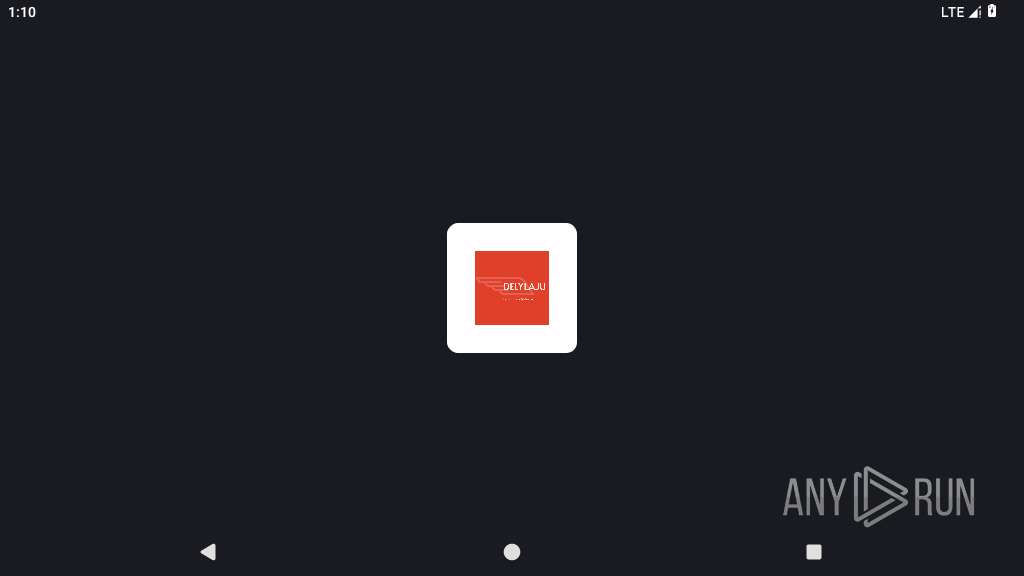
| File name: | Delivery.apk |
| Full analysis: | https://app.any.run/tasks/9d410384-88bd-40ee-b041-e0ab48a411d8 |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2025, 01:10:22 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with MANIFEST.MF and resources.arsc |
| MD5: | D066100A90D6333BD517719CBC8E3B0B |
| SHA1: | D5A3B8C0290117ABED564D3027EDC2E7BBA572C1 |
| SHA256: | 9C8D142E4F7219A8D3F49520F08A6FB2CFBFAC7D6743BC6050846B92AEF5DF8E |
| SSDEEP: | 6144:HdFzQy6uUvTgUJvWKJSNz7dOxah/vnIdaHpUhC1M87OFY4:9FsLzvWKJYzJOoh/AaHwC1BqY4 |
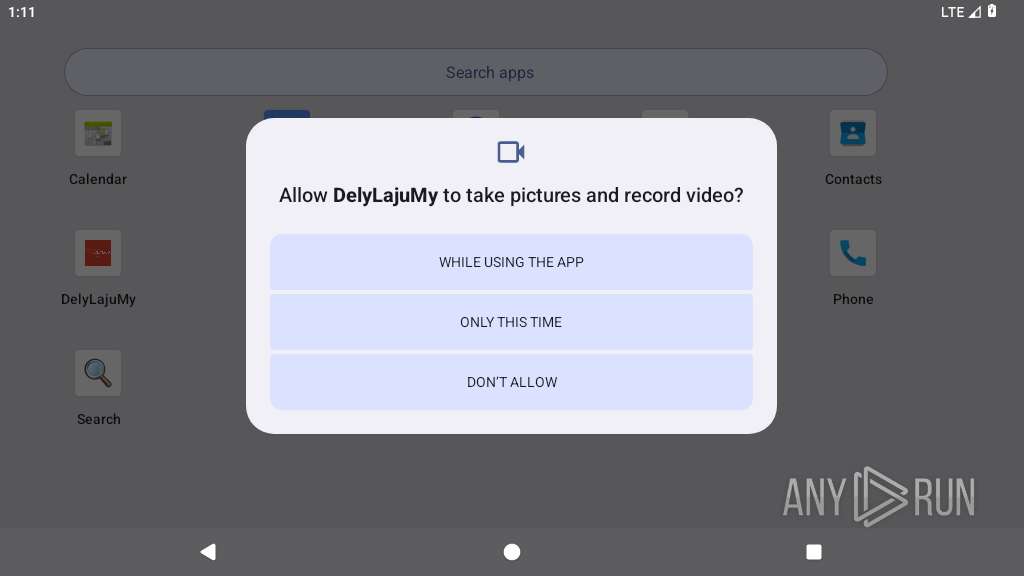
MALICIOUS
Determines whether a component is an active device admin
- app_process64 (PID: 2851)
- app_process64 (PID: 2798)
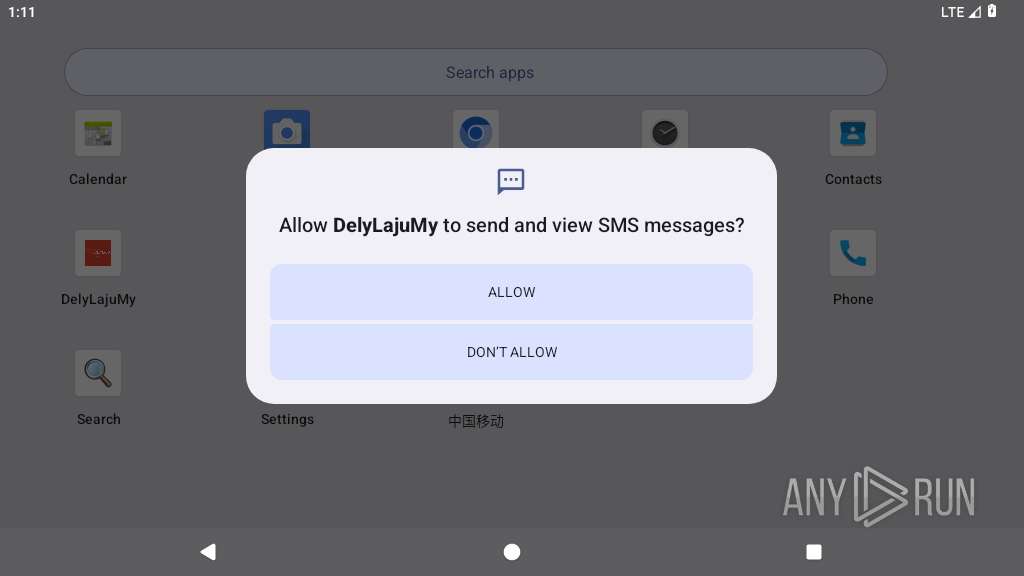
SUSPICIOUS
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2851)
- app_process64 (PID: 2798)
Checks exemption from battery optimization
- app_process64 (PID: 2798)
- app_process64 (PID: 2851)
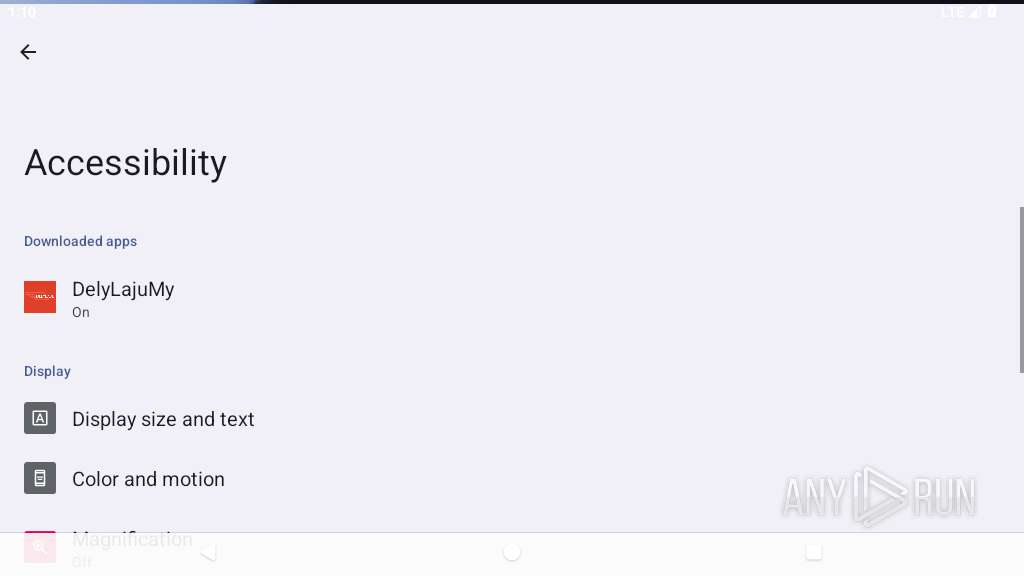
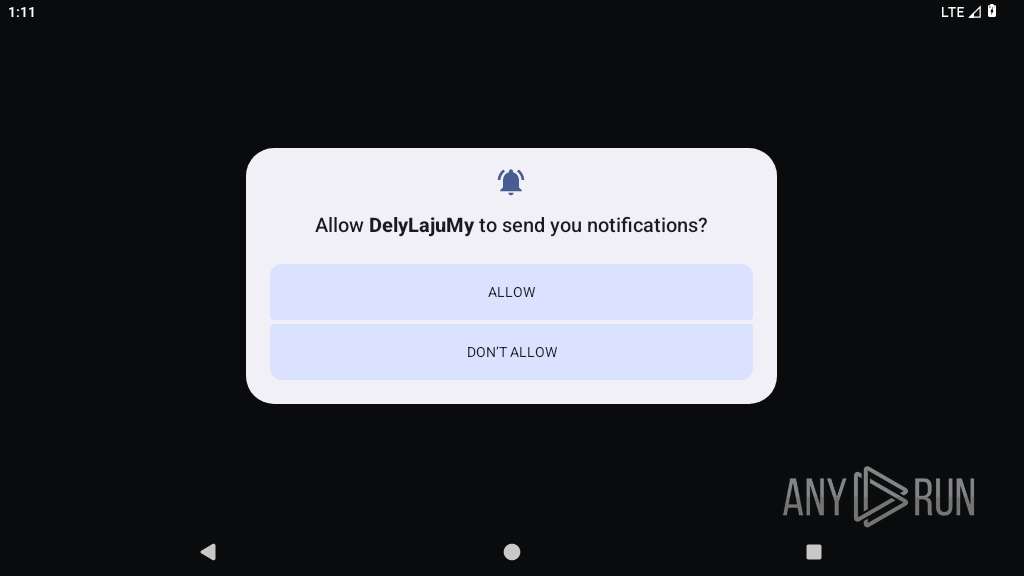
Requests access to accessibility settings
- app_process64 (PID: 2798)
Executes dynamic code using class loader
- app_process64 (PID: 2798)
- app_process64 (PID: 2851)
Performs UI accessibility actions without user input
- app_process64 (PID: 2851)
Creates a WakeLock to manage power state
- app_process64 (PID: 2851)
Acquires a wake lock to keep the device awake
- app_process64 (PID: 2851)
Checks if the device's lock screen is showing
