| File name: | HideToolz.exe |
| Full analysis: | https://app.any.run/tasks/2fd4d44e-e08f-4875-89a5-e085f78e49ec |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2021, 18:05:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 16FB540B297276D0A7624C8B23F79D87 |
| SHA1: | 2DD25170C9A36CBF656A793936C8D7DB0729A8BE |
| SHA256: | 9C51B691AABC5931F7E1B8DCE7B9810AD5A266843AA6EA30E666C3AFD98CB9F4 |
| SSDEEP: | 1536:crqWCQfhvJ6jYY7Nmpub8KWWDedty40Pjfzg2zDRH9SfV:KCsJ6jToyTeJ0PjfzrffUV |
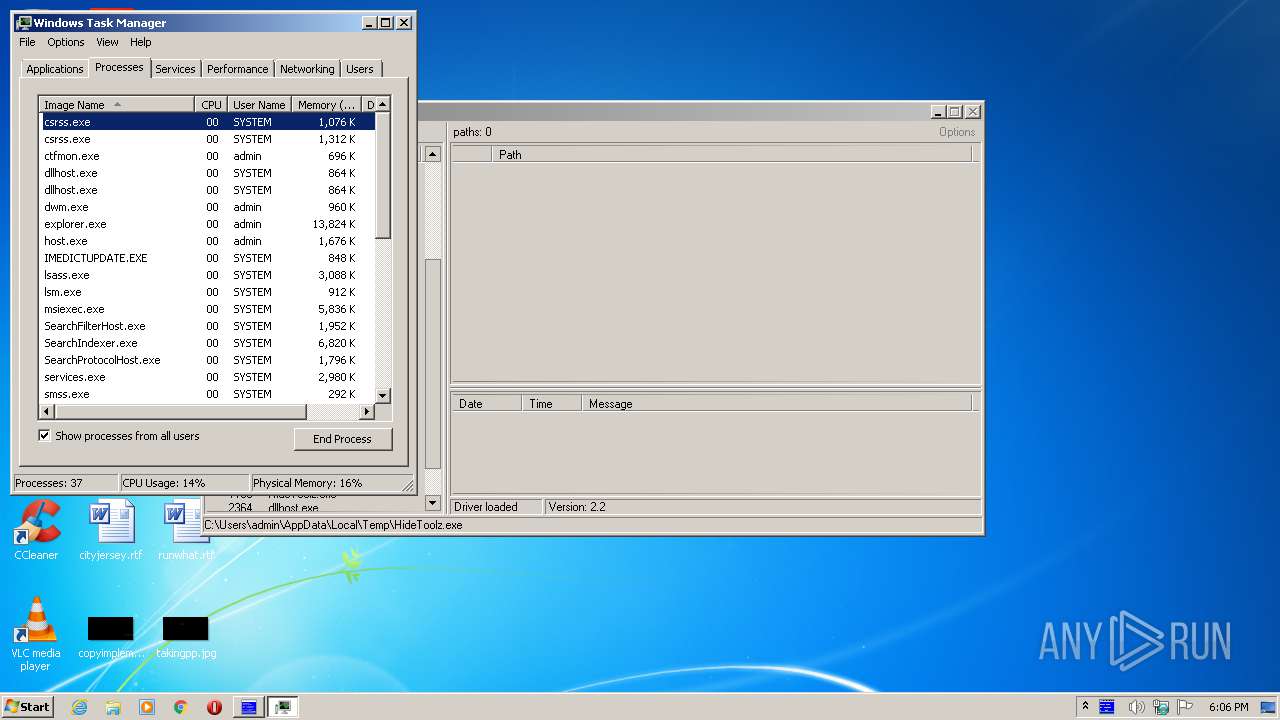
MALICIOUS
Drops executable file immediately after starts
- HideToolz.exe (PID: 1180)
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2120)
Steals credentials from Web Browsers
- CCleaner.exe (PID: 1000)
Actions looks like stealing of personal data
- CCleaner.exe (PID: 1000)
SUSPICIOUS
Creates files in the Windows directory
- HideToolz.exe (PID: 1180)
Executable content was dropped or overwritten
- HideToolz.exe (PID: 1180)
Drops a file with too old compile date
- HideToolz.exe (PID: 1180)
Creates or modifies windows services
- HideToolz.exe (PID: 1180)
Drops a file that was compiled in debug mode
- HideToolz.exe (PID: 1180)
Removes files from Windows directory
- HideToolz.exe (PID: 1180)
Executed via Task Scheduler
- CCleaner.exe (PID: 1000)
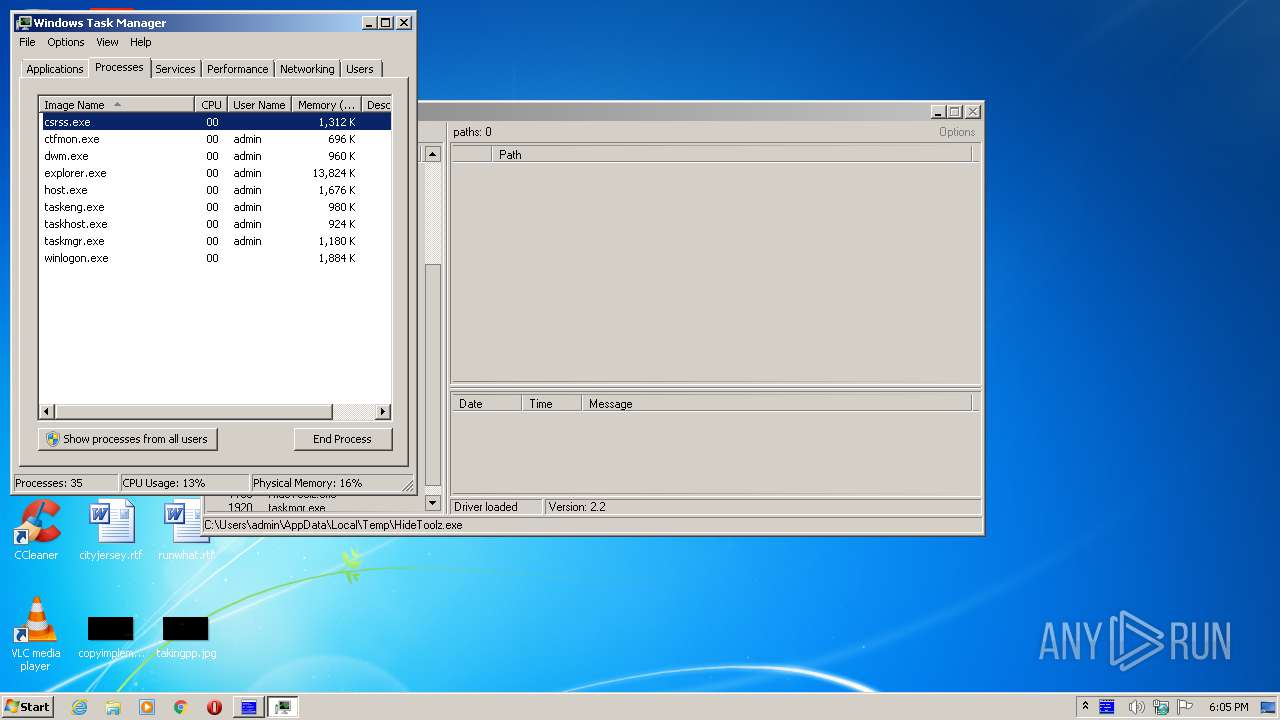
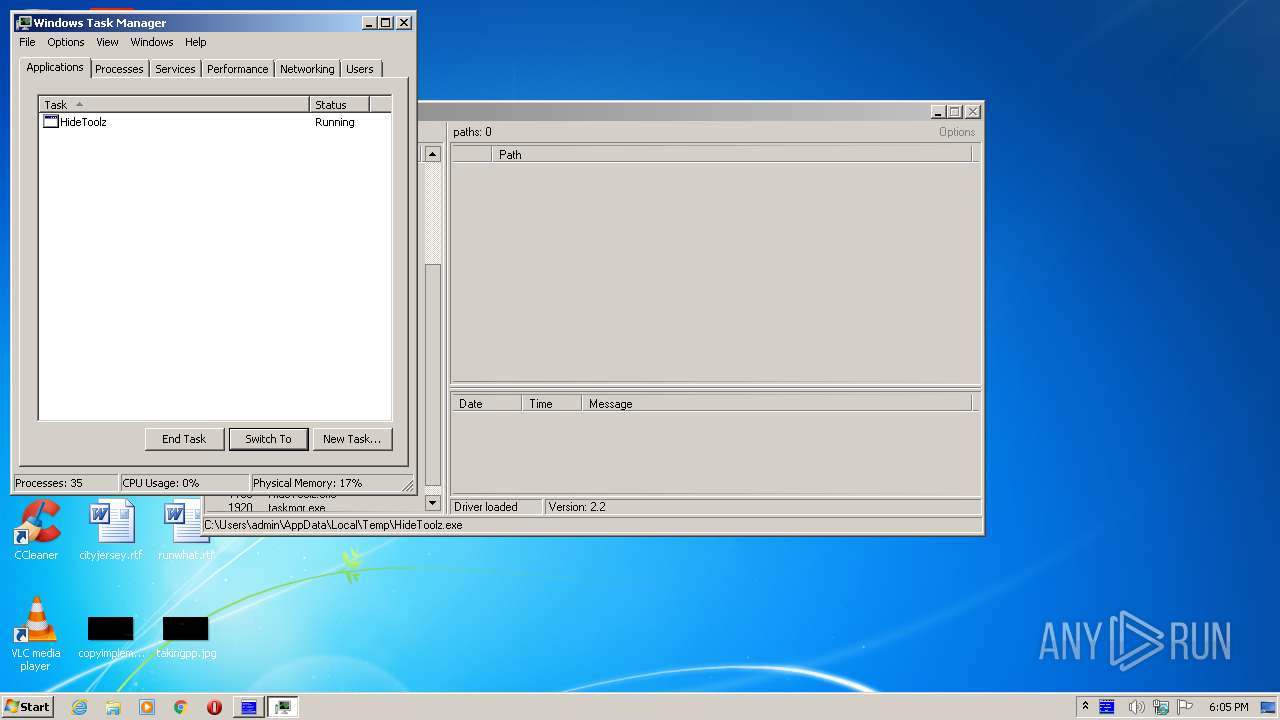
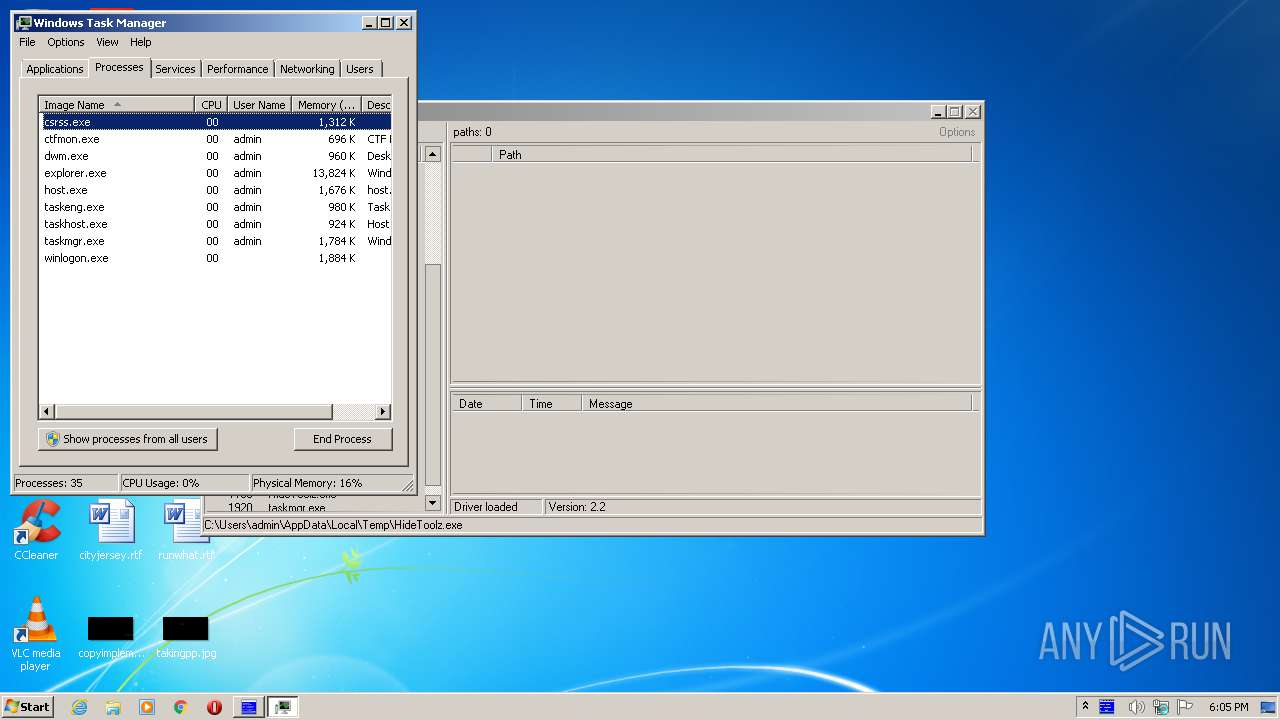
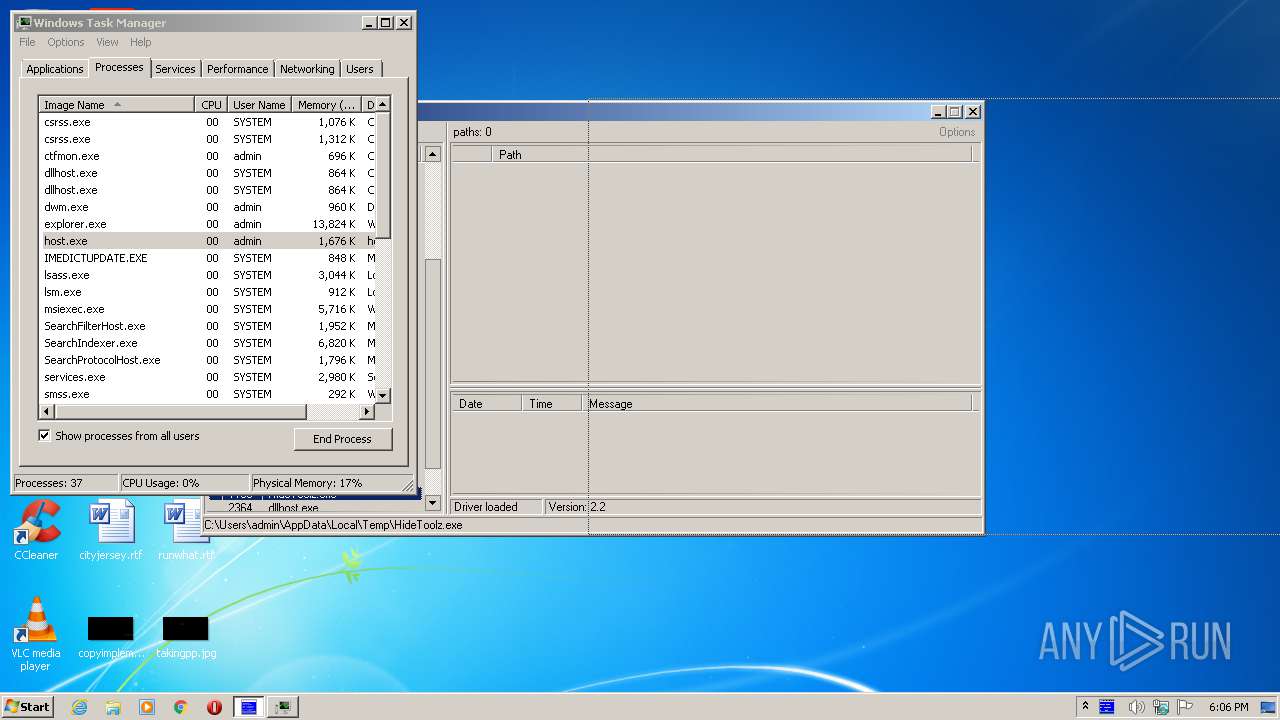
Application launched itself
- taskmgr.exe (PID: 1920)
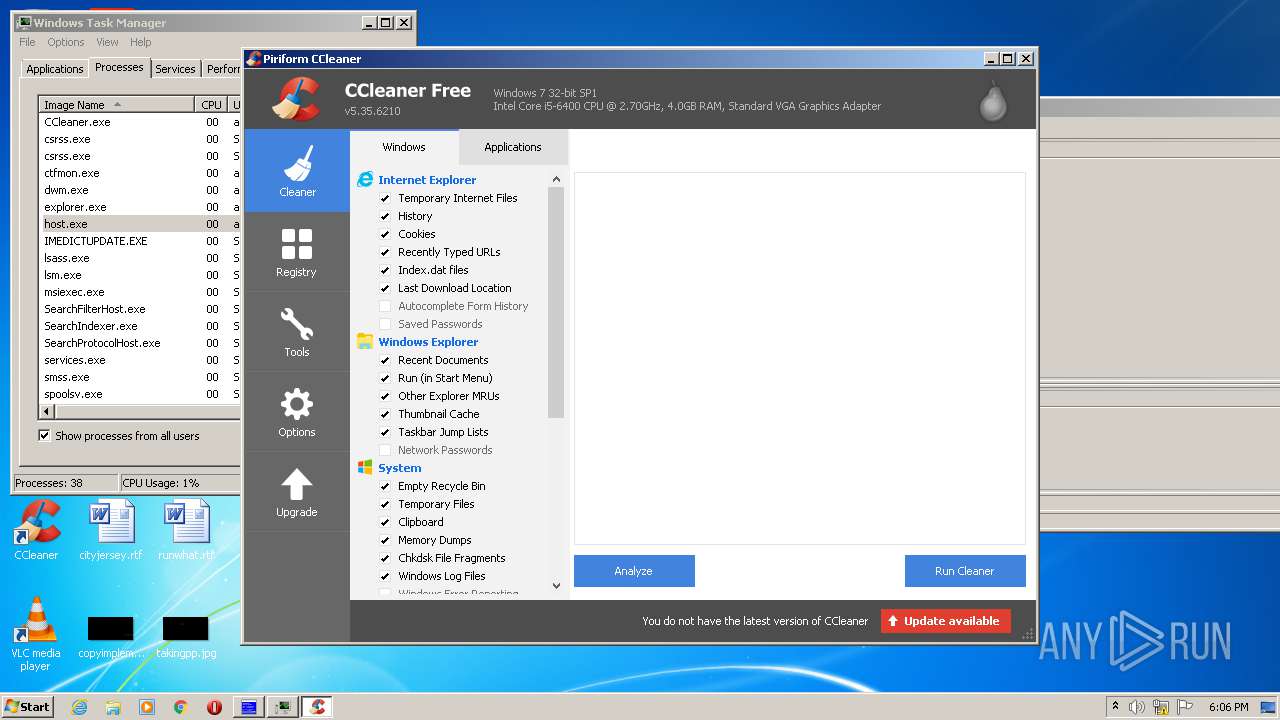
Reads internet explorer settings
- CCleaner.exe (PID: 1000)
Creates files in the user directory
- CCleaner.exe (PID: 1000)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 1000)
INFO
Manual execution by user
- taskmgr.exe (PID: 1920)
- CCleaner.exe (PID: 2120)
Reads settings of System Certificates
- CCleaner.exe (PID: 1000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.1) |
|---|---|---|
| .scr | | | Windows screen saver (17.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.7) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| PEType: | PE32 |
| LinkerVersion: | 77.7 |
| CodeSize: | 67072 |
| InitializedDataSize: | 29696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1155c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000105C8 | 0x00010600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47949 |
.data | 0x00012000 | 0x000003E8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.01468 |
.bss | 0x00013000 | 0x0000075D | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00014000 | 0x00001490 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.63937 |
.tls | 0x00016000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00017000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00018000 | 0x00000B98 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.60135 |
.rsrc | 0x00019000 | 0x00004C00 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.04374 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86299 | 646 | UNKNOWN | UNKNOWN | RT_MANIFEST |
HTDRV1 | 6.0993 | 16256 | UNKNOWN | English - United States | RESFILE |
ICON0_TIMAGE | 3.12638 | 616 | UNKNOWN | UNKNOWN | RT_BITMAP |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.29092 | 276 | UNKNOWN | UNKNOWN | RT_RCDATA |
_464D0_464D1 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
IMAGEHLP.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ntdll.dll |
ole32.dll |
shell32.dll |
shlwapi.dll |
user32.dll |
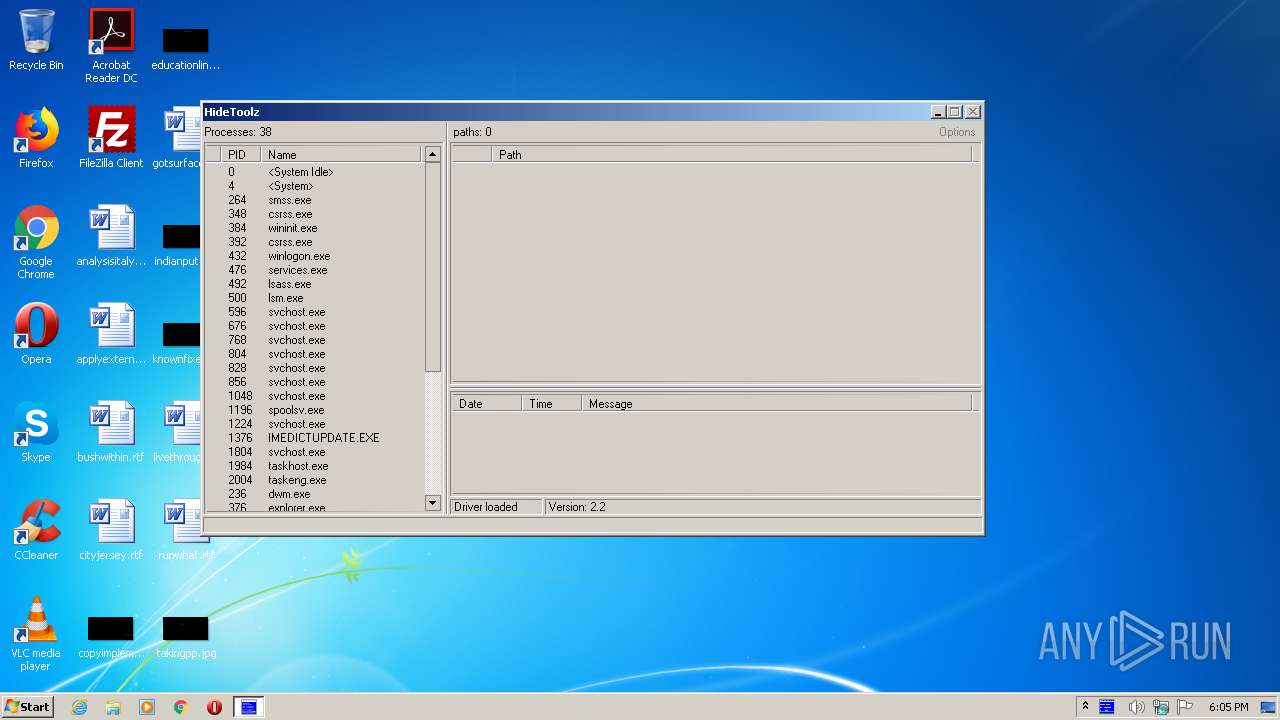
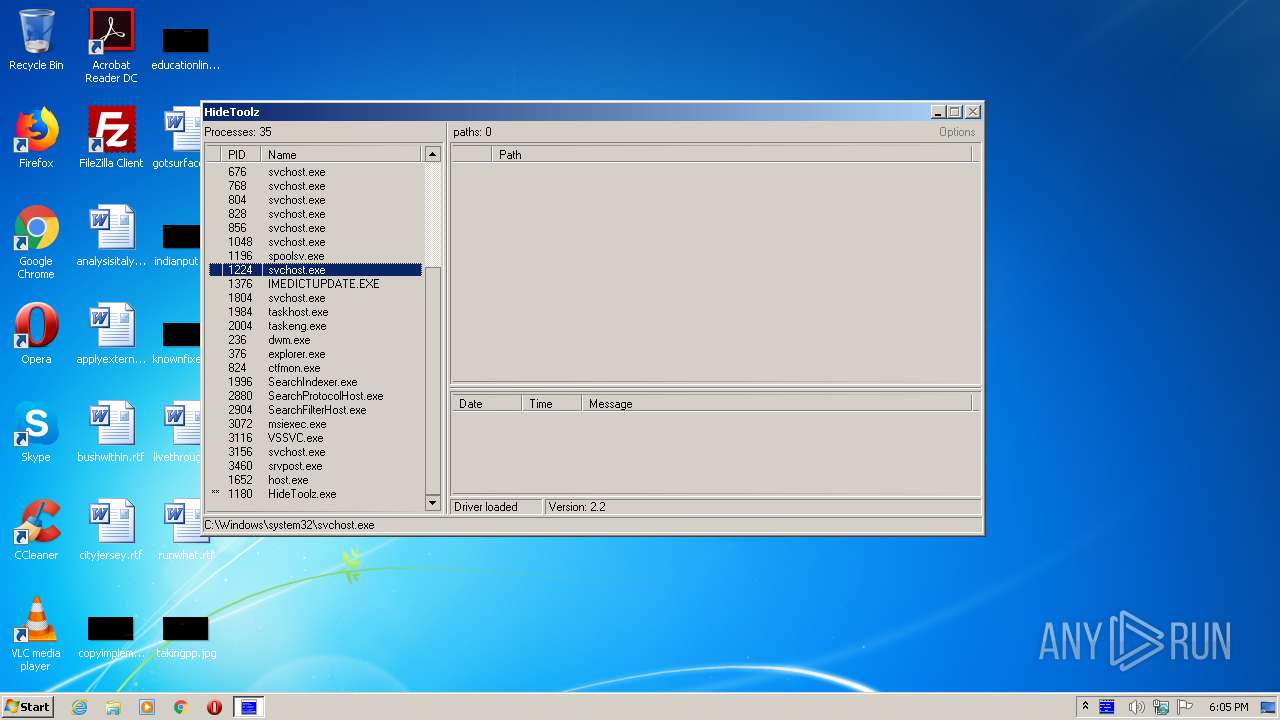
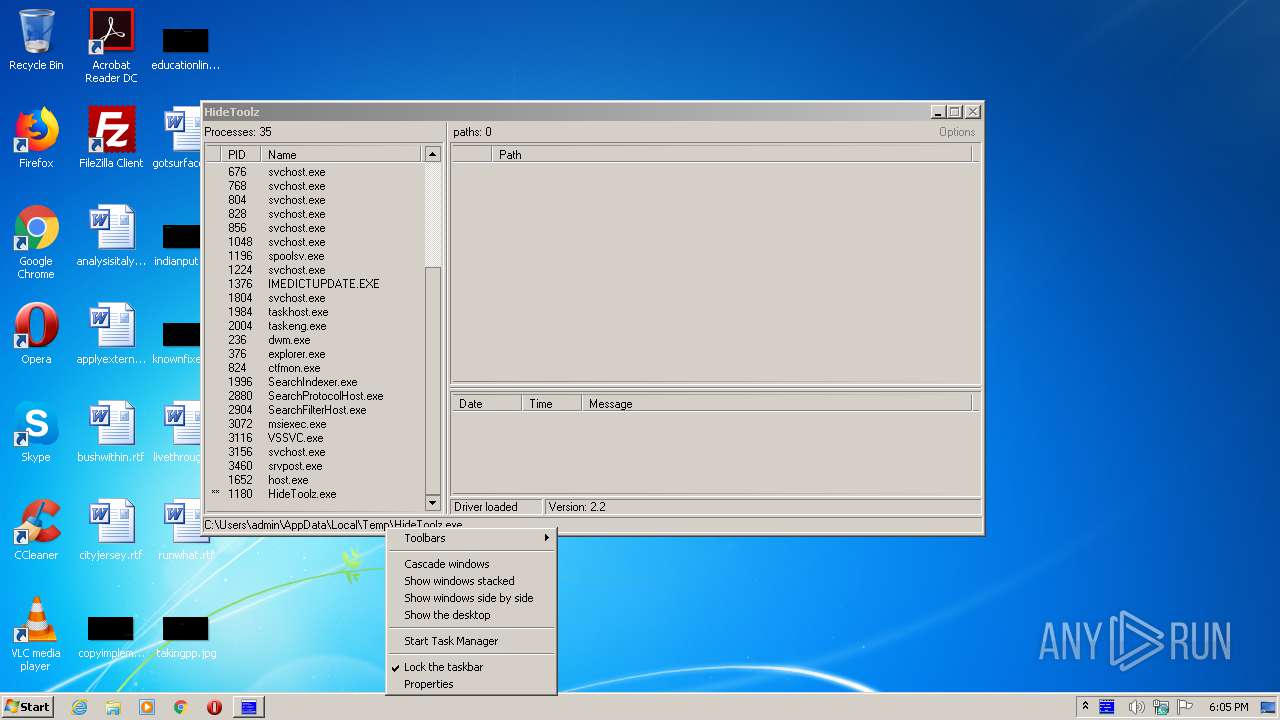
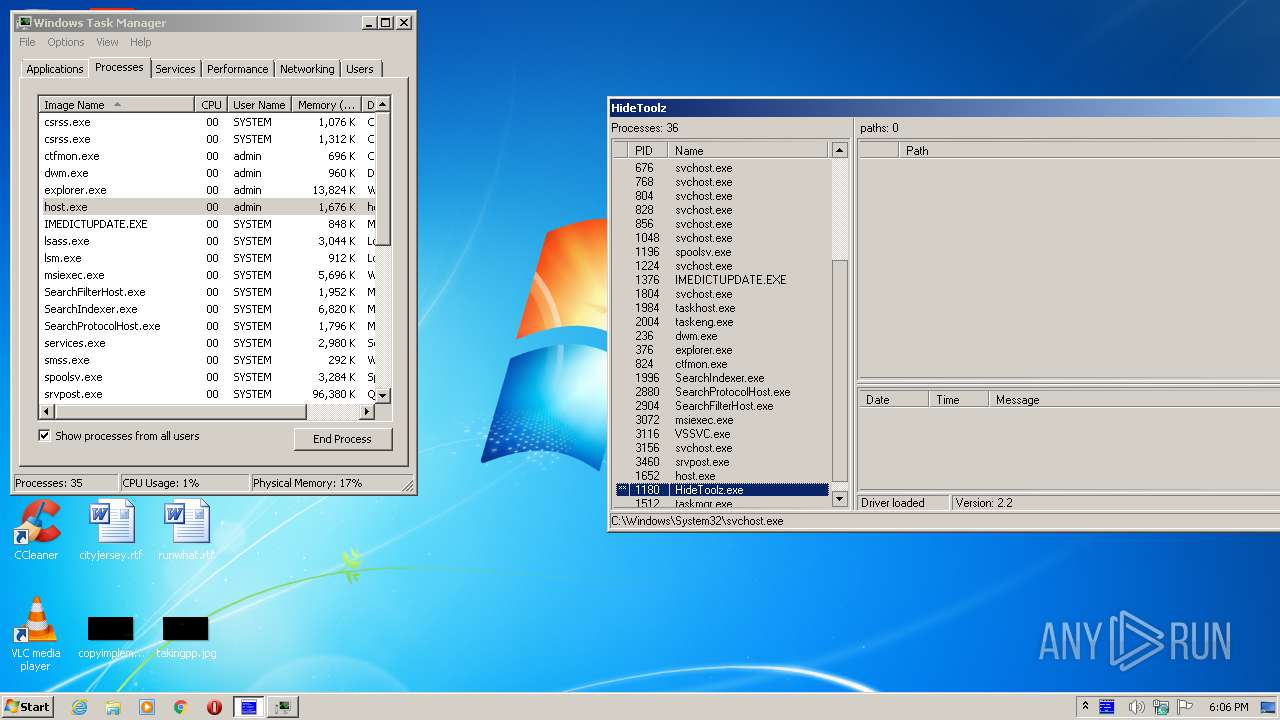
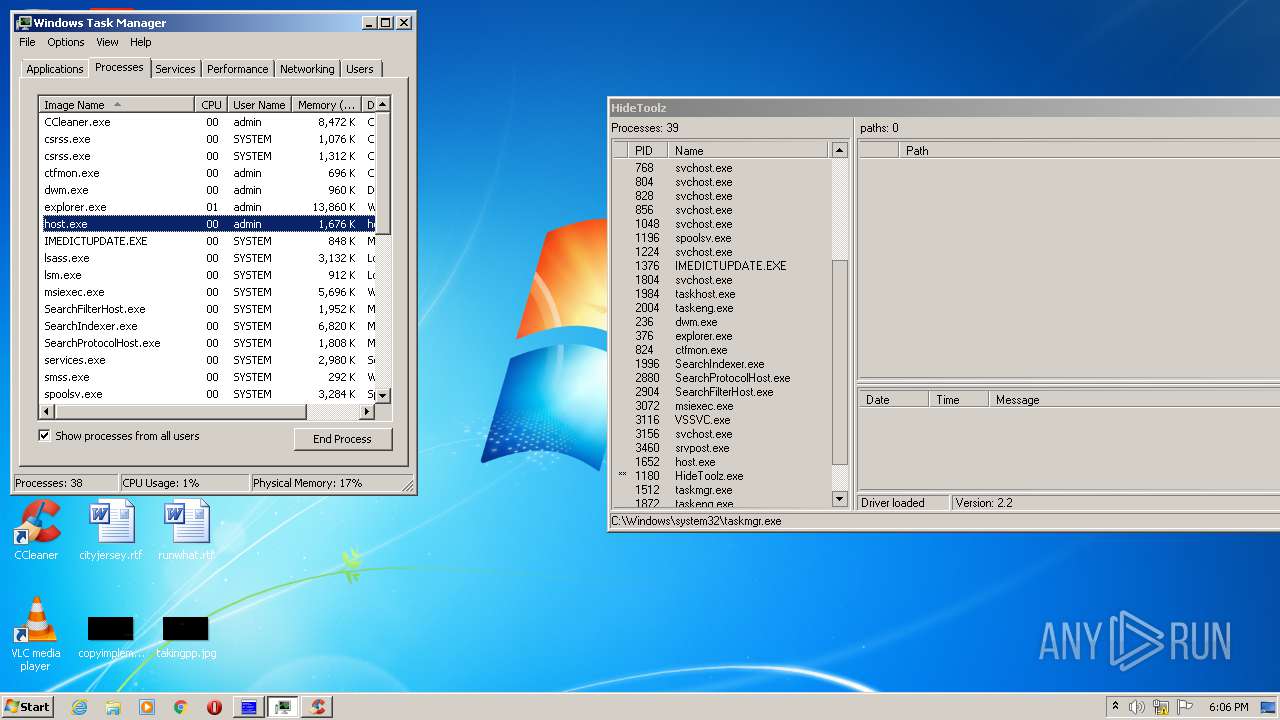
Total processes
50
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
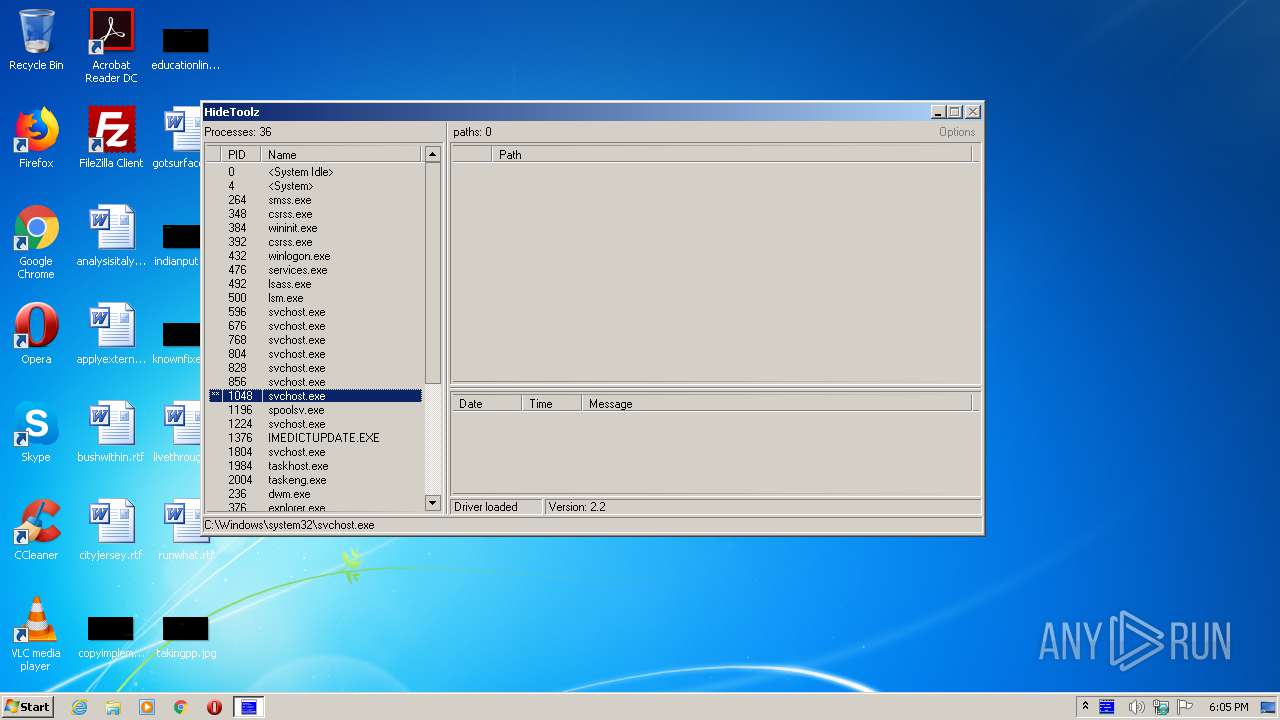
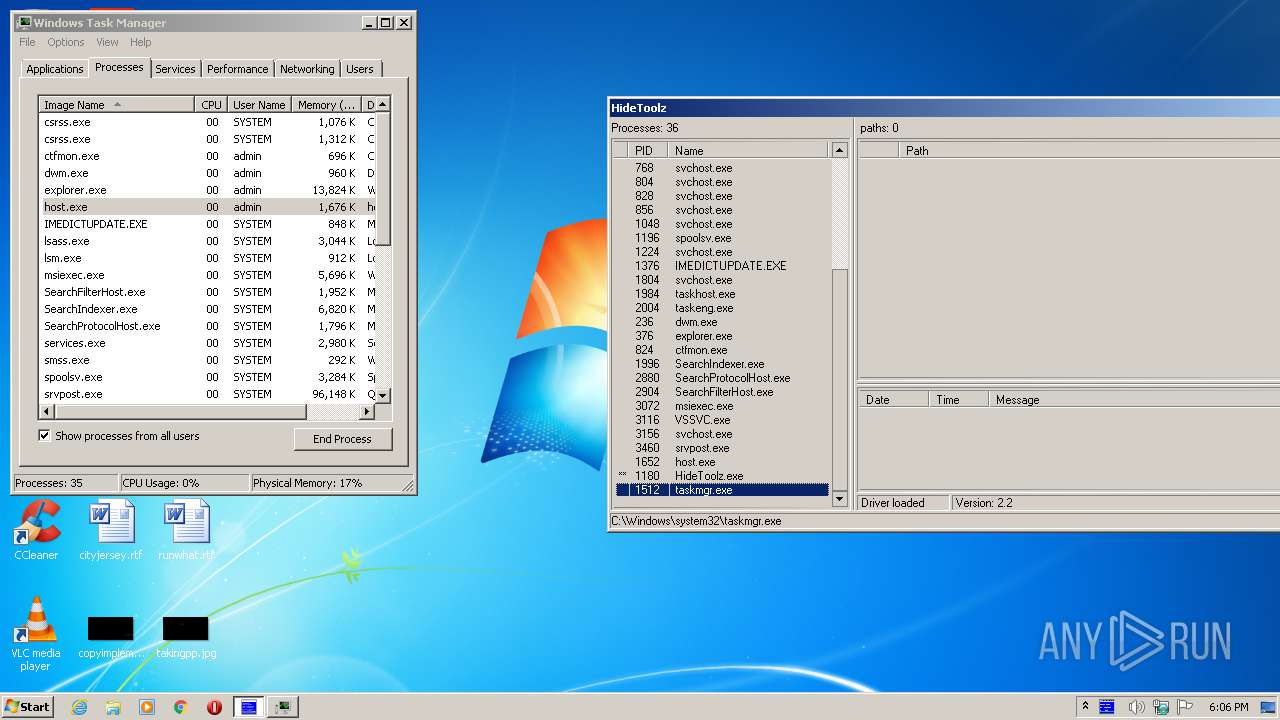
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
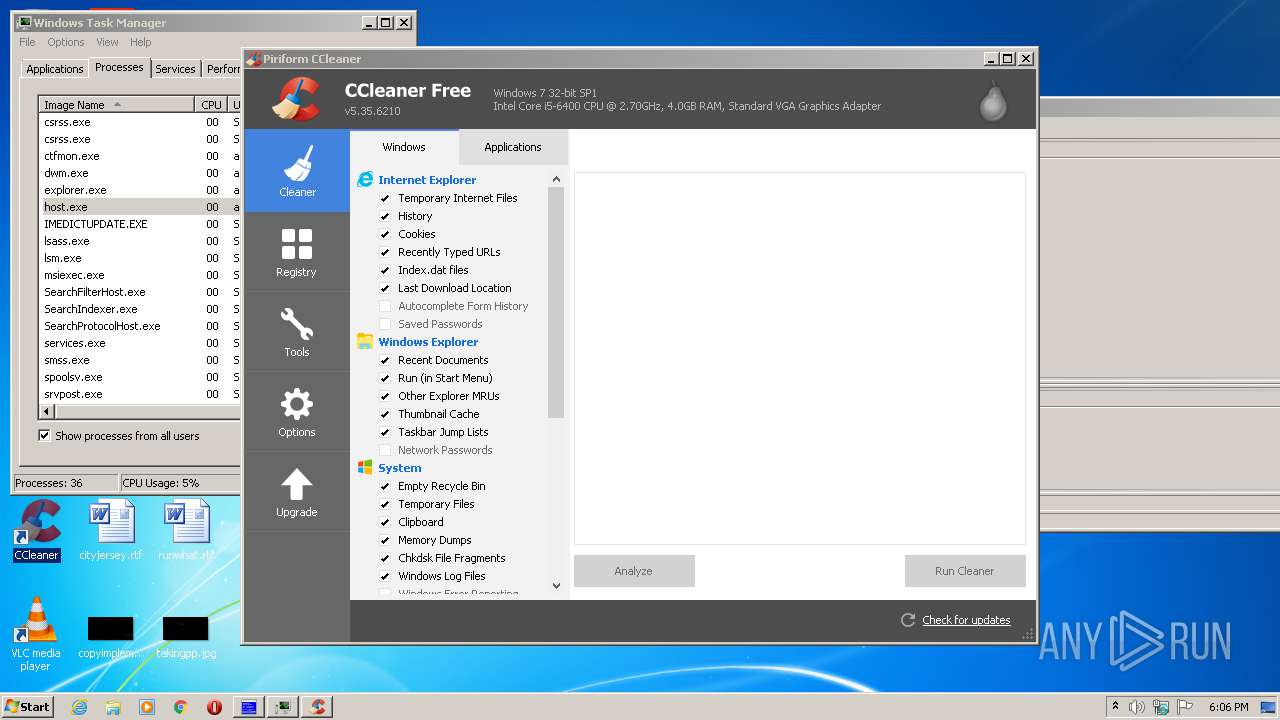
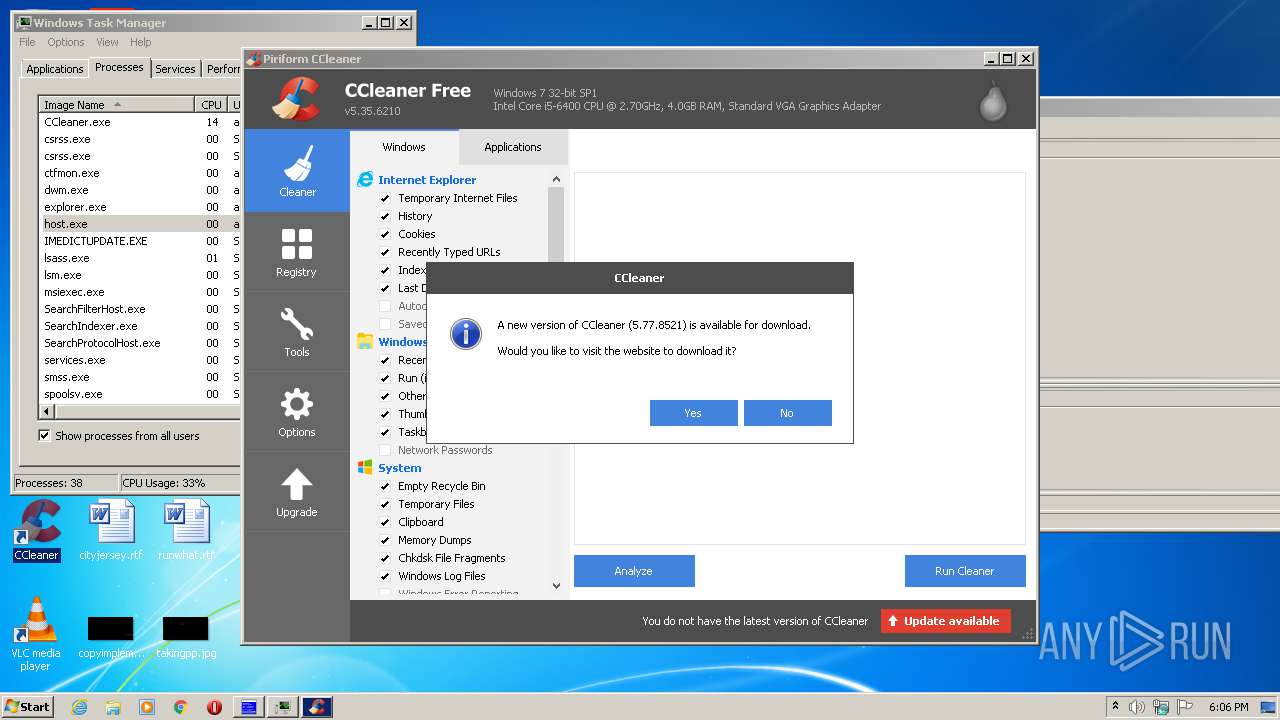
| 1000 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 1180 | "C:\Users\admin\AppData\Local\Temp\HideToolz.exe" | C:\Users\admin\AppData\Local\Temp\HideToolz.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1512 | "C:\Windows\system32\taskmgr.exe" /1 | C:\Windows\system32\taskmgr.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1920 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 3428 | "C:\Users\admin\AppData\Local\Temp\HideToolz.exe" | C:\Users\admin\AppData\Local\Temp\HideToolz.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
666
Read events
467
Write events
197
Delete events
2
Modification events
| (PID) Process: | (1180) HideToolz.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\96D.sys |
| Operation: | write | Name: | ImagePath |
Value: \??\C:\Windows\temp\96D.sys | |||
| (PID) Process: | (1180) HideToolz.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\96D.sys |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (1180) HideToolz.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\96D.sys\Enum |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1180) HideToolz.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\96D.sys |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1920) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1920) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1920) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000000A0000000A000000A2010000F00100000100000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
| (PID) Process: | (1920) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (1000) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | NewVersion |
Value: | |||
| (PID) Process: | (1000) CCleaner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
7
Text files
21
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1000 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UPGJTCFUD3H61X313H0I.temp | — | |
MD5:— | SHA256:— | |||
| 1000 | CCleaner.exe | C:\Users\admin\AppData\Local\Temp\Cab54D2.tmp | — | |
MD5:— | SHA256:— | |||
| 1000 | CCleaner.exe | C:\Users\admin\AppData\Local\Temp\Tar54D3.tmp | — | |
MD5:— | SHA256:— | |||
| 1000 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EVT0GDNPHQBPQZ0ELIWD.temp | — | |
MD5:— | SHA256:— | |||
| 1000 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\05VQKYZJF4WRRUE4AVM4.temp | — | |
MD5:— | SHA256:— | |||
| 1180 | HideToolz.exe | C:\Users\admin\AppData\Local\Temp\HideToolz.ini | text | |
MD5:— | SHA256:— | |||
| 1000 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0DA515F703BB9B49479E8697ADB0B955_7DC3E633EDFAEFC3AA3C99552548EC2F | binary | |
MD5:— | SHA256:— | |||
| 1000 | CCleaner.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\auto[1].txt | text | |
MD5:— | SHA256:— | |||
| 1000 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\ACF244F1A10D4DBED0D88EBA0C43A9B5_16756CC7371BB76A269719AA1471E96C | der | |
MD5:— | SHA256:— | |||
| 1000 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\ACF244F1A10D4DBED0D88EBA0C43A9B5_16756CC7371BB76A269719AA1471E96C | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1000 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VAKU&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
1000 | CCleaner.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8EJH | US | der | 1.48 Kb | whitelisted |
1000 | CCleaner.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
1000 | CCleaner.exe | GET | 200 | 151.101.2.109:80 | http://license.piriform.com/verify/?p=ccpro&c=cc&cv=5.35.6210&l=1033&lk=CJ9T-J7CU-SPNV-GWMB-WBEC&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VAKU&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | text | 14 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1000 | CCleaner.exe | 151.101.0.64:443 | www.piriform.com | Fastly | US | whitelisted |
1000 | CCleaner.exe | 151.101.0.64:80 | www.piriform.com | Fastly | US | whitelisted |
1000 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
1000 | CCleaner.exe | 151.101.2.133:80 | ocsp.globalsign.com | Fastly | US | malicious |
1000 | CCleaner.exe | 151.101.2.109:443 | license.piriform.com | Fastly | US | suspicious |
1000 | CCleaner.exe | 151.101.2.109:80 | license.piriform.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.piriform.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
license.piriform.com |
| whitelisted |