| File name: | Pensionskasse SHP_858151174_11.12.2018.docx |
| Full analysis: | https://app.any.run/tasks/b23db689-8174-4c47-9085-17d4684ef902 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 08:13:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7EAB6D83E7AE505D9AEDDECFBD51972B |
| SHA1: | 5DC30125F61AED479FD3A8F00178EAD0F9DBB7DC |
| SHA256: | 9C73EB4894133262BF0094E865A9855B7278062D4792E657C96ABA009D0FCA75 |
| SSDEEP: | 1536:j/ZSUZUCPuuBQoB9WEp20e5cvqbEOqefd6sAMEVycvjp3o6S4:j/ZZZnuymx0e6CbRd6pMrcve6S4 |
MALICIOUS
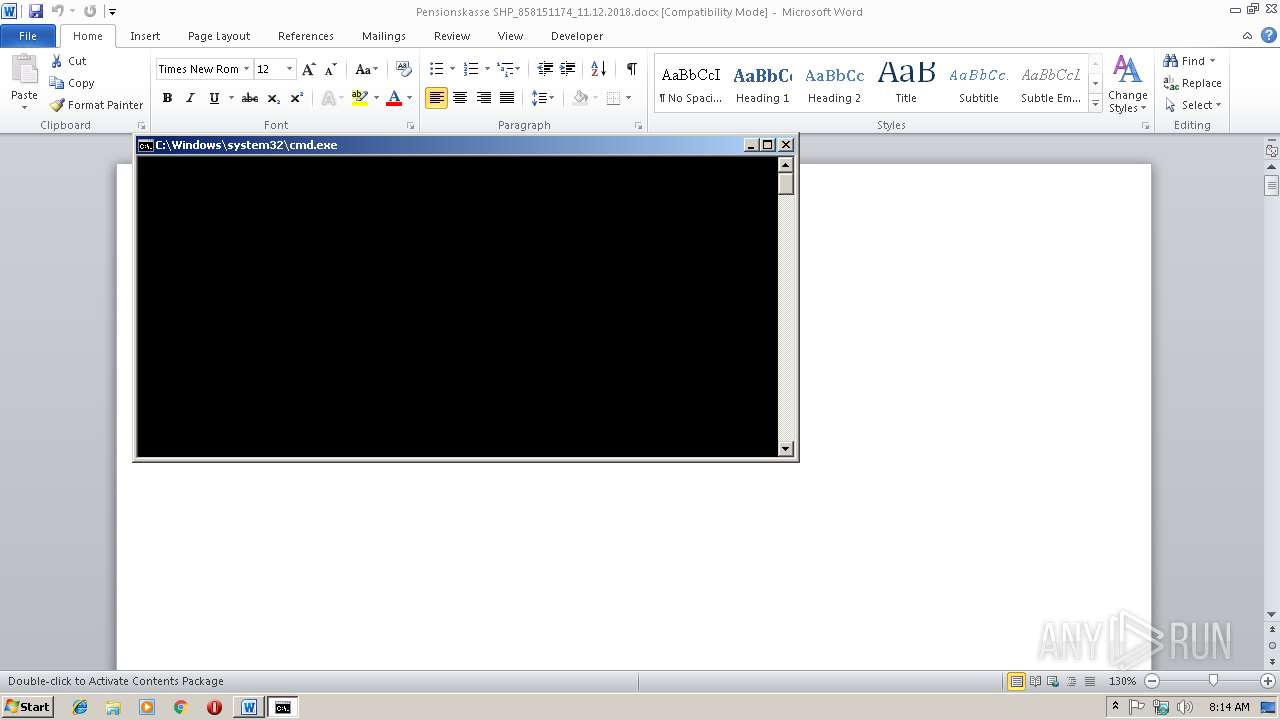
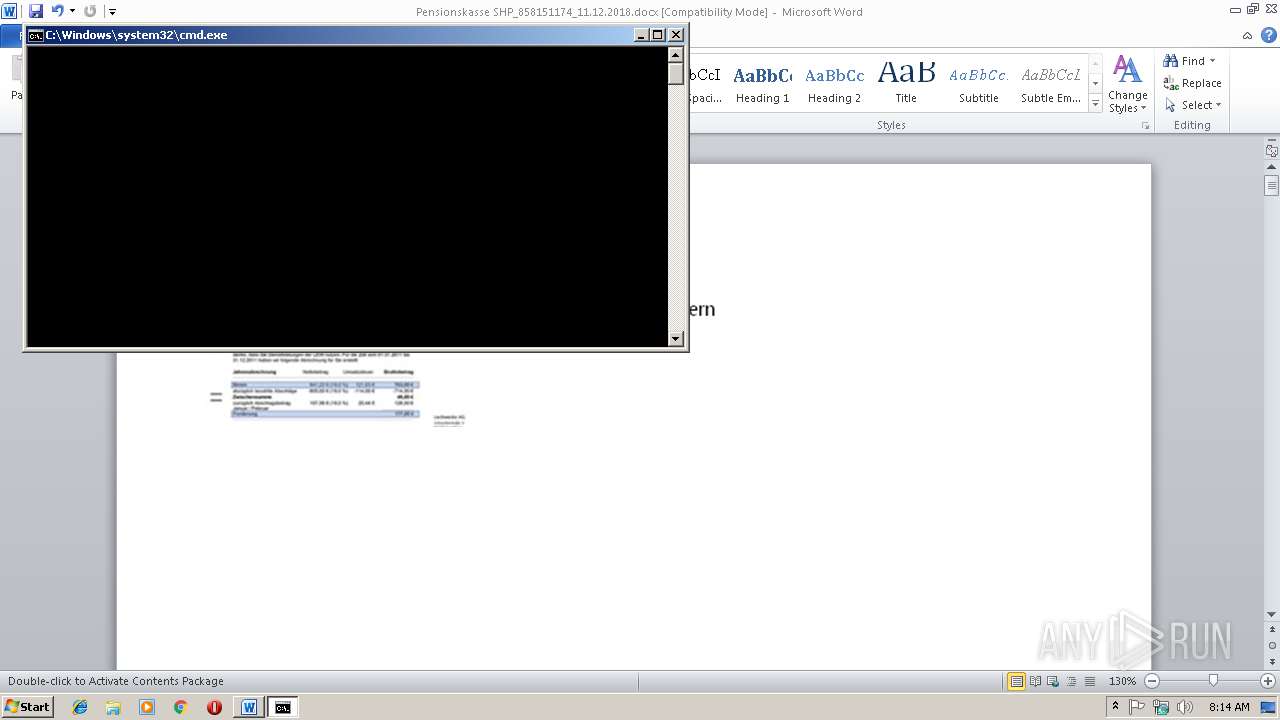
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2968)
Executes PowerShell scripts
- cmd.exe (PID: 3796)
- cmd.exe (PID: 3064)
- cmd.exe (PID: 3584)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 2836)
- cmd.exe (PID: 1428)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2968)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 3064)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3064)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 1428)
Creates files in the user directory
- powershell.exe (PID: 4000)
- powershell.exe (PID: 3156)
- powershell.exe (PID: 3828)
- powershell.exe (PID: 3092)
- powershell.exe (PID: 2720)
- powershell.exe (PID: 4012)
Executes scripts
- cmd.exe (PID: 3064)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 1428)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2968)
Creates files in the user directory
- WINWORD.EXE (PID: 2968)
Dropped object may contain TOR URL's
- powershell.exe (PID: 3156)
- powershell.exe (PID: 3092)
- powershell.exe (PID: 4012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:11 12:44:03 |
| ZipCRC: | 0x83f7eeea |
| ZipCompressedSize: | 1430 |
| ZipUncompressedSize: | 6507 |
| ZipFileName: | word/document.xml |
XMP
| Title: | Pensionskasse SHP N858151174 |
|---|---|
| Subject: | Pensionskasse SHP N858151174 |
| Creator: | Prof. Alice Kramer |
| Description: | Consequuntur accusamus quibusdam architecto rem perferendis laborum minima quae. |
XML
| Keywords: | fugiat, esse, voluptatem |
|---|---|
| LastModifiedBy: | Prof. Alice Kramer |
| RevisionNumber: | 322092 |
| CreateDate: | 2018:12:08 17:21:01Z |
| ModifyDate: | 2018:12:08 17:21:01Z |
| Category: | deleniti |
| Template: | Normal |
| Pages: | 72 |
| Words: | 24249 |
| Characters: | 315237 |
| CharactersWithSpaces: | 315237 |
| Application: | Microsoft Office Word |
| Lines: | 4515 |
| Paragraphs: | 388 |
| Manager: | Silvio Kuhl |
| Company: | Röhrdanz |
| AppVersion: | 12 |
Total processes
50
Monitored processes
16
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Windowseigener Bildviewer.cmd" " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2228 | wscript C:\Users\admin\AppData\Local\Temp\IKqYxwfzUpy.js | C:\Windows\system32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2384 | wscript C:\Users\admin\AppData\Local\Temp\xAY9mUbvF.js | C:\Windows\system32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2720 | powershell -w hidden -Command "(-join ((48..57)+(65..90)+(97..122) | Get-Random -Count (Get-Random -minimum 5 -maximum 15) | % {[char]$_}))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2836 | C:\Windows\system32\cmd.exe /c powershell -w hidden -Command "(-join ((48..57)+(65..90)+(97..122) | Get-Random -Count (Get-Random -minimum 5 -maximum 15) | % {[char]$_}))" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2880 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Windowseigener Bildviewer.cmd" " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Pensionskasse SHP_858151174_11.12.2018.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2992 | wscript C:\Users\admin\AppData\Local\Temp\cLnvqfARxk7.js | C:\Windows\system32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3064 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Windowseigener Bildviewer.cmd" " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3092 | powershell -WindowStyle hidden -c "[IO.File]::WriteAllBytes($env:IZEivcCTHc, [System.Convert]::FromBase64String([IO.File]::ReadAllText($env:IZEivcCTHc)));" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 620
Read events
1 922
Write events
693
Delete events
5
Modification events
| (PID) Process: | (2968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | '#0 |
Value: 27233000980B0000010000000000000000000000 | |||
| (PID) Process: | (2968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2968) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1311440917 | |||
| (PID) Process: | (2968) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311441036 | |||
| (PID) Process: | (2968) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311441037 | |||
| (PID) Process: | (2968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 980B00000E42BE9B85A9D40100000000 | |||
| (PID) Process: | (2968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 1$0 |
Value: 31243000980B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 1$0 |
Value: 31243000980B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2968) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
12
Text files
116
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6707.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2968 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\mso691C.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\557C7180.jpeg | — | |
MD5:— | SHA256:— | |||
| 4000 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZDXIWT3AWA64R50BXPUR.temp | — | |
MD5:— | SHA256:— | |||
| 3156 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Q2RYGI2NMDVQC5T1HJDJ.temp | — | |
MD5:— | SHA256:— | |||
| 3828 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KFUX8DG4IOTW369B7DO9.temp | — | |
MD5:— | SHA256:— | |||
| 3092 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZW3W8WXLX51I4NE39C80.temp | — | |
MD5:— | SHA256:— | |||
| 2720 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OAEMSA6M6LUL14N3S35Q.temp | — | |
MD5:— | SHA256:— | |||
| 2968 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2968 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Windowseigener Bildviewer.cmd | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report