- app_process64 (PID: 2798)
- app_process64 (PID: 2851)
Retrieves a list of running services
- app_process64 (PID: 2798)
- app_process64 (PID: 2851)
Abuses foreground service for persistence
- app_process64 (PID: 2798)
- app_process64 (PID: 2851)
Accesses system-level resources
- app_process64 (PID: 2851)
Intercepts events for accessibility services
- app_process64 (PID: 2851)
INFO
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2798)
- app_process64 (PID: 2851)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2851)
- app_process64 (PID: 2798)
Dynamically loads a class in Java
- app_process64 (PID: 2798)
- app_process64 (PID: 2851)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2851)
- app_process64 (PID: 2798)
Handles throwable exceptions in the app
- app_process64 (PID: 2798)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2851)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (92.9) |
|---|---|---|
| .zip | | | ZIP compressed archive (7) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:07:09 12:38:20 |
| ZipCRC: | 0x4fe3138b |
| ZipCompressedSize: | 425 |
| ZipUncompressedSize: | 736 |
| ZipFileName: | META-INF/MANIFEST.MF |
Total processes
131
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
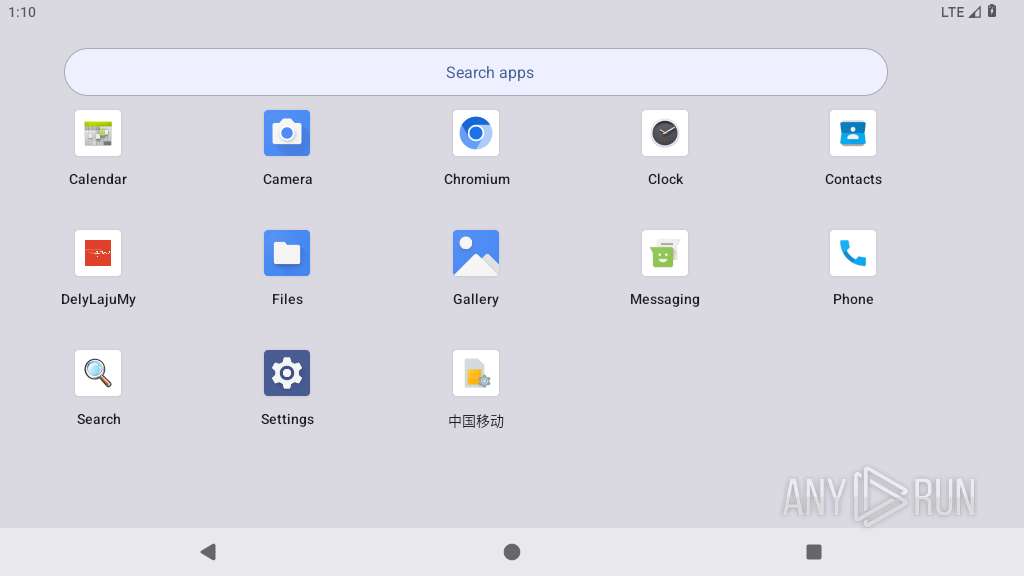
| 2798 | delylajumy.zra.kcmvcbdu | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2837 | com.android.systemui.accessibility.accessibilitymenu | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2851 | delylajumy.zra.kcmvcbdu | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3069 | com.android.webview:webview_service | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3070 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3113 | <pre-initialized> | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
36
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2798 | app_process64 | /data/user/0/delylajumy.apk.test/oat/arm64/Anonymous-DexFile@1619099604.vdex | binary | |
MD5:— | SHA256:— | |||
| 2798 | app_process64 | /data/user/0/delylajumy.apk.test/files/Factory/Plugins/classes.dex | binary | |
MD5:— | SHA256:— | |||
| 2798 | app_process64 | /data/user/0/delylajumy.apk.test/shared_prefs/PREFS_NAME.xml | xml | |
MD5:— | SHA256:— | |||
| 2798 | app_process64 | /data/user/0/delylajumy.apk.test/files/Factory/Plugins/oat/arm64/classes.vdex | binary | |
MD5:— | SHA256:— | |||
| 2851 | app_process64 | /data/user/0/delylajumy.apk.test/oat/arm64/Anonymous-DexFile@1619099604.vdex | binary | |
MD5:— | SHA256:— | |||
| 2851 | app_process64 | /data/user/0/delylajumy.apk.test/shared_prefs/PREFS_NAME.xml | xml | |
MD5:— | SHA256:— | |||
| 2851 | app_process64 | /data/user/0/delylajumy.apk.test/files/Factory/Plugins/oat/arm64/classes.vdex | binary | |
MD5:— | SHA256:— | |||
| 2851 | app_process64 | /data/user/0/delylajumy.apk.test/files/Factory/Plugins/classes.dex | binary | |
MD5:— | SHA256:— | |||
| 2851 | app_process64 | /data/user/0/delylajumy.apk.test/cache/oat_primary/arm64/base.2851.tmp | binary | |
MD5:— | SHA256:— | |||
| 2851 | app_process64 | /data/user/0/delylajumy.apk.test/app_webview/last-exit-info | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
18
DNS requests
10
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 216.58.206.36:80 | http://www.google.com/gen_204 | unknown | — | — | whitelisted |
831 | app_process64 | GET | 204 | 142.250.186.131:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
446 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 216.58.206.36:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.131:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 216.58.206.36:80 | www.google.com | GOOGLE | US | whitelisted |
574 | app_process64 | 216.239.35.12:123 | time.android.com | — | — | unknown |
831 | app_process64 | 216.58.206.36:443 | www.google.com | GOOGLE | US | whitelisted |
831 | app_process64 | 142.250.186.131:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
1711 | app_process64 | 142.250.102.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2851 | app_process64 | 38.181.52.134:7676 | — | COGENT-174 | US | unknown |
3069 | app_process32 | 142.250.184.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
time.android.com |
| unknown |
connectivitycheck.gstatic.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
dl.google.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
www.delylajufarm.shop |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
831 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |