| File name: | nvda_2020.2.exe |
| Full analysis: | https://app.any.run/tasks/b16e3a26-e02e-4d65-8826-2b853883c26d |
| Verdict: | Malicious activity |
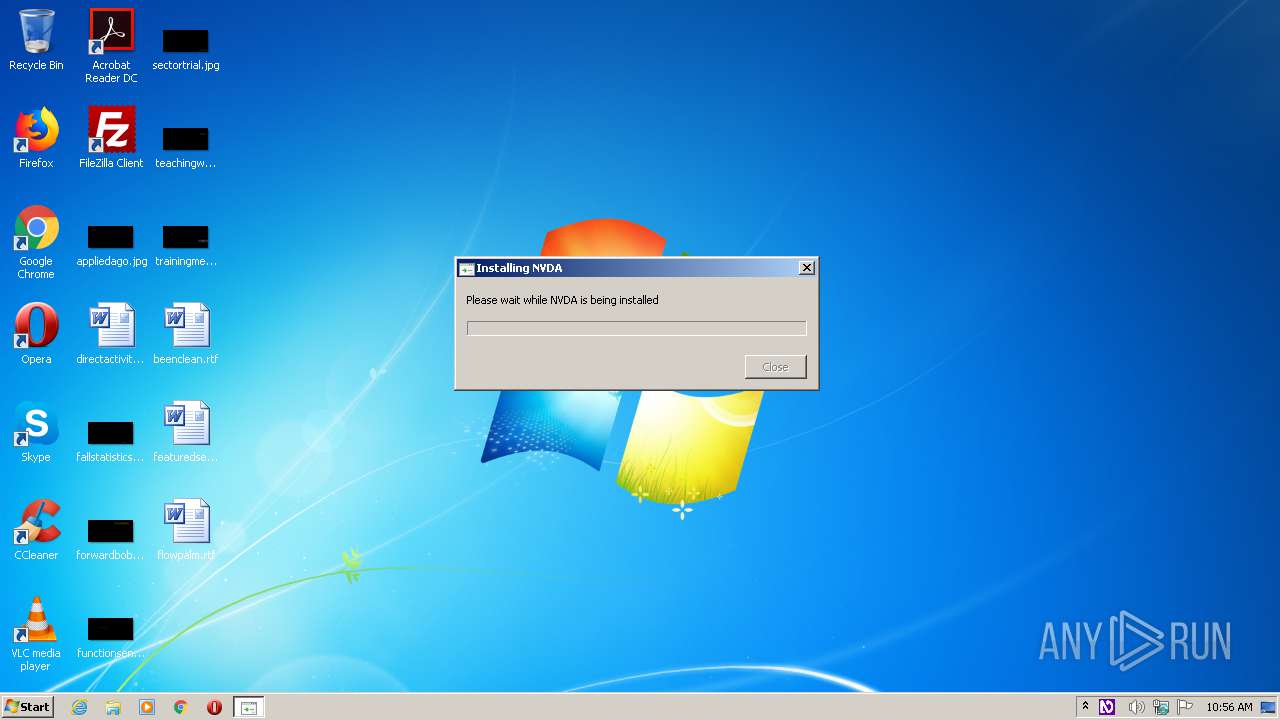
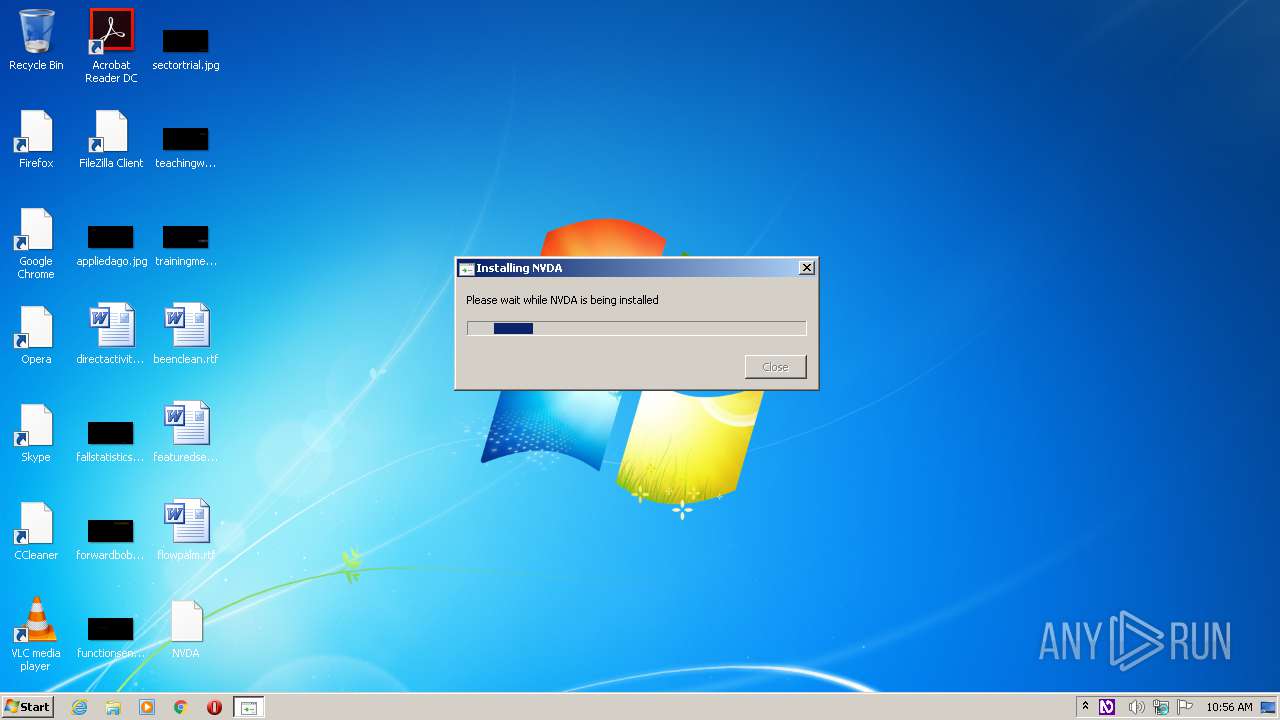
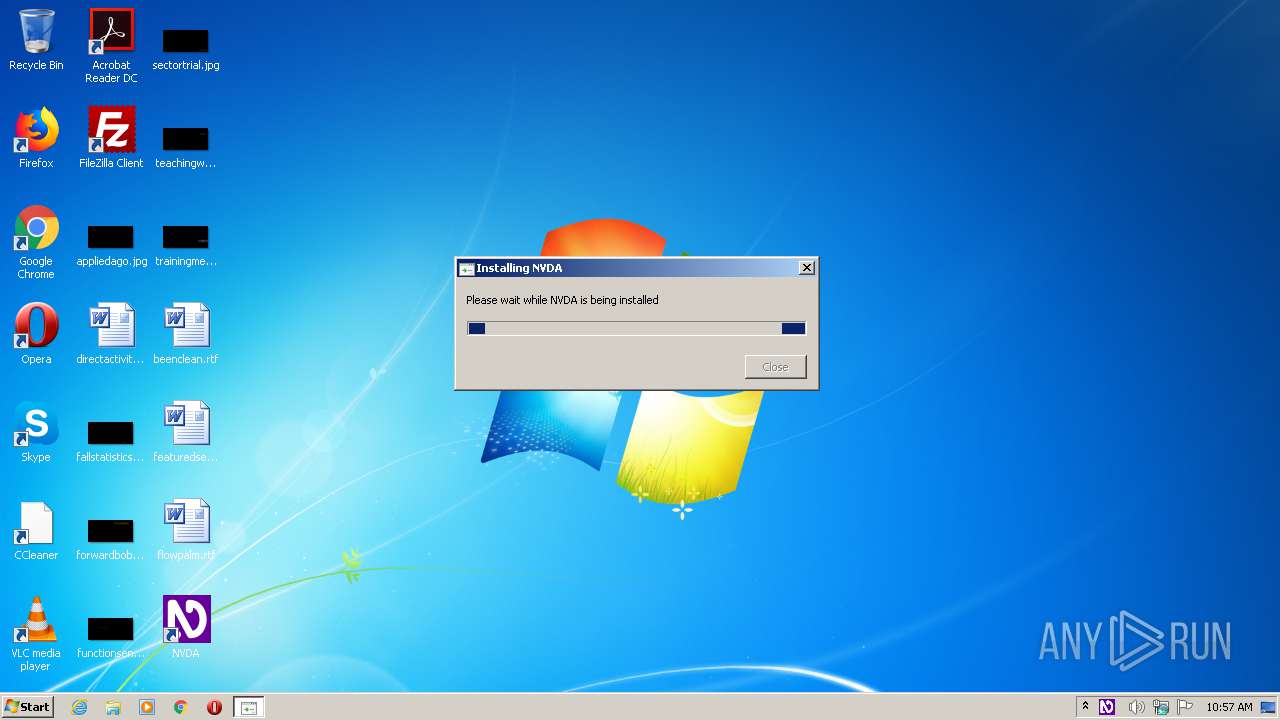
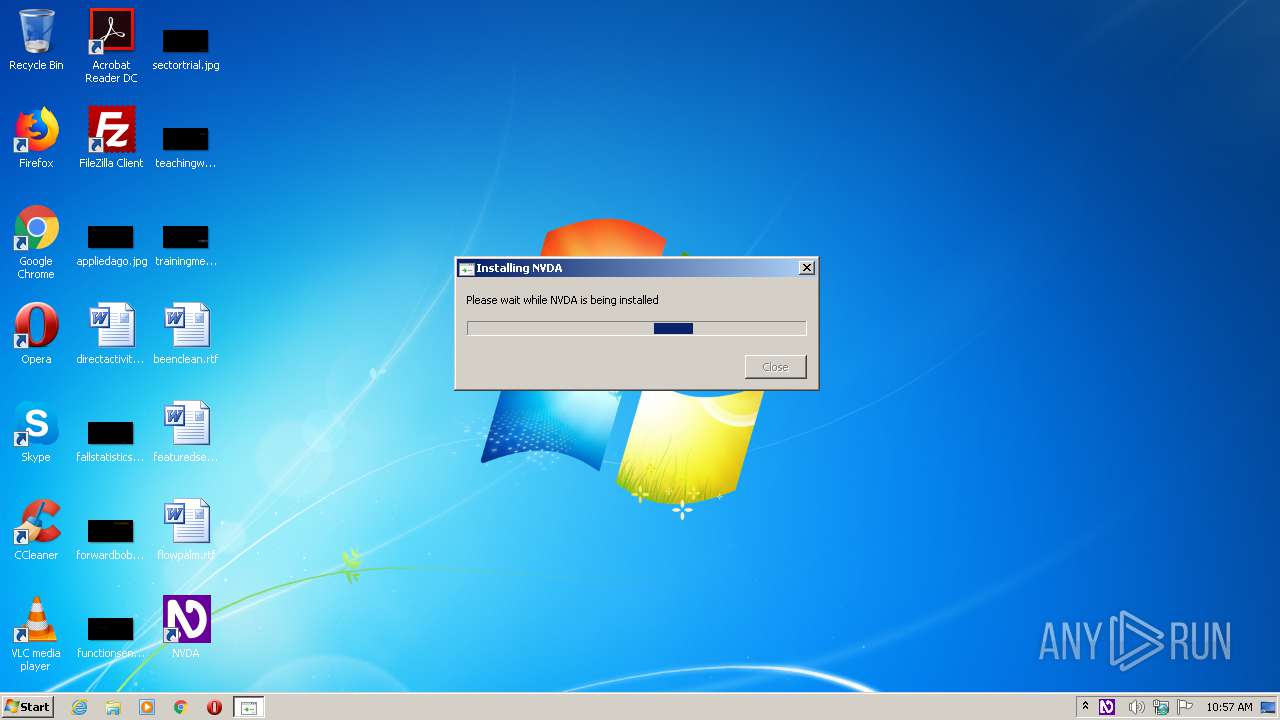
| Analysis date: | September 01, 2020, 09:56:16 |
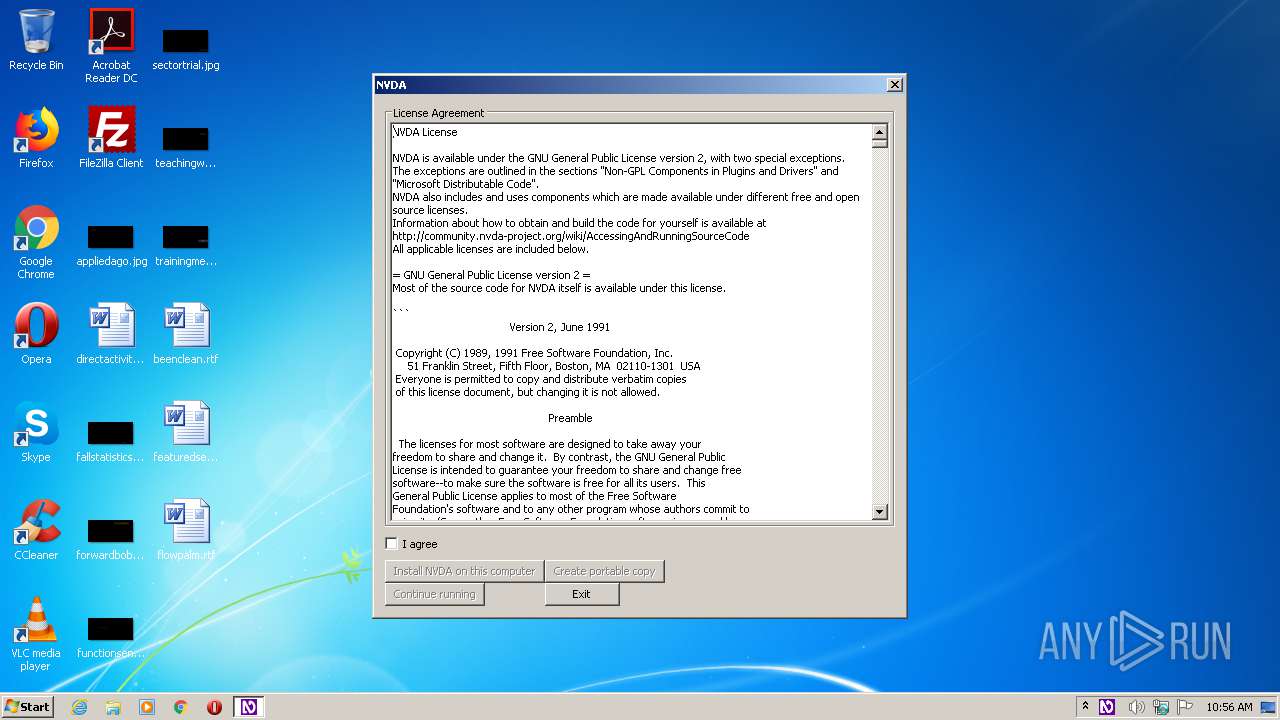
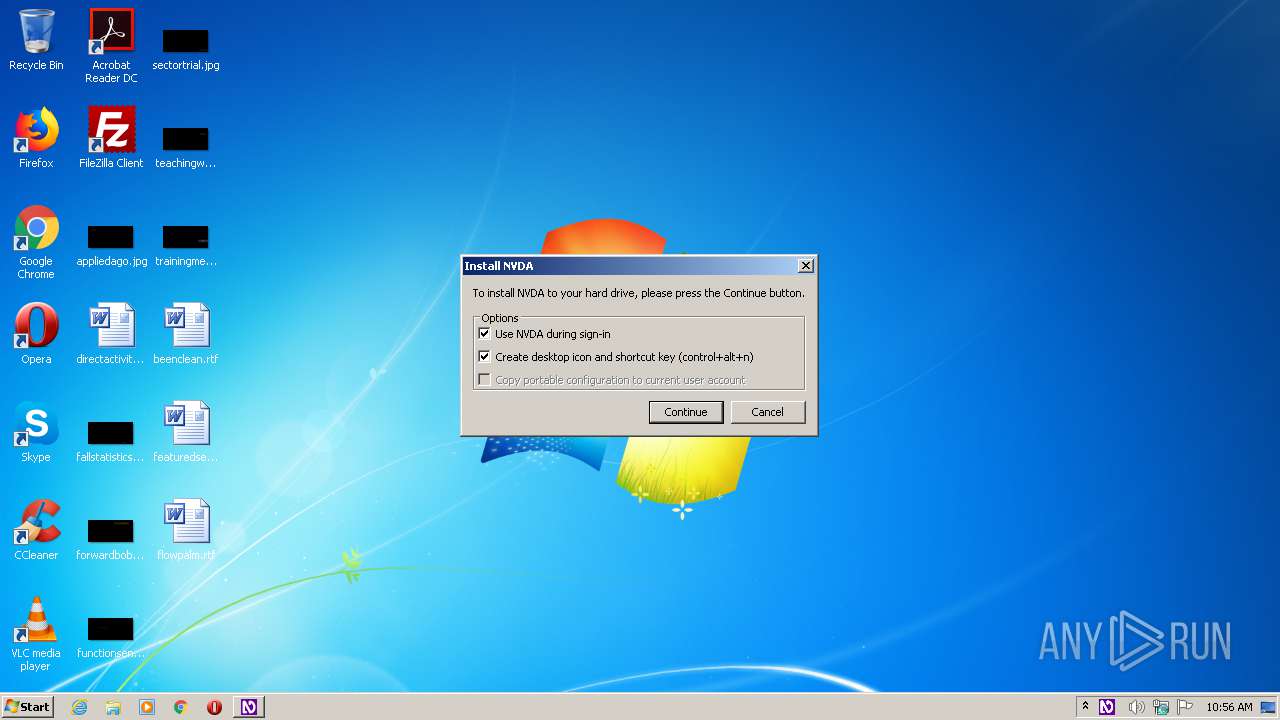
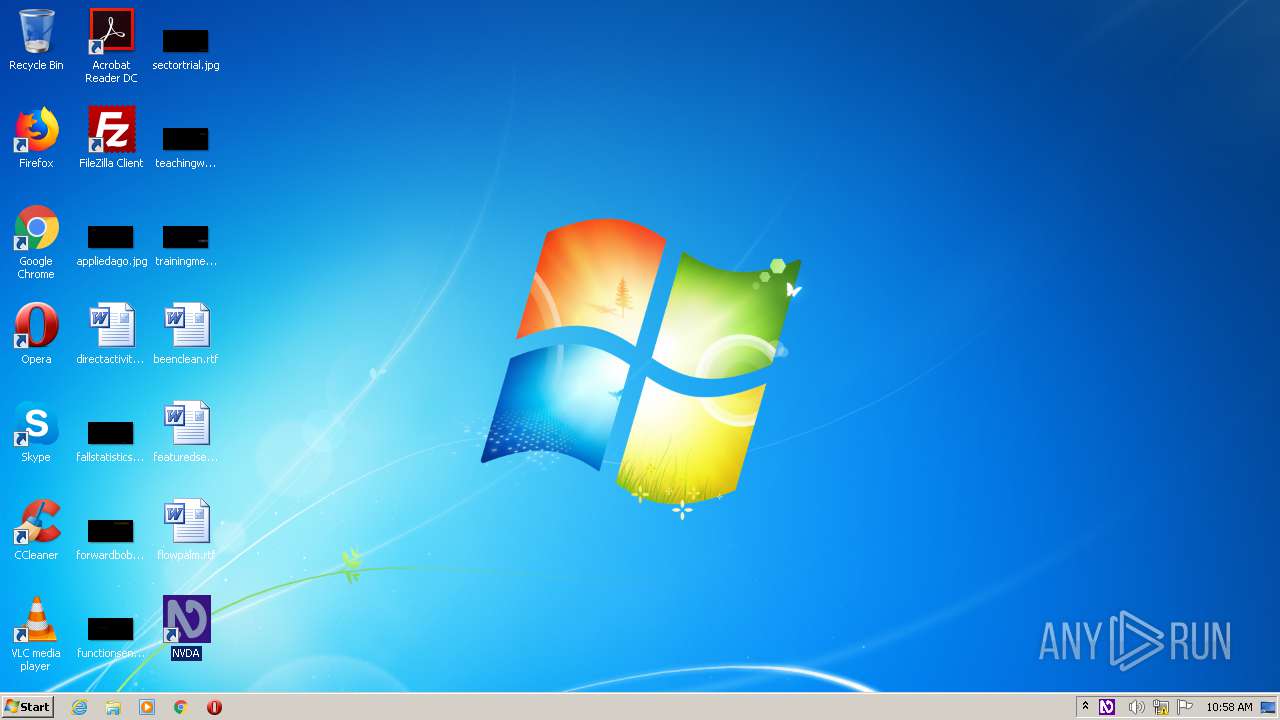
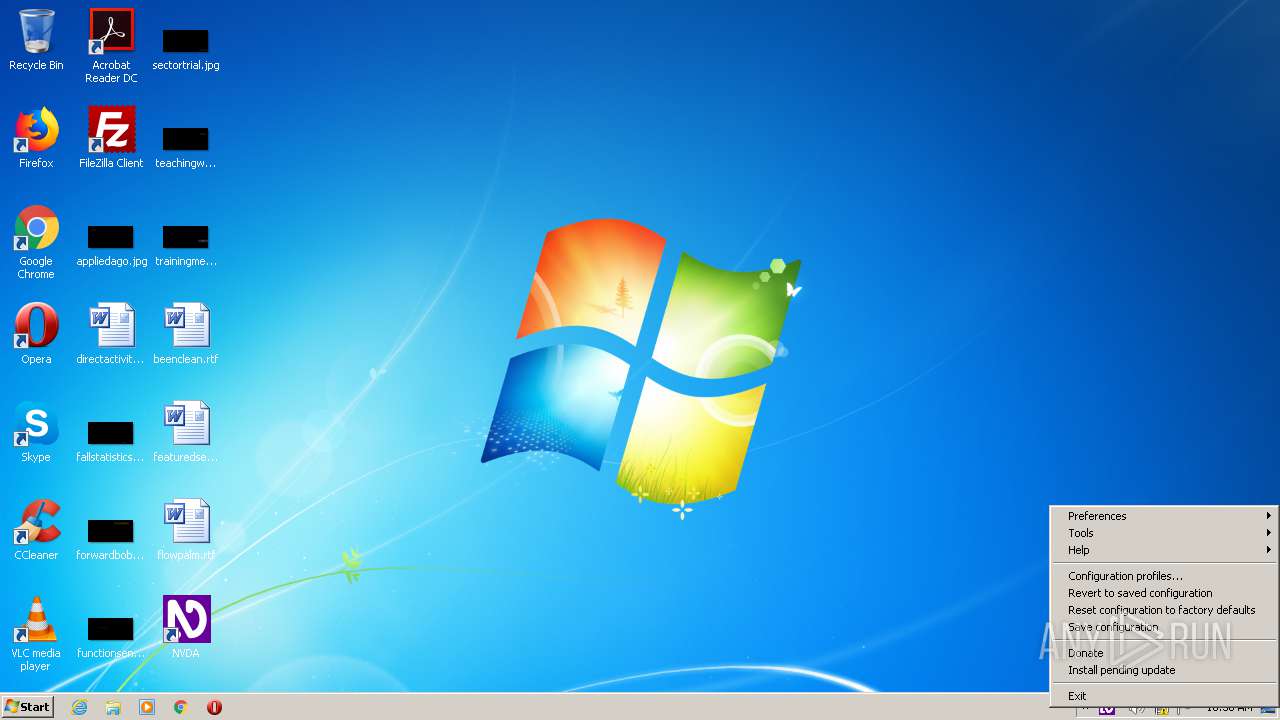
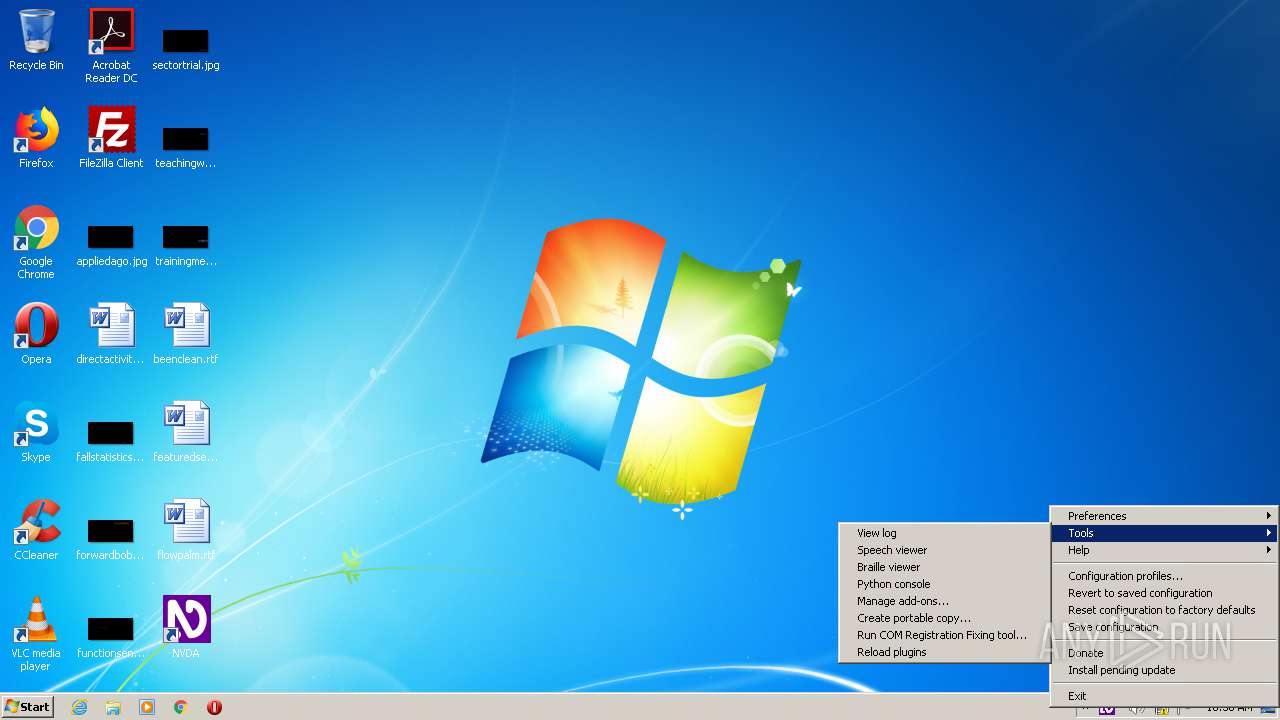
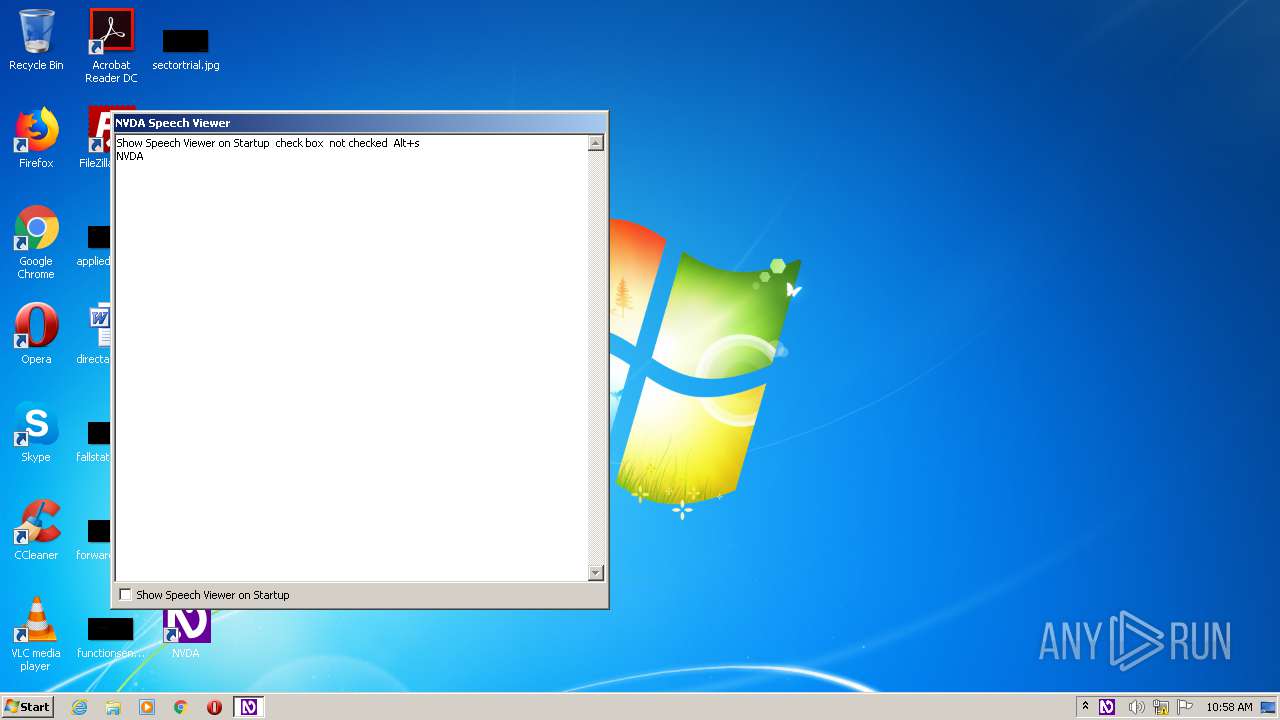
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 034A26F0908A63598E5765E54AA3A881 |
| SHA1: | 55CECB2DC865B344DC18039FDF2B80CB4229DAB5 |
| SHA256: | 9BEA6EB5F6DC13A7CFA48531732E6BEDA11A27F55986EDB4B0B6DDD8389B1359 |
| SSDEEP: | 393216:Xoa+tlftpQO9W8ePpTernQ5kYSBwAYUHwfNcWVii039Vn2BiJA1fbMc:4V/QO48mezQGJYwGNcWjNBiJApMc |
MALICIOUS
Application was dropped or rewritten from another process
- nvda_noUIAccess.exe (PID: 3832)
- nvda_slave.exe (PID: 1400)
- nvda.exe (PID: 2864)
- nvda.exe (PID: 3732)
- nvda.exe (PID: 772)
- nvda_eoaProxy.exe (PID: 1932)
- nvda_eoaProxy.exe (PID: 392)
- nvda_slave.exe (PID: 3804)
- nvda.exe (PID: 2460)
- nvda_eoaProxy.exe (PID: 3980)
- nvda_eoaProxy.exe (PID: 1496)
Loads dropped or rewritten executable
- nvda_2020.2.exe (PID: 1064)
- nvda_noUIAccess.exe (PID: 3832)
- explorer.exe (PID: 352)
- nvda_slave.exe (PID: 1400)
- nvda_eoaProxy.exe (PID: 392)
- nvda_slave.exe (PID: 3804)
- nvda.exe (PID: 2460)
- nvda.exe (PID: 3732)
- nvda_eoaProxy.exe (PID: 3980)
Registers / Runs the DLL via REGSVR32.EXE
- nvda_slave.exe (PID: 1400)
SUSPICIOUS
Executable content was dropped or overwritten
- nvda_2020.2.exe (PID: 1064)
- nvda_slave.exe (PID: 1400)
Loads Python modules
- nvda_noUIAccess.exe (PID: 3832)
- nvda_slave.exe (PID: 1400)
- nvda.exe (PID: 3732)
- nvda_eoaProxy.exe (PID: 392)
- nvda_slave.exe (PID: 3804)
- nvda.exe (PID: 2460)
- nvda_eoaProxy.exe (PID: 3980)
Modifies the open verb of a shell class
- nvda_slave.exe (PID: 1400)
Creates a software uninstall entry
- nvda_slave.exe (PID: 1400)
Creates COM task schedule object
- regsvr32.exe (PID: 2140)
- regsvr32.exe (PID: 3068)
Searches for installed software
- nvda.exe (PID: 3732)
- nvda.exe (PID: 2460)
Creates files in the user directory
- nvda.exe (PID: 3732)
- nvda.exe (PID: 2460)
Creates files in the program directory
- nvda_slave.exe (PID: 1400)
INFO
Dropped object may contain Bitcoin addresses
- nvda_2020.2.exe (PID: 1064)
- nvda_slave.exe (PID: 1400)
Reads settings of System Certificates
- nvda.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:20:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x326c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2020.2.0.20631 |
| ProductVersionNumber: | 2020.2.0.20631 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | NVDA launcher file |
| FileVersion: | 2020.2.0.20631 |
| LegalCopyright: | Copyright (C) 2006-2020 NVDA Contributors |
| ProductName: | NVDA |
| ProductVersion: | 2020.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:20:09 |
| Detected languages: |
|
| FileDescription: | NVDA launcher file |
| FileVersion: | 2020.2.0.20631 |
| LegalCopyright: | Copyright (C) 2006-2020 NVDA Contributors |
| ProductName: | NVDA |
| ProductVersion: | 2020.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:20:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C74 | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41039 |
.rdata | 0x00007000 | 0x00001196 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20374 |
.data | 0x00009000 | 0x0001B058 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.13053 |
.ndata | 0x00025000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00030000 | 0x000054A8 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.48873 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22372 | 947 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.89384 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
67
Monitored processes
17
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Program Files\NVDA\nvda_eoaProxy.exe" | C:\Program Files\NVDA\nvda_eoaProxy.exe | utilman.exe | ||||||||||||
User: admin Company: NV Access Integrity Level: HIGH Description: NVDA Ease of Access proxy Exit code: 0 Version: 2020.2.0.20631 Modules
| |||||||||||||||
| 772 | "C:\Program Files\NVDA\nvda.exe" -r | C:\Program Files\NVDA\nvda.exe | — | nvda_slave.exe | |||||||||||
User: admin Company: NV Access Integrity Level: MEDIUM Description: NVDA application Exit code: 3221226540 Version: 2020.2.0.20631 Modules
| |||||||||||||||
| 1064 | "C:\Users\admin\AppData\Local\Temp\nvda_2020.2.exe" | C:\Users\admin\AppData\Local\Temp\nvda_2020.2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: NVDA launcher file Exit code: 0 Version: 2020.2.0.20631 Modules
| |||||||||||||||
| 1400 | "C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\app\nvda_slave.exe" install 1 1 | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\app\nvda_slave.exe | nvda_noUIAccess.exe | ||||||||||||
User: admin Company: NV Access Integrity Level: HIGH Description: NVDA Exit code: 0 Version: 2020.2.0.20631 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\NVDA\nvda_eoaProxy.exe" | C:\Program Files\NVDA\nvda_eoaProxy.exe | — | utilman.exe | |||||||||||
User: admin Company: NV Access Integrity Level: MEDIUM Description: NVDA Ease of Access proxy Exit code: 3221226540 Version: 2020.2.0.20631 Modules
| |||||||||||||||
| 1716 | C:\Windows\regedit.exe /s COMRegistryFixes\oleaccProxy.reg | C:\Windows\regedit.exe | nvda_slave.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1932 | "C:\Program Files\NVDA\nvda_eoaProxy.exe" | C:\Program Files\NVDA\nvda_eoaProxy.exe | — | utilman.exe | |||||||||||
User: admin Company: NV Access Integrity Level: MEDIUM Description: NVDA Ease of Access proxy Exit code: 3221226540 Version: 2020.2.0.20631 Modules
| |||||||||||||||
| 2140 | C:\Windows\system32\regsvr32.exe /s C:\Windows\system32\actxprxy.dll | C:\Windows\system32\regsvr32.exe | — | nvda_slave.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2460 | "C:\Program Files\NVDA\nvda.exe" -r | C:\Program Files\NVDA\nvda.exe | nvda_slave.exe | ||||||||||||
User: admin Company: NV Access Integrity Level: HIGH Description: NVDA application Exit code: 0 Version: 2020.2.0.20631 Modules
| |||||||||||||||
Total events
5 155
Read events
2 487
Write events
2 666
Delete events
2
Modification events
| (PID) Process: | (3832) nvda_noUIAccess.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: nvda_noUIAccess.exe | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\afi495O.gzc\ncc\aiqn_abHVNpprff.rkr |
Value: 000000000000000000000000800A0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004A00000071000000FC7F32000C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D02 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\afi495O.gzc\ncc\aiqn_abHVNpprff.rkr |
Value: 0000000000000000000000002D100000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004A00000071000000A98532000C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D02 | |||
| (PID) Process: | (3832) nvda_noUIAccess.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3832) nvda_noUIAccess.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1400) nvda_slave.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NVDA |
| Operation: | write | Name: | DisplayName |
Value: NVDA | |||
| (PID) Process: | (1400) nvda_slave.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NVDA |
| Operation: | write | Name: | DisplayVersion |
Value: 2020.2 | |||
| (PID) Process: | (1400) nvda_slave.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NVDA |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\NVDA\images\nvda.ico | |||
Executable files
197
Suspicious files
82
Text files
1 847
Unknown types
347
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1064 | nvda_2020.2.exe | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\Banner.dll | executable | |
MD5:— | SHA256:— | |||
| 1064 | nvda_2020.2.exe | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\System.dll | executable | |
MD5:56A321BD011112EC5D8A32B2F6FD3231 | SHA256:BB6DF93369B498EAA638B0BCDC4BB89F45E9B02CA12D28BCEDF4629EA7F5E0F1 | |||
| 1064 | nvda_2020.2.exe | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\app\_decimal.pyd | executable | |
MD5:05549FE7558AE558E26A58EE6D0DBB54 | SHA256:9C659E032EA882268C76AB9B0D6AE0CCE6874EFF166F64CD321226879B6D6F17 | |||
| 1064 | nvda_2020.2.exe | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\app\API-MS-Win-core-xstate-l2-1-0.dll | executable | |
MD5:9E683825EAE3B6375CBD63623196BE96 | SHA256:CBD3FEF707ABF622B150DB1D10B5443264EB6DA8F4D7AA2ADC97C50A22D4D594 | |||
| 1064 | nvda_2020.2.exe | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\app\_bz2.pyd | executable | |
MD5:8A4C977BAA9BD8C626A949AFE1678963 | SHA256:D035C0D3C1815DDC61C343692EB0CB82E8F1ADF4EBEACC680E44B8903219BF27 | |||
| 1064 | nvda_2020.2.exe | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\app\VCRUNTIME140.dll | executable | |
MD5:2EBF45DA71BD8EF910A7ECE7E4647173 | SHA256:CF39E1E81F57F42F4D60ABC1D30ECF7D773E576157AA88BBC1D672BF5AD9BB8B | |||
| 1064 | nvda_2020.2.exe | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\app\_ctypes.pyd | executable | |
MD5:35F7EDF7DD2C9C64CE5D221D1CF9FB4F | SHA256:5E64A2FD884B19F544696F197D1D91B8F205CF91C3824604AD807ED40344FD23 | |||
| 1064 | nvda_2020.2.exe | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\app\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:AABBB38C4110CC0BF7203A567734A7E7 | SHA256:24B07028C1E38B9CA2F197750654A0DFB7D33C2E52C9DD67100609499E8028DB | |||
| 1064 | nvda_2020.2.exe | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\app\_hashlib.pyd | executable | |
MD5:3FD78CBF4EB14069EC7108DF8914F919 | SHA256:DBED1162EE5D1E7A1A7C83AE2A1337042F8A636F050C491CD54B818607719CBE | |||
| 1064 | nvda_2020.2.exe | C:\Users\admin\AppData\Local\Temp\nsv495B.tmp\app\_socket.pyd | executable | |
MD5:F815C78FD043AB384203C3C65A79F718 | SHA256:DF2960527ADC8B1004D46E0EF8664EF085A6C7DE2129EE2B9883984A45E017E9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3732 | nvda.exe | 45.33.21.113:443 | www.nvaccess.org | Linode, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.nvaccess.org |
| suspicious |
Threats
Process | Message |
|---|---|
nvda_noUIAccess.exe | C:\PROJECTS\buildbots\win7-py27\dist-win32-py37\Phoenix\ext\wxWidgets\include\wx/msw/private.h(394): 'GetWindowRect' failed with error 0x00000578 (invalid window handle.).
|
nvda_noUIAccess.exe | C:\PROJECTS\buildbots\win7-py27\dist-win32-py37\Phoenix\ext\wxWidgets\include\wx/msw/private.h(394): 'GetWindowRect' failed with error 0x00000578 (invalid window handle.).
|
nvda_noUIAccess.exe | C:\PROJECTS\buildbots\win7-py27\dist-win32-py37\Phoenix\ext\wxWidgets\include\wx/msw/private.h(394): 'GetWindowRect' failed with error 0x00000578 (invalid window handle.).
|
nvda_noUIAccess.exe | ..\..\src\msw\window.cpp(1962): 'MoveWindow' failed with error 0x00000578 (invalid window handle.).
|
nvda_noUIAccess.exe | ..\..\src\msw\window.cpp(1962): 'MoveWindow' failed with error 0x00000578 (invalid window handle.).
|
regedit.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|