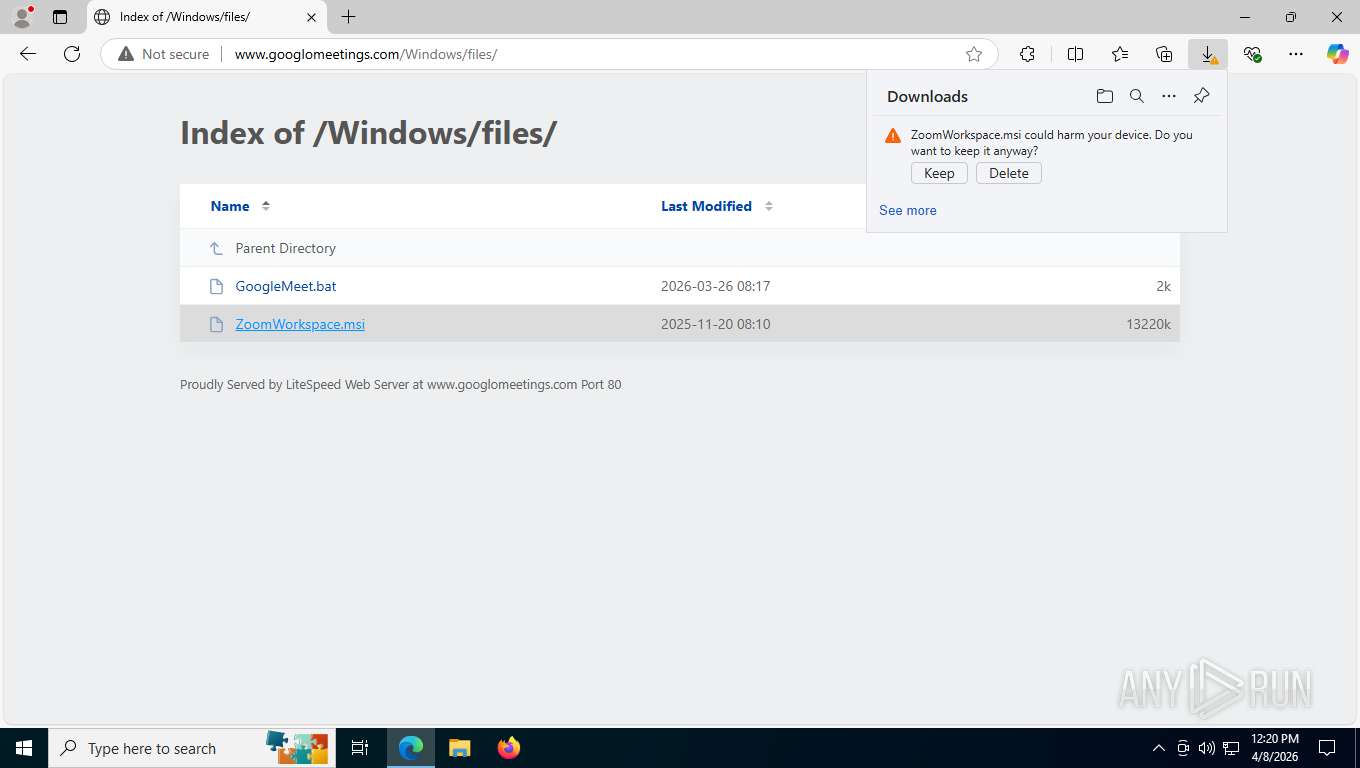
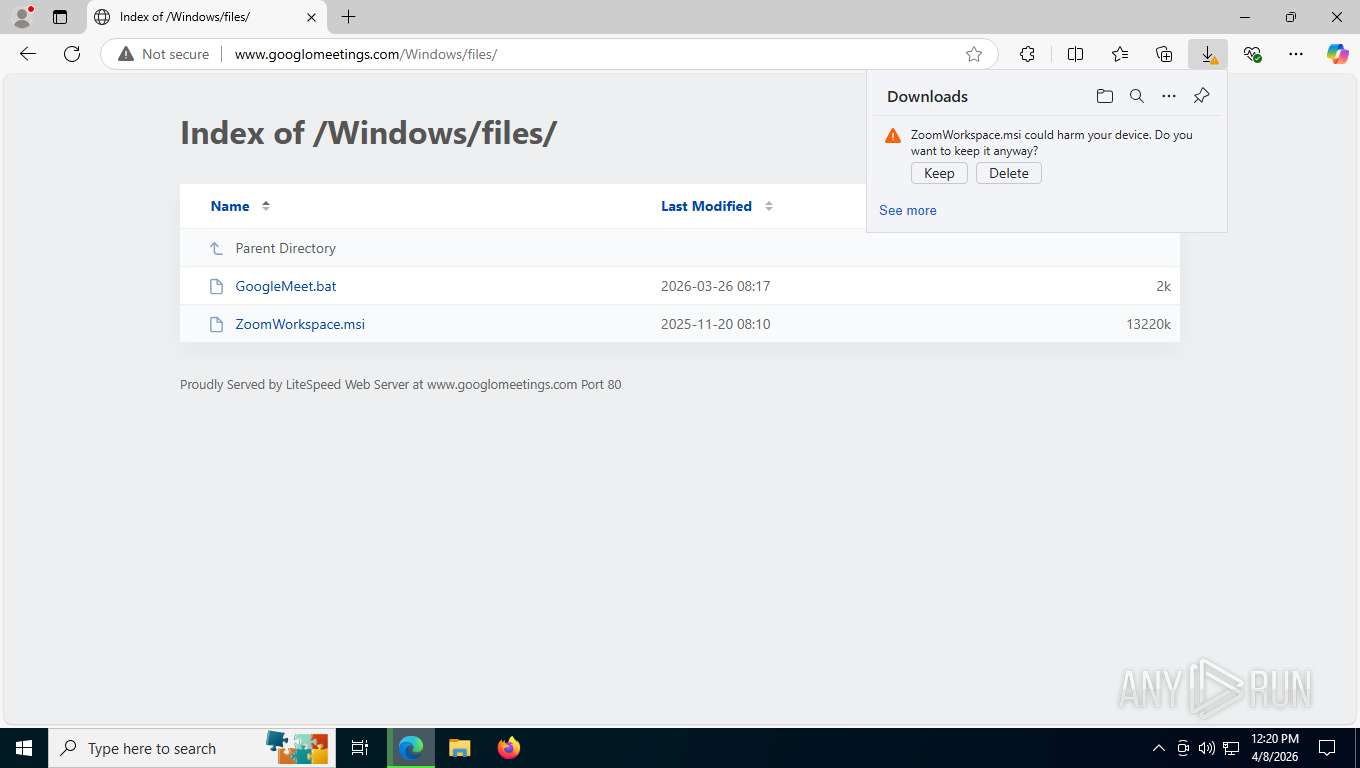
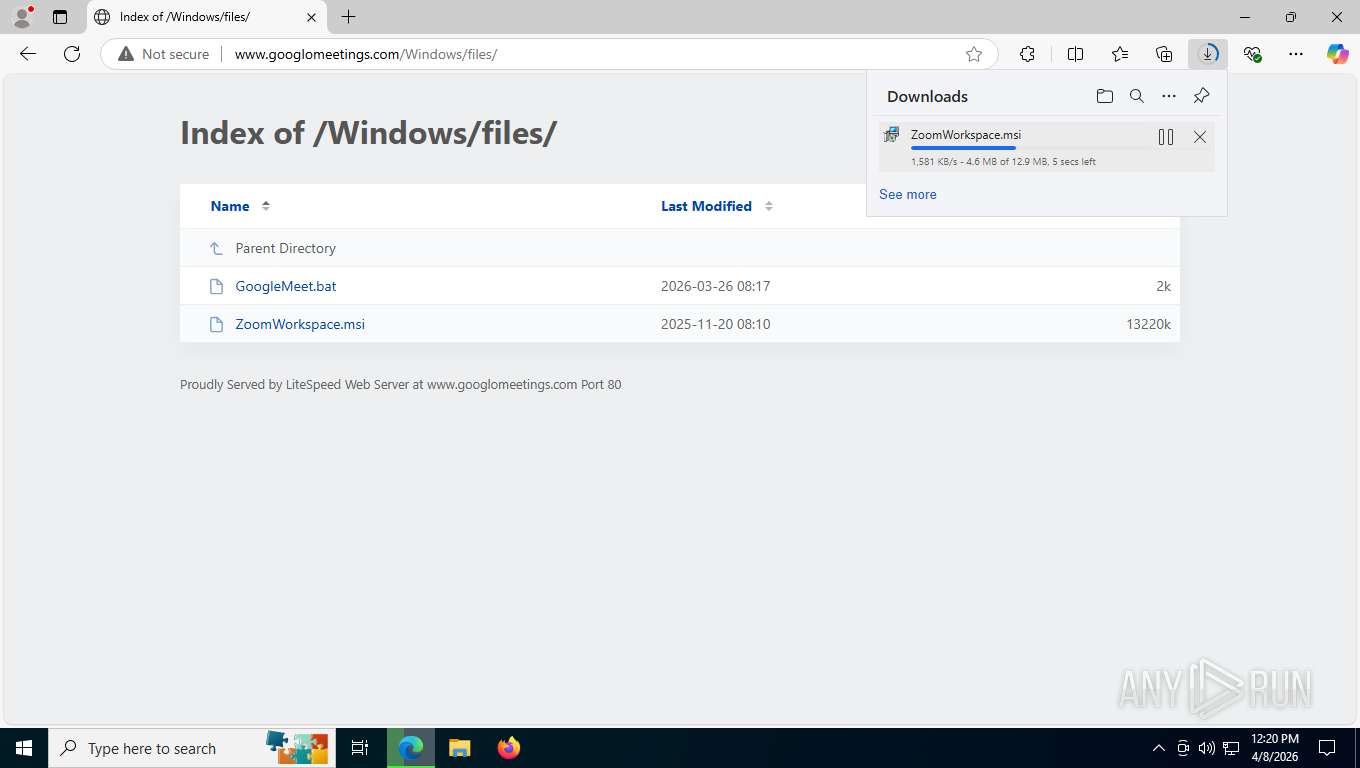
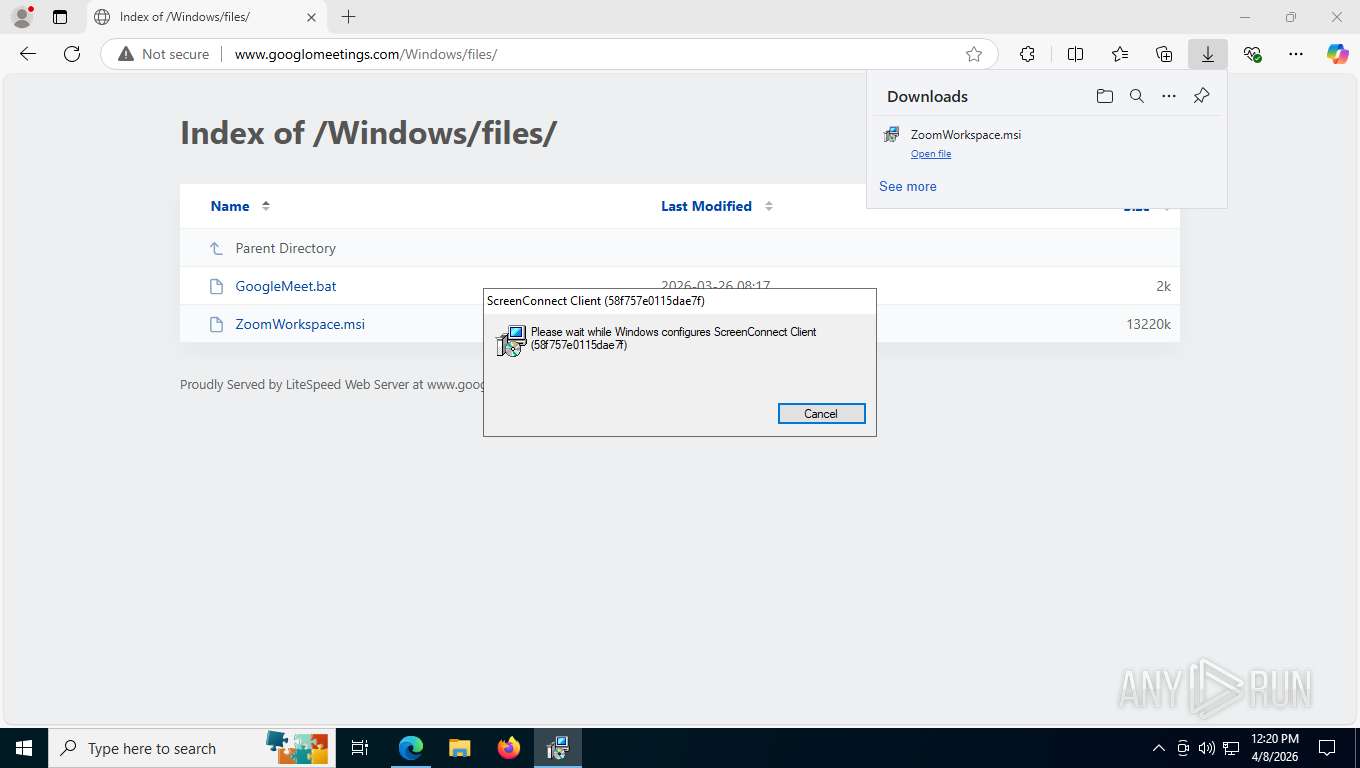
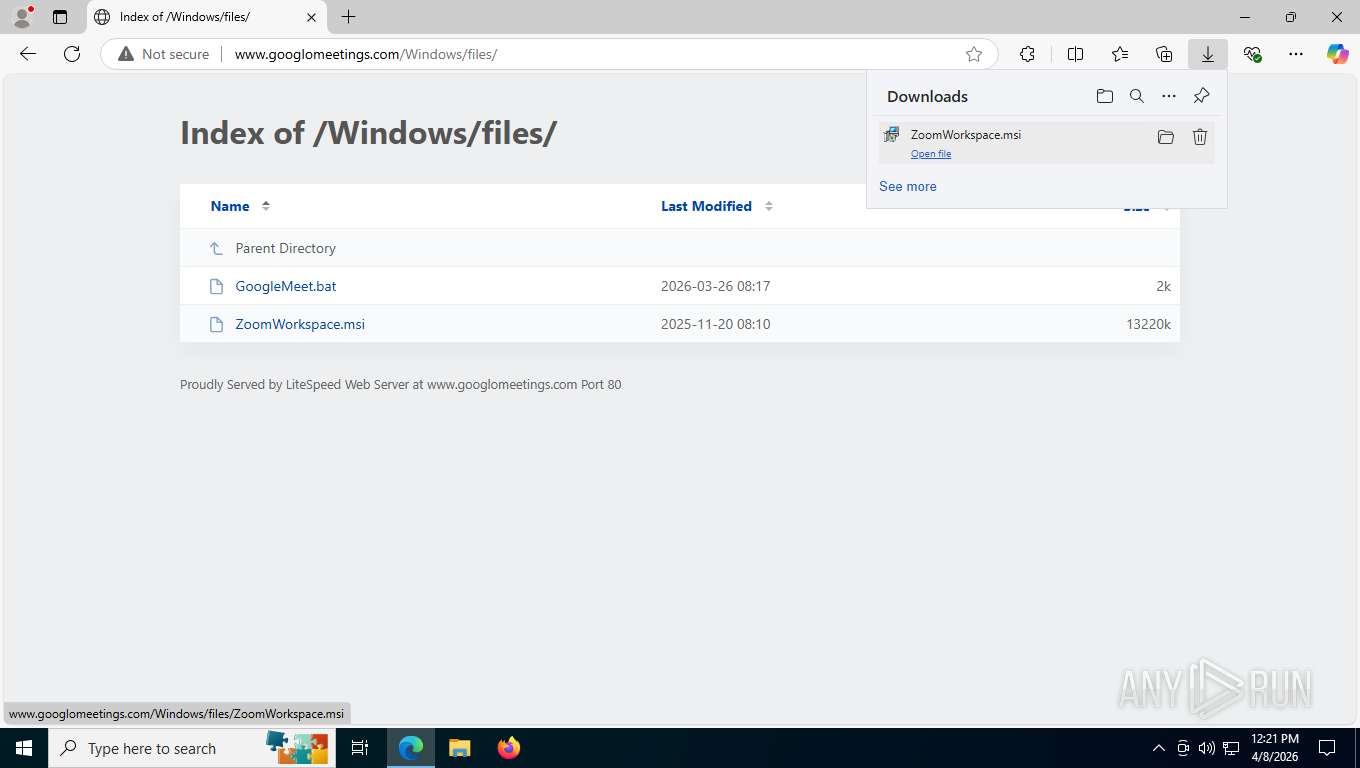
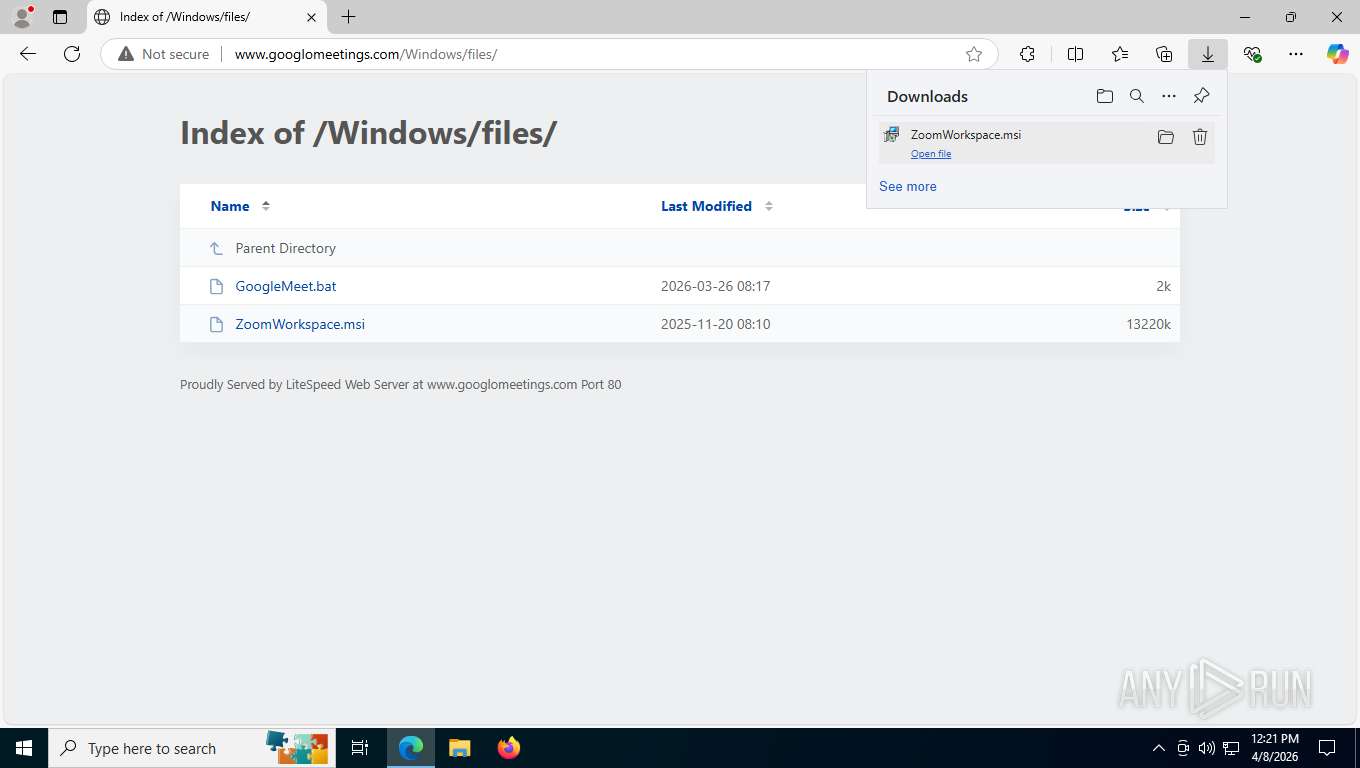
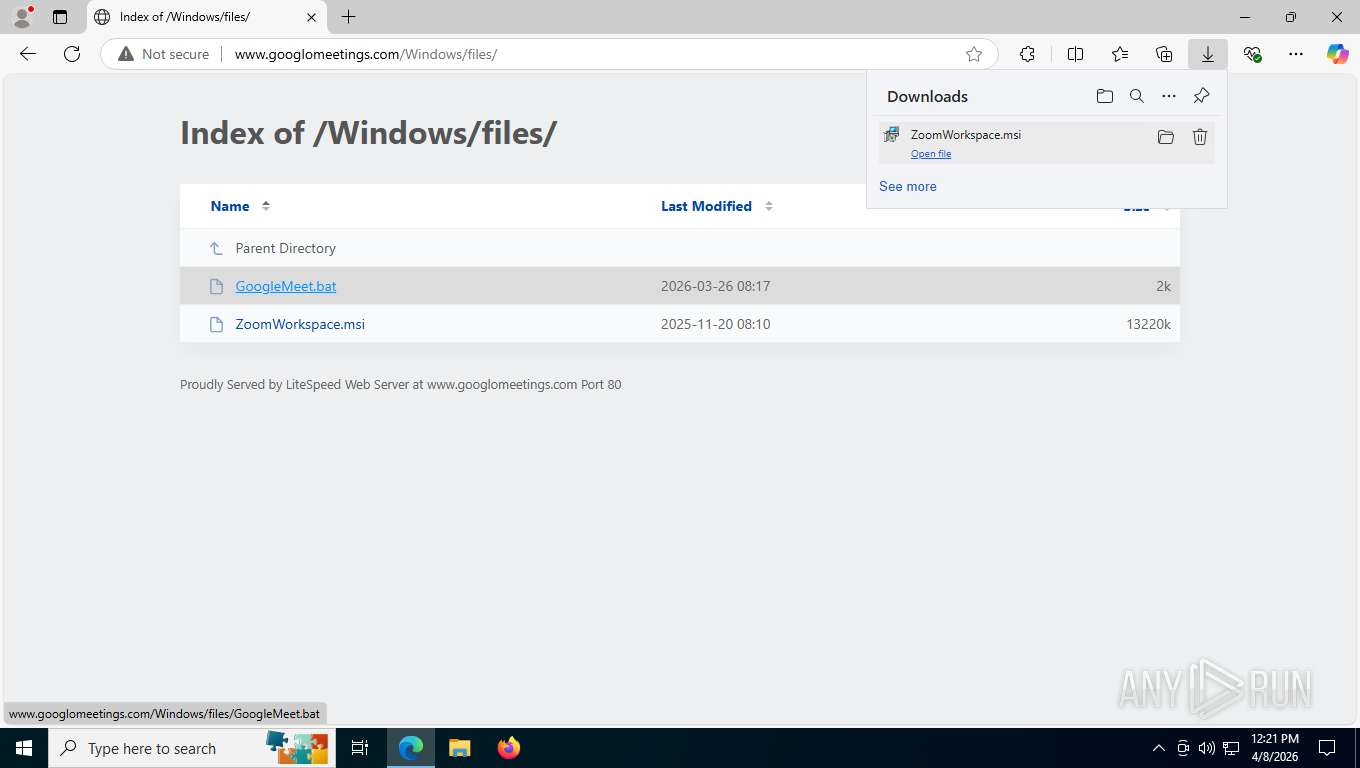
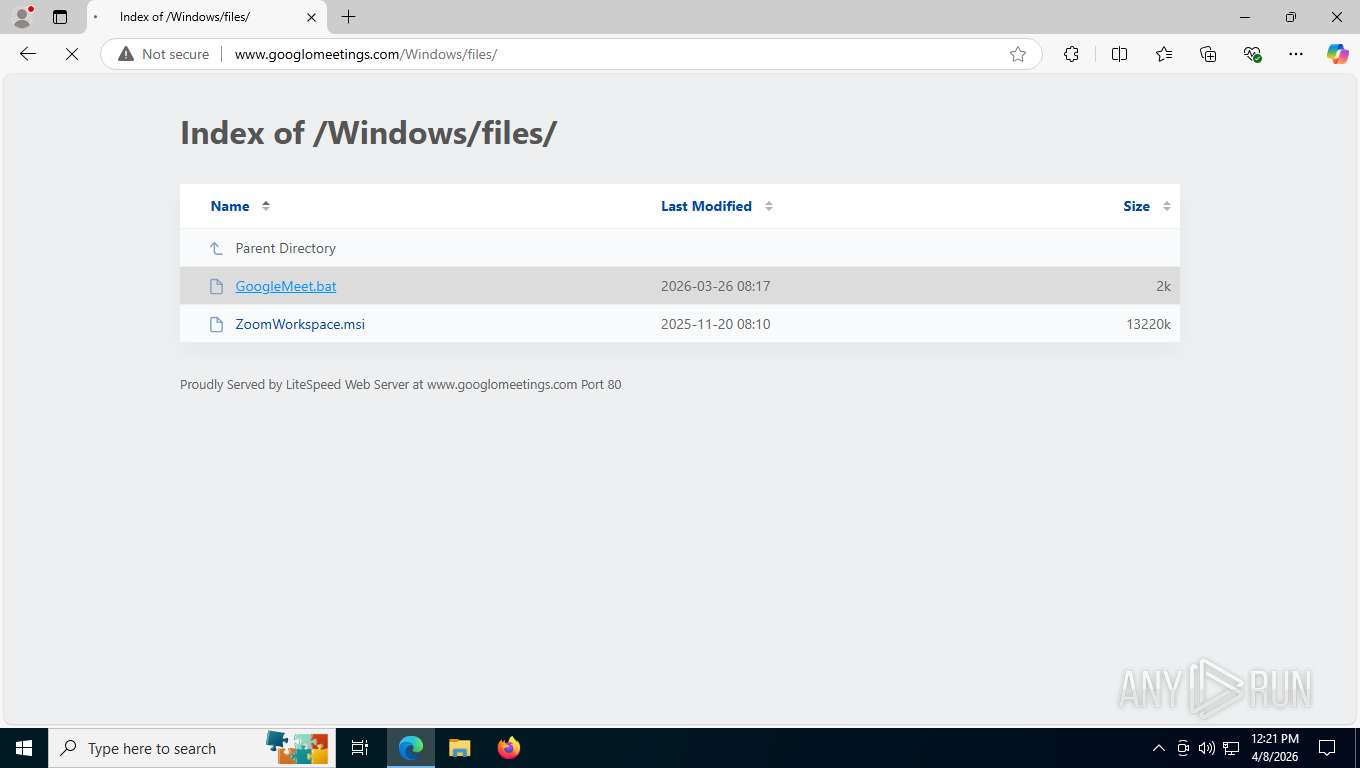
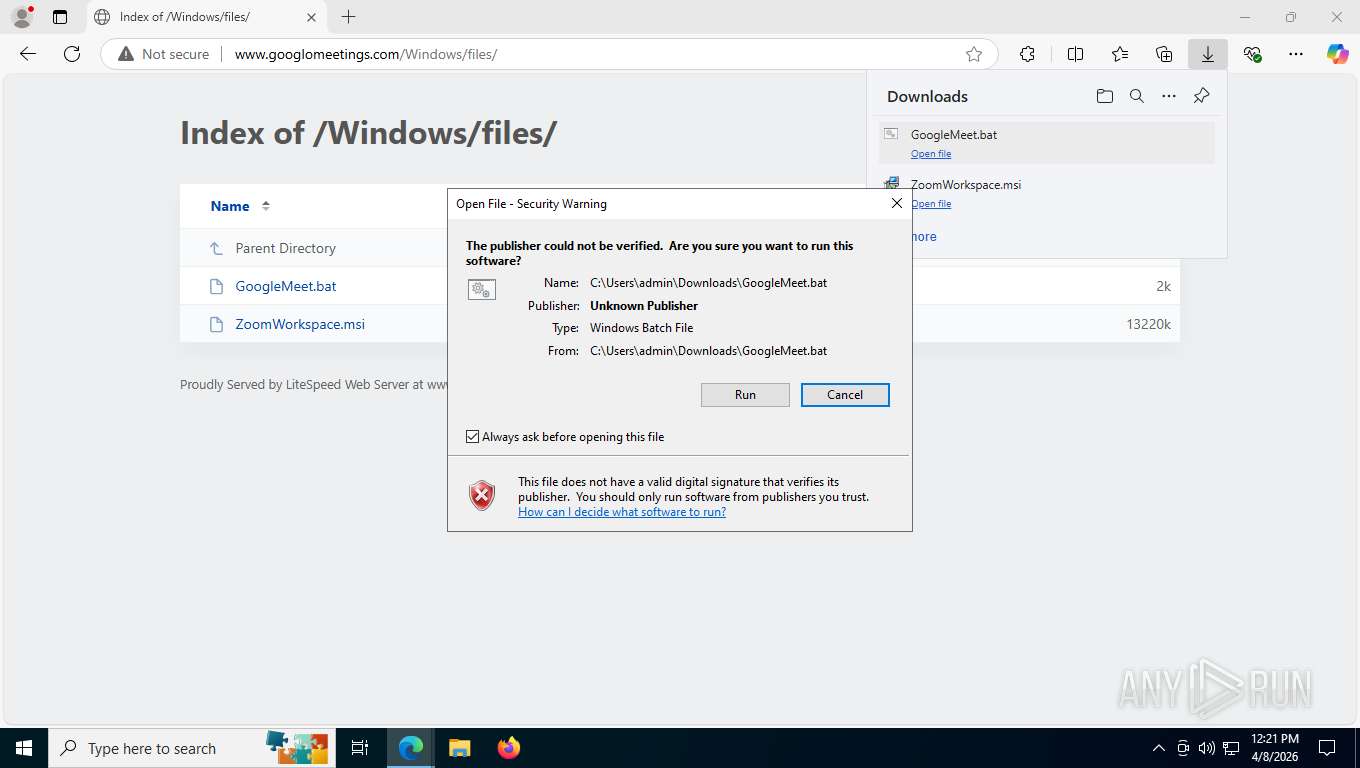
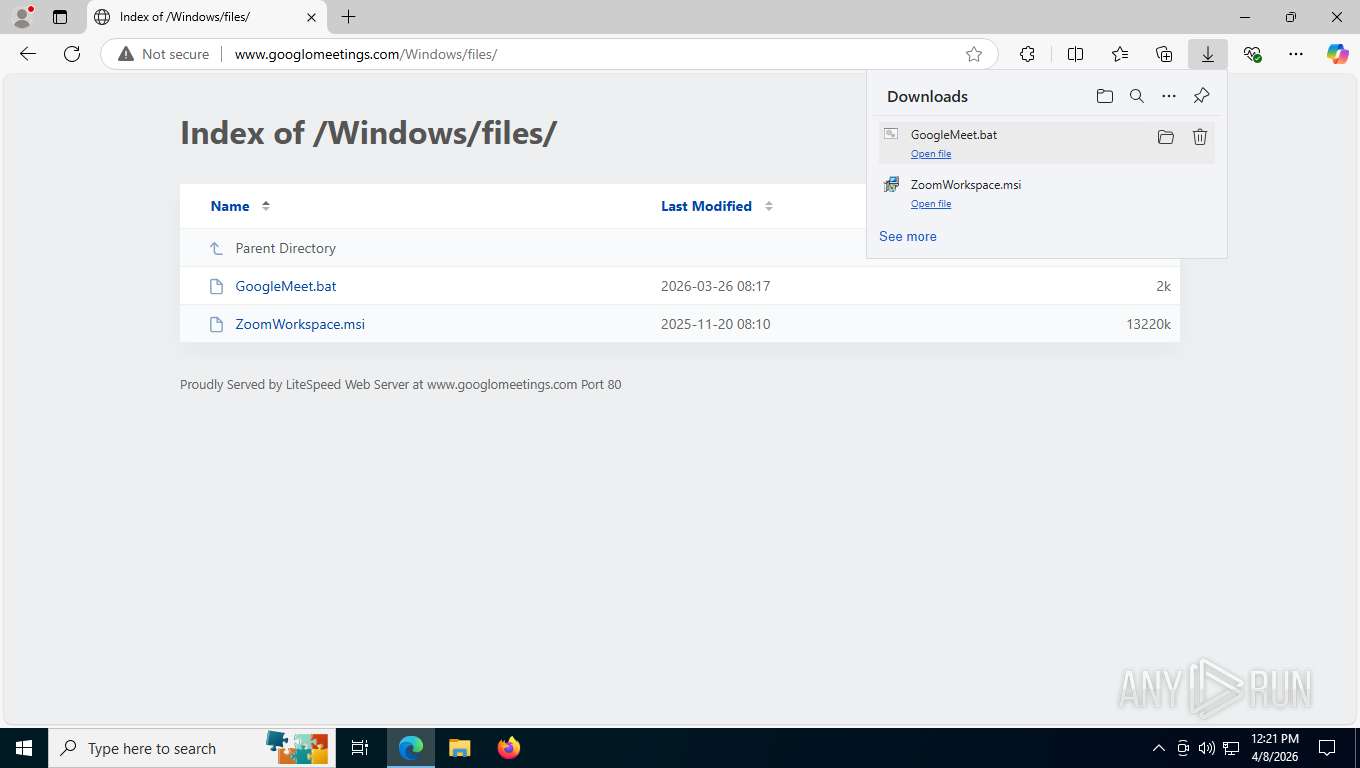
| URL: | www.googlomeetings.com |
| Full analysis: | https://app.any.run/tasks/c2ca7ee2-3e65-486d-aa7a-f6029c482143 |
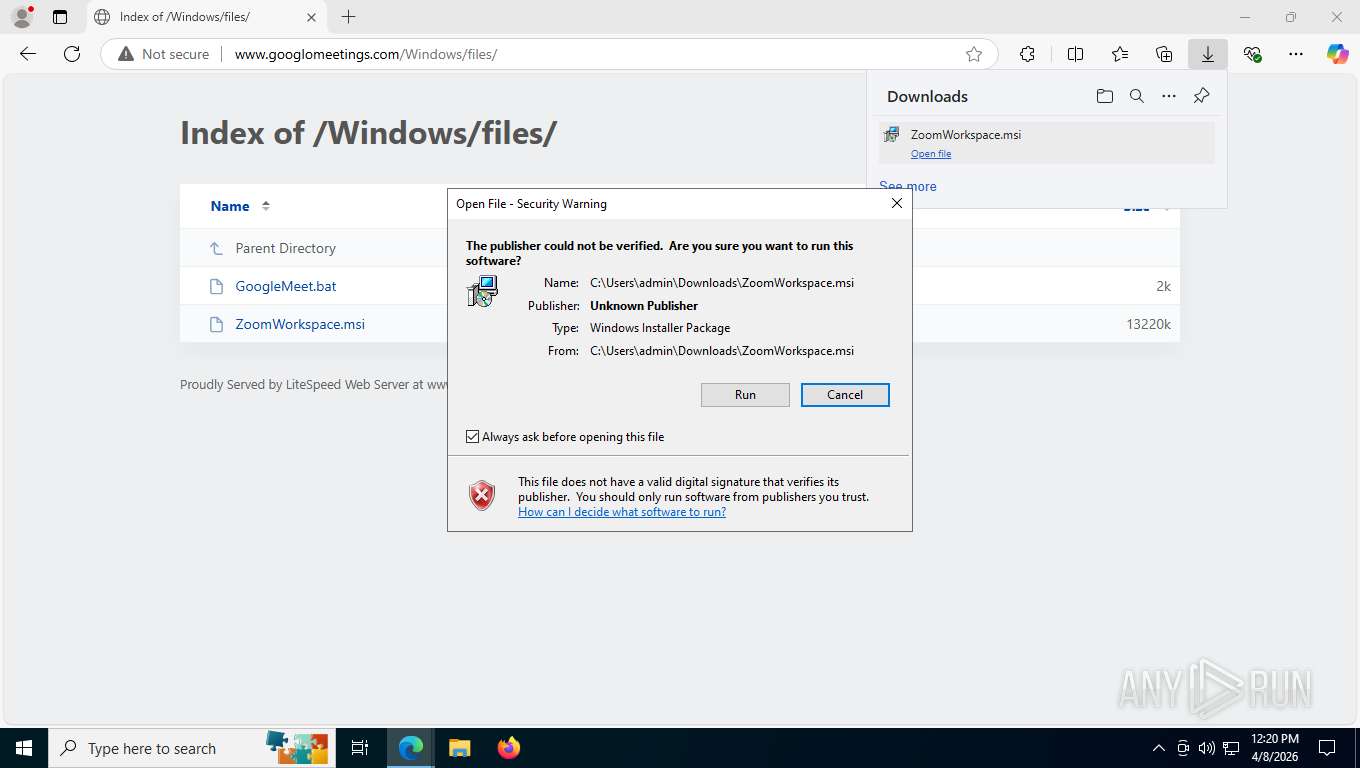
| Verdict: | Malicious activity |
| Analysis date: | April 08, 2026, 16:20:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7AF6AD733A8AE86FD783F2826660E80B |
| SHA1: | 49824E6F3CA3CC356FB14B0CCA1E01A6861F2D3B |
| SHA256: | 9BF6ED2F61799C139ED93146D14AA8A049B122ACCAA1D2F0EDD3779813B22A86 |
| SSDEEP: | 3:EIhK:lhK |
MALICIOUS
SCREENCONNECT has been detected
- msiexec.exe (PID: 8360)
- rundll32.exe (PID: 8452)
- rundll32.exe (PID: 5876)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7704)
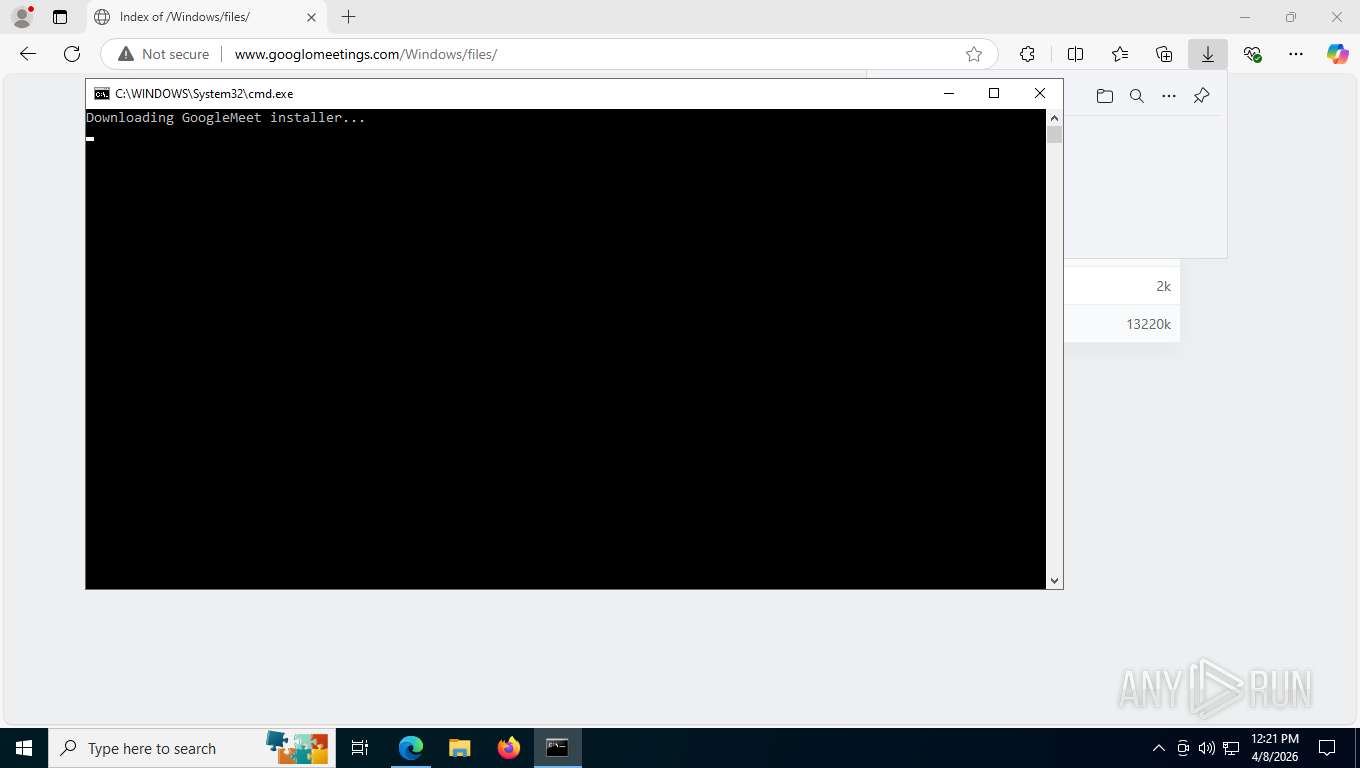
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8236)
SUSPICIOUS
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 3076)
- VSSVC.exe (PID: 8544)
- ScreenConnect.ClientService.exe (PID: 7096)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 3076)
- ScreenConnect.ClientService.exe (PID: 7096)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 3076)
- ScreenConnect.ClientService.exe (PID: 7096)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 3076)
- ScreenConnect.ClientService.exe (PID: 7096)
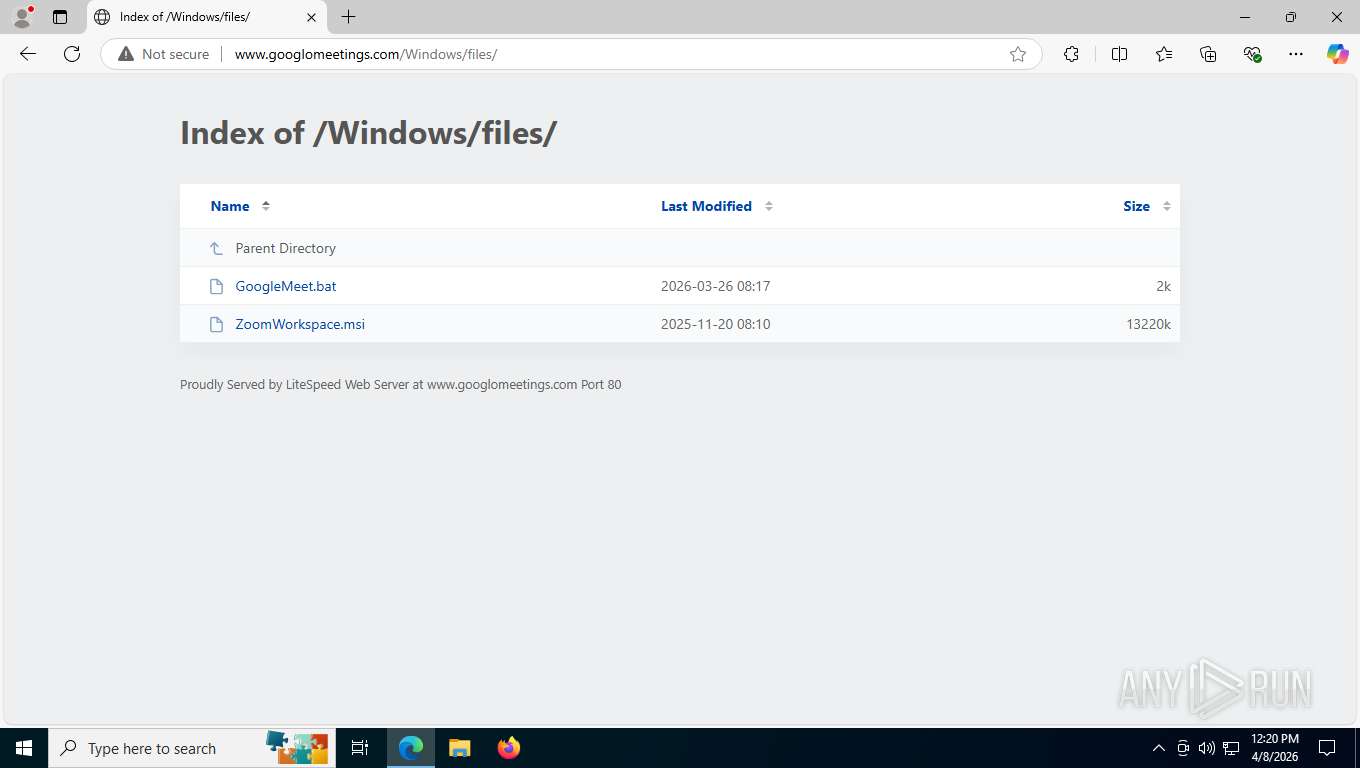
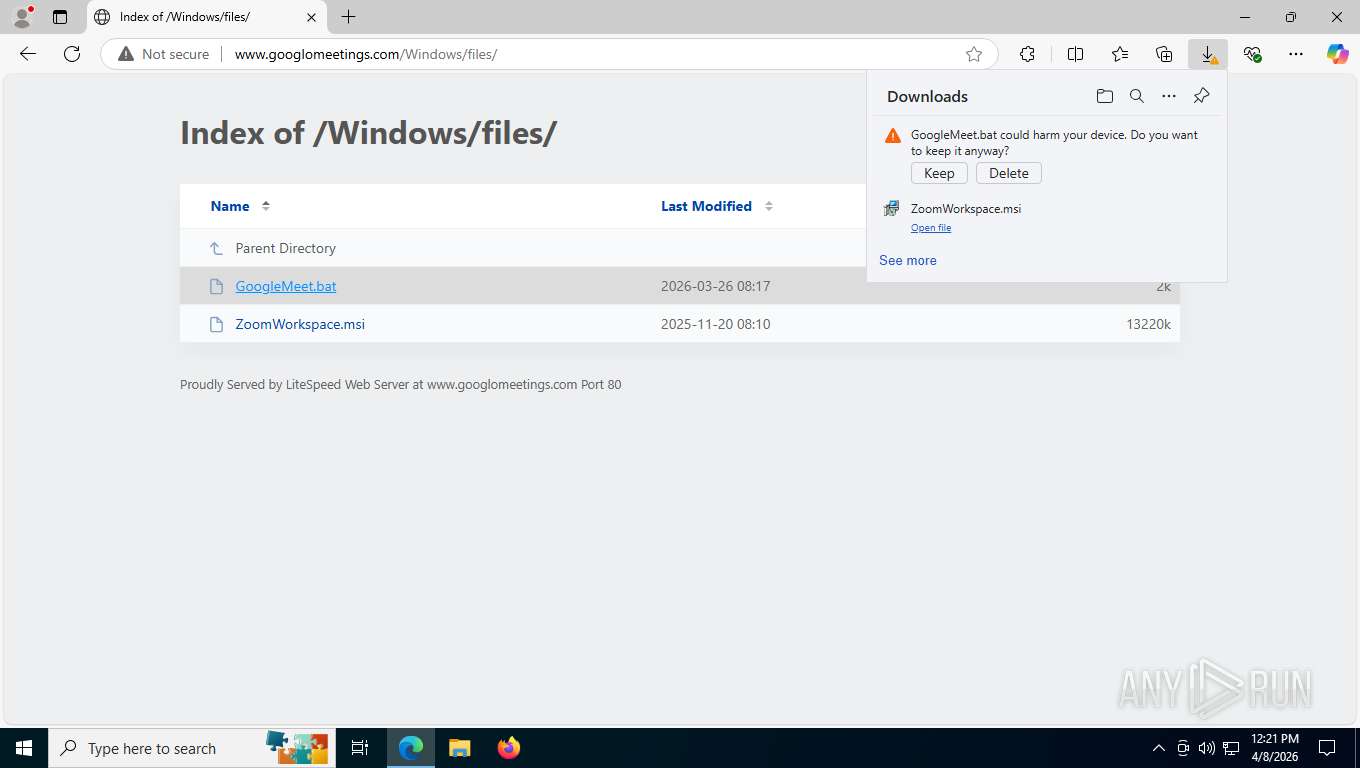
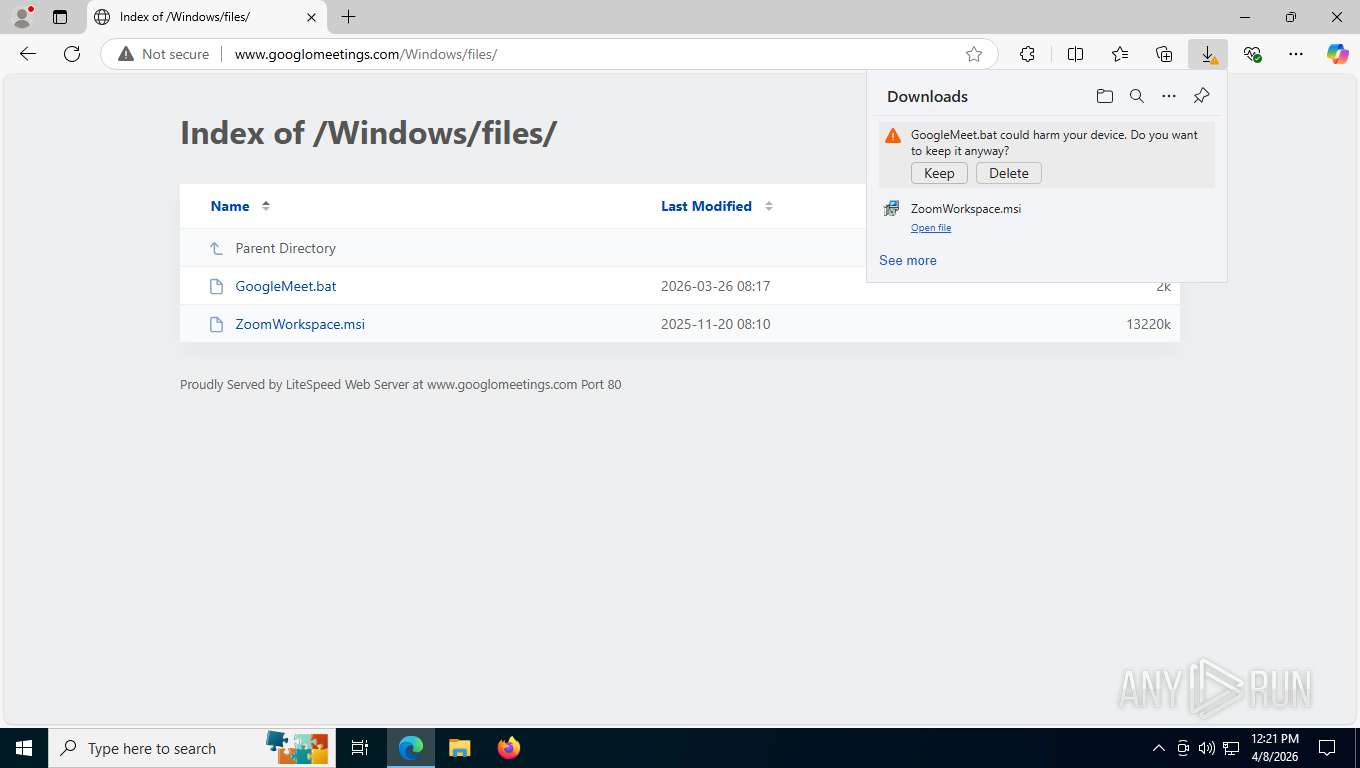
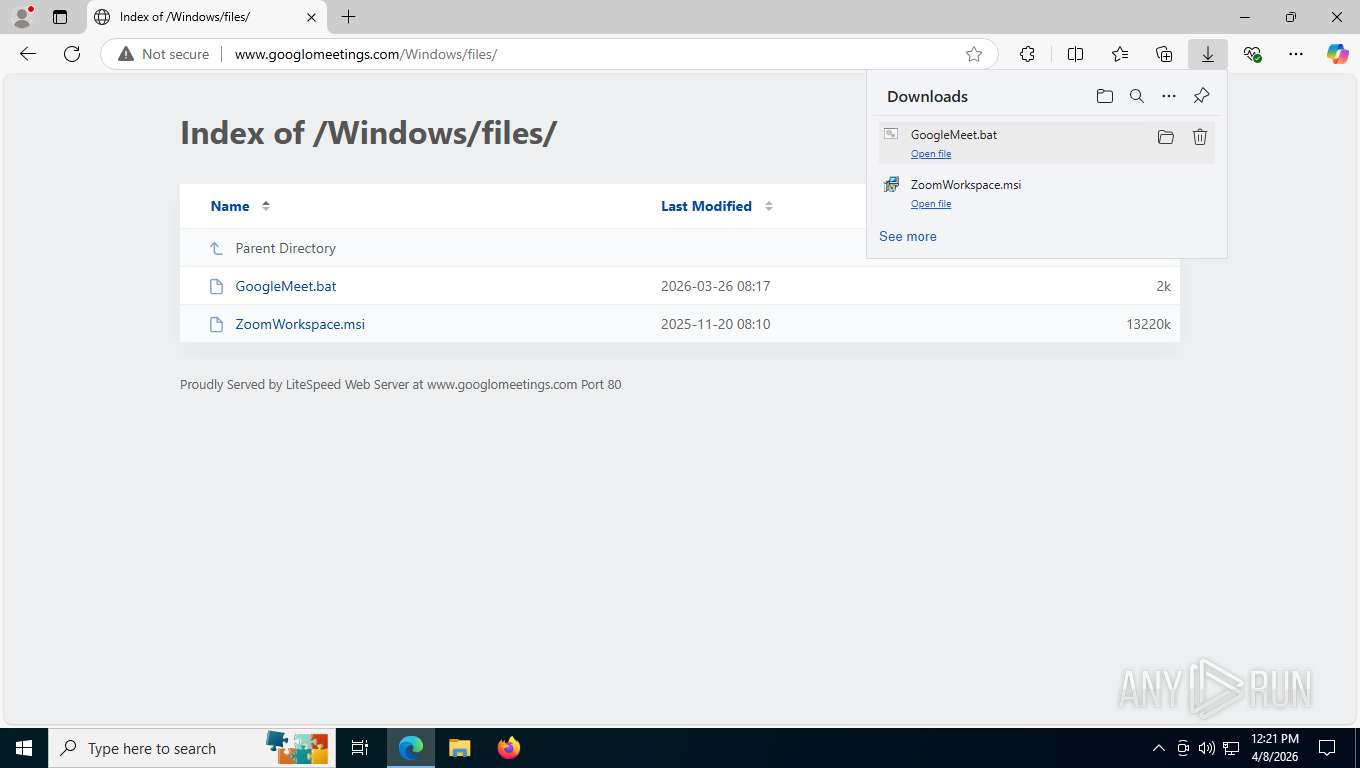
Executing commands from a ".bat" file
- msedge.exe (PID: 6988)
- powershell.exe (PID: 7300)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 8236)
- net.exe (PID: 8036)
- net.exe (PID: 9200)
- cmd.exe (PID: 7704)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8236)
- cmd.exe (PID: 7704)
Starts process via Powershell
- powershell.exe (PID: 7300)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8236)
- cmd.exe (PID: 7704)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7704)
Bypass execution policy to execute commands
- powershell.exe (PID: 8808)
Probably download files using WebClient
- cmd.exe (PID: 7704)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 8808)
Uses RUNDLL32.EXE to run a file without a DLL extension
- rundll32.exe (PID: 5876)
INFO
Checks supported languages
- identity_helper.exe (PID: 3076)
- msiexec.exe (PID: 5160)
- msiexec.exe (PID: 8360)
- ScreenConnect.ClientService.exe (PID: 3076)
- msiexec.exe (PID: 2880)
- ScreenConnect.WindowsClient.exe (PID: 7440)
- msiexec.exe (PID: 8408)
- msiexec.exe (PID: 7996)
- msiexec.exe (PID: 6816)
- ScreenConnect.ClientService.exe (PID: 7096)
- ScreenConnect.WindowsClient.exe (PID: 1652)
Reads the computer name
- msiexec.exe (PID: 8360)
- identity_helper.exe (PID: 3076)
- msiexec.exe (PID: 8408)
- msiexec.exe (PID: 5160)
- msiexec.exe (PID: 2880)
- ScreenConnect.ClientService.exe (PID: 3076)
- ScreenConnect.WindowsClient.exe (PID: 7440)
- msiexec.exe (PID: 7996)
- msiexec.exe (PID: 6816)
- ScreenConnect.ClientService.exe (PID: 7096)
- ScreenConnect.WindowsClient.exe (PID: 1652)
Reads Environment values
- identity_helper.exe (PID: 3076)
CONNECTWISE has been detected
- msiexec.exe (PID: 8324)
- ScreenConnect.ClientService.exe (PID: 3076)
- ScreenConnect.WindowsClient.exe (PID: 7440)
- ScreenConnect.ClientService.exe (PID: 7096)
- ScreenConnect.WindowsClient.exe (PID: 1652)
Manages system restore points
- SrTasks.exe (PID: 6404)
Create files in a temporary directory
- rundll32.exe (PID: 8452)
Reads the machine GUID from the registry
- ScreenConnect.WindowsClient.exe (PID: 7440)
- ScreenConnect.ClientService.exe (PID: 3076)
- ScreenConnect.ClientService.exe (PID: 7096)
- ScreenConnect.WindowsClient.exe (PID: 1652)
Reads security settings of Internet Explorer
- ScreenConnect.ClientService.exe (PID: 3076)
- ScreenConnect.WindowsClient.exe (PID: 7440)
- ScreenConnect.ClientService.exe (PID: 7096)
- ScreenConnect.WindowsClient.exe (PID: 1652)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 3076)
- ScreenConnect.ClientService.exe (PID: 7096)
Disables trace logs
- ScreenConnect.ClientService.exe (PID: 3076)
Launching a file from the Downloads directory
- msedge.exe (PID: 6988)
Application launched itself
- msedge.exe (PID: 6988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
185
Monitored processes
52
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2376,i,5850478523492859881,12122405189657264026,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2412 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1652 | "C:\Program Files (x86)\ScreenConnect Client (5b64ddc8cf1fd250)\ScreenConnect.WindowsClient.exe" "RunRole" "6dfacf23-c5af-462a-a8a4-82542d213d2c" "User" | C:\Program Files (x86)\ScreenConnect Client (5b64ddc8cf1fd250)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 25.2.4.9229 Modules
| |||||||||||||||
| 2120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=1452,i,5850478523492859881,12122405189657264026,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2204 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4816,i,5850478523492859881,12122405189657264026,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4800 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2324 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6296,i,5850478523492859881,12122405189657264026,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6112 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2340 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6844,i,5850478523492859881,12122405189657264026,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6204 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2368 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2528 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2880 | C:\Windows\syswow64\MsiExec.exe -Embedding D29DFD66F209C9C7301A31F1D6F43B32 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 783
Read events
13 599
Write events
175
Delete events
9
Modification events
| (PID) Process: | (8360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000962938AB73C7DC01A820000030210000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000051C735AB73C7DC01A820000030210000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000AF5F90AB73C7DC01A820000030210000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8544) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000065AADCAB73C7DC0160210000E0210000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8544) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000065AADCAB73C7DC0160210000D8210000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8544) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000065AADCAB73C7DC016021000080210000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8544) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000065AADCAB73C7DC016021000084210000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8544) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4800000000000000E733E6AB73C7DC0160210000D8210000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000AF5F90AB73C7DC01A820000030210000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000AF5F90AB73C7DC01A820000030210000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
32
Text files
210
Unknown types
137
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFe02ea.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe02ea.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe02ea.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe0309.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe0309.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
76
TCP/UDP connections
73
DNS requests
60
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
1132 | msedge.exe | GET | 302 | 104.225.130.131:80 | http://www.googlomeetings.com/z0f76a1d14fd21a8fb5fd0d03e0fdc3d3cedae52f?wsidchk=10131866&pdata=http%253A%252F%252Fwww.googlomeetings.com&id=7fa3b767c460b54a2be4d49030b349c7&ts=1775665234 | US | — | — | unknown |
1132 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
1132 | msedge.exe | GET | 200 | 13.107.253.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
1132 | msedge.exe | GET | 200 | 52.123.243.219:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | binary | 4.48 Kb | whitelisted |
1132 | msedge.exe | GET | 200 | 2.16.204.157:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 665 Kb | whitelisted |
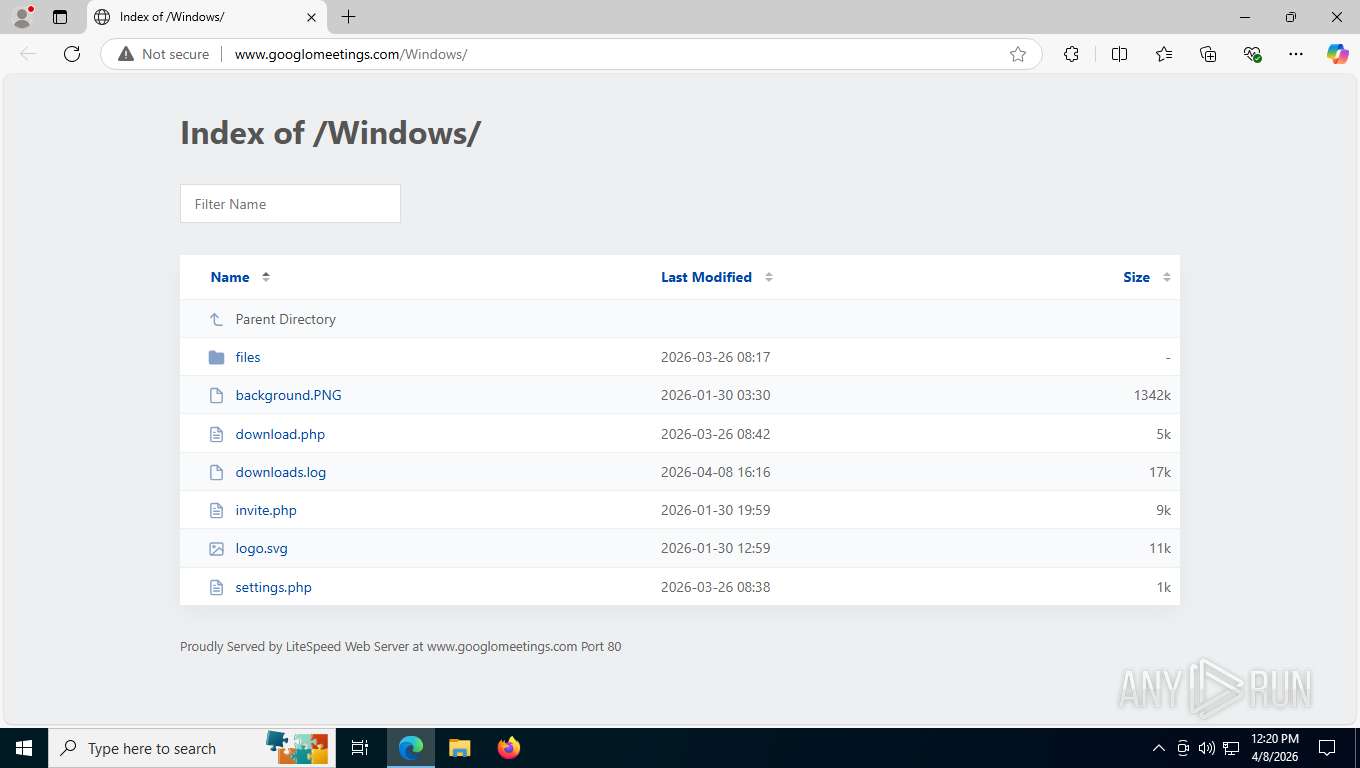
1132 | msedge.exe | GET | 200 | 104.225.130.131:80 | http://www.googlomeetings.com/ | US | binary | 11.4 Kb | unknown |
1132 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:2vwENr3rgaw4jlbtn7UJKLNDQn2cl_FE2xGL2AqWHOk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | binary | 100 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 960 b | whitelisted |
1132 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 295 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6260 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 128.24.231.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.157:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1132 | msedge.exe | 52.123.243.219:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
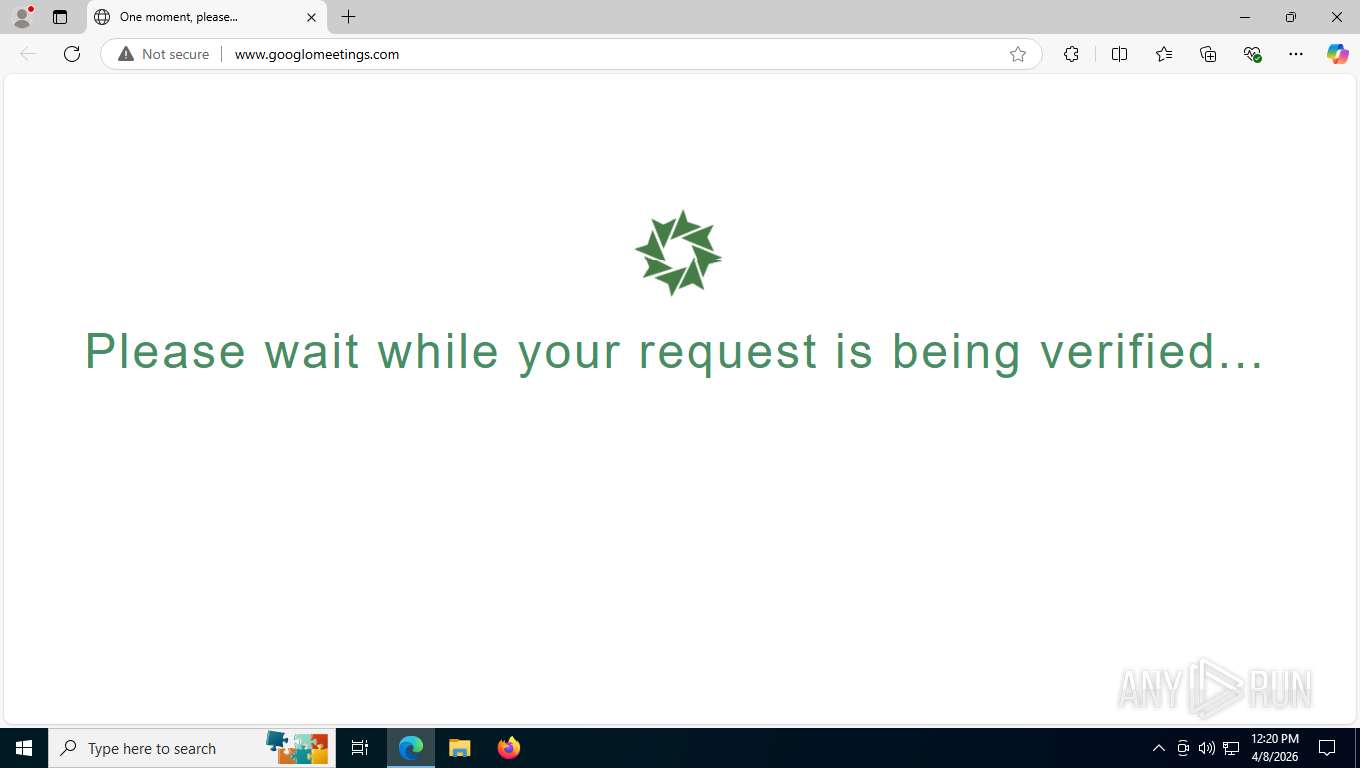
1132 | msedge.exe | Misc activity | HUNTING [ANY.RUN] Green Spinner browser checking page often used in phishing campaigns |
6260 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2232 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1132 | msedge.exe | Misc activity | HUNTING [ANY.RUN] .bat script file requested via HTTP |
1132 | msedge.exe | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |
1132 | msedge.exe | Potentially Bad Traffic | ET HUNTING PowerShell DownloadFile Command Common In Powershell Stagers |
2232 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
8808 | powershell.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
8808 | powershell.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
8808 | powershell.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |