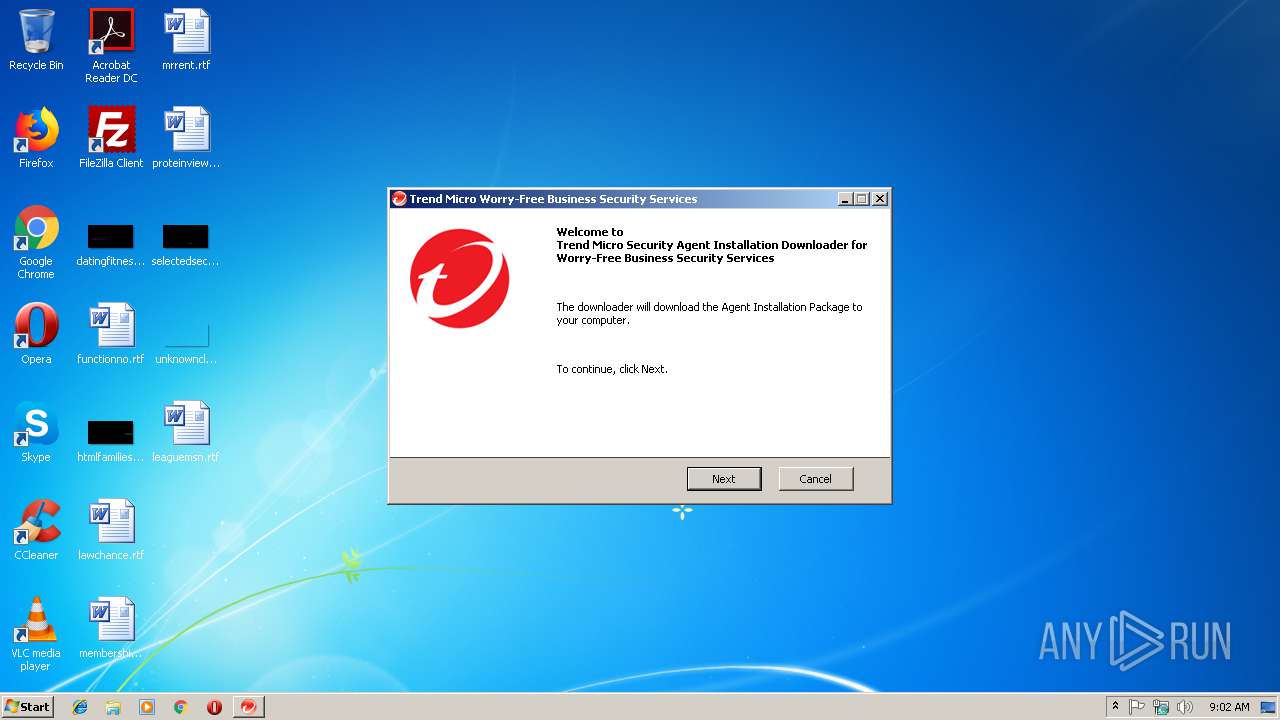
| File name: | WFBS-SVC_Downloader.exe |
| Full analysis: | https://app.any.run/tasks/872ee9e1-075a-4c12-8b89-6ffb7d00ab4f |
| Verdict: | Suspicious activity |
| Analysis date: | January 07, 2019, 09:01:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2A30EEF7308C4E7CABFD85F253102DA3 |
| SHA1: | ACEC54C91C96288D095003638181810305E48BBC |
| SHA256: | 9BE49403CF75E865D16012FECD17852BD5A7B34CF014D3C4246ECADAF1E34E0A |
| SSDEEP: | 49152:aZxtdqE1FgRJwrrqLZm6uKFuUoxPZbQpXf0X6S:aZxtdqE1FgRJqYXVuJ50sK |
MALICIOUS
Application was dropped or rewritten from another process
- Downloader.exe (PID: 584)
- WFBS-SVC_Downloader.exe (PID: 3524)
- HostedCooker.exe (PID: 2544)
Loads dropped or rewritten executable
- HostedCooker.exe (PID: 2544)
- Downloader.exe (PID: 584)
Changes settings of System certificates
- Downloader.exe (PID: 584)
SUSPICIOUS
Creates files in the user directory
- WFBS-SVC_Downloader.exe (PID: 3524)
Executable content was dropped or overwritten
- WFBS-SVC_Downloader.exe (PID: 3188)
- WFBS-SVC_Downloader.exe (PID: 3524)
Adds / modifies Windows certificates
- Downloader.exe (PID: 584)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:11 02:49:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 65536 |
| InitializedDataSize: | 40960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4b19 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.5.0.1370 |
| ProductVersionNumber: | 6.5.0.1370 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
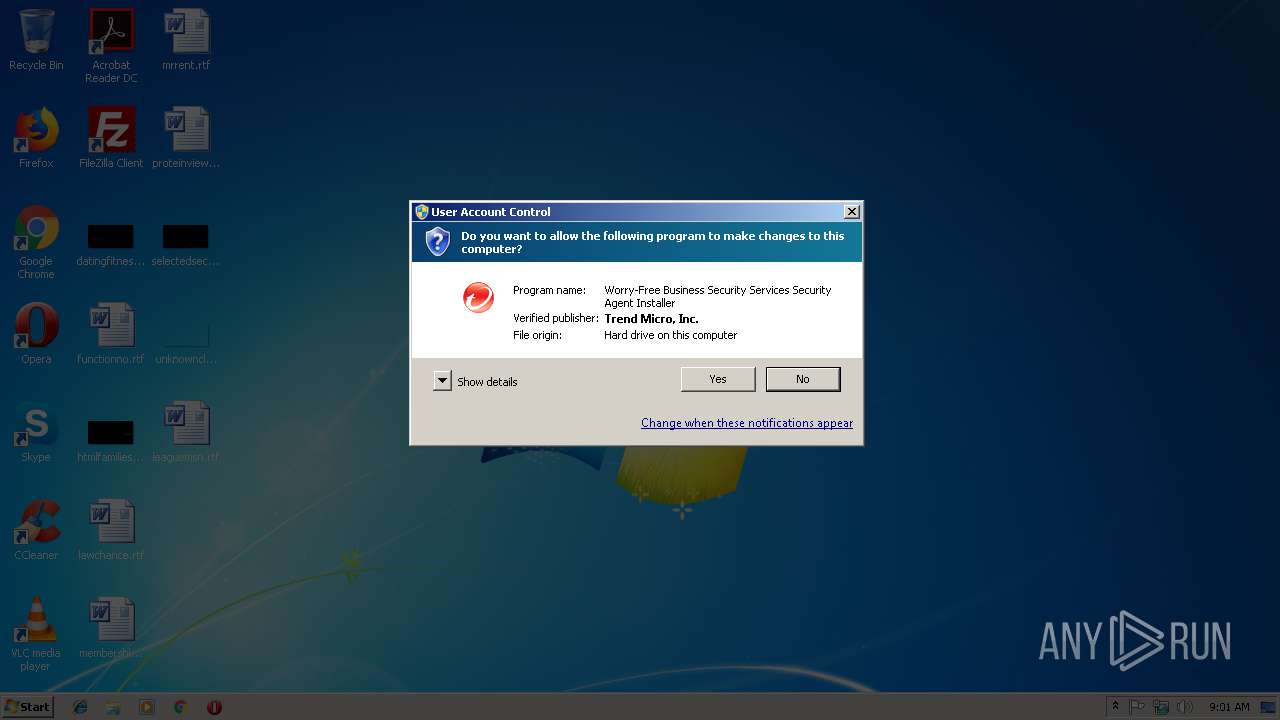
| FileDescription: | Worry-Free Business Security Services Security Agent Installer |
| InternalName: | SafeRunner.exe |
| OriginalFileName: | SafeRunner.exe |
| CompanyName: | Trend Micro Inc. |
| CoverageBuild: | None |
| CompileOption: | None |
| BuildType: | None |
| SpecialBuild: | 1370 |
| LegalTrademarks: | Copyright (C) Trend Micro Inc. |
| LegalCopyright: | Copyright (C) 2018 Trend Micro Incorporated. All rights reserved. |
| FileVersion: | 6.5.0.1370 |
| PrivateBuild: | 1370 |
| ProductName: | Trend Micro WFBSS |
| ProductVersion: | 6.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2018 01:49:23 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | Worry-Free Business Security Services Security Agent Installer |
| FileVersion: | 6.5.0.1370 |
| InternalName: | SafeRunner.exe |
| LegalCopyright: | Copyright (C) 2018 Trend Micro Incorporated. All rights reserved. |
| OriginalFilename: | SafeRunner.exe |
| CompanyName: | Trend Micro Inc. |
| CoverageBuild: | None |
| CompileOption: | None |
| BuildType: | None |
| SpecialBuild: | 1370 |
| PrivateBuild: | 1370 |
| LegalTrademarks: | Copyright (C) Trend Micro Inc. |
| ProductVersion: | 6.5 |
| ProductName: | Trend Micro WFBSS |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2018 01:49:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F771 | 0x00010000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50376 |
.rdata | 0x00011000 | 0x000033AA | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.50374 |
.data | 0x00015000 | 0x00002E9C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.636 |
.rsrc | 0x00018000 | 0x00001C20 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.86615 |
.reloc | 0x0001A000 | 0x00001A2C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.65562 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19603 | 1080 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.06035 | 872 | Latin 1 / Western European | English - United States | RT_ICON |
IDI_ICON1 | 2.40927 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Users\admin\AppData\Local\Temp\7zS5662.tmp\Downloader\Downloader.exe" /sys_dll_check /tag="dHlwZT1kb3dubG9hZGVyJmRpZD01NjUyODEma2V5PTVlMzM1YThmY2FkZjZjNGVhMzNmYjE0ZTZhNzZkYWFjJmxhbmc9ZGUmc2V2X2lwPXdmYnMtc3ZjLWVtZWEtYWFsLnRyZW5kbWljcm8uY29tJnN2Y19pZD0xJmFnZW50X21vZGU9MSZ1cmw9aHR0cHMlM0ElMkYlMkZ3ZmJzLXN2Yy1lbWVhLWFhbC50cmVuZG1pY3JvLmNvbSUyRmZpbGVyJTJGYWFsJTJGcGFja2FnZXMlMkZzZXJ2aWNlLmQlMkZ3ZmJzLXN2YyUyRkRvd25sb2FkZXIuaW5pJmZjPVptTXVZVzUwYVhacGNuVnpMbkJ5YjNacGMybHZiajB4Sm1aakxtWnBjbVYzWVd4c0xuQnliM1pwYzJsdmJqMHhKbVpqTG5kbFlsOXlaWEIxZEdGMGFXOXVMbkJ5YjNacGMybHZiajB4Sm1aakxuVnliRjltYVd4MFpYSnBibWN1Y0hKdmRtbHphVzl1UFRFbVptTXVZbVZvWVhacGIzSmZiVzl1YVhSdmNpNXdjbTkyYVhOcGIyNDlNU1ptWXk1MGIyOXNZbUZ5TG5CeWIzWnBjMmx2Ymowd0ptWmpMblJ2YjJ4aVlYSXVkSEJ2Wm1ZOU1TWm1ZeTUwYjI5c1ltRnlMblJuY0c5bVpqMHhKbVpqTG5SdmIyeGlZWEl1ZEcxaGMyOW1aajB4Sm1Ga2JTNTNabkp0UFRFJTNEJmNyZWF0ZWRfYXQ9MTU0NjUxMDQ1NCZzaWc9bkZuU0U0MS8zQkMwcDE2bWxrcE1haUdWdkQrTzYrZFRGcWUxYVh2QnM4WkZNYmN1WnBha1RpOVN0UHFTV244WVdkb3NxNjZjT3l0aVFLbGdUd2dZbGtIQzErckpyM0hwTHpwa2Q1bWptdE9XdkYwVm84dENRNmc5eGVXN0dkOTd4NDNuWWlKczhidjVtYmU2cUh4OVFubnFBVkZQcGpTTStyYURvTVU1RTVkcWRXUU1ZRHhlYnliSjVTWGFxYmtXSjJ4MTlRSFRjMHJmVDBGVUU1dFRuWjFQT3ZUSHFGbmhIMUJBZHdaSS9HZDVFeTBTQUNJa09uVTRzZGExOGVINGU2Mjl3Wmd4RHExQm11UDEwc3lqU05GWXUweldNSzBjdlRIMm5PZ1N2SjRZZTU0dVVQWG5QQUg2RHZaL1VjTWxKWk1xV1ltVVcyUVRXV3E5RGFuNGlBPT0=" | C:\Users\admin\AppData\Local\Temp\7zS5662.tmp\Downloader\Downloader.exe | WFBS-SVC_Downloader.exe | ||||||||||||
User: admin Company: Trend Micro Inc. Integrity Level: HIGH Exit code: 0 Version: 6.5.0.1370 Modules
| |||||||||||||||
| 2544 | "C:\Users\admin\AppData\Local\Temp\7zS5662.tmp\Downloader\HostedCooker.exe" openfwexception 1 | C:\Users\admin\AppData\Local\Temp\7zS5662.tmp\Downloader\HostedCooker.exe | — | Downloader.exe | |||||||||||
User: admin Company: Trend Micro Inc. Integrity Level: HIGH Description: Hosted Cooker Exit code: 0 Version: 6.5.0.1370 Modules
| |||||||||||||||
| 3156 | "C:\Users\admin\AppData\Local\Temp\WFBS-SVC_Downloader.exe" | C:\Users\admin\AppData\Local\Temp\WFBS-SVC_Downloader.exe | — | explorer.exe | |||||||||||
User: admin Company: Trend Micro Inc. Integrity Level: MEDIUM Description: Worry-Free Business Security Services Security Agent Installer Exit code: 3221226540 Version: 6.5.0.1370 Modules
| |||||||||||||||
| 3188 | "C:\Users\admin\AppData\Local\Temp\WFBS-SVC_Downloader.exe" | C:\Users\admin\AppData\Local\Temp\WFBS-SVC_Downloader.exe | explorer.exe | ||||||||||||
User: admin Company: Trend Micro Inc. Integrity Level: HIGH Description: Worry-Free Business Security Services Security Agent Installer Exit code: 0 Version: 6.5.0.1370 Modules
| |||||||||||||||
| 3524 | "C:\Users\admin\AppData\Local\Temp\WFBS-SVC_Downloader.exe" /sys_dll_check /tag="dHlwZT1kb3dubG9hZGVyJmRpZD01NjUyODEma2V5PTVlMzM1YThmY2FkZjZjNGVhMzNmYjE0ZTZhNzZkYWFjJmxhbmc9ZGUmc2V2X2lwPXdmYnMtc3ZjLWVtZWEtYWFsLnRyZW5kbWljcm8uY29tJnN2Y19pZD0xJmFnZW50X21vZGU9MSZ1cmw9aHR0cHMlM0ElMkYlMkZ3ZmJzLXN2Yy1lbWVhLWFhbC50cmVuZG1pY3JvLmNvbSUyRmZpbGVyJTJGYWFsJTJGcGFja2FnZXMlMkZzZXJ2aWNlLmQlMkZ3ZmJzLXN2YyUyRkRvd25sb2FkZXIuaW5pJmZjPVptTXVZVzUwYVhacGNuVnpMbkJ5YjNacGMybHZiajB4Sm1aakxtWnBjbVYzWVd4c0xuQnliM1pwYzJsdmJqMHhKbVpqTG5kbFlsOXlaWEIxZEdGMGFXOXVMbkJ5YjNacGMybHZiajB4Sm1aakxuVnliRjltYVd4MFpYSnBibWN1Y0hKdmRtbHphVzl1UFRFbVptTXVZbVZvWVhacGIzSmZiVzl1YVhSdmNpNXdjbTkyYVhOcGIyNDlNU1ptWXk1MGIyOXNZbUZ5TG5CeWIzWnBjMmx2Ymowd0ptWmpMblJ2YjJ4aVlYSXVkSEJ2Wm1ZOU1TWm1ZeTUwYjI5c1ltRnlMblJuY0c5bVpqMHhKbVpqTG5SdmIyeGlZWEl1ZEcxaGMyOW1aajB4Sm1Ga2JTNTNabkp0UFRFJTNEJmNyZWF0ZWRfYXQ9MTU0NjUxMDQ1NCZzaWc9bkZuU0U0MS8zQkMwcDE2bWxrcE1haUdWdkQrTzYrZFRGcWUxYVh2QnM4WkZNYmN1WnBha1RpOVN0UHFTV244WVdkb3NxNjZjT3l0aVFLbGdUd2dZbGtIQzErckpyM0hwTHpwa2Q1bWptdE9XdkYwVm84dENRNmc5eGVXN0dkOTd4NDNuWWlKczhidjVtYmU2cUh4OVFubnFBVkZQcGpTTStyYURvTVU1RTVkcWRXUU1ZRHhlYnliSjVTWGFxYmtXSjJ4MTlRSFRjMHJmVDBGVUU1dFRuWjFQT3ZUSHFGbmhIMUJBZHdaSS9HZDVFeTBTQUNJa09uVTRzZGExOGVINGU2Mjl3Wmd4RHExQm11UDEwc3lqU05GWXUweldNSzBjdlRIMm5PZ1N2SjRZZTU0dVVQWG5QQUg2RHZaL1VjTWxKWk1xV1ltVVcyUVRXV3E5RGFuNGlBPT0=" | C:\Users\admin\AppData\Local\Temp\srun_201901070901569050000015824\WFBS-SVC_Downloader.exe | WFBS-SVC_Downloader.exe | ||||||||||||
User: admin Company: Trend Micro Inc. Integrity Level: HIGH Description: SFXSetup program Exit code: 0 Version: 6.5.0.1370 Modules
| |||||||||||||||
Total events
893
Read events
849
Write events
44
Delete events
0
Modification events
| (PID) Process: | (3524) WFBS-SVC_Downloader.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (584) Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Downloader_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (584) Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Downloader_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (584) Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Downloader_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (584) Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Downloader_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (584) Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Downloader_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3524) WFBS-SVC_Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3524) WFBS-SVC_Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (584) Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Downloader_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (584) Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Downloader_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
21
Suspicious files
3
Text files
52
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3524 | WFBS-SVC_Downloader.exe | C:\Users\admin\AppData\Local\Temp\4E8C.tmp | — | |
MD5:— | SHA256:— | |||
| 3524 | WFBS-SVC_Downloader.exe | C:\Users\admin\AppData\Local\Temp\4EBC.tmp | — | |
MD5:— | SHA256:— | |||
| 3524 | WFBS-SVC_Downloader.exe | C:\Users\admin\AppData\Local\Temp\4F3A.tmp | — | |
MD5:— | SHA256:— | |||
| 3524 | WFBS-SVC_Downloader.exe | C:\Users\admin\AppData\Local\Temp\4F4B.tmp | — | |
MD5:— | SHA256:— | |||
| 3524 | WFBS-SVC_Downloader.exe | C:\Users\admin\AppData\Local\Temp\4F7B.tmp | — | |
MD5:— | SHA256:— | |||
| 3524 | WFBS-SVC_Downloader.exe | C:\Users\admin\AppData\Local\Temp\4FAB.tmp | — | |
MD5:— | SHA256:— | |||
| 3524 | WFBS-SVC_Downloader.exe | C:\Users\admin\AppData\Local\Temp\5077.tmp | — | |
MD5:— | SHA256:— | |||
| 3524 | WFBS-SVC_Downloader.exe | C:\Users\admin\AppData\Local\Temp\5124.tmp | — | |
MD5:— | SHA256:— | |||
| 3524 | WFBS-SVC_Downloader.exe | C:\Users\admin\AppData\Local\Temp\5134.tmp | — | |
MD5:— | SHA256:— | |||
| 3524 | WFBS-SVC_Downloader.exe | C:\Users\admin\AppData\Local\Temp\5193.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
584 | Downloader.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
584 | Downloader.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
584 | Downloader.exe | 150.70.226.32:443 | wfbs-svc-emea-aal.trendmicro.com | TREND MICRO INCORPORATED | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wfbs-svc-emea-aal.trendmicro.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |