| File name: | 4f2119fc10384857e2a6660f6fcd8cc9.bin |
| Full analysis: | https://app.any.run/tasks/3a685508-62a2-4417-acf8-7d14427fd531 |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2022, 03:19:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4F2119FC10384857E2A6660F6FCD8CC9 |
| SHA1: | 1937322B05D35390DC0BBF4E9C49712156E70243 |
| SHA256: | 9C6C309DF34A4D6D1E907BC808FA8C166F2DD50C8B4E37BB1EA59CFFCE065B30 |
| SSDEEP: | 24576:fiXzF6/A87KbfU0+gbSUTOBfRkTNtIOcz:qx6//Wb80+eyoBK |
MALICIOUS
Runs app for hidden code execution
- cmd.exe (PID: 1852)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1168)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 1852)
- 4f2119fc10384857e2a6660f6fcd8cc9.bin.exe (PID: 3820)
- cmd.exe (PID: 1168)
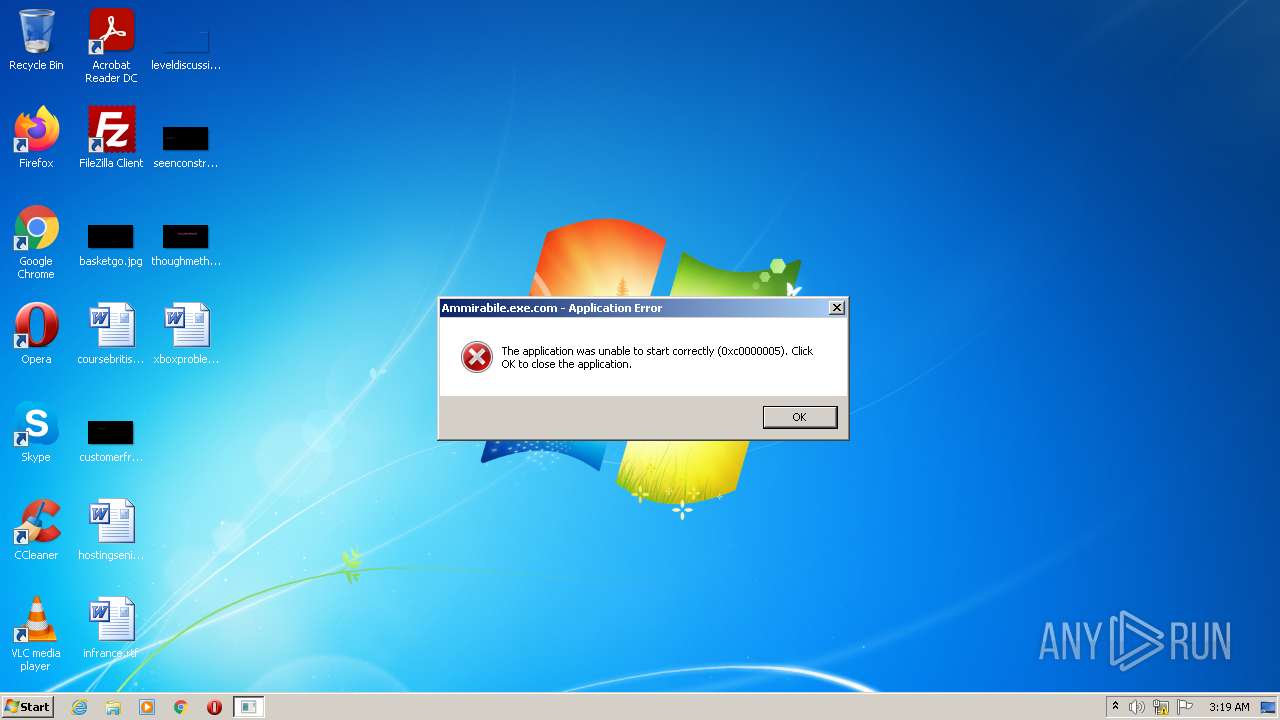
- Ammirabile.exe.com (PID: 3664)
- Ammirabile.exe.com (PID: 3464)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1852)
- 4f2119fc10384857e2a6660f6fcd8cc9.bin.exe (PID: 3820)
Uses RUNDLL32.EXE to load library
- 4f2119fc10384857e2a6660f6fcd8cc9.bin.exe (PID: 3820)
Application launched itself
- cmd.exe (PID: 1852)
- Ammirabile.exe.com (PID: 3664)
- Ammirabile.exe.com (PID: 3464)
Starts application with an unusual extension
- cmd.exe (PID: 1168)
- Ammirabile.exe.com (PID: 3664)
- Ammirabile.exe.com (PID: 3464)
Reads mouse settings
- Ammirabile.exe.com (PID: 3664)
- Ammirabile.exe.com (PID: 3464)
Reads the computer name
- Ammirabile.exe.com (PID: 3464)
INFO
Checks supported languages
- rundll32.exe (PID: 3596)
- findstr.exe (PID: 3216)
- PING.EXE (PID: 3948)
Reads the computer name
- PING.EXE (PID: 3948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 1 |
|---|---|
| ProductName: | Sandboxie Support for Process Hacker |
| OriginalFileName: | SbieSupport.dll |
| LegalCopyright: | Licensed under the GNU GPL, v3. |
| InternalName: | SbieSupport |
| FileVersion: | 1 |
| FileDescription: | Sandboxie Support for Process Hacker |
| CompanyName: | wj32 |
| CharacterSet: | Unicode |
| LanguageCode: | English (Australian) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 5.1 |
| OSVersion: | 5.1 |
| EntryPoint: | 0x645c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 934912 |
| CodeSize: | 39424 |
| LinkerVersion: | 7.1 |
| PEType: | PE32 |
| TimeStamp: | 2004:08:04 08:01:37+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Aug-2004 06:01:37 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | wj32 |
| FileDescription: | Sandboxie Support for Process Hacker |
| FileVersion: | 1.0 |
| InternalName: | SbieSupport |
| LegalCopyright: | Licensed under the GNU GPL, v3. |
| OriginalFilename: | SbieSupport.dll |
| ProductName: | Sandboxie Support for Process Hacker |
| ProductVersion: | 1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 04-Aug-2004 06:01:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000992C | 0x00009A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56535 |
.data | 0x0000B000 | 0x00001BE4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.248 |
.rsrc | 0x0000D000 | 0x000E3E73 | 0x000E4000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.88012 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05393 | 1511 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.96196 | 4895 | UNKNOWN | German - Germany | RT_ICON |
3 | 3.68456 | 9832 | UNKNOWN | German - Germany | RT_ICON |
4 | 3.23445 | 4392 | UNKNOWN | German - Germany | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
109 | 2.70146 | 212 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
202 | 2.9709 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
45
Monitored processes
9
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1168 | cmd | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1852 | cmd /c cmd < Crescente.wbk | C:\Windows\system32\cmd.exe | — | 4f2119fc10384857e2a6660f6fcd8cc9.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2428 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ammirabile.exe.com | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ammirabile.exe.com | Ammirabile.exe.com | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 3221225477 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 3216 | findstr /V /R "^sPnAiTnbaUSDtpadTQOwMqsAvCBgNbddcQNWRMXSNjVaVfqbQfJmfeSsbYtFslJUDBigvcmuSWhAyZEuBrbnORqzYvmSIaADCqPzoMwxPCGzOajnzXrgMluLf7f81a39-5f63-5b42-9efd-1f13b5431005quot; Ami.wbk | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3464 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ammirabile.exe.com X | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ammirabile.exe.com | — | Ammirabile.exe.com | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 3596 | rundll32 | C:\Windows\system32\rundll32.exe | — | 4f2119fc10384857e2a6660f6fcd8cc9.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | Ammirabile.exe.com X | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ammirabile.exe.com | — | cmd.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 3820 | "C:\Users\admin\AppData\Local\Temp\4f2119fc10384857e2a6660f6fcd8cc9.bin.exe" | C:\Users\admin\AppData\Local\Temp\4f2119fc10384857e2a6660f6fcd8cc9.bin.exe | — | Explorer.EXE | |||||||||||
User: admin Company: wj32 Integrity Level: MEDIUM Description: Sandboxie Support for Process Hacker Exit code: 0 Version: 1.0 Modules
| |||||||||||||||
| 3948 | ping localhost -n 30 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
400
Read events
400
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3820 | 4f2119fc10384857e2a6660f6fcd8cc9.bin.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ami.wbk | binary | |
MD5:— | SHA256:— | |||
| 3820 | 4f2119fc10384857e2a6660f6fcd8cc9.bin.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Crescente.wbk | text | |
MD5:— | SHA256:— | |||
| 3820 | 4f2119fc10384857e2a6660f6fcd8cc9.bin.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ben.wbk | text | |
MD5:— | SHA256:— | |||
| 1168 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\X | text | |
MD5:— | SHA256:— | |||
| 1168 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ammirabile.exe.com | text | |
MD5:AC6AD5D9B99757C3A878F2D275ACE198 | SHA256:9B8DB510EF42B8ED54A3712636FDA55A4F8CFCD5493E20B74AB00CD4F3979F2D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
eJkkHFGlqm.eJkkHFGlqm |
| unknown |