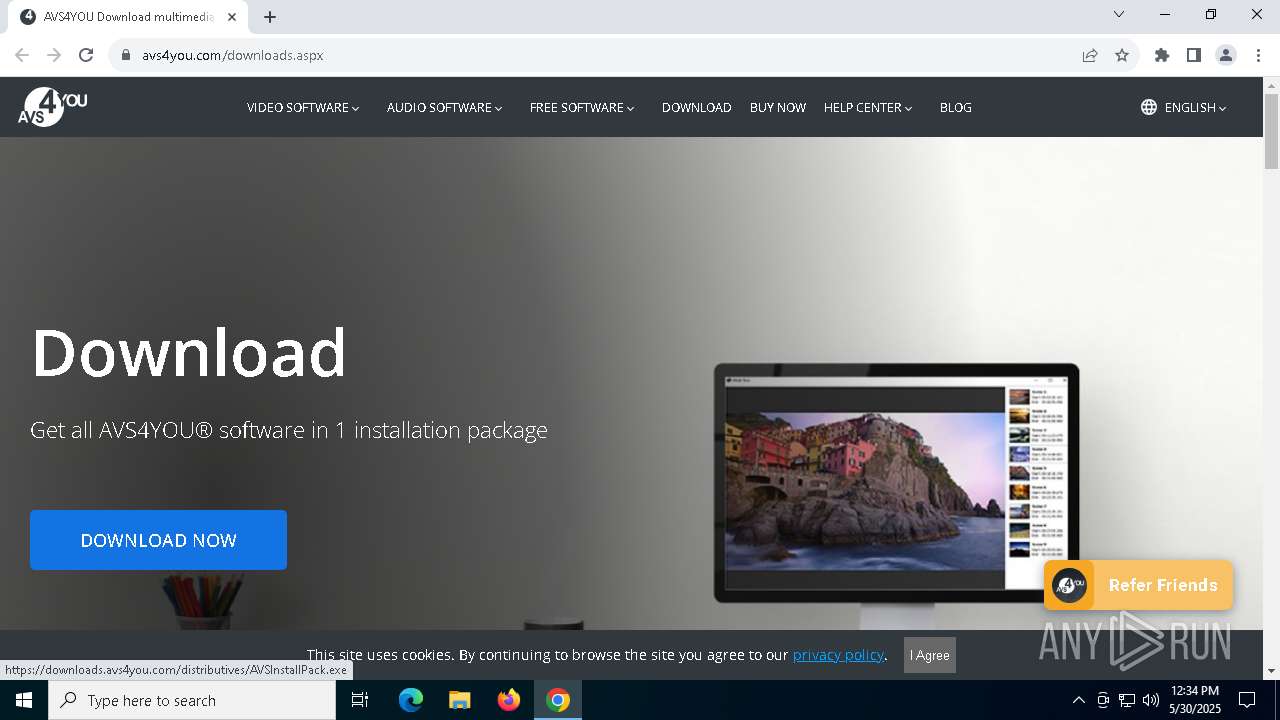
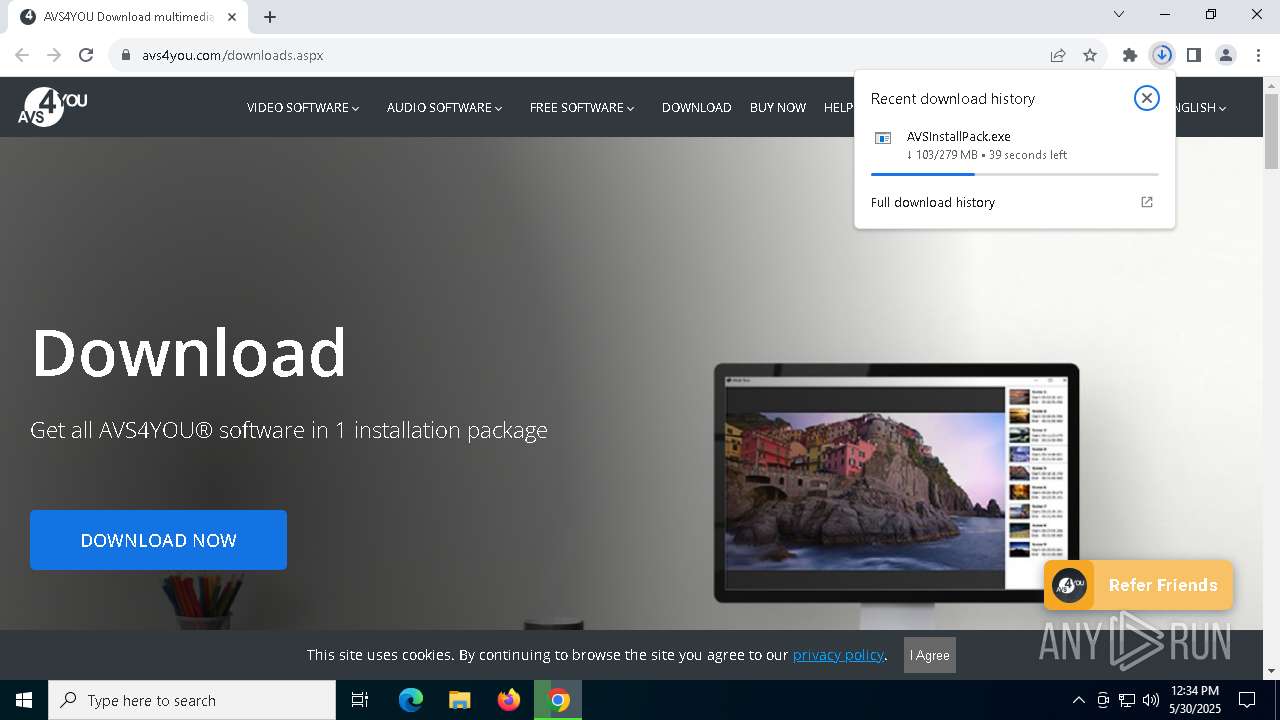
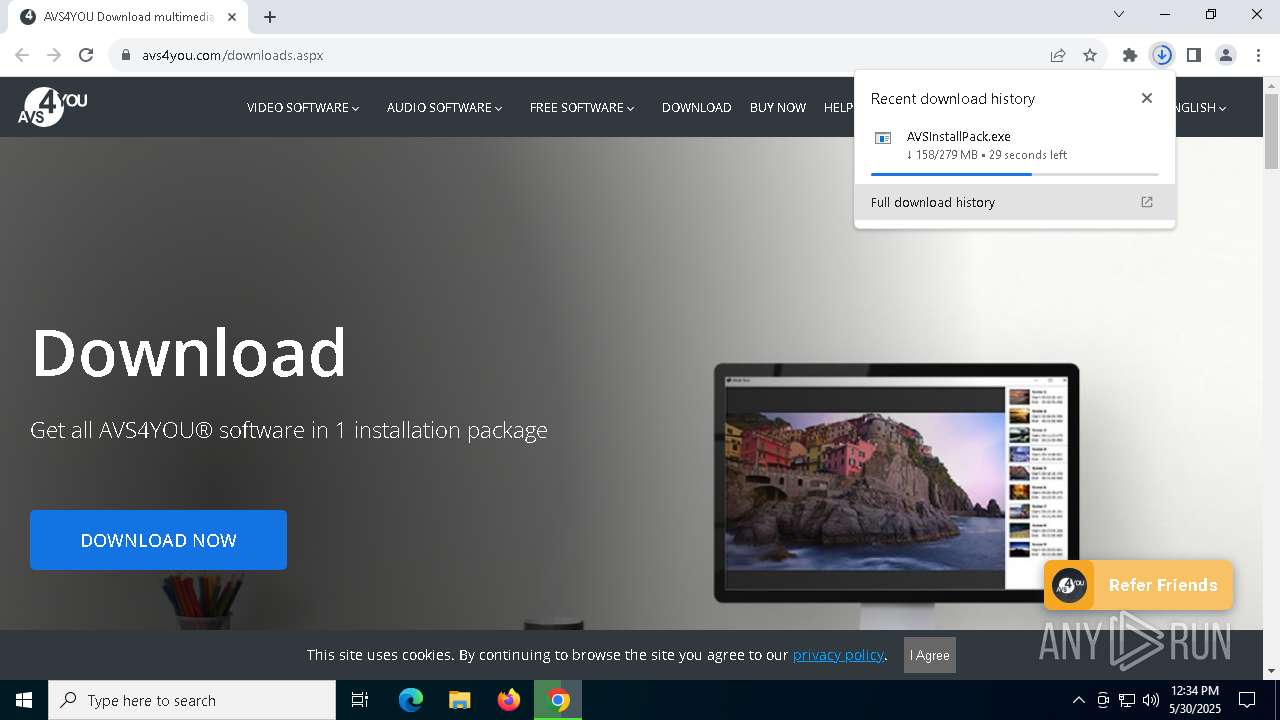
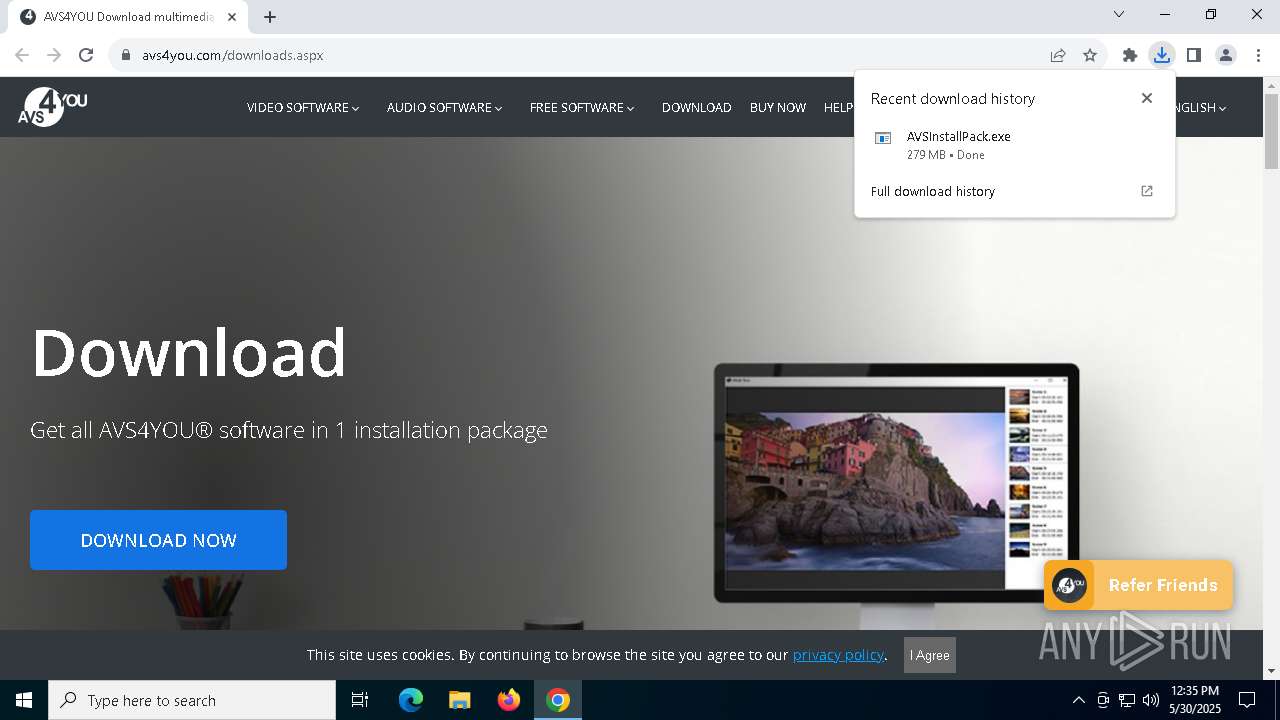
| URL: | https://www.avs4you.com/downloads.aspx |
| Full analysis: | https://app.any.run/tasks/190575fe-16e0-45f8-b261-6aba5a87bbcf |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2025, 12:33:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DEA0DF482D7BEB6EC39A450F8FB4AE27 |
| SHA1: | 1C14CE9D51ED7E95FB65762325B3E804B36C3E49 |
| SHA256: | 9C769195A2F15B83FA00558A55EA803119DD0D648CFBE5723CC0ACDDDA32D8BA |
| SSDEEP: | 3:N8DSL/ed38XL/3n:2OLmKj |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- AVSInstallPack.tmp (PID: 1240)
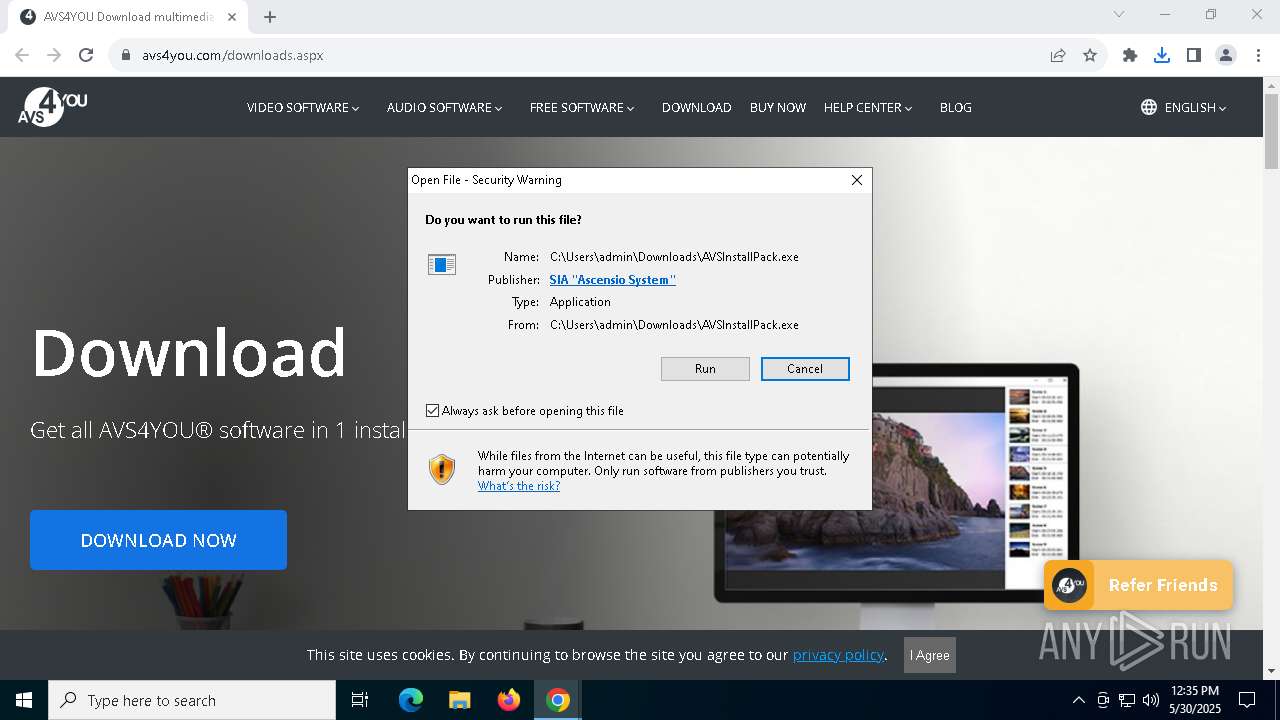
Executing a file with an untrusted certificate
- vcredist2005_x86.exe (PID: 5204)
- vcredist_x64.exe (PID: 7576)
Changes the autorun value in the registry
- vcredist2005_x86.exe (PID: 5204)
- vcredist_x64.exe (PID: 7576)
SUSPICIOUS
Executable content was dropped or overwritten
- AVSInstallPack.exe (PID: 1328)
- AVSInstallPack.exe (PID: 6592)
- vcredist2005_x86.exe (PID: 5204)
- TiWorker.exe (PID: 4200)
- vcredist_x64.exe (PID: 7576)
- vcredist2022_x86.exe (PID: 7144)
- AVSInstallPack.tmp (PID: 1240)
- vcredist2022_x86.exe (PID: 7732)
- VC_redist.x86.exe (PID: 6480)
- VC_redist.x86.exe (PID: 6108)
- AVSVideoConverter_light.tmp (PID: 7776)
- AVSVideoConverter_light.exe (PID: 7824)
- VC_redist.x86.exe (PID: 5084)
- AVSVideoEditor_light.exe (PID: 7576)
- AVSVideoEditor_light.tmp (PID: 4988)
Reads security settings of Internet Explorer
- AVSInstallPack.tmp (PID: 4068)
- AVSInstallPack.tmp (PID: 1240)
- vcredist2022_x86.exe (PID: 7732)
Reads the Windows owner or organization settings
- AVSInstallPack.tmp (PID: 1240)
- msiexec.exe (PID: 6760)
The process drops C-runtime libraries
- AVSInstallPack.tmp (PID: 1240)
- msiexec.exe (PID: 6760)
- TiWorker.exe (PID: 4200)
Process drops legitimate windows executable
- AVSInstallPack.tmp (PID: 1240)
- msiexec.exe (PID: 6760)
- TiWorker.exe (PID: 4200)
- vcredist2022_x86.exe (PID: 7144)
- VC_redist.x86.exe (PID: 5084)
- VC_redist.x86.exe (PID: 6480)
- vcredist2022_x86.exe (PID: 7732)
Searches for installed software
- AVSInstallPack.tmp (PID: 1240)
- vcredist2022_x86.exe (PID: 7732)
- VC_redist.x86.exe (PID: 6480)
- dllhost.exe (PID: 7804)
Starts a Microsoft application from unusual location
- vcredist2022_x86.exe (PID: 7732)
- VC_redist.x86.exe (PID: 6480)
Starts itself from another location
- vcredist2022_x86.exe (PID: 7732)
Executes as Windows Service
- VSSVC.exe (PID: 1116)
Application launched itself
- VC_redist.x86.exe (PID: 7892)
- VC_redist.x86.exe (PID: 6108)
INFO
Checks supported languages
- AVSInstallPack.exe (PID: 1328)
- AVSInstallPack.tmp (PID: 4068)
- AVSInstallPack.exe (PID: 6592)
- AVSInstallPack.tmp (PID: 1240)
- AVSInstLauncher.exe (PID: 5392)
- vcredist2005_x86.exe (PID: 5204)
- msiexec.exe (PID: 6760)
- msiexec.exe (PID: 2192)
- vcredist_x64.exe (PID: 7576)
- AVSInstLauncher.exe (PID: 7608)
- msiexec.exe (PID: 6192)
- AVSInstLauncher.exe (PID: 7936)
- vcredist2022_x86.exe (PID: 7144)
- vcredist2022_x86.exe (PID: 7732)
- VC_redist.x86.exe (PID: 6480)
Executable content was dropped or overwritten
- chrome.exe (PID: 6808)
- msiexec.exe (PID: 6760)
Application launched itself
- chrome.exe (PID: 6808)
Create files in a temporary directory
- AVSInstallPack.exe (PID: 1328)
- AVSInstallPack.exe (PID: 6592)
- AVSInstallPack.tmp (PID: 1240)
- vcredist2005_x86.exe (PID: 5204)
- vcredist_x64.exe (PID: 7576)
- vcredist2022_x86.exe (PID: 7732)
Reads the software policy settings
- slui.exe (PID: 7776)
- msiexec.exe (PID: 6760)
- slui.exe (PID: 6068)
Process checks computer location settings
- AVSInstallPack.tmp (PID: 4068)
- AVSInstallPack.tmp (PID: 1240)
- vcredist2022_x86.exe (PID: 7732)
Reads the computer name
- AVSInstallPack.tmp (PID: 4068)
- AVSInstallPack.tmp (PID: 1240)
- msiexec.exe (PID: 6760)
- msiexec.exe (PID: 2192)
- msiexec.exe (PID: 6192)
- VC_redist.x86.exe (PID: 6480)
- vcredist2022_x86.exe (PID: 7732)
Compiled with Borland Delphi (YARA)
- AVSInstallPack.tmp (PID: 4068)
- AVSInstallPack.exe (PID: 6592)
- AVSInstallPack.tmp (PID: 1240)
- AVSInstallPack.exe (PID: 1328)
Detects InnoSetup installer (YARA)
- AVSInstallPack.exe (PID: 6592)
- AVSInstallPack.exe (PID: 1328)
- AVSInstallPack.tmp (PID: 4068)
- AVSInstallPack.tmp (PID: 1240)
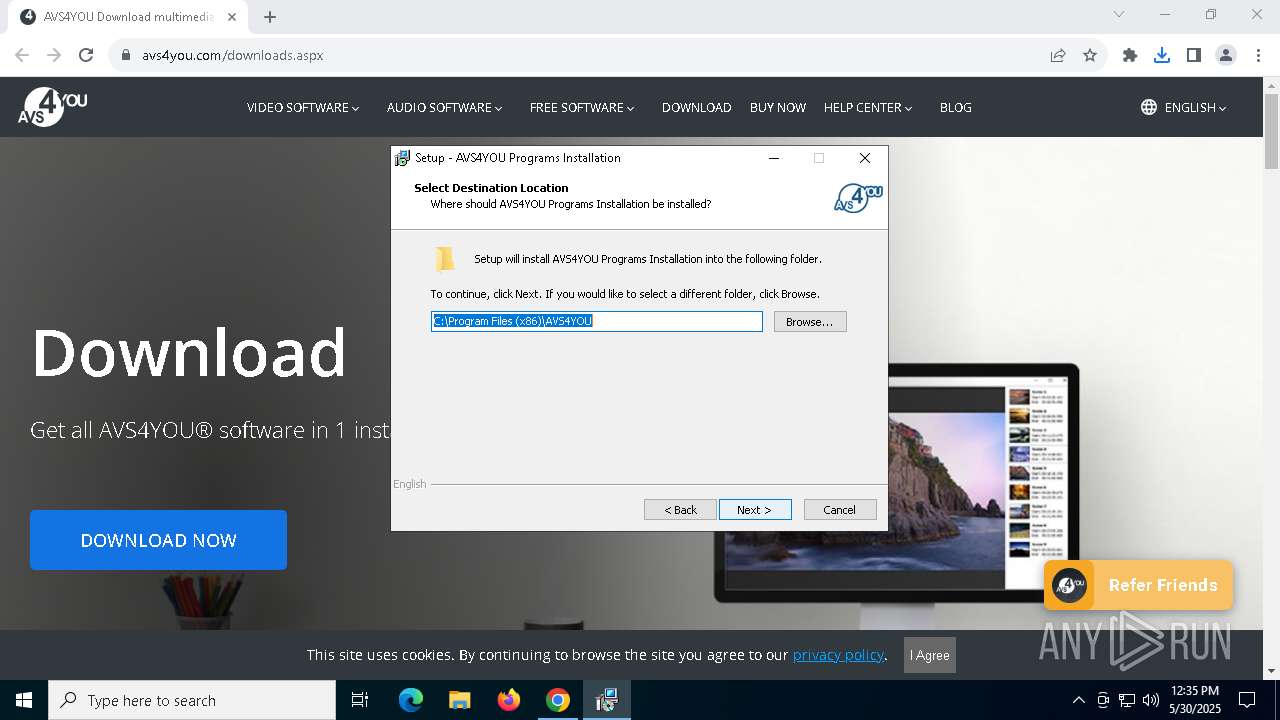
Creates files in the program directory
- AVSInstallPack.tmp (PID: 1240)
The sample compiled with english language support
- AVSInstallPack.tmp (PID: 1240)
- msiexec.exe (PID: 6760)
- TiWorker.exe (PID: 4200)
- vcredist2022_x86.exe (PID: 7144)
- vcredist2022_x86.exe (PID: 7732)
- VC_redist.x86.exe (PID: 6480)
- VC_redist.x86.exe (PID: 5084)
- VC_redist.x86.exe (PID: 6108)
- AVSVideoConverter_light.tmp (PID: 7776)
Launch of the file from Registry key
- vcredist2005_x86.exe (PID: 5204)
- vcredist_x64.exe (PID: 7576)
Creates files or folders in the user directory
- msiexec.exe (PID: 6760)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6760)
The sample compiled with french language support
- msiexec.exe (PID: 6760)
- TiWorker.exe (PID: 4200)
The sample compiled with spanish language support
- msiexec.exe (PID: 6760)
- TiWorker.exe (PID: 4200)
The sample compiled with german language support
- msiexec.exe (PID: 6760)
- TiWorker.exe (PID: 4200)
