| download: | install.ps1 |
| Full analysis: | https://app.any.run/tasks/ce072695-7a8a-4d3e-af3c-3660bc6253c6 |
| Verdict: | No threats detected |
| Analysis date: | January 14, 2020, 14:27:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text |
| MD5: | 27BDE2C20E39760214817E2BEEFA88E9 |
| SHA1: | 4BFA46FD3BE26597D8C3B4209043DBE92432E36D |
| SHA256: | 9C0929D286DFACDA60D7CFF29F65FDDFAA31E1B59924D010FA35ED324227BF44 |
| SSDEEP: | 96:XhKQHWSouYK+QhYfQ8VRxD5QZaklcg4bM9z5rFswzo:4QHWSzYK+QhYzRl5QPlFSo5Wwzo |
MALICIOUS
No malicious indicators.SUSPICIOUS
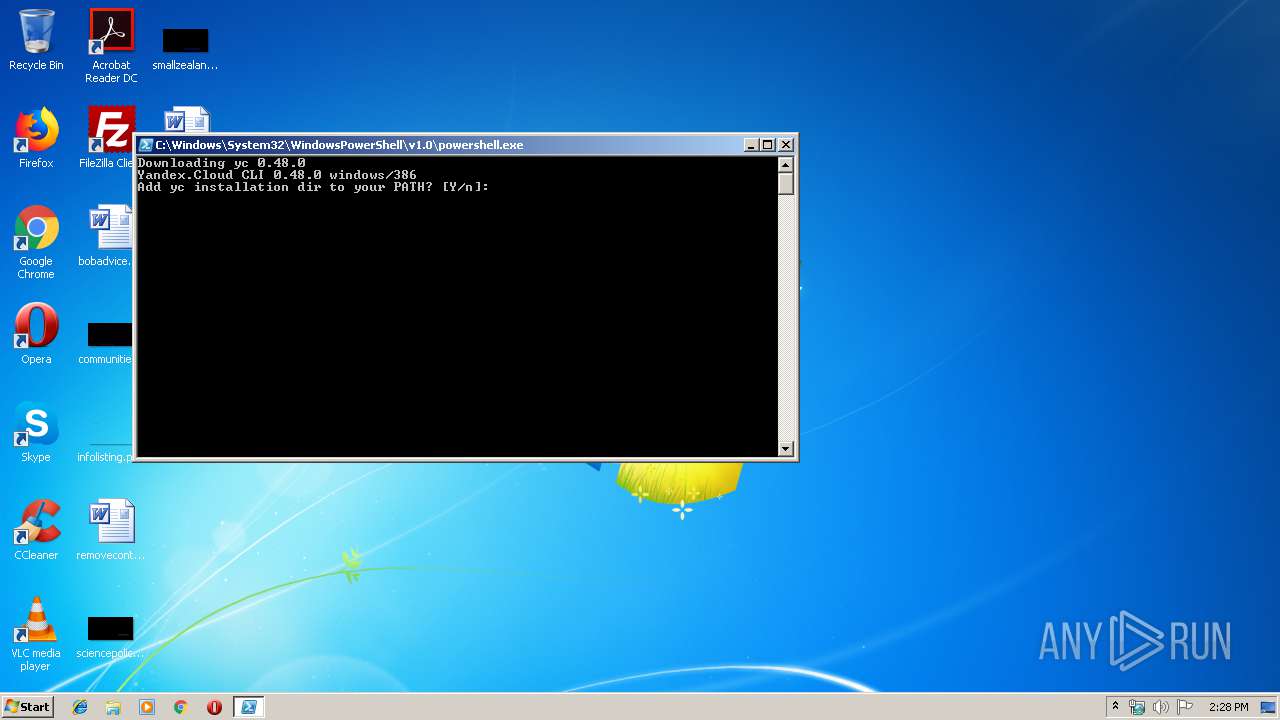
PowerShell script executed
- powershell.exe (PID: 2740)
Creates files in the user directory
- powershell.exe (PID: 2740)
INFO
Reads settings of System Certificates
- powershell.exe (PID: 2740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1936 | "C:\Users\admin\yandex-cloud\bin\yc.exe" components post-update | C:\Users\admin\yandex-cloud\bin\yc.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2740 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\install.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3776 | "C:\Users\admin\AppData\Local\Temp\ycInstall\yc.exe" version | C:\Users\admin\AppData\Local\Temp\ycInstall\yc.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
296
Read events
209
Write events
87
Delete events
0
Modification events
| (PID) Process: | (2740) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2740) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2740) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2740) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FNH0DXZQE8SLLJYOCEG3.temp | — | |
MD5:— | SHA256:— | |||
| 2740 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ycInstall\yc.exe | — | |
MD5:— | SHA256:— | |||
| 2740 | powershell.exe | C:\Users\admin\yandex-cloud\bin\yc.exe | — | |
MD5:— | SHA256:— | |||
| 2740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39a6ca.TMP | binary | |
MD5:— | SHA256:— | |||
| 1936 | yc.exe | C:\Users\admin\yandex-cloud\bin\docker-credential-yc.cmd | text | |
MD5:224D64A1CBE1CD9156DE44F2104614CE | SHA256:0FB2A982AE9D37C913761046E2AAF47F15824DAFEED9B75B46347261DF549318 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2740 | powershell.exe | 213.180.193.243:443 | storage.yandexcloud.net | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
storage.yandexcloud.net |
| unknown |