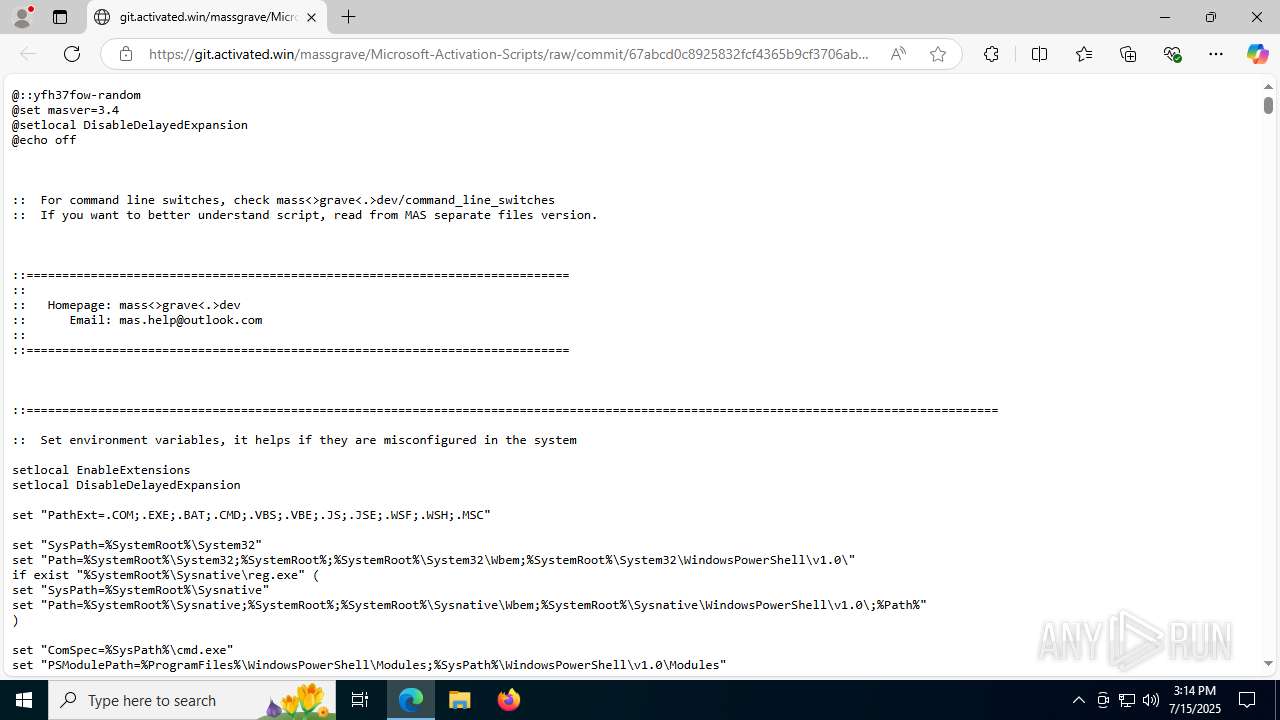
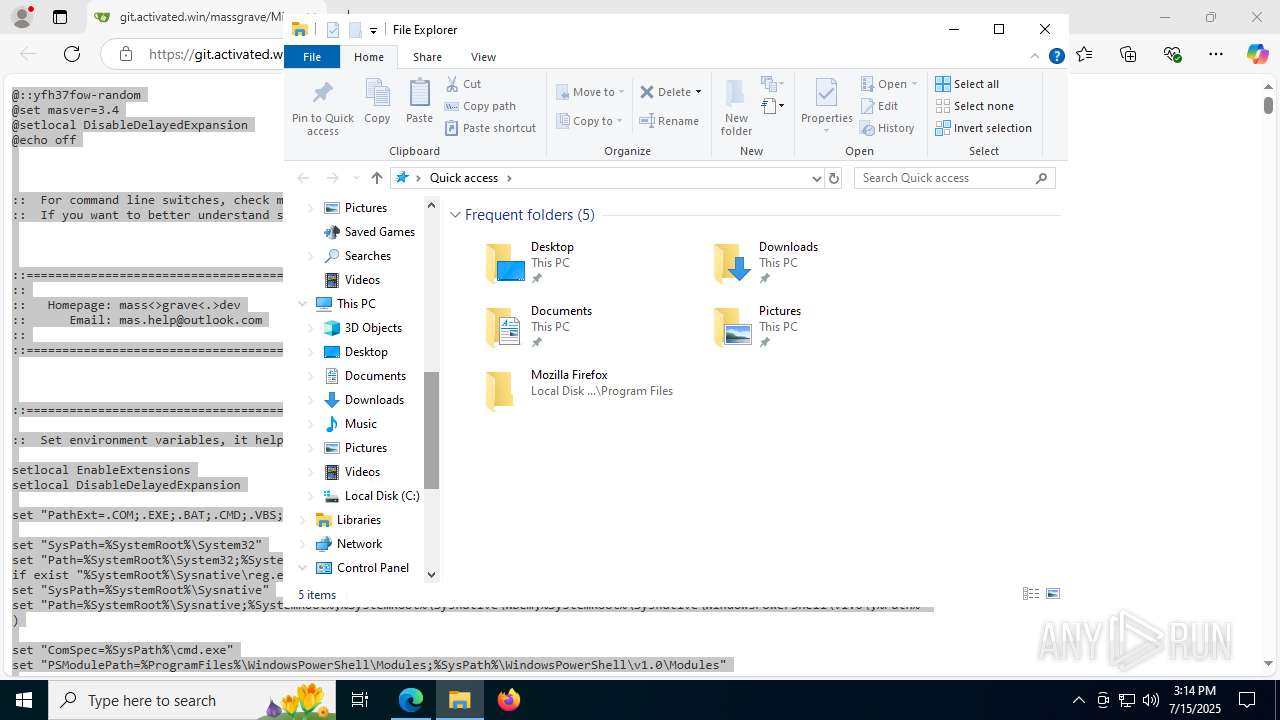
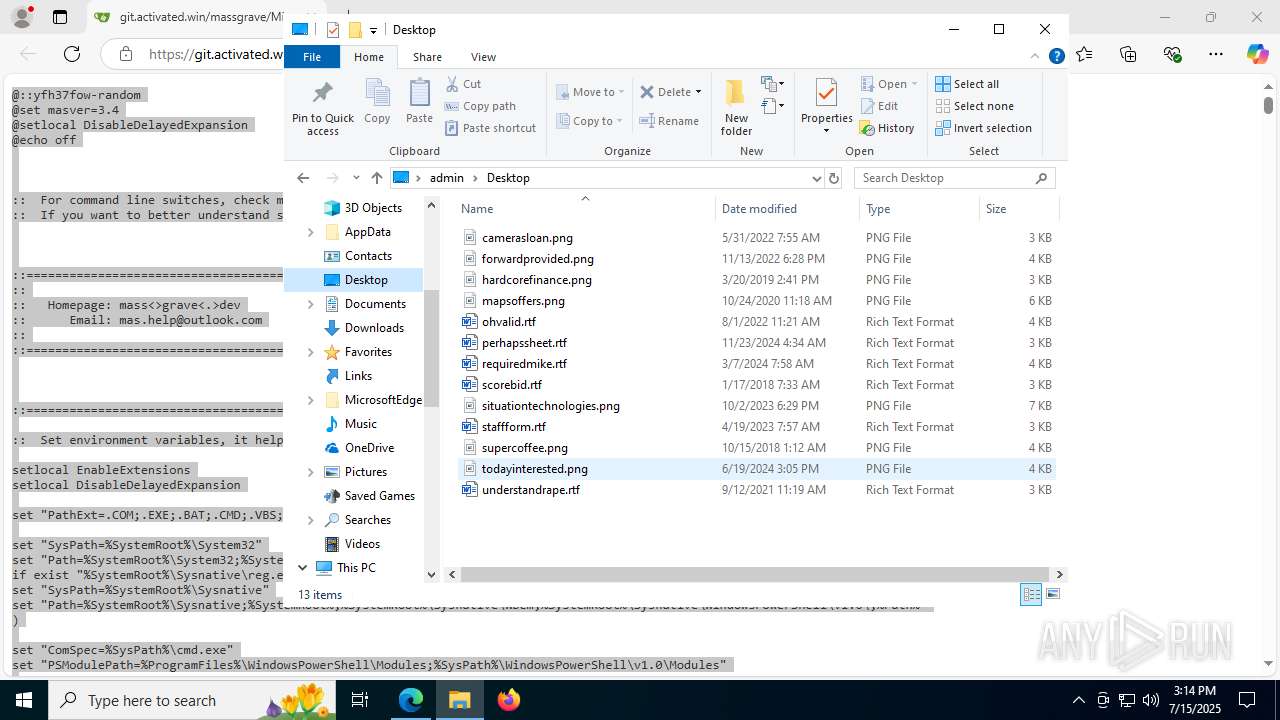
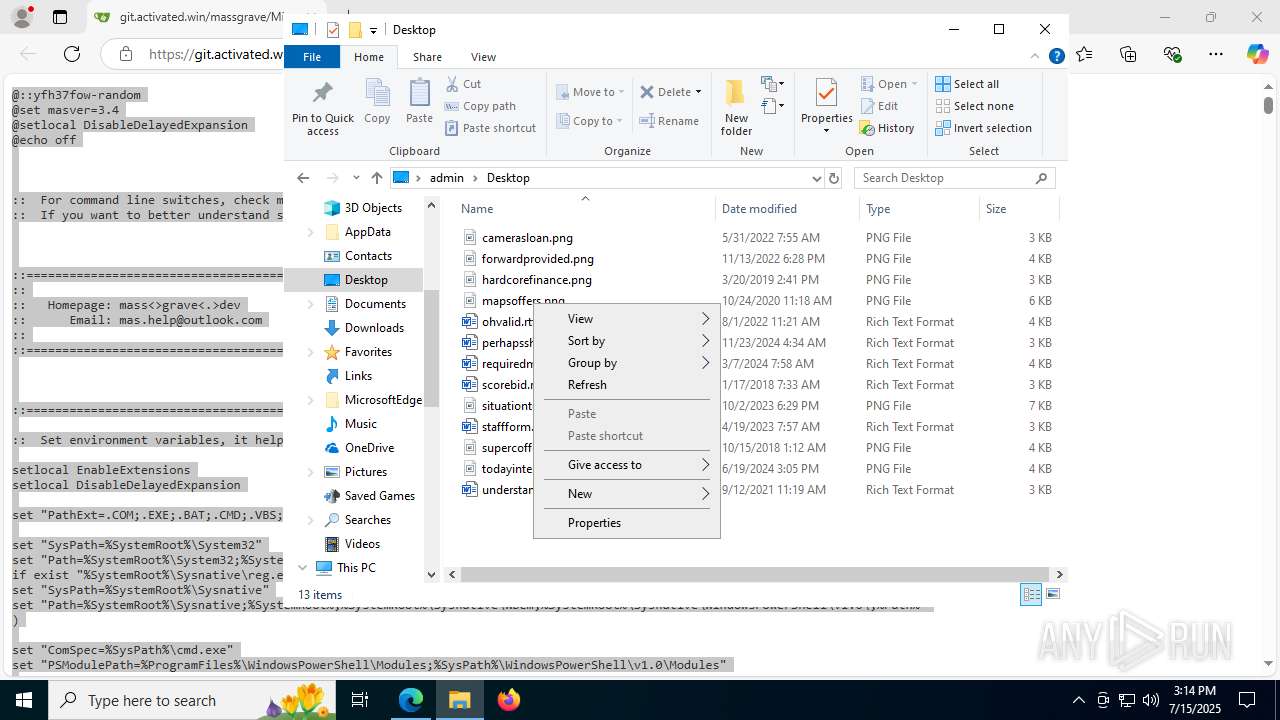
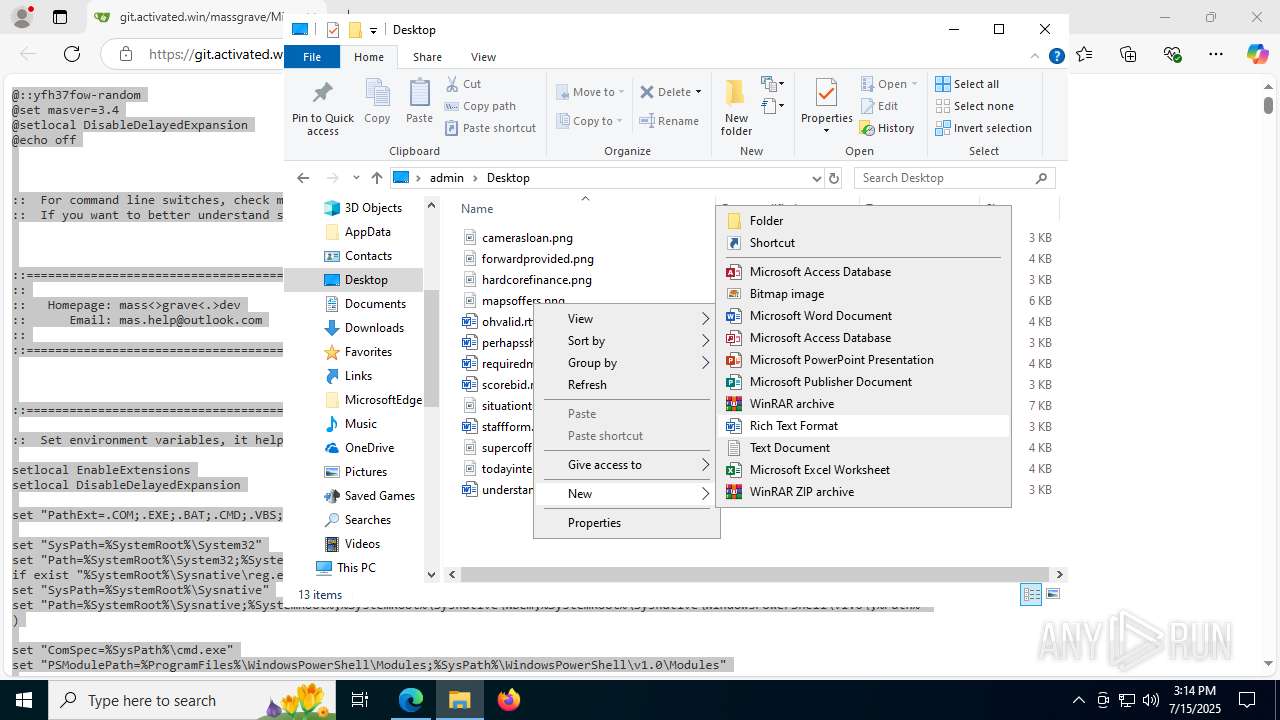
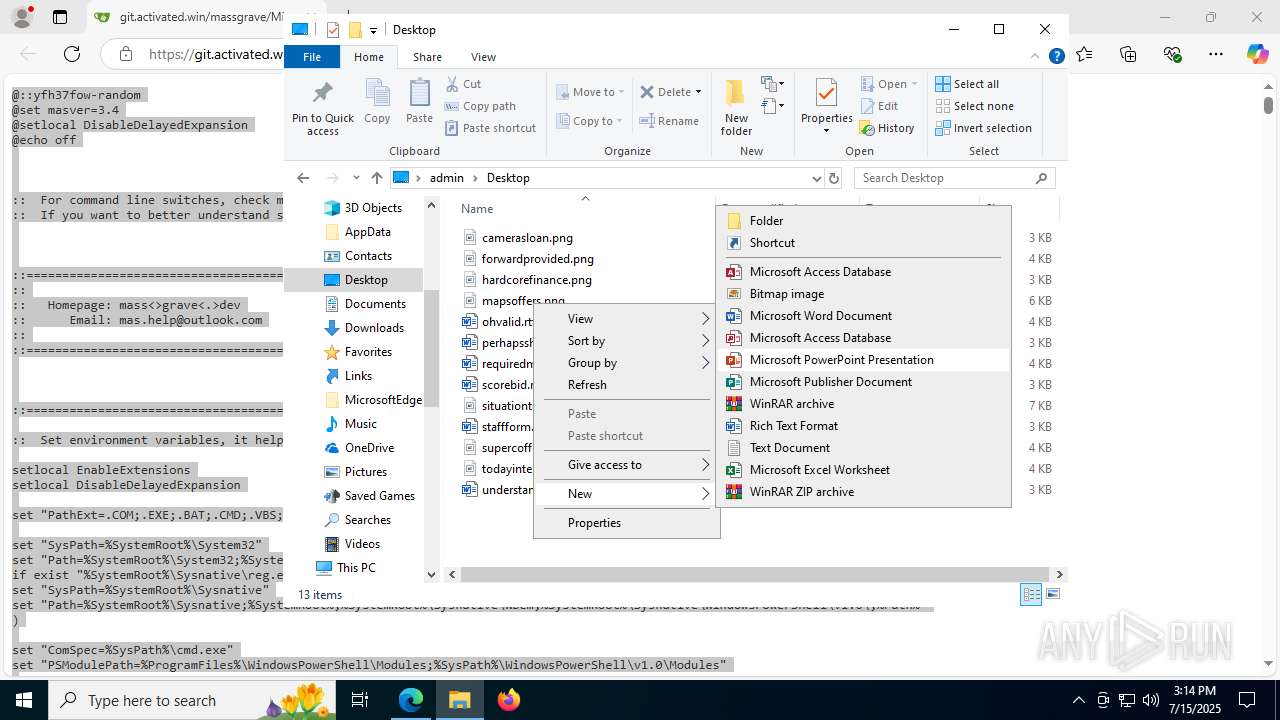
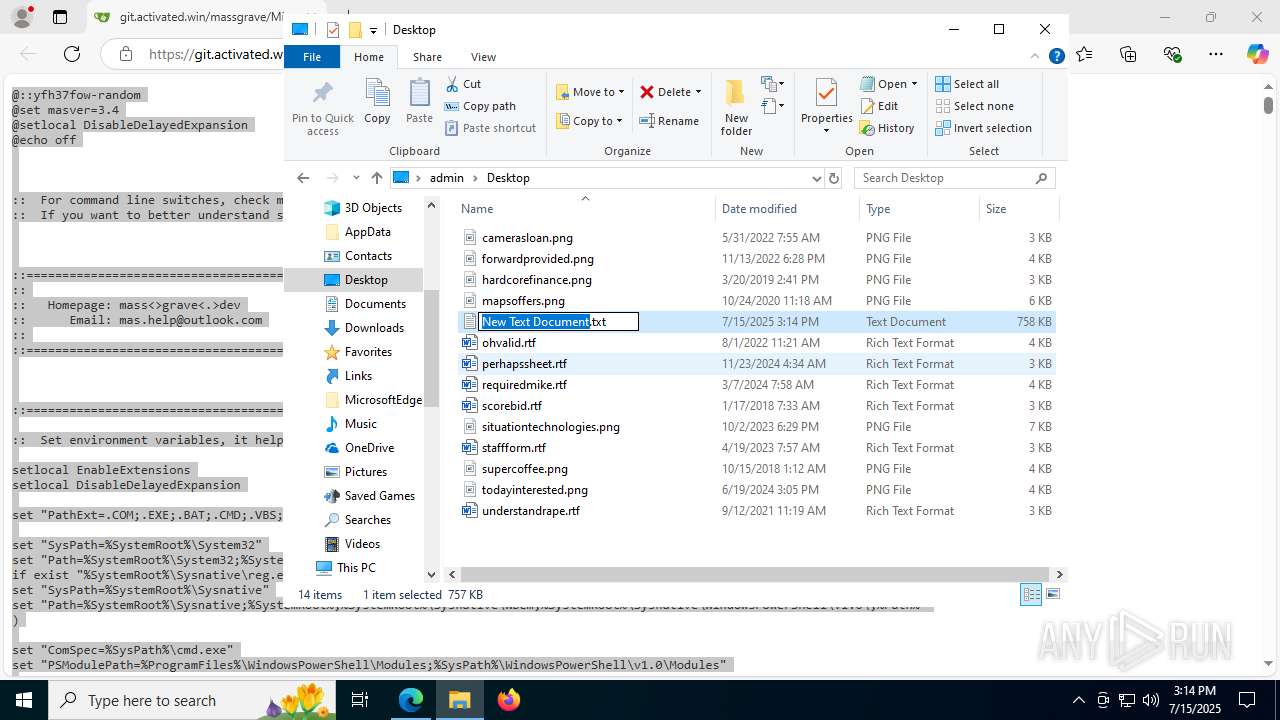
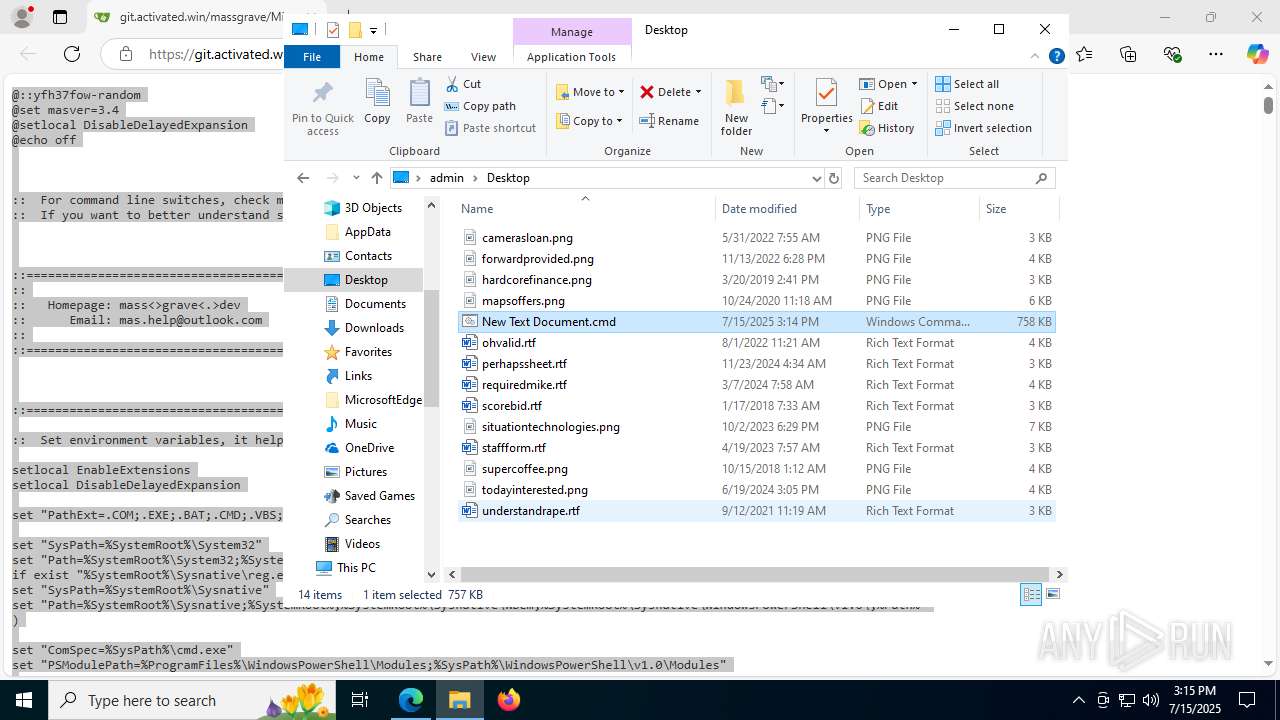
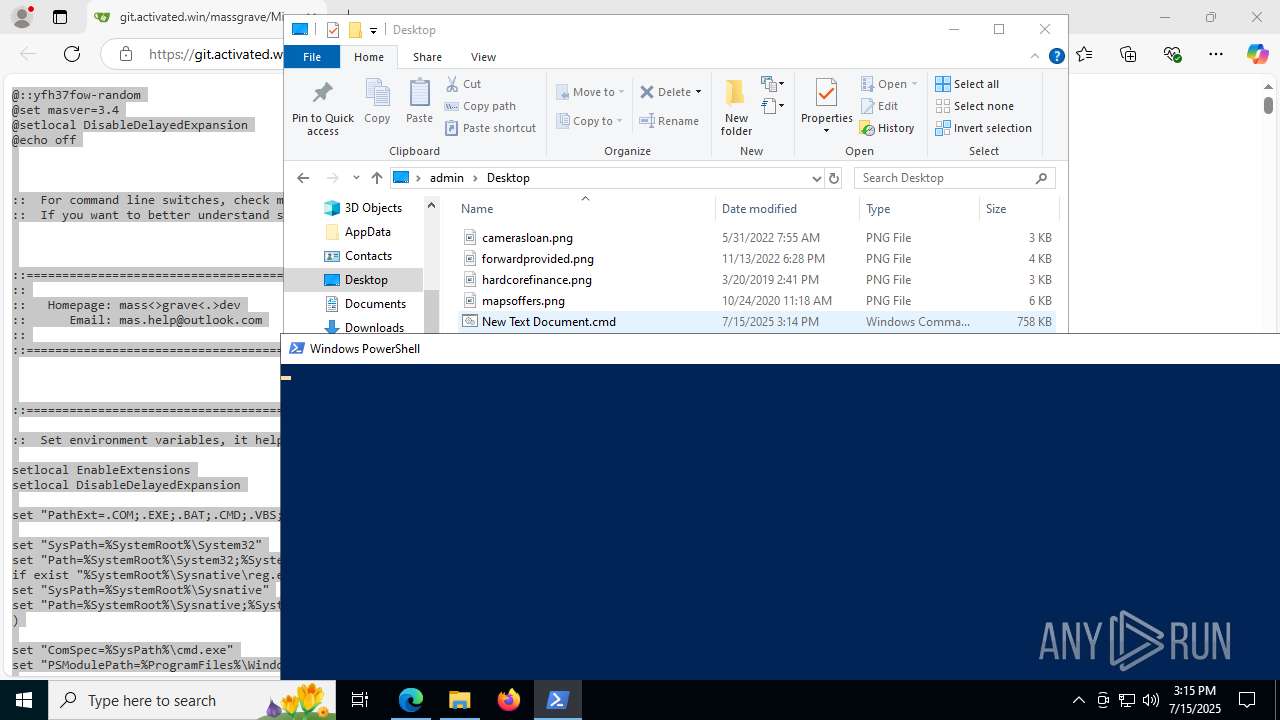
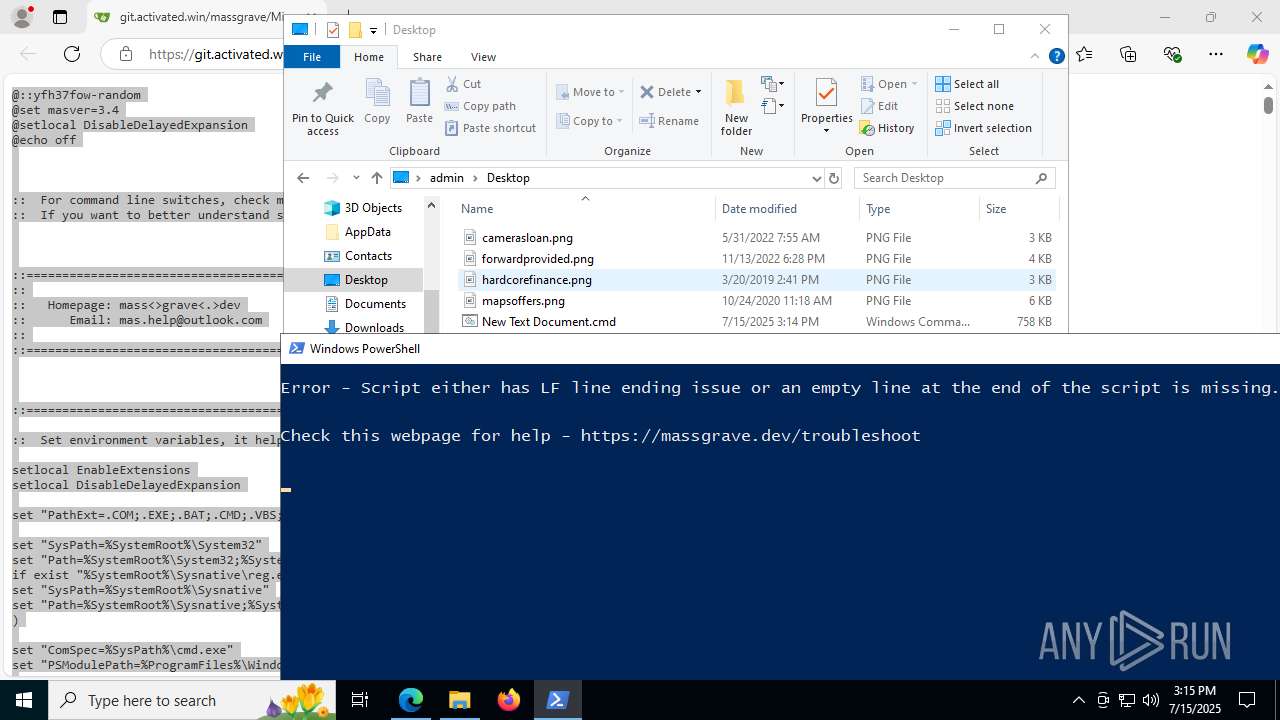
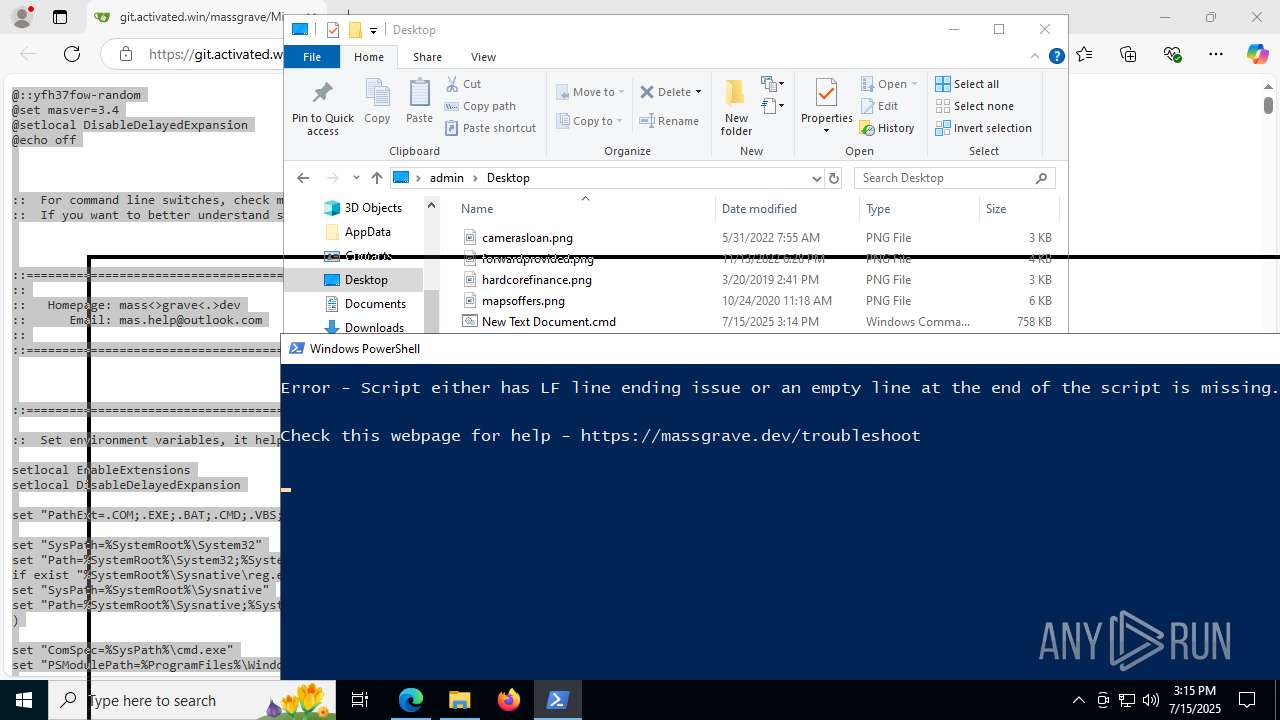
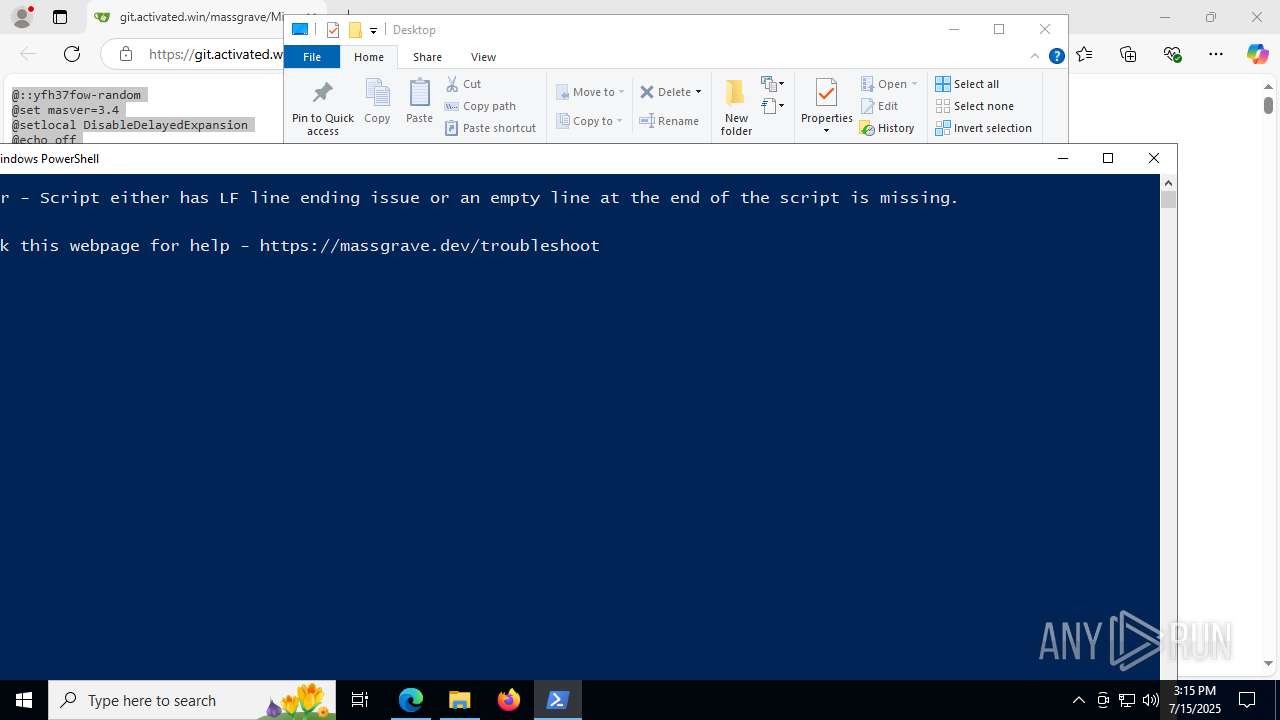
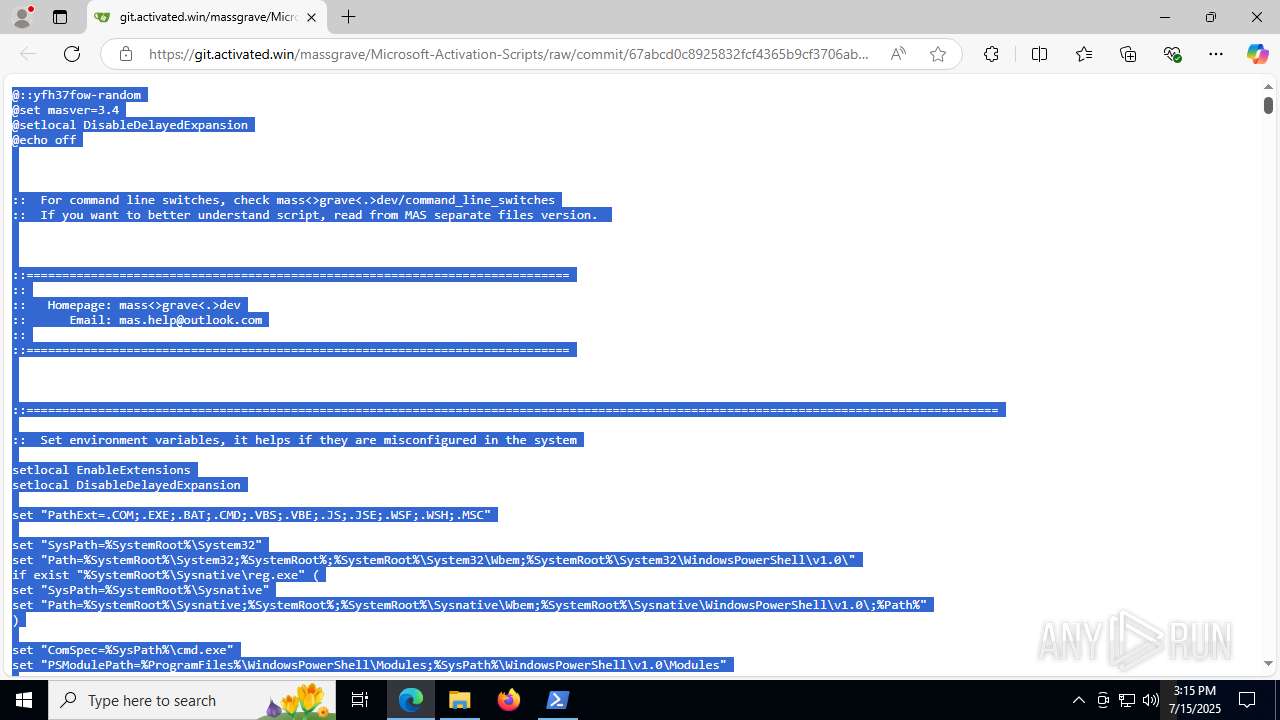
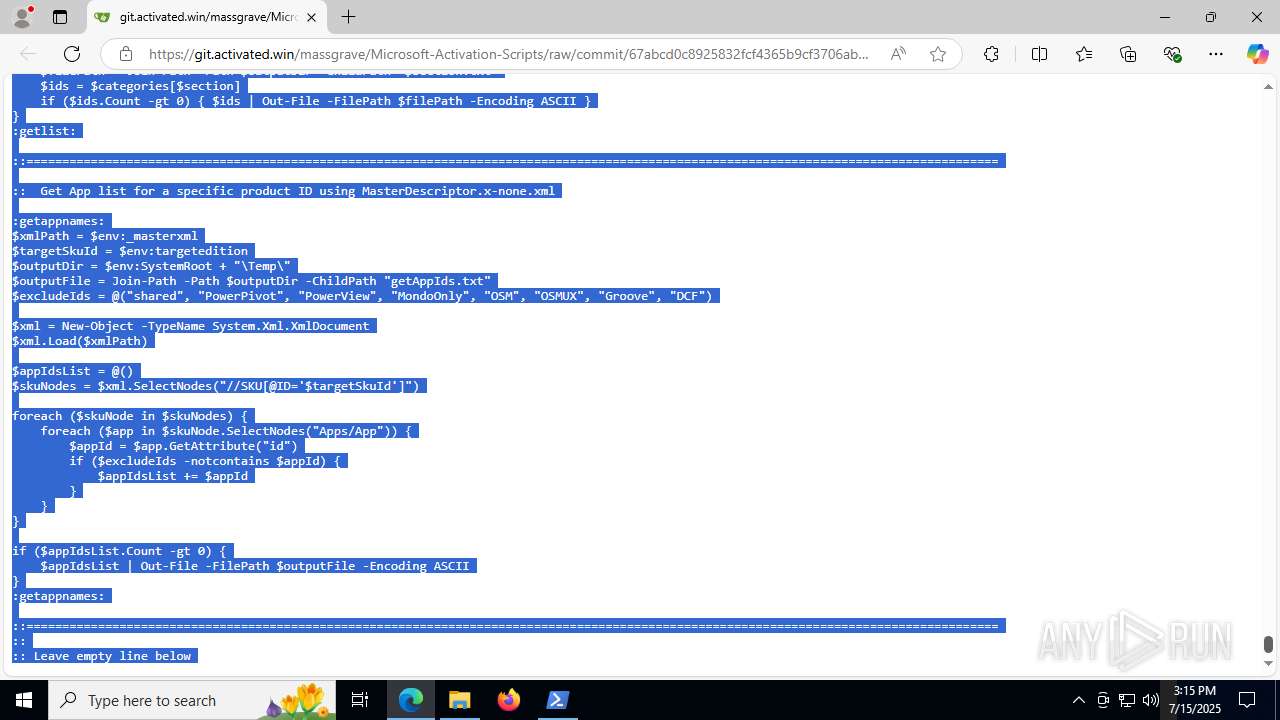
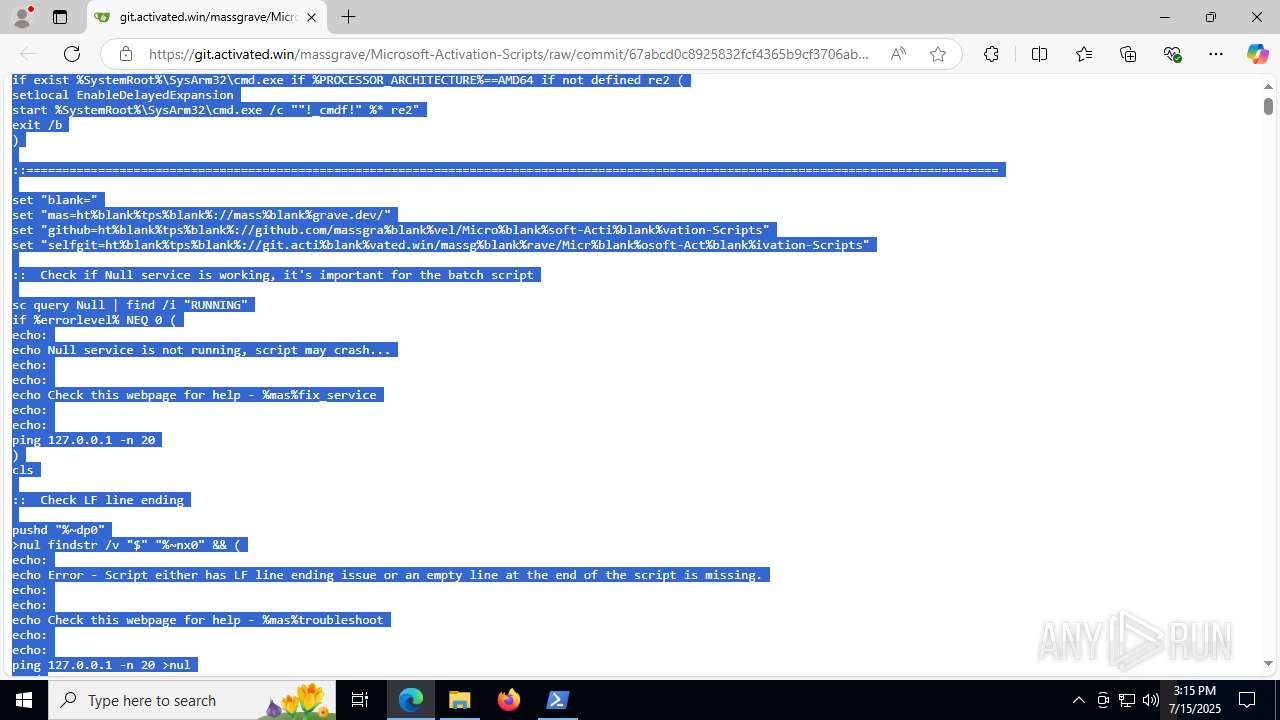
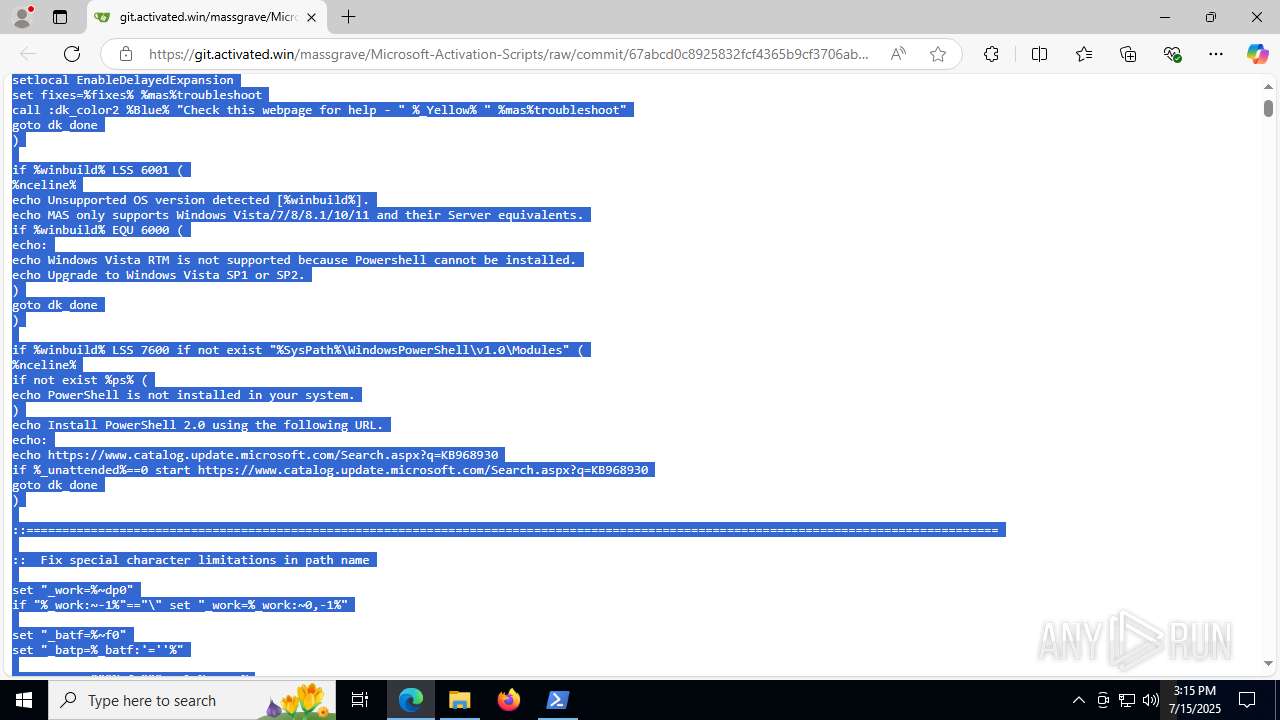
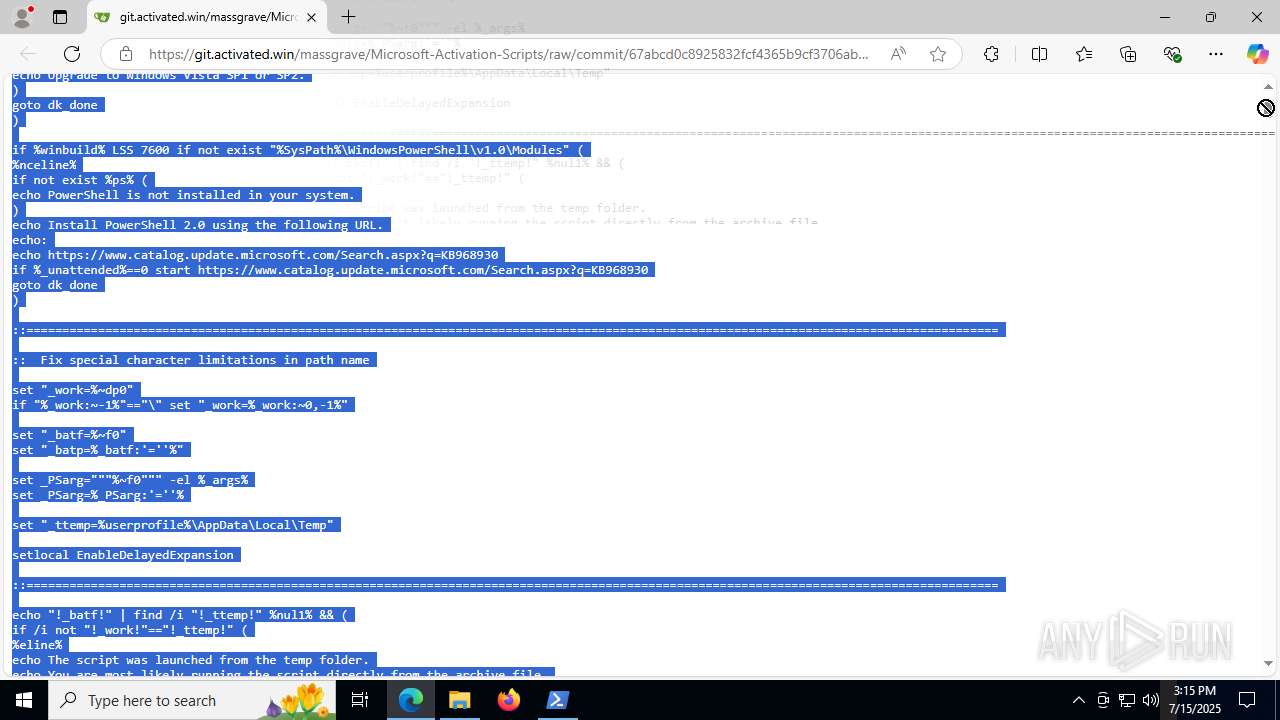
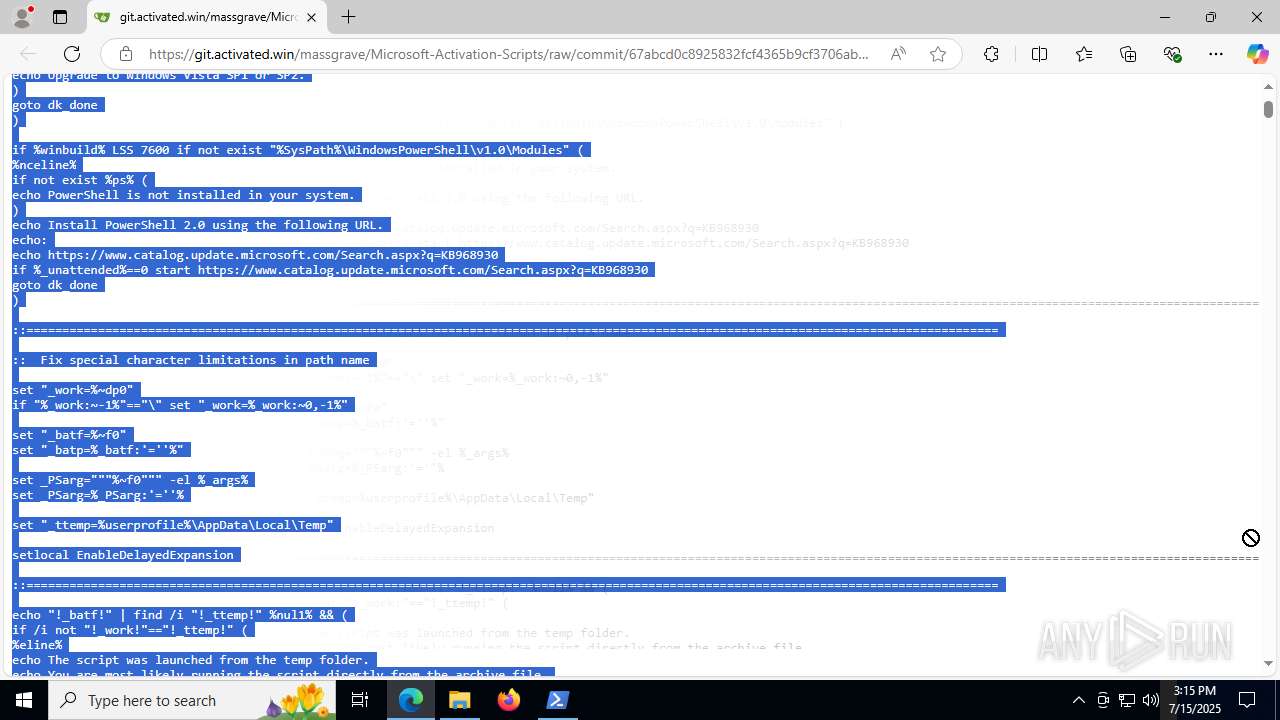
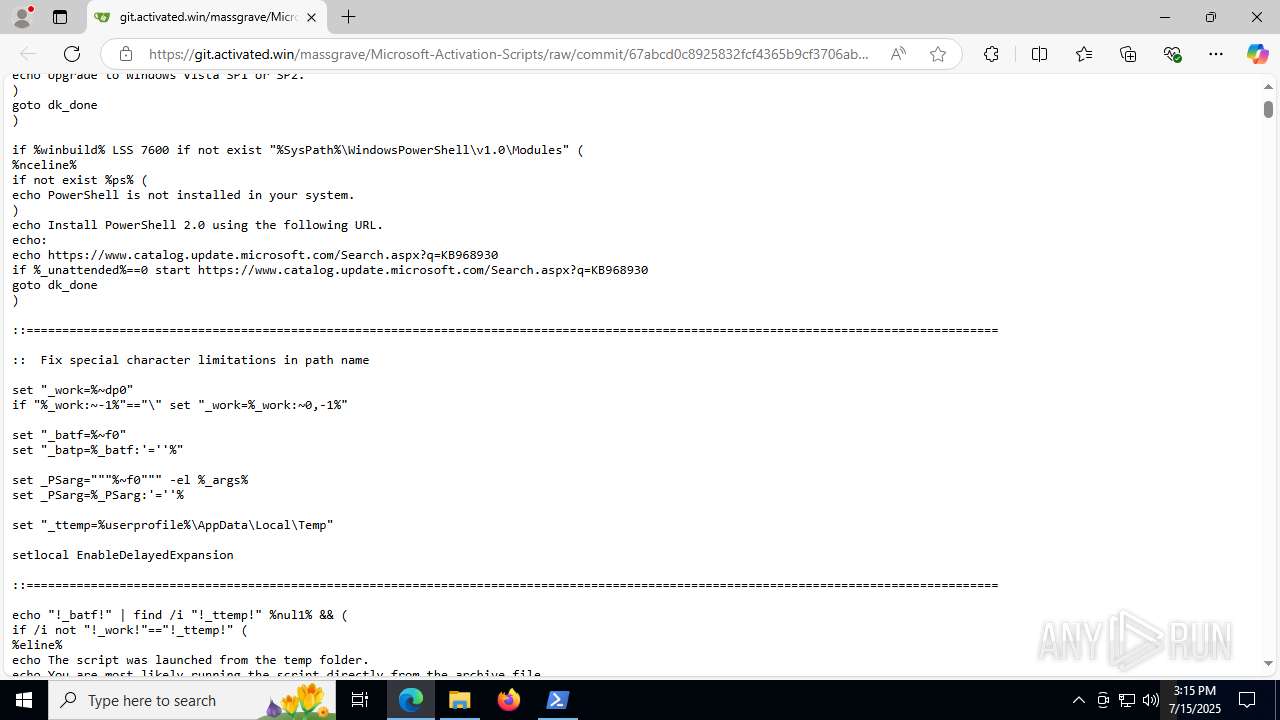
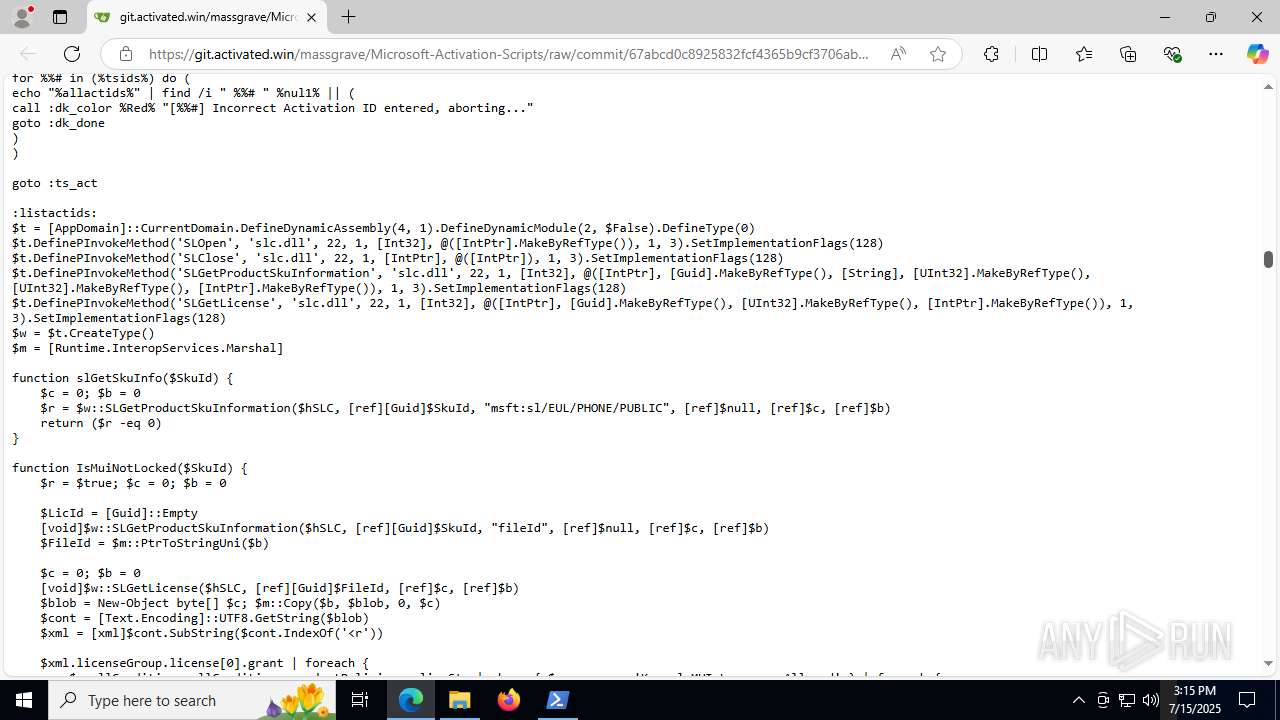
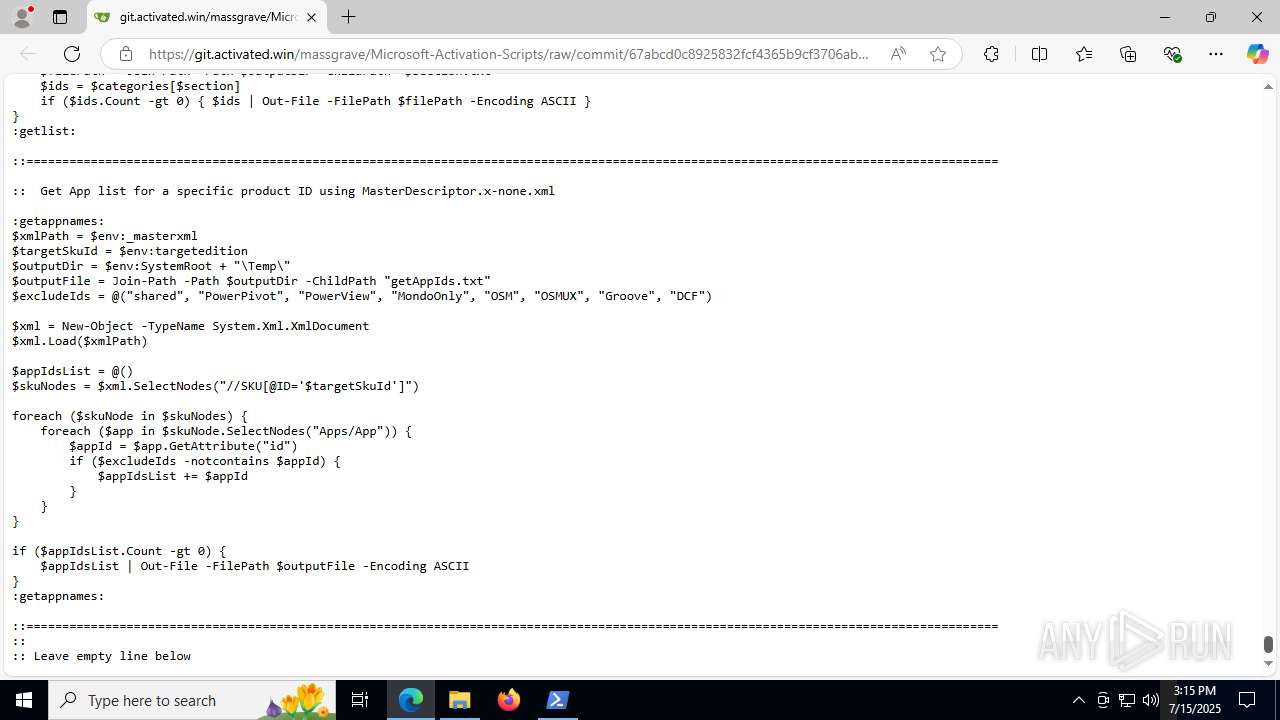
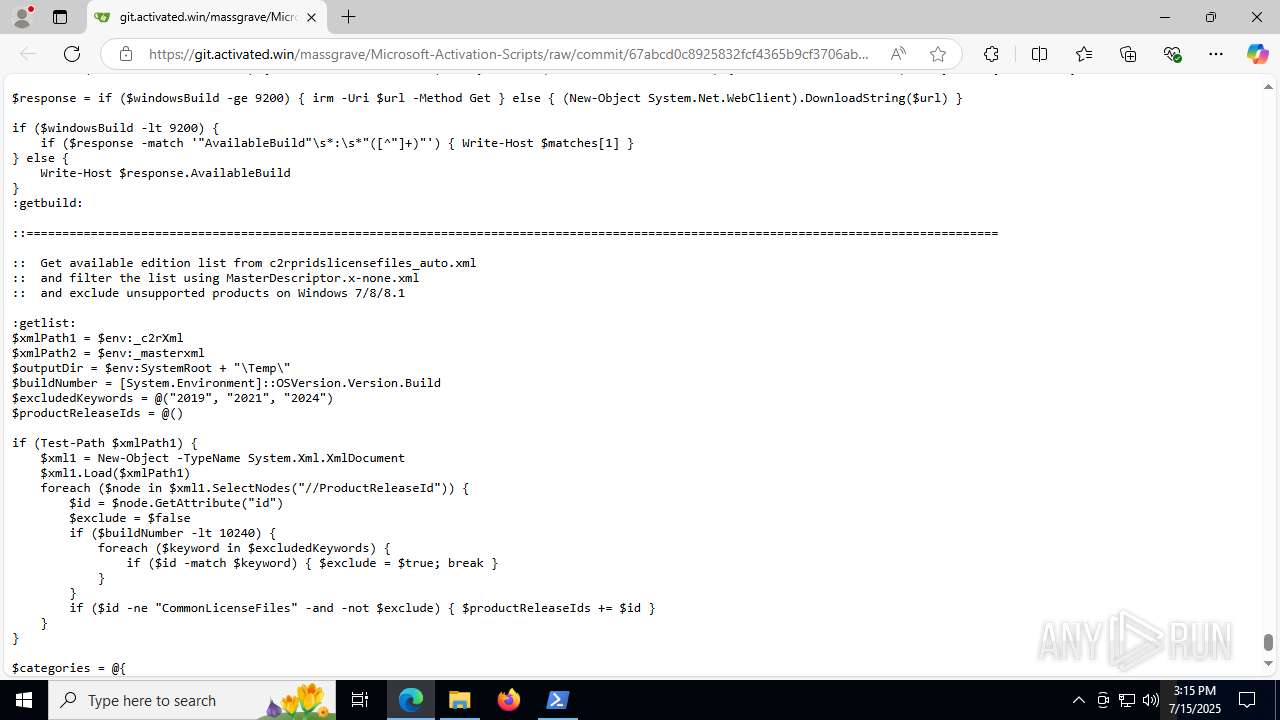
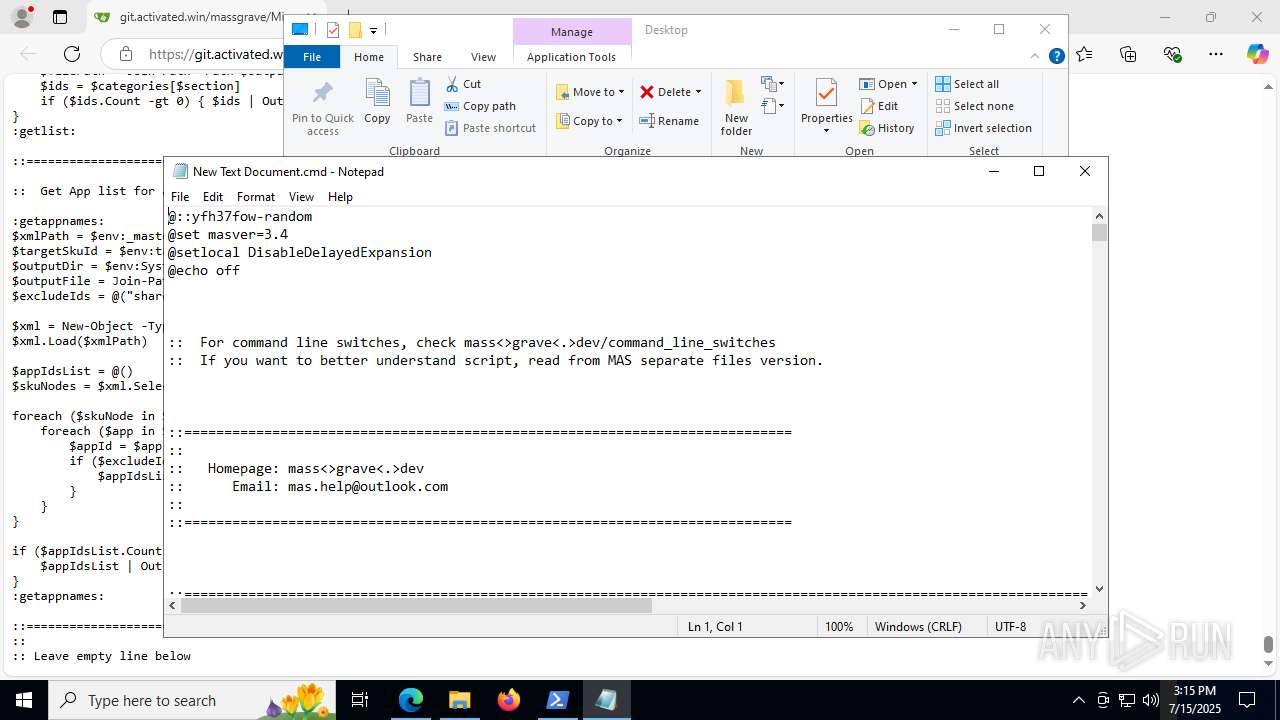
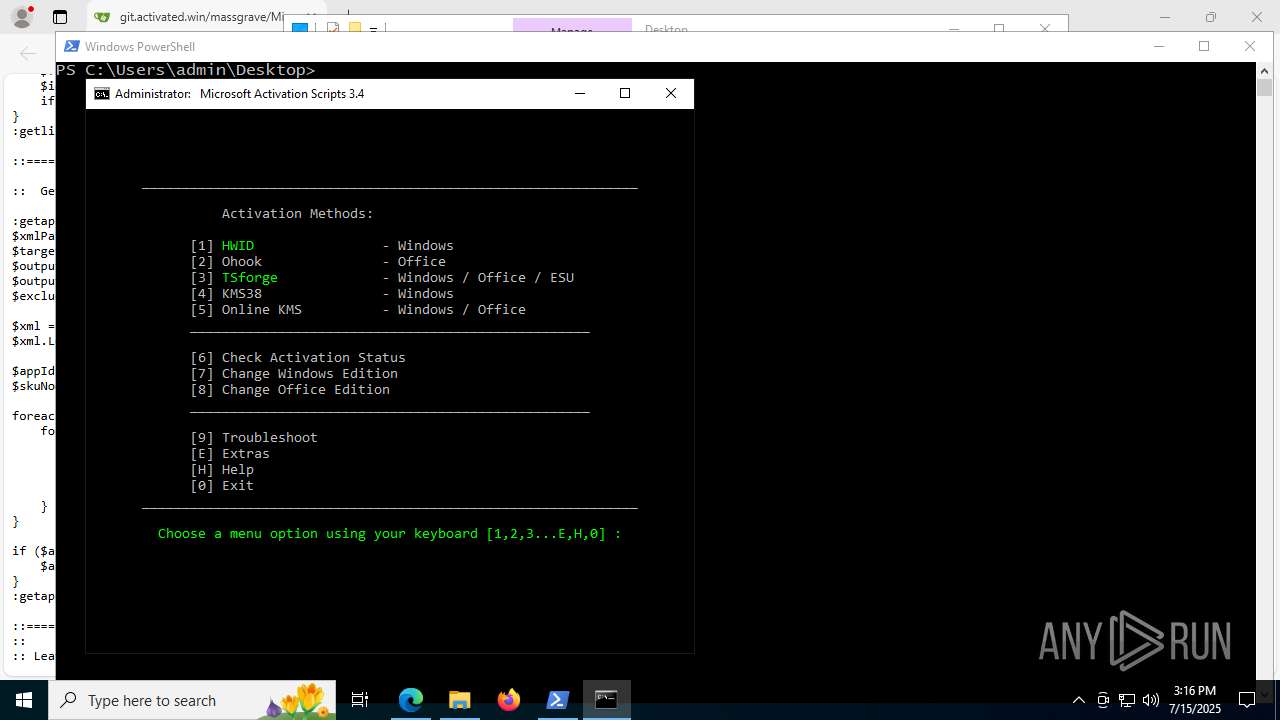
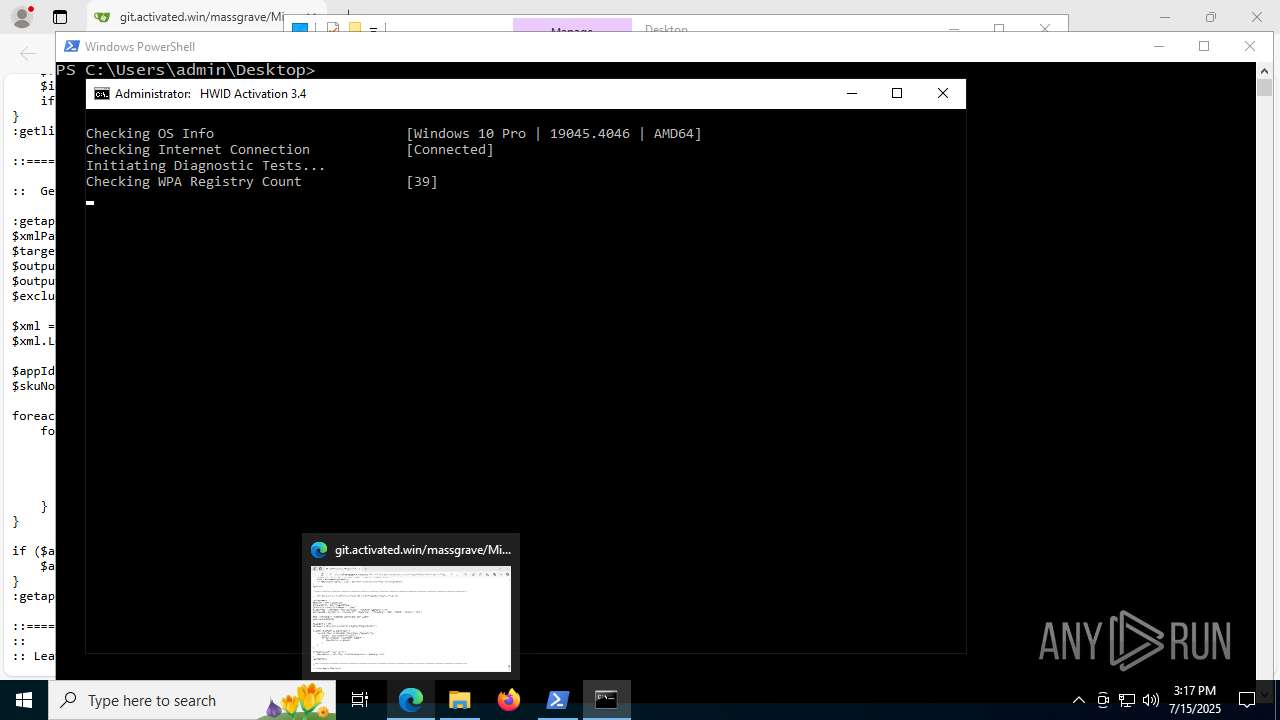
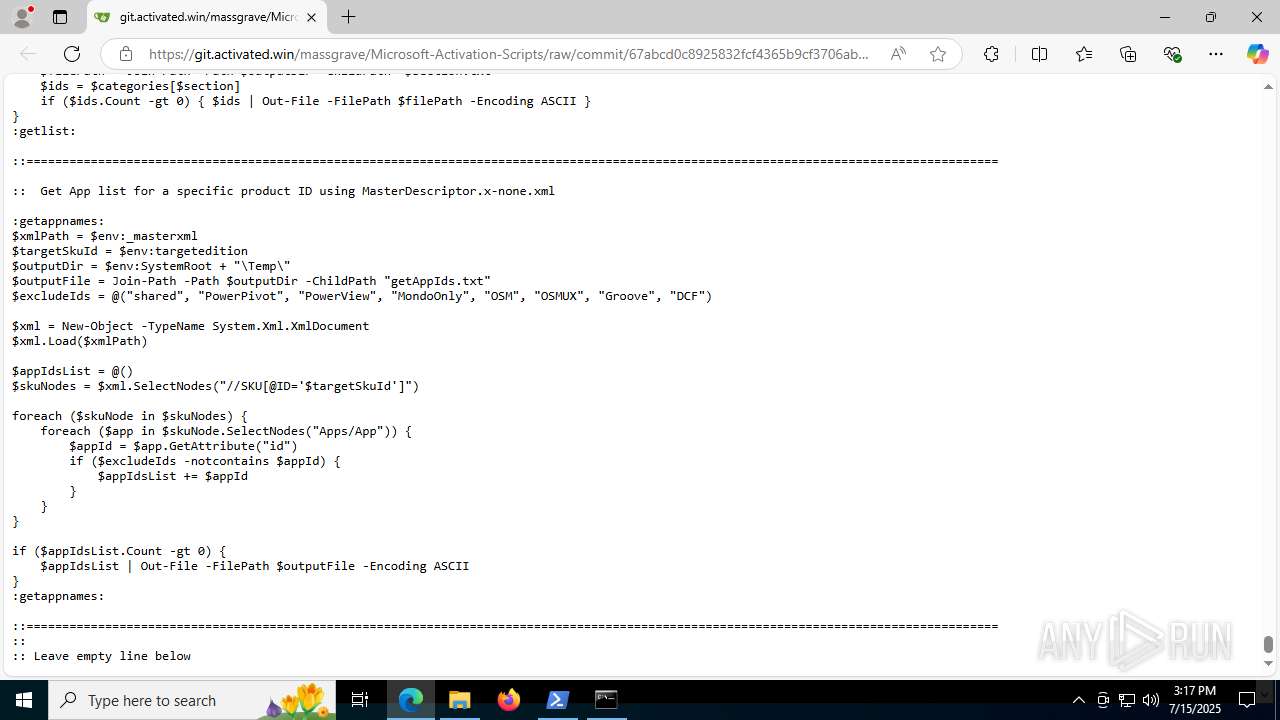
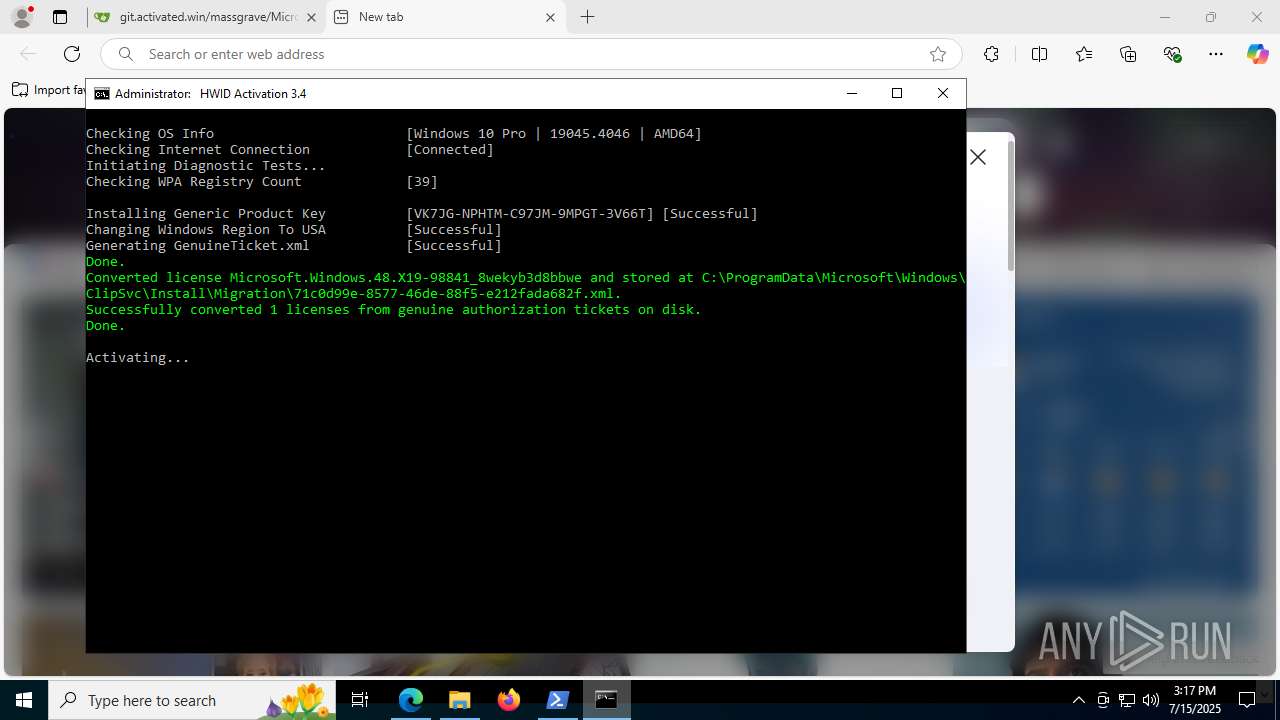
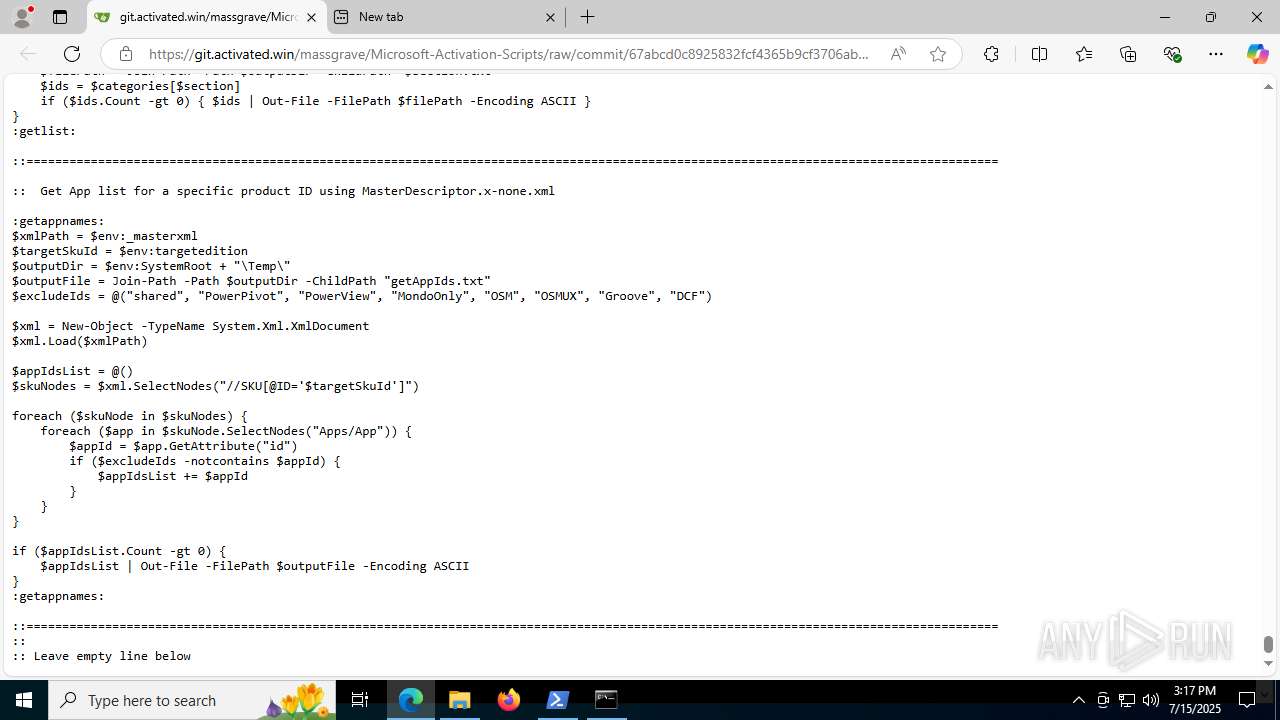
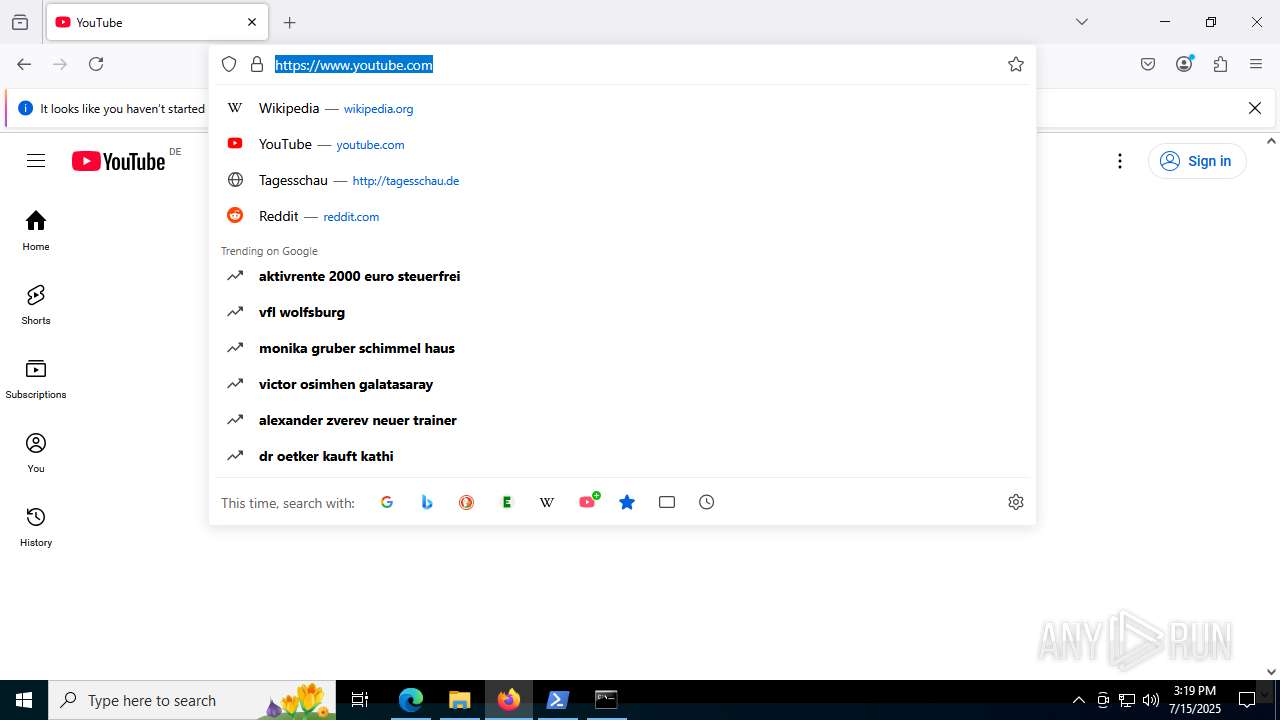
| URL: | https://git.activated.win/massgrave/Microsoft-Activation-Scripts/raw/commit/67abcd0c8925832fcf4365b9cf3706ab6fbf8571/MAS/All-In-One-Version-KL/MAS_AIO.cmd |
| Full analysis: | https://app.any.run/tasks/cd573341-3cc2-429c-91d1-cff305a74209 |
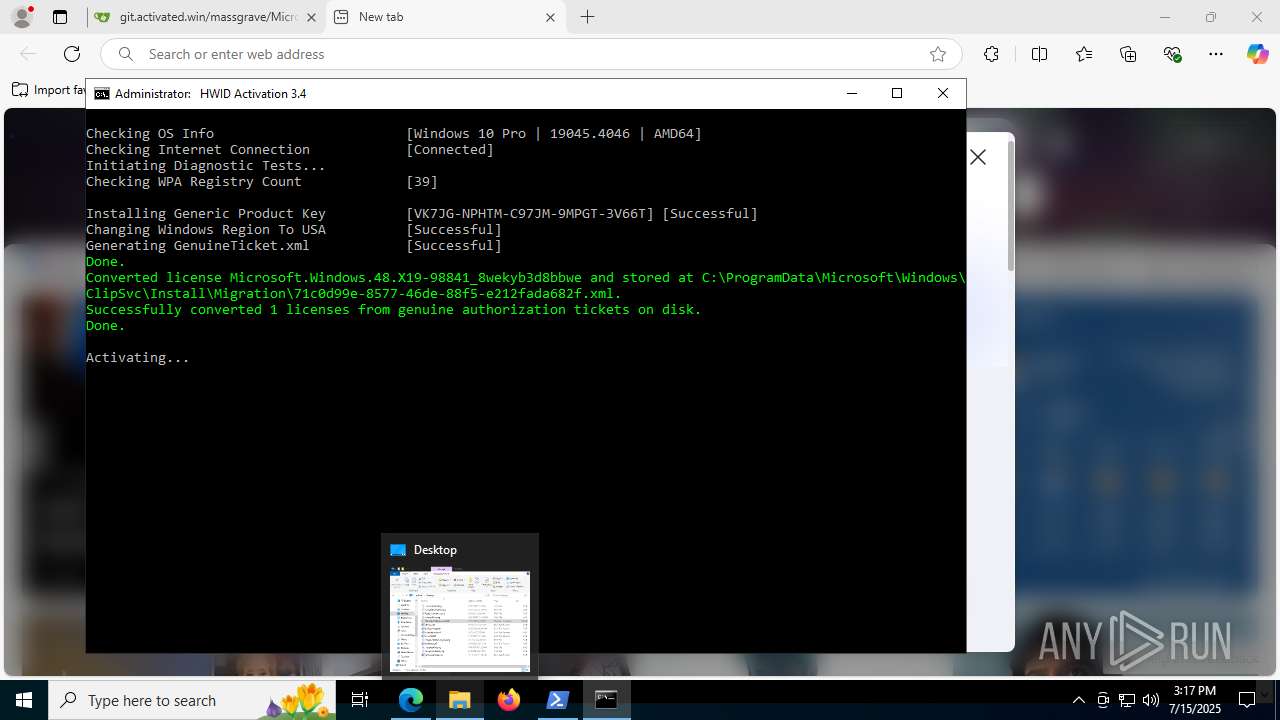
| Verdict: | Malicious activity |
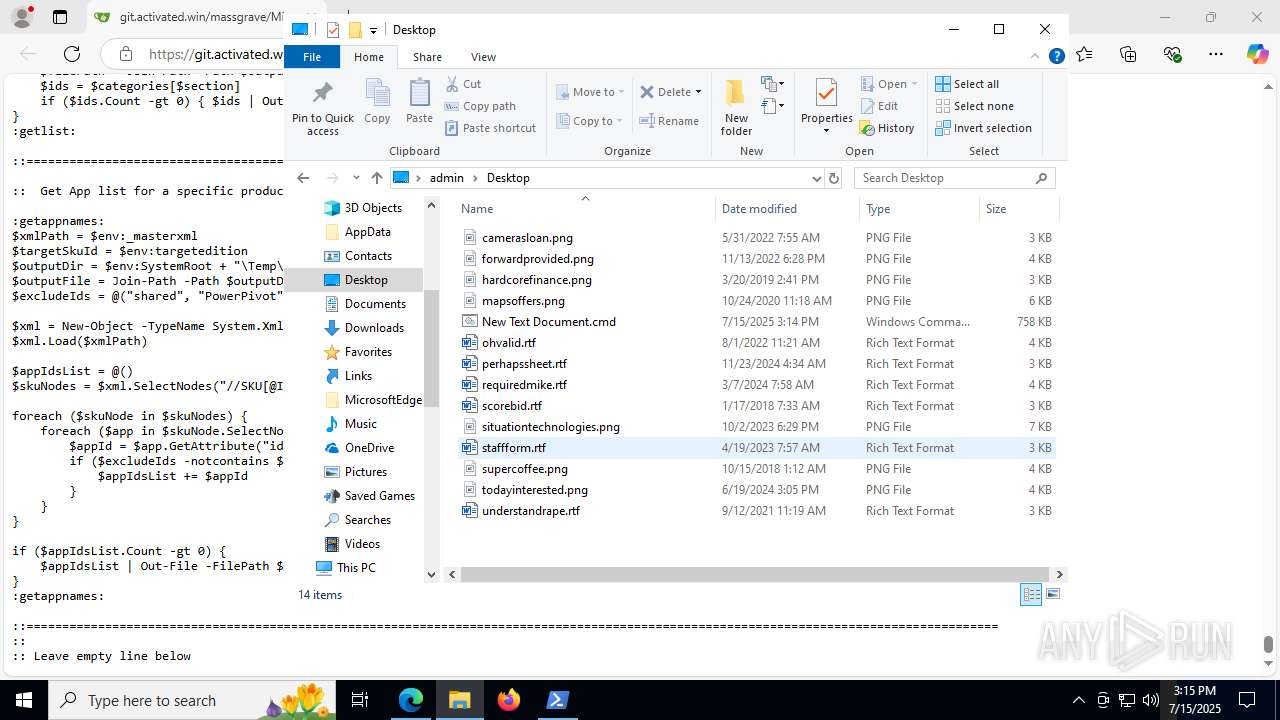
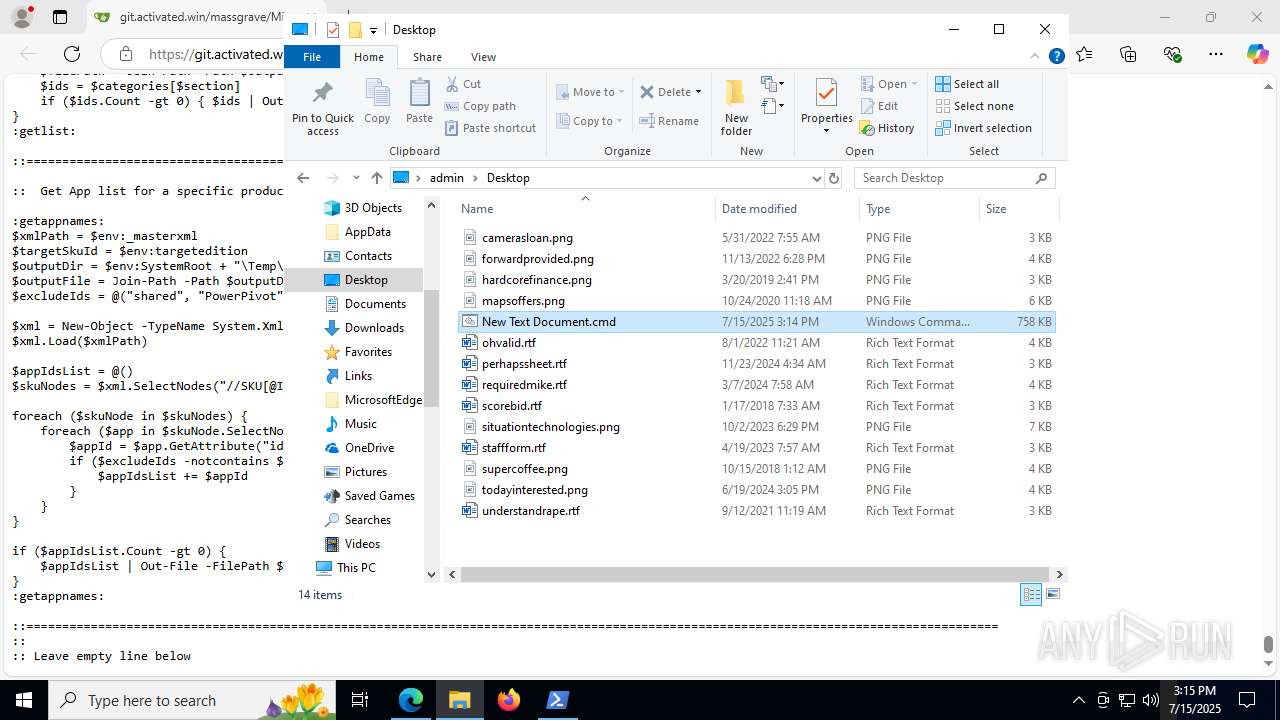
| Analysis date: | July 15, 2025, 15:14:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E55084D00298B976B4CDAB23A8D856DF |
| SHA1: | B4F2B01FE62DE830096EA3592091108E024673EC |
| SHA256: | 9C8864A94C0CCC5EE7A3DED5DBE753D3AE5AB8DD82196AB03524406D6FF4D682 |
| SSDEEP: | 3:N8thoE2mM0kugXuukGR3RLLLGXUs5dGvEHGBNXrKE7PmIHTDFokmtIqLAOAh9wln:2/smLIXuukGv/LGXUmdG2G3KAP5DFohz |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts SC.EXE for service management
- cmd.exe (PID: 7556)
- cmd.exe (PID: 2160)
- cmd.exe (PID: 4044)
- cmd.exe (PID: 8012)
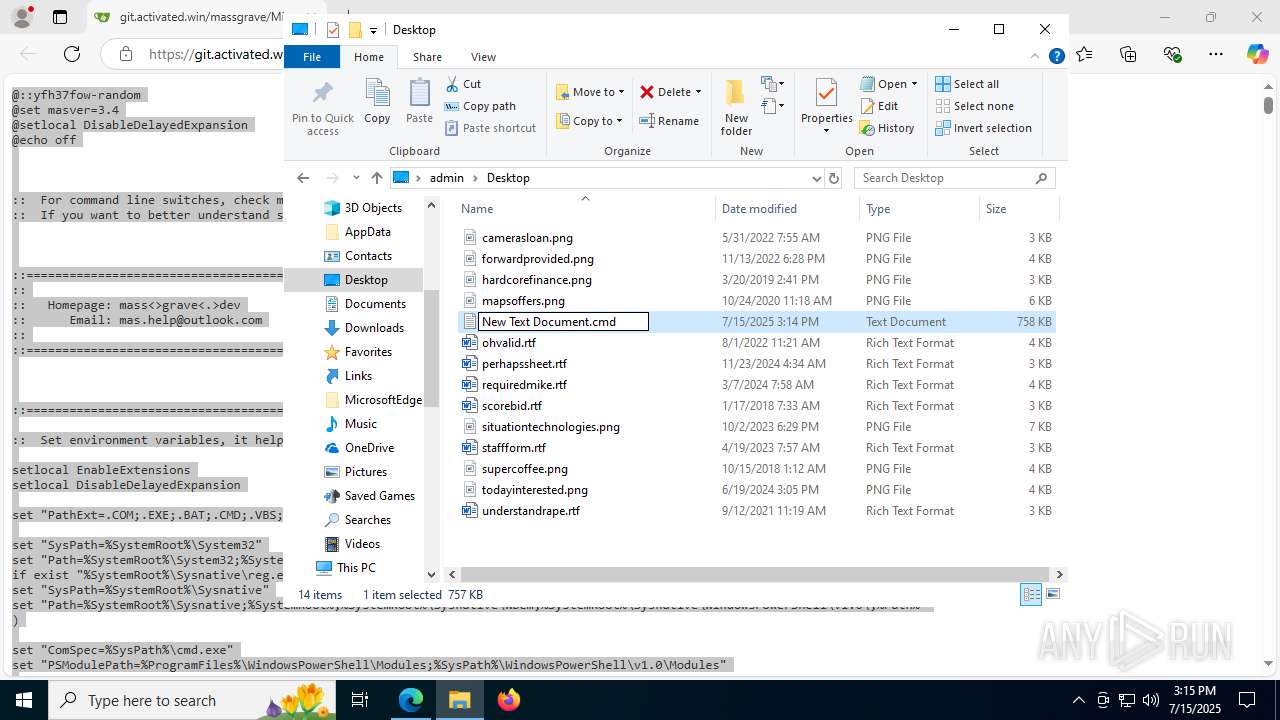
Executing commands from ".cmd" file
- powershell.exe (PID: 7648)
- powershell.exe (PID: 2348)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 2160)
- cmd.exe (PID: 4044)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7648)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 7224)
- powershell.exe (PID: 2348)
- cmd.exe (PID: 2160)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 4044)
- cmd.exe (PID: 5460)
Windows service management via SC.EXE
- sc.exe (PID: 7984)
- sc.exe (PID: 1212)
- sc.exe (PID: 6364)
- sc.exe (PID: 2220)
- sc.exe (PID: 6420)
- sc.exe (PID: 5644)
- sc.exe (PID: 3092)
- sc.exe (PID: 7464)
- sc.exe (PID: 504)
- sc.exe (PID: 6528)
- sc.exe (PID: 8096)
- sc.exe (PID: 5684)
- sc.exe (PID: 7416)
- sc.exe (PID: 2464)
- sc.exe (PID: 2848)
- sc.exe (PID: 7684)
- sc.exe (PID: 3148)
- sc.exe (PID: 5060)
- sc.exe (PID: 8012)
- sc.exe (PID: 7344)
- sc.exe (PID: 7288)
- sc.exe (PID: 7296)
- sc.exe (PID: 7248)
- sc.exe (PID: 1216)
- sc.exe (PID: 1056)
- sc.exe (PID: 7260)
- sc.exe (PID: 5084)
- sc.exe (PID: 4824)
- sc.exe (PID: 4644)
- sc.exe (PID: 7772)
- sc.exe (PID: 7180)
- sc.exe (PID: 5992)
- sc.exe (PID: 5080)
- sc.exe (PID: 2596)
- sc.exe (PID: 7700)
- sc.exe (PID: 6520)
- sc.exe (PID: 6104)
- sc.exe (PID: 3872)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 8012)
Application launched itself
- cmd.exe (PID: 7556)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 2160)
- cmd.exe (PID: 4044)
- cmd.exe (PID: 5460)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 2280)
- ClipUp.exe (PID: 7276)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 7924)
- powershell.exe (PID: 7136)
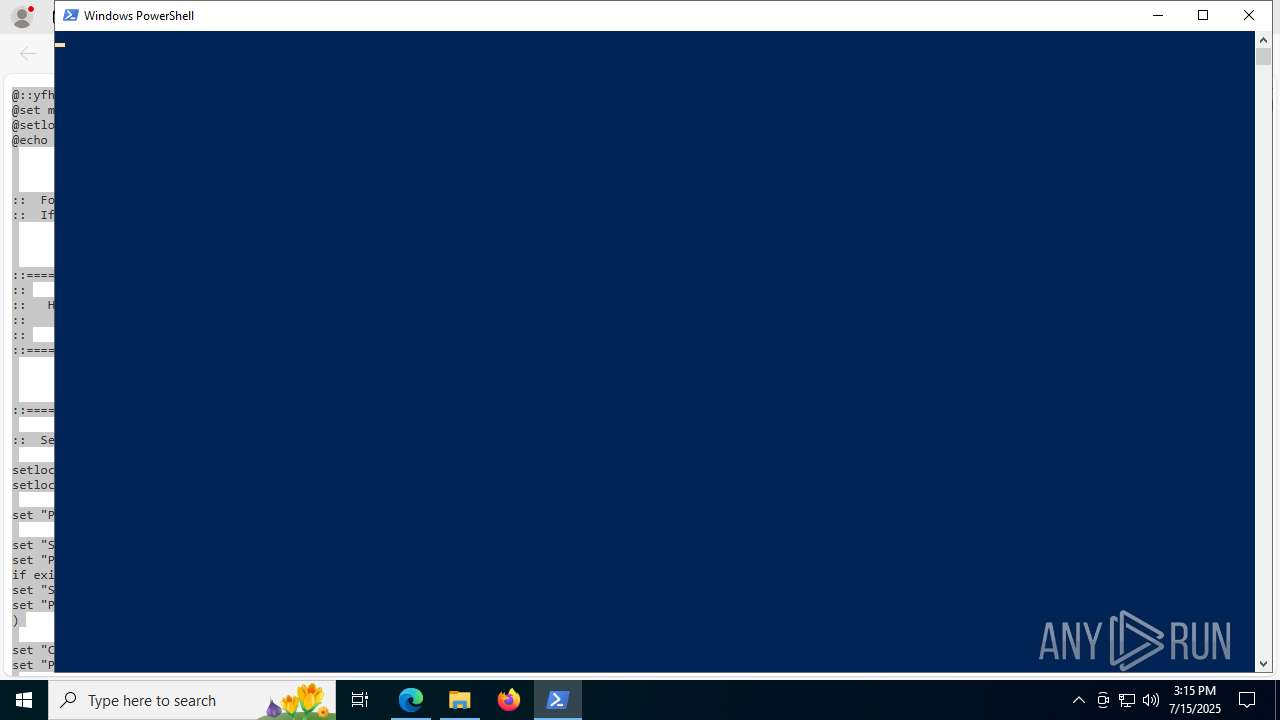
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7556)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 4044)
- cmd.exe (PID: 4948)
- powershell.exe (PID: 7480)
- cmd.exe (PID: 6536)
- cmd.exe (PID: 440)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 3392)
- powershell.exe (PID: 2280)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 7136)
- powershell.exe (PID: 7924)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7556)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 4044)
- cmd.exe (PID: 4948)
- powershell.exe (PID: 7480)
- cmd.exe (PID: 6536)
- cmd.exe (PID: 440)
- cmd.exe (PID: 7348)
- powershell.exe (PID: 2280)
- cmd.exe (PID: 3392)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 7924)
- powershell.exe (PID: 7136)
Executes script without checking the security policy
- powershell.exe (PID: 2348)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 1832)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 3924)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6828)
- powershell.exe (PID: 5708)
- powershell.exe (PID: 6068)
- powershell.exe (PID: 6220)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 6308)
- powershell.exe (PID: 7212)
- powershell.exe (PID: 7660)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 2280)
- powershell.exe (PID: 7136)
- powershell.exe (PID: 6600)
- powershell.exe (PID: 7924)
- powershell.exe (PID: 7496)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7556)
- cmd.exe (PID: 2160)
- cmd.exe (PID: 4044)
- cmd.exe (PID: 8012)
Hides command output
- cmd.exe (PID: 6256)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 2508)
- cmd.exe (PID: 2704)
- cmd.exe (PID: 6536)
- cmd.exe (PID: 5424)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 1288)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 440)
- cmd.exe (PID: 6104)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 7108)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 6256)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 4044)
- cmd.exe (PID: 6536)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6256)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 4044)
- cmd.exe (PID: 4948)
- cmd.exe (PID: 6536)
- cmd.exe (PID: 3392)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 1832)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 6828)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 1832)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 6828)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 1832)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 6828)
- powershell.exe (PID: 6308)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2160)
- cmd.exe (PID: 4044)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 5652)
- cmd.exe (PID: 4044)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 2704)
Probably file/command deobfuscation
- cmd.exe (PID: 4948)
- cmd.exe (PID: 3392)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 7480)
- powershell.exe (PID: 2280)
- powershell.exe (PID: 7136)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 7924)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4044)
- cmd.exe (PID: 5424)
- cmd.exe (PID: 1288)
- cmd.exe (PID: 6104)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 4044)
INFO
Reads Environment values
- identity_helper.exe (PID: 7440)
Application launched itself
- msedge.exe (PID: 1044)
- firefox.exe (PID: 8140)
- firefox.exe (PID: 7296)
Reads the software policy settings
- slui.exe (PID: 7568)
Reads the computer name
- identity_helper.exe (PID: 7440)
Checks supported languages
- identity_helper.exe (PID: 7440)
- mode.com (PID: 6224)
- mode.com (PID: 3844)
- mode.com (PID: 7684)
- mode.com (PID: 4860)
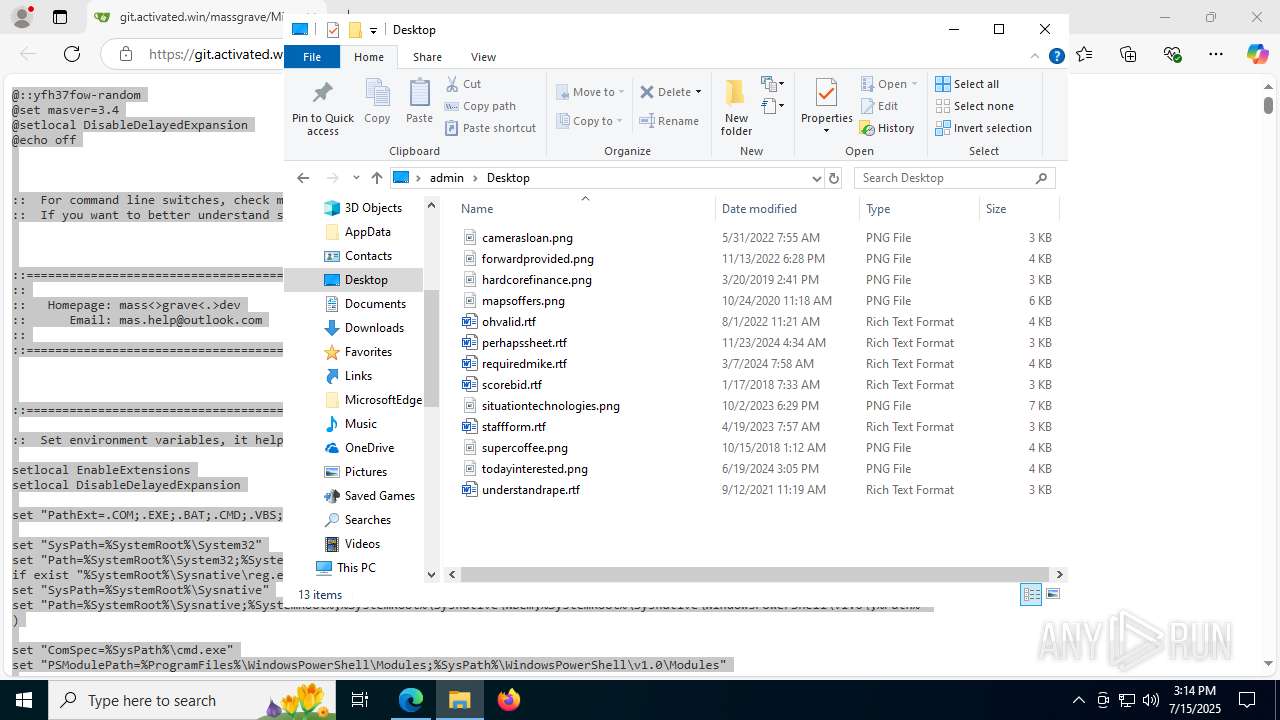
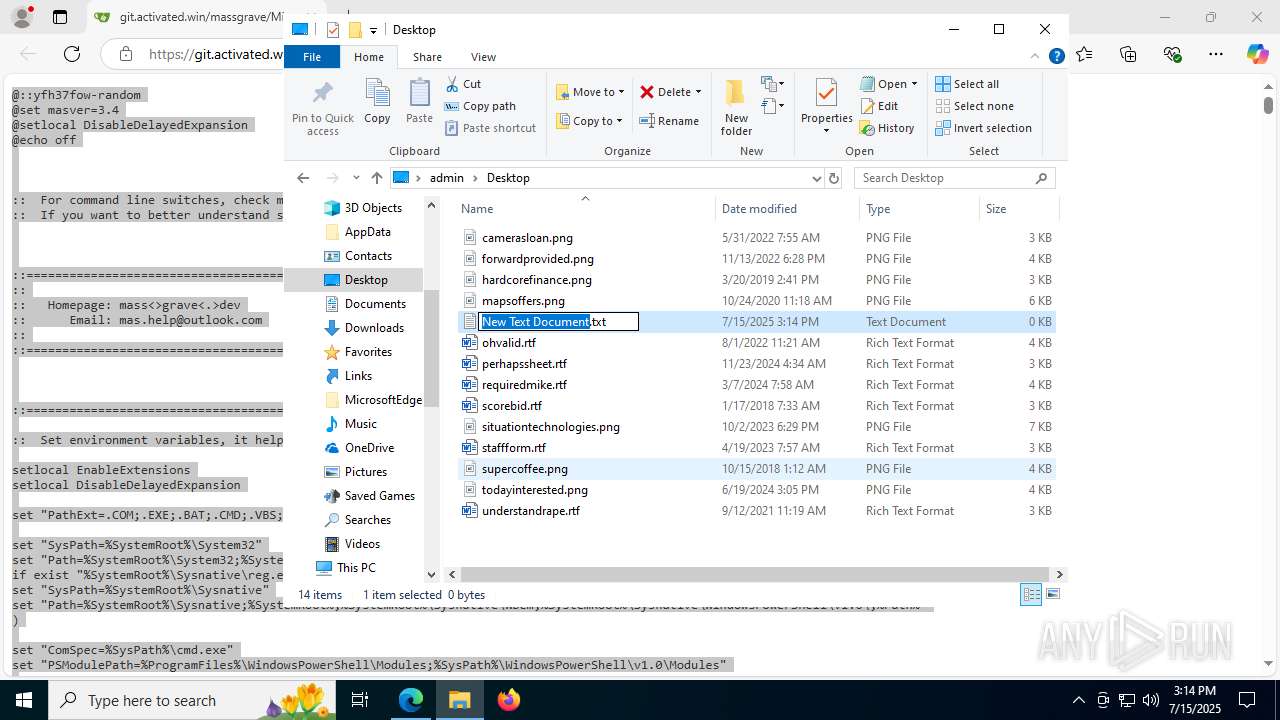
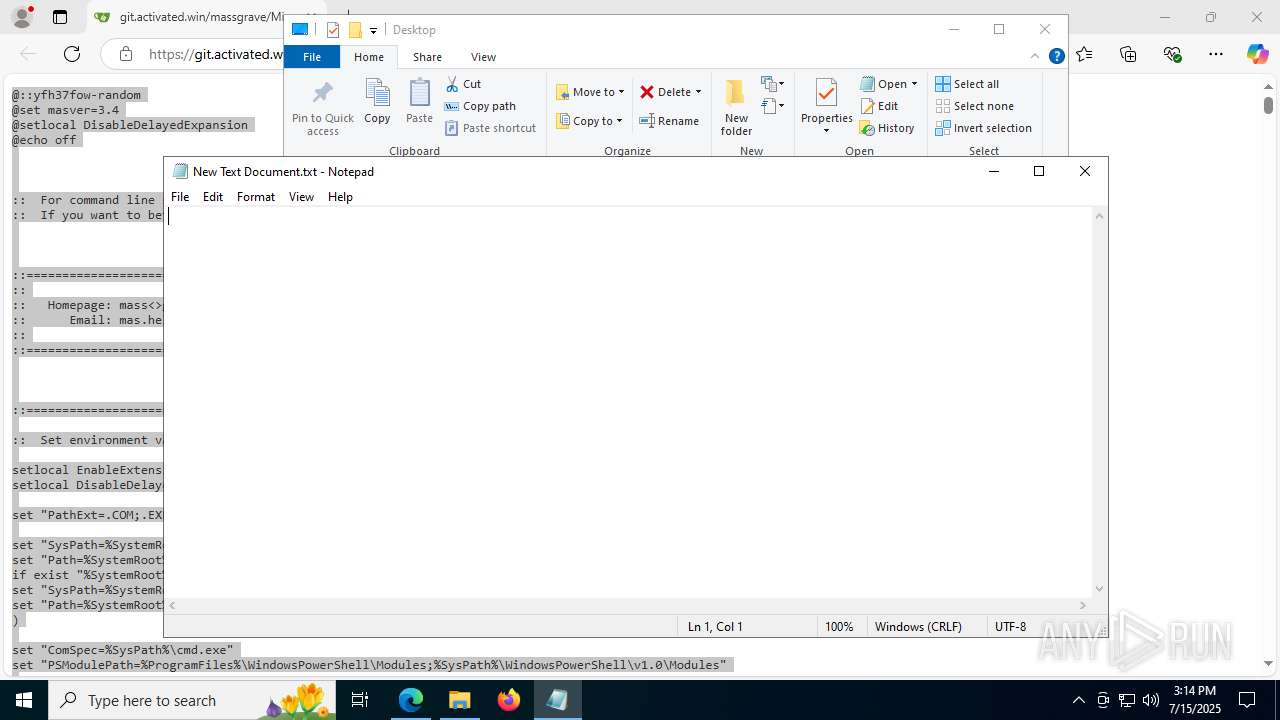
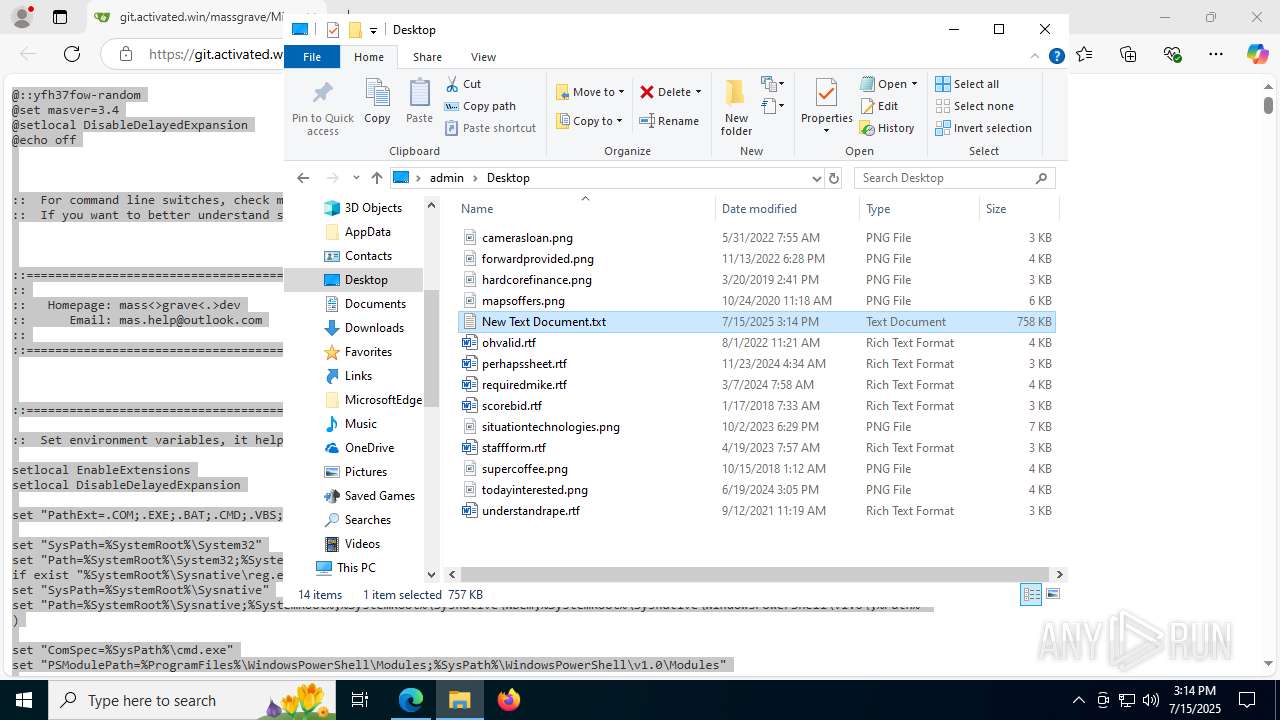
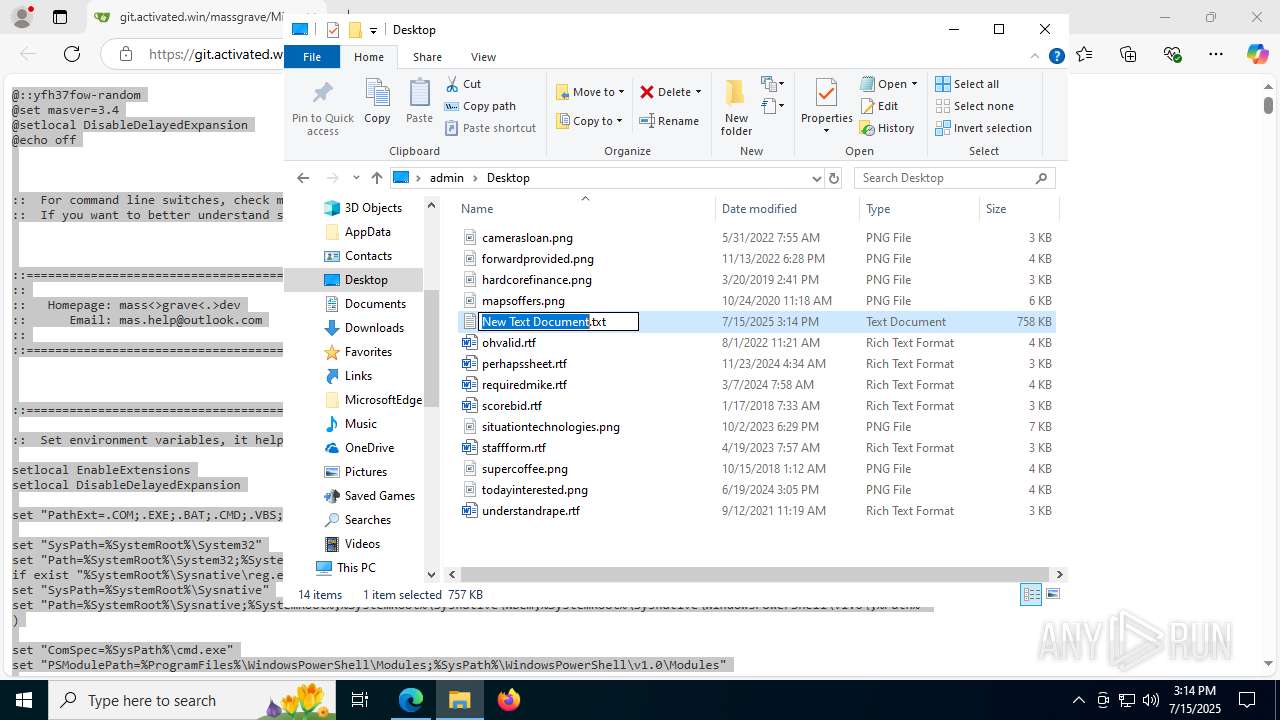
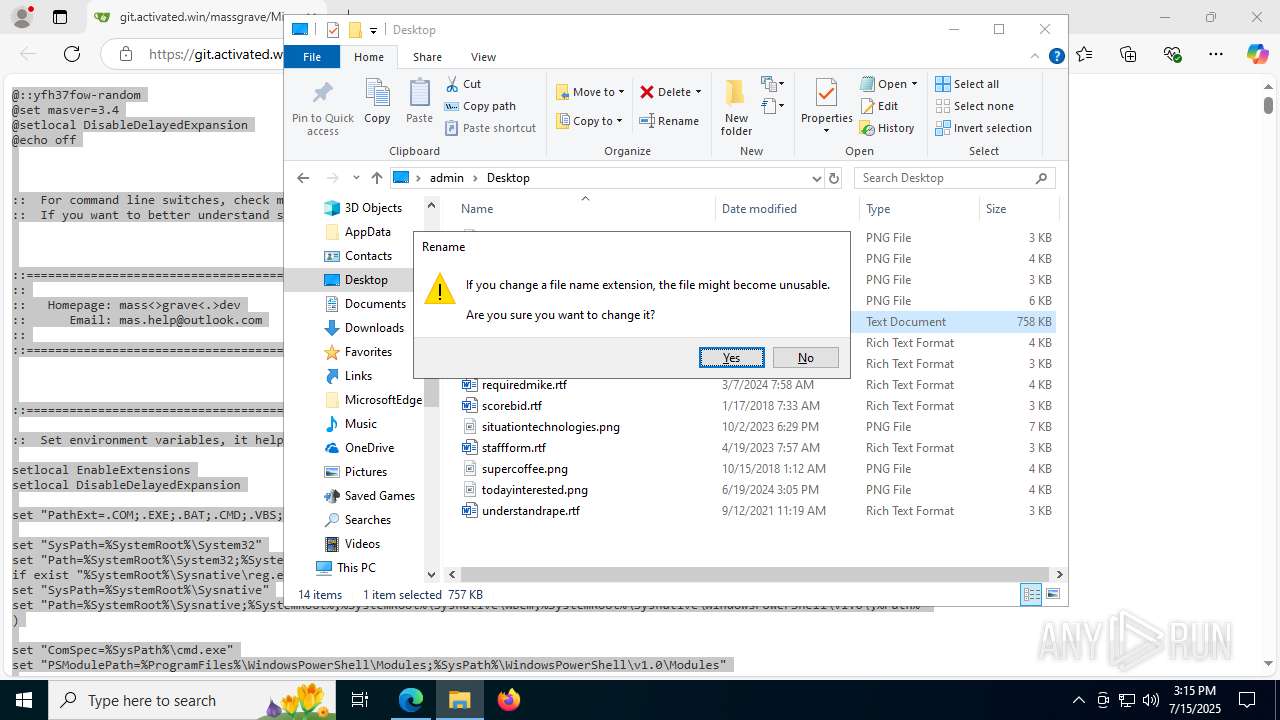
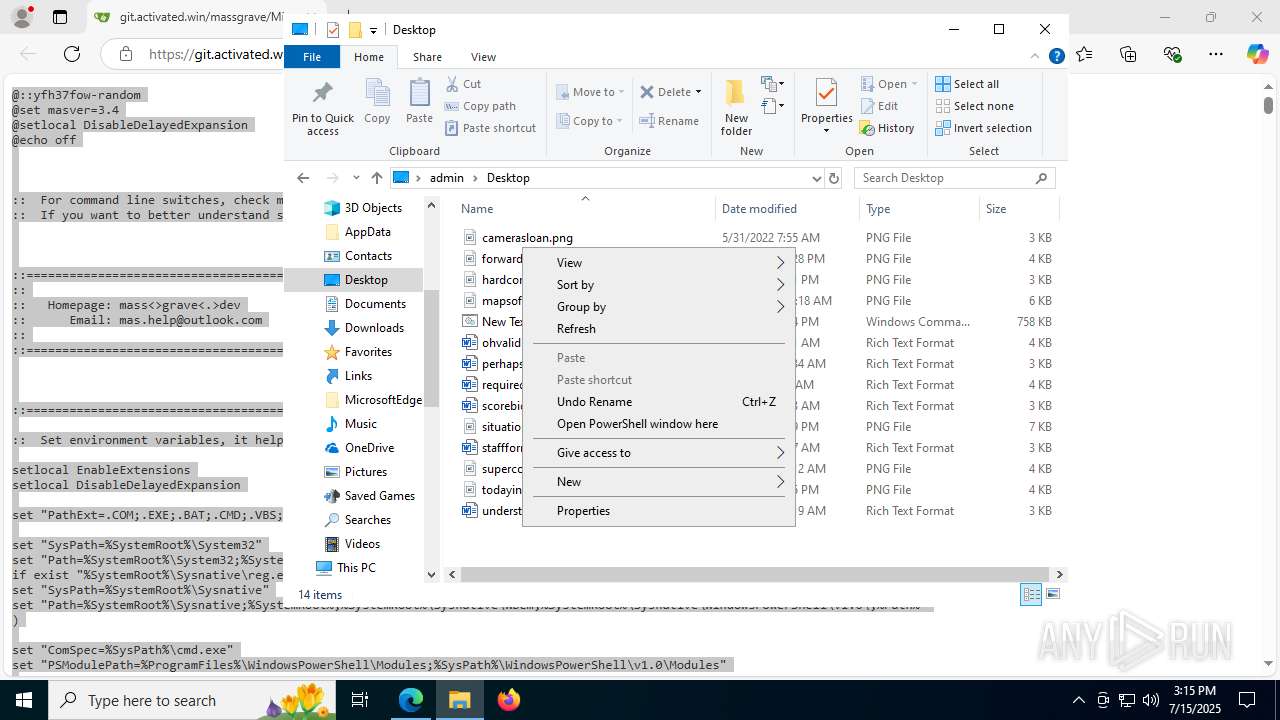
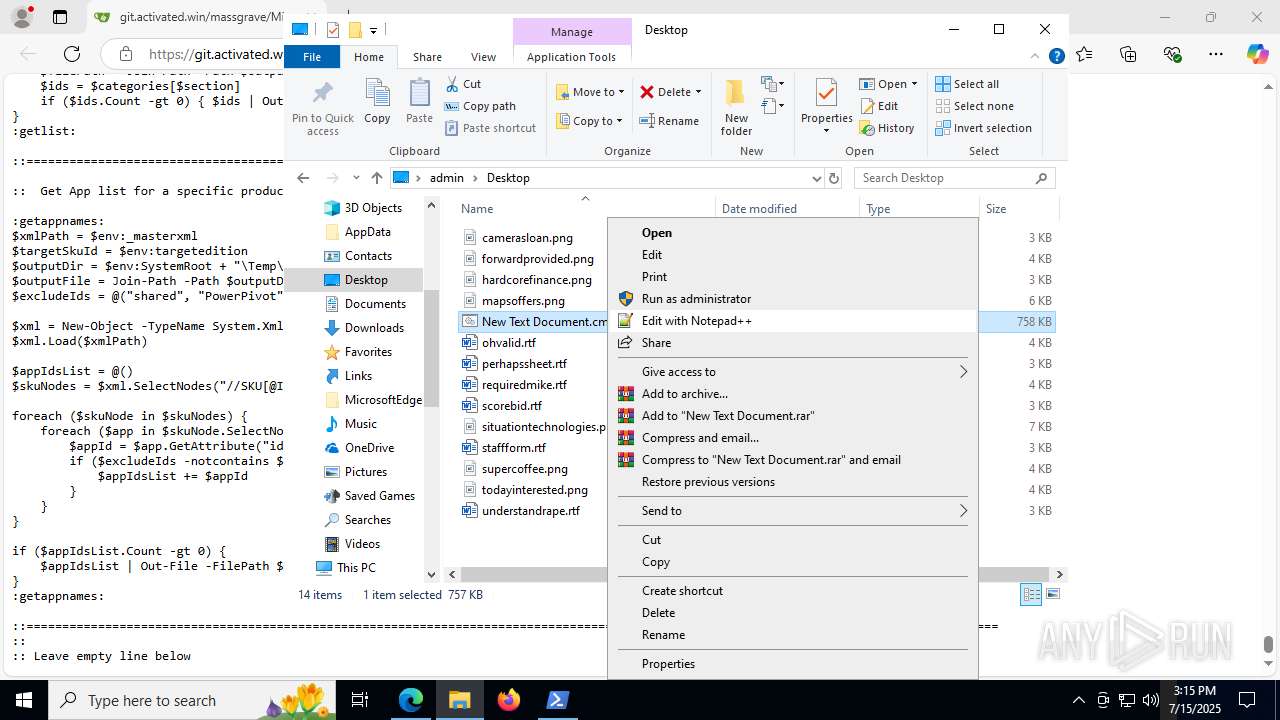
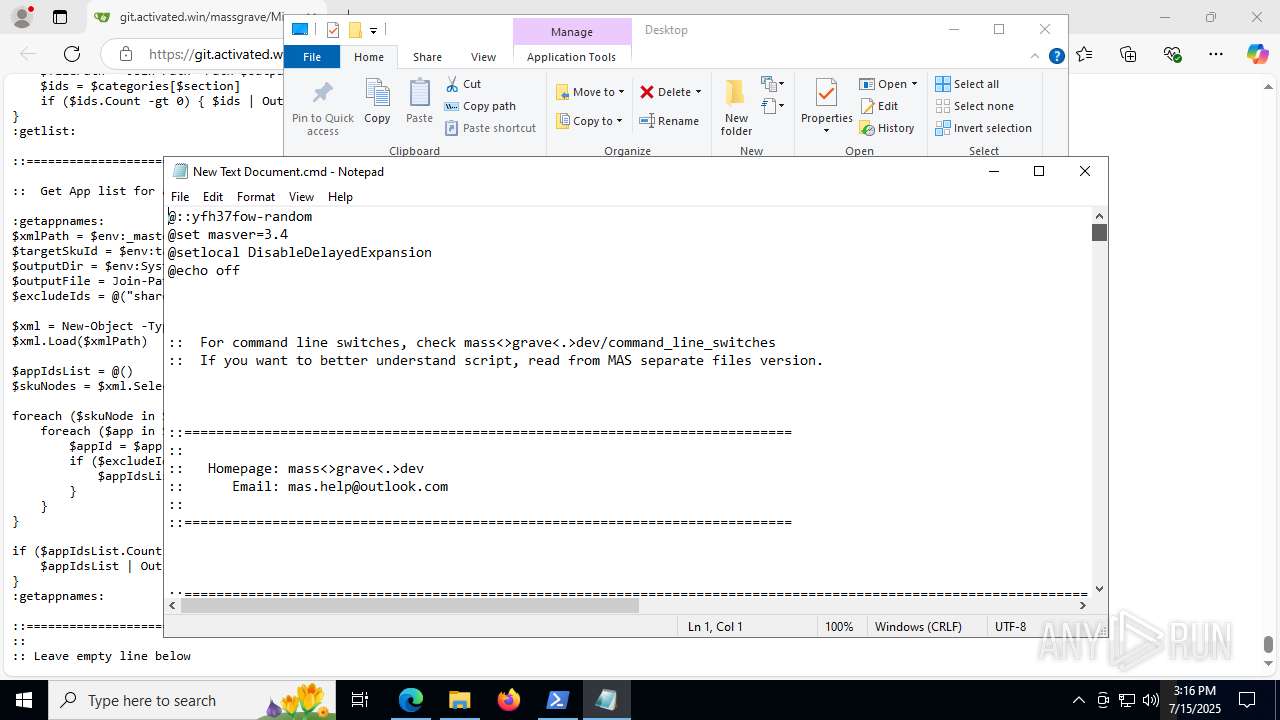
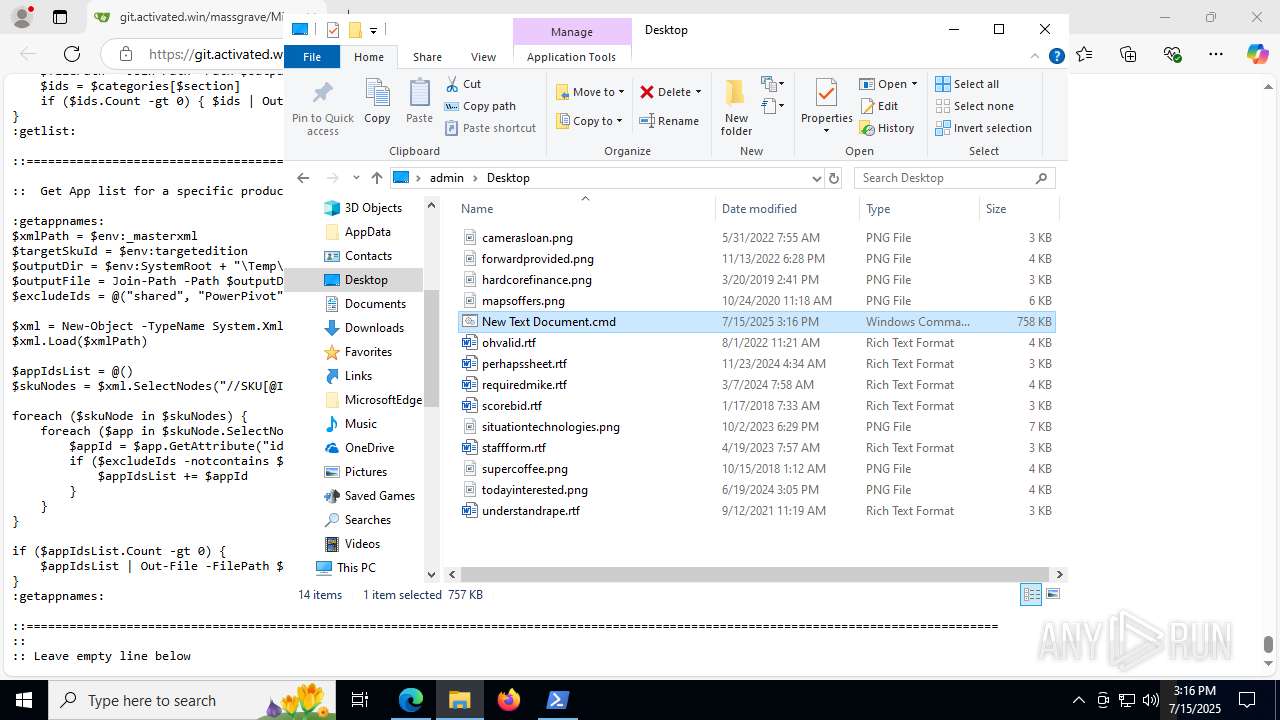
Manual execution by a user
- notepad.exe (PID: 7548)
- powershell.exe (PID: 7648)
- notepad.exe (PID: 3932)
- firefox.exe (PID: 8140)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7548)
- notepad.exe (PID: 3932)
- WMIC.exe (PID: 2280)
- WMIC.exe (PID: 4764)
- WMIC.exe (PID: 7248)
- WMIC.exe (PID: 3972)
- WMIC.exe (PID: 2520)
- WMIC.exe (PID: 7400)
- WMIC.exe (PID: 1580)
- WMIC.exe (PID: 6584)
- WMIC.exe (PID: 3520)
- WMIC.exe (PID: 7820)
- WMIC.exe (PID: 2760)
- WMIC.exe (PID: 1352)
- WMIC.exe (PID: 7496)
- WMIC.exe (PID: 7552)
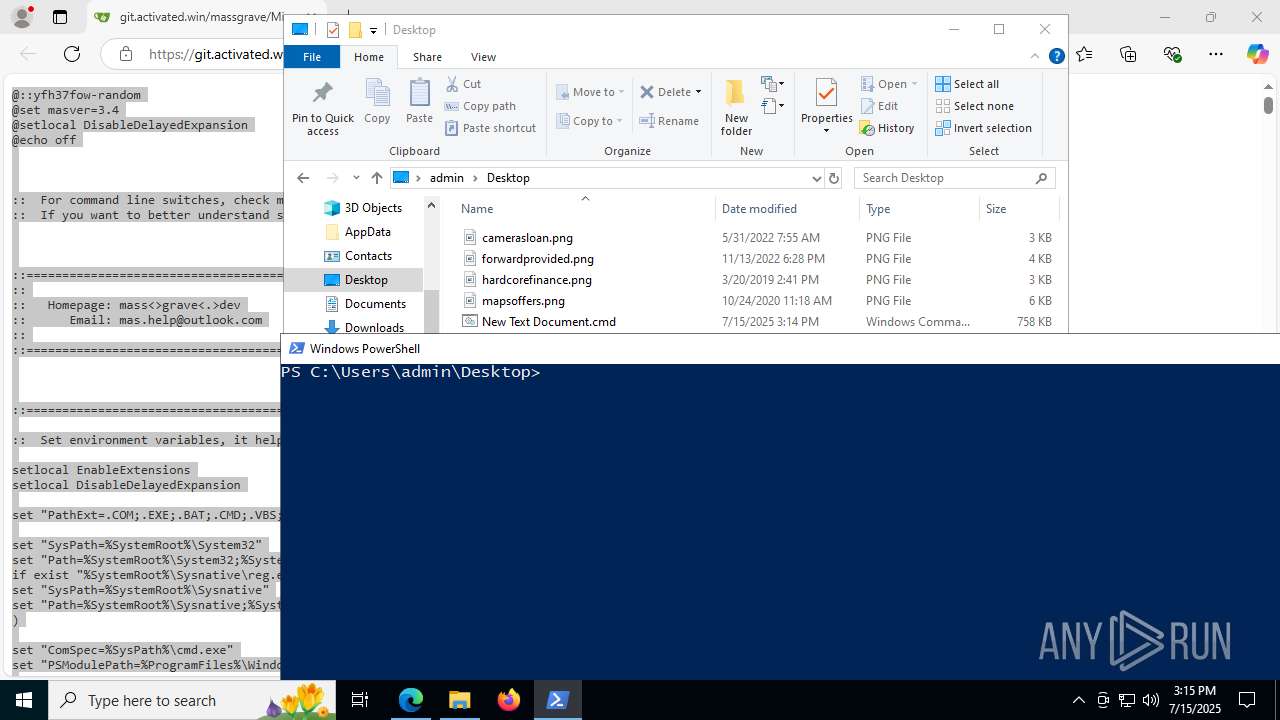
Checks current location (POWERSHELL)
- powershell.exe (PID: 7648)
Checks proxy server information
- slui.exe (PID: 7568)
Checks operating system version
- cmd.exe (PID: 7556)
- cmd.exe (PID: 2160)
- cmd.exe (PID: 4044)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 1832)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 6828)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 1832)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 6828)
Starts MODE.COM to configure console settings
- mode.com (PID: 6224)
- mode.com (PID: 7684)
- mode.com (PID: 4860)
- mode.com (PID: 3844)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 1832)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 6828)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6068)
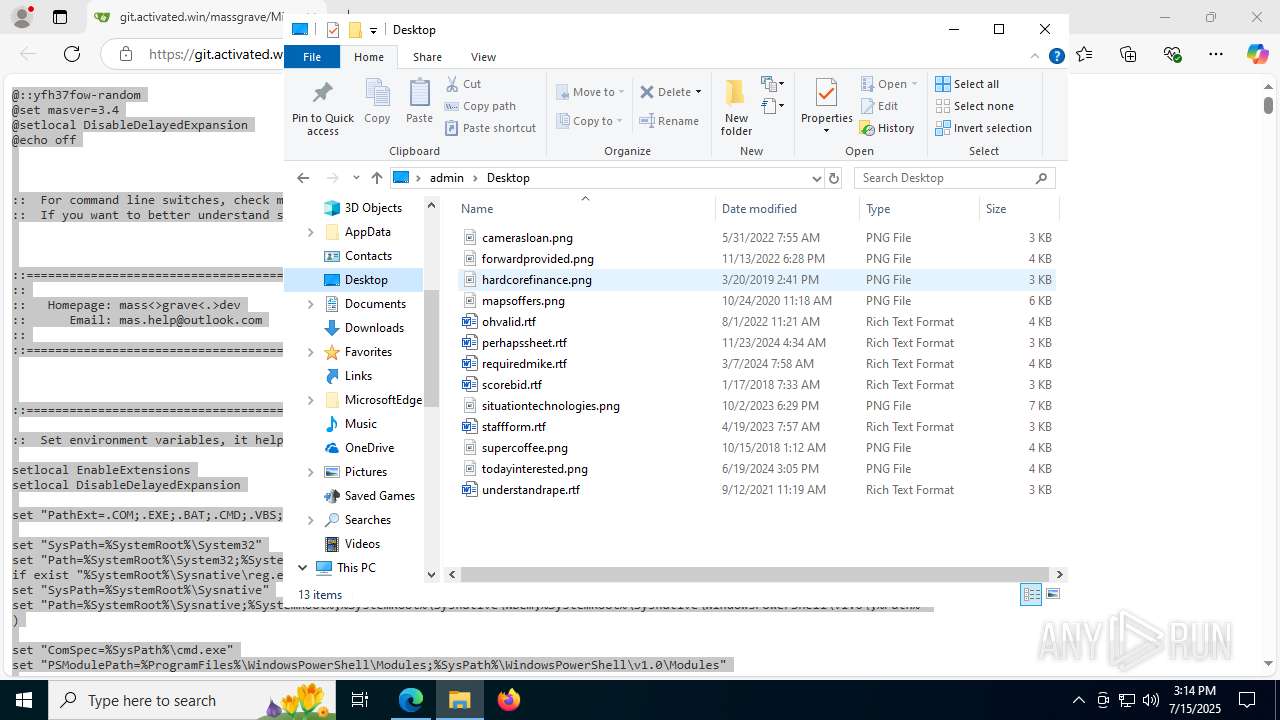
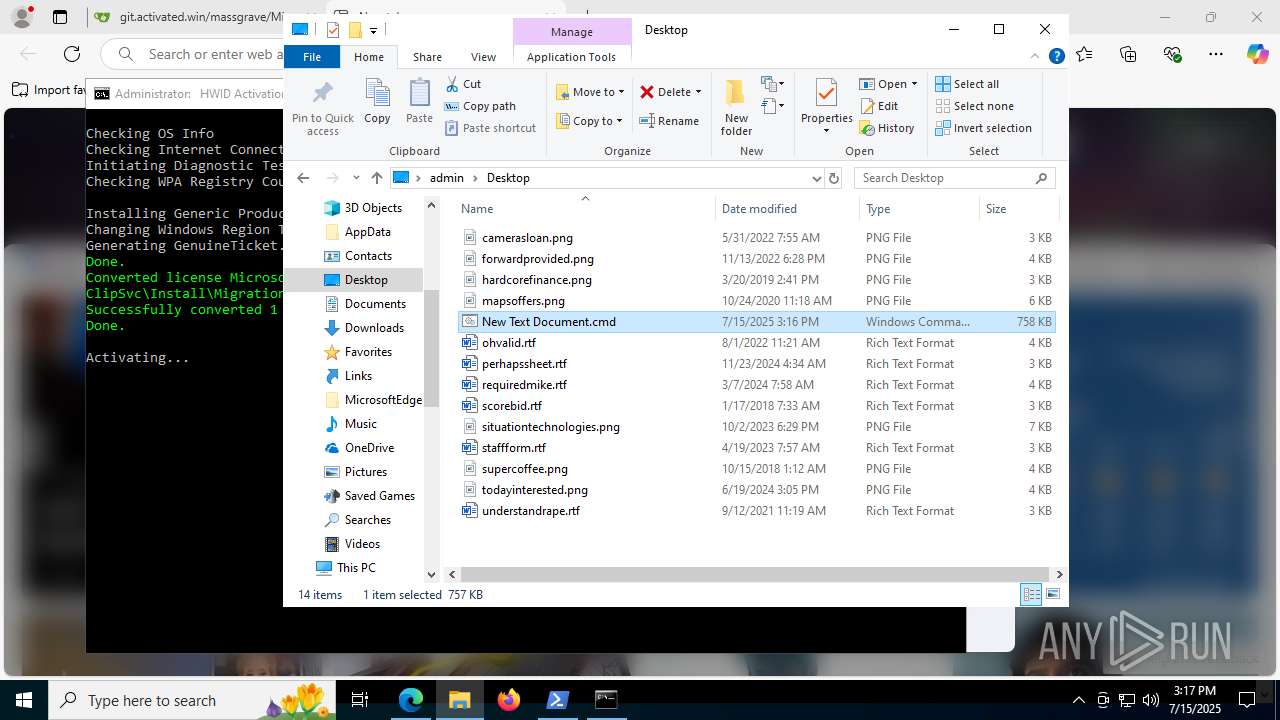
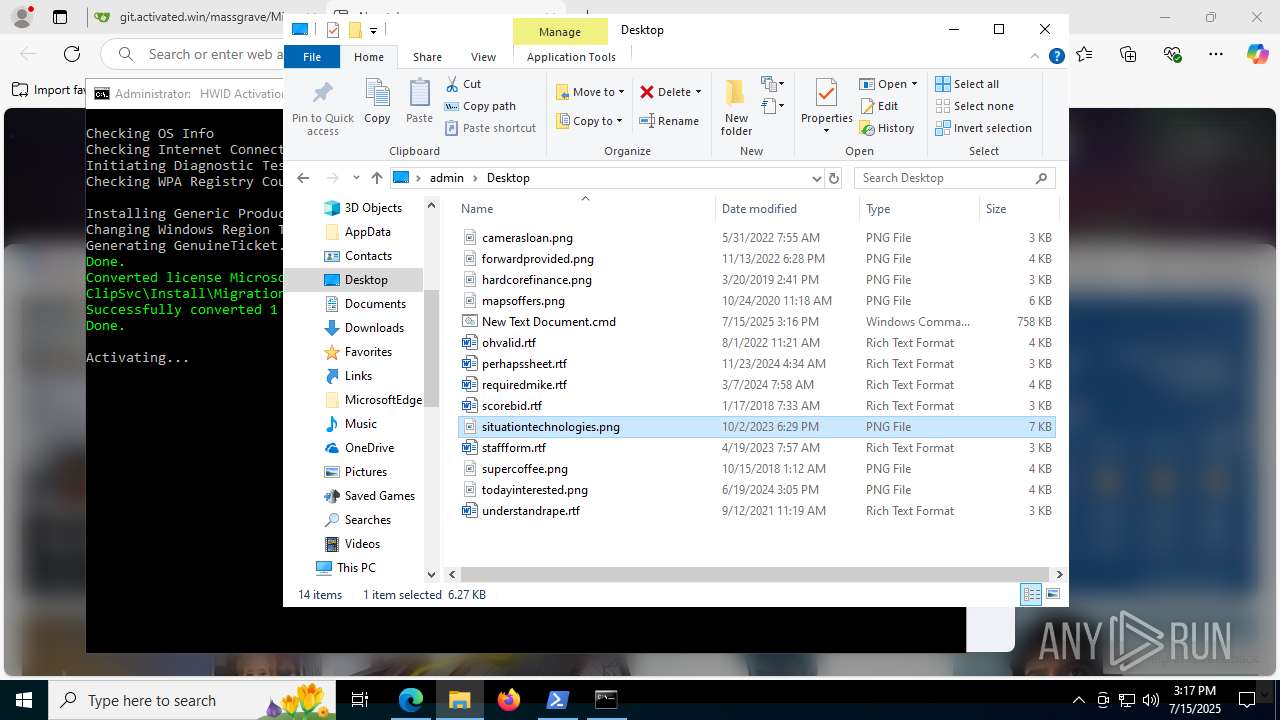
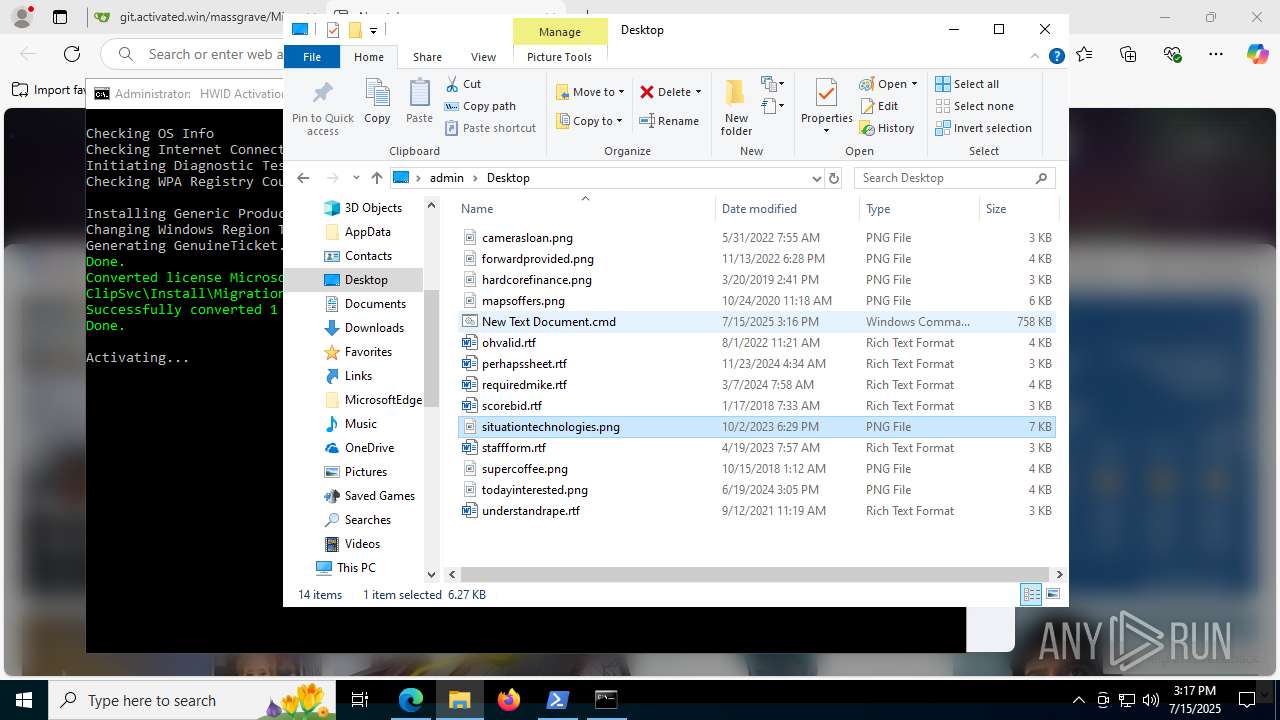
Creates files in the program directory
- cmd.exe (PID: 4044)
- ClipUp.exe (PID: 1392)
Create files in a temporary directory
- ClipUp.exe (PID: 1392)
Reads Microsoft Office registry keys
- firefox.exe (PID: 7296)
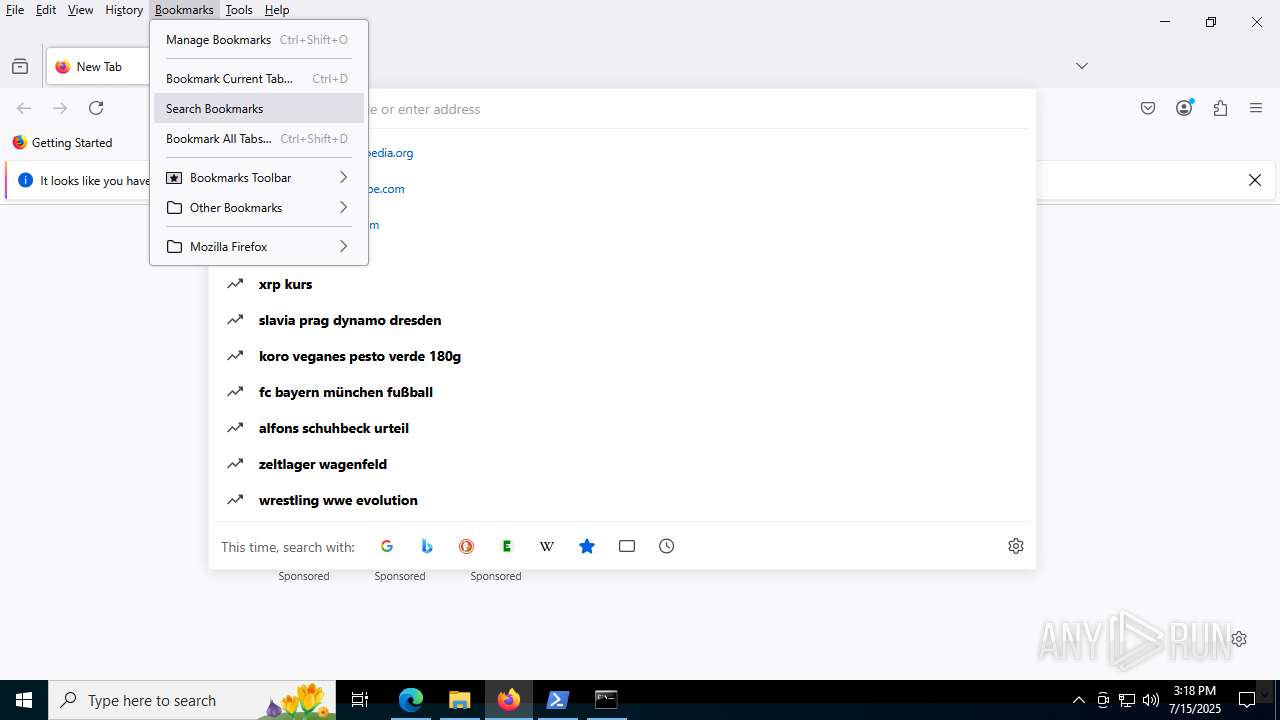
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
523
Monitored processes
363
Malicious processes
13
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4516,i,5855331274201112733,716154922297195472,262144 --variations-seed-version --mojo-platform-channel-handle=3484 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 320 | findstr /i "0x800410 0x800440 0x80131501" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | C:\WINDOWS\System32\cmd.exe /c C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "(Get-ScheduledTask -TaskName 'SvcRestartTask' -TaskPath '\Microsoft\Windows\SoftwareProtectionPlatform\').State" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 480 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 504 | sc start wlidsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | C:\WINDOWS\System32\cmd.exe /c reg query "HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Environment" /v PROCESSOR_ARCHITECTURE | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4400 -prefsLen 39068 -prefMapHandle 5112 -prefMapSize 272997 -jsInitHandle 5108 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5040 -initialChannelId {469132c7-a5b5-4770-943e-a0d09f0db373} -parentPid 7296 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7296" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 8 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1028 | C:\WINDOWS\System32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://git.activated.win/massgrave/Microsoft-Activation-Scripts/raw/commit/67abcd0c8925832fcf4365b9cf3706ab6fbf8571/MAS/All-In-One-Version-KL/MAS_AIO.cmd" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
157 524
Read events
157 487
Write events
30
Delete events
7
Modification events
| (PID) Process: | (1044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1044) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6C7542838F982F00 | |||
| (PID) Process: | (1044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328590 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {501FE85C-BCFB-4B46-B595-52BF493D7ADB} | |||
| (PID) Process: | (1044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (1044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (1044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328590 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D172434E-FE9C-42EC-83A4-1F7A67ED5D72} | |||
| (PID) Process: | (1044) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 75BF8C838F982F00 | |||
Executable files
0
Suspicious files
652
Text files
267
Unknown types
500
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1754d6.TMP | — | |
MD5:— | SHA256:— | |||
| 1044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1754e6.TMP | — | |
MD5:— | SHA256:— | |||
| 1044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1754e6.TMP | — | |
MD5:— | SHA256:— | |||
| 1044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1754b7.TMP | — | |
MD5:— | SHA256:— | |||
| 1044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175505.TMP | — | |
MD5:— | SHA256:— | |||
| 1044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF175505.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
162
DNS requests
257
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1508 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:oZCKt8fx7Lf0pg5Z5hTCTRupPjBCaTOlF2gLg_4n7bU&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8100 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8100 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7716 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752750056&P2=404&P3=2&P4=V%2bCGPa4i1x7rjwIi9p1Q%2fVHFomgvl62iH3CkC89%2b8BQYQAnlauQWCqLOM7JODAIiJh4mvaN5p%2f%2boCEc0He3ECw%3d%3d | unknown | — | — | whitelisted |
7716 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752750056&P2=404&P3=2&P4=V%2bCGPa4i1x7rjwIi9p1Q%2fVHFomgvl62iH3CkC89%2b8BQYQAnlauQWCqLOM7JODAIiJh4mvaN5p%2f%2boCEc0He3ECw%3d%3d | unknown | — | — | whitelisted |
7716 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752750056&P2=404&P3=2&P4=V%2bCGPa4i1x7rjwIi9p1Q%2fVHFomgvl62iH3CkC89%2b8BQYQAnlauQWCqLOM7JODAIiJh4mvaN5p%2f%2boCEc0He3ECw%3d%3d | unknown | — | — | whitelisted |
7716 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1752746454&P2=404&P3=2&P4=b%2f6WVyHcxF0kdWAfWtw0rO71AoBRYoubNLPWdvX%2fTpnU3HGmyVg1F4MThZL%2bdOfsnJZbPd9CTxTSsiL8FddtTQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2368 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1508 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1508 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1508 | msedge.exe | 104.21.24.156:443 | git.activated.win | CLOUDFLARENET | — | unknown |
1508 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1508 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
git.activated.win |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |