| File name: | 9c4315dad05f9f70982630ff023a6073d6badaed840130ce1342ca9ebf3bb5d1.apk |
| Full analysis: | https://app.any.run/tasks/991f1212-5cba-4078-b7a8-5f339a79bcdb |
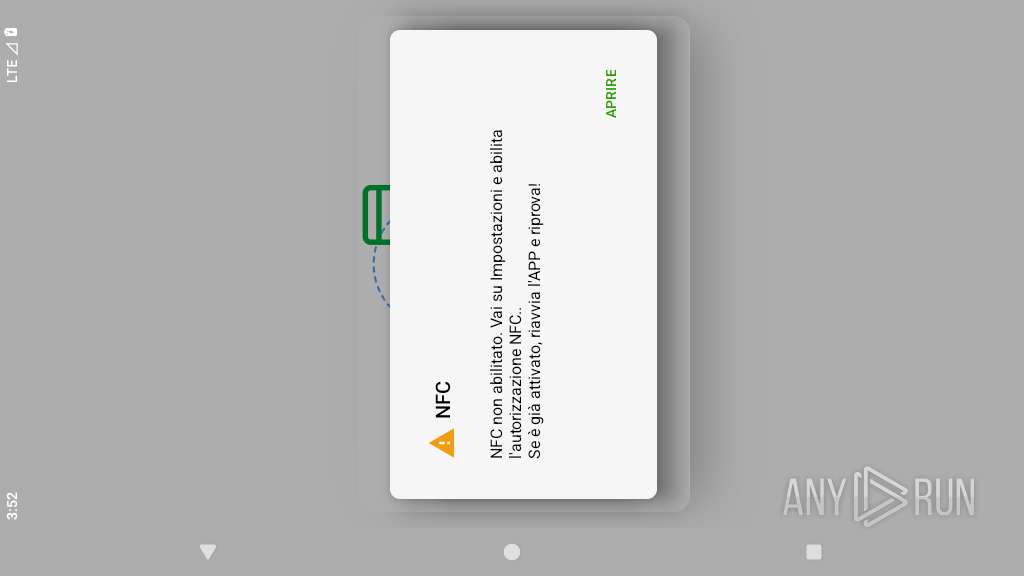
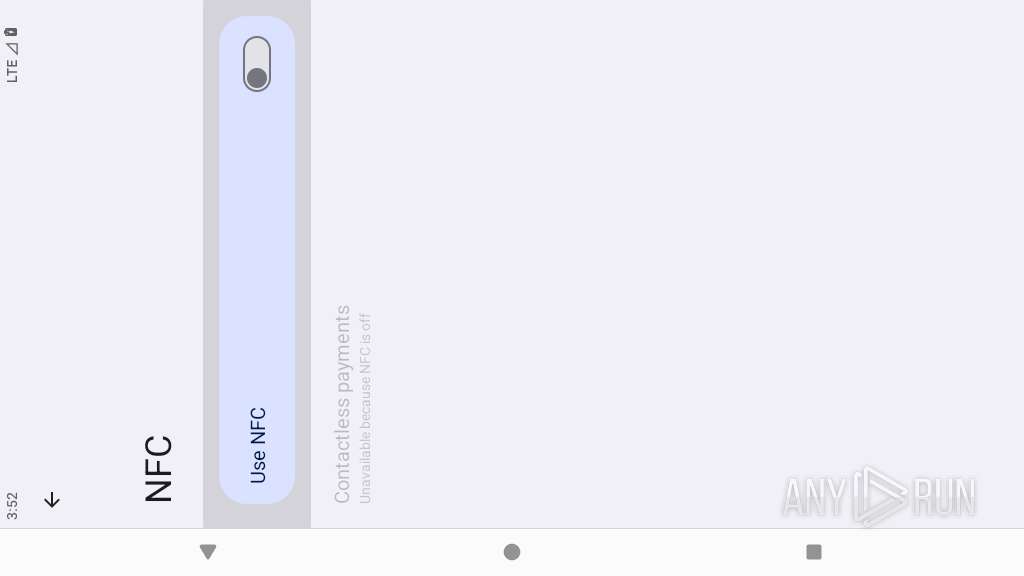
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2026, 15:52:27 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with classes.dex, with APK Signing Block |
| MD5: | F8F0158BA2C904585534C547F3C0A05B |
| SHA1: | 35BC6632F6EFBE414519E115C0C748312855B43D |
| SHA256: | 9C4315DAD05F9F70982630FF023A6073D6BADAED840130CE1342CA9EBF3BB5D1 |
| SSDEEP: | 98304:sYLq3h21PTlXRRvbn96QVbmxR2SjlAlYVrxvGaznpbKEynmzcckCY2y3KCI7VBNV:dPs |
MALICIOUS
No malicious indicators.SUSPICIOUS
Retrieves Android OS build information
- app_process64 (PID: 2837)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2837)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2837)
Launches a new activity
- app_process64 (PID: 2837)
INFO
Dynamically loads a class in Java
- app_process64 (PID: 2837)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2837)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2837)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2837)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2837)
Gets file name without full path
- app_process64 (PID: 2837)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (67.3) |
|---|---|---|
| .jar | | | Java Archive (18.5) |
| .zip | | | ZIP compressed archive (5.1) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2026:03:17 14:13:20 |
| ZipCRC: | 0xb7499fbc |
| ZipCompressedSize: | 114368 |
| ZipUncompressedSize: | 261264 |
| ZipFileName: | classes.dex |
Total processes
130
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2837 | zygote64 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2878 | com.android.webview:webview_service | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2890 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2976 | com.android.webview:webview_apk | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
17
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2837 | app_process64 | /data/data/com.modol.nap/app_webview/last-exit-info | text | |
MD5:— | SHA256:— | |||
| 2837 | app_process64 | /data/data/com.modol.nap/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2837 | app_process64 | /data/data/com.modol.nap/app_webview/Default/Web Data-journal | binary | |
MD5:— | SHA256:— | |||
| 2837 | app_process64 | /data/data/com.modol.nap/cache/WebView/Default/HTTP Cache/Code Cache/js/index | binary | |
MD5:— | SHA256:— | |||
| 2837 | app_process64 | /data/data/com.modol.nap/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index | binary | |
MD5:— | SHA256:— | |||
| 2837 | app_process64 | /data/data/com.modol.nap/cache/WebView/Default/HTTP Cache/Code Cache/js/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
| 2837 | app_process64 | /data/data/com.modol.nap/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
| 2837 | app_process64 | /data/data/com.modol.nap/app_webview/Default/Shared Dictionary/cache/index | binary | |
MD5:— | SHA256:— | |||
| 2837 | app_process64 | /data/data/com.modol.nap/app_webview/Default/Shared Dictionary/cache/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
| 2837 | app_process64 | /data/data/com.modol.nap/app_webview/Default/DIPS-journal | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
11
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
822 | app_process64 | GET | 204 | 142.251.154.119:443 | https://www.google.com/generate_204 | unknown | — | — | whitelisted |
822 | app_process64 | GET | 204 | 142.251.141.99:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
1756 | app_process64 | POST | 200 | 142.251.127.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | unknown | binary | 778 b | whitelisted |
1756 | app_process64 | POST | 200 | 142.251.127.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:signCertificates?challenge=AAABnT9yodkBILStY5X3c3M-vlESUiPXPUk3e5M=&request_id=54a1f129-fd09-4819-b86c-03b6cf6e9296 | unknown | binary | 11.8 Kb | whitelisted |
2976 | app_process32 | POST | 200 | 172.217.16.195:443 | https://update.googleapis.com/service/update2/json?cup2key=15:DPIIi_wuheyvSGlXLpHVHGEfSixJlNACpD9VtSYb-DU&cup2hreq=96ed4f01ff7039e97e02d2a969396cf303aa607eea33851376bf96395383c3b5 | unknown | text | 1.92 Kb | whitelisted |
2976 | app_process32 | POST | 200 | 172.217.16.195:443 | https://update.googleapis.com/service/update2/json | unknown | text | 252 b | whitelisted |
2976 | app_process32 | GET | 200 | 34.104.35.123:443 | https://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acmmwq7dser4xm5sepzjv74g65vq_2023.7.28.10/cffplpkejcbdpfnfabnjikeicbedmifn_2023.07.28.10_all_acgbwixmcanakp2bkoppyszsbkrq.crx3 | unknown | binary | 6.71 Kb | whitelisted |
2878 | app_process32 | GET | 200 | 142.251.127.94:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=android_webview&milestone=137 | unknown | compressed | 14.8 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 142.251.153.119:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.141.99:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.251.151.119:443 | www.google.com | GOOGLE | US | whitelisted |
443 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
822 | app_process64 | 142.251.141.99:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
571 | app_process64 | 216.239.35.4:123 | time.android.com | GOOGLE | US | whitelisted |
822 | app_process64 | 142.251.154.119:443 | www.google.com | GOOGLE | US | whitelisted |
2976 | app_process32 | 172.217.16.195:443 | update.googleapis.com | GOOGLE | US | whitelisted |
1756 | app_process64 | 142.251.127.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2878 | app_process32 | 142.251.127.94:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
822 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |