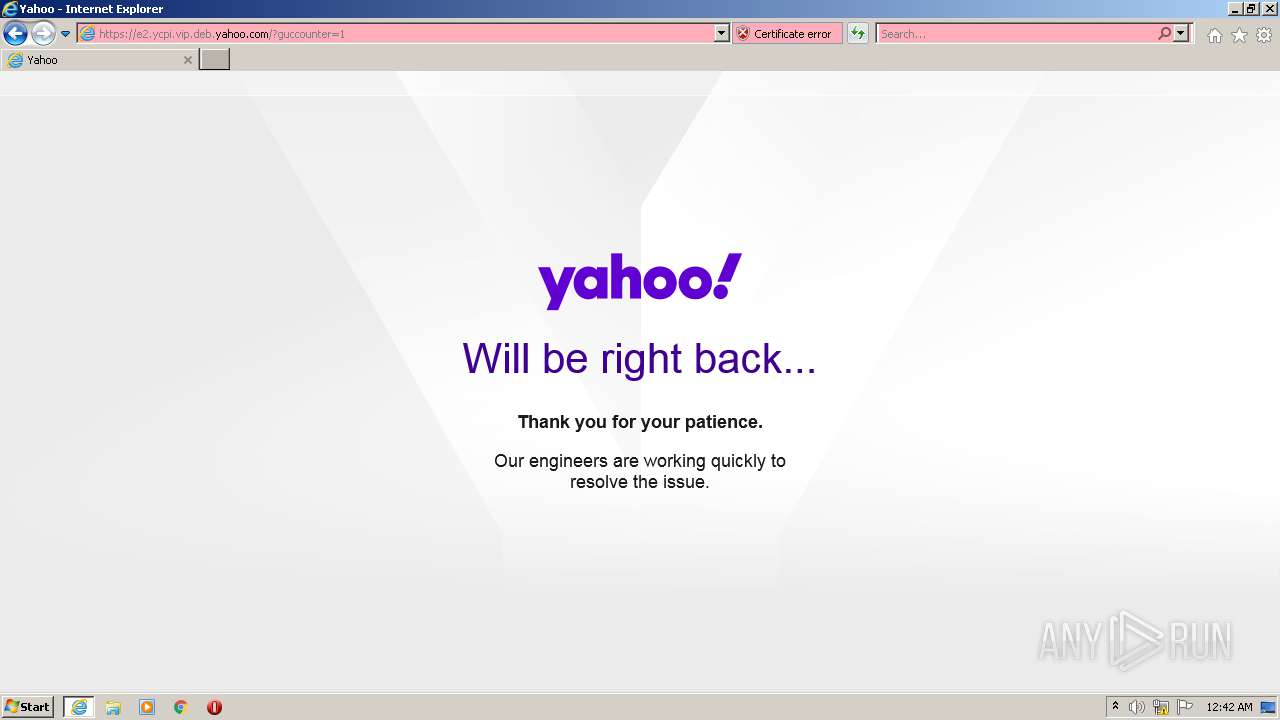
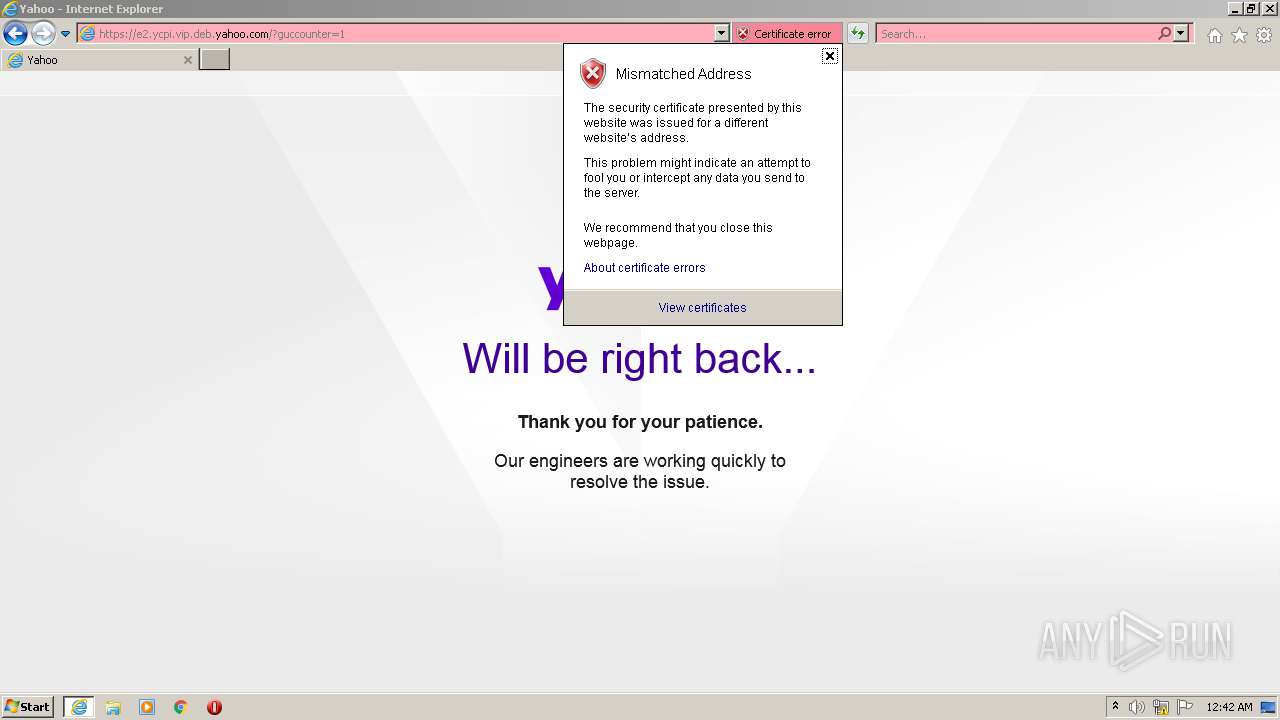
| URL: | http://e2.ycpi.vip.deb.yahoo.com |
| Full analysis: | https://app.any.run/tasks/9cf7cabf-ba87-470b-bdfb-f5989c9ab1fb |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2021, 23:41:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D7109A2BCACDD50413057284DAA392EC |
| SHA1: | 1AD2D7D7380D64566C48A58125061A1B01B46D73 |
| SHA256: | 9BE6DE2AA157F54866E83773DD92CAFF05C9B2FD26DB34F8382F3EBC53897A07 |
| SSDEEP: | 3:N1KbbWS2IEnLGT:CnJ2dyT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2700)
INFO
Checks supported languages
- iexplore.exe (PID: 900)
- iexplore.exe (PID: 2700)
Reads the computer name
- iexplore.exe (PID: 900)
- iexplore.exe (PID: 2700)
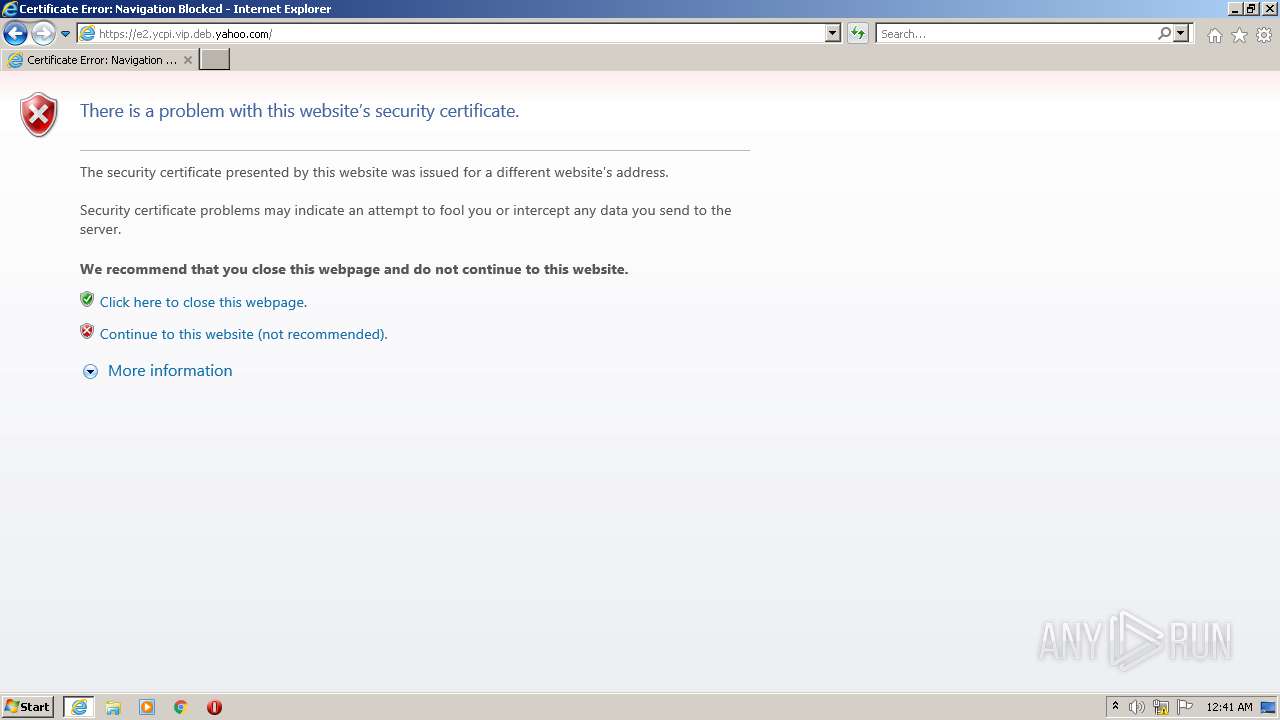
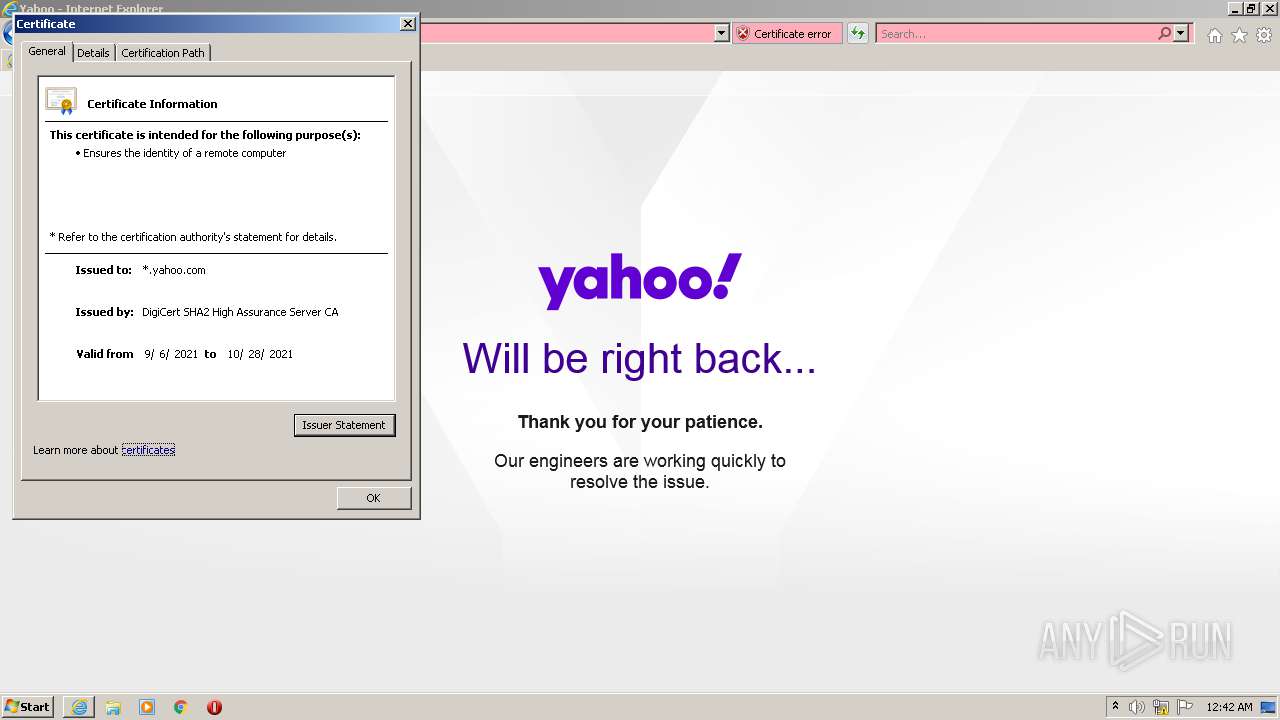
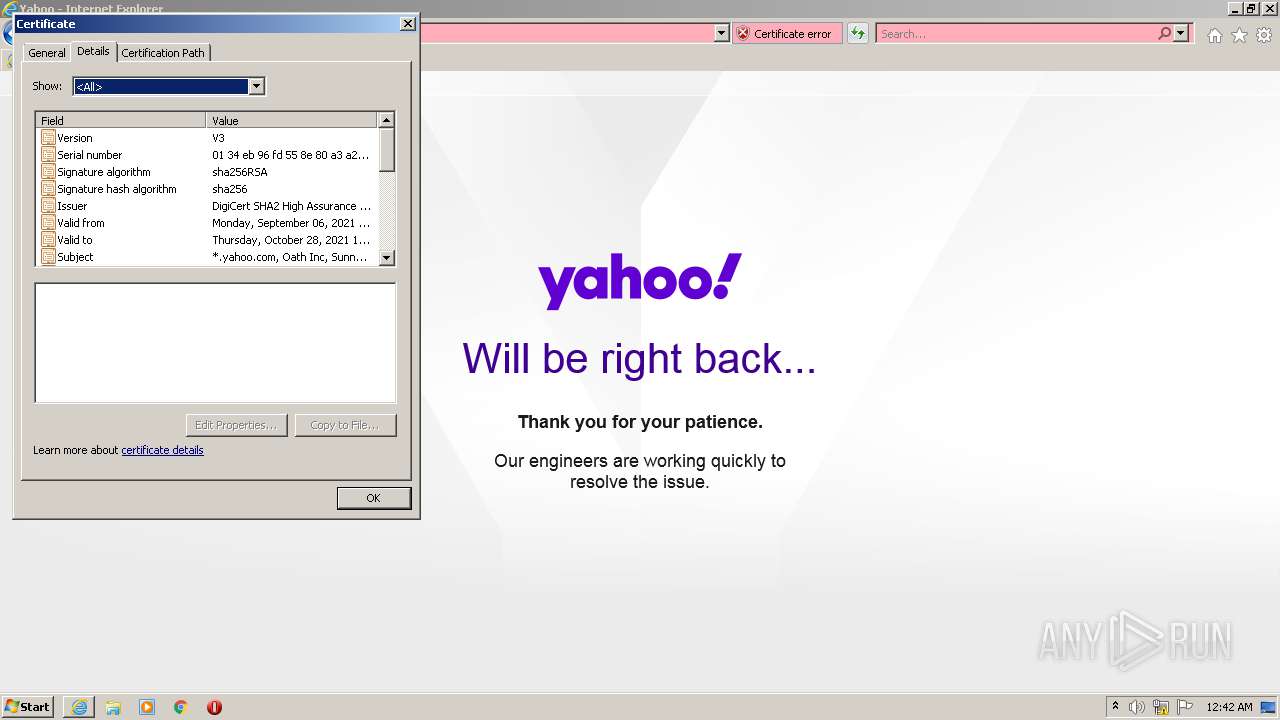
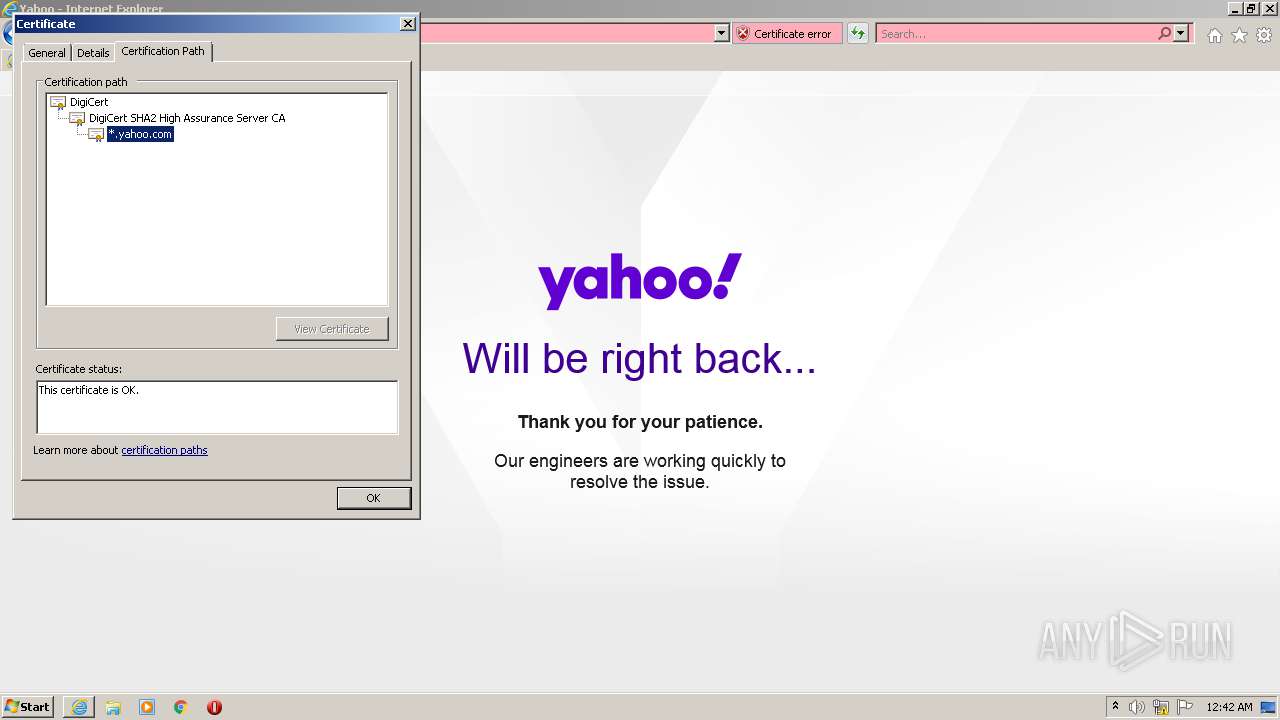
Reads settings of System Certificates
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 900)
Checks Windows Trust Settings
- iexplore.exe (PID: 900)
- iexplore.exe (PID: 2700)
Reads internet explorer settings
- iexplore.exe (PID: 2700)
Creates files in the user directory
- iexplore.exe (PID: 2700)
Changes internet zones settings
- iexplore.exe (PID: 900)
Application launched itself
- iexplore.exe (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://e2.ycpi.vip.deb.yahoo.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:900 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
14 508
Read events
14 379
Write events
129
Delete events
0
Modification events
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 948104960 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30911115 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30911115 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
10
Text files
28
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3YDORRP2.txt | text | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_56EB5147895B9679C0F6100A75FEBD21 | der | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\ZPOKDLVQ.txt | text | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\35DDEDF268117918D1D277A171D8DF7B_56EB5147895B9679C0F6100A75FEBD21 | binary | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_D1FEB916F941619E2D785FDC23E139F1 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
42
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2700 | iexplore.exe | GET | — | 99.80.204.178:80 | http://bcn.fp.yahoo.com/p?s=1197757129&t=1631749299318&err_url=http%3A%2F%2Fe2.ycpi.vip.deb.yahoo.com%2F&err=404&test=-&ats_host=e3.ycpi.deb.yahoo.com&rid=-&message=Not%20Found%20on%20Accelerator&source=brb | US | — | — | suspicious |
2700 | iexplore.exe | GET | — | 99.80.204.178:80 | http://bcn.fp.yahoo.com/p?s=1197757129&t=1631749299318&err_url=http%3A%2F%2Fe2.ycpi.vip.deb.yahoo.com%2F&err=404&test=-&ats_host=e3.ycpi.deb.yahoo.com&rid=-&message=Not%20Found%20on%20Accelerator&source=brb | US | — | — | suspicious |
2700 | iexplore.exe | GET | 404 | 87.248.118.23:80 | http://e2.ycpi.vip.deb.yahoo.com/ | GB | html | 4.64 Kb | malicious |
900 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2700 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAZWvhcvD664Av95NdAGUp4%3D | US | der | 471 b | whitelisted |
2700 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA8%2ByrdrMrlwMHSyG%2BDNqgo%3D | US | der | 471 b | whitelisted |
2700 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
900 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2700 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAdrnqMXP9deJKG5CAU3eis%3D | US | der | 471 b | whitelisted |
900 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?21c745b430f5b8b0 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
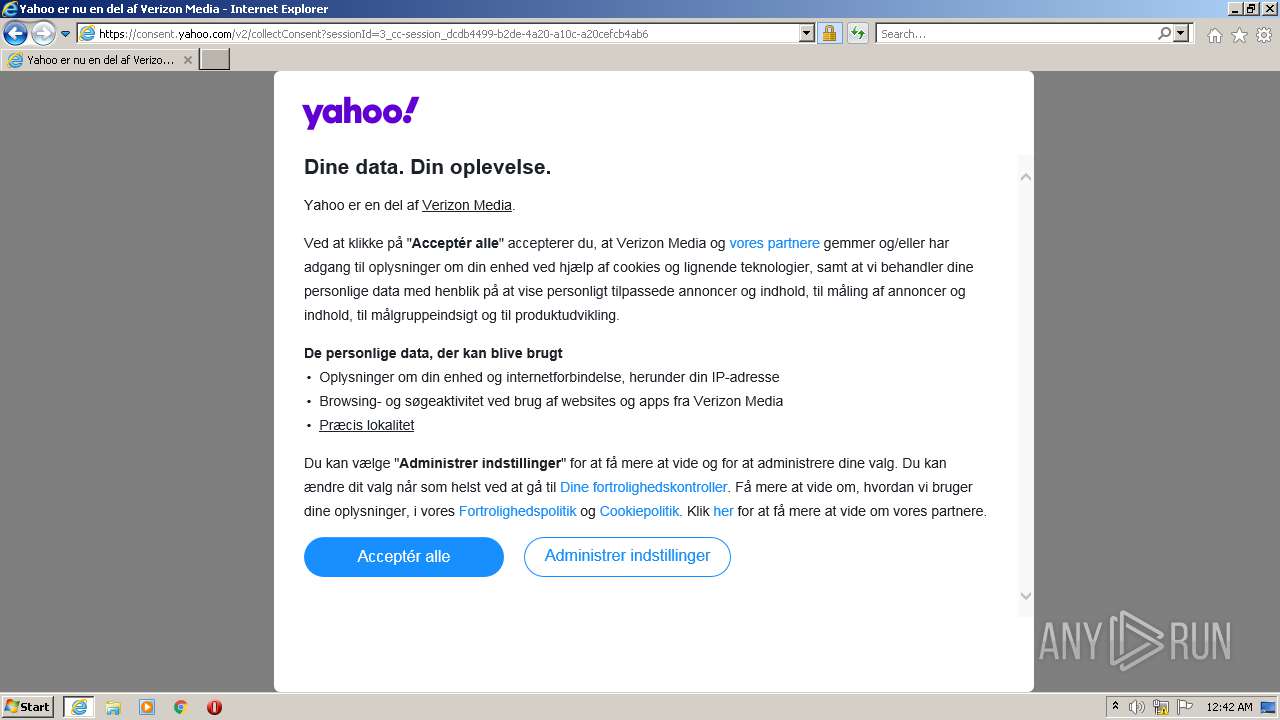
2700 | iexplore.exe | 52.208.96.136:443 | guce.yahoo.com | Amazon.com, Inc. | IE | unknown |
2700 | iexplore.exe | 52.214.129.220:443 | guce.yahoo.com | Amazon.com, Inc. | IE | unknown |
900 | iexplore.exe | 87.248.118.22:443 | s.yimg.com | Yahoo! UK Services Limited | GB | shared |
900 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2700 | iexplore.exe | 87.248.118.23:80 | e2.ycpi.vip.deb.yahoo.com | Yahoo! UK Services Limited | GB | malicious |
2700 | iexplore.exe | 188.125.72.139:80 | geo.yahoo.com | — | CH | suspicious |
2700 | iexplore.exe | 87.248.118.22:443 | s.yimg.com | Yahoo! UK Services Limited | GB | shared |
2700 | iexplore.exe | 99.80.204.178:80 | bcn.fp.yahoo.com | AT&T Services, Inc. | US | unknown |
2700 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
900 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
e2.ycpi.vip.deb.yahoo.com |
| malicious |
geo.yahoo.com |
| whitelisted |
bcn.fp.yahoo.com |
| suspicious |
s.yimg.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
guce.yahoo.com |
| whitelisted |
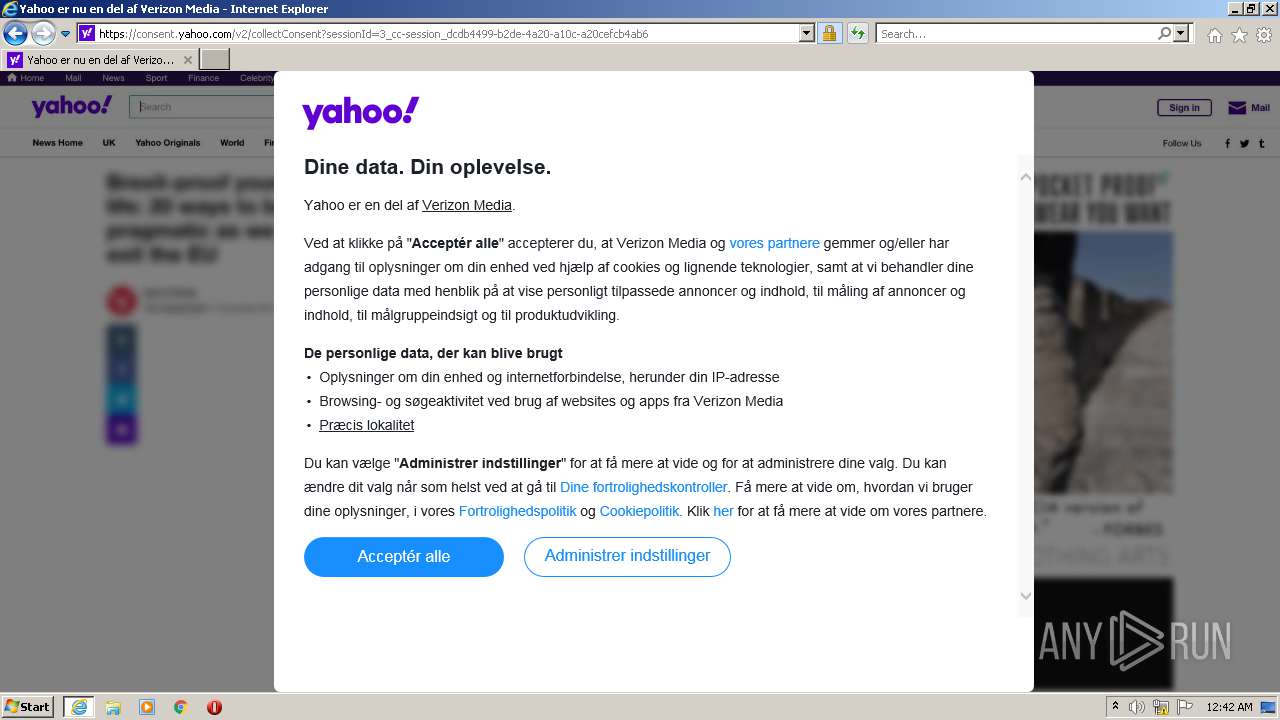
consent.yahoo.com |
| whitelisted |