The sample compiled with chinese language support
- msiexec.exe (PID: 6760)
- TiWorker.exe (PID: 4200)
The sample compiled with japanese language support
- msiexec.exe (PID: 6760)
- TiWorker.exe (PID: 4200)
The sample compiled with Italian language support
- msiexec.exe (PID: 6760)
- TiWorker.exe (PID: 4200)
Creates a software uninstall entry
- msiexec.exe (PID: 6760)
Checks proxy server information
- slui.exe (PID: 6068)
The sample compiled with korean language support
- TiWorker.exe (PID: 4200)
- msiexec.exe (PID: 6760)
Manages system restore points
- SrTasks.exe (PID: 5756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
193
Monitored processes
49
Malicious processes
8
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1116 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | "C:\Users\admin\AppData\Local\Temp\is-GF9UR.tmp\AVSInstallPack.tmp" /SL5="$802CC,292279396,121344,C:\Users\admin\Downloads\AVSInstallPack.exe" /SPAWNWND=$C02D4 /NOTIFYWND=$A00BE | C:\Users\admin\AppData\Local\Temp\is-GF9UR.tmp\AVSInstallPack.tmp | AVSInstallPack.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
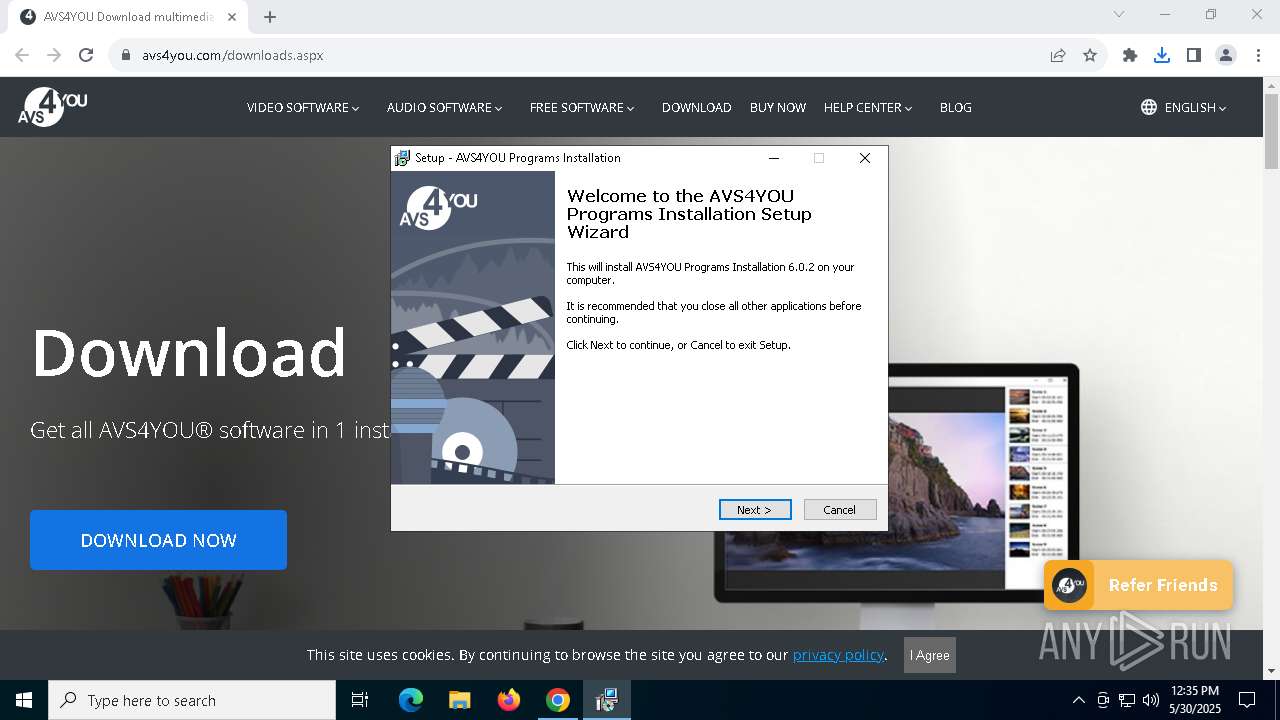
| 1328 | "C:\Users\admin\Downloads\AVSInstallPack.exe" | C:\Users\admin\Downloads\AVSInstallPack.exe | chrome.exe | ||||||||||||
User: admin Company: Ascensio System SIA Integrity Level: MEDIUM Description: AVS4YOU Programs Installation 6.0.2 Version: 6.0.2.21 Modules
| |||||||||||||||
| 2192 | C:\Windows\syswow64\MsiExec.exe -Embedding 2830329DDF14B2E0B2F6AE51C90B1C58 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4068 | "C:\Users\admin\AppData\Local\Temp\is-PGM8B.tmp\AVSInstallPack.tmp" /SL5="$A00BE,292279396,121344,C:\Users\admin\Downloads\AVSInstallPack.exe" | C:\Users\admin\AppData\Local\Temp\is-PGM8B.tmp\AVSInstallPack.tmp | — | AVSInstallPack.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
| 4200 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x204,0x228,0x7ffc88e2dc40,0x7ffc88e2dc4c,0x7ffc88e2dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4988 | "C:\Users\admin\AppData\Local\Temp\is-UQ4GU.tmp\AVSVideoEditor_light.tmp" /SL5="$A02CA,127348847,121344,C:\Users\admin\AppData\Local\Temp\is-31H6H.tmp\AVS4YOU\AVSVideoEditor_light.exe" /VERYSILENT /SUPPRESSMSGBOXES /GROUP="AVS4YOU" /LANG=en /DIR="C:\Program Files (x86)\AVS4YOU\AVSVideoEditor\" /TASKS=!desktopicon,installshext,sampleproject,systemwindowframe | C:\Users\admin\AppData\Local\Temp\is-UQ4GU.tmp\AVSVideoEditor_light.tmp | AVSVideoEditor_light.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
| 5084 | "C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{4DA9C346-EA43-436F-B848-F8F5FE34B92E} {660C7601-2128-40F9-9665-E57E00C9039B} 6108 | C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 5164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5828 --field-trial-handle=1912,i,13601385864809775341,3005375034325781904,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
31 500
Read events
28 694
Write events
2 397
Delete events
409
Modification events
| (PID) Process: | (6808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6808) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (6808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (6808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (6808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (6808) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
594
Suspicious files
258
Text files
2 594
Unknown types
103
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c296.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c296.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c2a6.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c2a6.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c2a6.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
100
DNS requests
107
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1312 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7232 | chrome.exe | GET | 200 | 192.124.249.41:80 | http://certificates.godaddy.com/repository/gdig2.crt | unknown | — | — | whitelisted |
1312 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7728 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
7232 | chrome.exe | GET | 200 | 192.124.249.41:80 | http://certificates.godaddy.com/repository/gdig2.crt | unknown | — | — | whitelisted |
7728 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
7728 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.32.238.112:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7232 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6808 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7232 | chrome.exe | 18.245.31.25:443 | www.avs4you.com | — | US | whitelisted |
7232 | chrome.exe | 192.124.249.41:80 | certificates.godaddy.com | SUCURI-SEC | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.avs4you.com |
| whitelisted |
accounts.google.com |
| whitelisted |
certificates.godaddy.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
secure.avangate.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7232 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7232 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7232 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7232 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7232 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7232 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |