| File name: | 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6 |
| Full analysis: | https://app.any.run/tasks/ab376458-976a-4ca8-811b-4ad12fe13b59 |
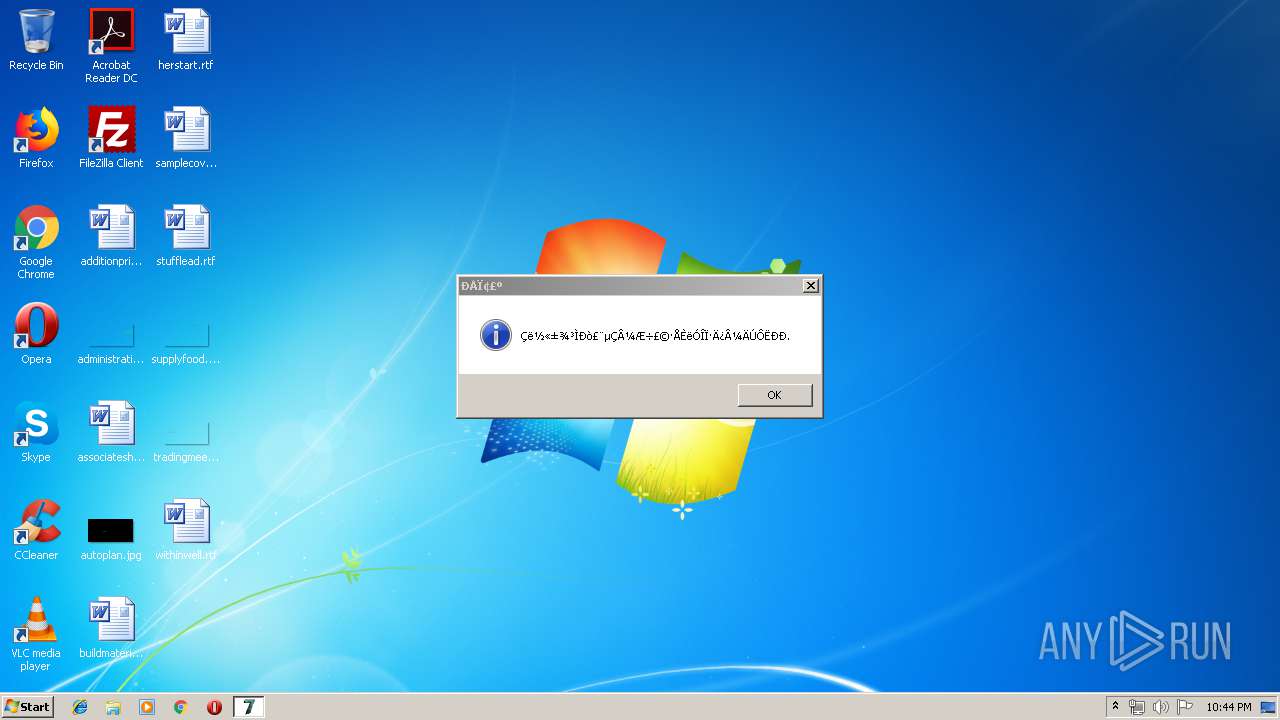
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 21:44:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 41F803B67D8E71BAF3DED52430C59B52 |
| SHA1: | 50D621CA671CEF718DA2B3A09744099D19790D3A |
| SHA256: | 9BFAB76542E63A86D45F3B233D54510B2EEB10A7532EB21BF53DBA0288721FE6 |
| SSDEEP: | 98304:ovaAQf8VFZN98jGUxFCTXyh9Rs7hlDOoaCauiwWnkgQsk4PojHRMUeVkNWmICs6u:iff98jl/YXyhPuiwd4PgKk4e5fp9m |
MALICIOUS
Changes settings of System certificates
- svchost.exe (PID: 116)
Uses SVCHOST.EXE for hidden code execution
- 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe (PID: 2368)
SUSPICIOUS
Reads internet explorer settings
- svchost.exe (PID: 3644)
- svchost.exe (PID: 116)
- svchost.exe (PID: 2456)
- svchost.exe (PID: 3260)
Executable content was dropped or overwritten
- 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe (PID: 2368)
Reads Internet Cache Settings
- svchost.exe (PID: 116)
- svchost.exe (PID: 3260)
- svchost.exe (PID: 3644)
- svchost.exe (PID: 2456)
Creates files in the user directory
- svchost.exe (PID: 116)
Low-level read access rights to disk partition
- 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe (PID: 2368)
Adds / modifies Windows certificates
- svchost.exe (PID: 116)
INFO
Reads settings of System Certificates
- svchost.exe (PID: 116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (22.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (17.1) |
| .exe | | | Win64 Executable (generic) (15.1) |
| .exe | | | UPX compressed Win32 Executable (14.8) |
| .exe | | | Win32 EXE Yoda's Crypter (14.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:03 12:06:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1003520 |
| InitializedDataSize: | 11206656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd34c5 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.8.0 |
| ProductVersionNumber: | 1.6.8.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.6.8.0 |
| FileDescription: | 七日杀反外挂登录器-客户端 |
| ProductName: | 七日杀反外挂登录器-客户端 |
| ProductVersion: | 1.6.8.0 |
| CompanyName: | 腾龙网络 |
| LegalCopyright: | Yy:9912746 |
| Comments: | 七日杀反外挂登录器-客户端 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Sep-2018 10:06:33 |
| Detected languages: |
|
| FileVersion: | 1.6.8.0 |
| FileDescription: | 七日杀反外挂登录器-客户端 |
| ProductName: | 七日杀反外挂登录器-客户端 |
| ProductVersion: | 1.6.8.0 |
| CompanyName: | 腾龙网络 |
| LegalCopyright: | Yy:9912746 |
| Comments: | 七日杀反外挂登录器-客户端 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Sep-2018 10:06:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000F42E6 | 0x000F5000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47982 |
.rdata | 0x000F6000 | 0x00A0320A | 0x00A04000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.27003 |
.data | 0x00AFA000 | 0x00068EEA | 0x0001B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.43403 |
.rsrc | 0x00B63000 | 0x00090128 | 0x00091000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.42716 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02094 | 697 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 3.23583 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.94557 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.91689 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 2.57764 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 2.57903 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 2.28337 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 2.28315 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 2.08551 | 152104 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
AVIFIL32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVFW32.dll |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
USER32.dll |
Total processes
40
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | svchost.exe | C:\Windows\system32\svchost.exe | 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Users\admin\AppData\Local\Temp\9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe" | C:\Users\admin\AppData\Local\Temp\9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | explorer.exe | ||||||||||||
User: admin Company: 腾龙网络 Integrity Level: HIGH Description: 七日杀反外挂登录器-客户端 Exit code: 0 Version: 1.6.8.0 Modules
| |||||||||||||||
| 2456 | svchost.exe | C:\Windows\system32\svchost.exe | — | 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | svchost.exe | C:\Windows\system32\svchost.exe | — | 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3320 | "C:\Users\admin\AppData\Local\Temp\9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe" | C:\Users\admin\AppData\Local\Temp\9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | — | explorer.exe | |||||||||||
User: admin Company: 腾龙网络 Integrity Level: MEDIUM Description: 七日杀反外挂登录器-客户端 Exit code: 3221226540 Version: 1.6.8.0 Modules
| |||||||||||||||
| 3644 | svchost.exe | C:\Windows\system32\svchost.exe | — | 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
433
Read events
365
Write events
67
Delete events
1
Modification events
| (PID) Process: | (2368) 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | vga.drv 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
| (PID) Process: | (2456) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2456) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (116) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (116) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3644) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3644) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3260) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3260) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (116) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
113
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2368 | 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | C:\Users\admin\AppData\Local\Temp\135806.tmp | — | |
MD5:— | SHA256:— | |||
| 2368 | 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | C:\Users\admin\AppData\Local\Temp\135817.tmp | — | |
MD5:— | SHA256:— | |||
| 2368 | 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | C:\Users\admin\AppData\Local\Temp\135818.tmp | — | |
MD5:— | SHA256:— | |||
| 116 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019052020190521\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2368 | 9bfab76542e63a86d45f3b233d54510b2eeb10a7532eb21bf53dba0288721fe6.exe | C:\Users\admin\AppData\Local\Temp\TxKePfU.sys | executable | |
MD5:— | SHA256:— | |||
| 116 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\mojunyy_cn[1].txt | html | |
MD5:— | SHA256:— | |||
| 116 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\cansu521[1].txt | text | |
MD5:— | SHA256:— | |||
| 116 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\style[1].css | text | |
MD5:— | SHA256:— | |||
| 116 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\index[1].css | text | |
MD5:— | SHA256:— | |||
| 116 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\icomoon[1].eot | eot | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
74
TCP/UDP connections
47
DNS requests
22
Threats
74
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | svchost.exe | GET | 200 | 45.249.95.61:80 | http://www.mojunyy.cn/css/style.css | CN | text | 57.7 Kb | malicious |
116 | svchost.exe | GET | 200 | 99.84.87.217:80 | http://p4.qhimg.com/d/dy_480ce098fefc7cf73f5f9eb686fc19be.jpg | US | image | 23.2 Kb | whitelisted |
116 | svchost.exe | GET | 200 | 45.249.95.61:80 | http://www.mojunyy.cn/js/view-history.js | CN | text | 206 Kb | malicious |
116 | svchost.exe | GET | 200 | 99.84.87.152:80 | http://p8.qhimg.com/d/dy_282bbddb83908377daa9c2d3c1f0b0e4.jpg | US | image | 22.4 Kb | whitelisted |
116 | svchost.exe | GET | 200 | 45.249.95.61:80 | http://www.mojunyy.cn/images/qrcode.png | CN | image | 49.3 Kb | malicious |
116 | svchost.exe | GET | 200 | 99.84.87.217:80 | http://p4.qhimg.com/d/dy_c2c8e5ca2c8f3a449c38c725d0ce2fca.jpg | US | image | 32.4 Kb | whitelisted |
116 | svchost.exe | GET | 200 | 99.84.87.89:80 | http://p5.qhimg.com/d/dy_853190cb781fa29b2ed649f89b5c1903.jpg | US | image | 22.2 Kb | whitelisted |
116 | svchost.exe | GET | 200 | 99.84.87.152:80 | http://p8.qhimg.com/d/dy_3cb6775097e573fcca0dbf0e671bb98f. | US | image | 405 Kb | whitelisted |
116 | svchost.exe | GET | 200 | 45.249.95.61:80 | http://www.mojunyy.cn/cansu521.txt | CN | text | 2.57 Kb | malicious |
116 | svchost.exe | GET | 200 | 99.84.87.80:80 | http://p2.qhimg.com/d/dy_31fad1a6769d0bc02da0d154efaada42.jpg | US | image | 39.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
116 | svchost.exe | 45.249.95.61:80 | www.mojunyy.cn | hongkong kwaifong information service limited | CN | suspicious |
116 | svchost.exe | 119.146.74.49:80 | apps.bdimg.com | Guangdong | CN | suspicious |
116 | svchost.exe | 99.84.87.217:80 | p5.qhimg.com | AT&T Services, Inc. | US | suspicious |
116 | svchost.exe | 183.131.207.66:80 | ia.51.la | DaLi | CN | malicious |
116 | svchost.exe | 121.42.17.239:443 | item.taobao.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
116 | svchost.exe | 99.84.87.152:80 | p5.qhimg.com | AT&T Services, Inc. | US | suspicious |
116 | svchost.exe | 99.84.87.89:80 | p5.qhimg.com | AT&T Services, Inc. | US | suspicious |
116 | svchost.exe | 220.242.140.187:443 | js.users.51.la | — | CN | suspicious |
116 | svchost.exe | 99.84.87.80:80 | p5.qhimg.com | AT&T Services, Inc. | US | suspicious |
— | — | 121.42.17.239:80 | item.taobao.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mojunyy.cn |
| malicious |
apps.bdimg.com |
| whitelisted |
p5.qhimg.com |
| whitelisted |
p4.qhimg.com |
| whitelisted |
p0.qhimg.com |
| whitelisted |
p6.qhimg.com |
| whitelisted |
p8.qhimg.com |
| whitelisted |
p9.qhimg.com |
| whitelisted |
p1.qhimg.com |
| whitelisted |
p3.qhimg.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
116 | svchost.exe | A Network Trojan was detected | ET POLICY Abnormal User-Agent No space after colon - Likely Hostile |
116 | svchost.exe | A Network Trojan was detected | ET POLICY Abnormal User-Agent No space after colon - Likely Hostile |
116 | svchost.exe | A Network Trojan was detected | ET POLICY Abnormal User-Agent No space after colon - Likely Hostile |
116 | svchost.exe | A Network Trojan was detected | ET POLICY Abnormal User-Agent No space after colon - Likely Hostile |
116 | svchost.exe | A Network Trojan was detected | ET POLICY Abnormal User-Agent No space after colon - Likely Hostile |
116 | svchost.exe | A Network Trojan was detected | ET POLICY Abnormal User-Agent No space after colon - Likely Hostile |
116 | svchost.exe | A Network Trojan was detected | ET POLICY Abnormal User-Agent No space after colon - Likely Hostile |
116 | svchost.exe | A Network Trojan was detected | ET POLICY Abnormal User-Agent No space after colon - Likely Hostile |
116 | svchost.exe | A Network Trojan was detected | ET POLICY Abnormal User-Agent No space after colon - Likely Hostile |
116 | svchost.exe | A Network Trojan was detected | ET POLICY Abnormal User-Agent No space after colon - Likely Hostile |