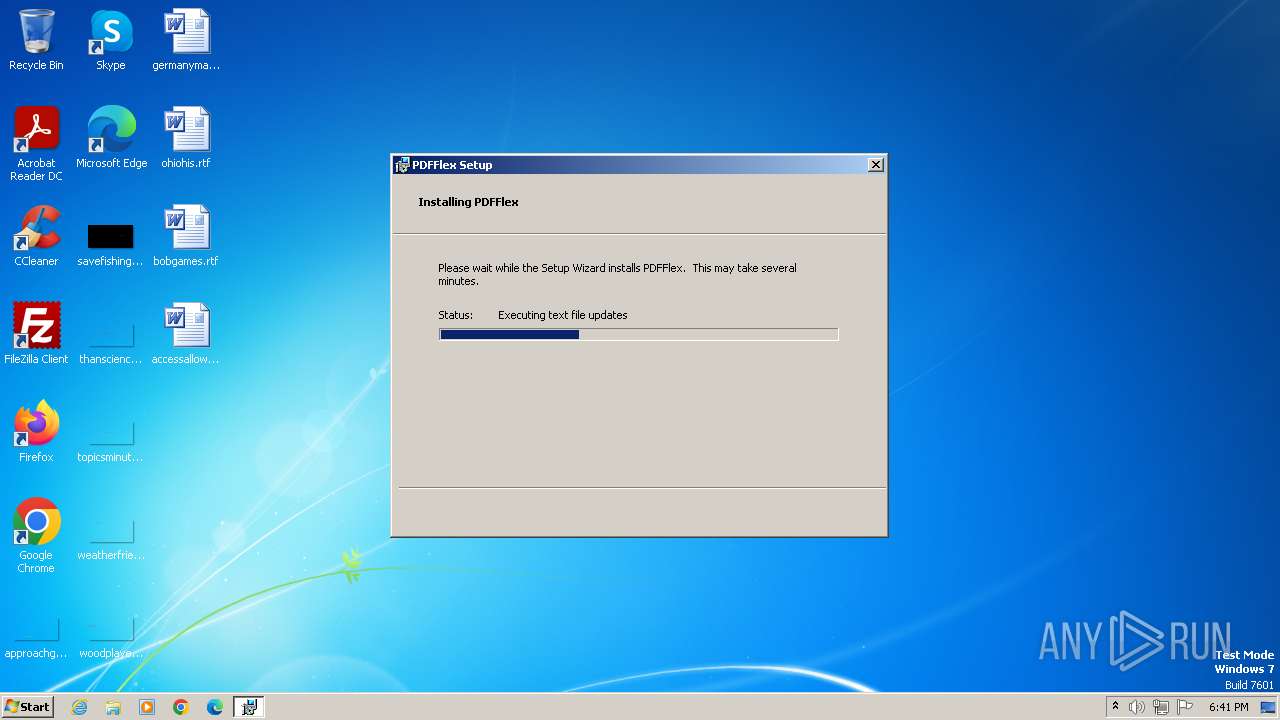
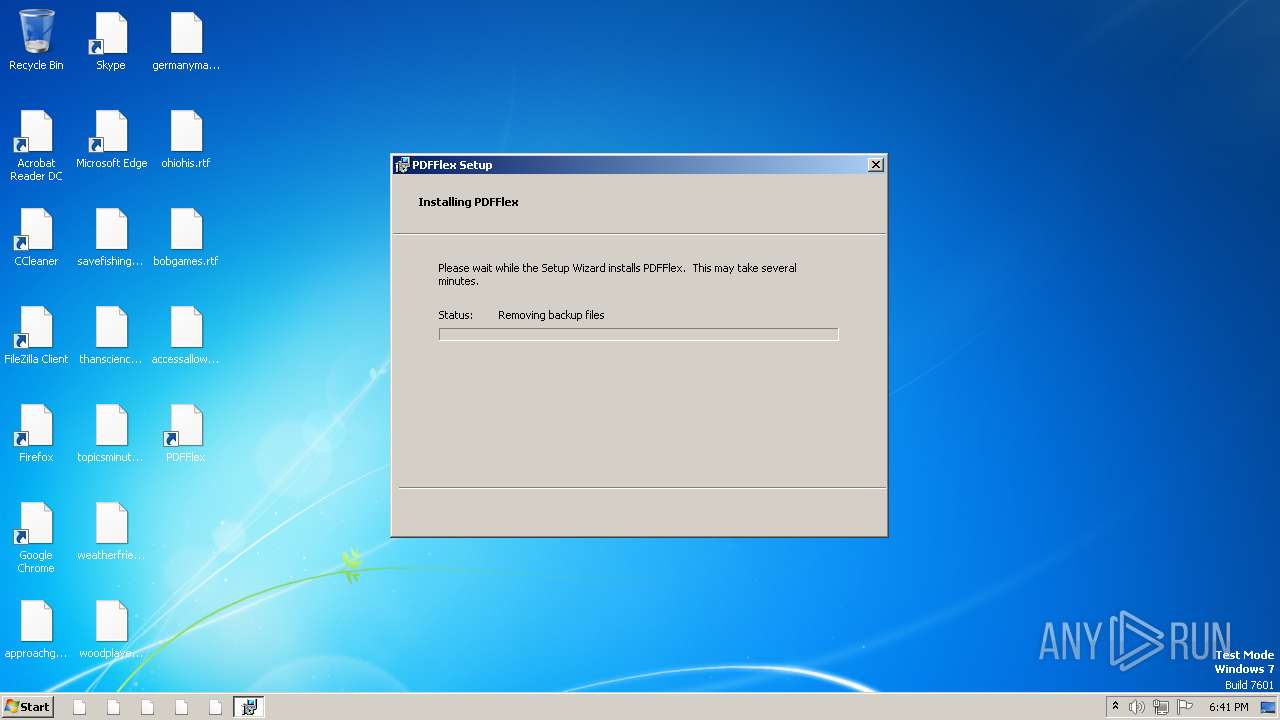
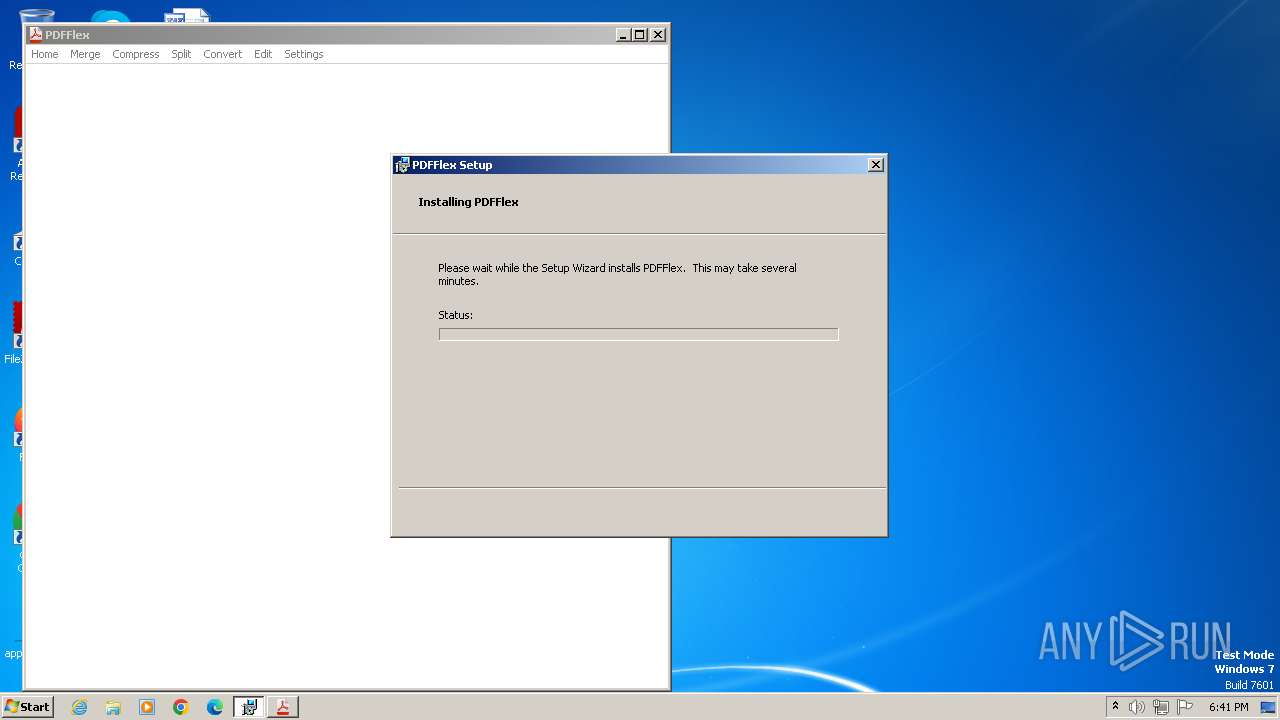
| File name: | GetPDFQuick_49223263.msi |
| Full analysis: | https://app.any.run/tasks/227393be-c1f8-4d03-98ad-fed6a2f6ab52 |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2024, 17:40:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
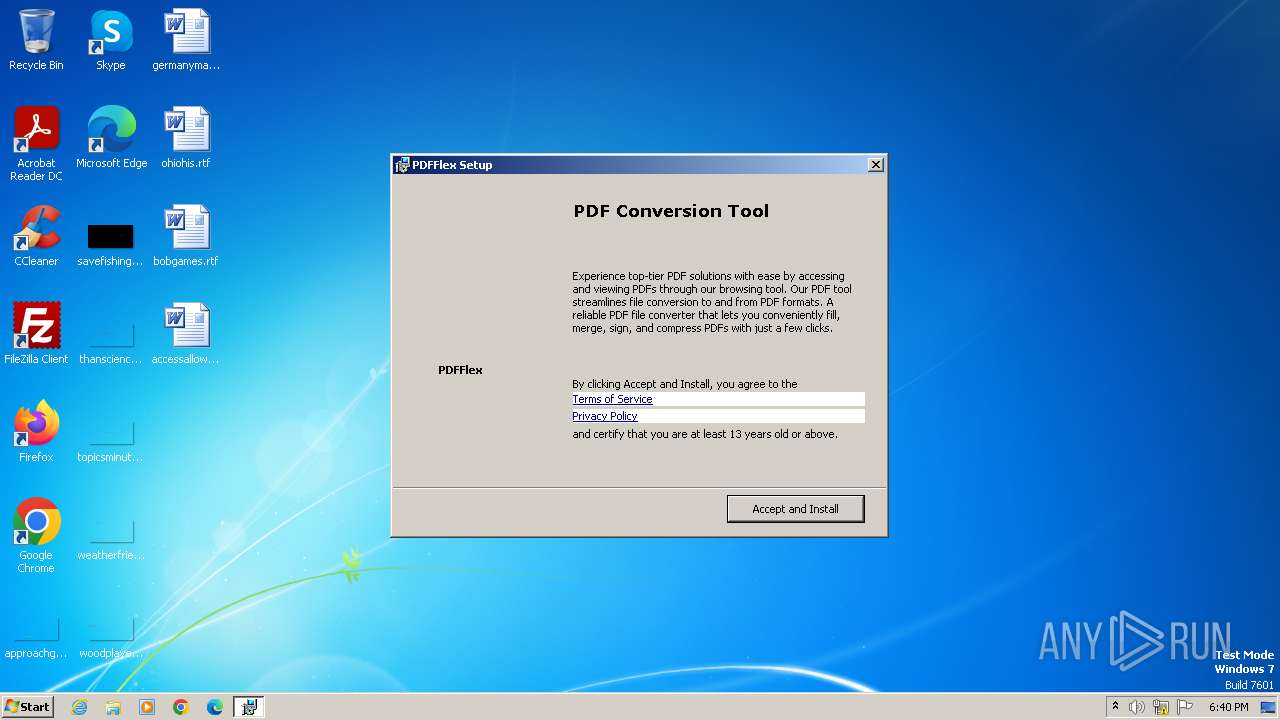
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code page: 1252, Title: Installation Database, Subject: PDFFlex, Author: PDFFlex.io, Keywords: Installer, MSI, Database, Comments: A base dados do instalador contm a lgica e os dados necessrios para instalar o PDFFlex., Create Time/Date: Fri May 3 06:40:18 2024, Name of Creating Application: PDFFlex, Security: 0, Template: ;1033, Last Saved By: ;1046, Revision Number: {B47F4499-DF9E-4B07-91DD-DD89A1A9640C}3.202.1208.0;{B47F4499-DF9E-4B07-91DD-DD89A1A9640C}3.202.1208.0;{50C54027-847F-4B86-849A-9C02C888EE0B}, Number of Pages: 450, Number of Characters: 63 |
| MD5: | 4012EFD9C8B10B519E58BF29930A55FA |
| SHA1: | 7B4DAE32939D09CF18298D68F3317501D09BCF90 |
| SHA256: | 9C5D756045FD479A742B81241CCF439D02FC668581A3002913811A341278DE43 |
| SSDEEP: | 98304:S9IYolSpkBN/2Wex0xaAW9I+9DE+mzSE5lIP4GASazPtiG6CPUF0csMof+iZZjDR:gNG7z |
MALICIOUS
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 1024)
- msiexec.exe (PID: 2516)
Bypass execution policy to execute commands
- powershell.exe (PID: 1064)
- powershell.exe (PID: 1768)
- powershell.exe (PID: 1960)
- powershell.exe (PID: 1028)
Drops the executable file immediately after the start
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 2516)
Changes the autorun value in the registry
- msiexec.exe (PID: 4060)
SUSPICIOUS
Reads the Internet Settings
- msiexec.exe (PID: 3960)
- msiexec.exe (PID: 2516)
- powershell.exe (PID: 1960)
- MSIC64A.tmp (PID: 2392)
- powershell.exe (PID: 1028)
- msiexec.exe (PID: 1024)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 1024)
- msiexec.exe (PID: 2516)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 1024)
