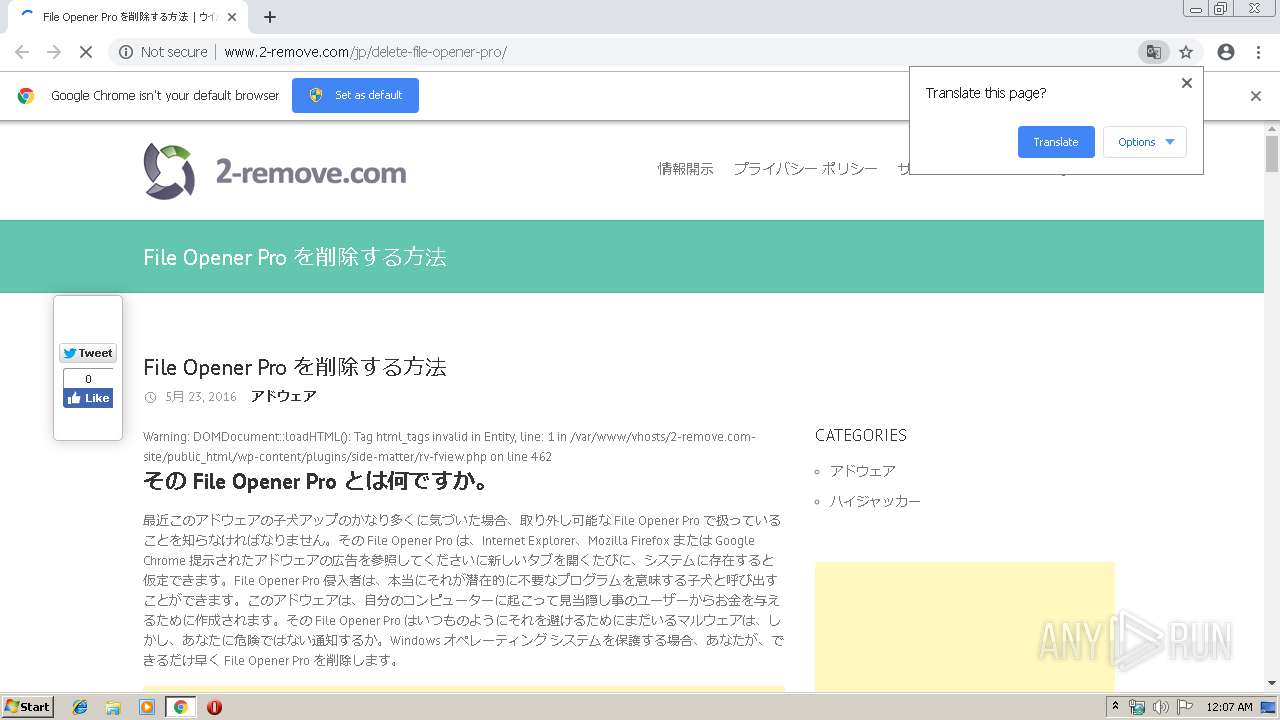
| URL: | http://www.2-remove.com/jp/delete-file-opener-pro/ |
| Full analysis: | https://app.any.run/tasks/06412b58-dfb3-4ce1-b9e6-c0b1be301536 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 00:07:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2056A473276E0D77E5D48838826C50C3 |
| SHA1: | 45BF94D440F98489E077048071F8C54AC51A0D5B |
| SHA256: | 9C942447B37981BB8F644B6B5C8BD70C1E23041139F71FA0CD0DDFAE5E538501 |
| SSDEEP: | 3:N1KJS4YdPgBs0ADOvoXR:Cc4Yd4pASvoB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3336)
INFO
Application launched itself
- chrome.exe (PID: 3336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa30f18,0x6fa30f28,0x6fa30f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9383753417929605512,13871647843689479341,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9298514447782918640 --mojo-platform-channel-handle=4440 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9383753417929605512,13871647843689479341,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2520758985842316597 --mojo-platform-channel-handle=4232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=908,9383753417929605512,13871647843689479341,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16584362463007797047 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9383753417929605512,13871647843689479341,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8745439784947723167 --mojo-platform-channel-handle=4364 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,9383753417929605512,13871647843689479341,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14678881601465557960 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14678881601465557960 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9383753417929605512,13871647843689479341,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3920043770086117321 --mojo-platform-channel-handle=1512 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9383753417929605512,13871647843689479341,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1854817752143511285 --mojo-platform-channel-handle=4436 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9383753417929605512,13871647843689479341,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2972366677451343420 --mojo-platform-channel-handle=4352 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,9383753417929605512,13871647843689479341,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5806197716934720798 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5806197716934720798 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
562
Read events
477
Write events
81
Delete events
4
Modification events
| (PID) Process: | (3284) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3336-13197686864693625 |
Value: 259 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
94
Text files
111
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7bfe2803-05a8-46af-9a2c-ae466921c80c.tmp | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
67
DNS requests
47
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2512 | chrome.exe | GET | 200 | 192.169.197.22:80 | http://www.2-remove.com/wp-content/plugins/social-comments/assets/css/social_comments.css?ver=3.9.1 | US | text | 835 b | unknown |
2512 | chrome.exe | GET | 200 | 192.169.197.22:80 | http://www.2-remove.com/wp-content/themes/interface/style.css?ver=3.9.1 | US | text | 11.1 Kb | unknown |
2512 | chrome.exe | GET | 200 | 192.169.197.22:80 | http://www.2-remove.com/jp/delete-file-opener-pro/ | US | html | 9.75 Kb | unknown |
2512 | chrome.exe | GET | 200 | 192.169.197.22:80 | http://www.2-remove.com/wp-content/themes/interface/css/responsive.css?ver=3.9.1 | US | text | 2.41 Kb | unknown |
2512 | chrome.exe | GET | 200 | 192.169.197.22:80 | http://www.2-remove.com/wp-content/plugins/side-matter/js/jquery.autosize.js?ver=3.9.1 | US | text | 2.92 Kb | unknown |
2512 | chrome.exe | GET | 200 | 192.169.197.22:80 | http://www.2-remove.com/wp-content/themes/interface/js/scripts.js?ver=3.9.1 | US | text | 418 b | unknown |
2512 | chrome.exe | GET | 200 | 192.169.197.22:80 | http://www.2-remove.com/wp-content/plugins/side-matter/css/style.css?ver=3.9.1 | US | text | 954 b | unknown |
2512 | chrome.exe | GET | 200 | 192.169.197.22:80 | http://www.2-remove.com/wp-content/uploads/2015/01/winxp-remove-program.png | US | image | 38.0 Kb | unknown |
2512 | chrome.exe | GET | 200 | 192.169.197.22:80 | http://www.2-remove.com/wp-content/uploads/2015/01/winxp-startmenu.png | US | image | 90.1 Kb | unknown |
2512 | chrome.exe | GET | 200 | 192.169.197.22:80 | http://www.2-remove.com/wp-content/uploads/2015/01/winxp-add-remove-programs.png | US | image | 163 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2512 | chrome.exe | 172.217.22.98:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2512 | chrome.exe | 172.217.16.162:443 | adservice.google.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 199.16.156.236:443 | r.twimg.com | Twitter Inc. | US | unknown |
2512 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 192.169.197.22:80 | www.2-remove.com | GoDaddy.com, LLC | US | unknown |
2512 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 216.58.205.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 172.217.16.130:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 172.217.21.195:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 63.215.202.80:80 | www.tqlkg.com | Conversant, Inc. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.2-remove.com |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.tqlkg.com |
| whitelisted |
2-remove.com |
| unknown |
platform.twitter.com |
| whitelisted |
www.facebook.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2512 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible Keitaro TDS Redirect |