443 | i.imgur.com | Fastly | US | malicious |
2500 | firefox.exe | 35.161.134.161:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2500 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2500 | firefox.exe | 18.66.248.105:443 | content-signature-2.cdn.mozilla.net | Massachusetts Institute of Technology | US | unknown |
2500 | firefox.exe | 54.148.56.186:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2500 | firefox.exe | 3.88.122.21:443 | spocs.getpocket.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
checkip.dyndns.org |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
www.mozilla.org |
| whitelisted |
www.mozorg.moz.works |
| suspicious |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
i.imgur.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
— | — | Misc activity | AV INFO Query to checkip.dyndns. Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
— | — | Misc activity | AV INFO Query to checkip.dyndns. Domain |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
— | — | Misc activity | AV INFO Query to checkip.dyndns. Domain |
2512 | cvtres.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
2500 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2500 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
1 ETPRO signatures available at the full report