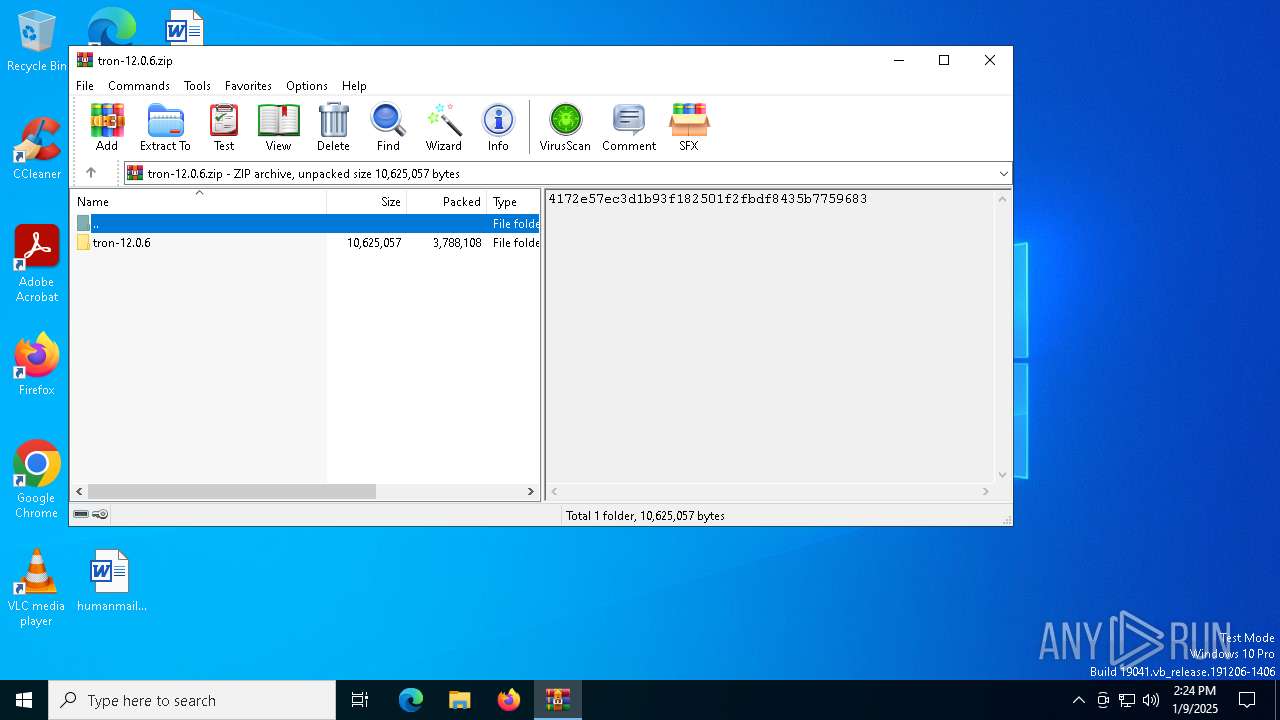
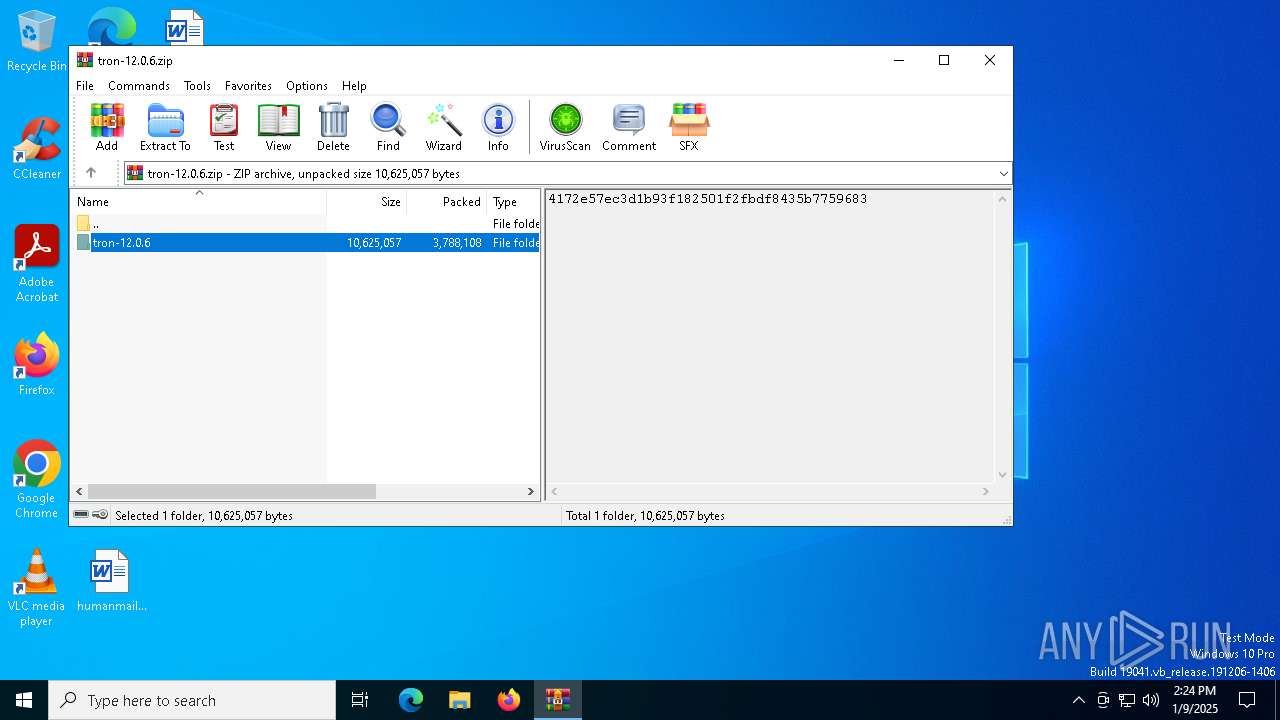
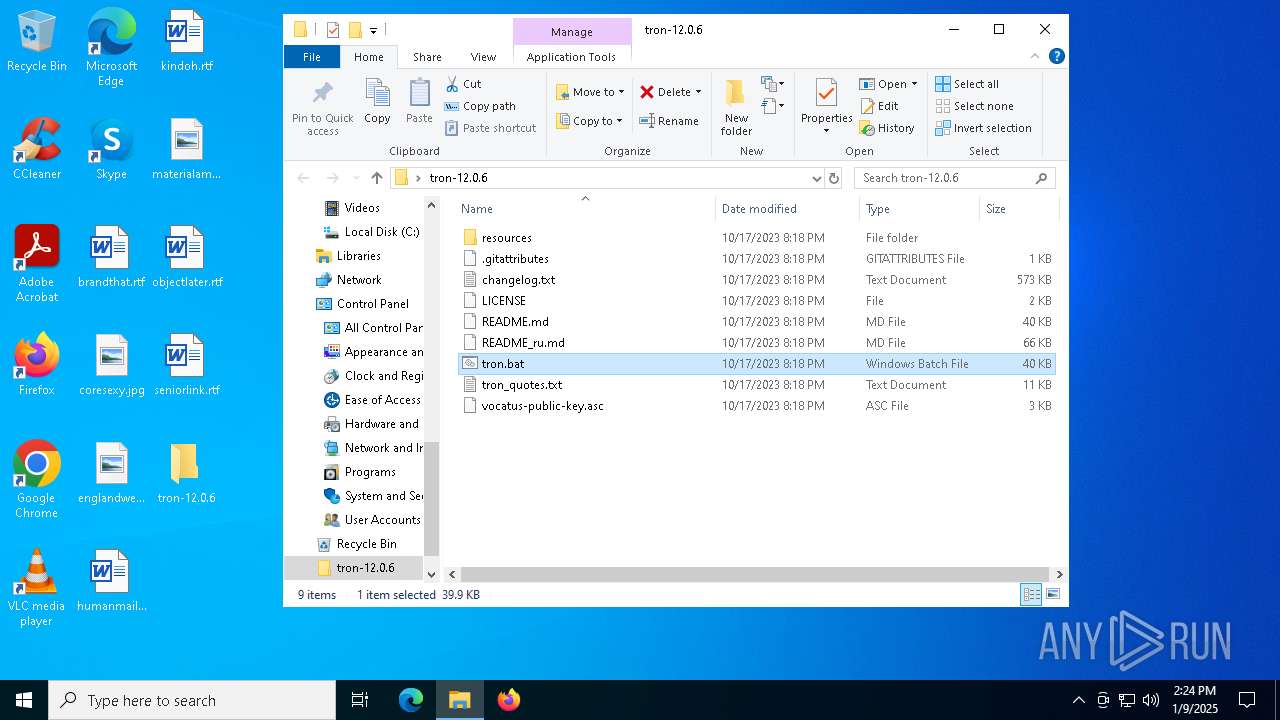
| File name: | tron-12.0.6.zip |
| Full analysis: | https://app.any.run/tasks/f6186215-601a-41a7-a5fe-708c11799c53 |
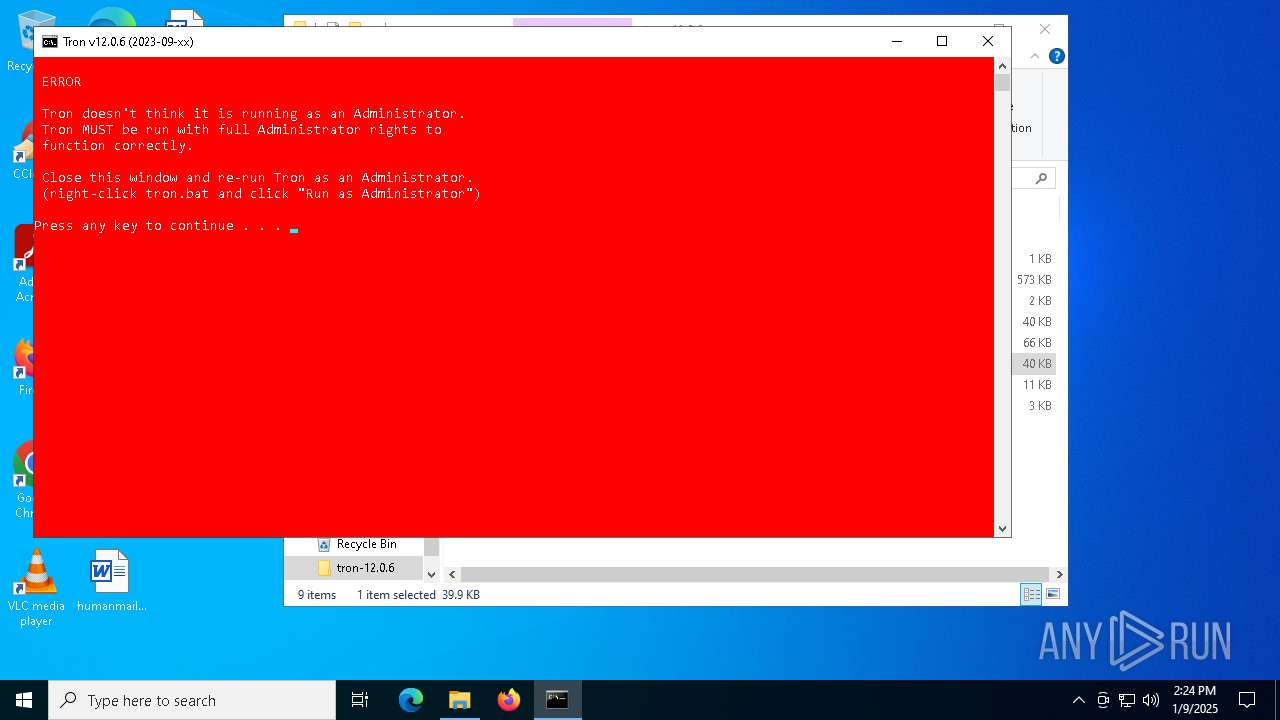
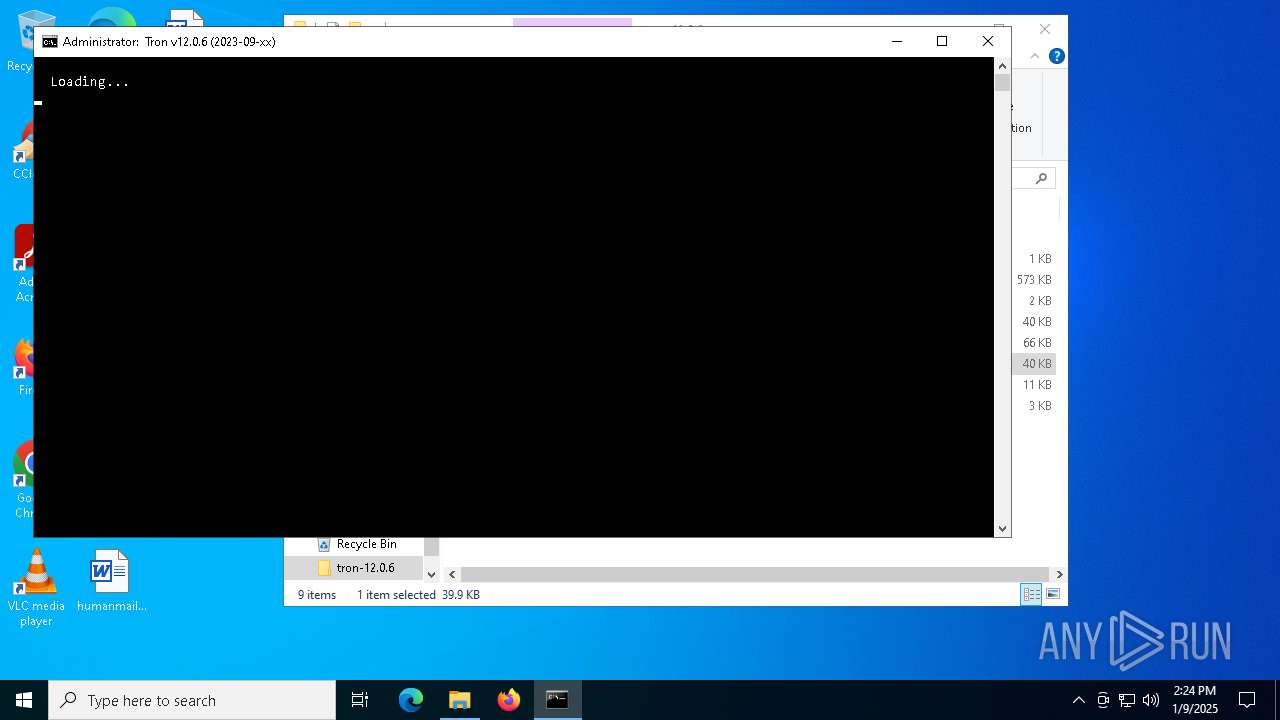
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2025, 14:24:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 2E69A6EFDC38B1FE1D1C915885F58B46 |
| SHA1: | 89411AC32E66BBCB090B82566FFF9A077F8BA897 |
| SHA256: | 9C93B0B6FCE38EE4D3AC346BE28D97E549BE4A15C0C7FF183FC2FCEF2C9ED577 |
| SSDEEP: | 98304:HMKbO0vwW9K8PGB1wadktGJoDBeoitoxeVbVoBUcdj29ivSdK5baK8jl5UyZgYJl:wutTwX |
MALICIOUS
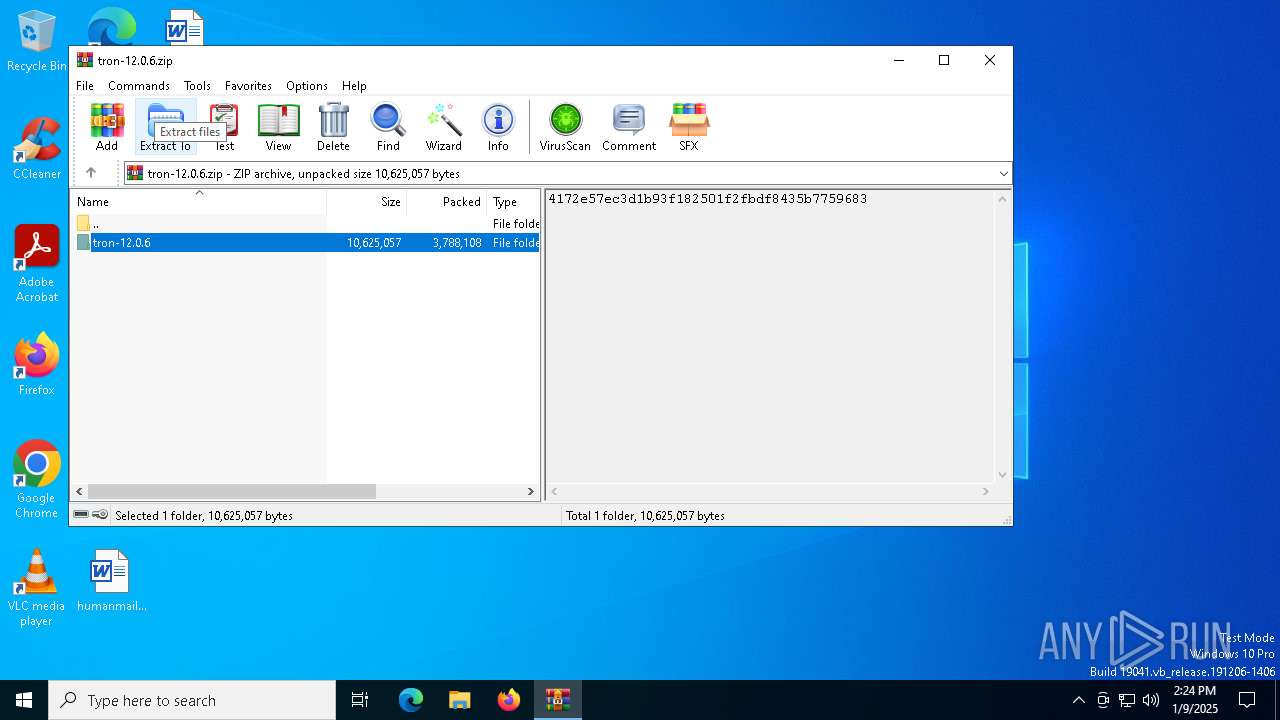
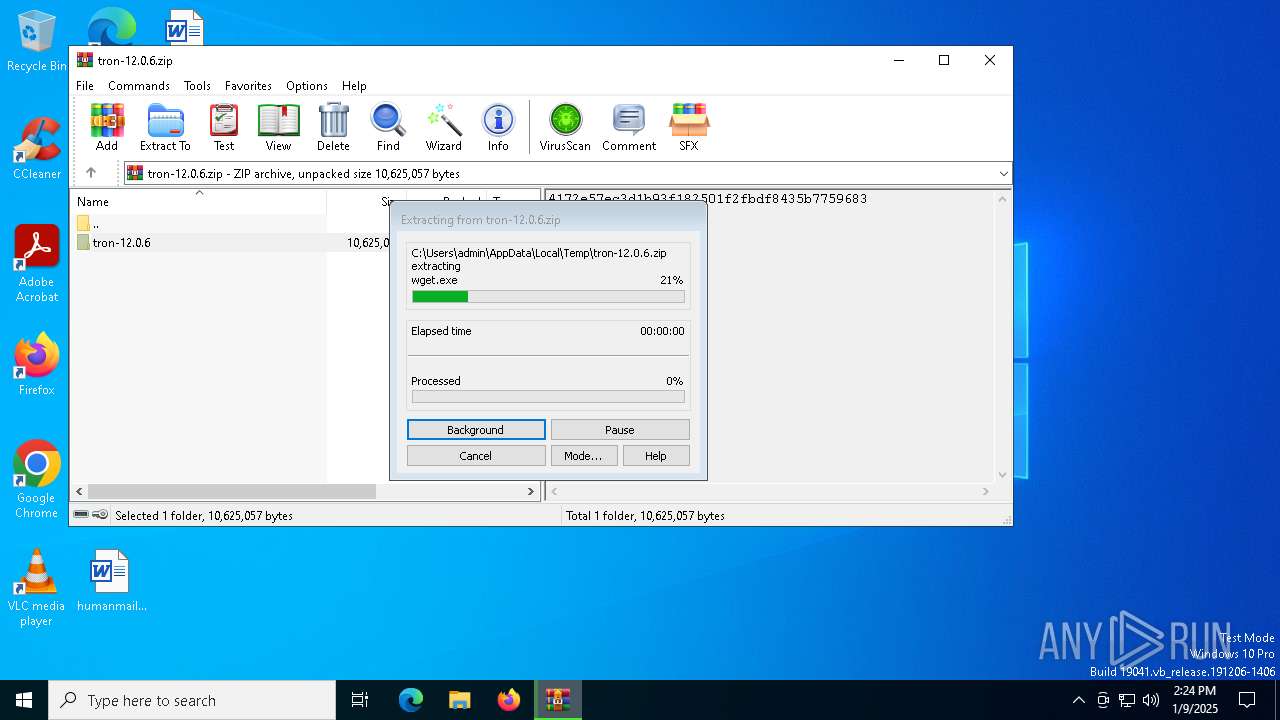
Generic archive extractor
- WinRAR.exe (PID: 6628)
SUSPICIOUS
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 5400)
- cmd.exe (PID: 6276)
Uses WMIC.EXE to obtain time zone data
- cmd.exe (PID: 2728)
- cmd.exe (PID: 7048)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6572)
- cmd.exe (PID: 6464)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5400)
- cmd.exe (PID: 6276)
Application launched itself
- cmd.exe (PID: 5400)
- cmd.exe (PID: 6276)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2728)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 6276)
Malware-specific behavior (creating "System.dll" in Temp)
- update-smart-drivedb.exe (PID: 3608)
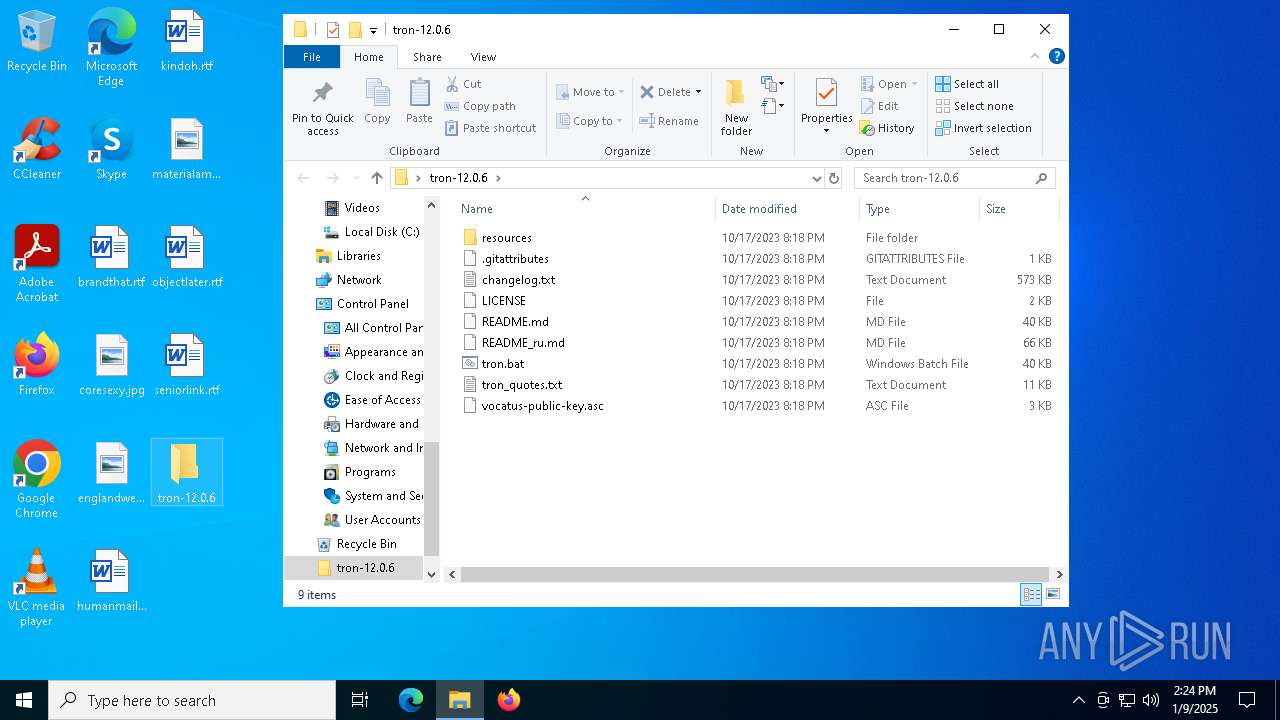
Executable content was dropped or overwritten
- update-smart-drivedb.exe (PID: 3608)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 4740)
INFO
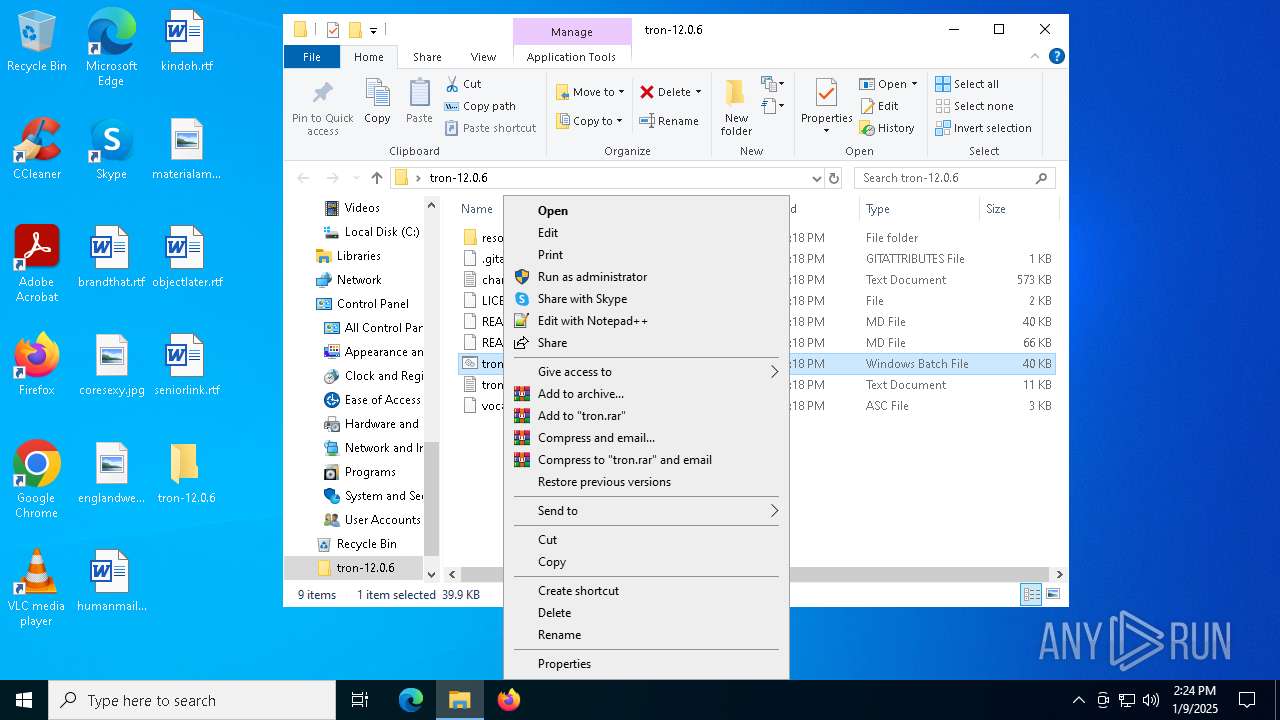
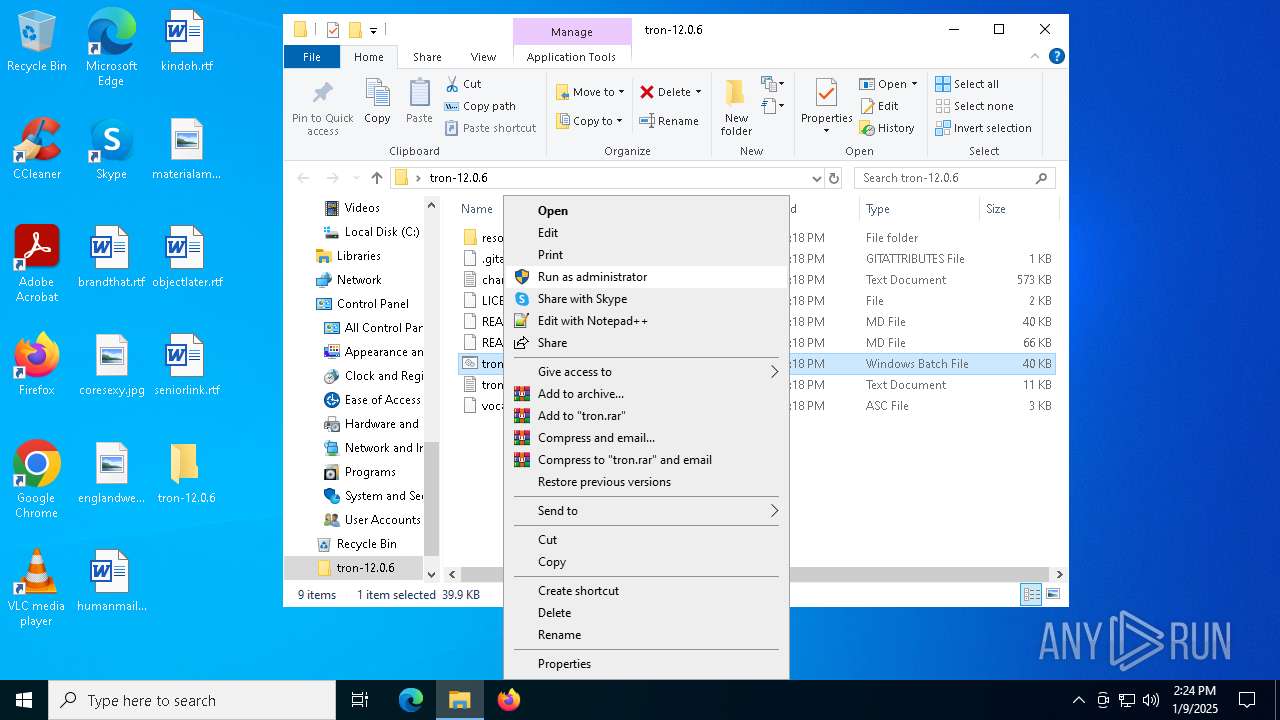
Manual execution by a user
- cmd.exe (PID: 5400)
- cmd.exe (PID: 6276)
The sample compiled with english language support
- WinRAR.exe (PID: 6628)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6628)
The process uses the downloaded file
- WinRAR.exe (PID: 6628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:10:17 13:18:40 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | tron-12.0.6/ |
Total processes
191
Monitored processes
66
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | C:\WINDOWS\System32\wbem\wmic.exe OS GET LocalDateTime | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\System32\wbem\wmic.exe OS GET LocalDateTime | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | bcdedit /set {default} bootmenupolicy legacy | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | reg query "hklm\system\controlset001\control\nls\language" /v Installlanguage | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | C:\WINDOWS\system32\cmd.exe /c reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion" /v CurrentVersion | C:\WINDOWS\System32\find.exe "CurrentVersion" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
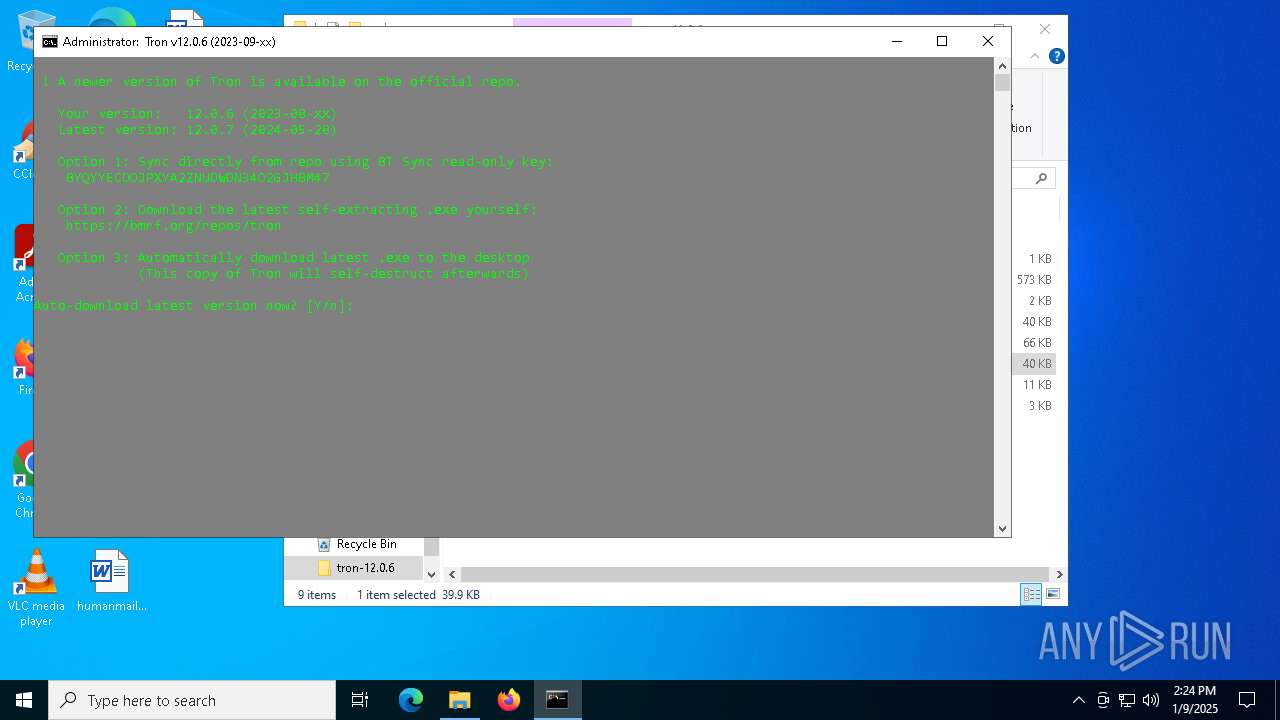
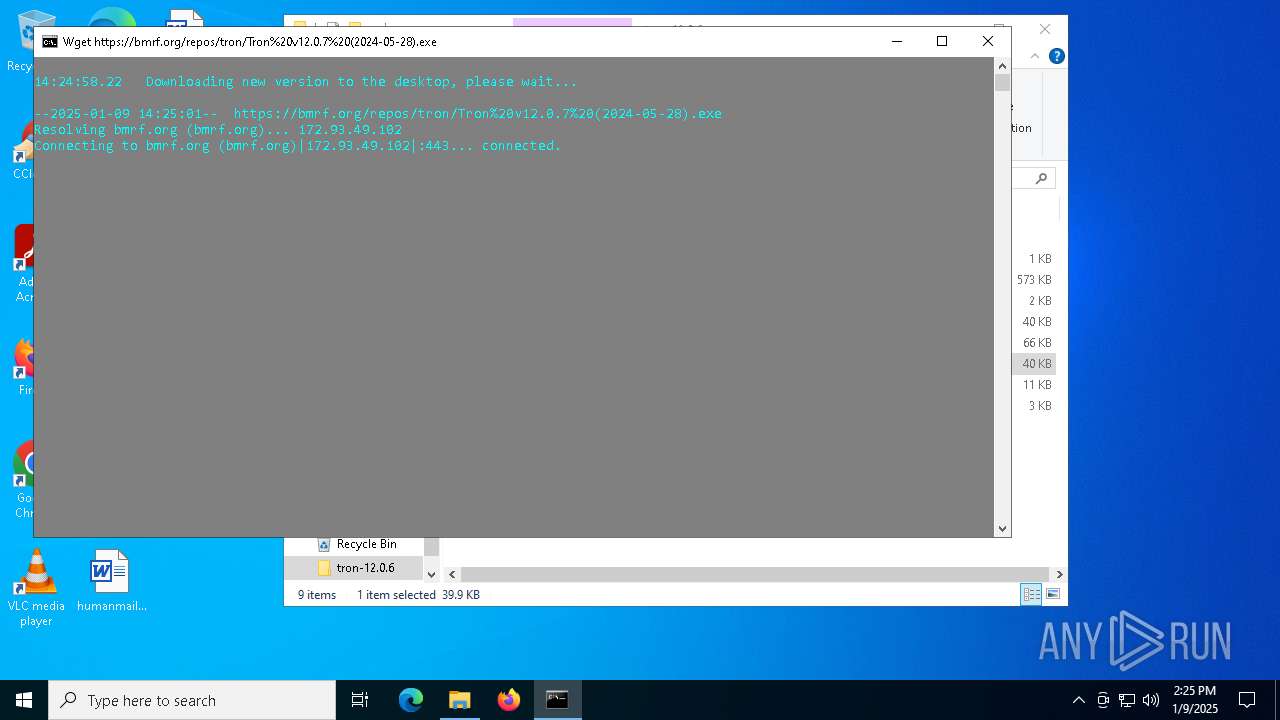
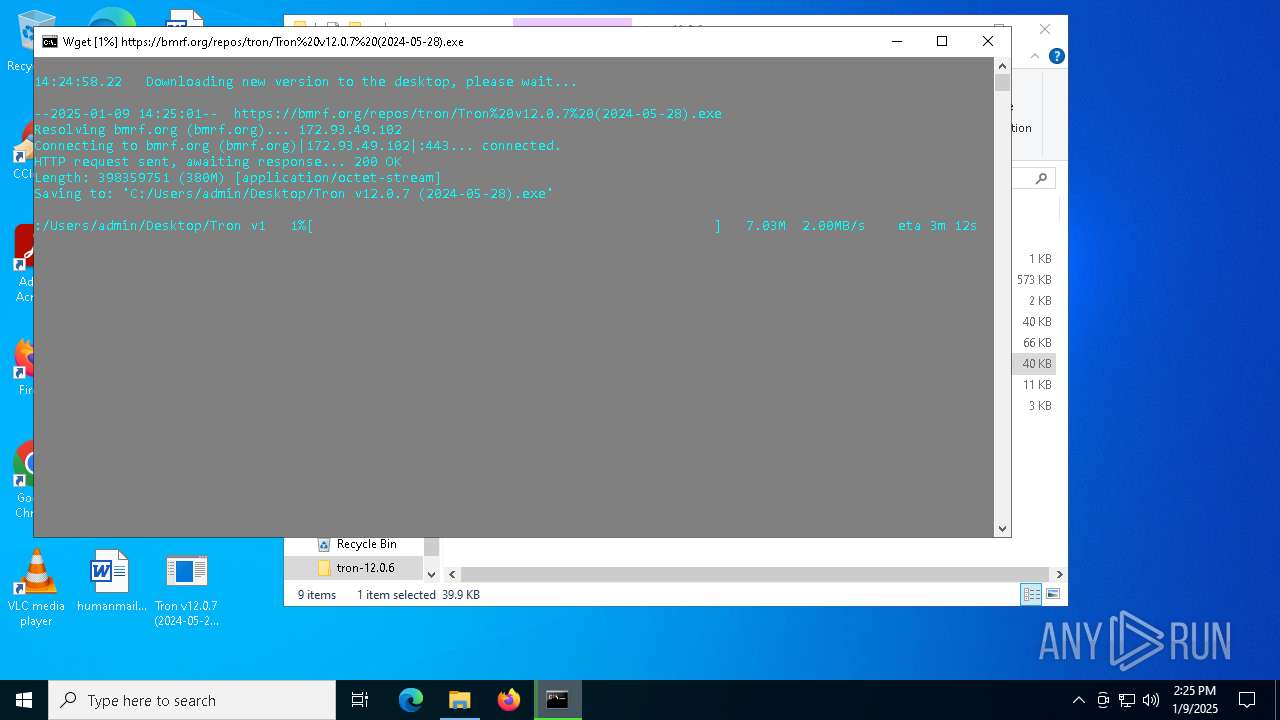
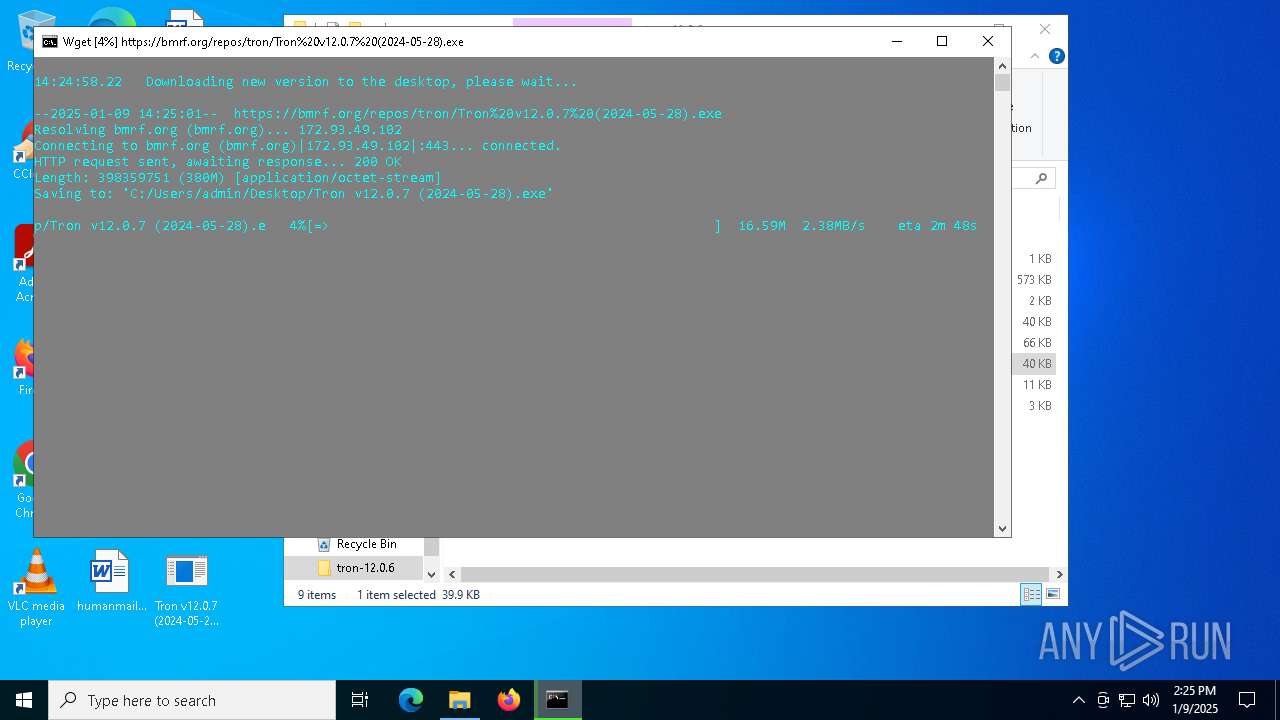
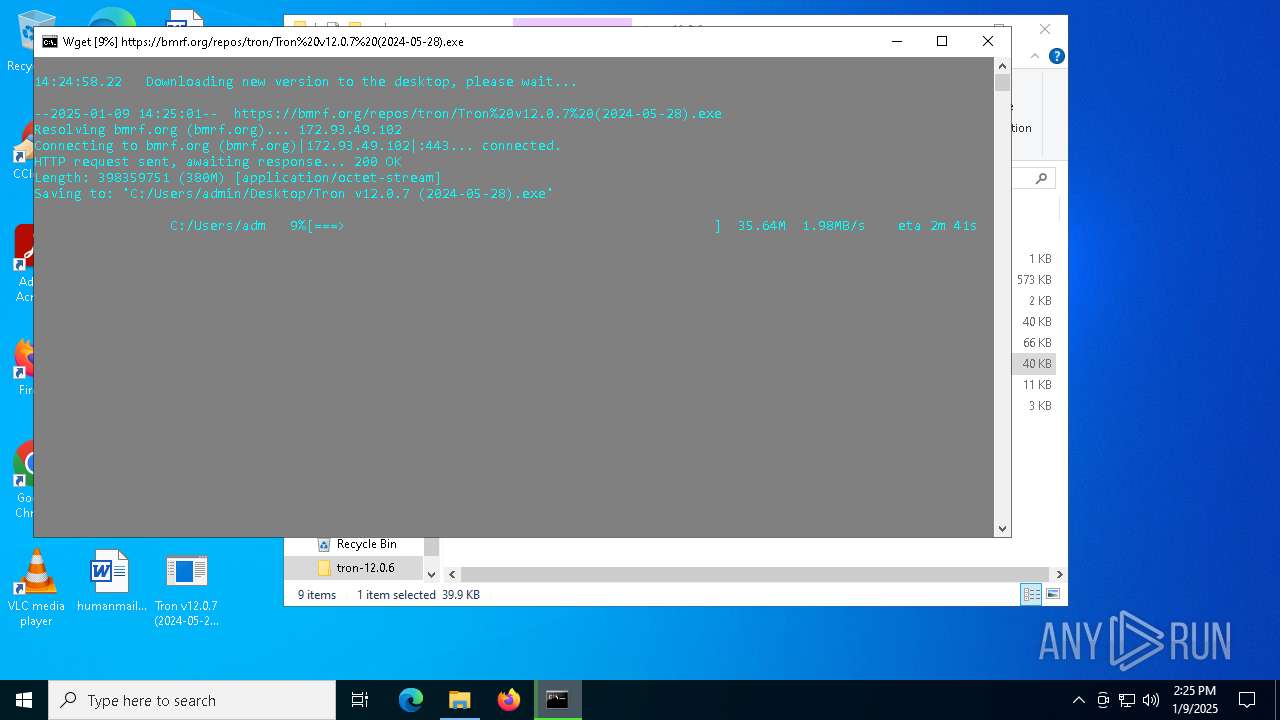
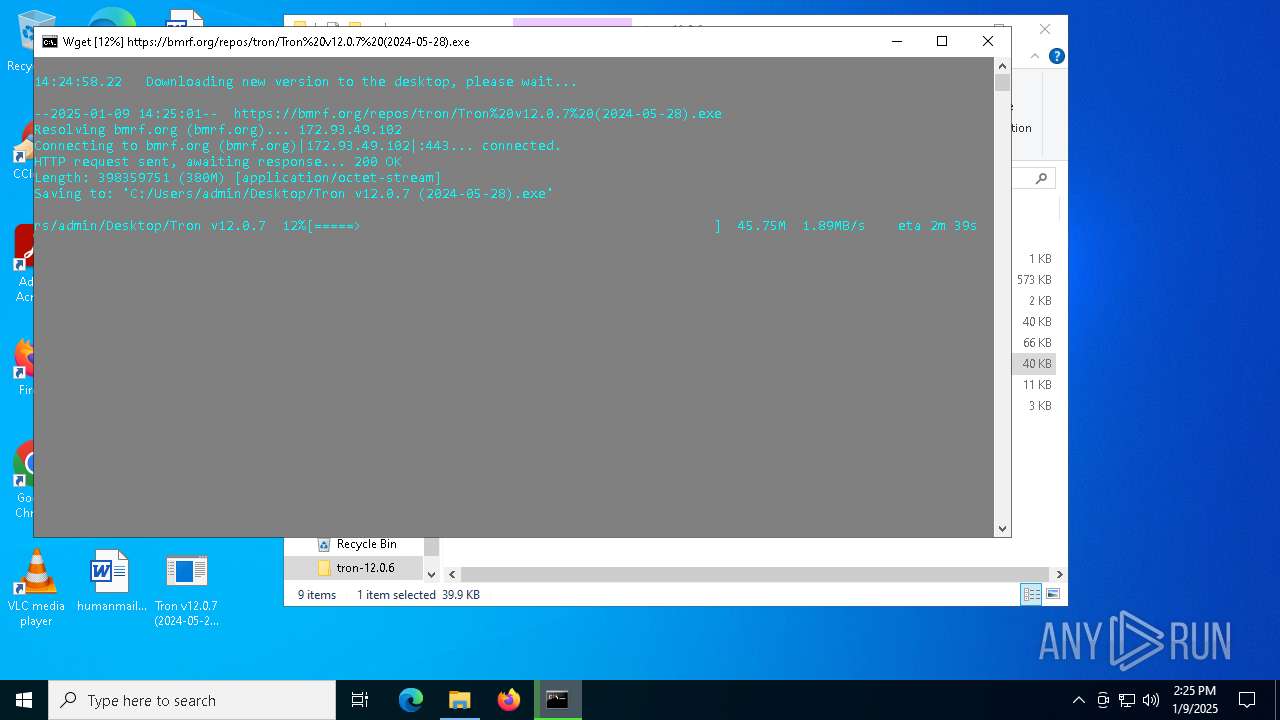
| 848 | stage_0_prep\check_update\wget.exe --user-agent="Tron-Update-Downloader/12.0.6 (Windows 10 Pro)" "https://bmrf.org/repos/tron/Tron v12.0.7 (2024-05-28).exe" -O "C:\Users\admin\Desktop\Tron v12.0.7 (2024-05-28).exe" | C:\Users\admin\Desktop\tron-12.0.6\resources\stage_0_prep\check_update\wget.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 936 | C:\WINDOWS\System32\find.exe "." | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1480 | C:\WINDOWS\System32\find.exe /i "0409" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 364
Read events
8 312
Write events
30
Delete events
22
Modification events
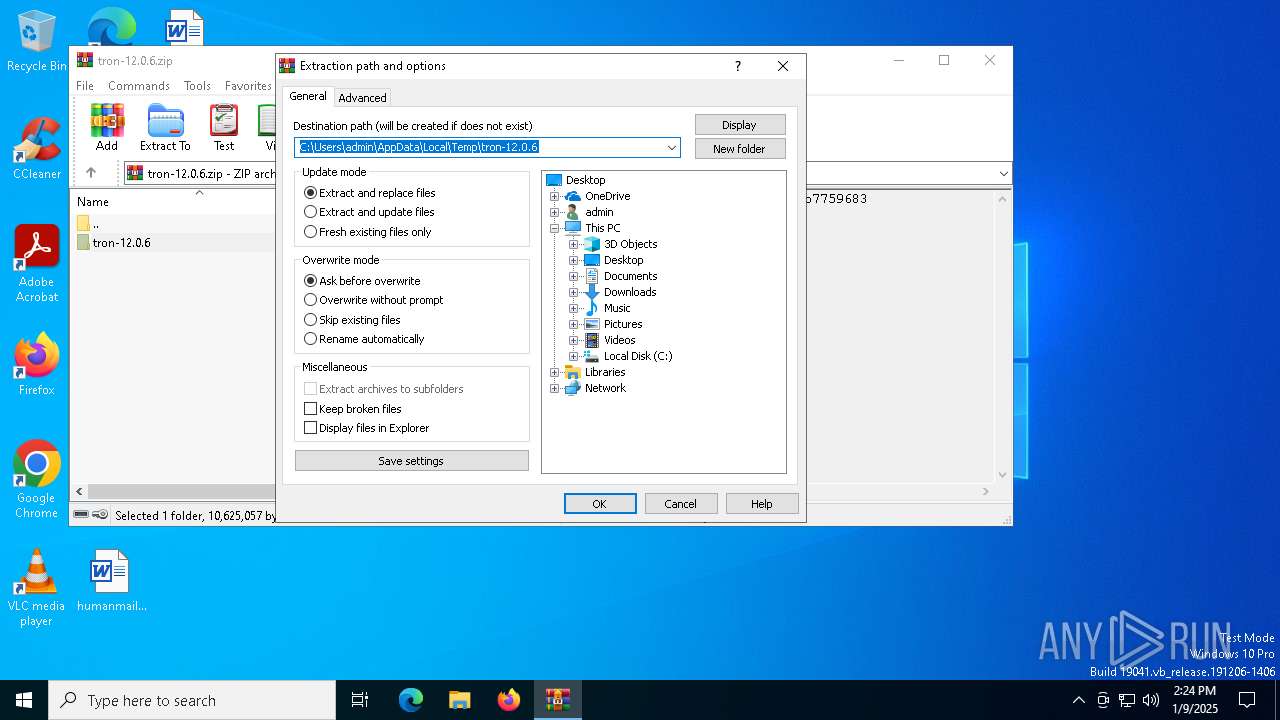
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\tron-12.0.6.zip | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
11
Suspicious files
1
Text files
170
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\tron-12.0.6\.gitattributes | text | |
MD5:459BE5ADEDB4992F507210D6AE7E8A37 | SHA256:1B59A304318929CE1A4F69C69AC52AAC375C3F0F2F5ED7D4A36C205C180EAEE1 | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\tron-12.0.6\LICENSE | text | |
MD5:0706C0DF09100792B973214963263096 | SHA256:D756AFE3BE6EEBBA3C3283A4F82425CD9545267566FF1E3404E1EA2700A5F425 | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\tron-12.0.6\README.md | text | |
MD5:CC88668666AF08E8B91A4FB8DED5B7C6 | SHA256:494AF8D5F6941FB75054950BC1974B385BE54D09DF2534D938DE1FC1004C2D8B | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\tron-12.0.6\README_ru.md | text | |
MD5:EAEA2D0751CB877582B8470A8EF3B032 | SHA256:CA593A19178800868E0848D3631B203F58C0B6702194DC1FC7DC578B2FF886B2 | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\tron-12.0.6\resources\functions\log.bat | text | |
MD5:EE23ADC713D81C8C0D1534C6B0F65BD5 | SHA256:36D10A3B25705B0C6F24569B7FEBF8A5C4EECD4BA35E278F6D2F51CD10445813 | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\tron-12.0.6\resources\functions\initialize_environment.bat | text | |
MD5:3E6FA082610F86E562AC368E5F23920F | SHA256:BEECB6CB5A23458A1FDD7995CE177DDB9DF710C5661616501EAF8EE3C5312F65 | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\tron-12.0.6\resources\stage_0_prep\rkill\rkill_process_whitelist.txt | text | |
MD5:46F264DA42C3C215AEED2C05FEA23290 | SHA256:91C99E1A1C81A7283BDAB90199AE7BEC5497B779722F24308BA9910457017F65 | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\tron-12.0.6\resources\stage_0_prep\check_update\check_update_debloat_lists.bat | text | |
MD5:2D453C701199BDA139820991B86594D8 | SHA256:1FD29D359FCB1367B33C48F080602928D8368525D2DEABDCFD88DE872B20EB18 | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\tron-12.0.6\resources\stage_0_prep\processkiller\ProcessKiller_v1.1.0-TRON.bat | text | |
MD5:457EF4682BE7D58D43C4904C7544652F | SHA256:B314A6F768BAE992FFE561E5189E287D145ACD26713E33FC4AC9278040651A80 | |||
| 6628 | WinRAR.exe | C:\Users\admin\Desktop\tron-12.0.6\resources\functions\log_with_date.bat | text | |
MD5:844C50DC940F09724434022B43DB0AC2 | SHA256:F1EAB65C5C17DE961E81AA5992CABA4FDCBCE18EA2035996737F1098F8DEF978 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
37
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5036 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6412 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5036 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3608 | update-smart-drivedb.exe | GET | 200 | 216.105.38.41:80 | http://svn.code.sf.net/p/smartmontools/code/branches/RELEASE_6_6_DRIVEDB/smartmontools/drivedb.h | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5064 | SearchApp.exe | 2.23.227.221:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report