- msiexec.exe (PID: 2516)
The process executes Powershell scripts
- msiexec.exe (PID: 1024)
- msiexec.exe (PID: 2516)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 1024)
- msiexec.exe (PID: 2516)
Reverses array data (POWERSHELL)
- powershell.exe (PID: 1768)
Executes as Windows Service
- VSSVC.exe (PID: 768)
Checks Windows Trust Settings
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 2516)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4060)
Process drops legitimate windows executable
- msiexec.exe (PID: 4060)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 2516)
- MSIC64A.tmp (PID: 2392)
- msiexec.exe (PID: 1024)
Node.exe was dropped
- msiexec.exe (PID: 2516)
Unusual connection from system programs
- powershell.exe (PID: 1960)
- powershell.exe (PID: 1028)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 1024)
INFO
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3960)
- powershell.exe (PID: 1064)
- powershell.exe (PID: 1768)
- powershell.exe (PID: 1960)
- powershell.exe (PID: 1028)
An automatically generated document
- msiexec.exe (PID: 3960)
Reads the computer name
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 1024)
- msiexec.exe (PID: 2516)
- wmpnscfg.exe (PID: 1976)
- MSIC67A.tmp (PID: 2424)
- MSIC64A.tmp (PID: 2392)
Checks supported languages
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 1024)
- msiexec.exe (PID: 2516)
- wmpnscfg.exe (PID: 1976)
- MSIC64A.tmp (PID: 2392)
- MSIC67A.tmp (PID: 2424)
- PDFFlex.exe (PID: 2376)
Creates files or folders in the user directory
- msiexec.exe (PID: 3960)
- msiexec.exe (PID: 2516)
- msiexec.exe (PID: 4060)
- PDFFlex.exe (PID: 2376)
Create files in a temporary directory
- msiexec.exe (PID: 3960)
- powershell.exe (PID: 1064)
- powershell.exe (PID: 1768)
- msiexec.exe (PID: 1024)
- powershell.exe (PID: 1960)
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 2516)
- powershell.exe (PID: 1028)
Reads the software policy settings
- msiexec.exe (PID: 3960)
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 2516)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 1024)
- msiexec.exe (PID: 2516)
Application launched itself
- msiexec.exe (PID: 4060)
Drops the executable file immediately after the start
- msiexec.exe (PID: 3960)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3960)
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 2516)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1064)
- powershell.exe (PID: 1768)
- powershell.exe (PID: 1960)
- powershell.exe (PID: 1028)
Reads Environment values
- msiexec.exe (PID: 1024)
- msiexec.exe (PID: 2516)
Disables trace logs
- powershell.exe (PID: 1960)
- powershell.exe (PID: 1028)
Manual execution by a user
- wmpnscfg.exe (PID: 1976)
Checks proxy server information
- msiexec.exe (PID: 2516)
Creates a software uninstall entry
- msiexec.exe (PID: 4060)
Starts application with an unusual extension
- msiexec.exe (PID: 4060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {5CC5243C-3A9A-4868-90C3-9CEA3AEEFCAF} |
| Words: | 10 |
| Subject: | PDFFlex |
| Author: | PDFFlex.io |
| LastModifiedBy: | - |
| Software: | PDFFlex |
| Template: | ;1033,1046,3082,1055 |
| Comments: | PDFFlex 3.202.1208.0 |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:05:03 06:40:36 |
| ModifyDate: | 2024:05:03 06:40:36 |
| LastPrinted: | 2024:05:03 06:40:36 |
| Pages: | 450 |
| Characters: | 63 |
Total processes
54
Monitored processes
14
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 768 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | C:\Windows\system32\MsiExec.exe -Embedding C12EB203FC96B631911BA50FD712DC85 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1028 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\PDFFlex\pssC762.ps1" -propFile "C:\Users\admin\AppData\Local\PDFFlex\msiC740.txt" -scriptFile "C:\Users\admin\AppData\Local\PDFFlex\scrC741.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\PDFFlex\scrC742.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1064 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss37BE.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi37AC.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr37AD.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr37AE.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1768 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss3CF3.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi3CD1.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr3CD2.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr3CE3.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1960 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss649B.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi6478.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr6479.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr647A.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | "C:\Users\admin\AppData\Local\PDFFlex\PDFFlex.exe" | C:\Users\admin\AppData\Local\PDFFlex\PDFFlex.exe | MSIC64A.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 3.202.1208.0 Modules
| |||||||||||||||
| 2392 | "C:\Windows\Installer\MSIC64A.tmp" /DontWait /dir "C:\Users\admin\AppData\Local\PDFFlex\" "C:\Users\admin\AppData\Local\PDFFlex\PDFFlex.exe" | C:\Windows\Installer\MSIC64A.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 21.5.1.0 Modules
| |||||||||||||||
| 2424 | "C:\Windows\Installer\MSIC67A.tmp" /HideWindow /dir "C:\Users\admin\AppData\Local\PDFFlex\installer\" "C:\Users\admin\AppData\Local\PDFFlex\installer\OperaSetup.exe" --silent --allusers=0 | C:\Windows\Installer\MSIC67A.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 4294967295 Version: 21.5.1.0 Modules
| |||||||||||||||
Total events
34 798
Read events
34 444
Write events
332
Delete events
22
Modification events
| (PID) Process: | (3960) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4060) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000003C1CF8DA93AFDA01DC0F000034060000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000003C1CF8DA93AFDA01DC0F000034060000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 75 | |||
| (PID) Process: | (4060) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000BCB290DB93AFDA01DC0F000034060000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000161593DB93AFDA01DC0F000000070000E803000001000000000000000000000028FBBB8F62D61A4F96BB169973AAC1440000000000000000 | |||
| (PID) Process: | (768) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007E9E9CDB93AFDA01000300001C010000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (768) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007E9E9CDB93AFDA01000300000C060000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (768) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007E9E9CDB93AFDA0100030000FC060000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (768) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007E9E9CDB93AFDA01000300003C090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
24
Suspicious files
51
Text files
25
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1024 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi37AC.txt | — | |
MD5:— | SHA256:— | |||
| 1024 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr37AD.ps1 | — | |
MD5:— | SHA256:— | |||
| 1024 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr37AE.txt | — | |
MD5:— | SHA256:— | |||
| 1024 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss37BE.ps1 | — | |
MD5:— | SHA256:— | |||
| 1024 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi3CD1.txt | — | |
MD5:— | SHA256:— | |||
| 1024 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr3CD2.ps1 | — | |
MD5:— | SHA256:— | |||
| 1024 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr3CE3.txt | — | |
MD5:— | SHA256:— | |||
| 1024 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss3CF3.ps1 | — | |
MD5:— | SHA256:— | |||
| 3960 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:29F65BA8E88C063813CC50A4EA544E93 | SHA256:1ED81FA8DFB6999A9FEDC6E779138FFD99568992E22D300ACD181A6D2C8DE184 | |||
| 3960 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab348F.tmp | compressed | |
MD5:29F65BA8E88C063813CC50A4EA544E93 | SHA256:1ED81FA8DFB6999A9FEDC6E779138FFD99568992E22D300ACD181A6D2C8DE184 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
14
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3960 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://secure.globalsign.com/cacert/codesigningrootr45.crt | unknown | — | — | unknown |
3960 | msiexec.exe | GET | 200 | 217.20.57.34:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3f47513eb9645b87 | unknown | — | — | unknown |
1960 | powershell.exe | POST | 200 | 65.9.94.206:80 | http://d1jorhhovk7rc8.cloudfront.net/ | unknown | — | — | unknown |
2516 | msiexec.exe | GET | 304 | 217.20.57.34:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5daa7ac2767c5f9b | unknown | — | — | unknown |
2516 | msiexec.exe | GET | 200 | 108.138.2.107:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | — | — | unknown |
2516 | msiexec.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | — | — | unknown |
2516 | msiexec.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | unknown | — | — | unknown |
1088 | svchost.exe | GET | 304 | 217.20.57.18:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?83bdd76cfa43776c | unknown | — | — | unknown |
1028 | powershell.exe | POST | 200 | 18.66.107.68:80 | http://d1jorhhovk7rc8.cloudfront.net/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3960 | msiexec.exe | 104.18.21.226:80 | secure.globalsign.com | CLOUDFLARENET | — | shared |
3960 | msiexec.exe | 217.20.57.34:80 | ctldl.windowsupdate.com | — | US | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1960 | powershell.exe | 65.9.94.206:80 | d1jorhhovk7rc8.cloudfront.net | AMAZON-02 | US | unknown |
2516 | msiexec.exe | 18.66.92.74:443 | dn0diw4x4ljz4.cloudfront.net | — | US | unknown |
2516 | msiexec.exe | 217.20.57.34:80 | ctldl.windowsupdate.com | — | US | unknown |
2516 | msiexec.exe | 108.138.2.107:80 | o.ss2.us | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
secure.globalsign.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
d1jorhhovk7rc8.cloudfront.net |
| unknown |
dn0diw4x4ljz4.cloudfront.net |
| unknown |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
Threats
Process | Message |
|---|---|
PDFFlex.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|