| File name: | tdsskiller.exe |
| Full analysis: | https://app.any.run/tasks/7910a22b-2c01-42fb-908e-7dc83d9c88ab |
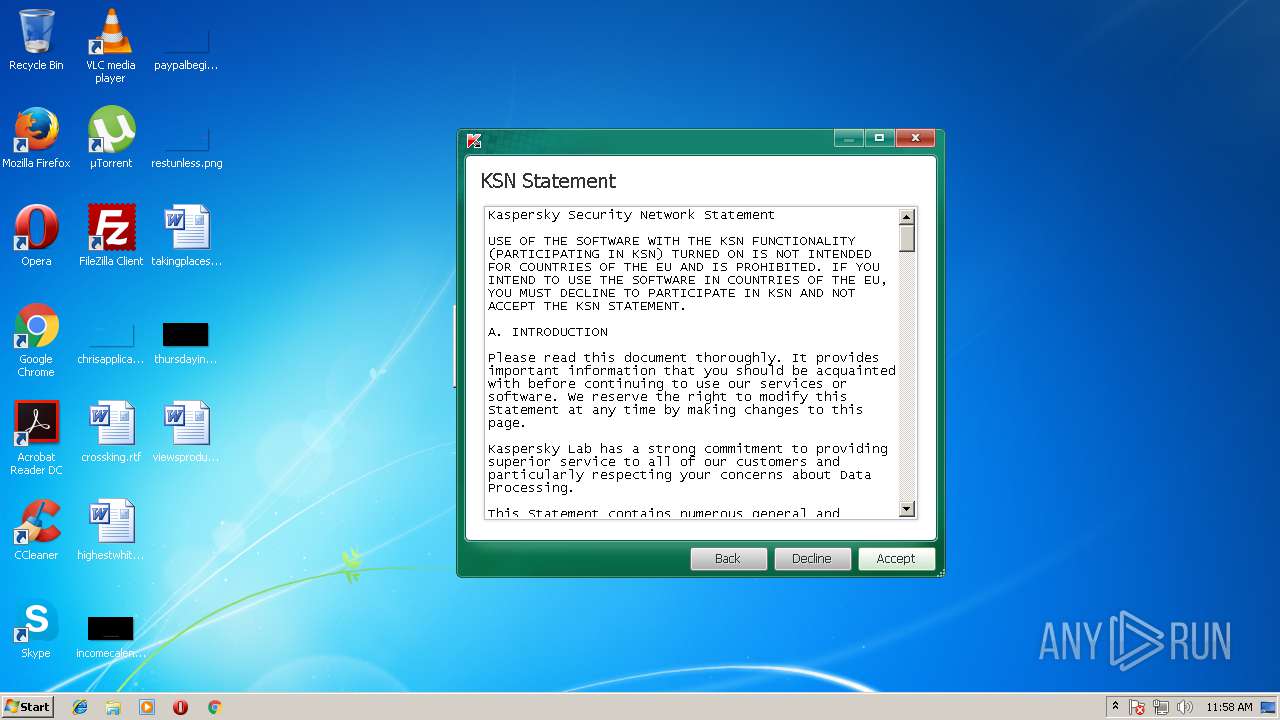
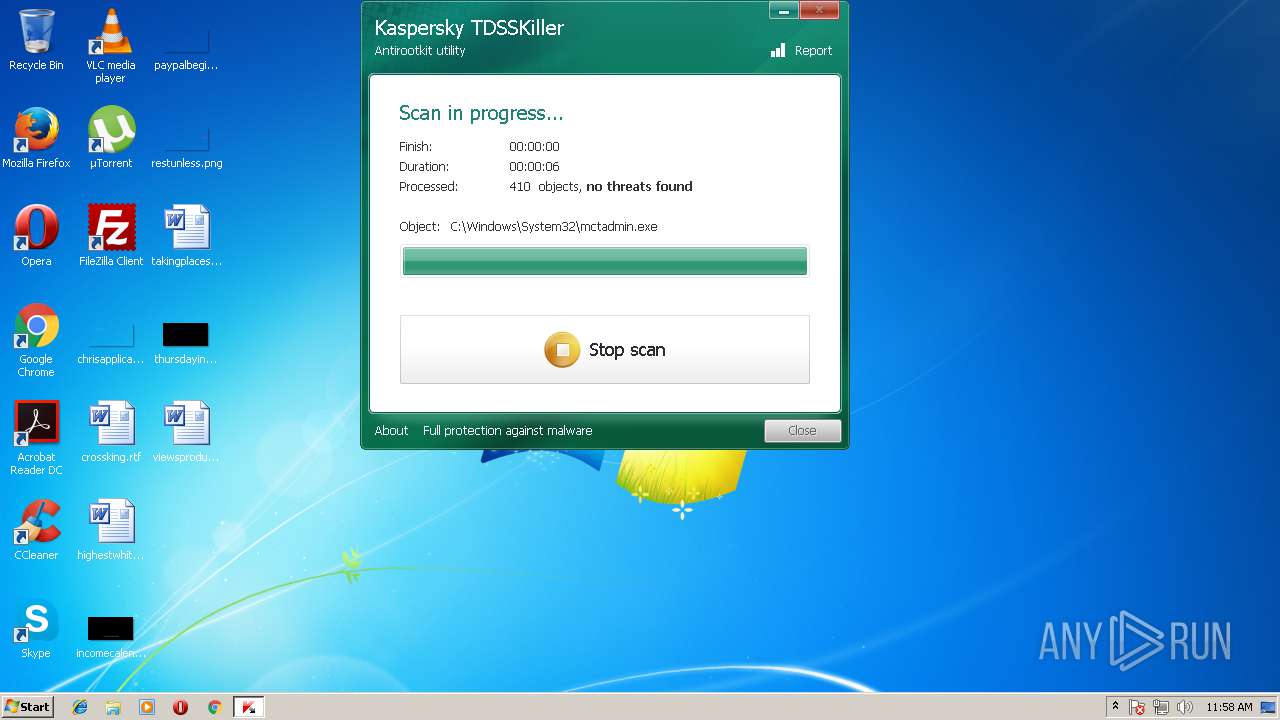
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2018, 10:58:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C2B4BD1C2806848665D5BDFC3427A46C |
| SHA1: | B4714D3CFC2E619688EEEEA404128FF6A8AC01EB |
| SHA256: | 9BCB4F980549CFD9AFCC244BE1FBAB88118035BF9C7159F91CC7AC1AE3130624 |
| SSDEEP: | 98304:u7Qm0yI6fnitzIqaMEEvaoG/DKIk7IkZDCeBCGELGF:w0d6fit8nMEEC37Hk7Ik/Be |
MALICIOUS
Application was dropped or rewritten from another process
- {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe (PID: 3728)
Deletes the SafeBoot registry key
- {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe (PID: 3728)
SUSPICIOUS
Creates files in the Windows directory
- {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe (PID: 3728)
Creates files in the driver directory
- {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe (PID: 3728)
Creates or modifies windows services
- {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe (PID: 3728)
Low-level read access rights to disk partition
- {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe (PID: 3728)
INFO
Loads rich edit control libraries
- {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe (PID: 3728)
Dropped object may contain URL's
- {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (30.7) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (30.1) |
| .exe | | | Win32 EXE Yoda's Crypter (29.5) |
| .exe | | | Win32 Executable (generic) (5) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:11 19:13:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 75776 |
| InitializedDataSize: | 4784640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3200 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
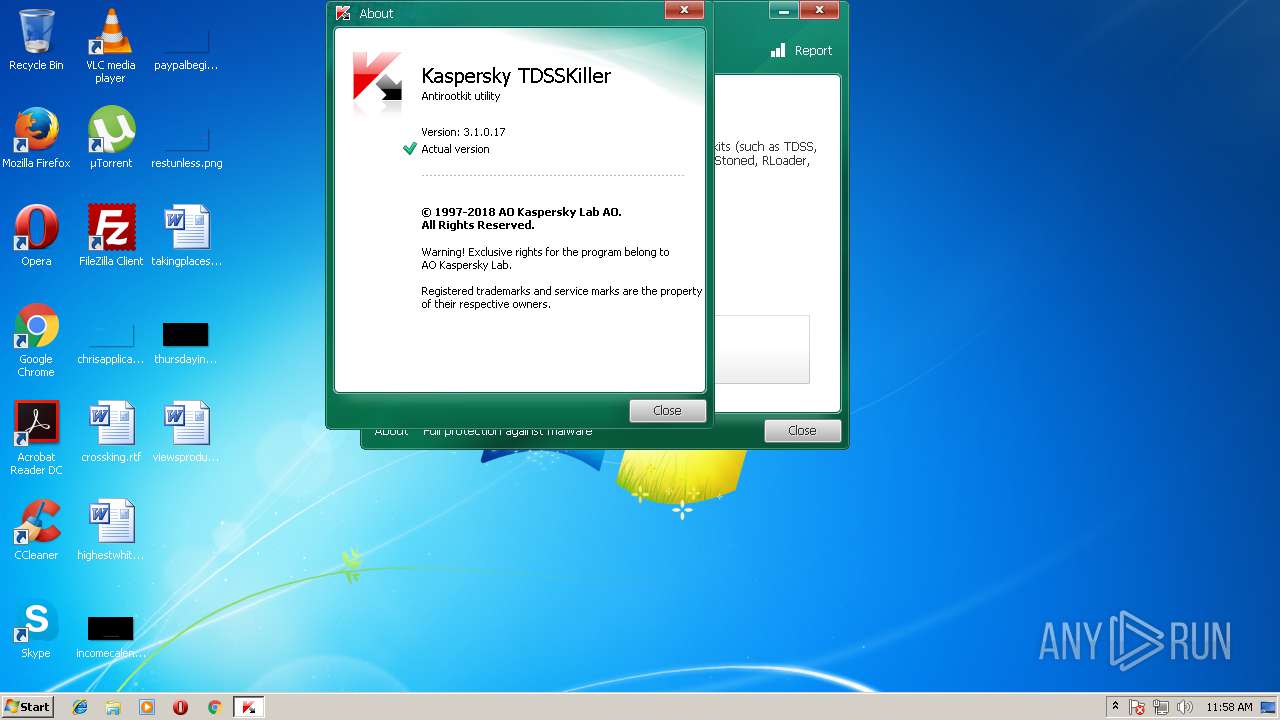
| FileVersionNumber: | 3.1.0.17 |
| ProductVersionNumber: | 3.1.0.17 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | AO Kaspersky Lab |
| LegalCopyright: | © 1997-2018 AO Kaspersky Lab. |
| LegalTrademarks: | Kaspersky™ Anti-Virus ® is registered trademark of AO Kaspersky Lab. |
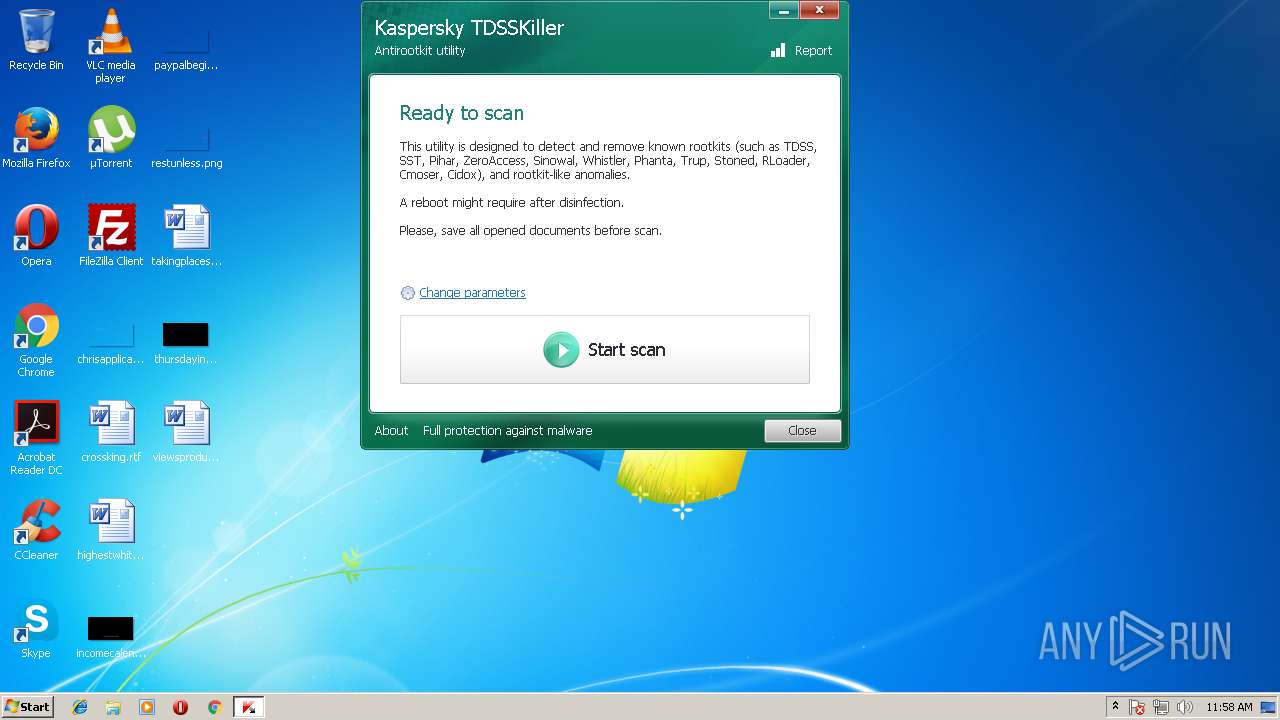
| ProductName: | TDSSKiller |
| ProductVersion: | 3.1.0.17 |
| FileVersion: | 3.1.0.17 |
| FileDescription: | TDSS rootkit removing tool |
| InternalName: | TDSSKiller |
| OriginalFileName: | TDSSKiller.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2015 18:13:14 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | AO Kaspersky Lab |
| LegalCopyright: | © 1997-2018 AO Kaspersky Lab. |
| LegalTrademarks: | Kaspersky™ Anti-Virus ® is registered trademark of AO Kaspersky Lab. |
| ProductName: | TDSSKiller |
| ProductVersion: | 3.1.0.17 |
| FileVersion: | 3.1.0.17 |
| FileDescription: | TDSS rootkit removing tool |
| InternalName: | TDSSKiller |
| OriginalFilename: | TDSSKiller.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2015 18:13:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001269F | 0x00012800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61234 |
.rdata | 0x00014000 | 0x0000714A | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20588 |
.data | 0x0001C000 | 0x000013D4 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.39338 |
.rsrc | 0x0001E000 | 0x00487260 | 0x00487400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99577 |
.reloc | 0x004A6000 | 0x0000110C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.41549 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28771 | 1117 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.70591 | 488 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 2.72293 | 296 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 3.39609 | 3752 | Latin 1 / Western European | Russian - Russia | RT_ICON |
5 | 2.99642 | 2216 | Latin 1 / Western European | Russian - Russia | RT_ICON |
6 | 3.04565 | 1736 | Latin 1 / Western European | Russian - Russia | RT_ICON |
7 | 1.27489 | 1384 | Latin 1 / Western European | Russian - Russia | RT_ICON |
101 | 7.9975 | 4734416 | Latin 1 / Western European | Russian - Russia | RT_RCDATA |
102 | 2.95517 | 104 | Latin 1 / Western European | Russian - Russia | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
RPCRT4.dll |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1756 | "C:\Users\admin\AppData\Local\Temp\tdsskiller.exe" | C:\Users\admin\AppData\Local\Temp\tdsskiller.exe | — | explorer.exe | |||||||||||
User: admin Company: AO Kaspersky Lab Integrity Level: MEDIUM Description: TDSS rootkit removing tool Exit code: 3221226540 Version: 3.1.0.17 Modules
| |||||||||||||||
| 3168 | "C:\Users\admin\AppData\Local\Temp\tdsskiller.exe" | C:\Users\admin\AppData\Local\Temp\tdsskiller.exe | explorer.exe | ||||||||||||
User: admin Company: AO Kaspersky Lab Integrity Level: HIGH Description: TDSS rootkit removing tool Exit code: 0 Version: 3.1.0.17 Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\Temp\{3F482011-E194-43A2-9AA7-F8139F6C0658}\{722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe" | C:\Users\admin\AppData\Local\Temp\{3F482011-E194-43A2-9AA7-F8139F6C0658}\{722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | tdsskiller.exe | ||||||||||||
User: admin Company: AO Kaspersky Lab Integrity Level: HIGH Description: TDSS rootkit removing tool Exit code: 0 Version: 3.1.0.17 Modules
| |||||||||||||||
Total events
228
Read events
206
Write events
18
Delete events
4
Modification events
| (PID) Process: | (3728) {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\91\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3728) {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\27511321 |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (3728) {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\27511321 |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (3728) {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\27511321 |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (3728) {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\27511321 |
| Operation: | write | Name: | ImagePath |
Value: system32\drivers\04391893.sys | |||
| (PID) Process: | (3728) {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Minimal\27511321.sys |
| Operation: | write | Name: | |
Value: Driver | |||
| (PID) Process: | (3728) {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\27511321.sys |
| Operation: | write | Name: | |
Value: Driver | |||
| (PID) Process: | (3728) {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\27511321\Enum |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3728) {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\27511321 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3728) {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Minimal\27511321.sys |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
11
Suspicious files
5
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | C:\Users\admin\AppData\Local\Temp\CabA280.tmp | — | |
MD5:— | SHA256:— | |||
| 3728 | {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | C:\Users\admin\AppData\Local\Temp\TarA291.tmp | — | |
MD5:— | SHA256:— | |||
| 3728 | {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | C:\Users\admin\AppData\Local\Temp\CabA2A1.tmp | — | |
MD5:— | SHA256:— | |||
| 3728 | {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | C:\Users\admin\AppData\Local\Temp\TarA2A2.tmp | — | |
MD5:— | SHA256:— | |||
| 3728 | {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | C:\Users\admin\AppData\Local\Temp\CabB735.tmp | — | |
MD5:— | SHA256:— | |||
| 3728 | {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | C:\Users\admin\AppData\Local\Temp\TarB736.tmp | — | |
MD5:— | SHA256:— | |||
| 3728 | {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | C:\Windows\system32\drivers\04391893.sys | — | |
MD5:— | SHA256:— | |||
| 3728 | {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3168 | tdsskiller.exe | C:\Users\admin\AppData\Local\Temp\{3F482011-E194-43A2-9AA7-F8139F6C0658}\{722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | executable | |
MD5:— | SHA256:— | |||
| 3728 | {722C28C6-BC6B-428B-BEA6-2A4393014AAA}.exe | C:\Users\admin\AppData\Local\Temp\{362195F4-9E0E-4D87-AF4A-A76C2EA854AE}\{C6CD01C2-F918-42D8-953A-3AD479A5A705}.tmp | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
19
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 52.4 Kb | whitelisted |
— | — | GET | 301 | 185.85.15.30:80 | http://support.kaspersky.com/viruses/tdsskiller.xml | RU | html | 175 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.85.15.30:80 | support.kaspersky.com | Kaspersky Lab AO | RU | suspicious |
— | — | 185.85.15.30:443 | support.kaspersky.com | Kaspersky Lab AO | RU | suspicious |
— | — | 62.128.100.131:443 | ksn-file-geo.kaspersky-labs.com | Linx Telecommunications B.V. | RU | unknown |
— | — | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 62.128.100.159:443 | ksn-file-geo.kaspersky-labs.com | Linx Telecommunications B.V. | RU | unknown |
— | — | 81.19.104.37:443 | ksn-file-geo.kaspersky-labs.com | NTT America, Inc. | ES | unknown |
— | — | 81.19.104.108:443 | ksn-file-geo.kaspersky-labs.com | NTT America, Inc. | ES | unknown |
— | — | 81.19.104.40:443 | ksn-file-geo.kaspersky-labs.com | NTT America, Inc. | ES | unknown |
— | — | 195.122.177.135:443 | ksn-file-geo.kaspersky-labs.com | Level 3 Communications, Inc. | GB | unknown |
— | — | 81.19.104.111:443 | ksn-file-geo.kaspersky-labs.com | NTT America, Inc. | ES | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
support.kaspersky.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ksn-file-geo.kaspersky-labs.com |
| suspicious |
ksn-stat-geo.kaspersky-labs.com |
| unknown |