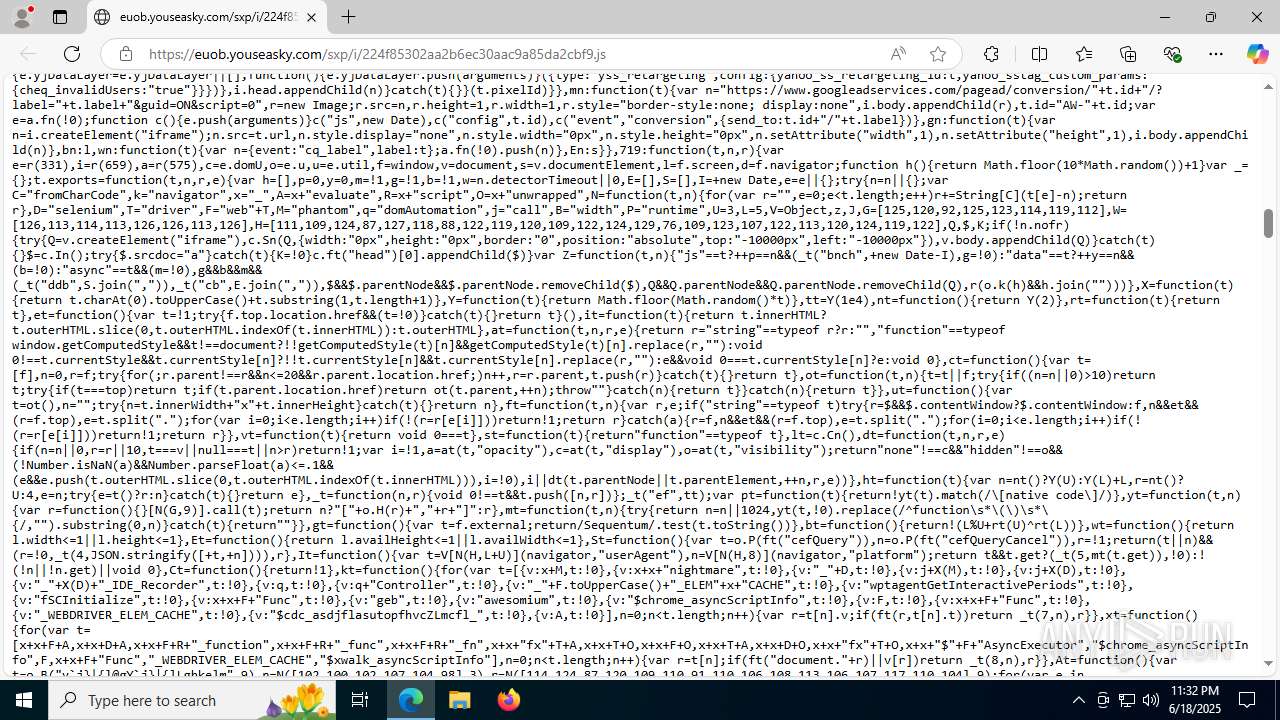
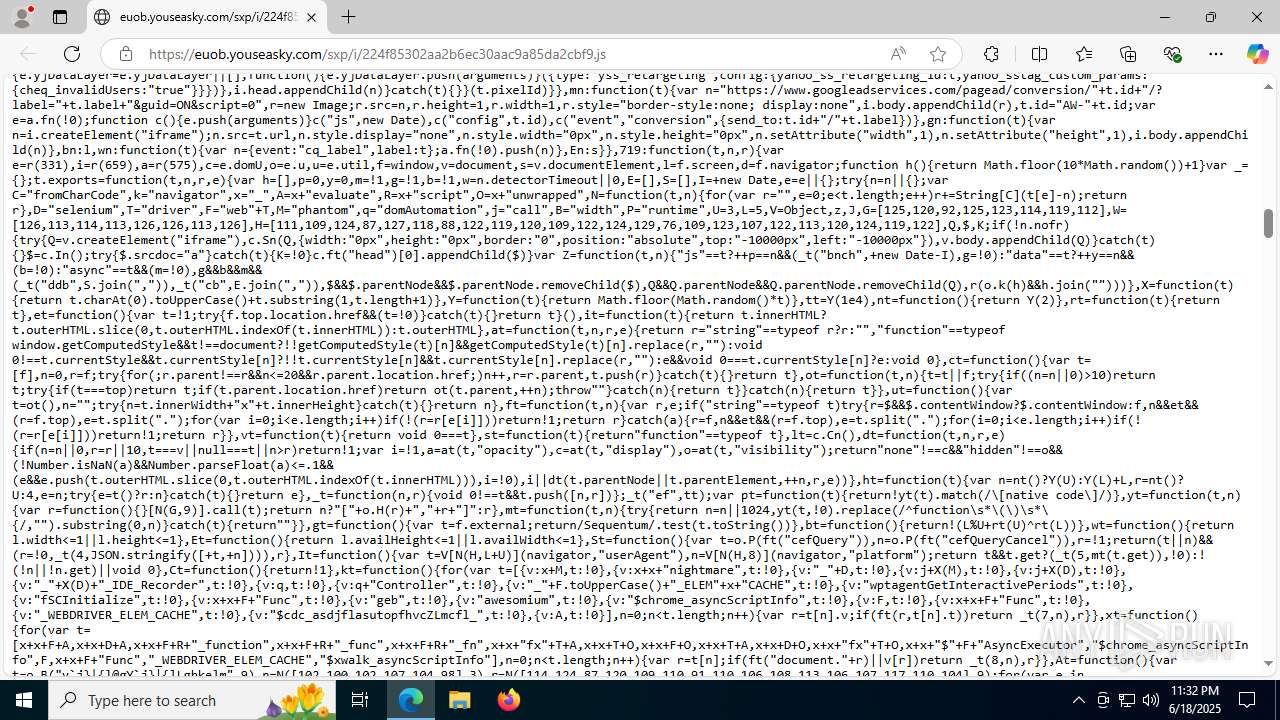
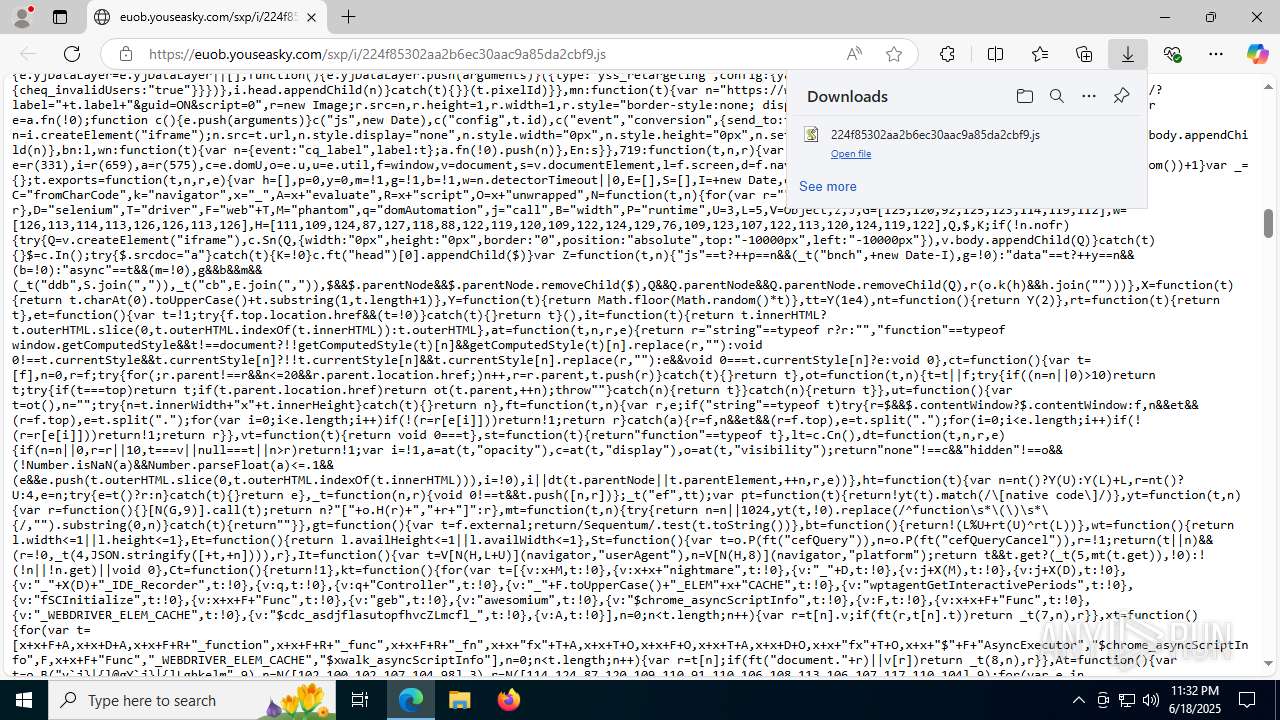
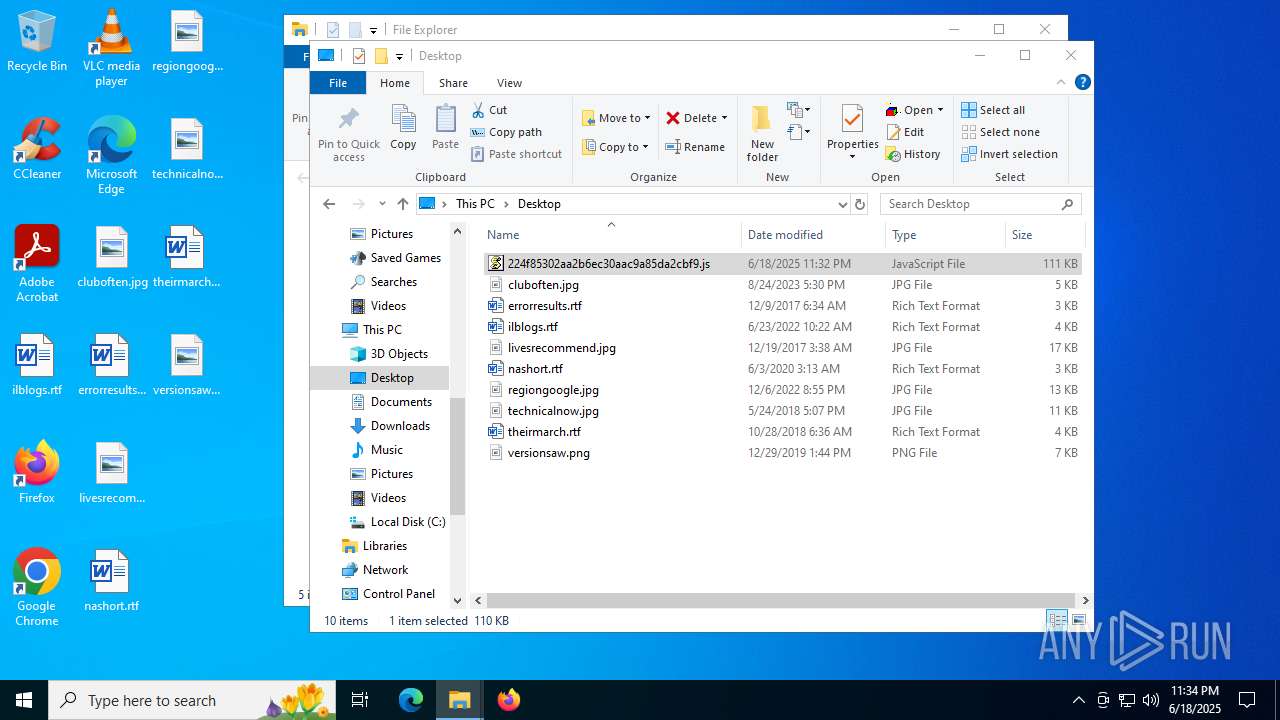
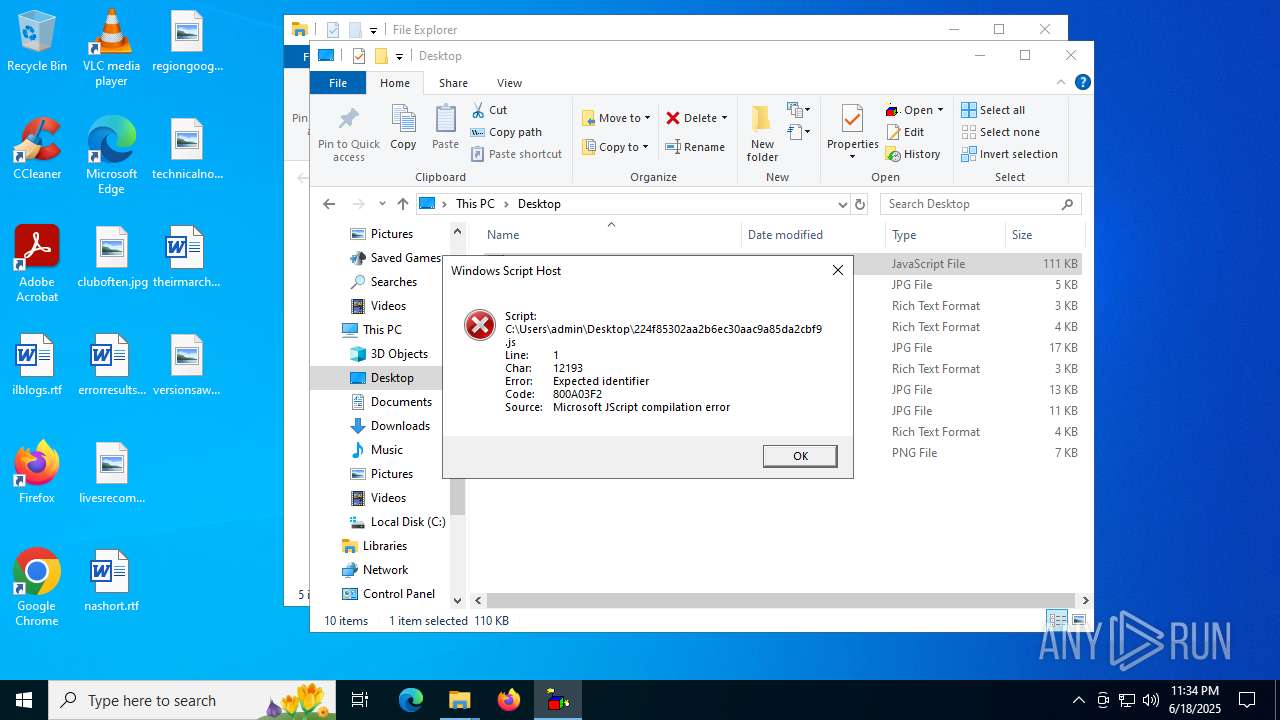
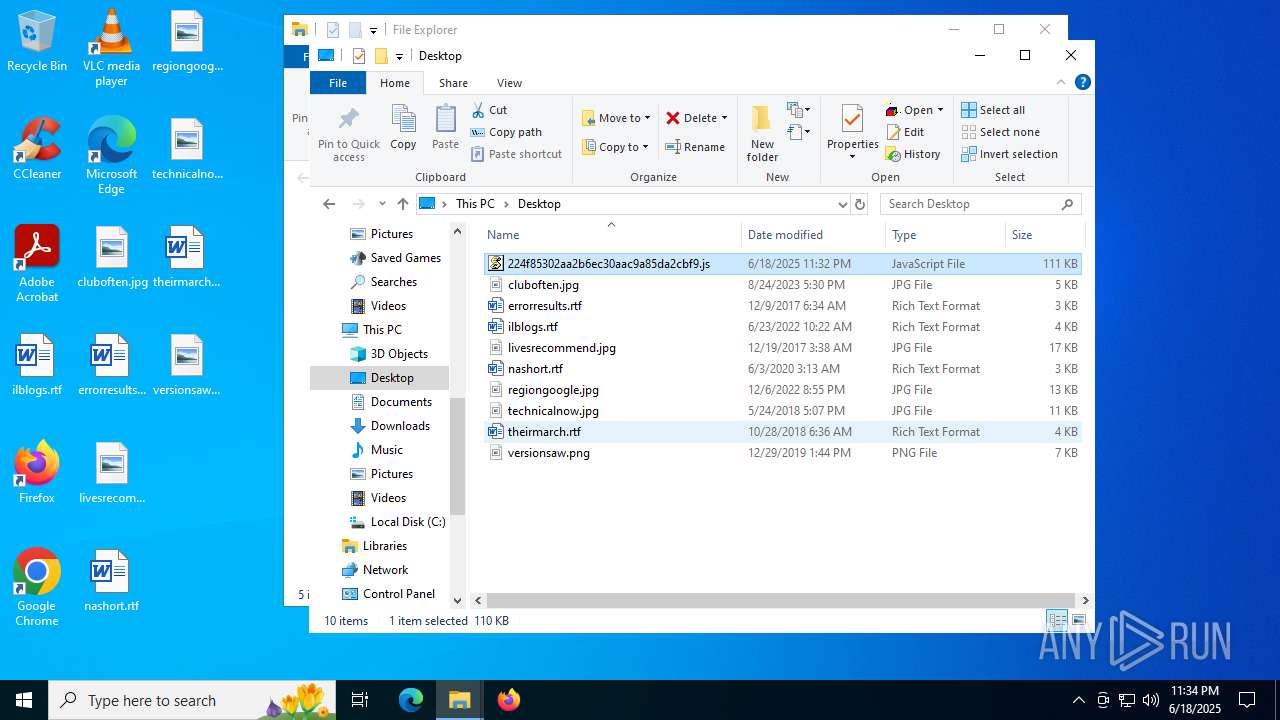
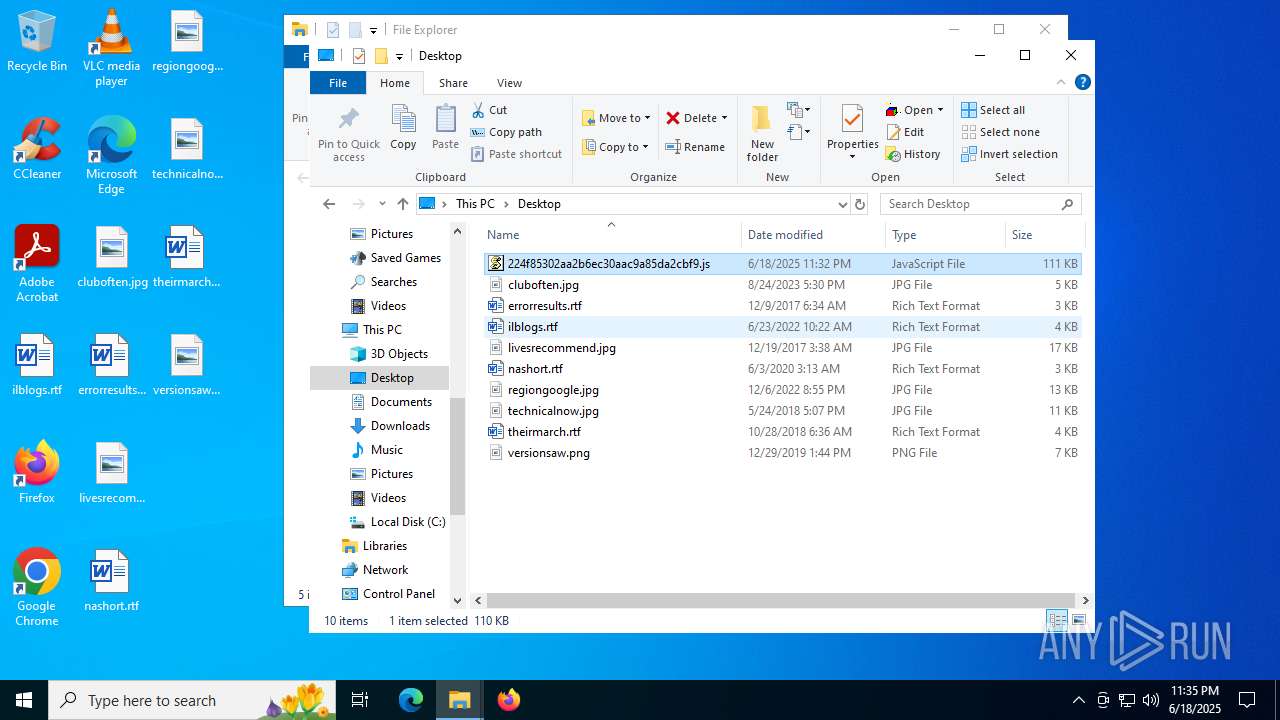
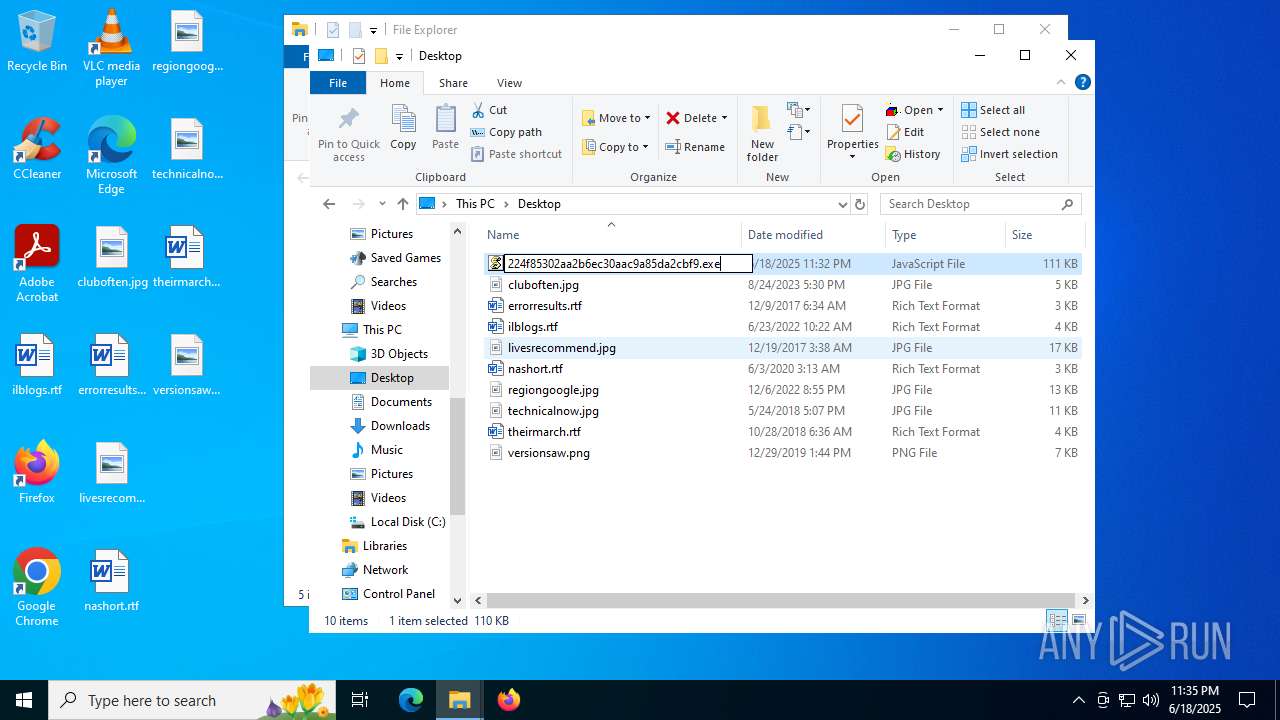
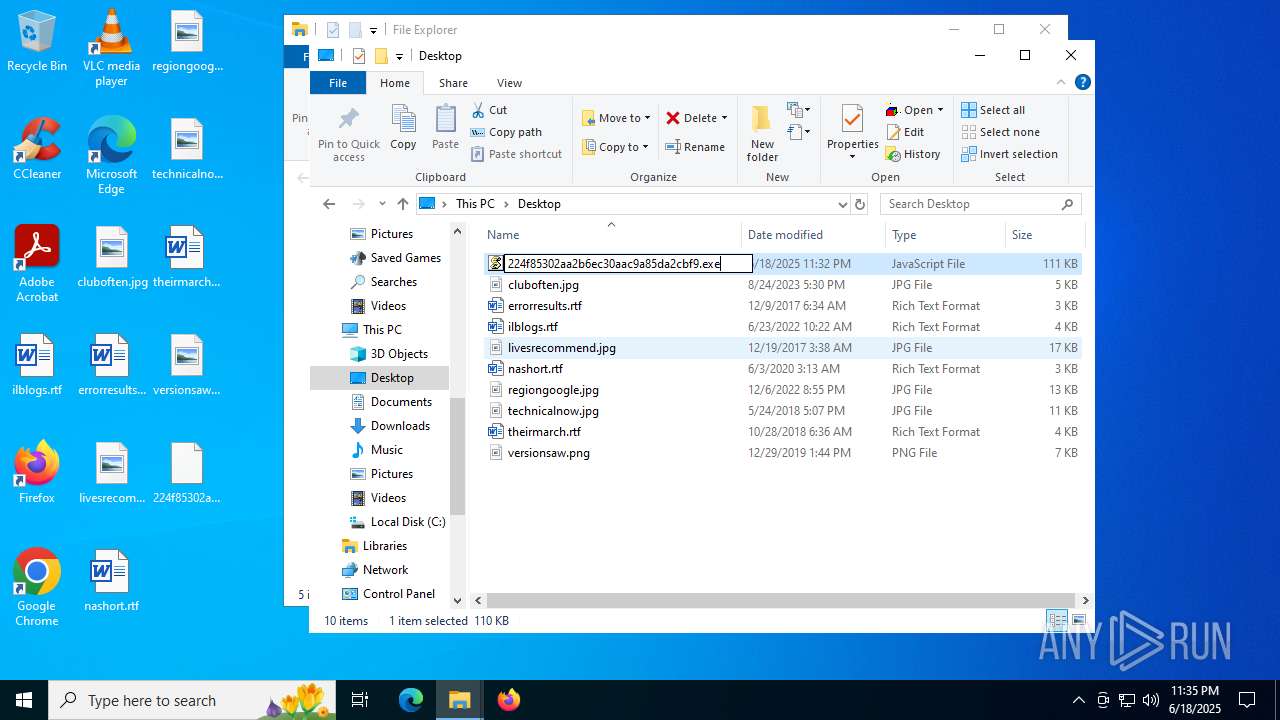
| URL: | https://euob.youseasky.com/sxp/i/224f85302aa2b6ec30aac9a85da2cbf9.js |
| Full analysis: | https://app.any.run/tasks/76d00fe4-2b28-4c53-91b3-30df51cbda1a |
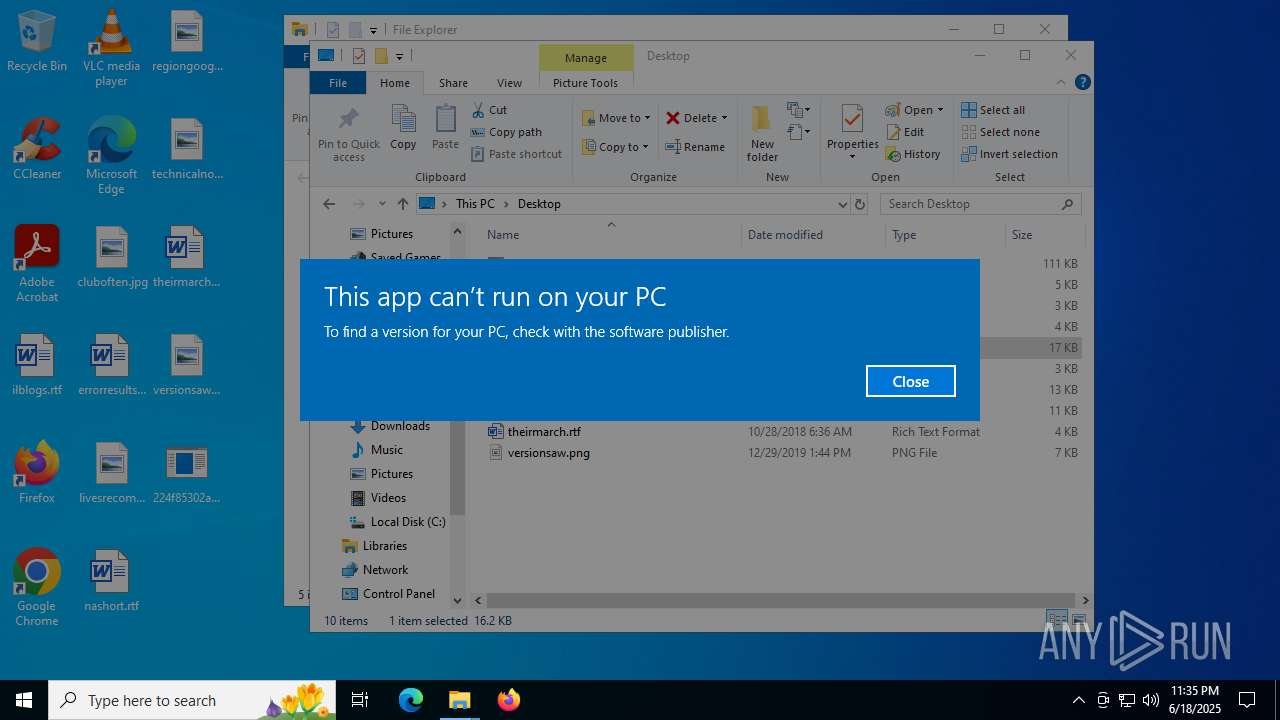
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2025, 23:31:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 55A77A1E8263E7196D6440E812FE7C0F |
| SHA1: | 28D425439E3CEF70276D8181866C4637034C68AE |
| SHA256: | 9C72D972BD85C1BFD5E63EBAD76F26E9D77A496A163751C80335A0E18DFE310C |
| SSDEEP: | 3:N8iIbGTKaJKHwkEE3MEXGOun:2iIyTPJKHwkt3M+GOu |
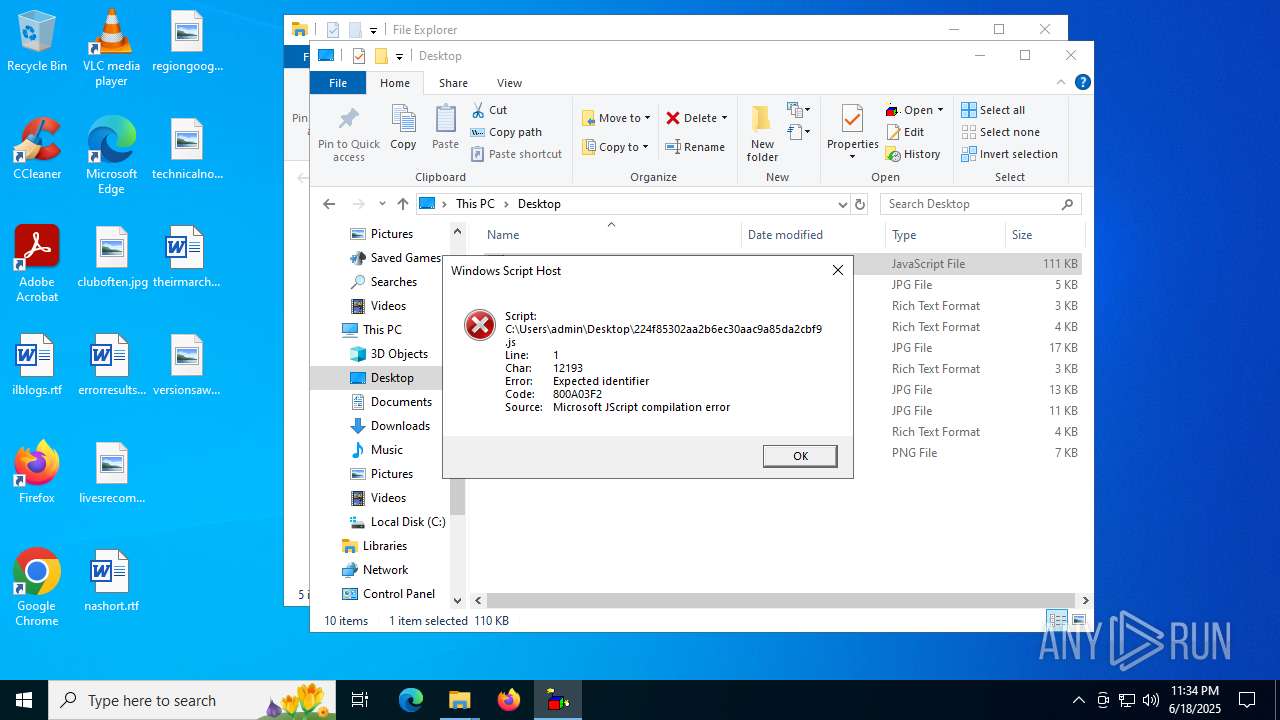
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 768)
- wscript.exe (PID: 1720)
SUSPICIOUS
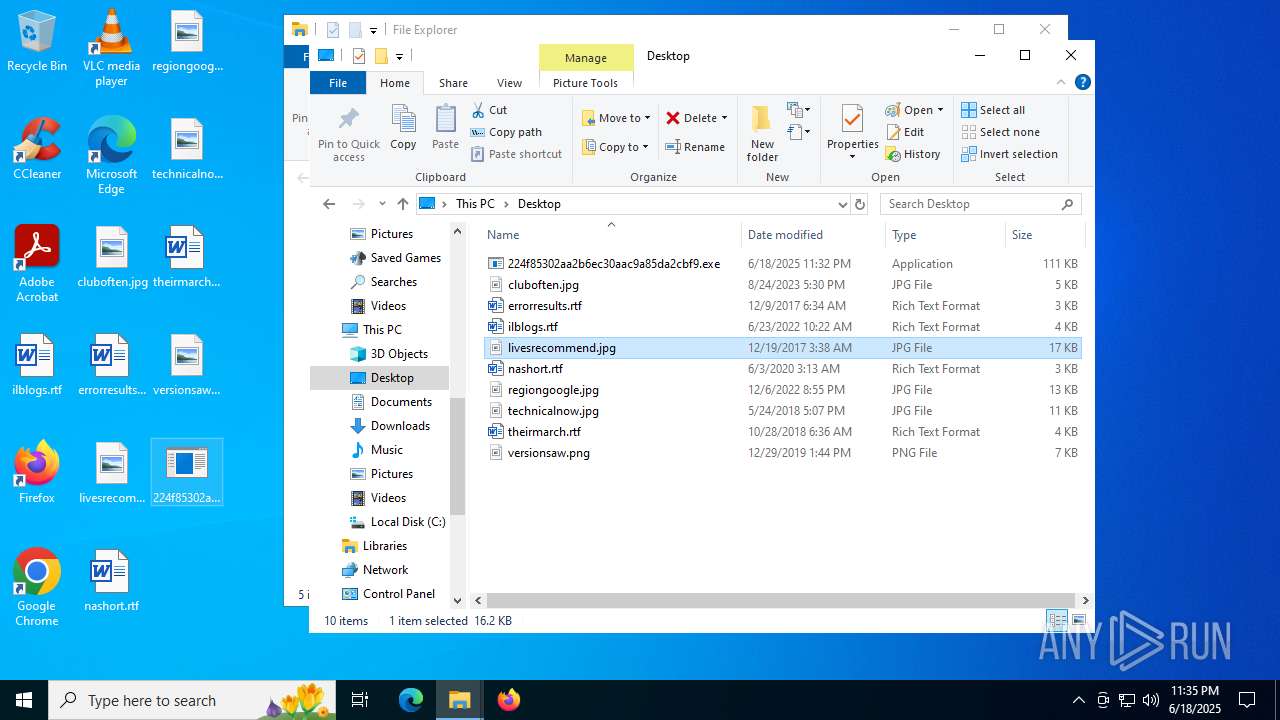
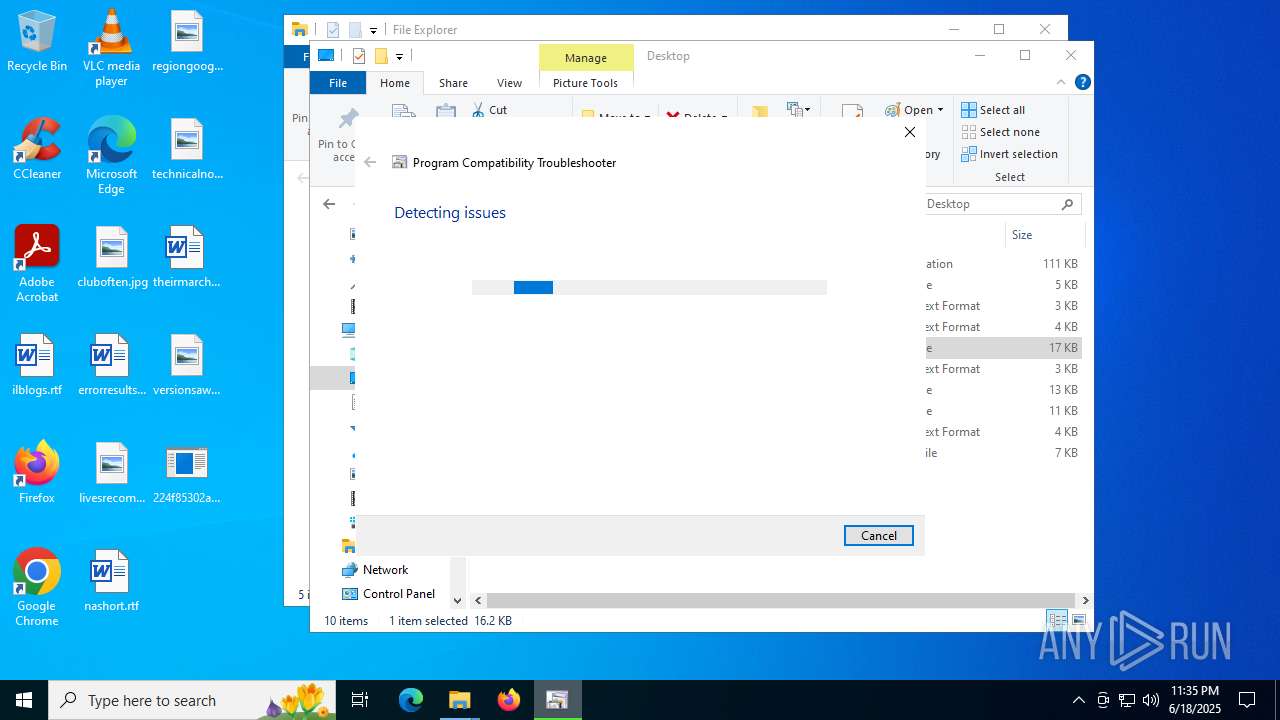
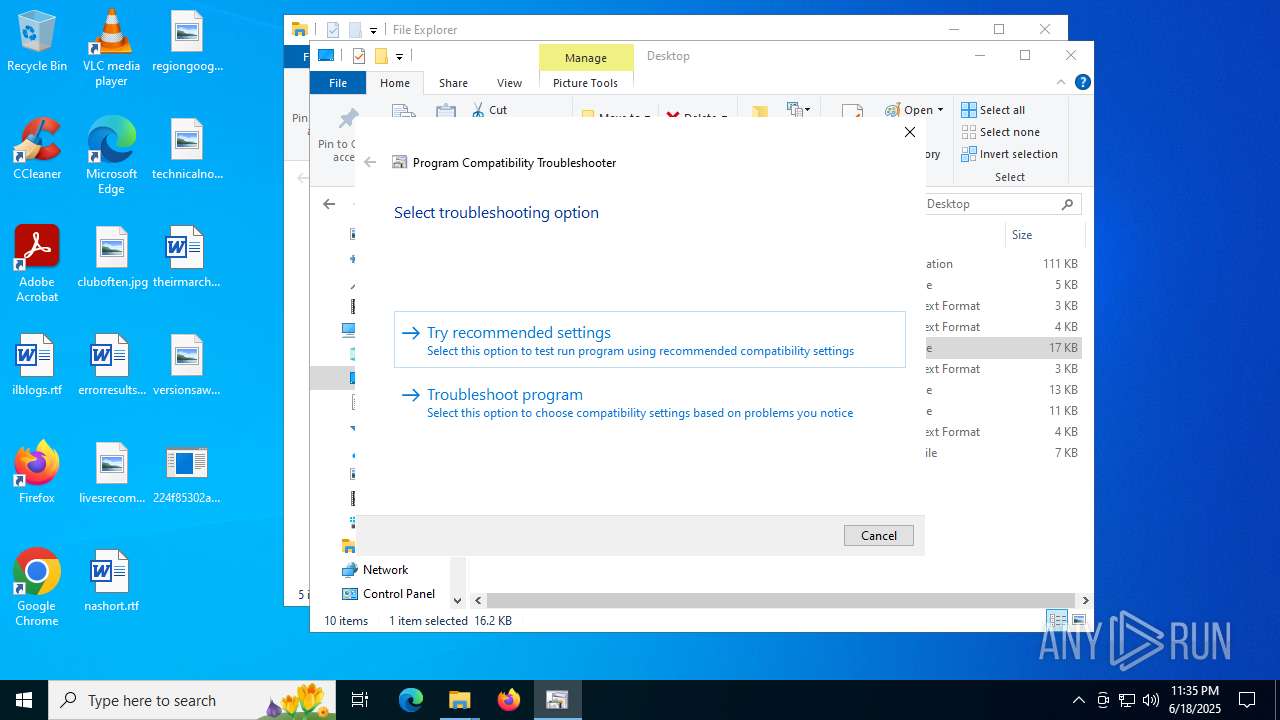
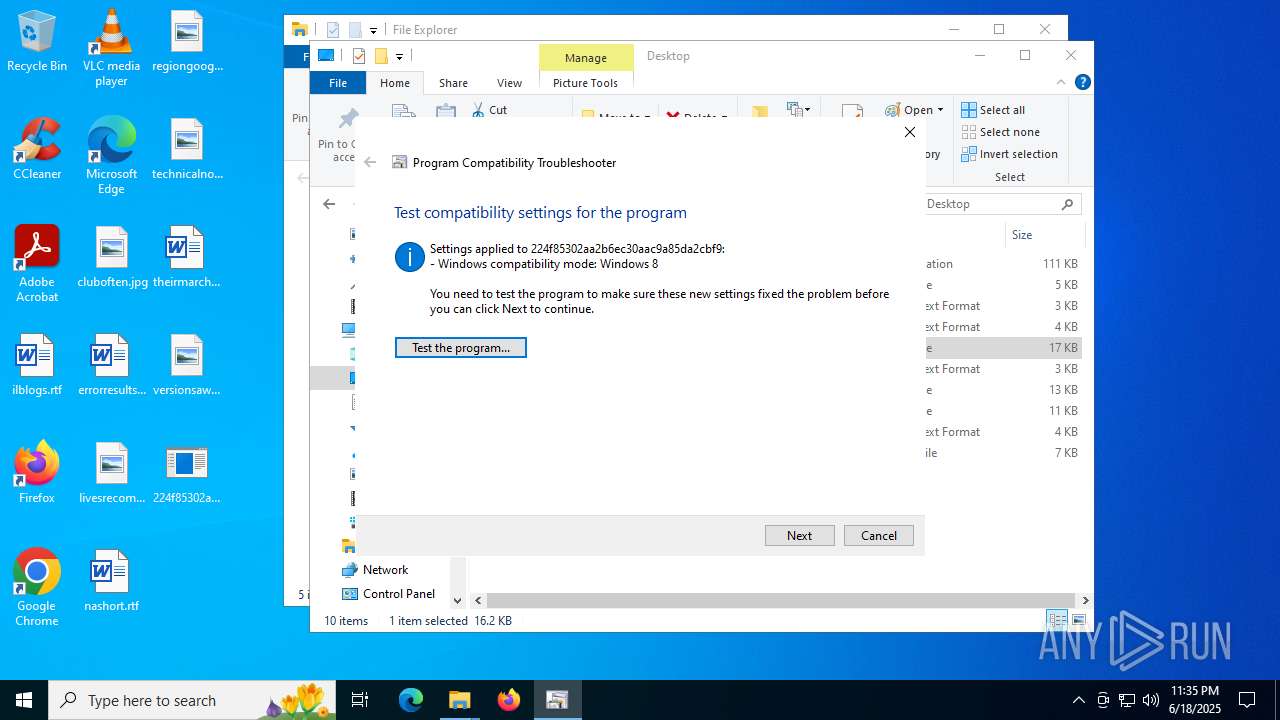
Probably uses Microsoft diagnostics tool to execute malicious payload
- pcwrun.exe (PID: 6772)
Executable content was dropped or overwritten
- csc.exe (PID: 2144)
- csc.exe (PID: 7324)
- csc.exe (PID: 8108)
Converts a string into array of characters (POWERSHELL)
- sdiagnhost.exe (PID: 7128)
Gets file extension (POWERSHELL)
- sdiagnhost.exe (PID: 7128)
Uses RUNDLL32.EXE to load library
- msdt.exe (PID: 5708)
INFO
Reads Environment values
- identity_helper.exe (PID: 4664)
- identity_helper.exe (PID: 7504)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5328)
- csc.exe (PID: 2144)
- csc.exe (PID: 7324)
- csc.exe (PID: 8108)
Checks supported languages
- identity_helper.exe (PID: 7504)
- identity_helper.exe (PID: 4664)
- SearchApp.exe (PID: 5328)
- csc.exe (PID: 2144)
- cvtres.exe (PID: 1740)
- cvtres.exe (PID: 4692)
- csc.exe (PID: 7324)
- csc.exe (PID: 8108)
- cvtres.exe (PID: 7548)
Checks proxy server information
- slui.exe (PID: 7372)
- sdiagnhost.exe (PID: 7128)
Application launched itself
- msedge.exe (PID: 7796)
- msedge.exe (PID: 6620)
Reads the computer name
- identity_helper.exe (PID: 7504)
- identity_helper.exe (PID: 4664)
Reads the software policy settings
- SearchApp.exe (PID: 5328)
- slui.exe (PID: 7372)
- msdt.exe (PID: 5708)
- sdiagnhost.exe (PID: 7128)
Process checks computer location settings
- SearchApp.exe (PID: 5328)
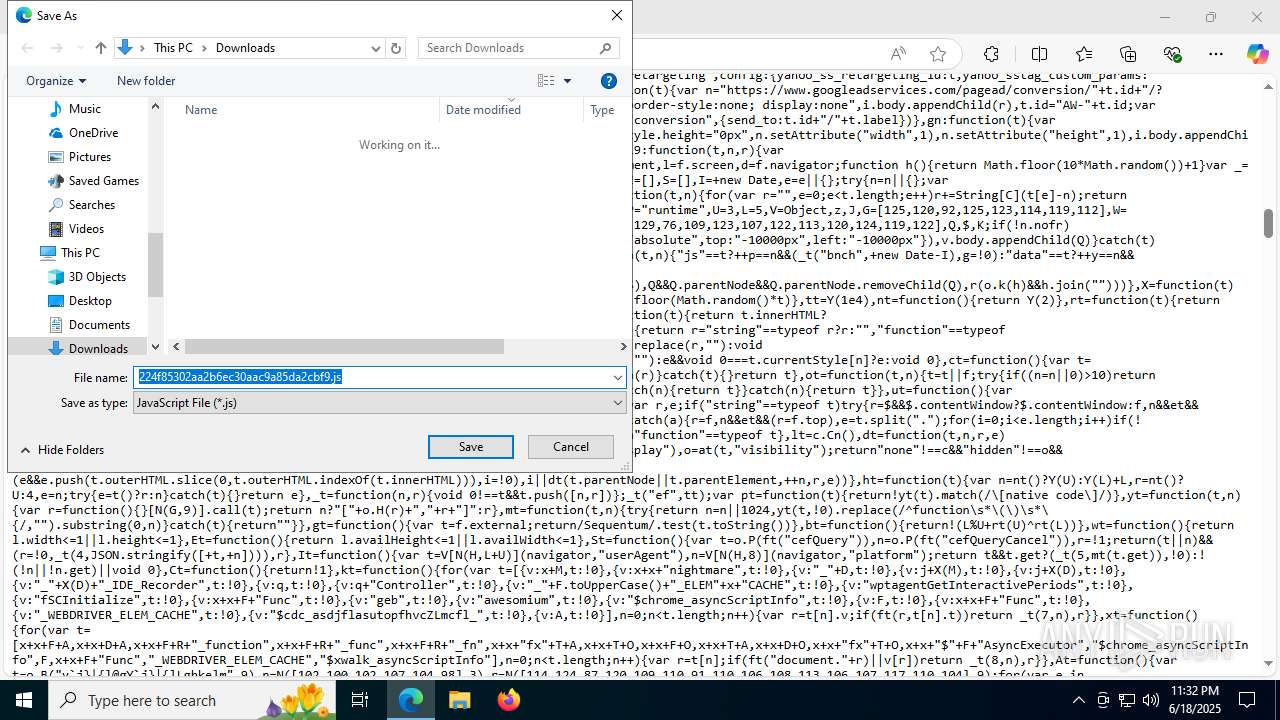
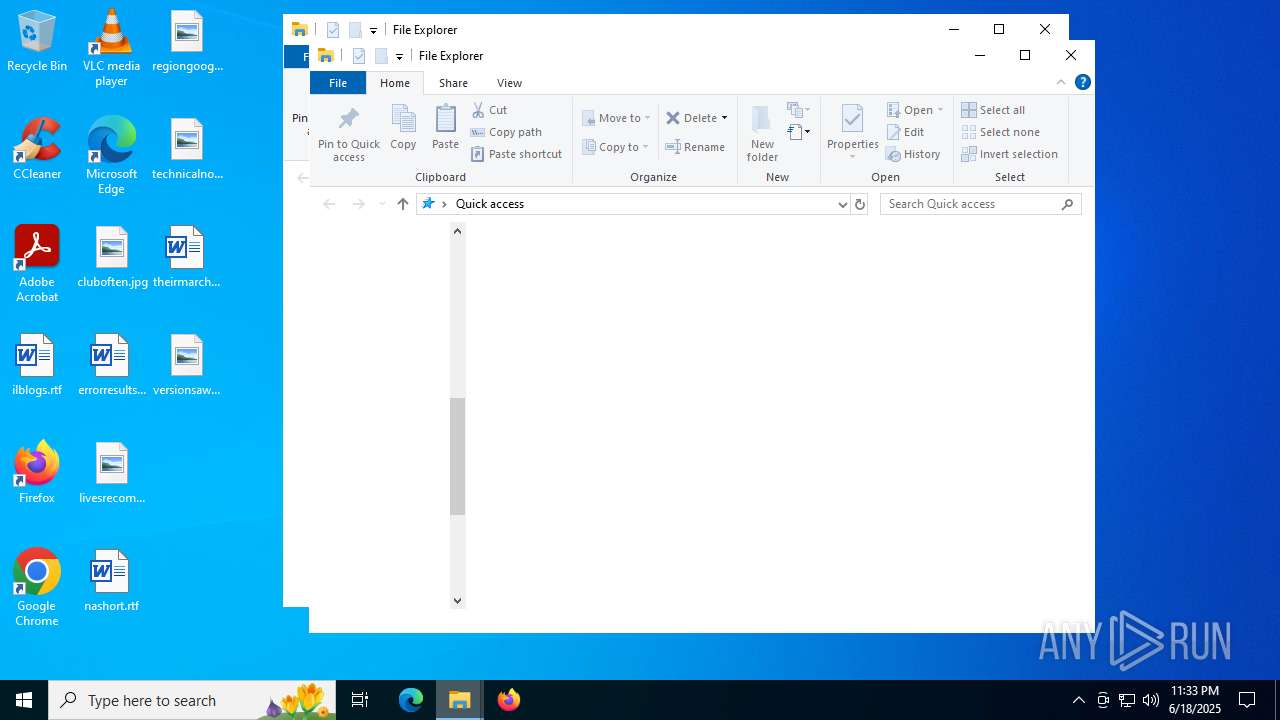
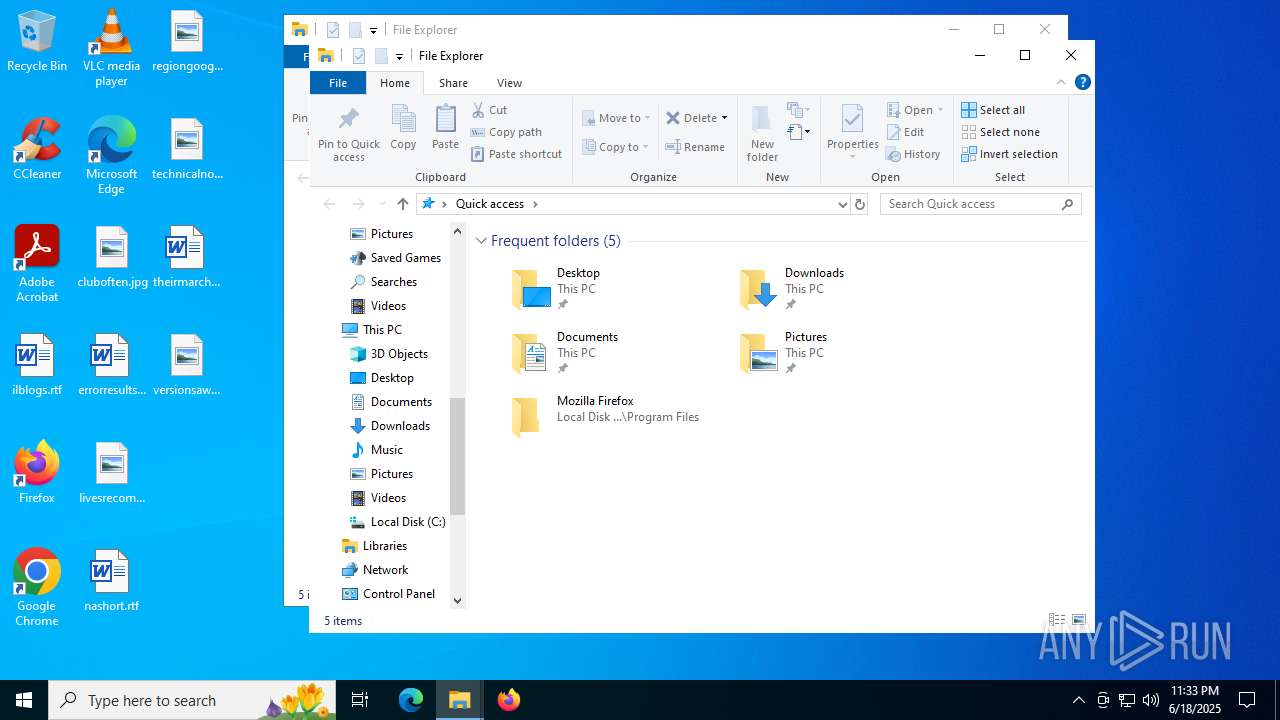
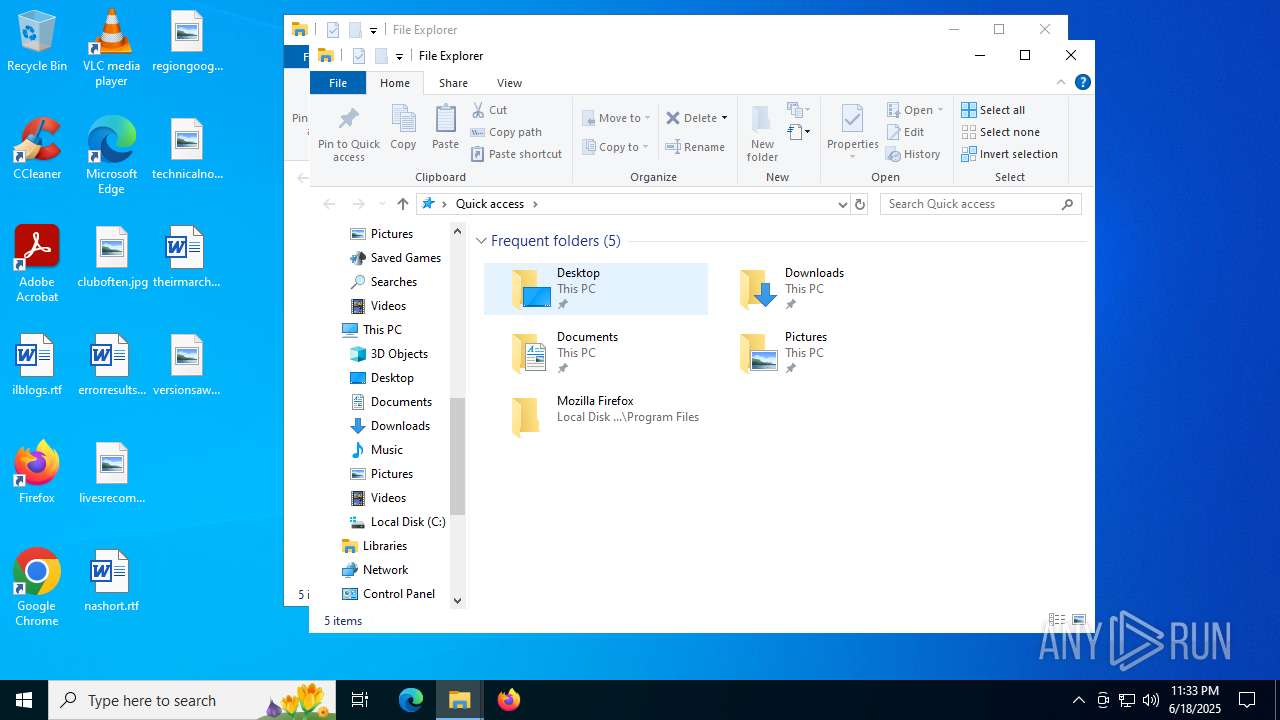
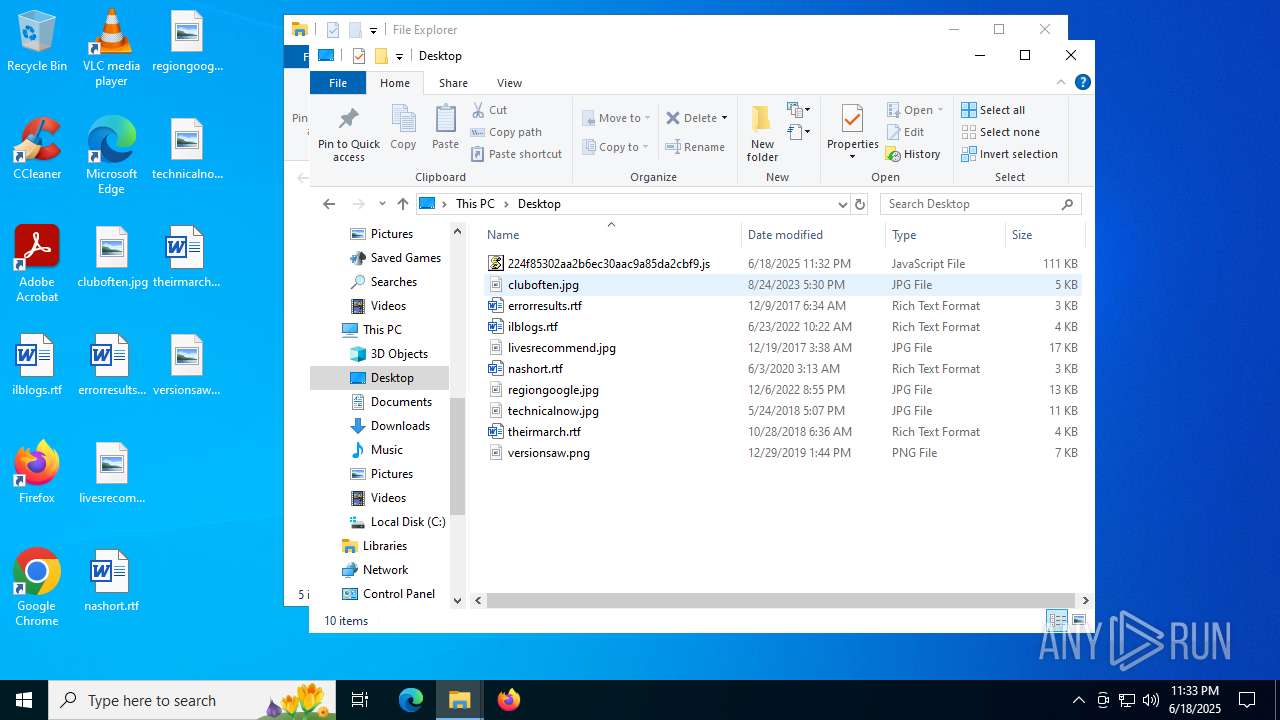
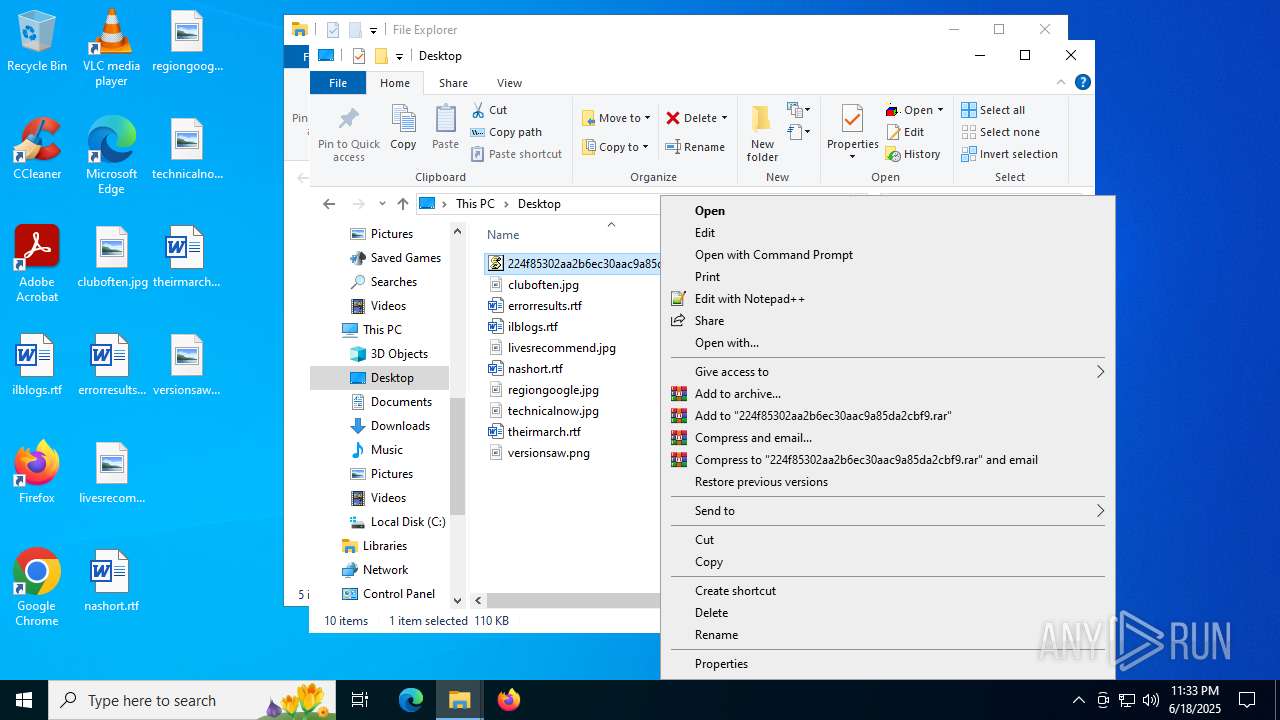
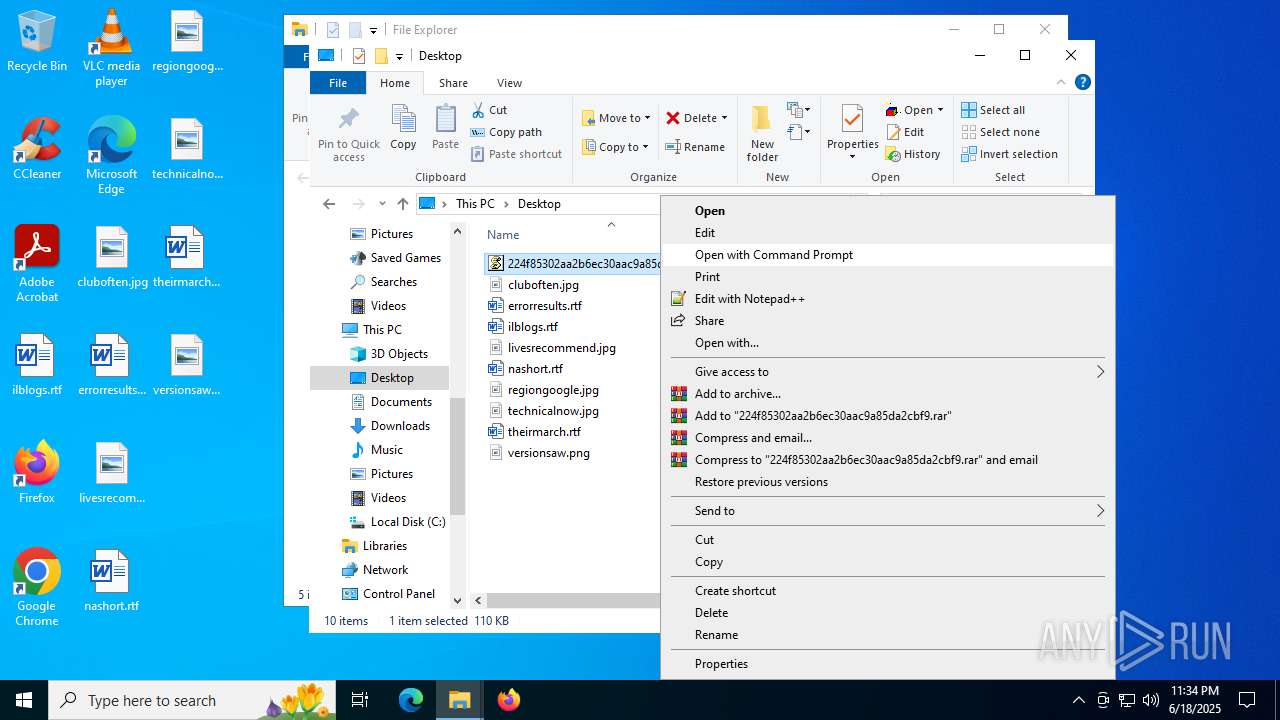
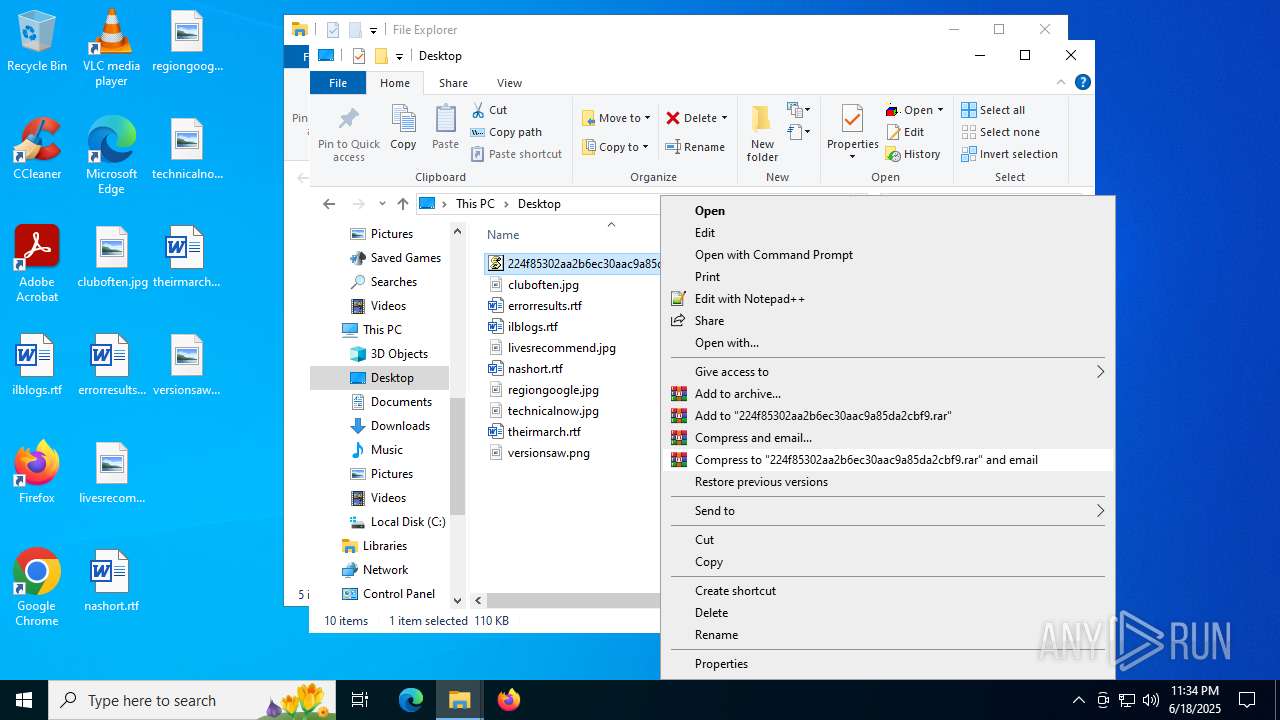
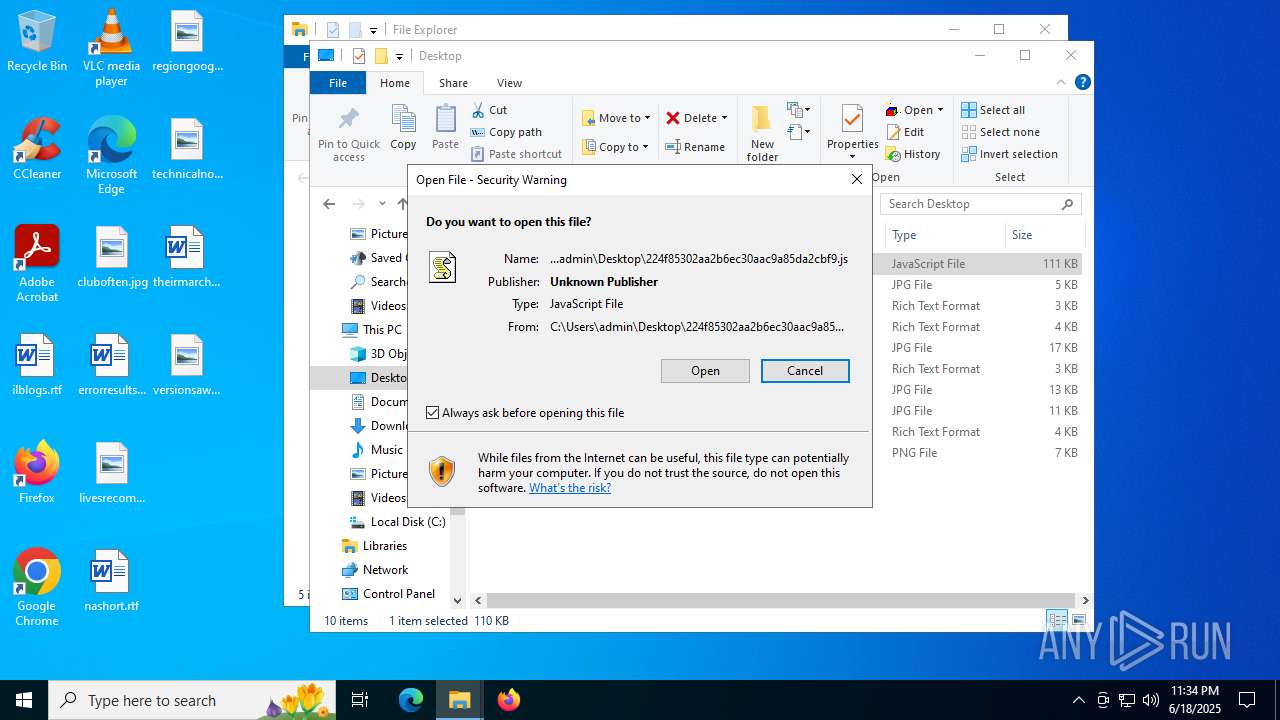
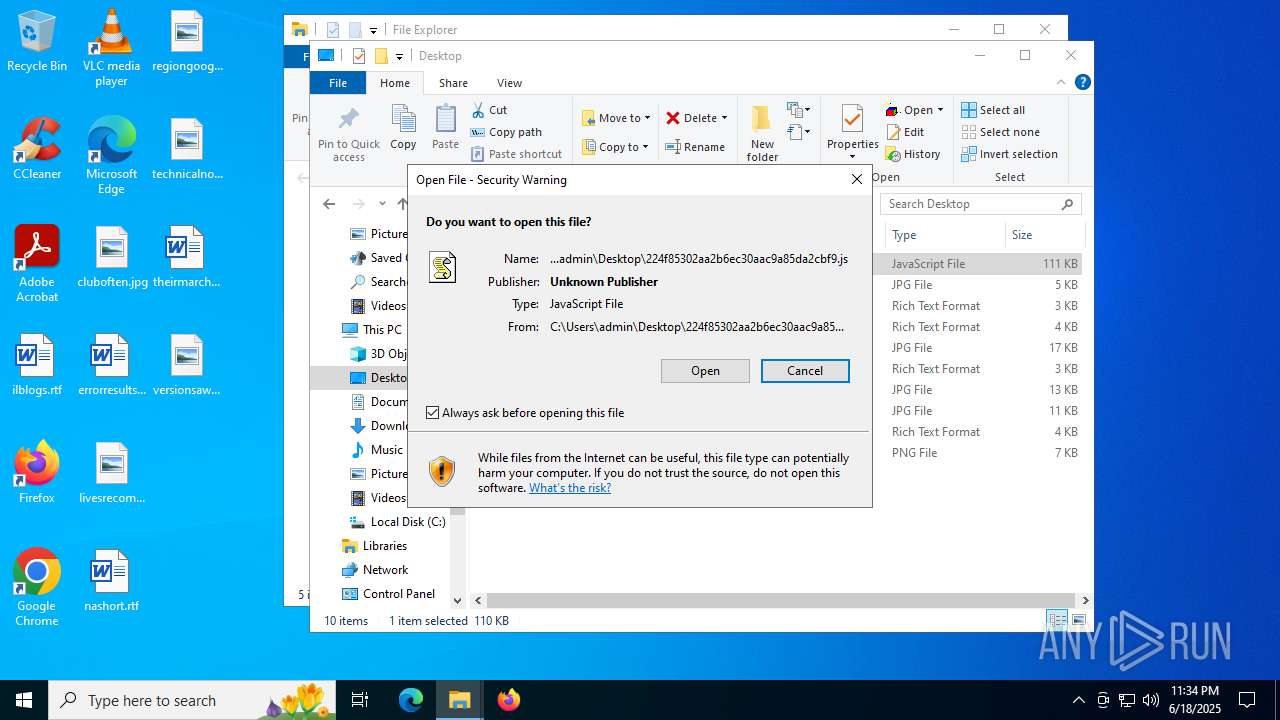
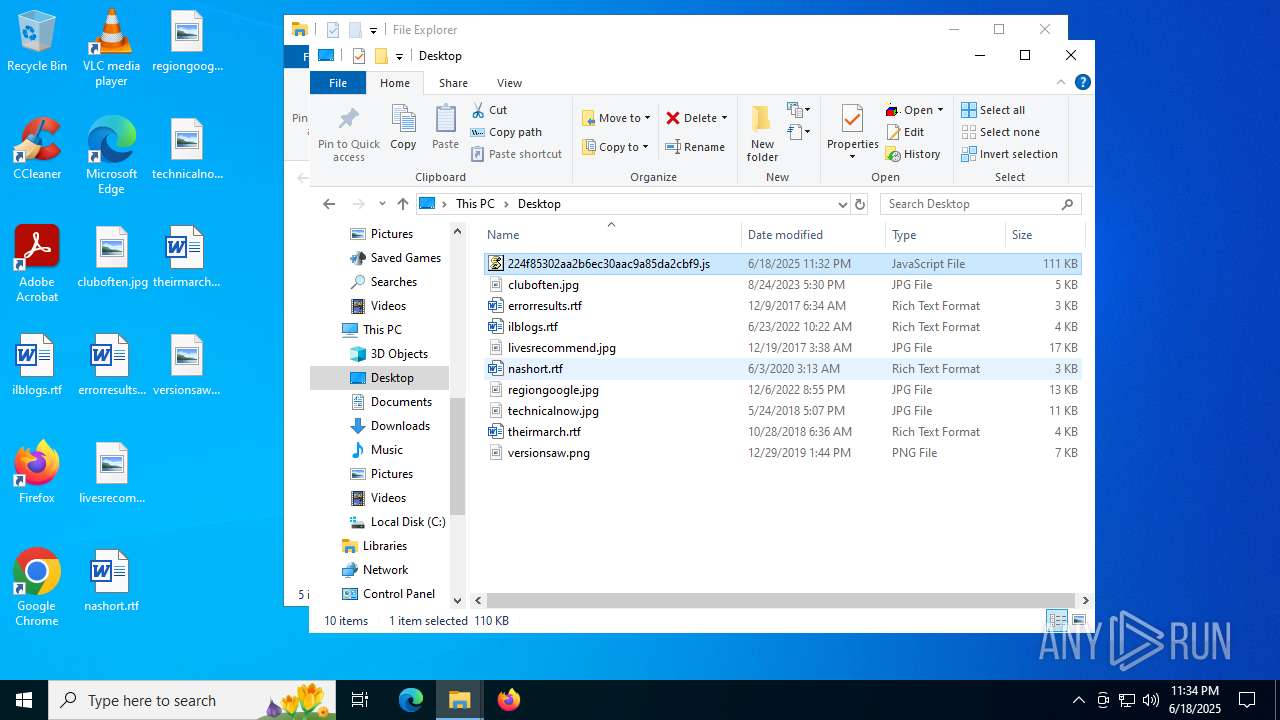
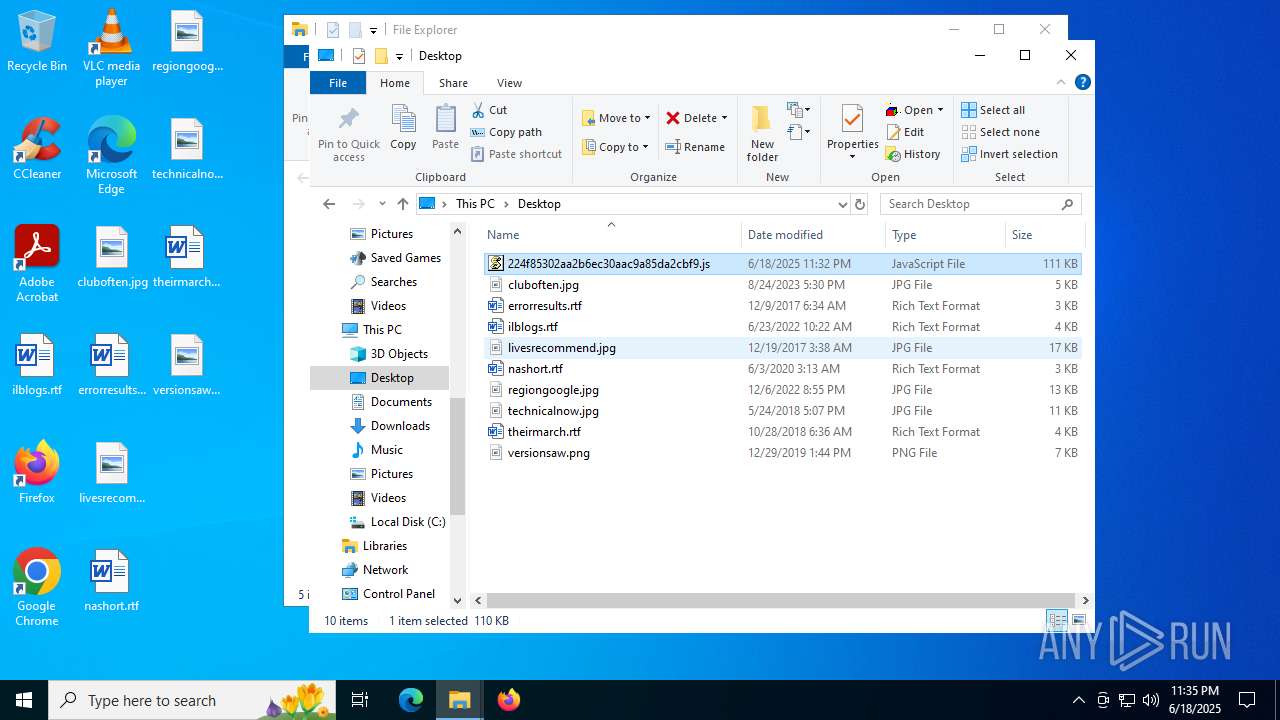
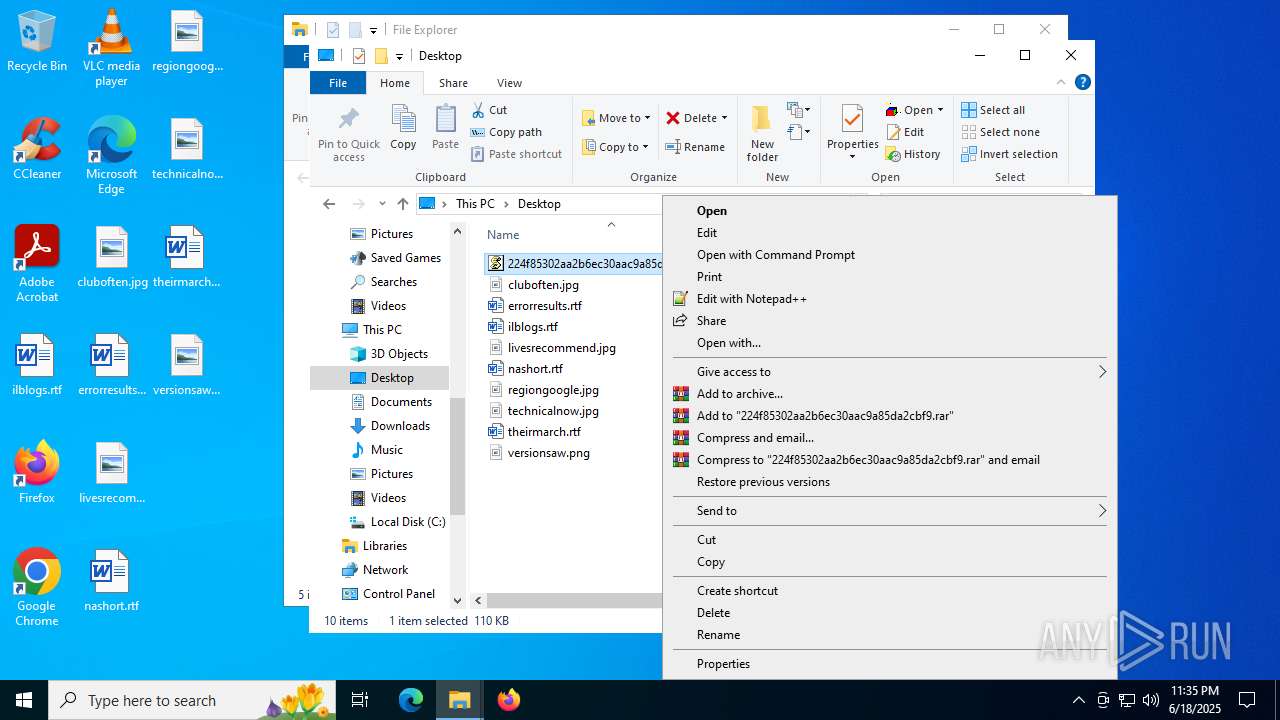
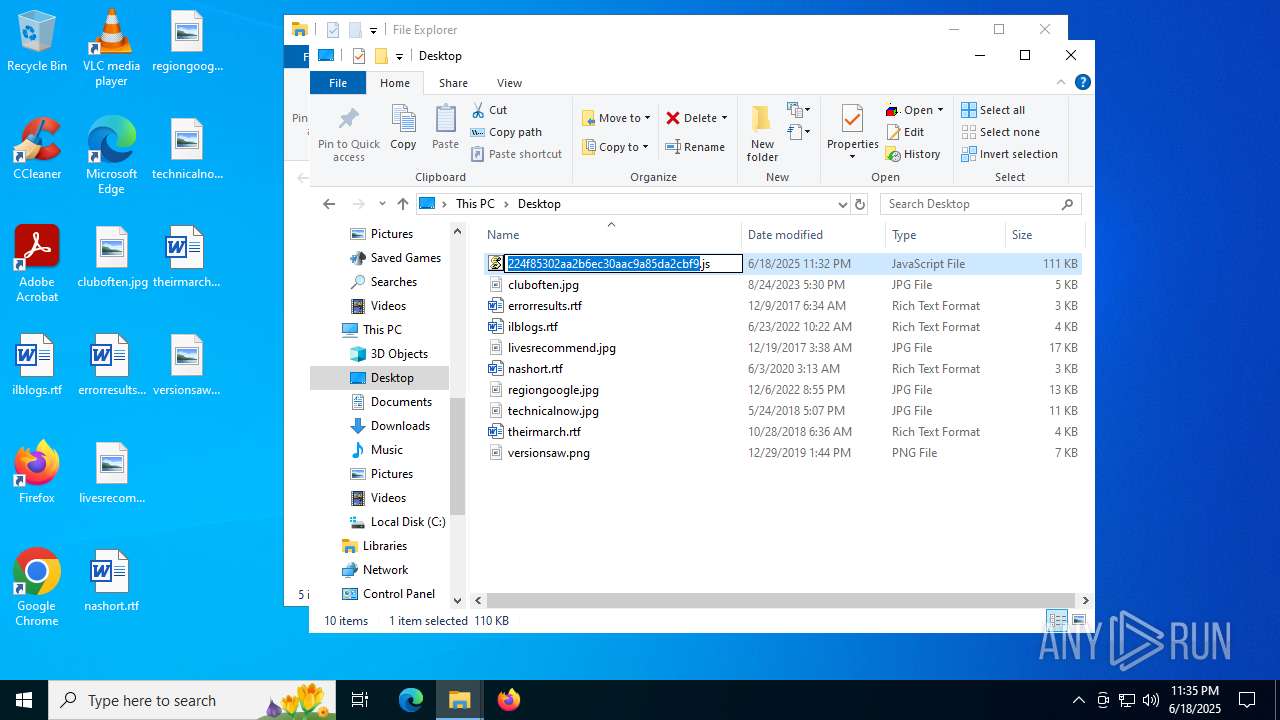
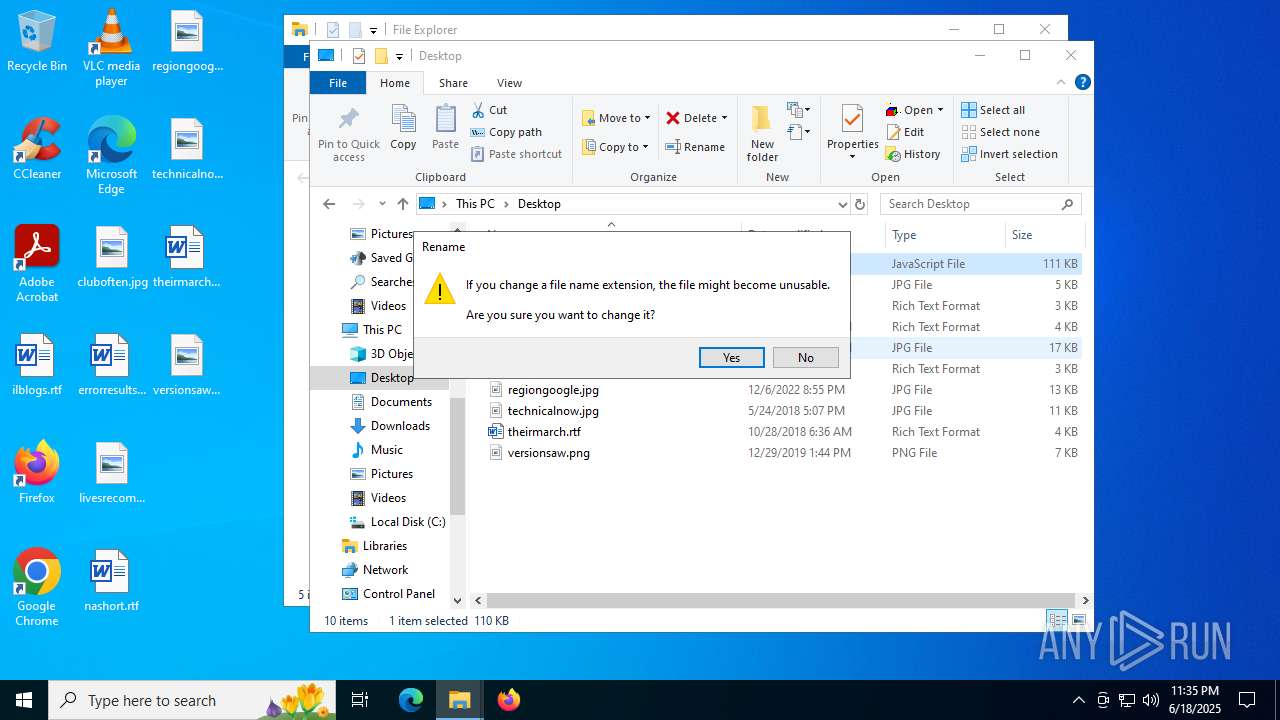
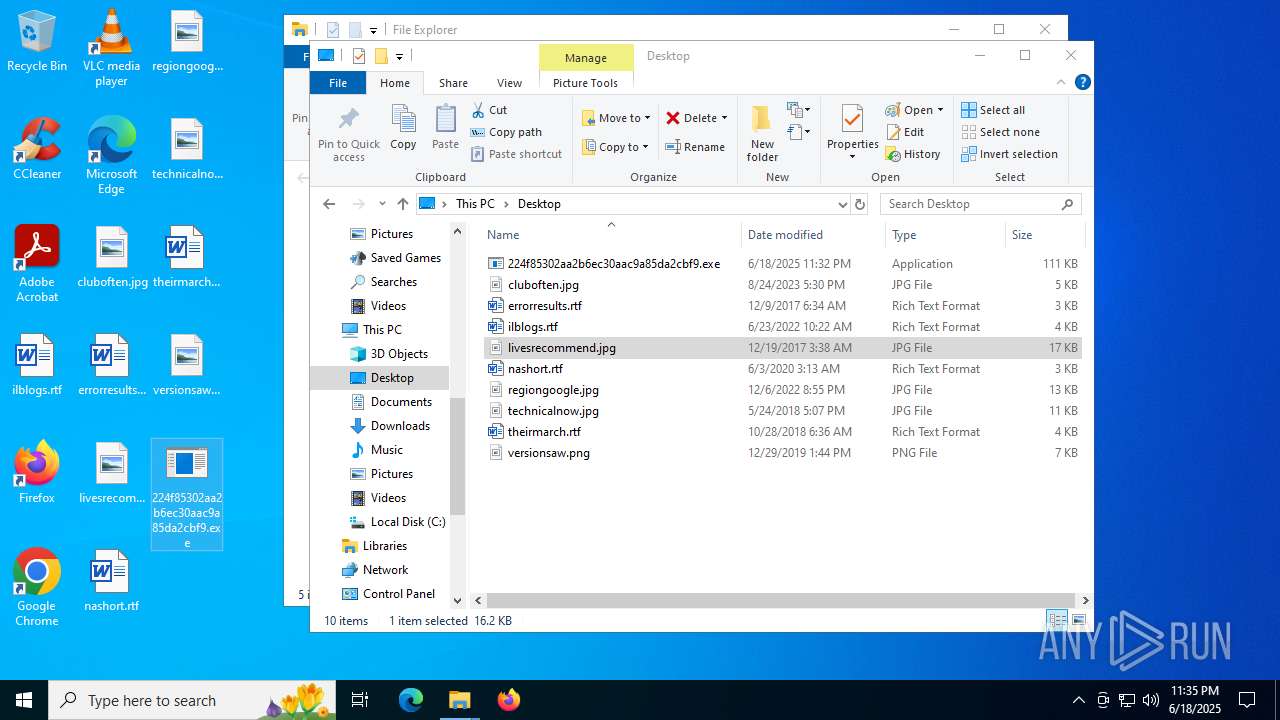
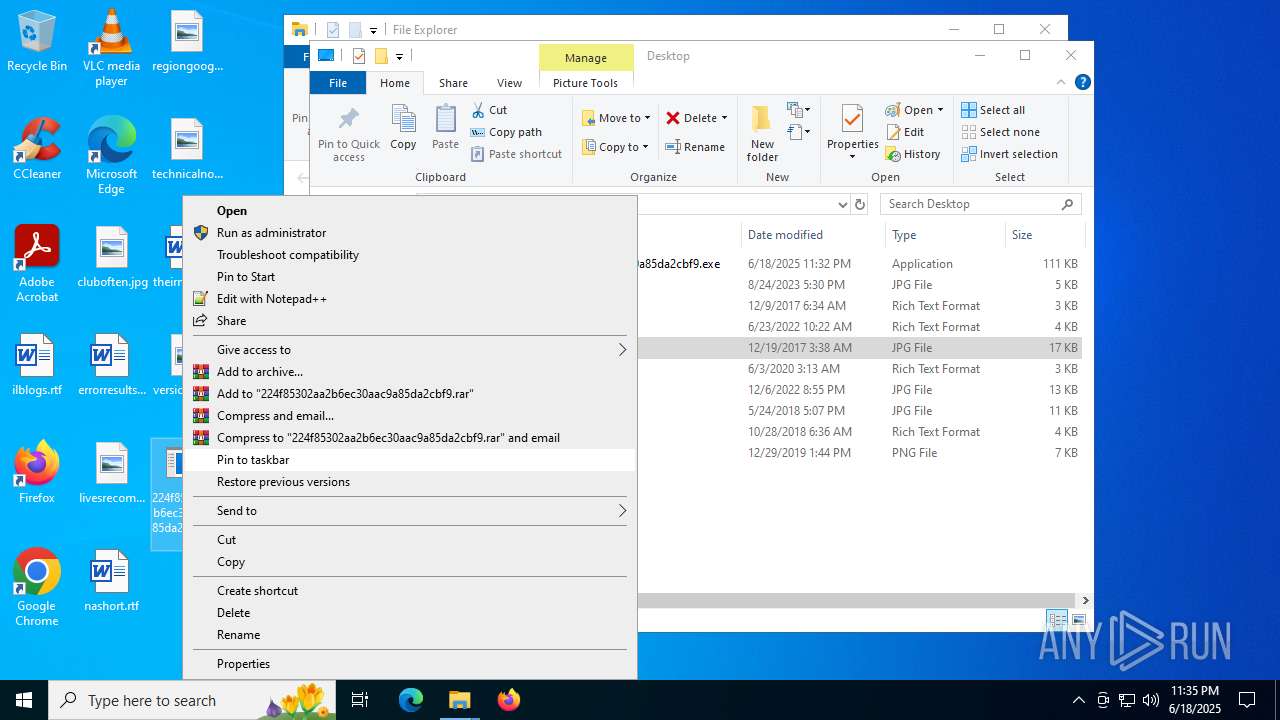
Manual execution by a user
- pcwrun.exe (PID: 6772)
- wscript.exe (PID: 1720)
- wscript.exe (PID: 768)
Create files in a temporary directory
- pcwrun.exe (PID: 6772)
- msdt.exe (PID: 5708)
- sdiagnhost.exe (PID: 7128)
- csc.exe (PID: 2144)
- cvtres.exe (PID: 1740)
- csc.exe (PID: 7324)
- cvtres.exe (PID: 4692)
- cvtres.exe (PID: 7548)
- csc.exe (PID: 8108)
Reads security settings of Internet Explorer
- msdt.exe (PID: 5708)
- sdiagnhost.exe (PID: 7128)
- rundll32.exe (PID: 4444)
The sample compiled with english language support
- msdt.exe (PID: 5708)
Uses string replace method (POWERSHELL)
- sdiagnhost.exe (PID: 7128)
Creates files or folders in the user directory
- sdiagnhost.exe (PID: 7128)
Uses string split method (POWERSHELL)
- sdiagnhost.exe (PID: 7128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
199
Monitored processes
57
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 768 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\224f85302aa2b6ec30aac9a85da2cbf9.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6692,i,18088602636365887963,996923527408912596,262144 --variations-seed-version --mojo-platform-channel-handle=5596 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2276,i,18088602636365887963,996923527408912596,262144 --variations-seed-version --mojo-platform-channel-handle=2416 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1720 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\224f85302aa2b6ec30aac9a85da2cbf9.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1740 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=4792,i,11364961151312710093,12931598875497642654,262144 --variations-seed-version --mojo-platform-channel-handle=5008 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1740 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES78DB.tmp" "c:\Users\admin\AppData\Local\Temp\CSC9994843B47D741038CD7A2B3B247728.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2144 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\kygzr1iu.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5172,i,11364961151312710093,12931598875497642654,262144 --variations-seed-version --mojo-platform-channel-handle=4252 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2780 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3764,i,11364961151312710093,12931598875497642654,262144 --variations-seed-version --mojo-platform-channel-handle=4792 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2804 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc43a0f208,0x7ffc43a0f214,0x7ffc43a0f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
23 650
Read events
23 504
Write events
141
Delete events
5
Modification events
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9C11215277962F00 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524848 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7FB0C099-C6AE-49B1-A536-075FFDEAEA14} | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524848 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0C368A19-F310-439F-A9DA-404E58432B25} | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 23F56F5277962F00 | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (6620) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524848 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6A2A9920-7D80-4AB5-98D2-0B34C183A69D} | |||
Executable files
19
Suspicious files
203
Text files
100
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176a62.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176a62.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176a72.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176a72.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176a72.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
70
DNS requests
69
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7244 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1750787927&P2=404&P3=2&P4=LtAx%2fEoe6r0uKnyx4EB%2brAxyS%2faYQsDX31vKlJoPgW6NYs33weGrLB3RCWPwf4xm0v09%2f4HVi5RRlO43KoMHdg%3d%3d | US | binary | 2.98 Kb | whitelisted |
1520 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:3r1cEJP3WqJABU_awLcljqe1mKq1rhAGMhbIYYb-974&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 98 b | whitelisted |
2292 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | US | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 868 b | whitelisted |
7996 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | ID | binary | 734 b | whitelisted |
7996 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
7244 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750787926&P2=404&P3=2&P4=cCbpNXIT8FX%2bBKaT8T0yFHaN3elOl3EvXwp7rzGdSDrovIDdqWkCIza57U7G3YT5FlkQJRMhg9ladfr94D2qLQ%3d%3d | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4832 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1520 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1520 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1520 | msedge.exe | 18.172.112.73:443 | euob.youseasky.com | — | US | unknown |
1520 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1520 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
euob.youseasky.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |