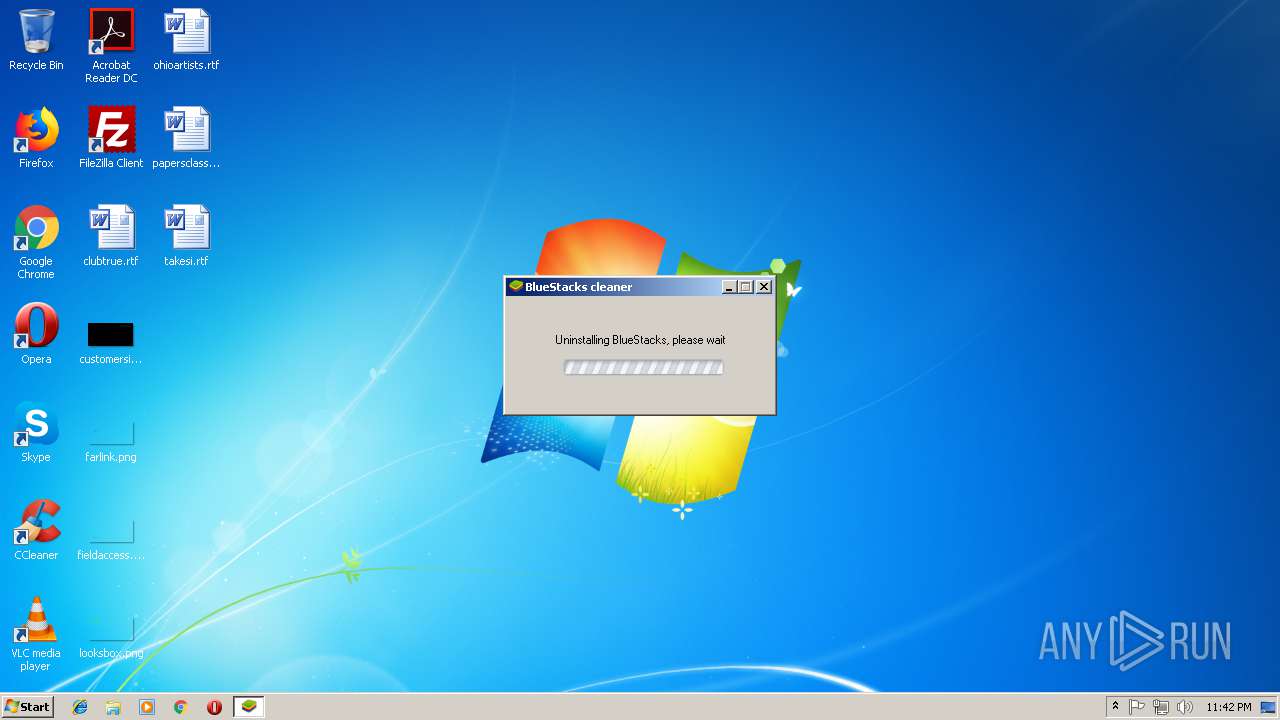
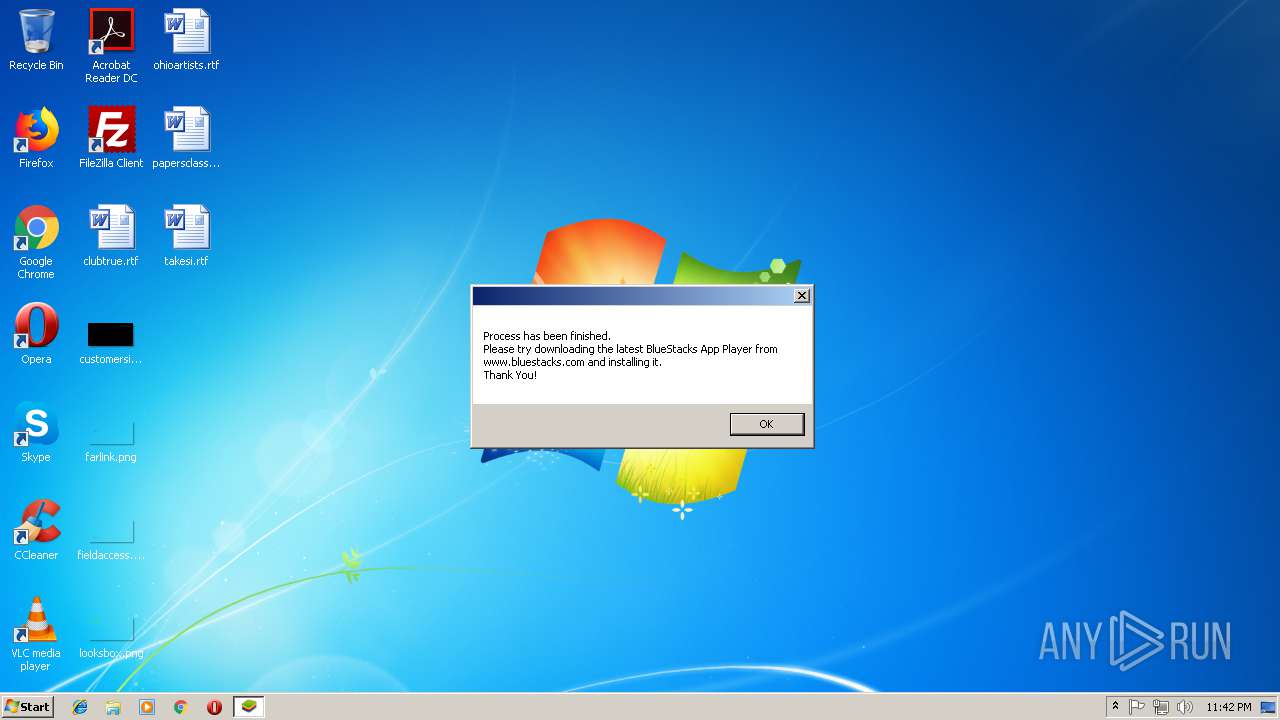
| download: | BSTCleaner_All.exe |
| Full analysis: | https://app.any.run/tasks/89c4dadc-97b5-4ce3-bc21-9b14a1023bd7 |
| Verdict: | No threats detected |
| Analysis date: | October 26, 2018, 22:41:51 |
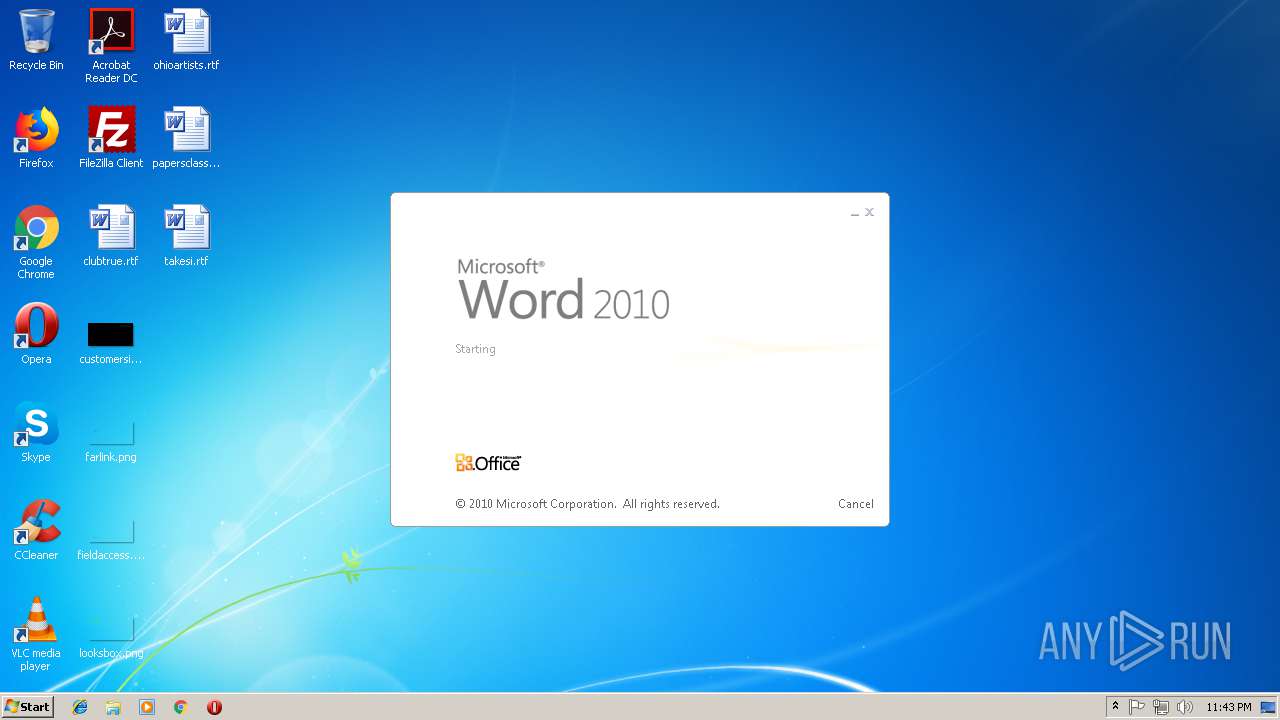
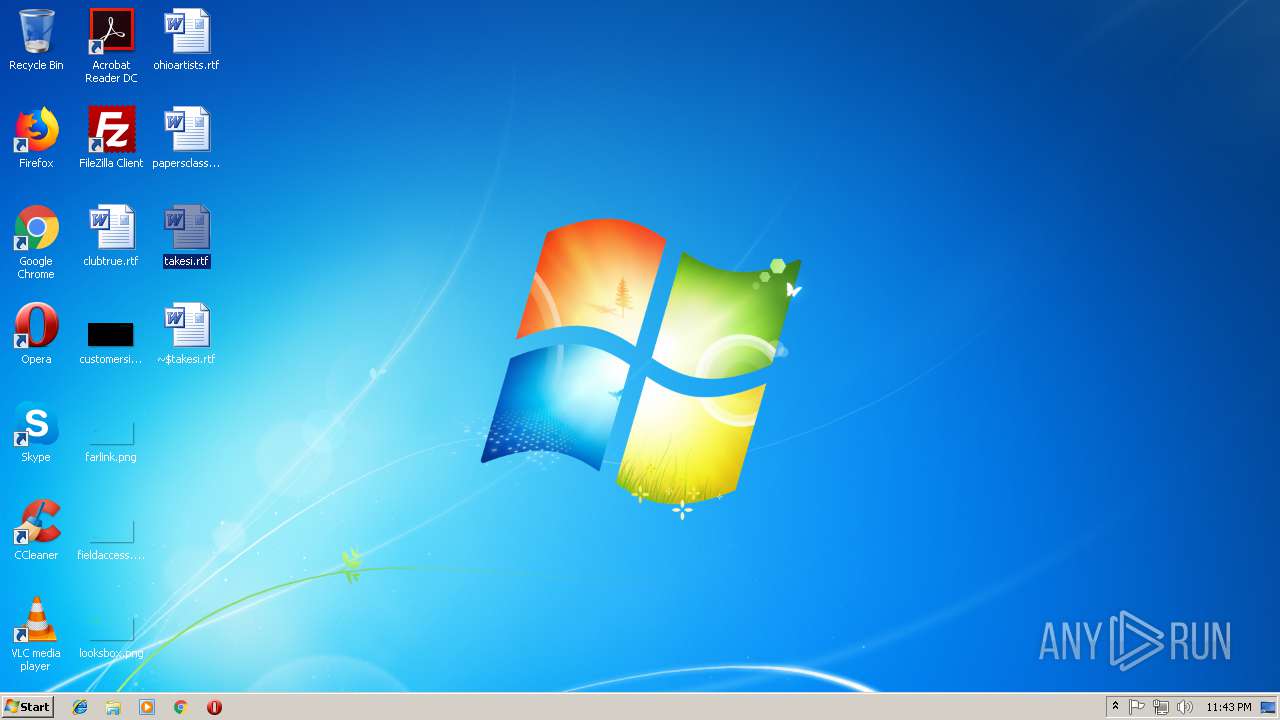
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0A5E177F9FCAE9926C98854449D17669 |
| SHA1: | F25AE2B039FE0AD18B503F486F0097F20838A5CE |
| SHA256: | 9BF5BF27E61C026C2CE28F85A6F0020725A32AAB0989033E413135B6B90B4635 |
| SSDEEP: | 24576:h1OYdaVhgFaNbZtBLwEaw3cvWd6MLfW2cjp:h1Os+WFa91Jfsg6MLffcjp |
MALICIOUS
Application was dropped or rewritten from another process
- BSTCleaner.exe (PID: 2320)
Loads dropped or rewritten executable
- BSTCleaner.exe (PID: 2320)
SUSPICIOUS
Executable content was dropped or overwritten
- BSTCleaner_All.exe (PID: 3740)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3528)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:18 17:27:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 104960 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14b04 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.20.0.0 |
| ProductVersionNumber: | 9.20.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 9.2 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| OriginalFileName: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 9.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2010 16:27:35 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 9.20 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| OriginalFilename: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 9.20 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Nov-2010 16:27:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000199EA | 0x00019A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60849 |
.rdata | 0x0001B000 | 0x00004494 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.36802 |
.data | 0x00020000 | 0x00005A48 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.37054 |
.sxdata | 0x00026000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00027000 | 0x00000A60 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.30196 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.44049 | 700 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.18403 | 296 | UNKNOWN | English - United States | RT_ICON |
5 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
500 | 3.09294 | 184 | UNKNOWN | English - United States | RT_DIALOG |
Imports
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2320 | .\BSTCleaner.exe -Oem all | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\BSTCleaner.exe | — | BSTCleaner_All.exe | |||||||||||
User: admin Company: BlueStack Systems, Inc. Integrity Level: HIGH Description: BlueStacks Cleaner Exit code: 0 Version: 4.20.20.1010 Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\AppData\Local\Temp\BSTCleaner_All.exe" | C:\Users\admin\AppData\Local\Temp\BSTCleaner_All.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z Setup SFX Exit code: 3221226540 Version: 9.20 Modules
| |||||||||||||||
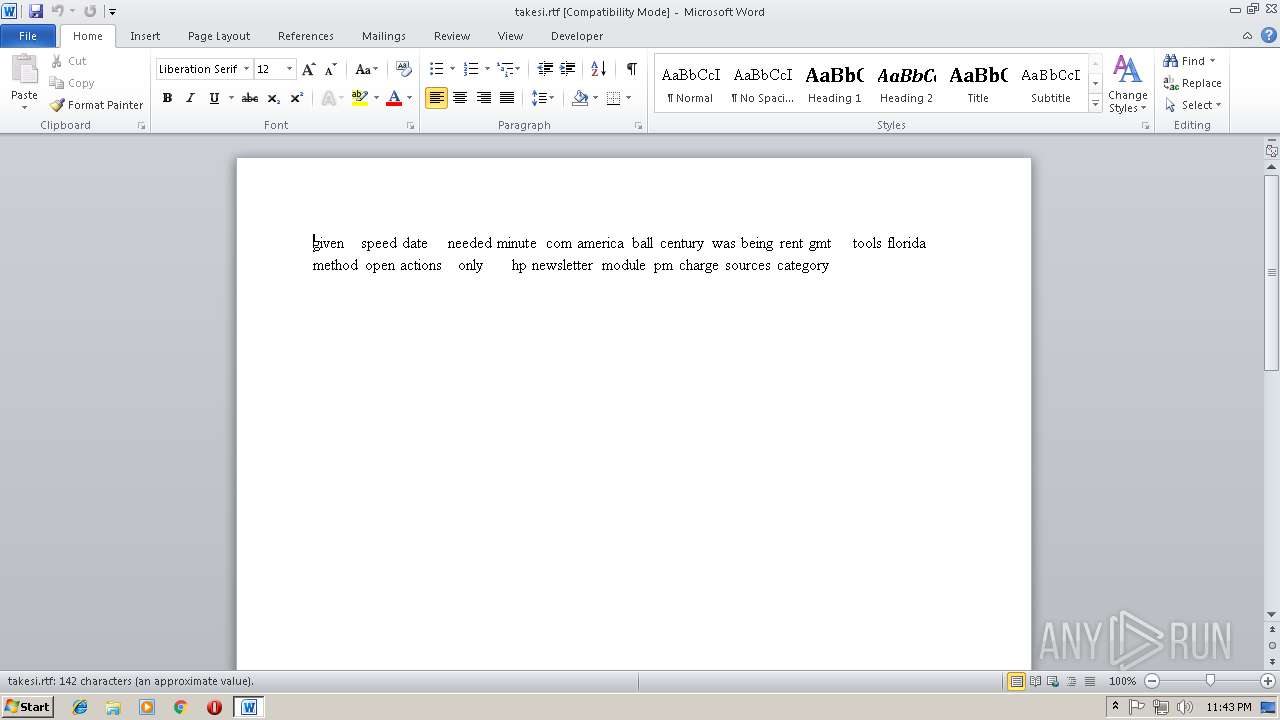
| 3528 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\takesi.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3740 | "C:\Users\admin\AppData\Local\Temp\BSTCleaner_All.exe" | C:\Users\admin\AppData\Local\Temp\BSTCleaner_All.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Setup SFX Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
Total events
1 042
Read events
673
Write events
357
Delete events
12
Modification events
| (PID) Process: | (2320) BSTCleaner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 5!b |
Value: 35216200C80D0000010000000000000000000000 | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1297743888 | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1297744000 | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1297744001 | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: C80D00009AF483407D6DD40100000000 | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :#b |
Value: 3A236200C80D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | :#b |
Value: 3A236200C80D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
Executable files
3
Suspicious files
0
Text files
81
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3740 | BSTCleaner_All.exe | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\Locales\i18n.es-ES.txt | text | |
MD5:— | SHA256:— | |||
| 3740 | BSTCleaner_All.exe | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\Locales\i18n.ar-EG.txt | text | |
MD5:— | SHA256:— | |||
| 3740 | BSTCleaner_All.exe | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\Assets\bluestacks.ico | image | |
MD5:63251C717D9BC1E5FC6370671F38EEDC | SHA256:5947201ED9206281D8E6E8B46BF562C78D3C9EE1DD74C0792DF18EACAD04EAE6 | |||
| 3740 | BSTCleaner_All.exe | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\Assets\loadingbar.gif | image | |
MD5:60ABE239A54C40B5E76F8932B52EB7EE | SHA256:40C41AC4DA4C945C1439EBA260F2A86B1D61D01568283167F8AD9A41EF078C02 | |||
| 3740 | BSTCleaner_All.exe | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\Locales\i18n.de-DE.txt | text | |
MD5:— | SHA256:— | |||
| 3740 | BSTCleaner_All.exe | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\Locales\i18n.ja-JP.txt | text | |
MD5:— | SHA256:— | |||
| 3740 | BSTCleaner_All.exe | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\Locales\i18n.ko-KR.txt | text | |
MD5:— | SHA256:— | |||
| 3740 | BSTCleaner_All.exe | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\Locales\i18n.pl-PL.txt | text | |
MD5:— | SHA256:— | |||
| 3740 | BSTCleaner_All.exe | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\Locales\i18n.pt-BR.txt | text | |
MD5:— | SHA256:— | |||
| 3740 | BSTCleaner_All.exe | C:\Users\admin\AppData\Local\Temp\7zS83F5.tmp\Locales\i18n.ru-RU.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report