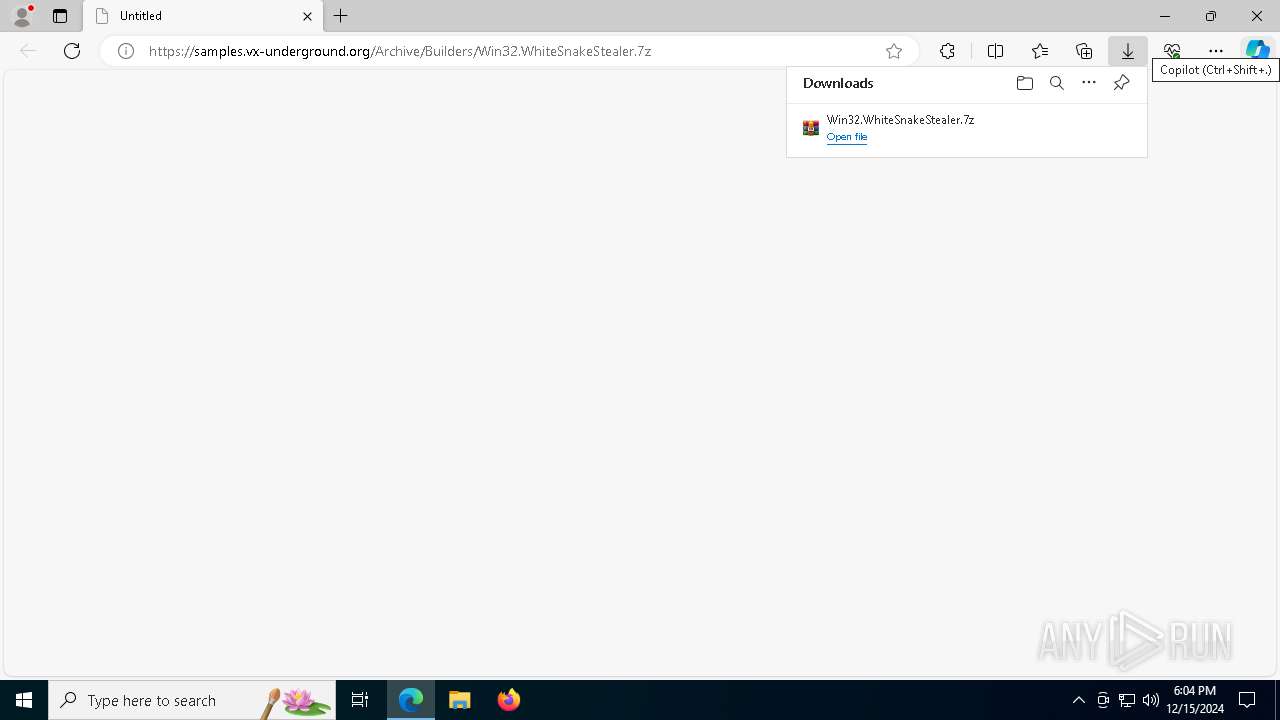
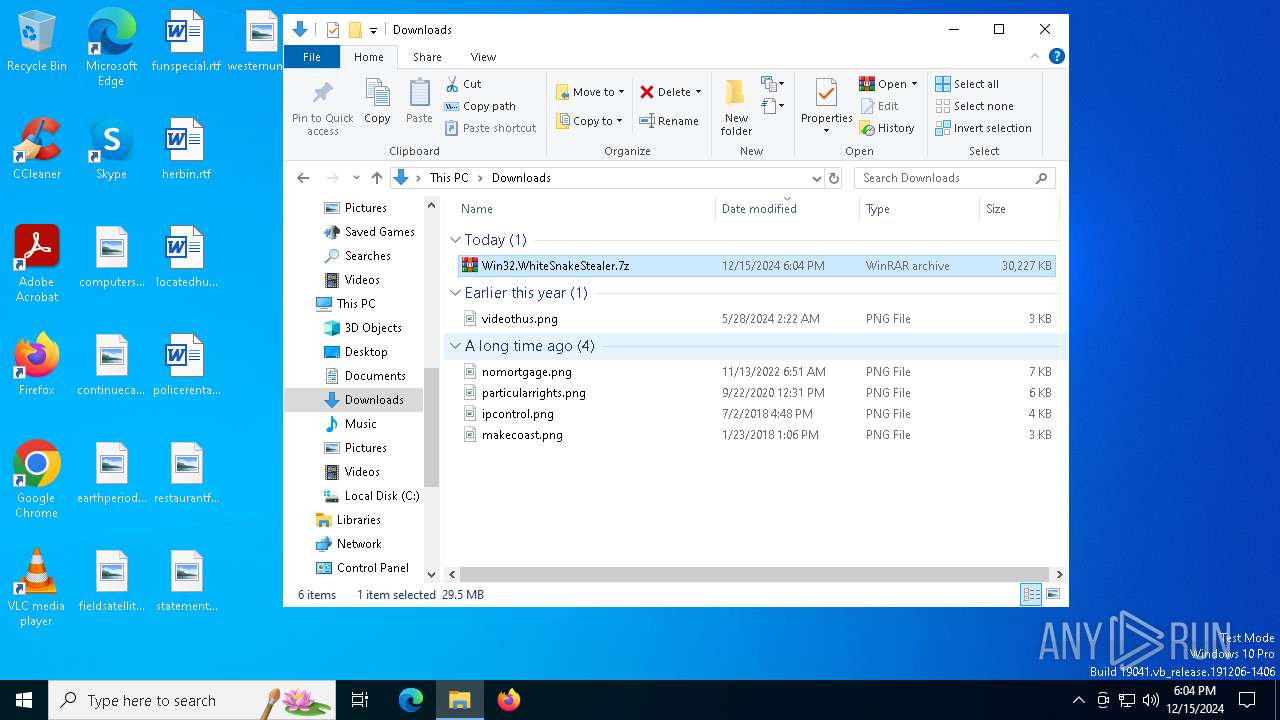
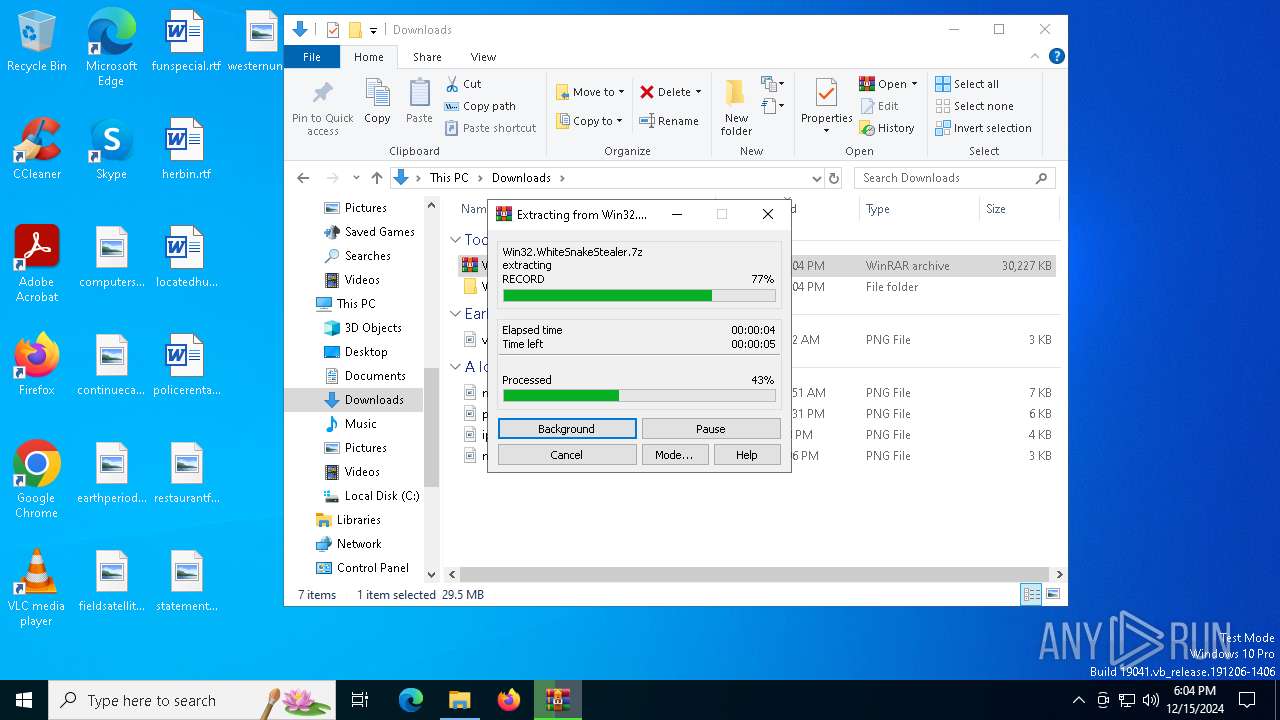
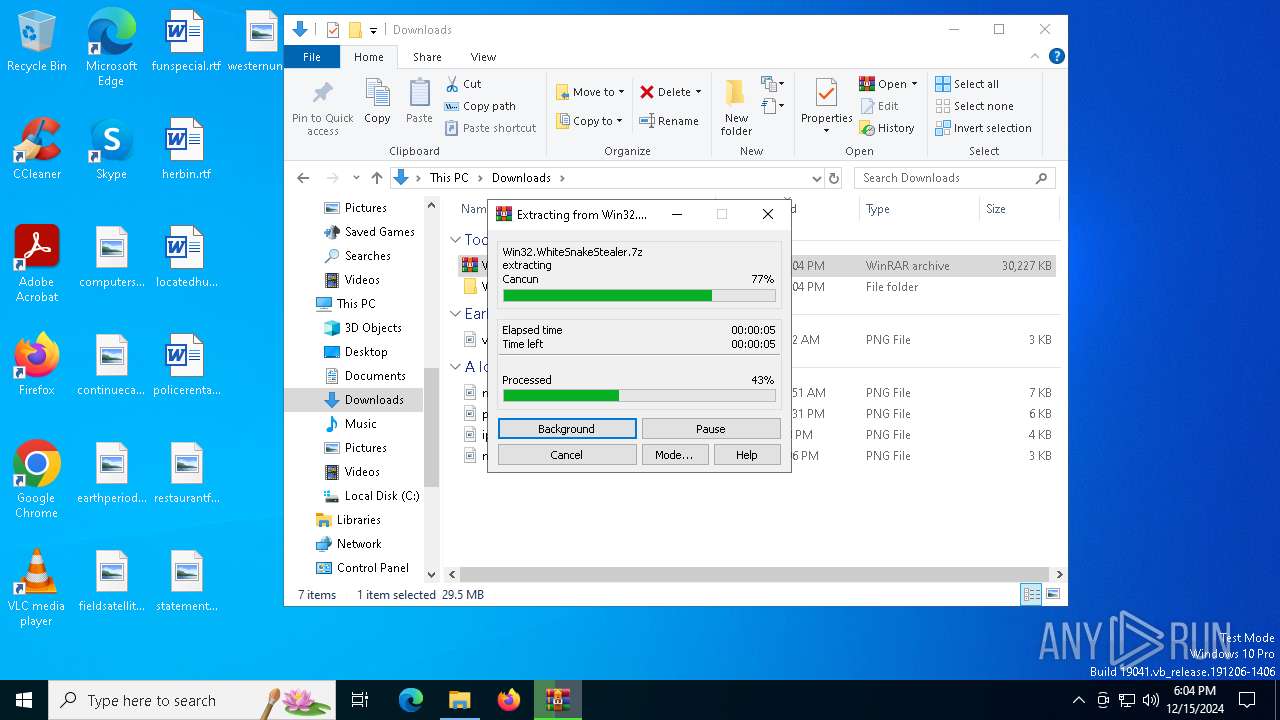
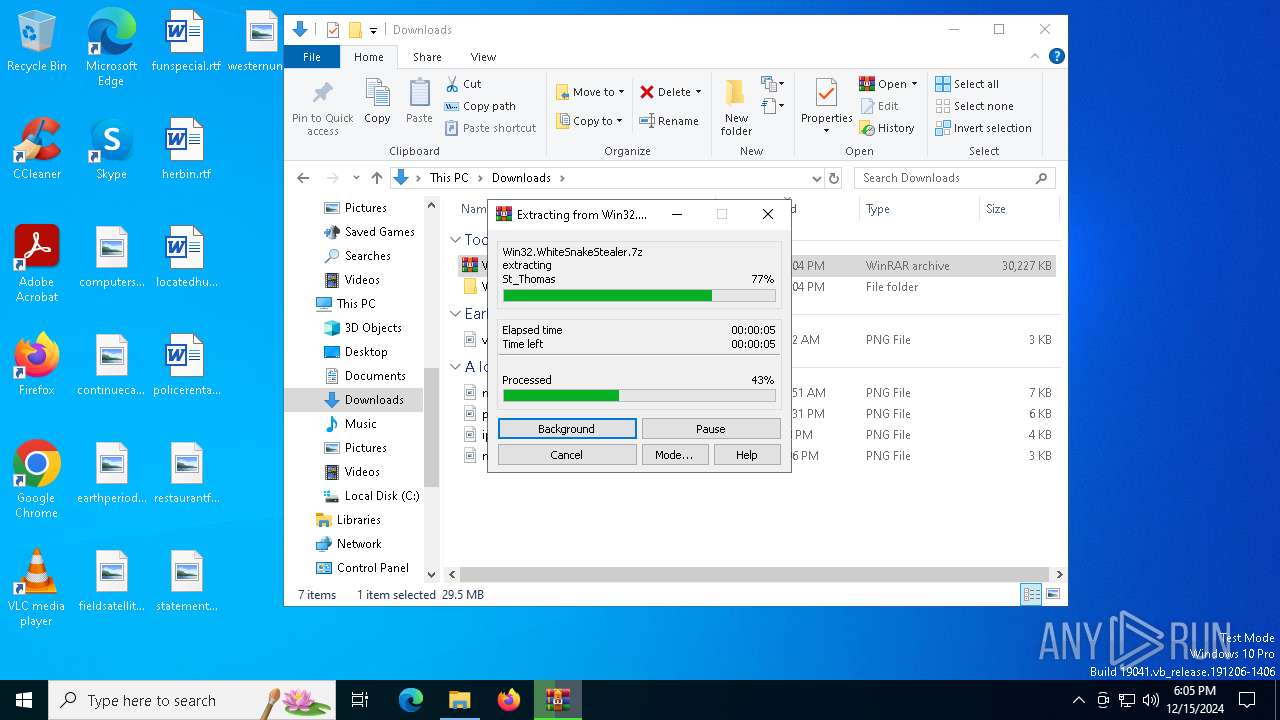
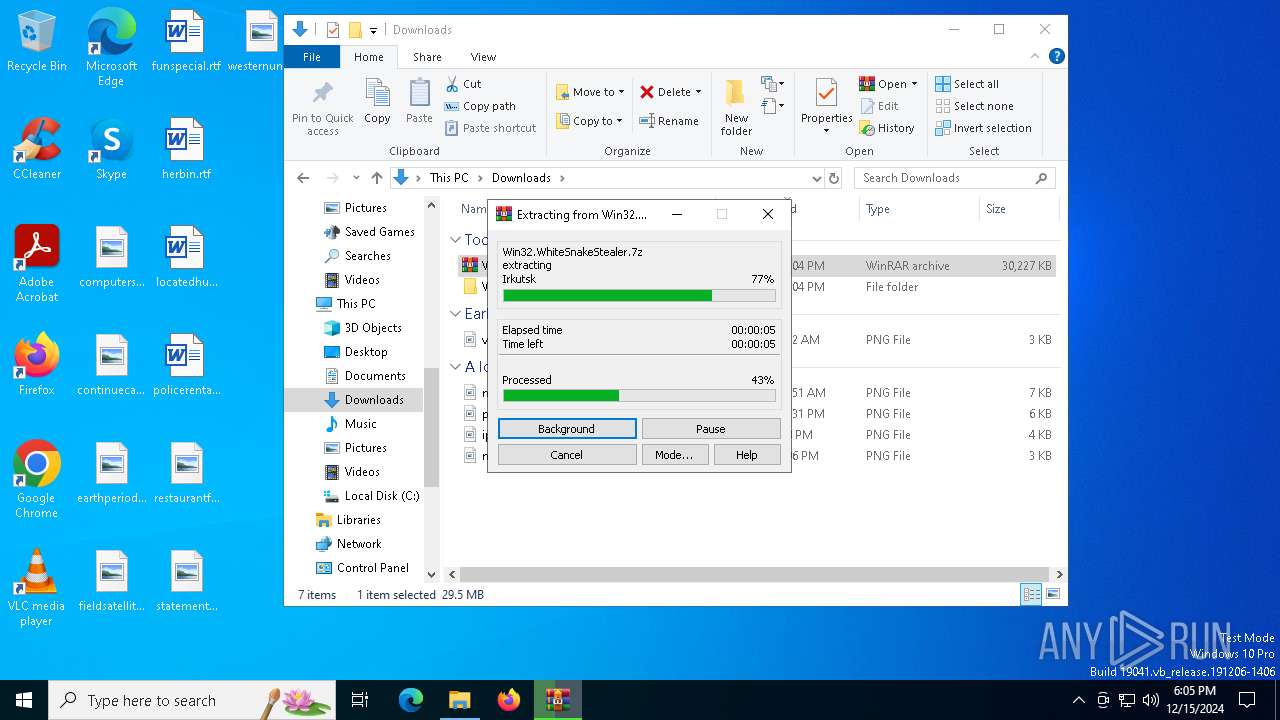
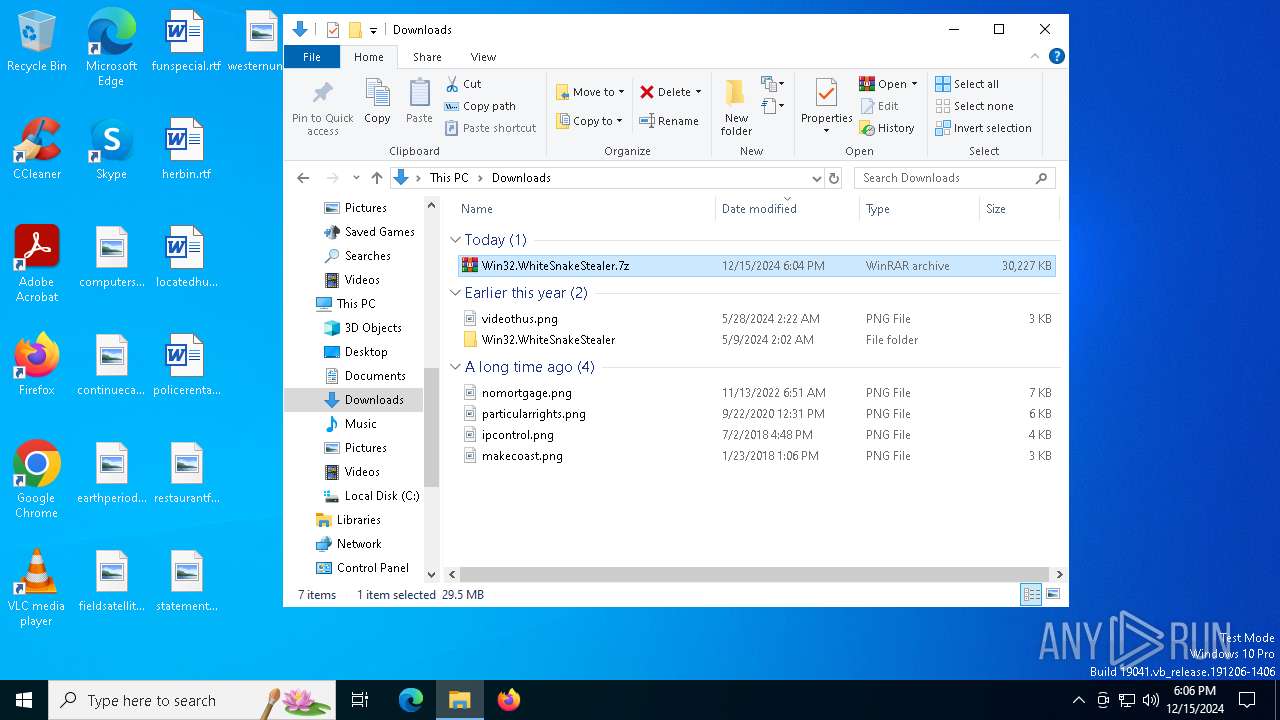
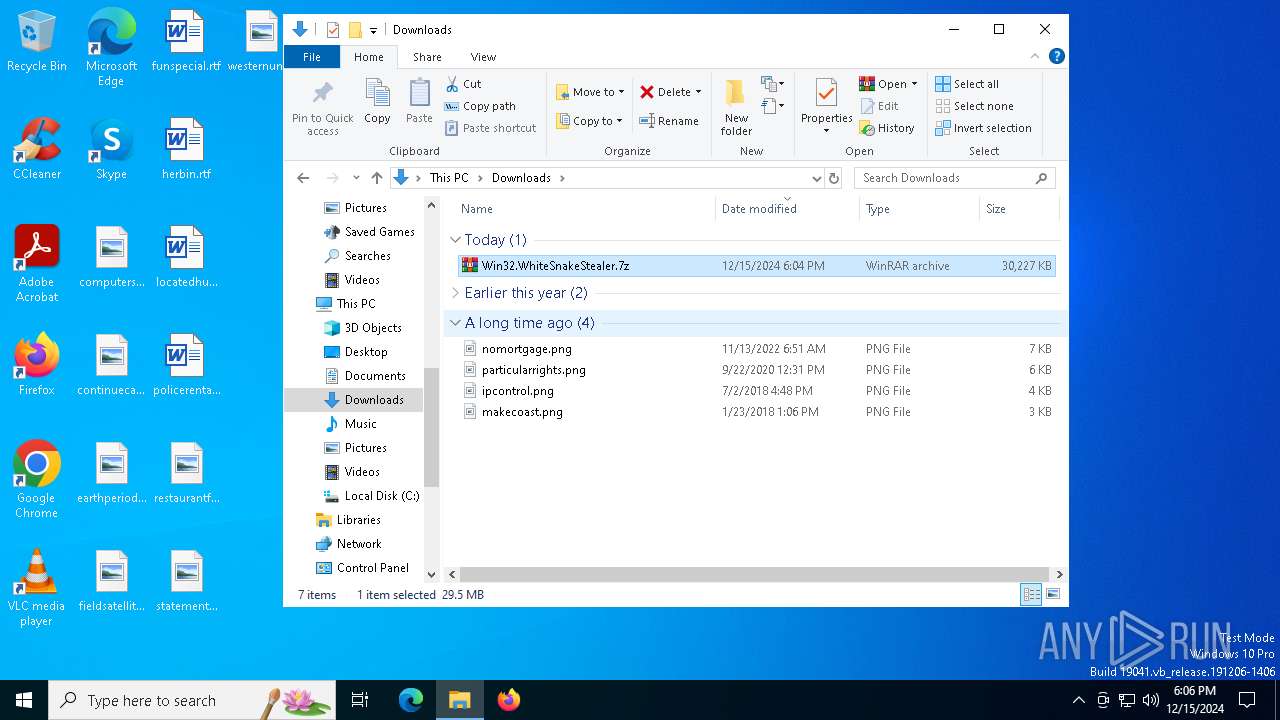
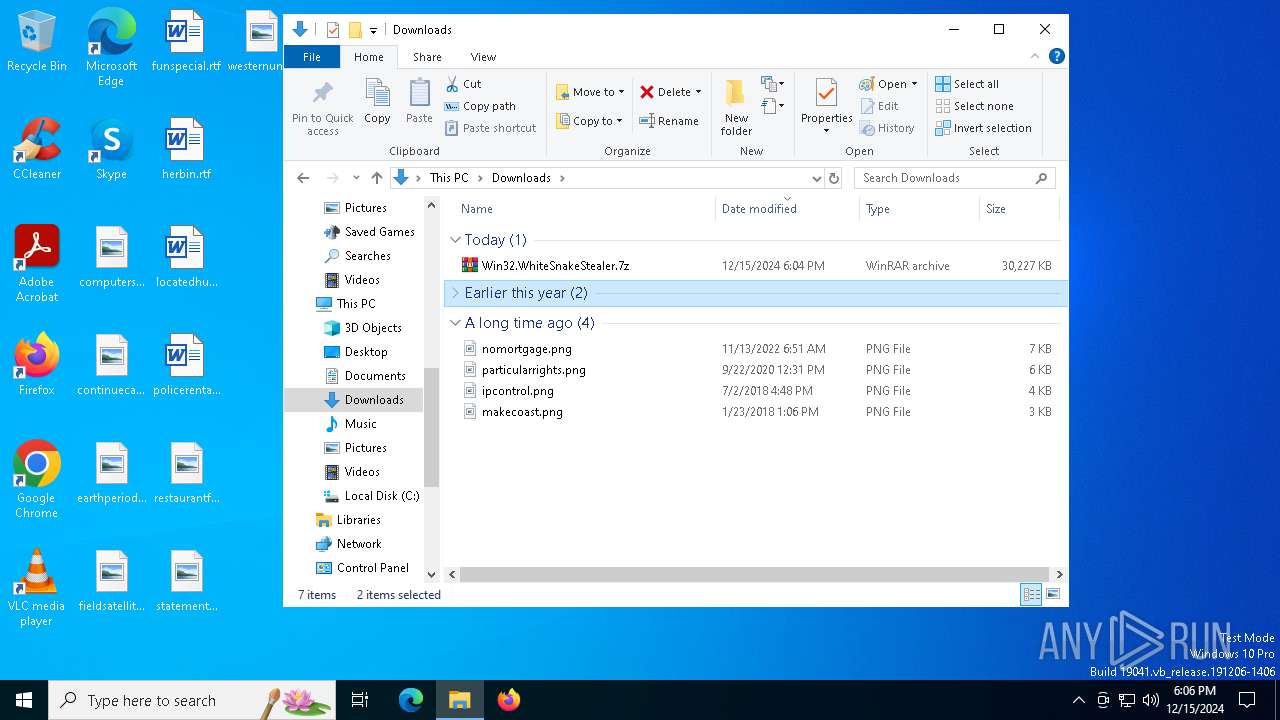
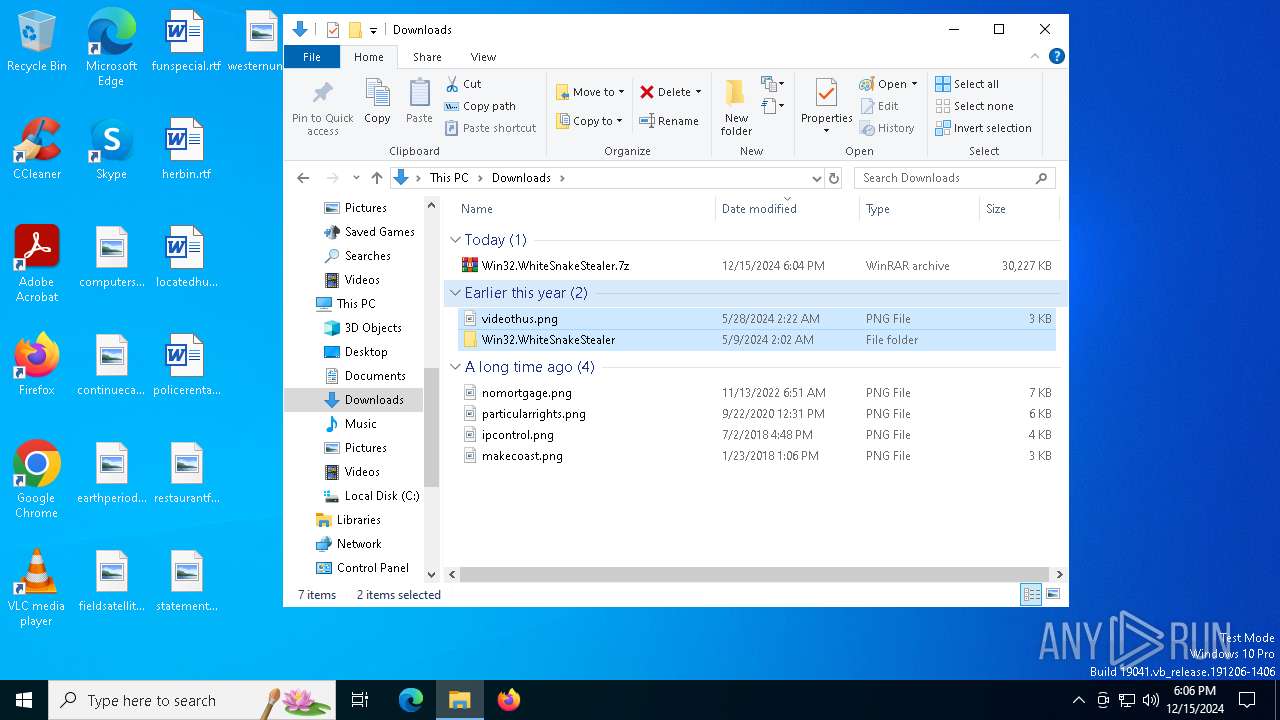
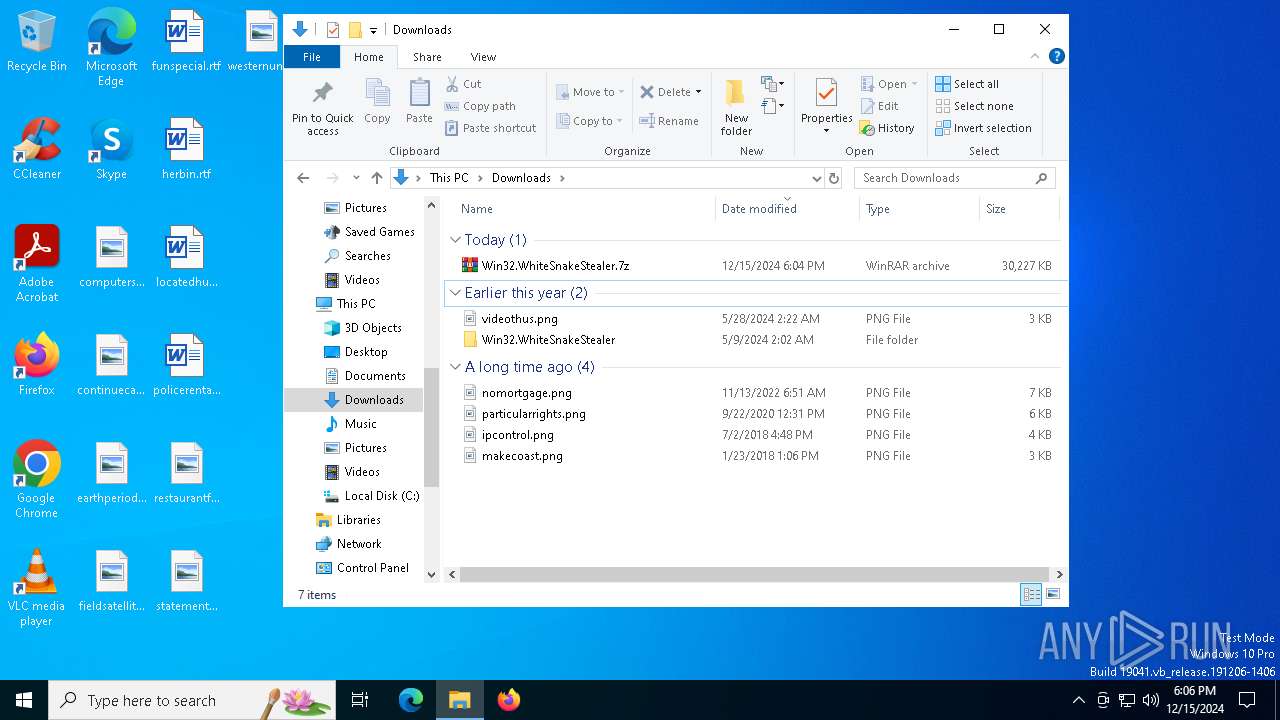
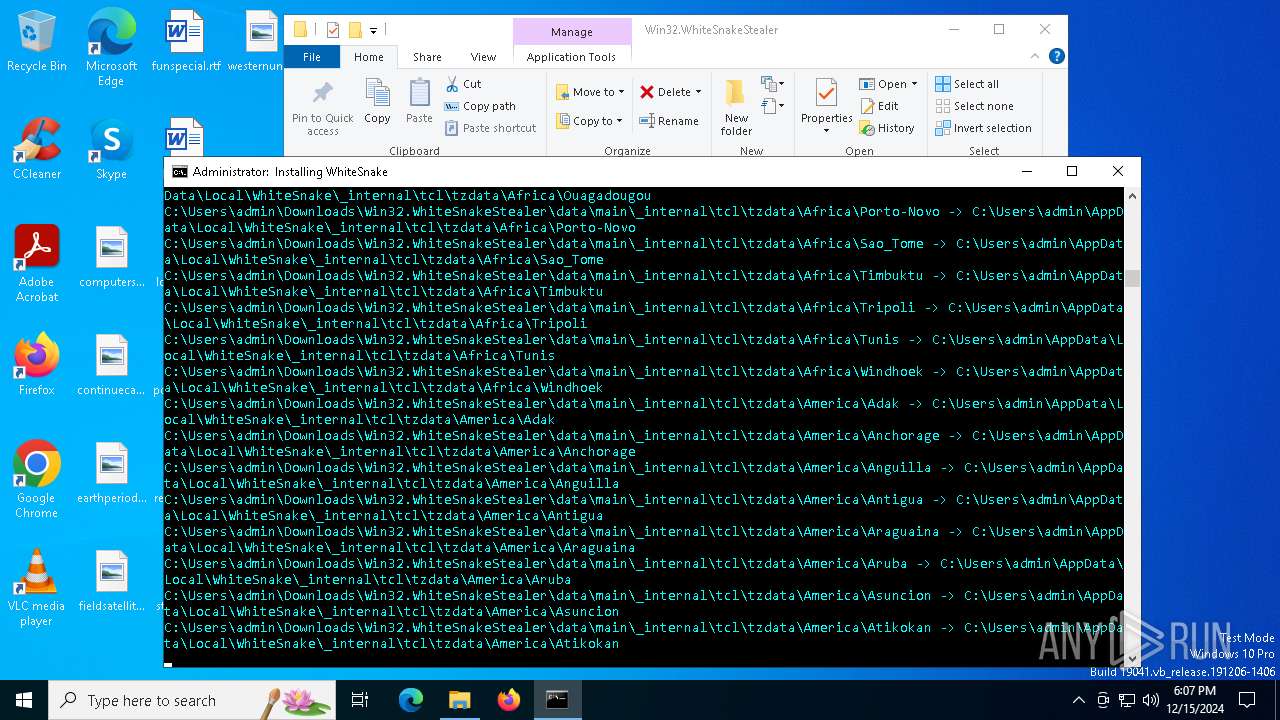
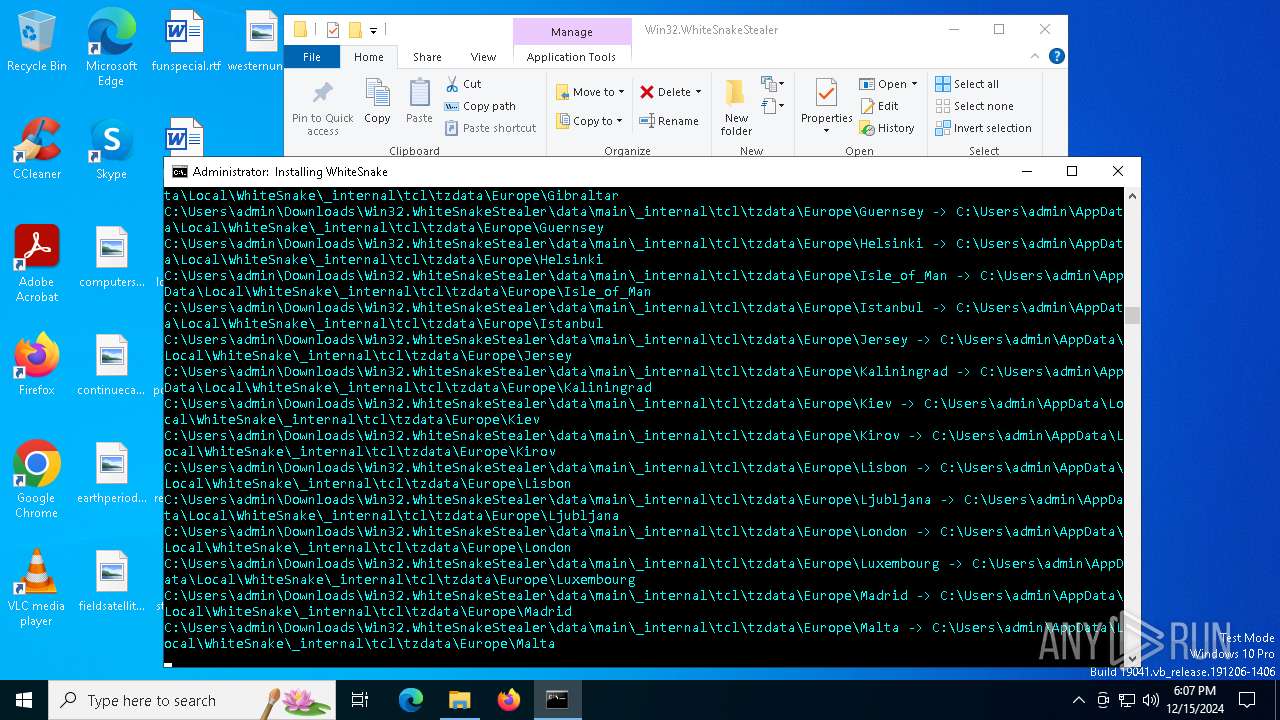
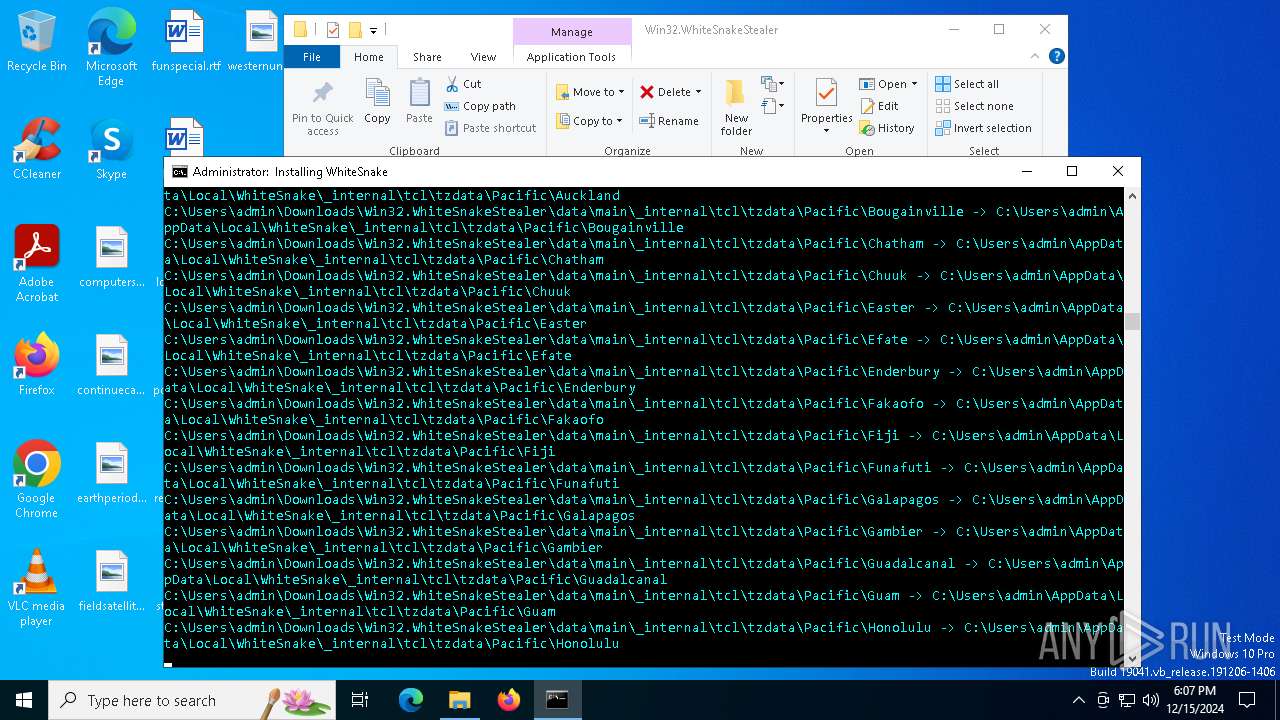
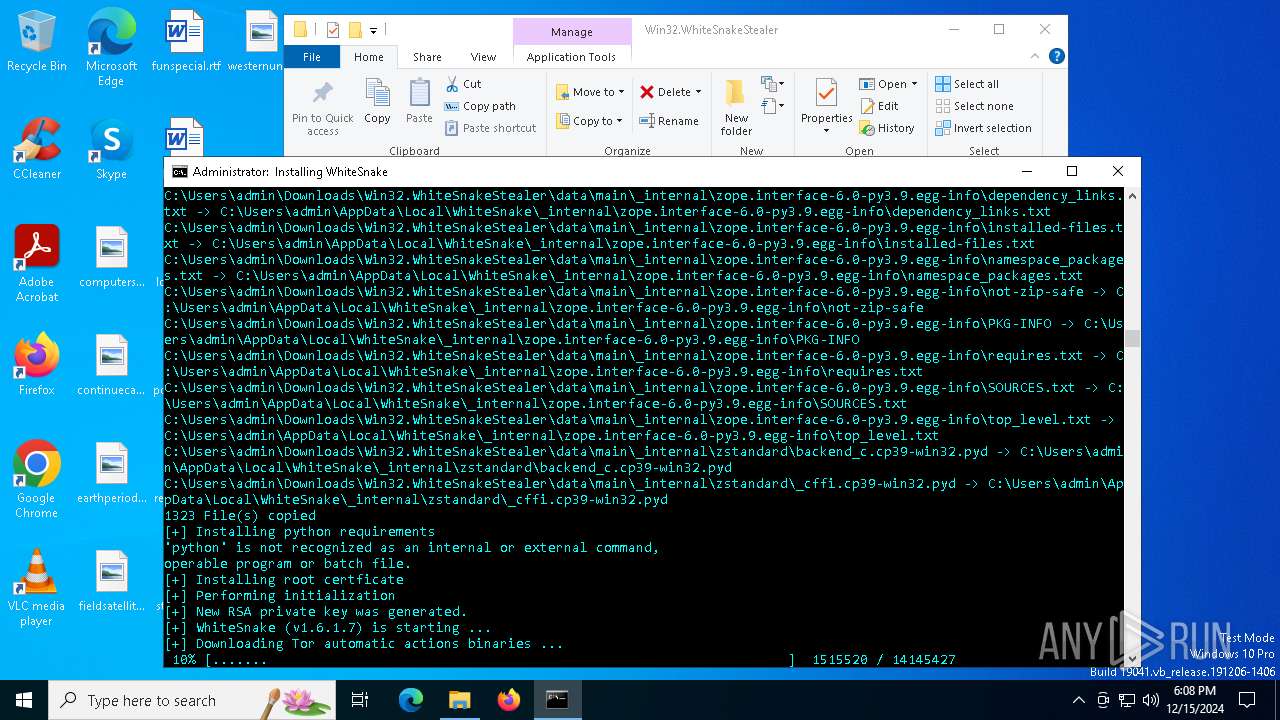
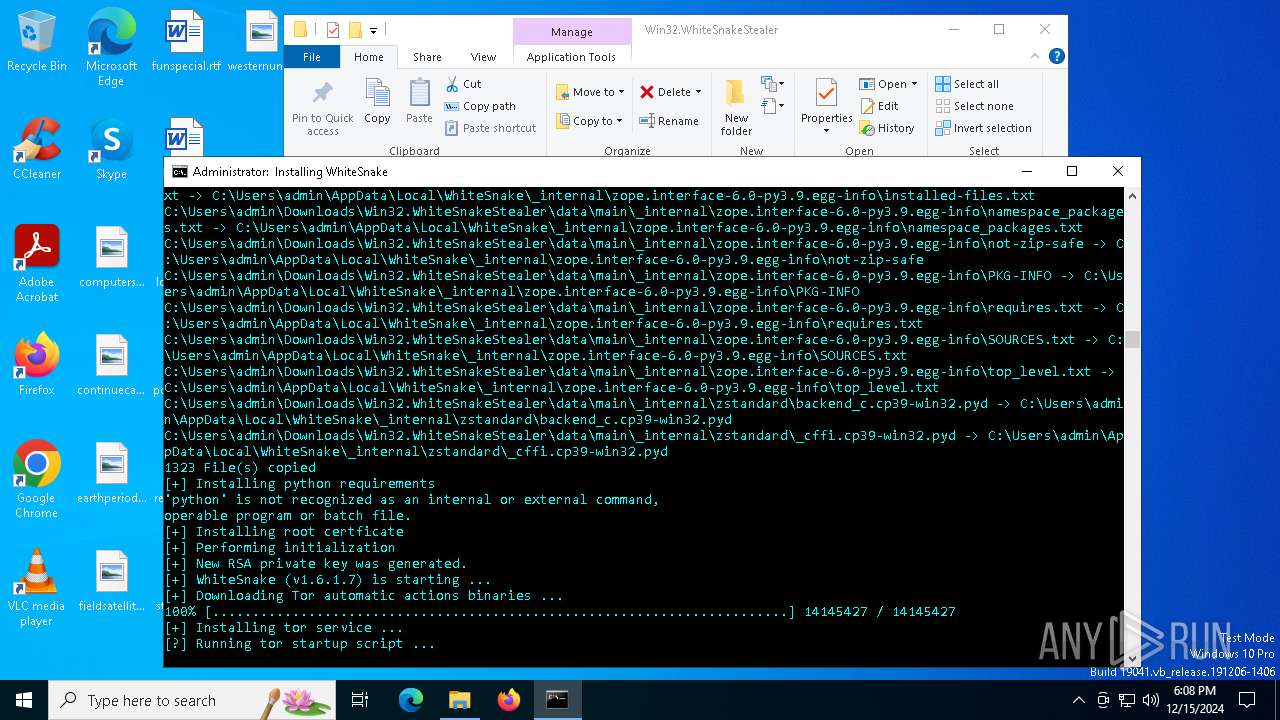
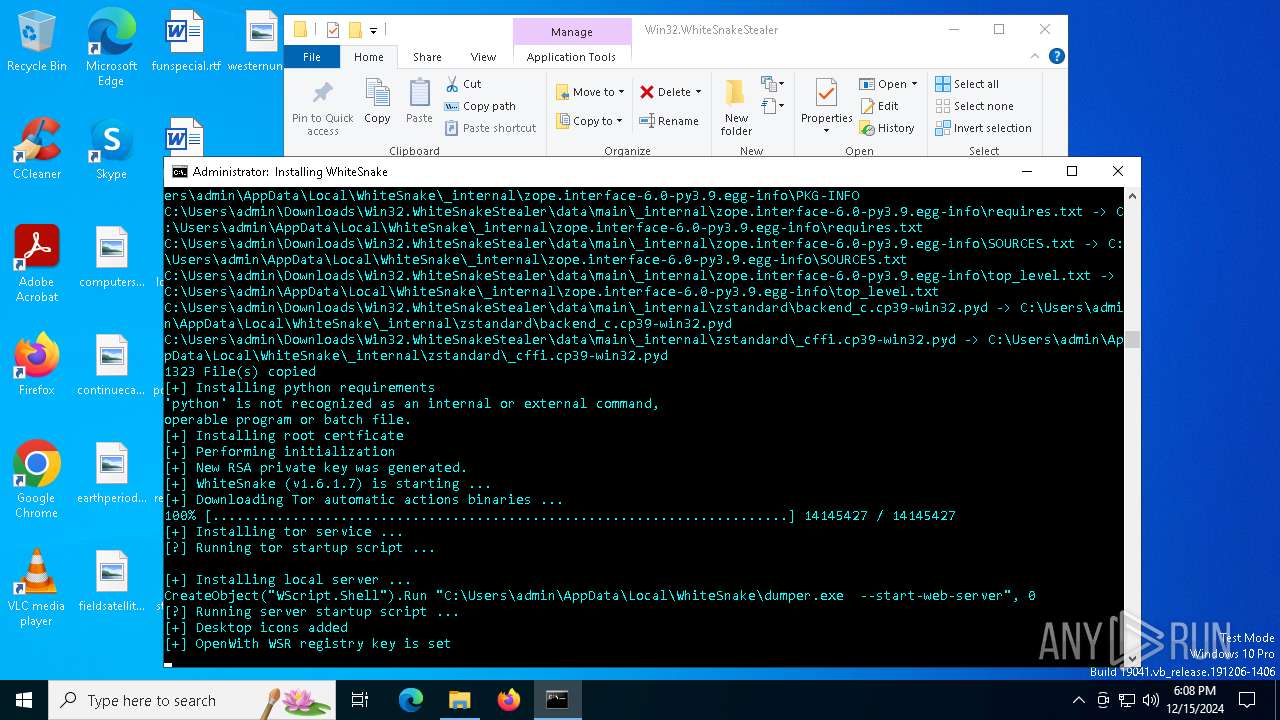
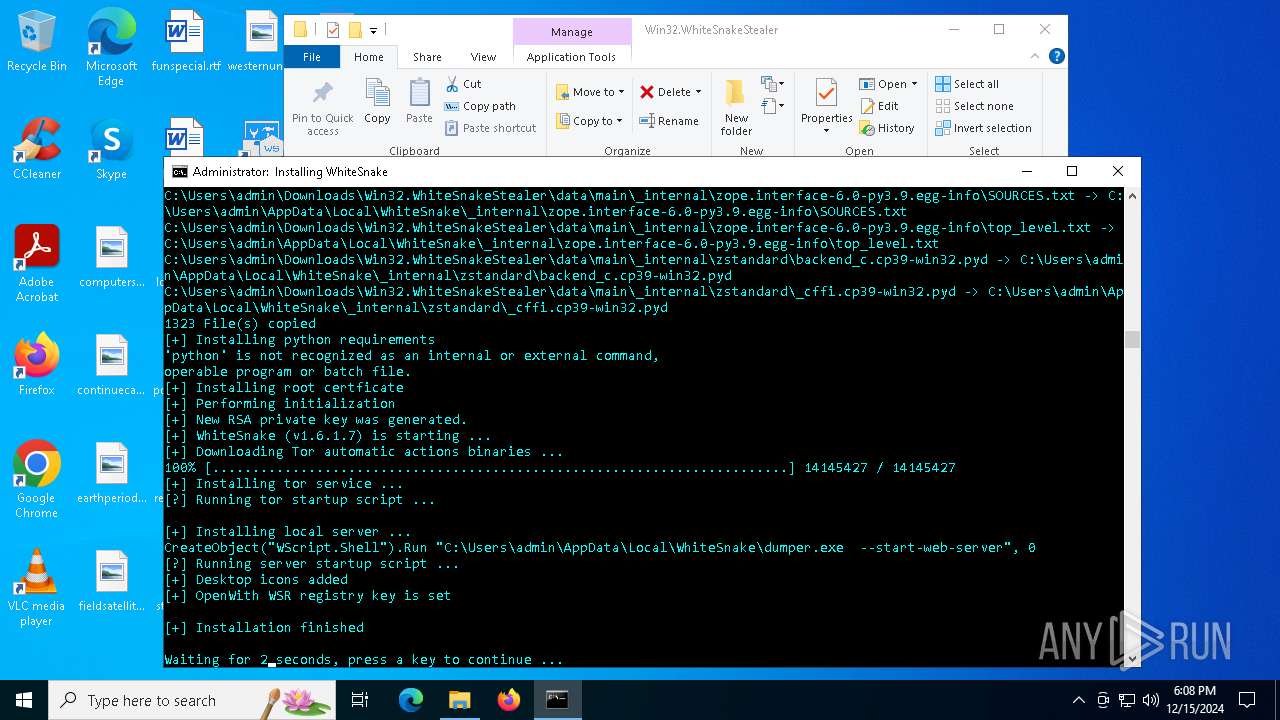
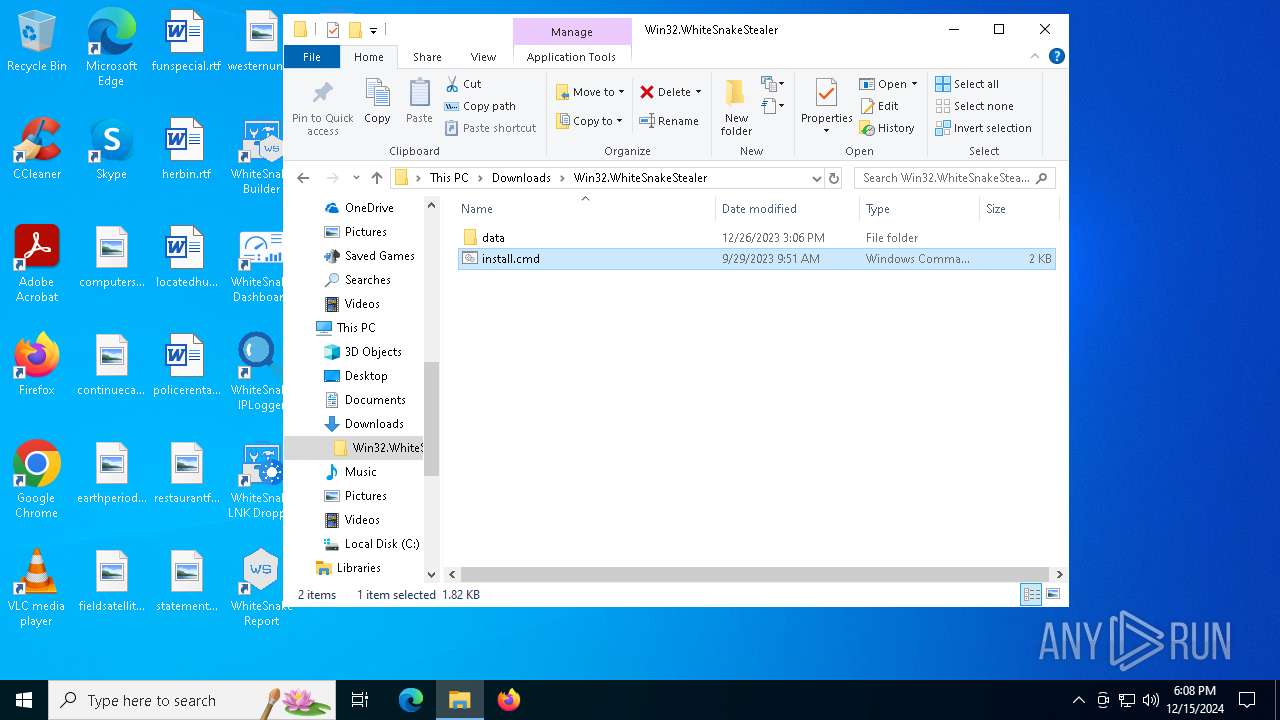
| URL: | https://samples.vx-underground.org/Archive/Builders/Win32.WhiteSnakeStealer.7z |
| Full analysis: | https://app.any.run/tasks/a2f3baec-d309-4adf-8b38-d01a45c0b1c2 |
| Verdict: | Malicious activity |
| Analysis date: | December 15, 2024, 18:04:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3BFAC089F7421CB9C3DF75C04BA1F3E0 |
| SHA1: | 3F4B4D671AED377FECE0FF3AD46A5388CE5CB53E |
| SHA256: | 9C81BF71BBB4783D4320214DA05A65ED72B19AFF2FFA91B5A2EFC02834D862DB |
| SSDEEP: | 3:N8JEIsGNMM8ZPM0GeBE2mMf:2iDaz8ZtGRnMf |
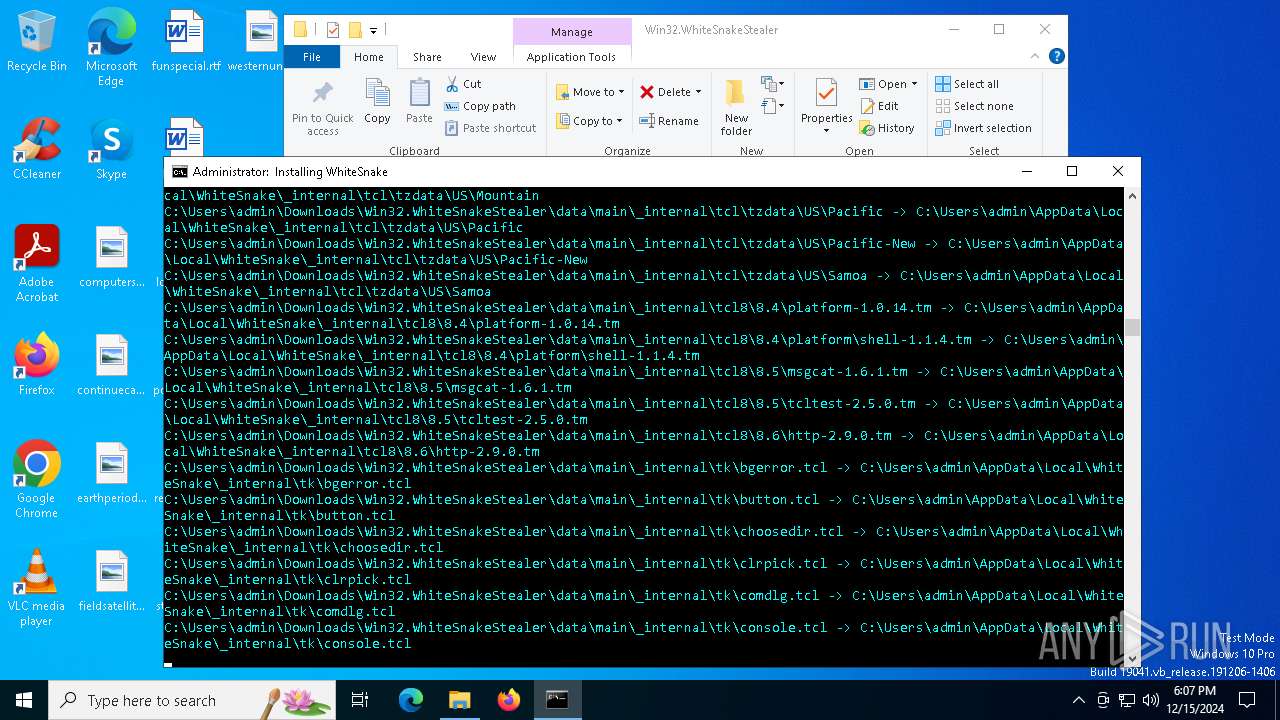
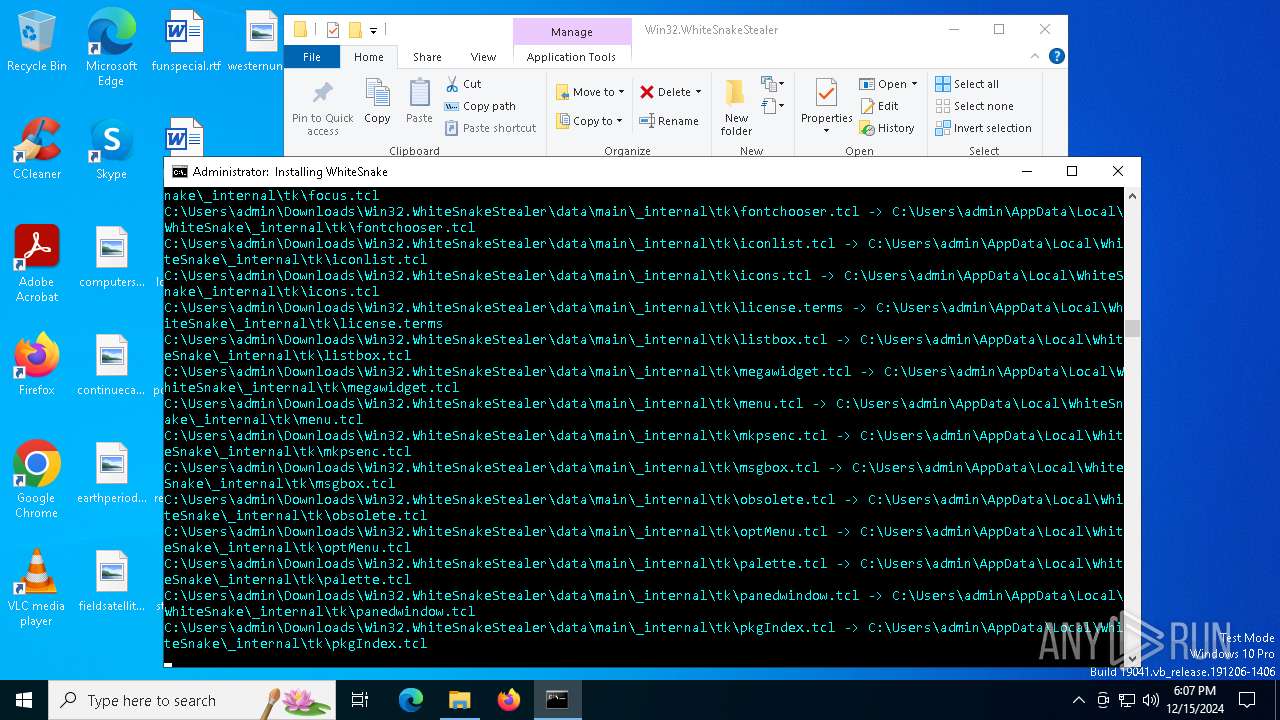
MALICIOUS
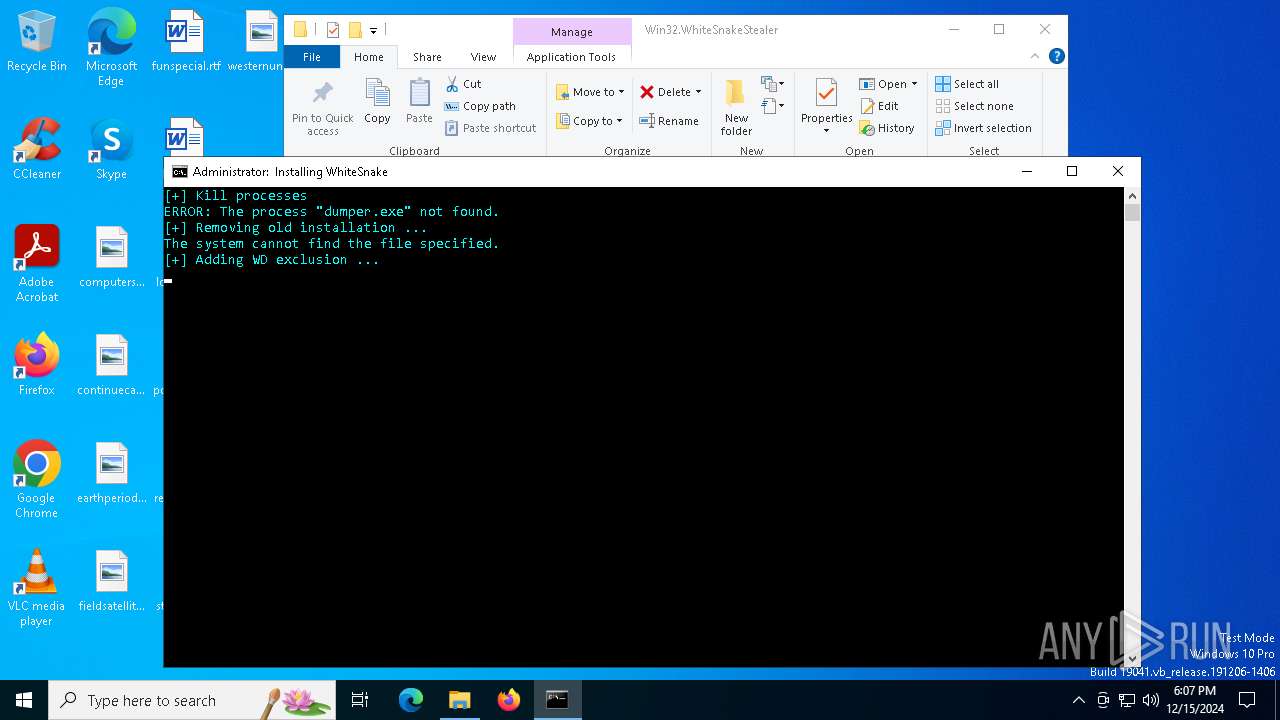
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7052)
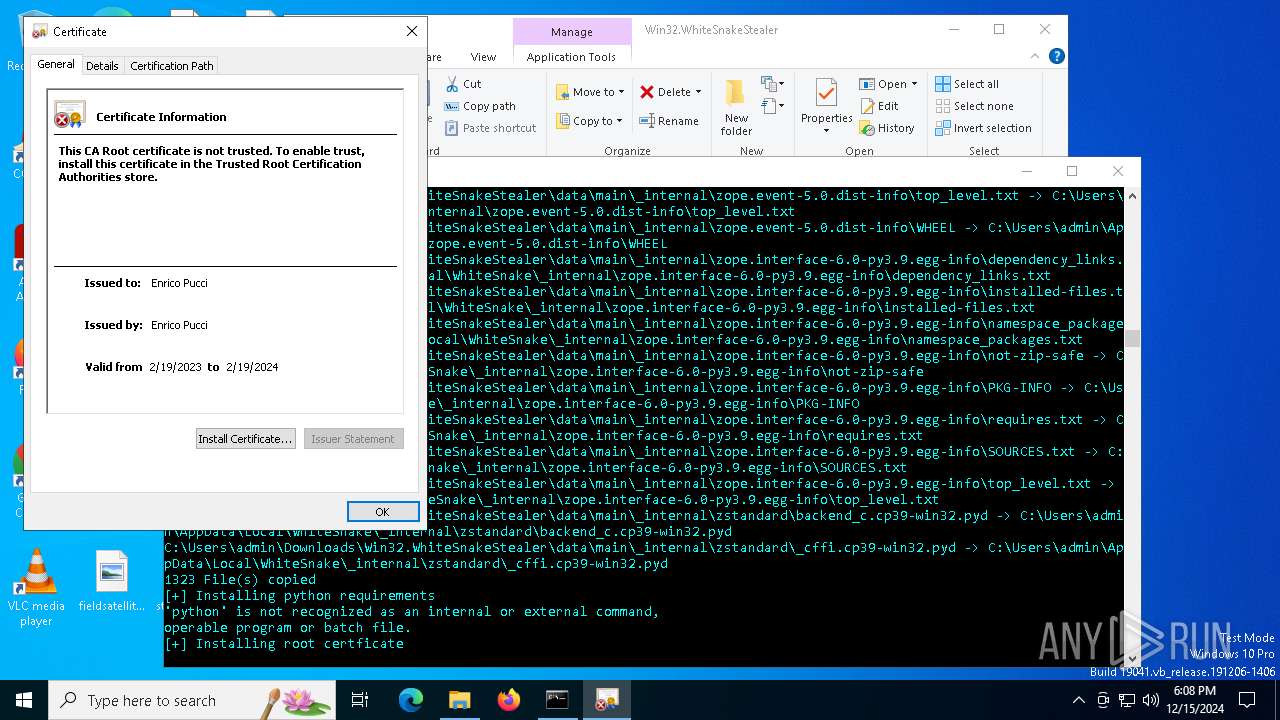
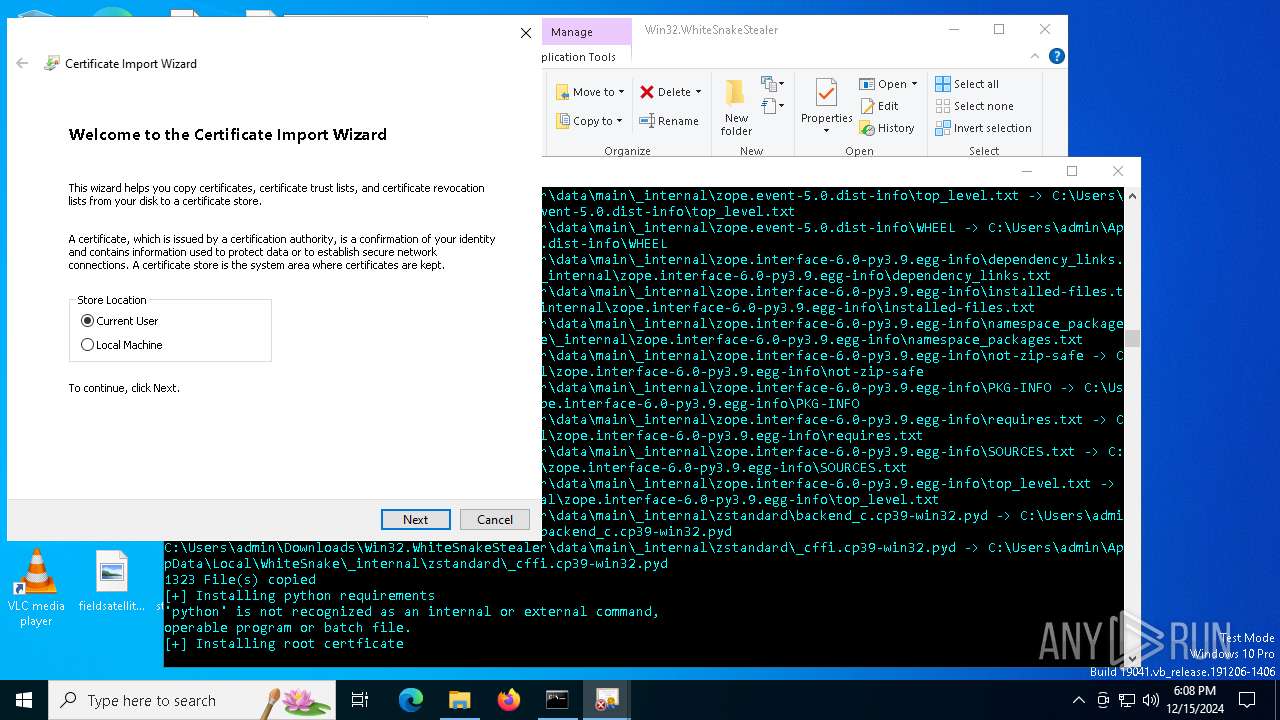
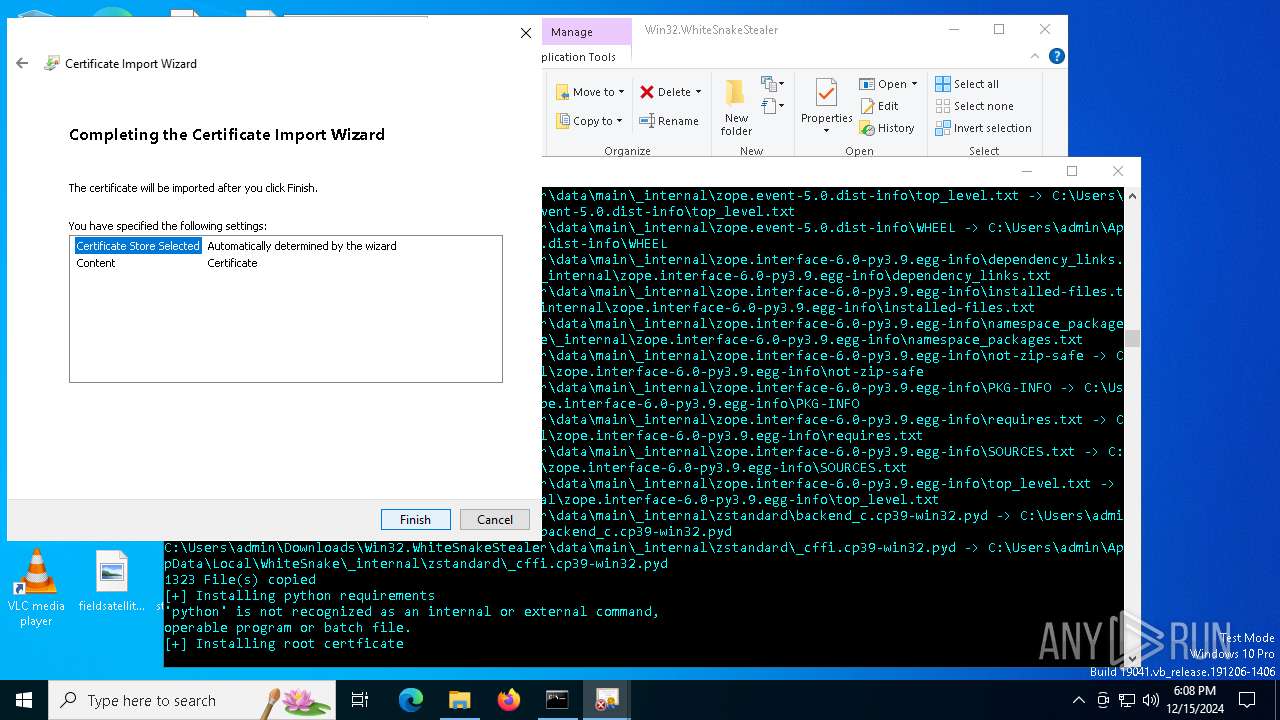
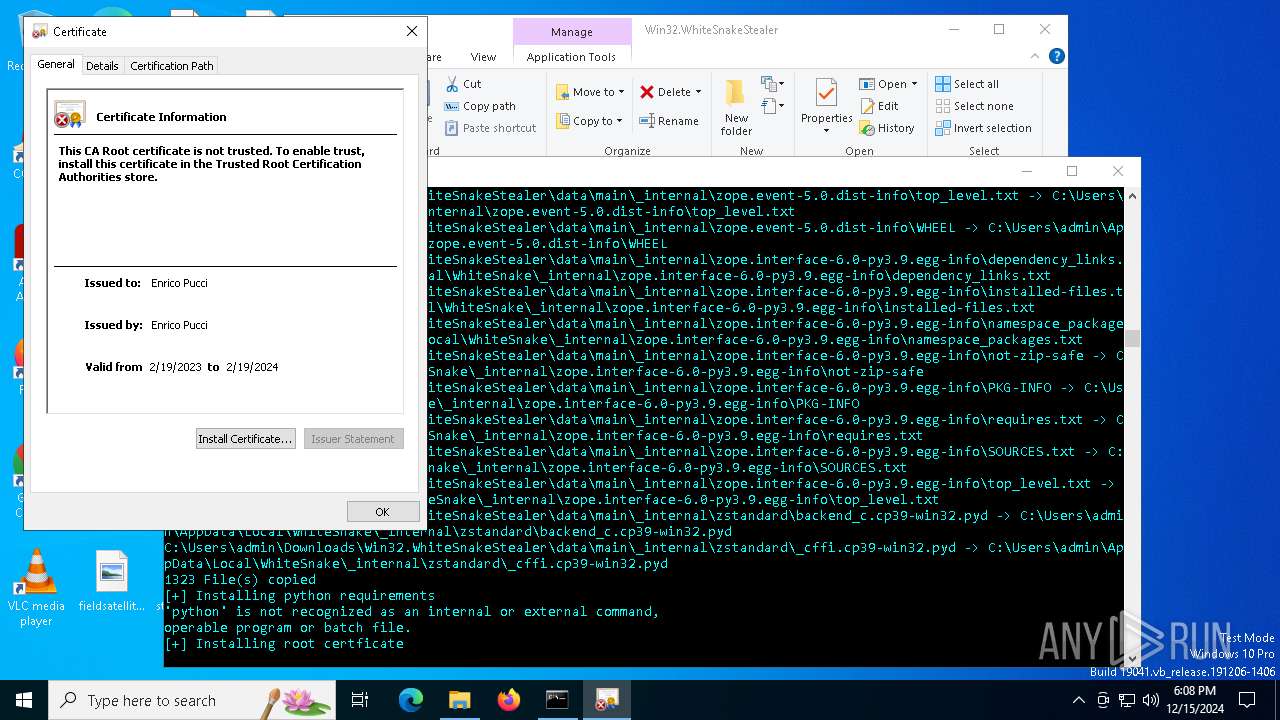
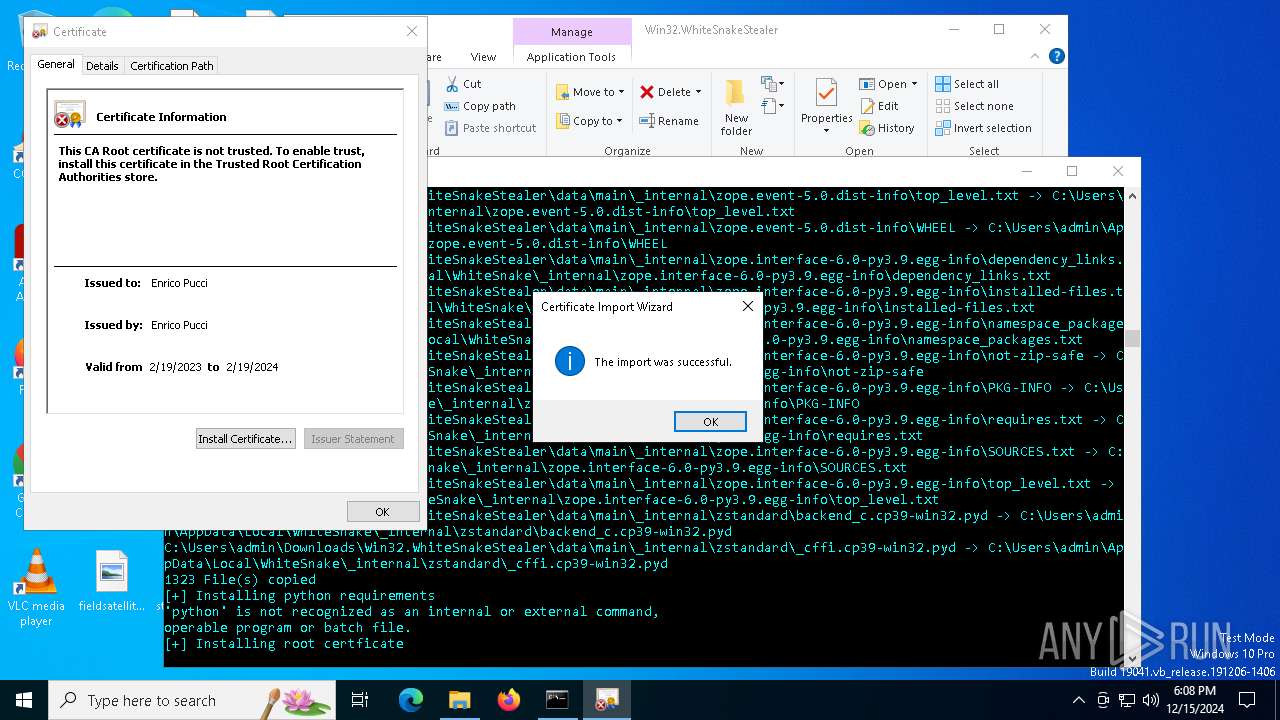
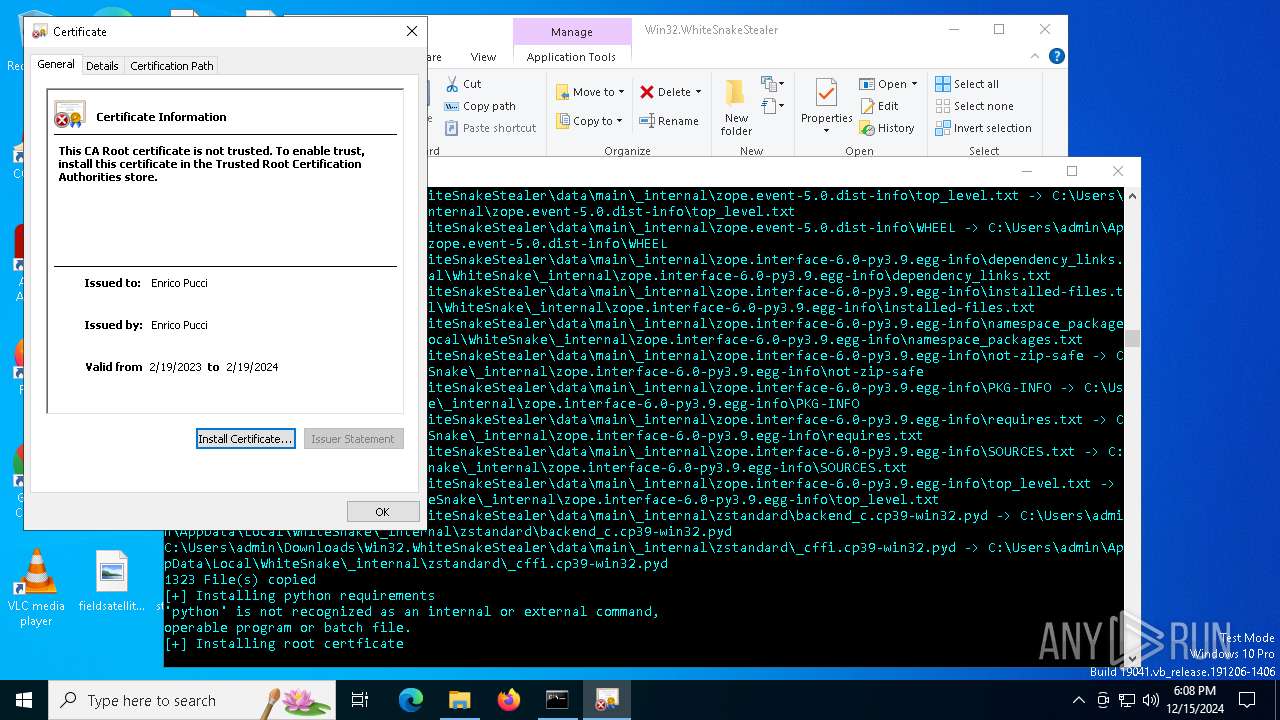
Executing a file with an untrusted certificate
- dumper.exe (PID: 6420)
- dumper.exe (PID: 2904)
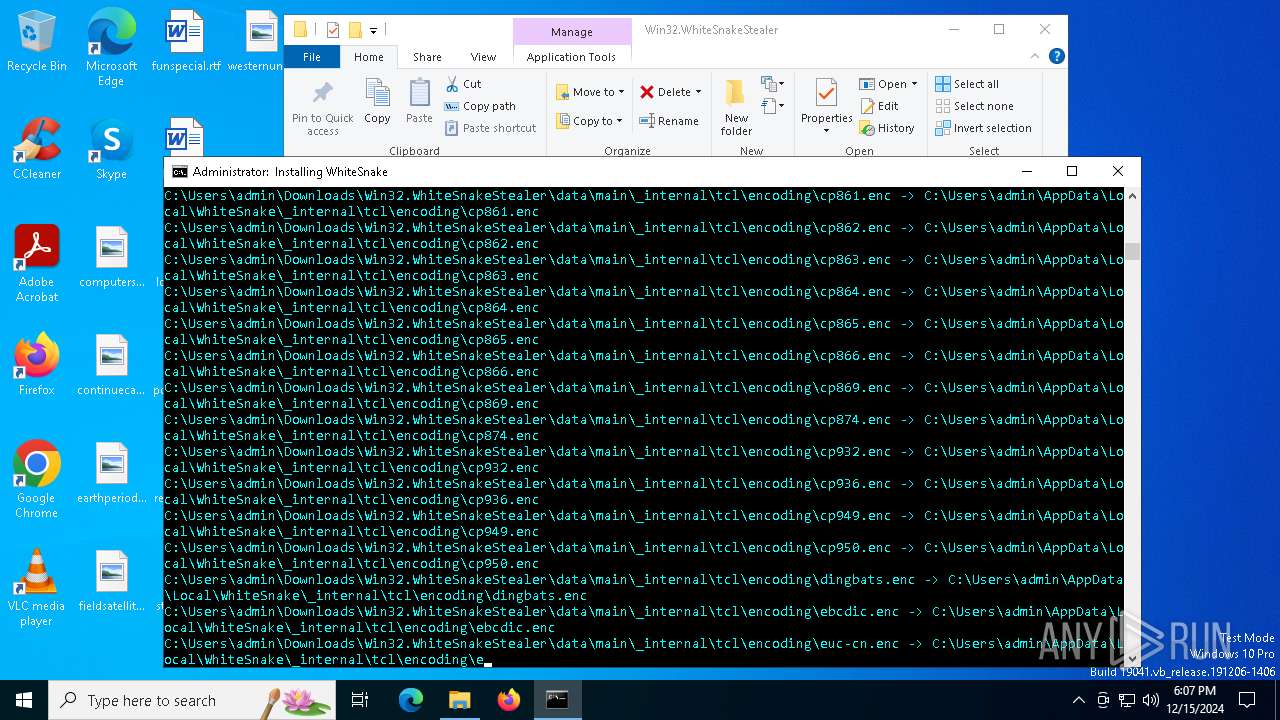
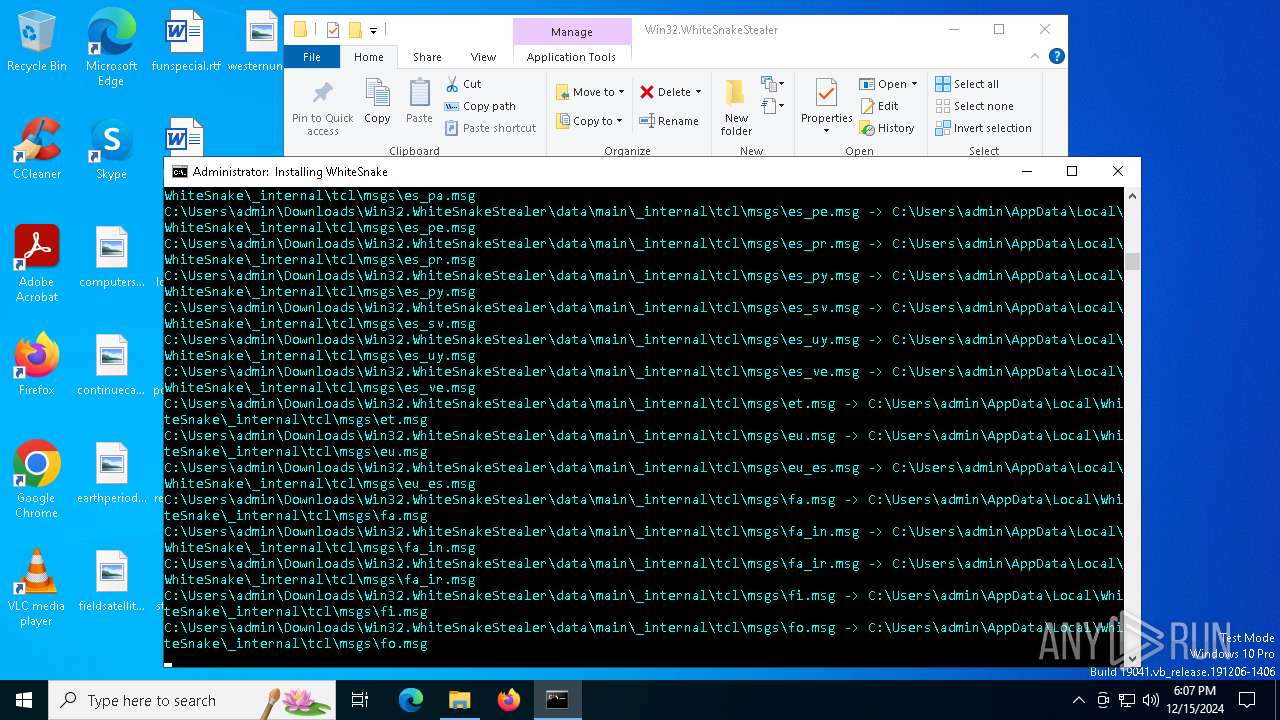
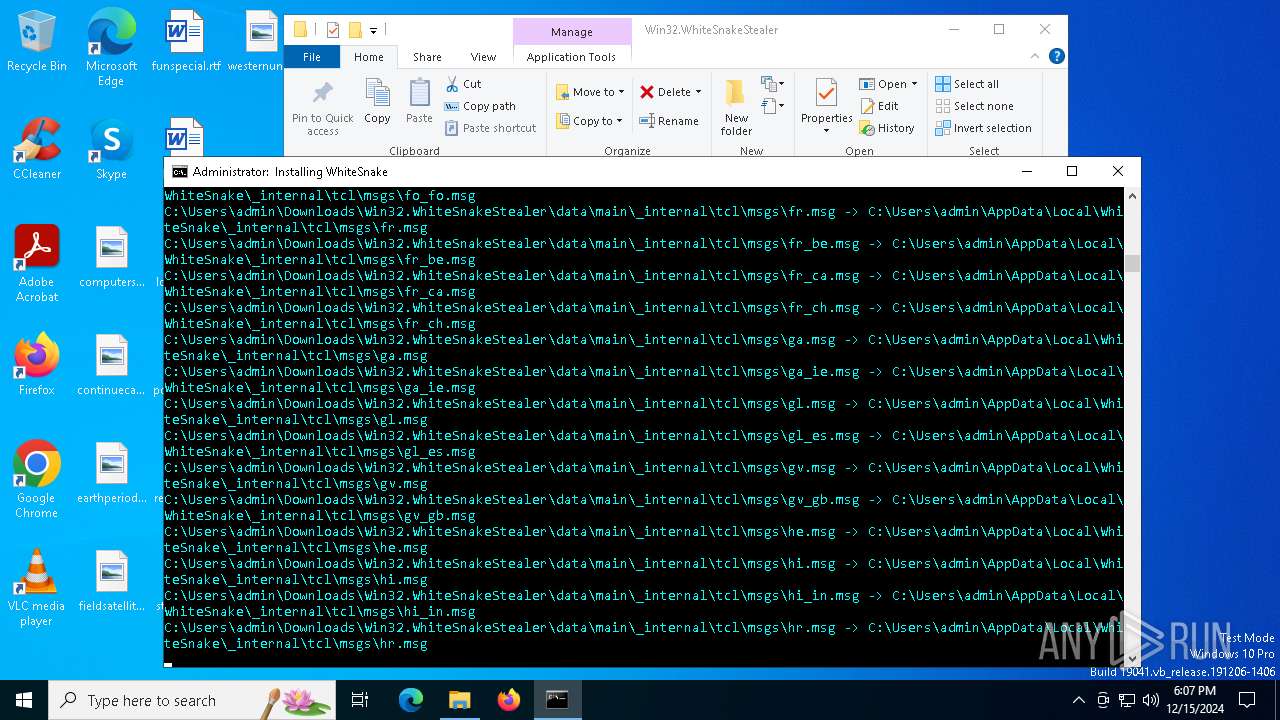
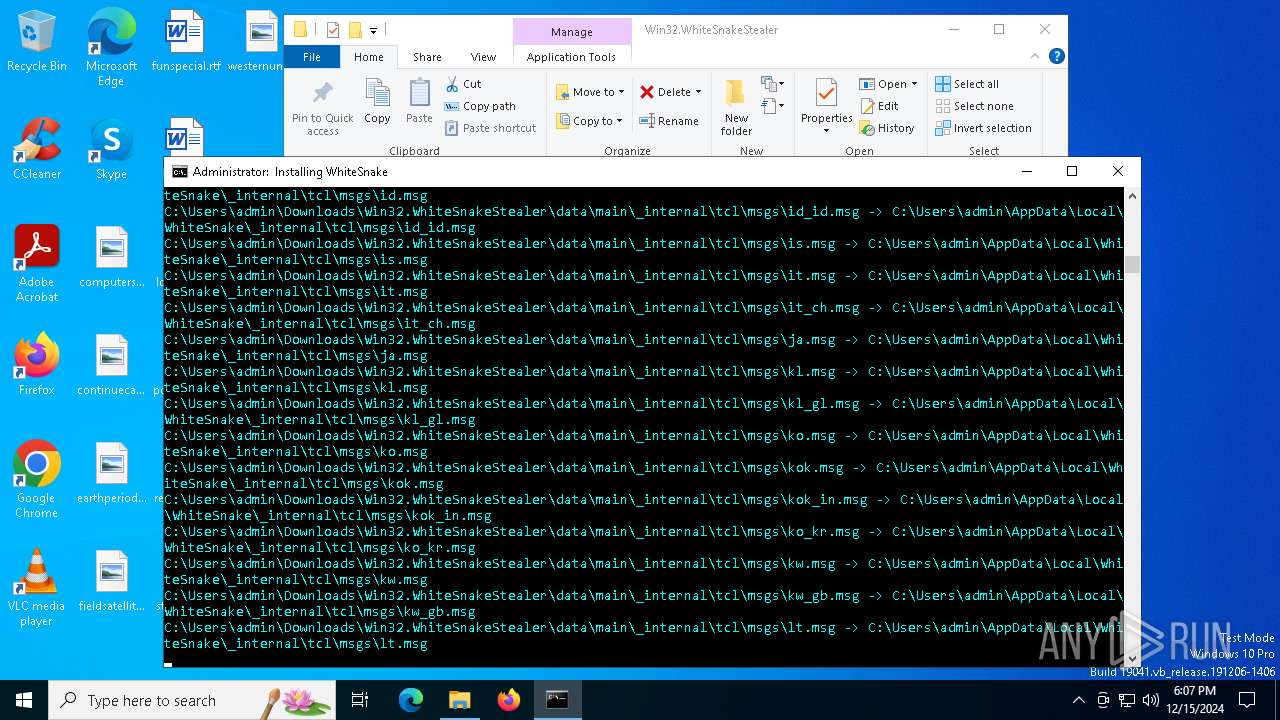
Create files in the Startup directory
- dumper.exe (PID: 6420)
SUSPICIOUS
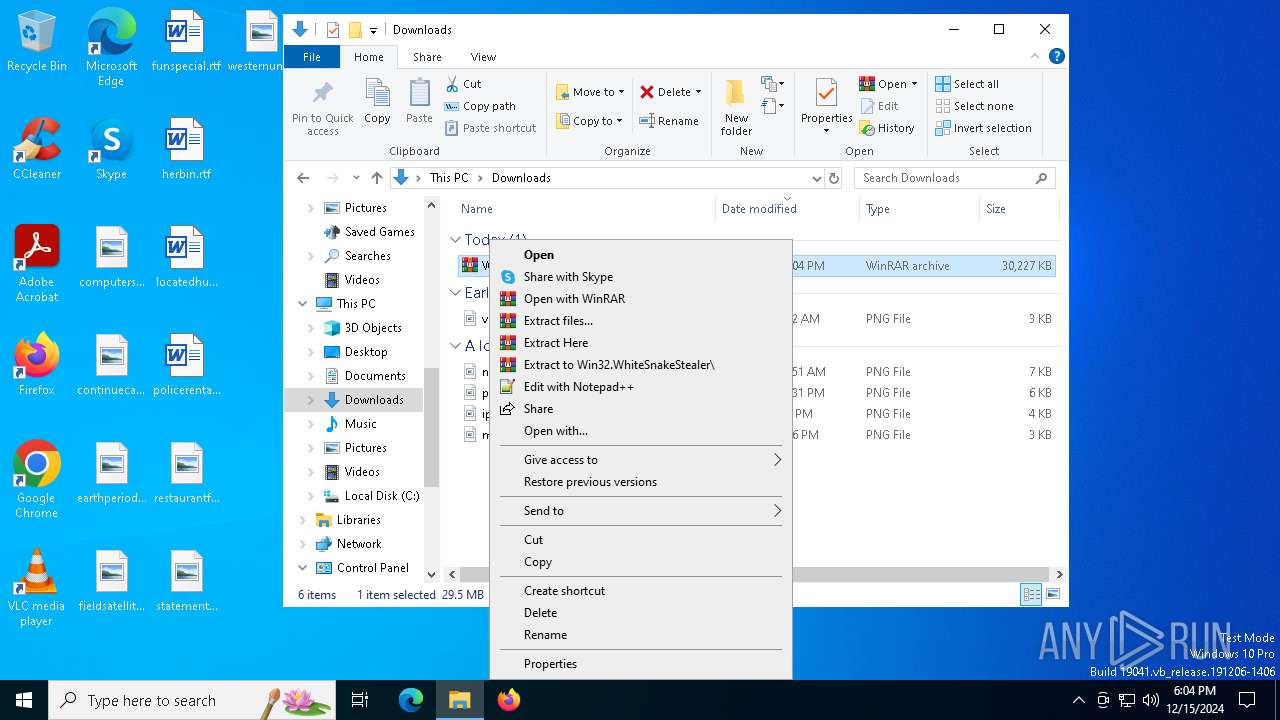
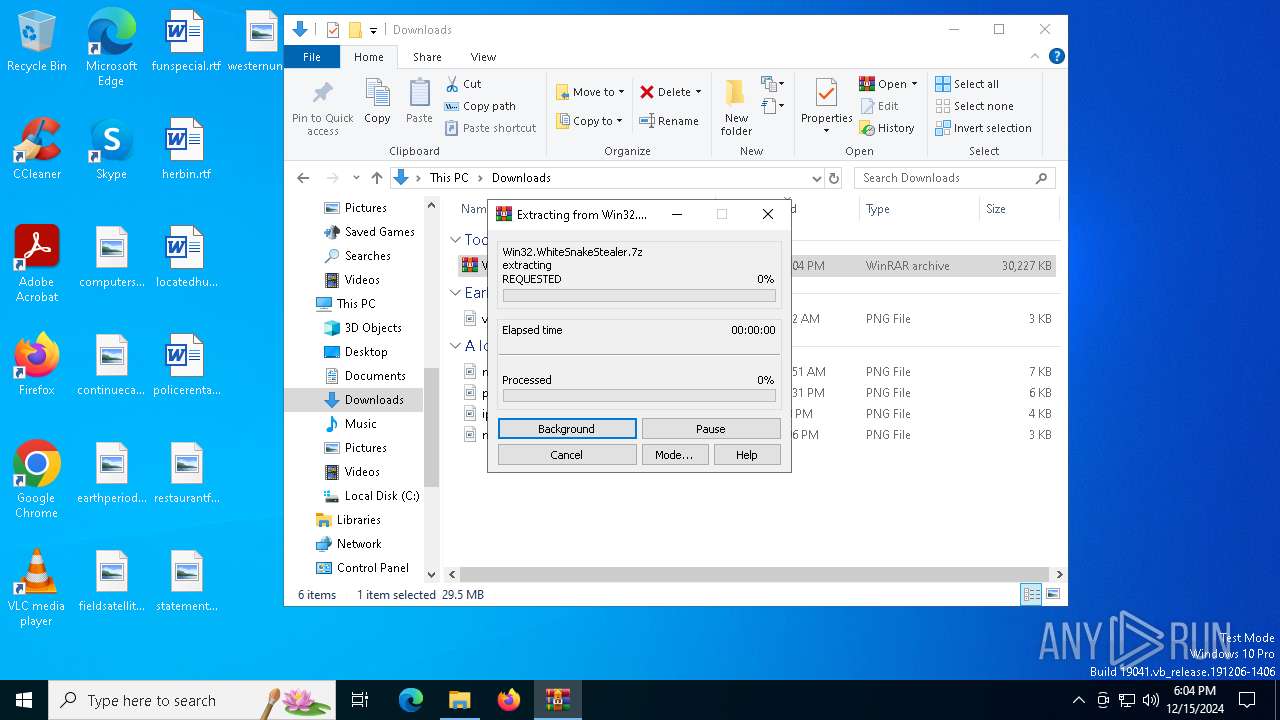
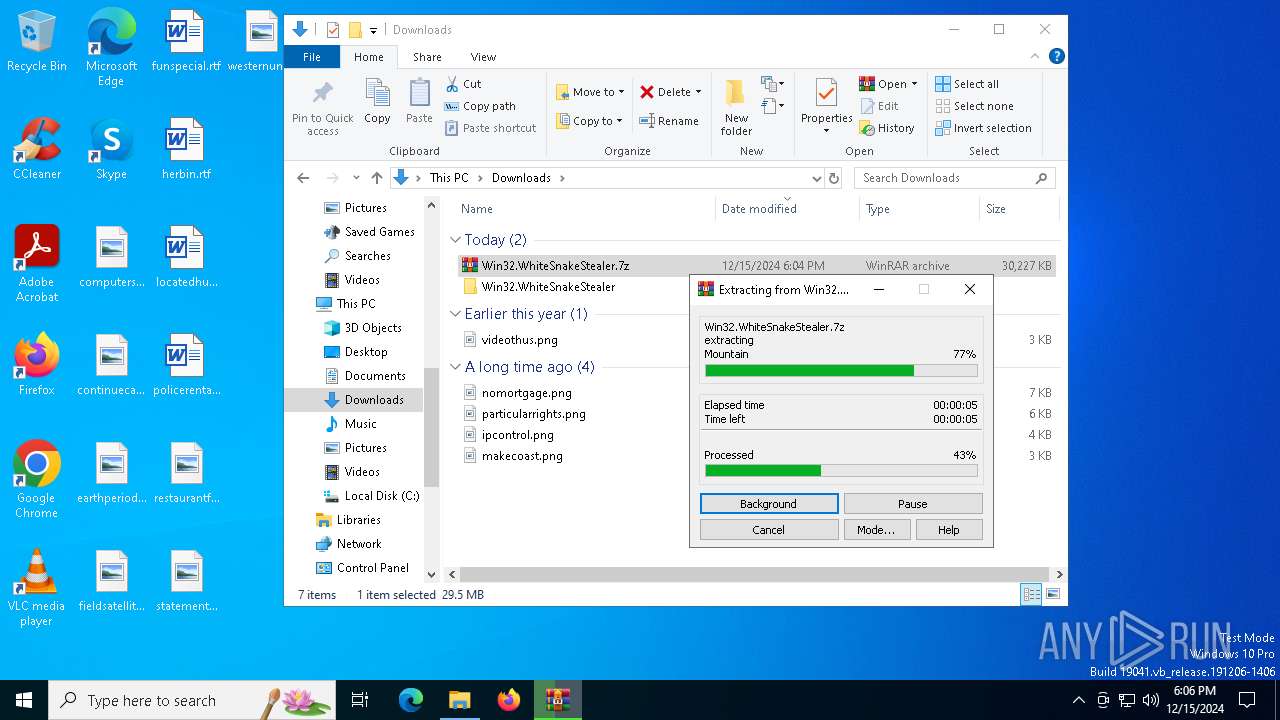
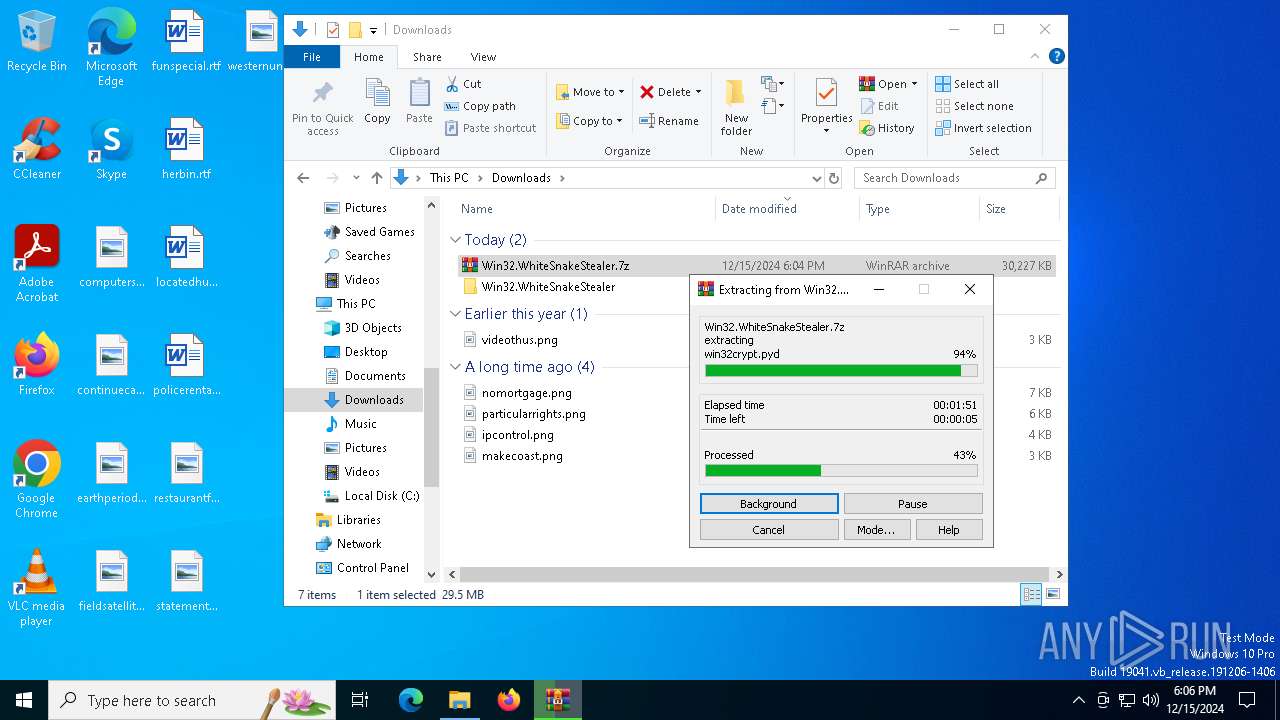
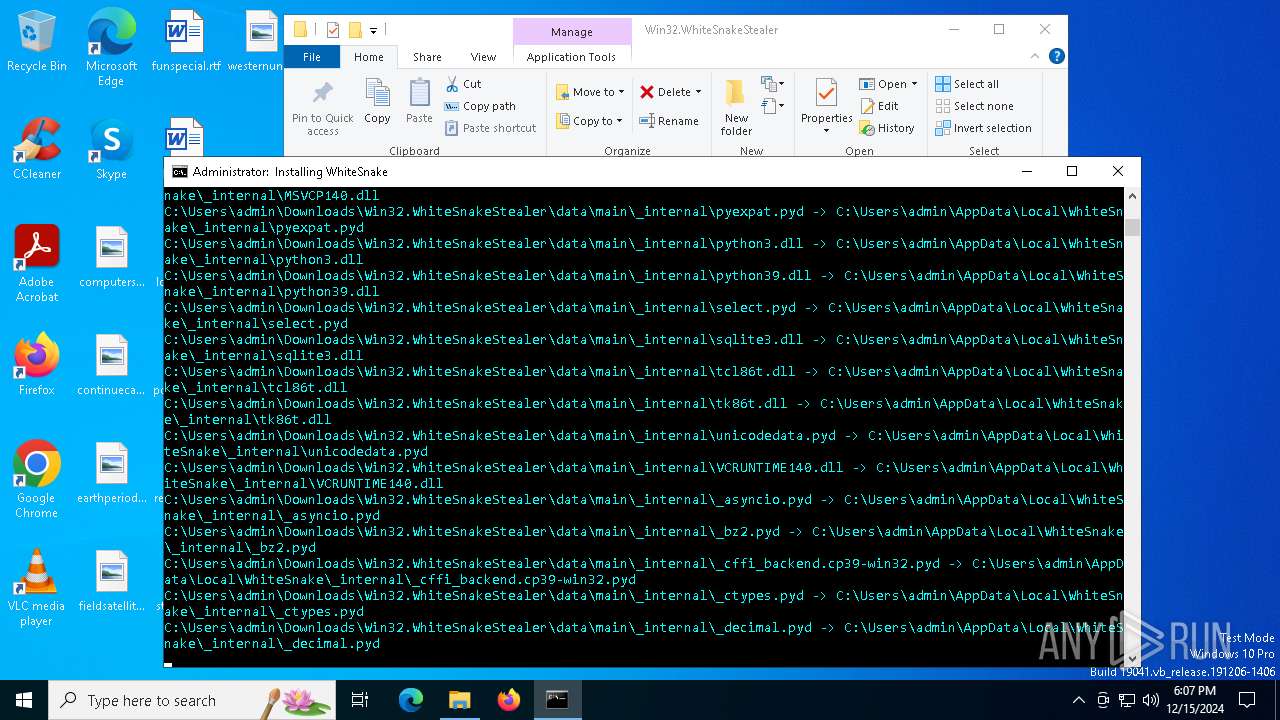
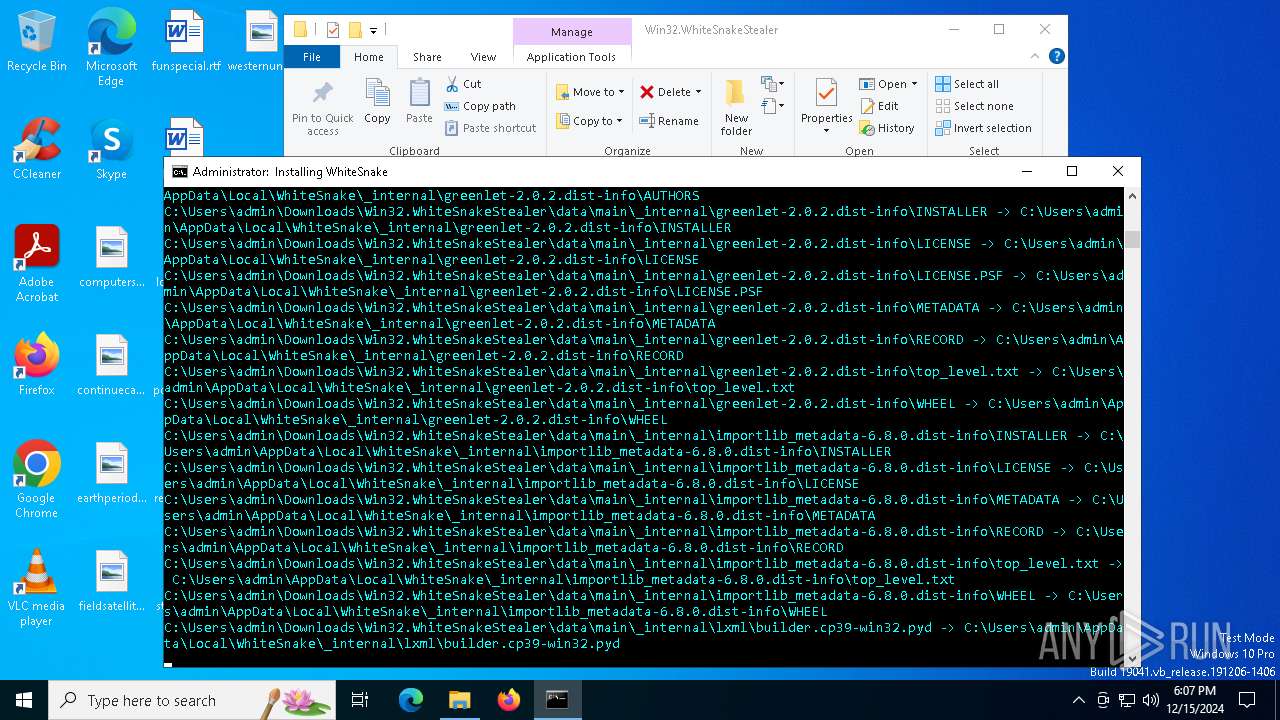
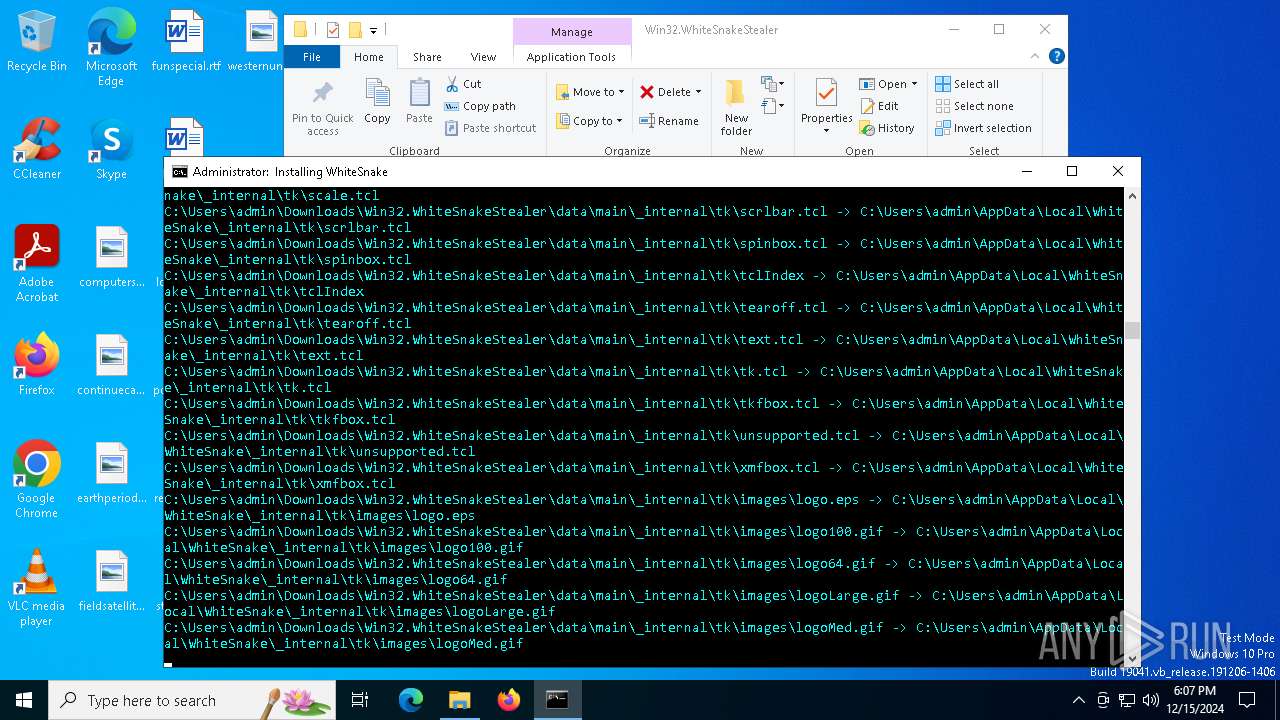
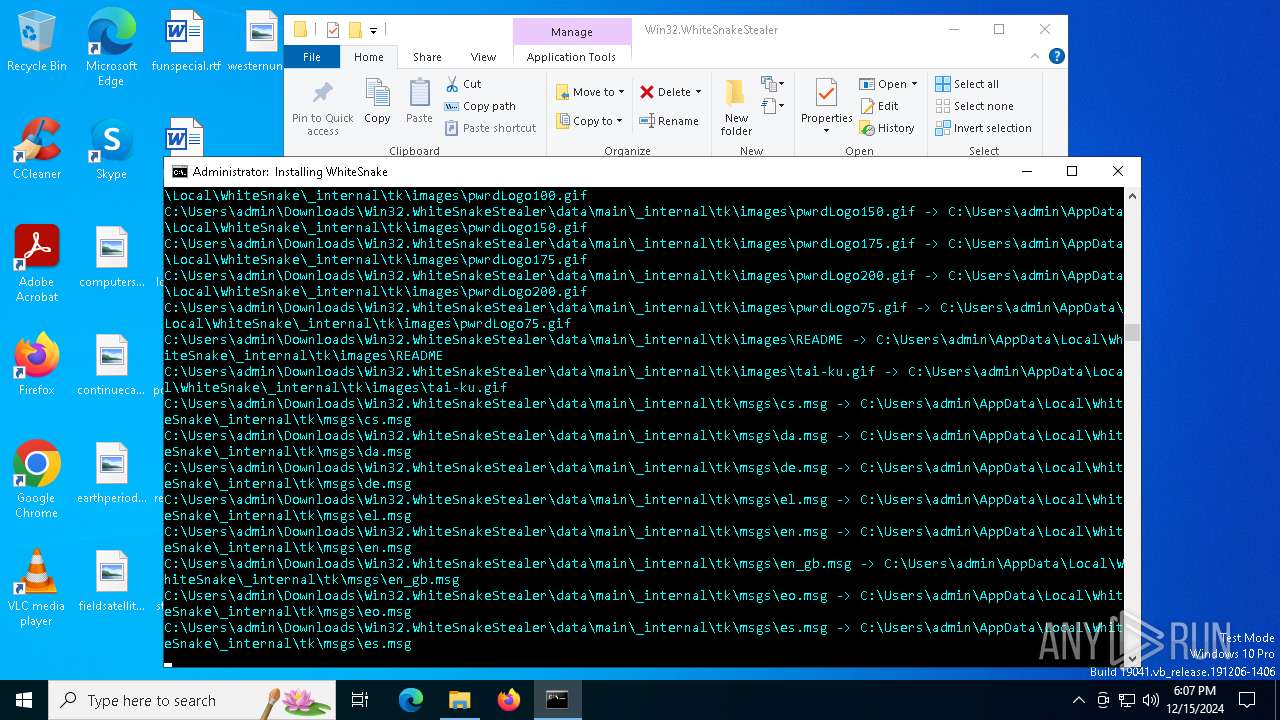
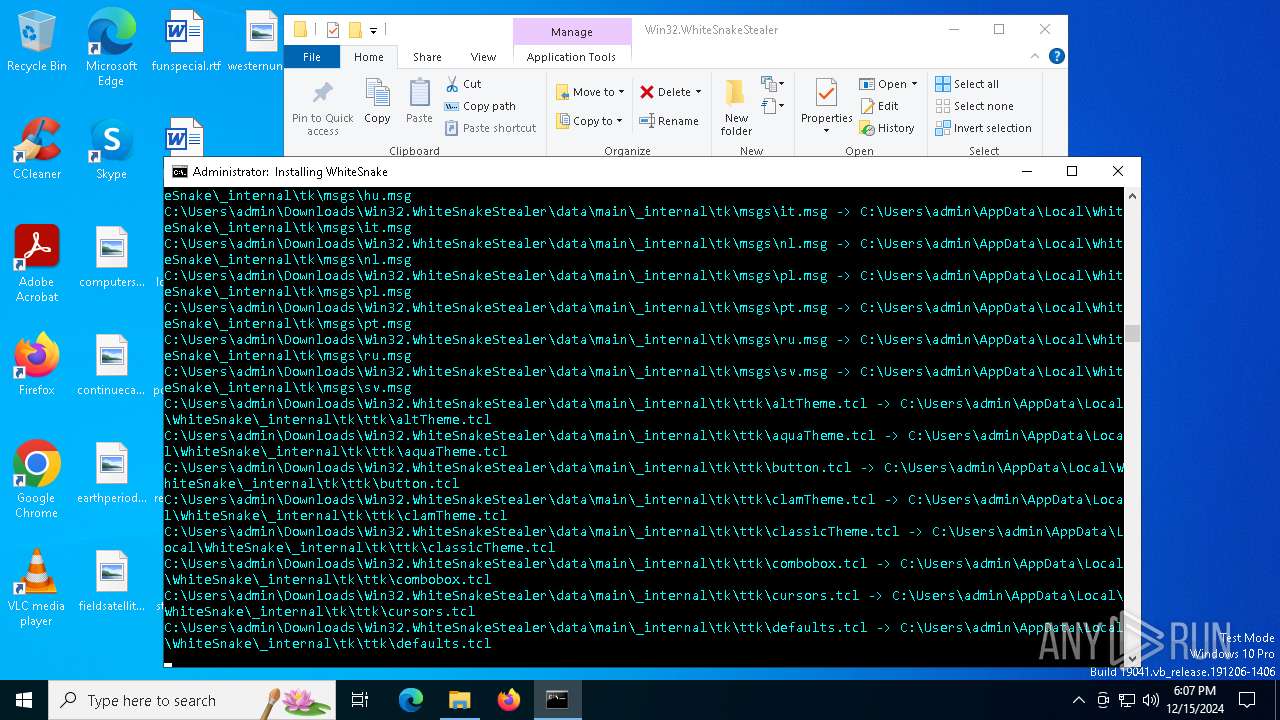
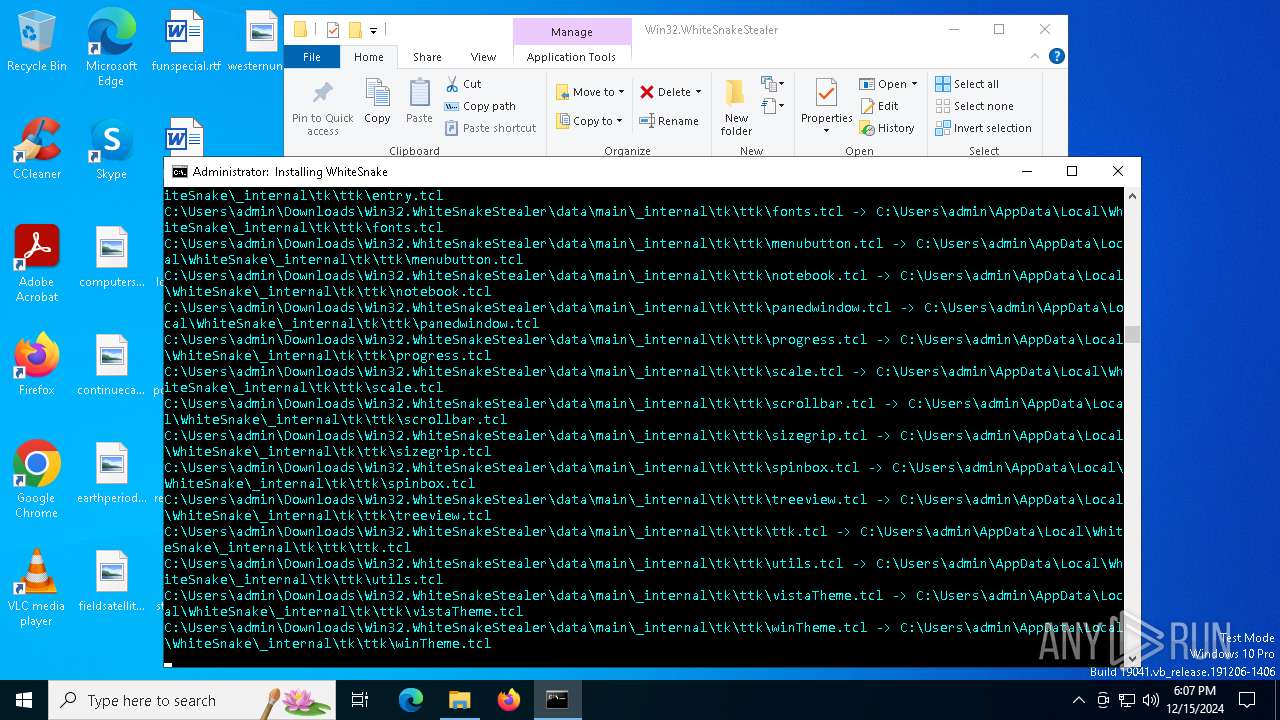
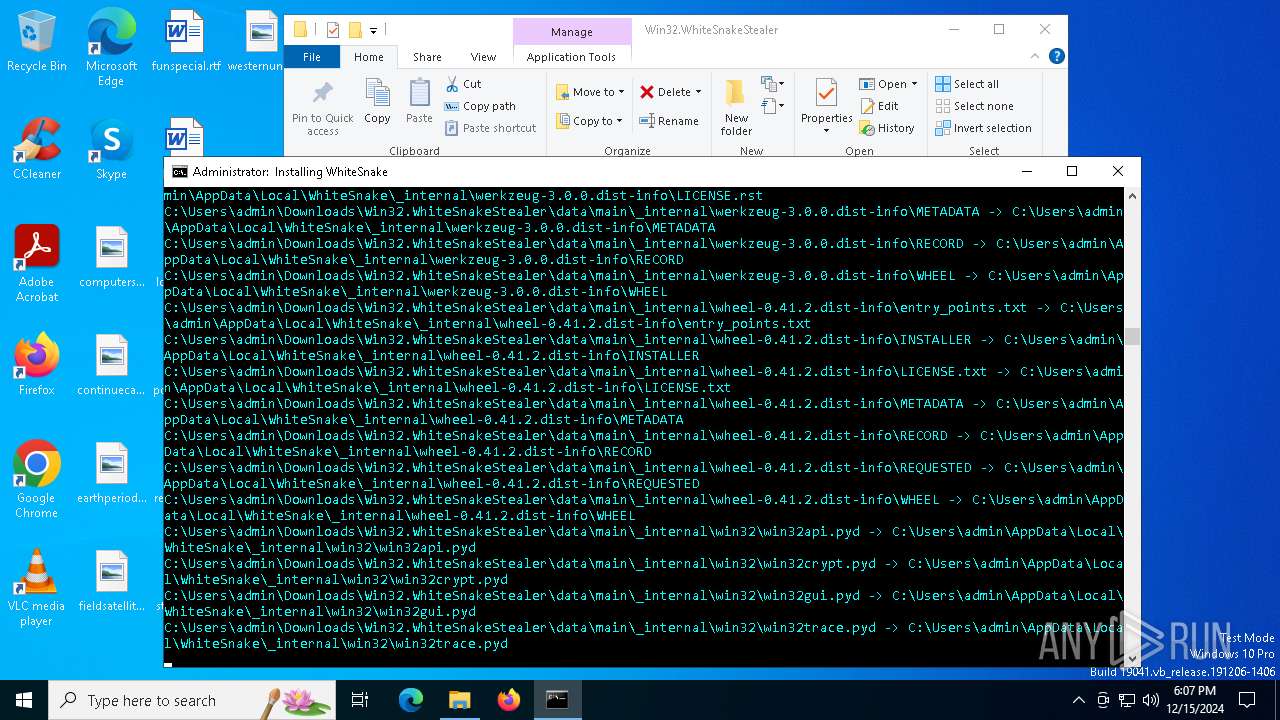
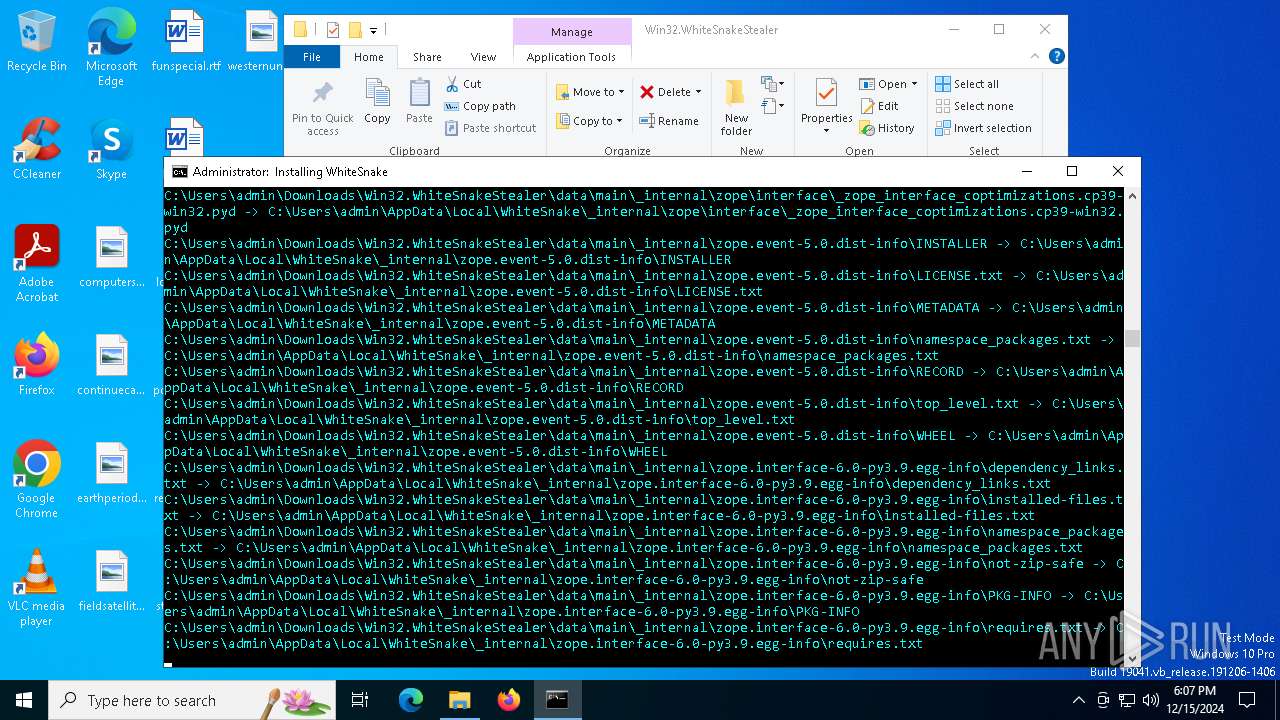
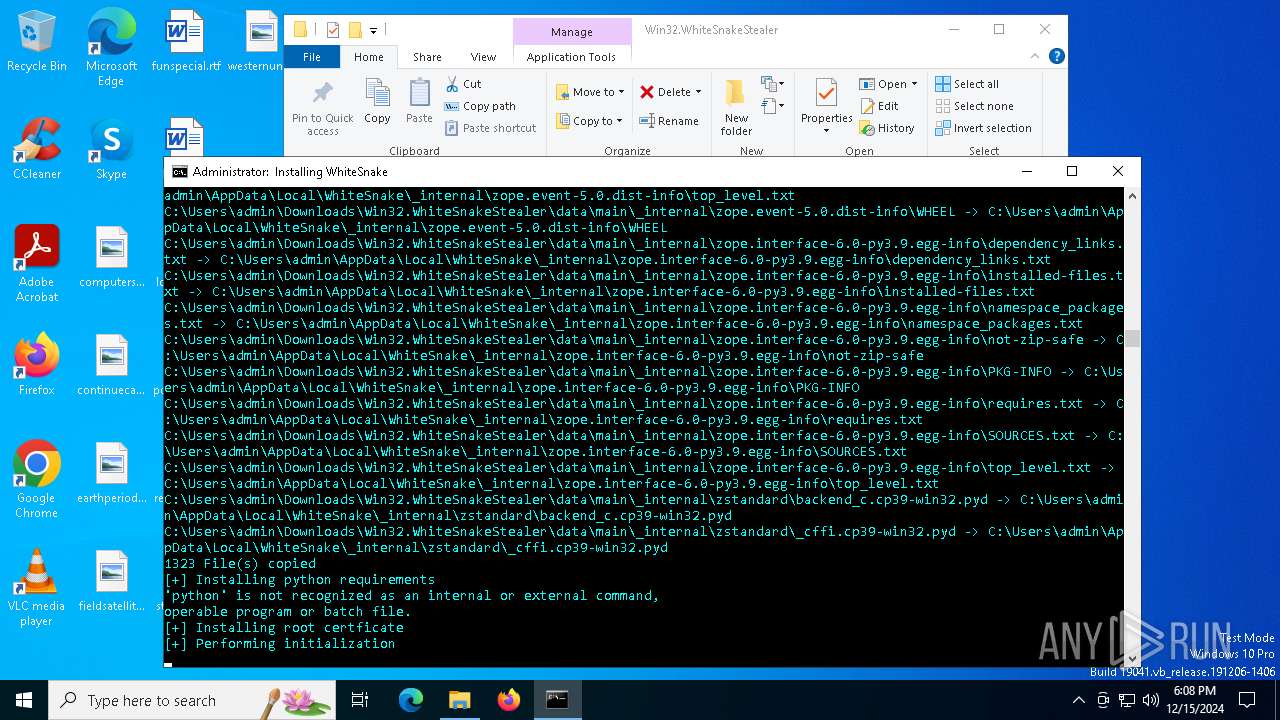
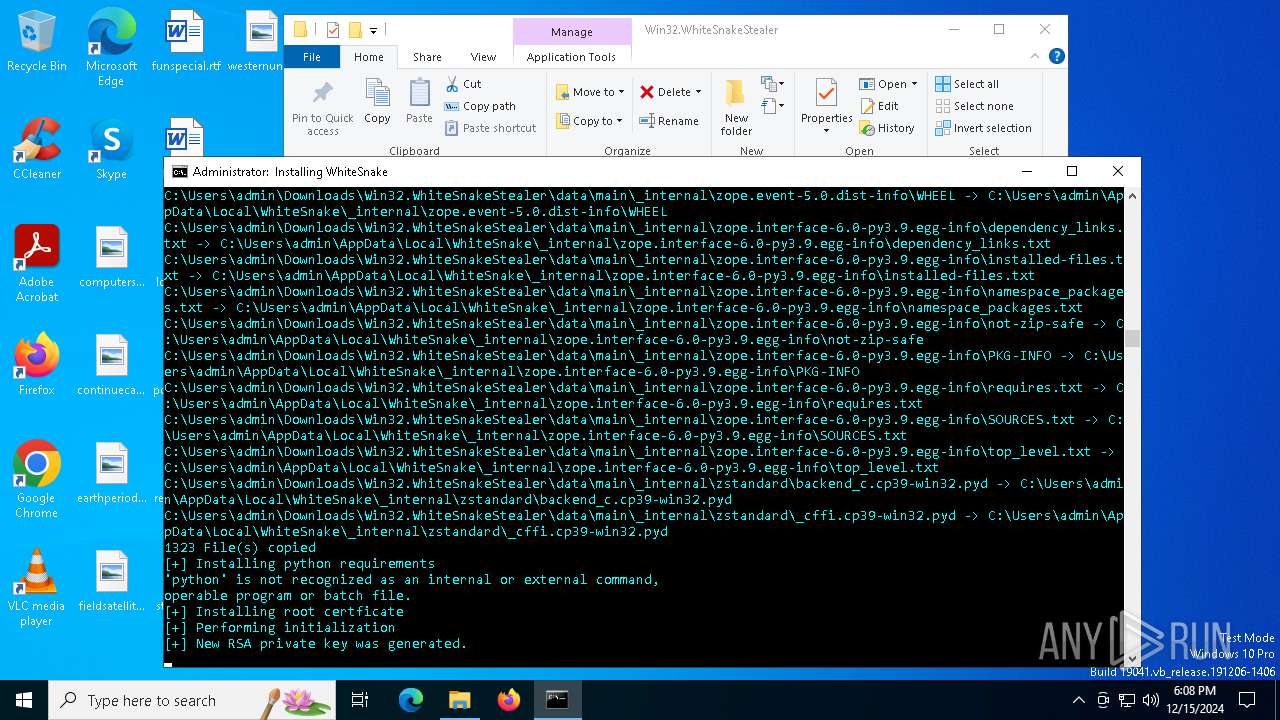
Process drops python dynamic module
- WinRAR.exe (PID: 556)
- xcopy.exe (PID: 2792)
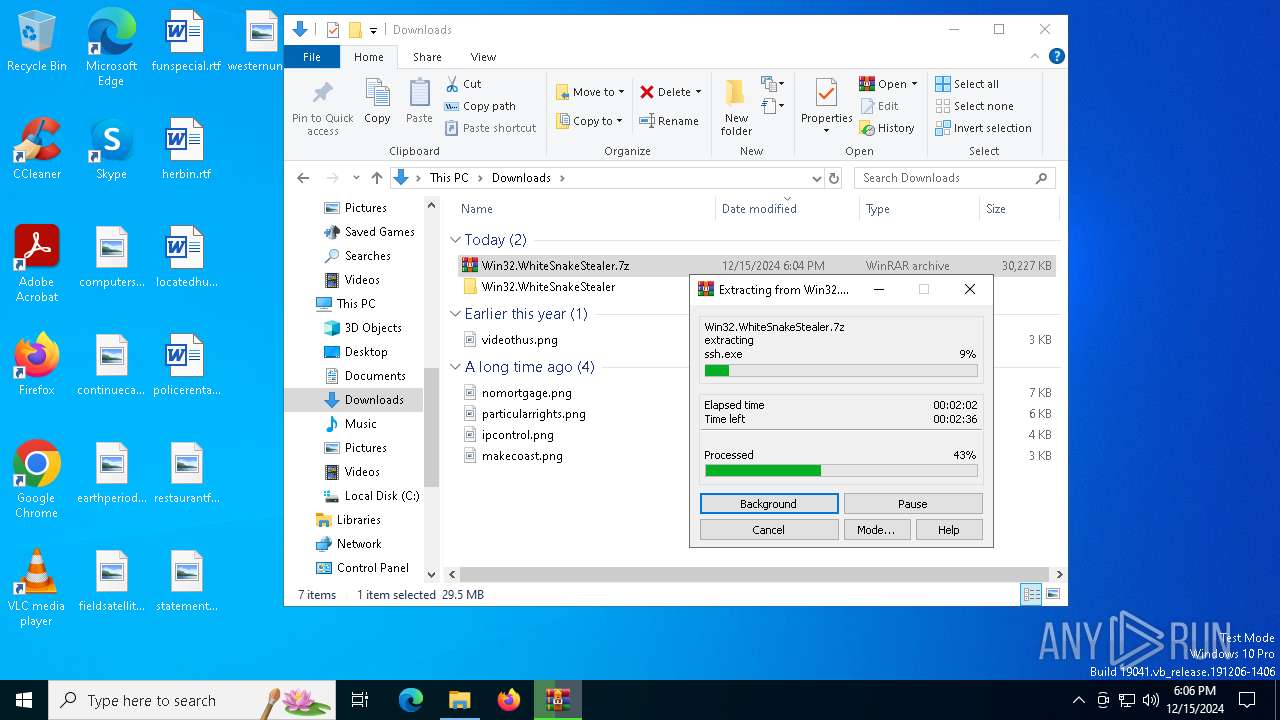
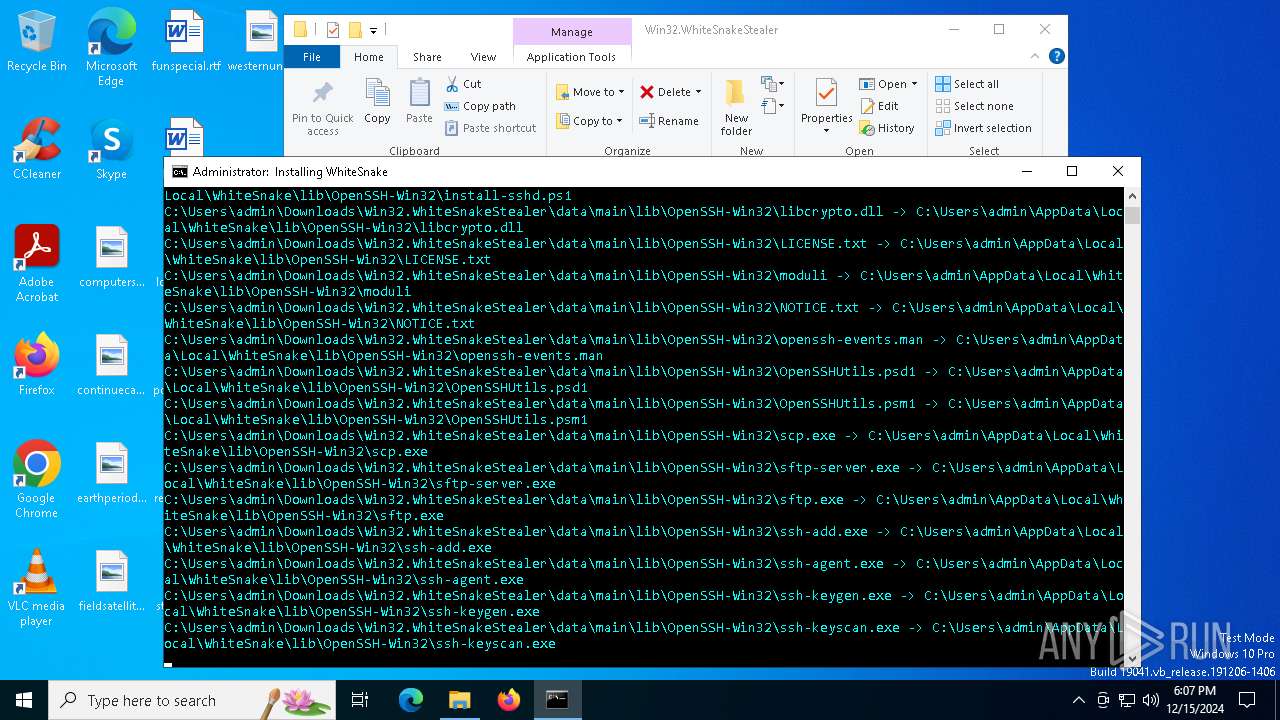
Process drops legitimate windows executable
- WinRAR.exe (PID: 556)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 556)
- xcopy.exe (PID: 2792)
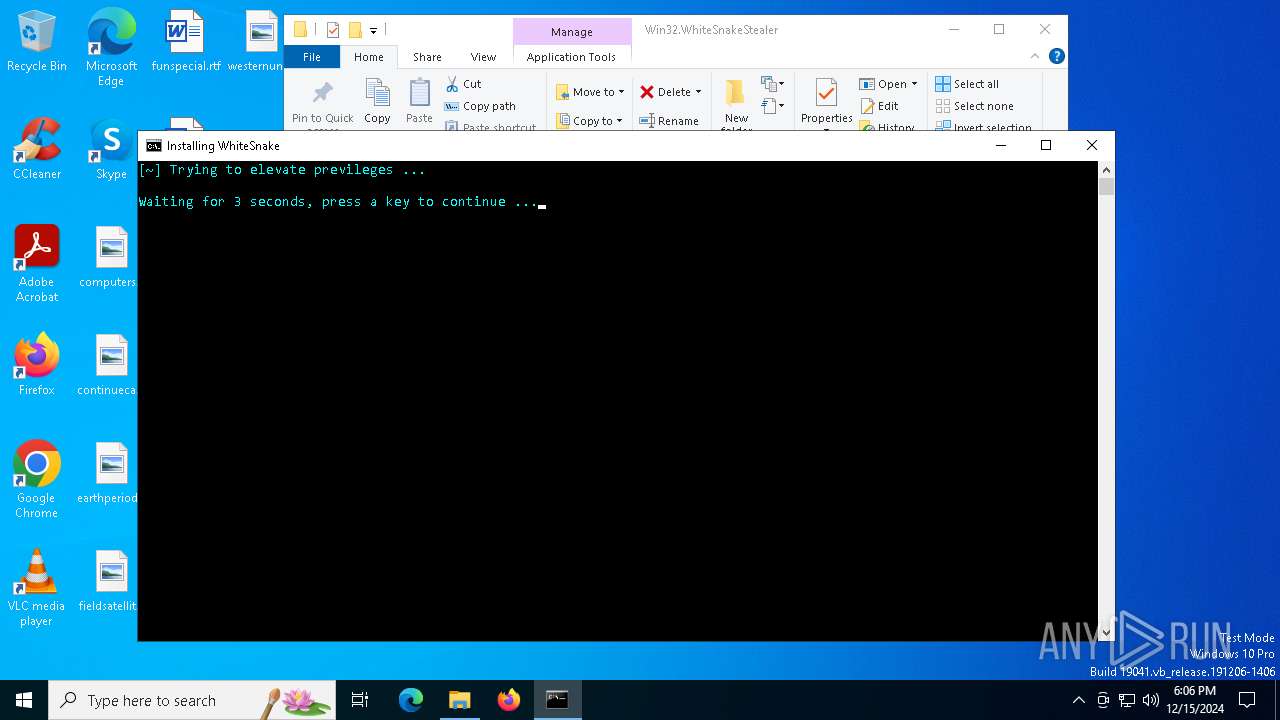
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6664)
- cmd.exe (PID: 7052)
Starts process via Powershell
- powershell.exe (PID: 6948)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6664)
- cmd.exe (PID: 7052)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7052)
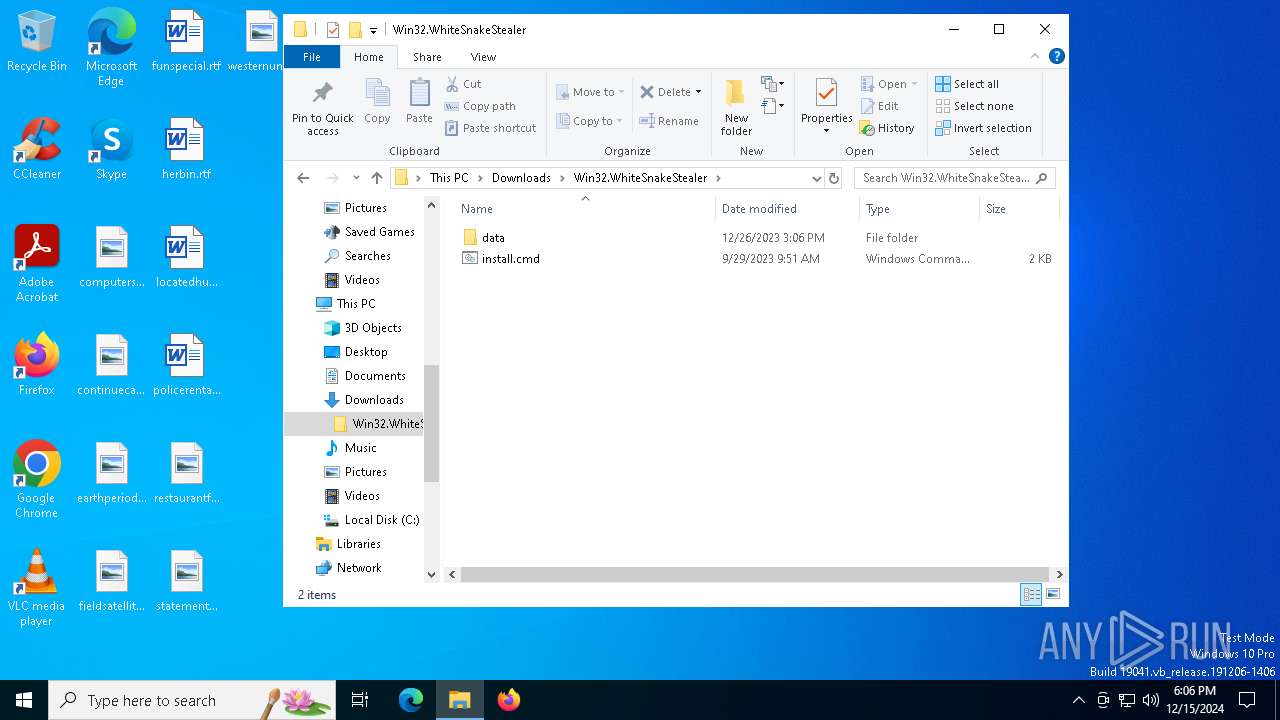
Executing commands from ".cmd" file
- powershell.exe (PID: 6948)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6948)
- dumper.exe (PID: 6420)
- cmd.exe (PID: 1476)
- cmd.exe (PID: 4908)
The process hide an interactive prompt from the user
- cmd.exe (PID: 7052)
Process changes security settings for the VBA macro
- reg.exe (PID: 6992)
- reg.exe (PID: 6940)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7052)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7052)
Executable content was dropped or overwritten
- xcopy.exe (PID: 2792)
- dumper.exe (PID: 6420)
The process drops C-runtime libraries
- xcopy.exe (PID: 2792)
The executable file from the user directory is run by the CMD process
- dumper.exe (PID: 6420)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 7052)
Adds/modifies Windows certificates
- rundll32.exe (PID: 6608)
Reads security settings of Internet Explorer
- dumper.exe (PID: 6420)
- dumper.exe (PID: 2904)
Loads Python modules
- dumper.exe (PID: 6420)
- dumper.exe (PID: 2904)
Application launched itself
- cmd.exe (PID: 1476)
- cmd.exe (PID: 4908)
The process executes VB scripts
- cmd.exe (PID: 6936)
- cmd.exe (PID: 3840)
Runs shell command (SCRIPT)
- wscript.exe (PID: 4188)
- wscript.exe (PID: 5564)
The process checks if it is being run in the virtual environment
- dumper.exe (PID: 2904)
Connects to unusual port
- tor.exe (PID: 6560)
Checks for external IP
- svchost.exe (PID: 2192)
- dumper.exe (PID: 2904)
Potential Corporate Privacy Violation
- dumper.exe (PID: 2904)
INFO
Application launched itself
- msedge.exe (PID: 6444)
- msedge.exe (PID: 4624)
- chrome.exe (PID: 5572)
The process uses the downloaded file
- iexplore.exe (PID: 6228)
- msedge.exe (PID: 6056)
- WinRAR.exe (PID: 556)
- powershell.exe (PID: 6948)
- xcopy.exe (PID: 2792)
- cmd.exe (PID: 7052)
- dumper.exe (PID: 6420)
- cmd.exe (PID: 6936)
- wscript.exe (PID: 4188)
- cmd.exe (PID: 3840)
- chrome.exe (PID: 6200)
- wscript.exe (PID: 5564)
- chrome.exe (PID: 1828)
Reads the computer name
- identity_helper.exe (PID: 5008)
- identity_helper.exe (PID: 716)
- dumper.exe (PID: 6420)
- dumper.exe (PID: 2904)
- tor.exe (PID: 6560)
Checks supported languages
- identity_helper.exe (PID: 5008)
- identity_helper.exe (PID: 716)
- dumper.exe (PID: 6420)
- tor.exe (PID: 6560)
- dumper.exe (PID: 2904)
Reads Environment values
- identity_helper.exe (PID: 5008)
- identity_helper.exe (PID: 716)
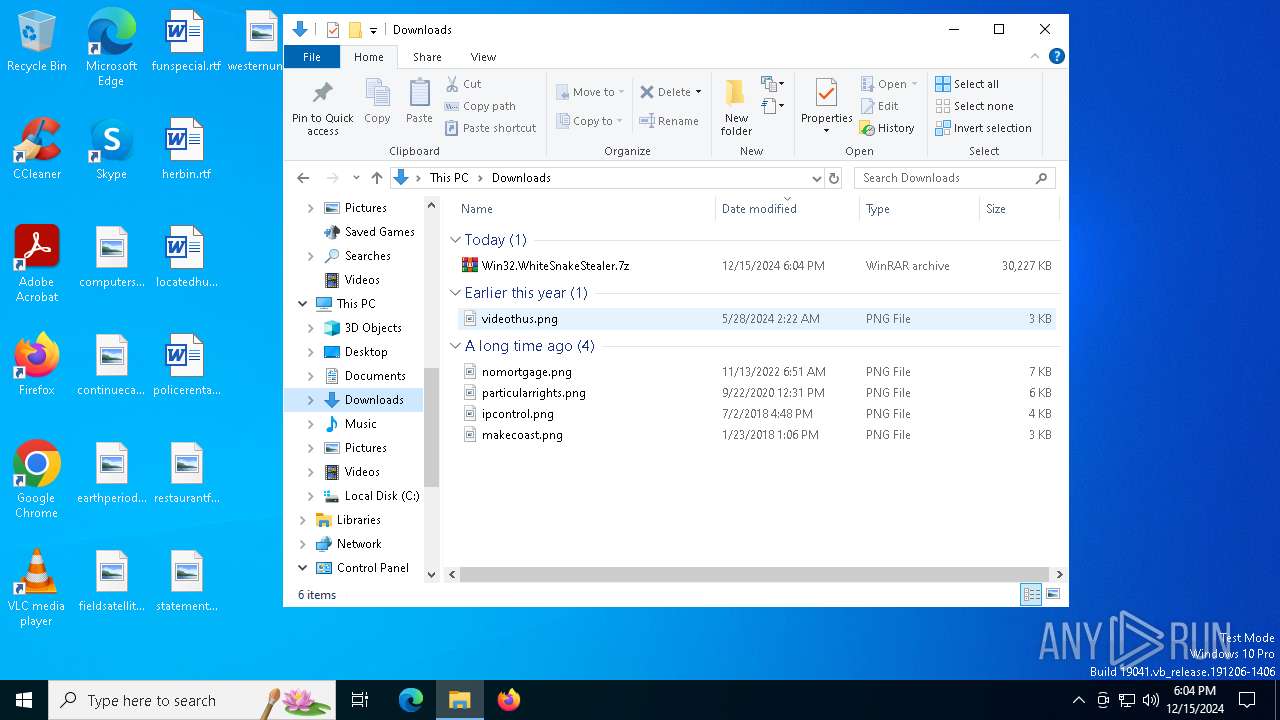
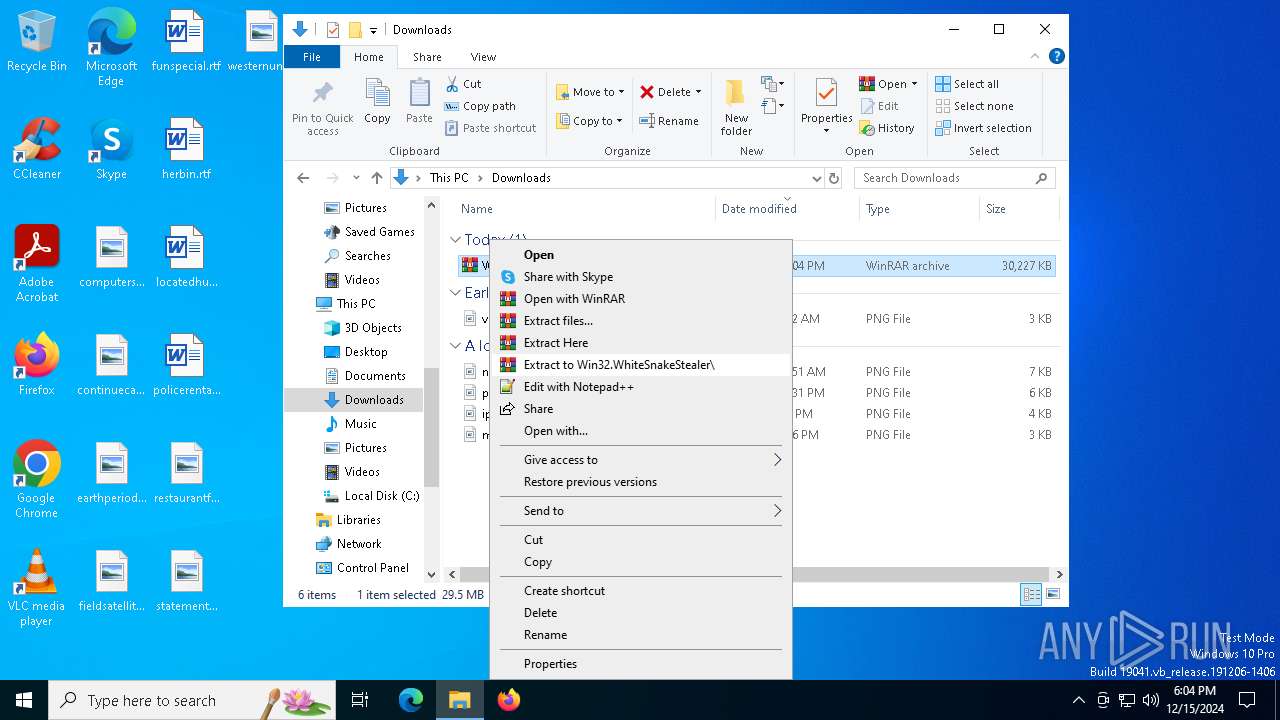
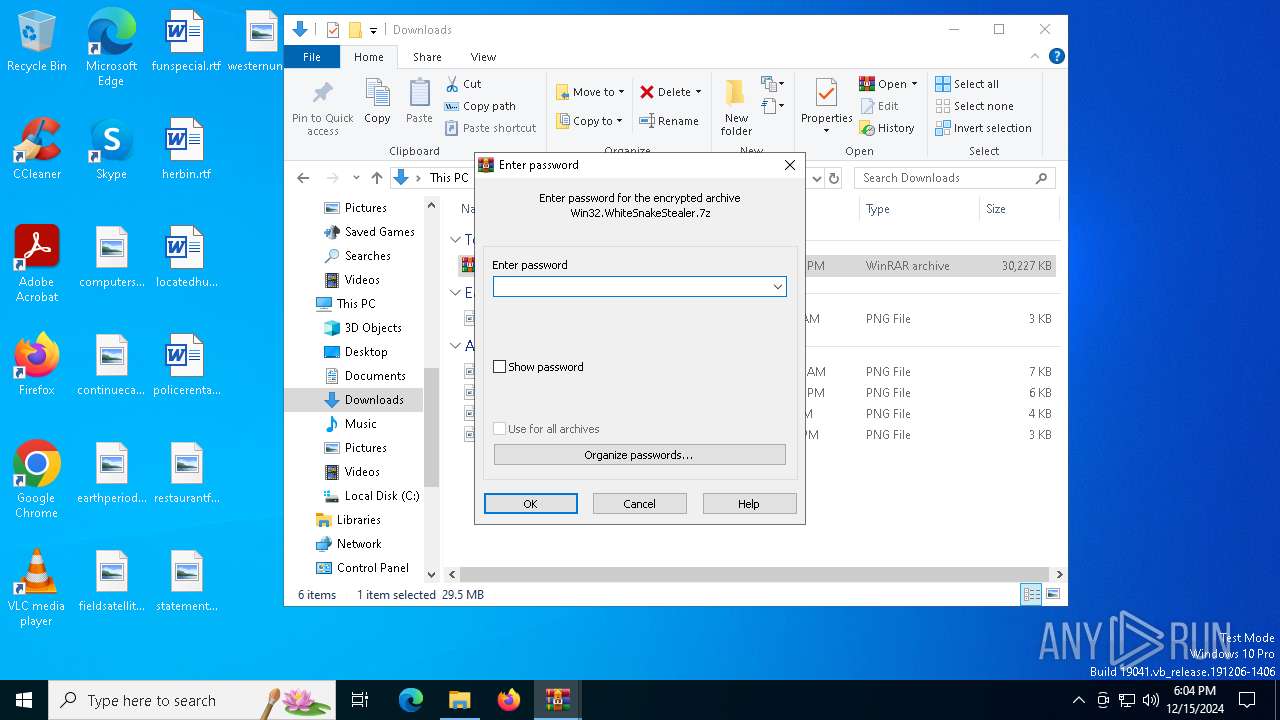
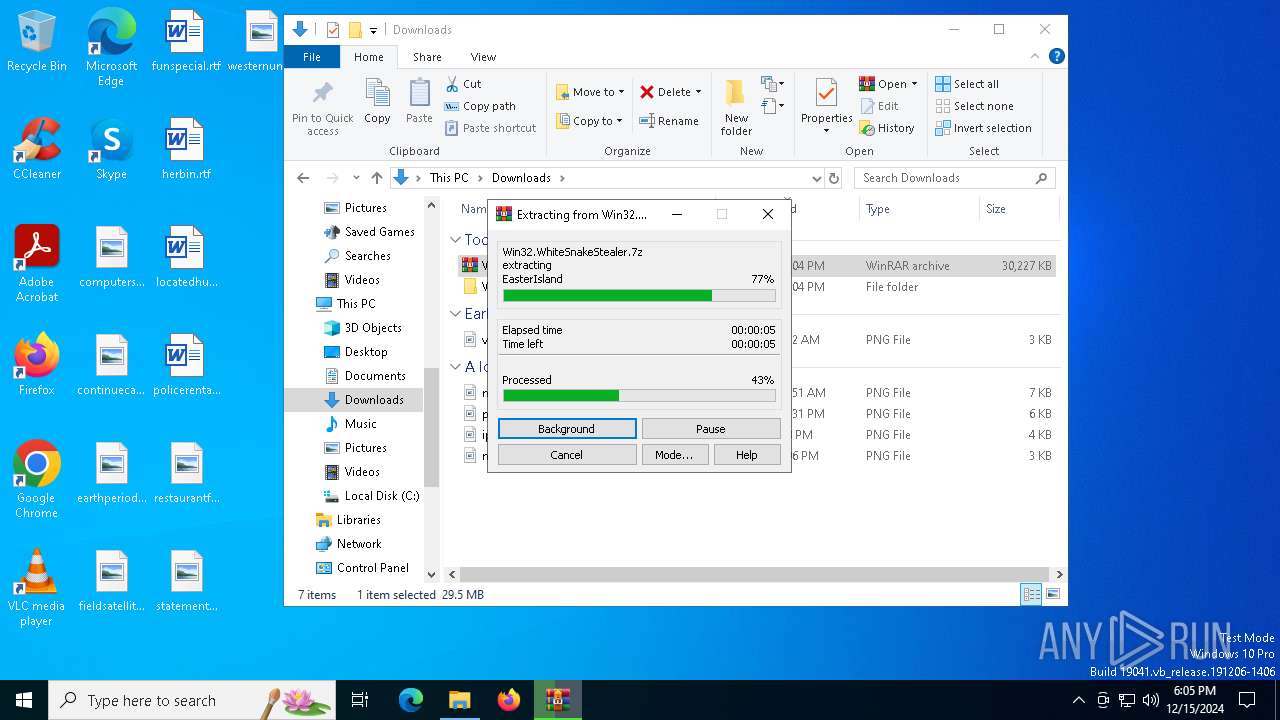
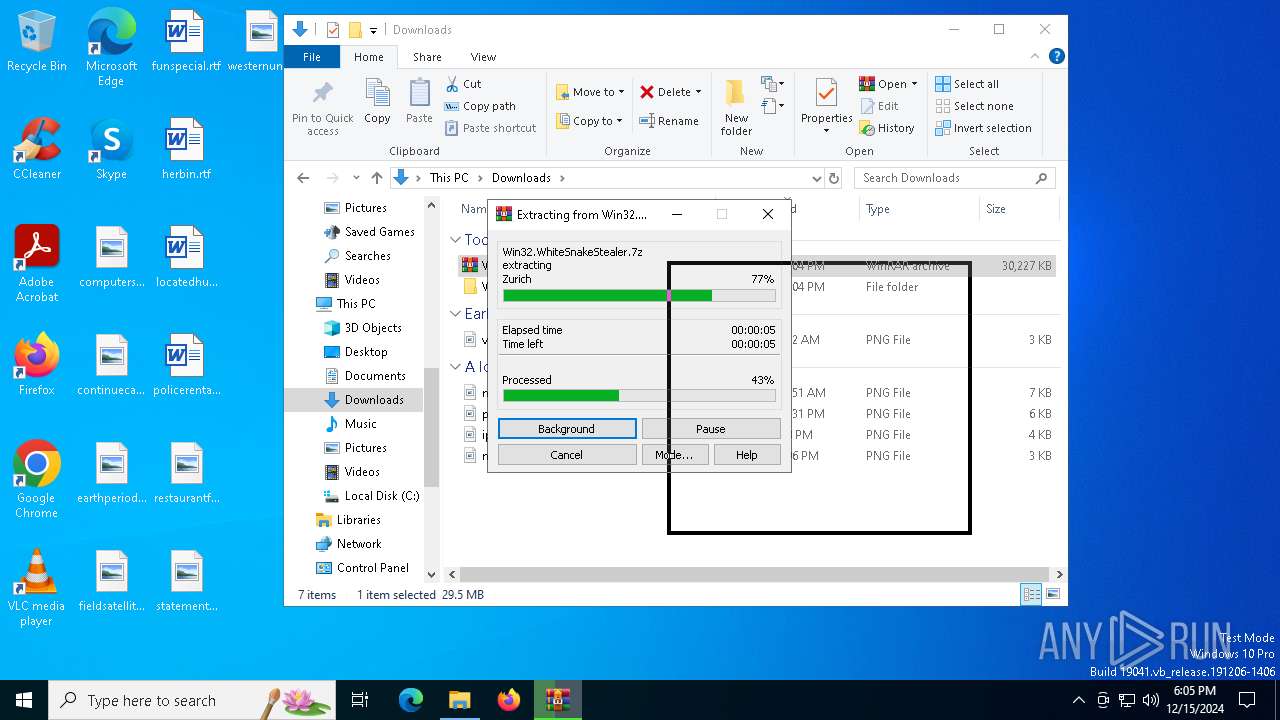
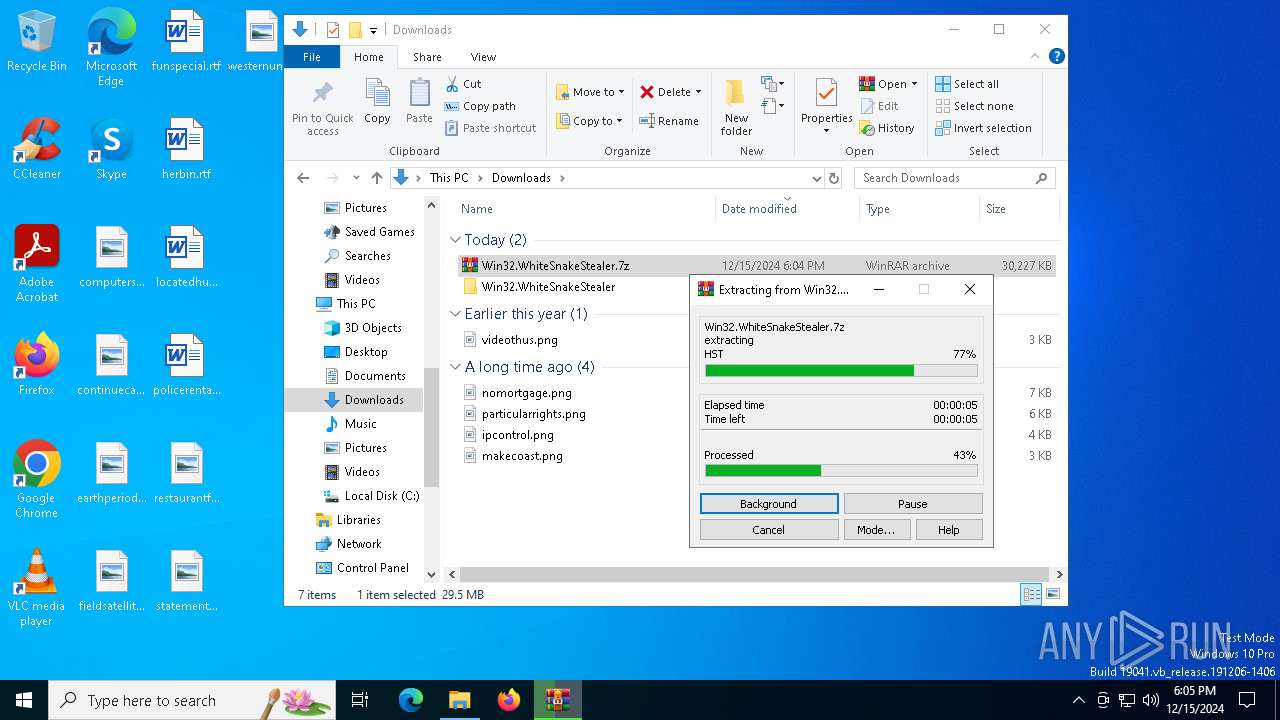
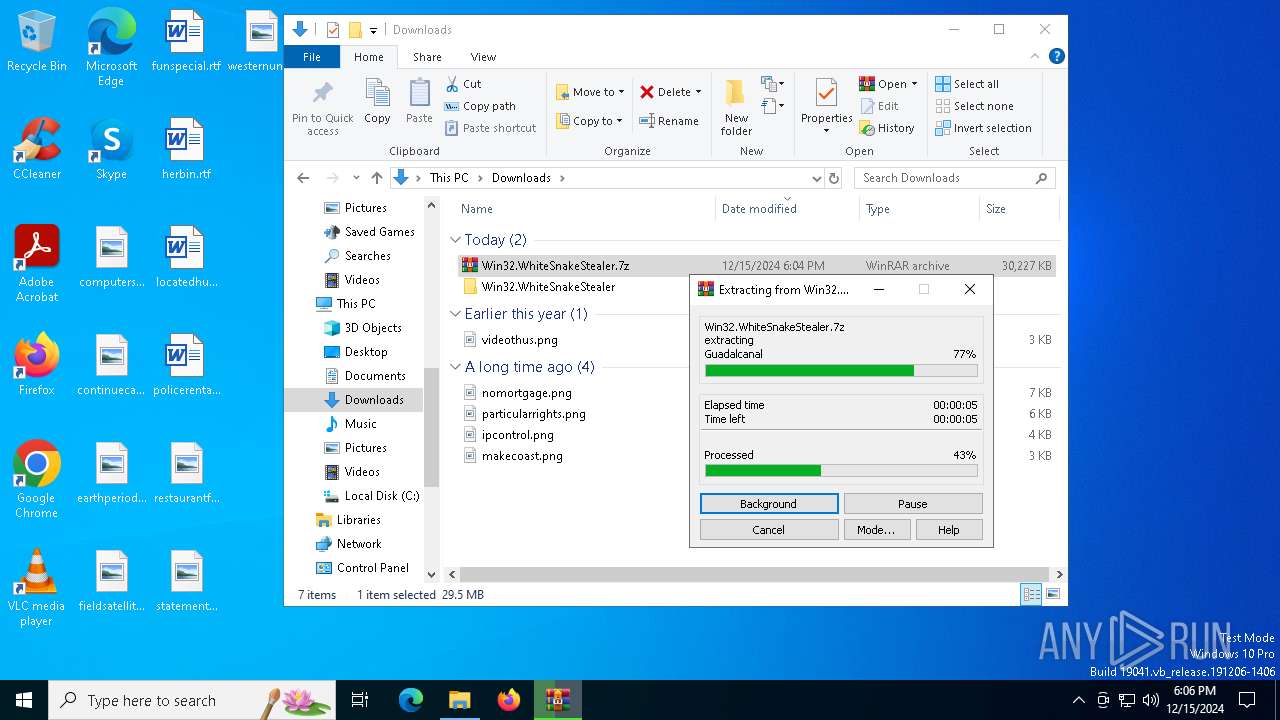
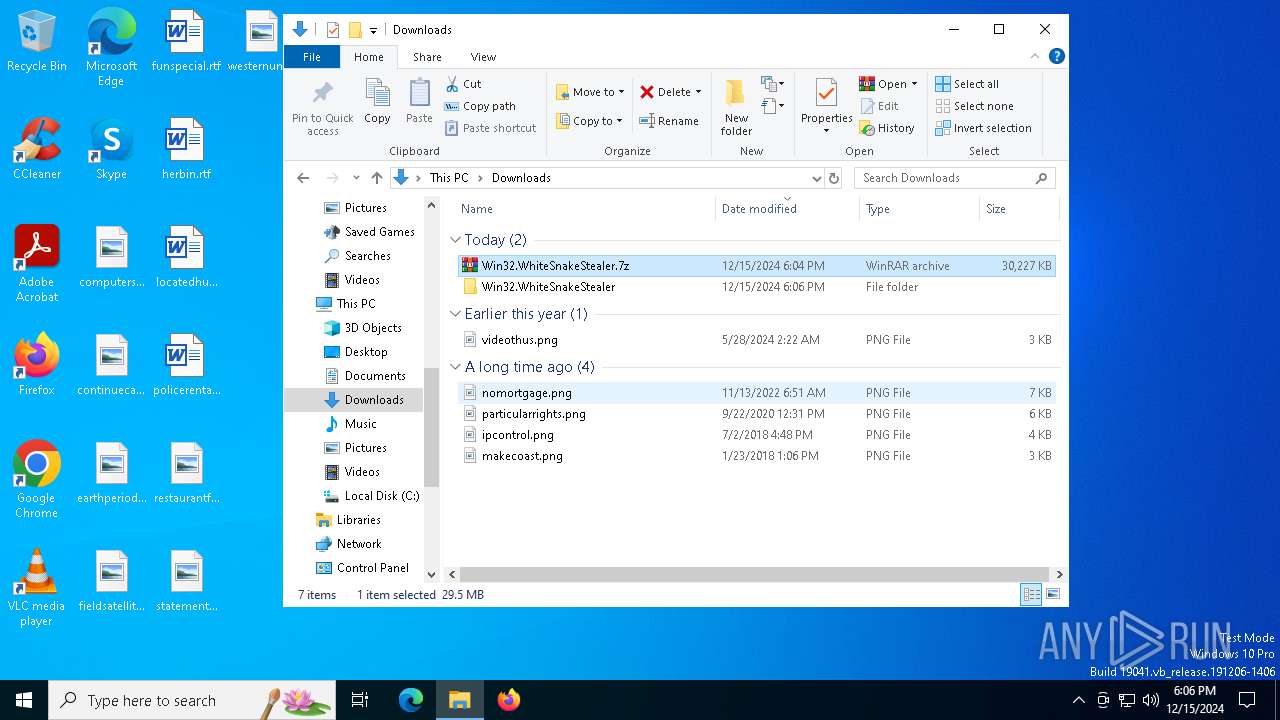
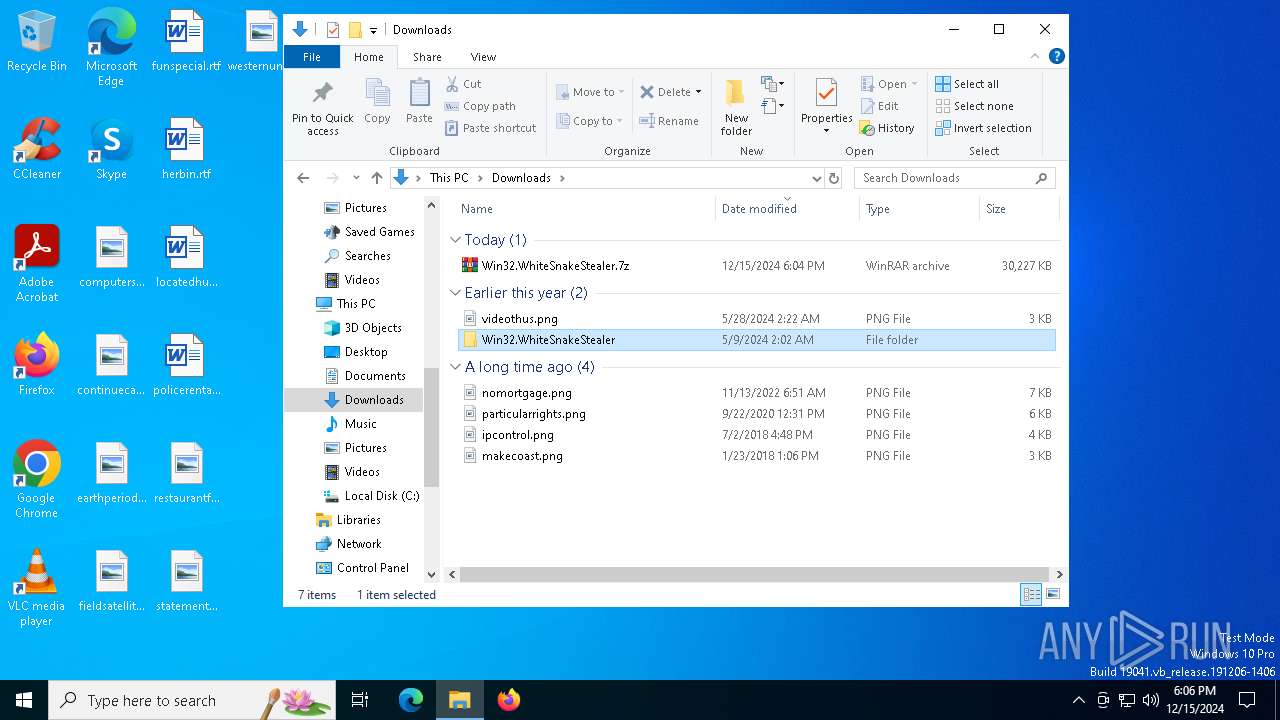
Manual execution by a user
- WinRAR.exe (PID: 556)
- cmd.exe (PID: 6664)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 556)
- msedge.exe (PID: 4228)
The sample compiled with english language support
- WinRAR.exe (PID: 556)
- msedge.exe (PID: 4228)
- xcopy.exe (PID: 2792)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2904)
- powershell.exe (PID: 5340)
Reads Microsoft Office registry keys
- reg.exe (PID: 6992)
- reg.exe (PID: 6940)
- reg.exe (PID: 6924)
- reg.exe (PID: 6932)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 6608)
Reads the software policy settings
- rundll32.exe (PID: 6608)
Creates files or folders in the user directory
- xcopy.exe (PID: 2792)
- dumper.exe (PID: 6420)
Checks proxy server information
- dumper.exe (PID: 6420)
- dumper.exe (PID: 2904)
Create files in a temporary directory
- dumper.exe (PID: 6420)
- tor.exe (PID: 6560)
- dumper.exe (PID: 2904)
Reads the machine GUID from the registry
- dumper.exe (PID: 6420)
- tor.exe (PID: 6560)
- dumper.exe (PID: 2904)
PyInstaller has been detected (YARA)
- dumper.exe (PID: 6420)
Sends debugging messages
- chrome.exe (PID: 5572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
244
Monitored processes
114
Malicious processes
11
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --user-data-dir="C:\Users\admin\AppData\Local\Temp\WhiteSnake\UI-Data" --no-appcompat-clear --mojo-platform-channel-handle=5920 --field-trial-handle=1940,i,11759844817470226412,10945628022304037819,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=7288 --field-trial-handle=2372,i,8998543473905653330,3158247438140662868,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 556 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Win32.WhiteSnakeStealer.7z" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 716 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4876 --field-trial-handle=2332,i,966736184297172241,7688611293632914463,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3400 --field-trial-handle=2332,i,966736184297172241,7688611293632914463,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1016 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6824 --field-trial-handle=2372,i,8998543473905653330,3158247438140662868,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Local\Temp\WhiteSnake\UI-Data" --no-appcompat-clear --mojo-platform-channel-handle=5268 --field-trial-handle=1940,i,11759844817470226412,10945628022304037819,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 1476 | C:\WINDOWS\system32\cmd.exe /c %ComSpec% /c "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\tor.vbs" | C:\Windows\SysWOW64\cmd.exe | — | dumper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Local\Temp\WhiteSnake\UI-Data" --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=5940 --field-trial-handle=1940,i,11759844817470226412,10945628022304037819,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 1576 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2852 --field-trial-handle=2332,i,966736184297172241,7688611293632914463,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
43 641
Read events
43 585
Write events
54
Delete events
2
Modification events
| (PID) Process: | (6228) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6228) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6228) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6228) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (6228) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (6228) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6444) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
315
Suspicious files
640
Text files
2 443
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1358e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1358e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135910.TMP | — | |
MD5:— | SHA256:— | |||
| 6444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13592f.TMP | — | |
MD5:— | SHA256:— | |||
| 6444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135910.TMP | — | |
MD5:— | SHA256:— | |||
| 6444 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
84
DNS requests
87
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.73.2.140:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.73.2.140:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.202.117.137:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.202.117.137:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4556 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d50ccf3e-dd06-4e6f-bb20-931c8ce33527?P1=1734740323&P2=404&P3=2&P4=GGzw8jHlJROKHWyERcJLsLRarCtEO5G%2bkt73qJrlTgyLmMzOUqkJKe1Tl3muIVp57LK5zx8%2byDNdw4xd3BmBOQ%3d%3d | unknown | — | — | whitelisted |
4556 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d50ccf3e-dd06-4e6f-bb20-931c8ce33527?P1=1734740323&P2=404&P3=2&P4=GGzw8jHlJROKHWyERcJLsLRarCtEO5G%2bkt73qJrlTgyLmMzOUqkJKe1Tl3muIVp57LK5zx8%2byDNdw4xd3BmBOQ%3d%3d | unknown | — | — | whitelisted |
4556 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d50ccf3e-dd06-4e6f-bb20-931c8ce33527?P1=1734740323&P2=404&P3=2&P4=GGzw8jHlJROKHWyERcJLsLRarCtEO5G%2bkt73qJrlTgyLmMzOUqkJKe1Tl3muIVp57LK5zx8%2byDNdw4xd3BmBOQ%3d%3d | unknown | — | — | whitelisted |
4556 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d50ccf3e-dd06-4e6f-bb20-931c8ce33527?P1=1734740323&P2=404&P3=2&P4=GGzw8jHlJROKHWyERcJLsLRarCtEO5G%2bkt73qJrlTgyLmMzOUqkJKe1Tl3muIVp57LK5zx8%2byDNdw4xd3BmBOQ%3d%3d | unknown | — | — | whitelisted |
4556 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d50ccf3e-dd06-4e6f-bb20-931c8ce33527?P1=1734740323&P2=404&P3=2&P4=GGzw8jHlJROKHWyERcJLsLRarCtEO5G%2bkt73qJrlTgyLmMzOUqkJKe1Tl3muIVp57LK5zx8%2byDNdw4xd3BmBOQ%3d%3d | unknown | — | — | whitelisted |
4556 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c24e88e1-8ebc-420a-8b50-ddc1a5ad7d16?P1=1734770705&P2=404&P3=2&P4=HzY3azU4bm24dcq6y45akfP0zMGYpmqev4W5lI%2bmSmIUvbbEXV30mclqis3GXoWHr0L7%2bHWf4%2bFy50%2b7OliRPg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5340 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 23.73.2.140:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.73.2.140:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5064 | SearchApp.exe | 96.16.49.223:443 | www.bing.com | Akamai International B.V. | SE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.202.117.137:80 | www.microsoft.com | CW Vodafone Group PLC | FR | whitelisted |
— | — | 23.202.117.137:80 | www.microsoft.com | CW Vodafone Group PLC | FR | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
samples.vx-underground.org |
| malicious |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6560 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 279 |
6560 | tor.exe | Misc Attack | ET TOR Known Tor Exit Node Traffic group 8 |
6560 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 8 |
6560 | tor.exe | Misc Attack | ET TOR Known Tor Exit Node Traffic group 64 |
6560 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 64 |
6560 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 231 |
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2904 | dumper.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6560 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 654 |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\WhiteSnake\UI-Data directory exists )
|