| File name: | rmtomp3converter.exe |
| Full analysis: | https://app.any.run/tasks/3f87a0c6-1b23-4832-bacc-0202c1081eff |
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2024, 06:30:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | B8E486396096197FC75D1E15A147EE69 |
| SHA1: | A4A95F8618A3E0D2B37D0533AA7083A9958728C4 |
| SHA256: | 9BC9A627033417E09683EC5C94CF249C4E2F63F05744A9822CBF9EA09713832B |
| SSDEEP: | 98304:7RKQbG3PQnvnpxUkRsck/TfYMPKX6dUGEoRqXvC3Aka+31KkjFzrnki/AvgtSxIa:BOwl1KYkZi |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- is-R9H91.tmp (PID: 4136)
- is-S4P54.tmp (PID: 7056)
SUSPICIOUS
Process drops legitimate windows executable
- is-R9H91.tmp (PID: 4136)
- is-S4P54.tmp (PID: 7056)
Executable content was dropped or overwritten
- rmtomp3converter.exe (PID: 128)
- realalt160lite.exe (PID: 7036)
- is-R9H91.tmp (PID: 4136)
- is-S4P54.tmp (PID: 7056)
Starts CMD.EXE for commands execution
- is-R9H91.tmp (PID: 4136)
Executing commands from a ".bat" file
- is-R9H91.tmp (PID: 4136)
INFO
Checks supported languages
- rmtomp3converter.exe (PID: 128)
Create files in a temporary directory
- rmtomp3converter.exe (PID: 128)
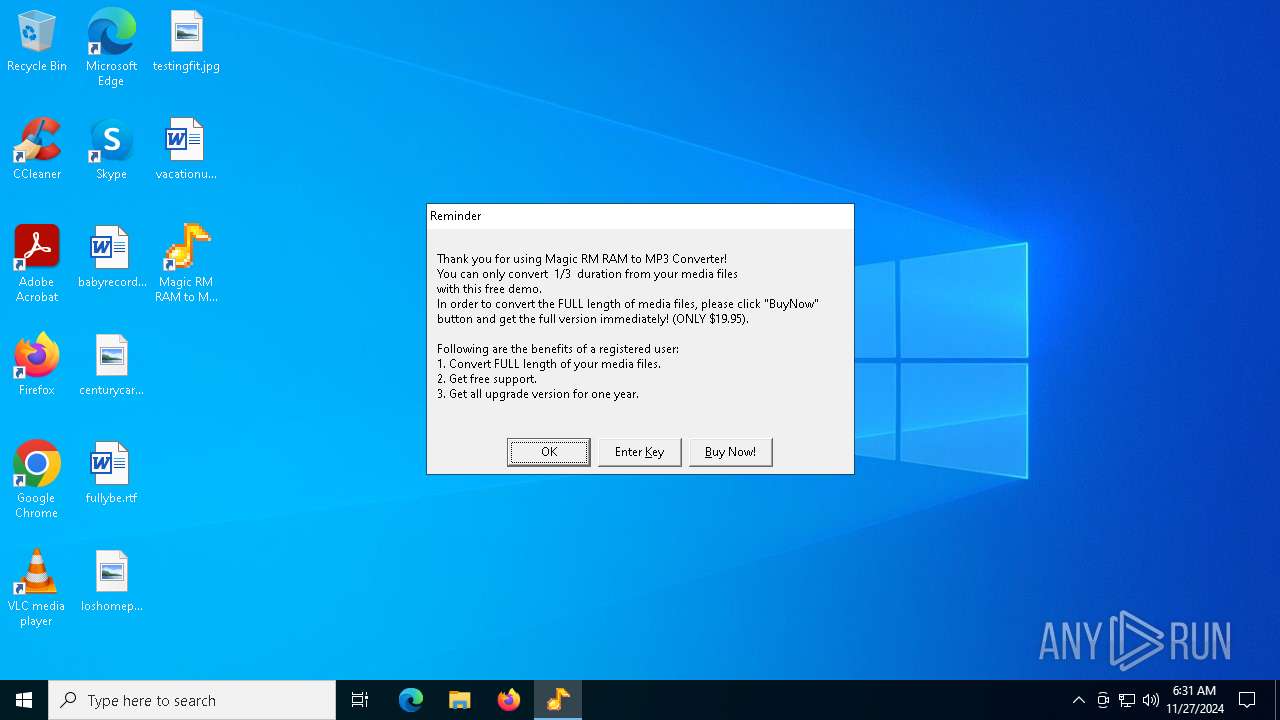
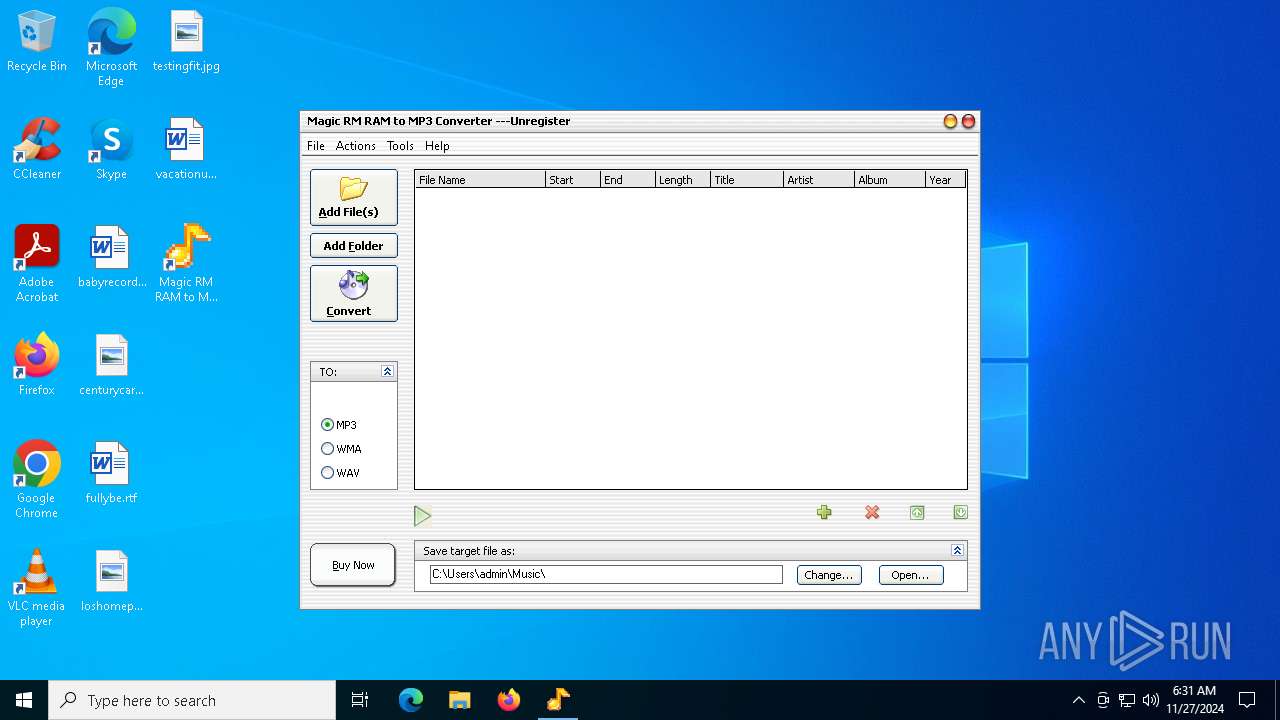
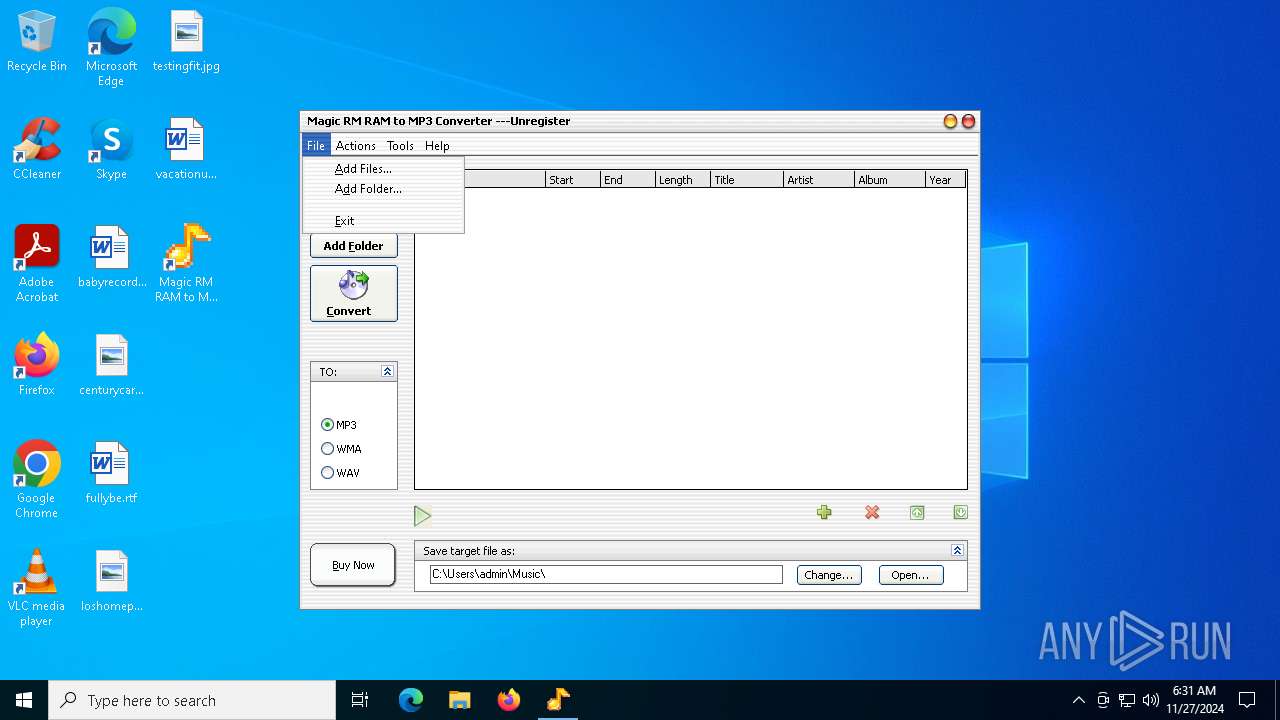
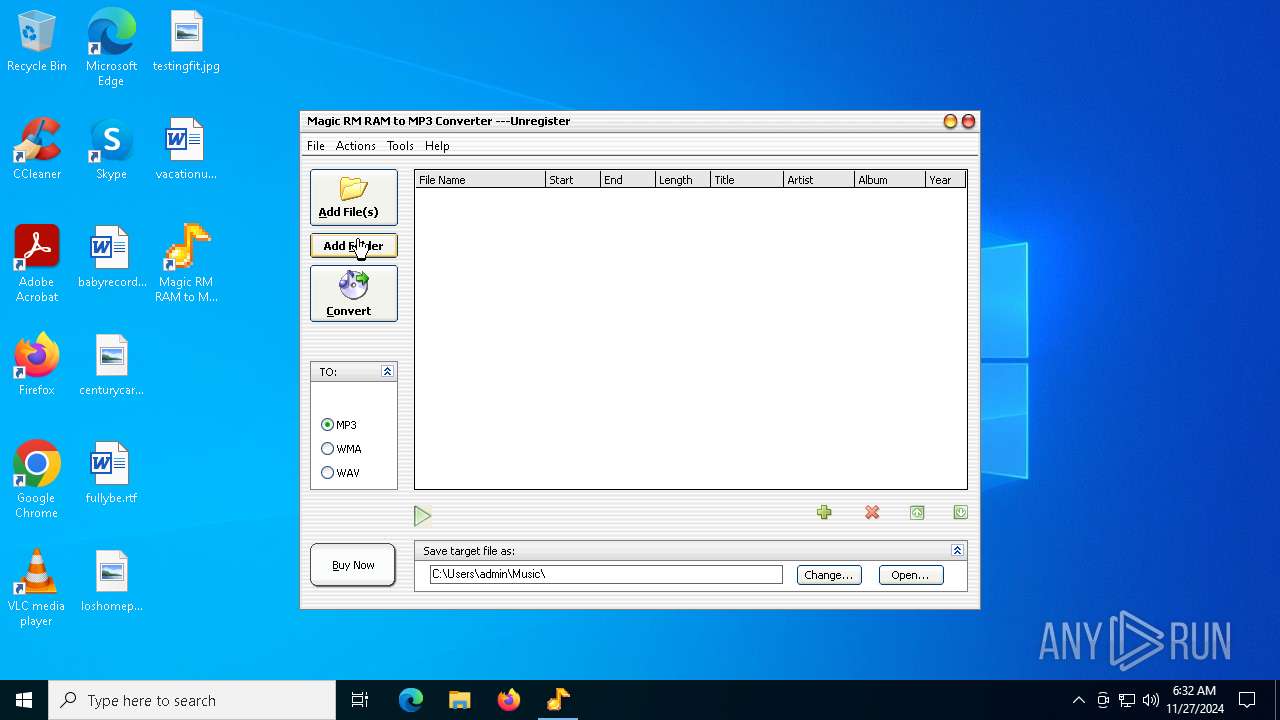
Manual execution by a user
- all2mp3.exe (PID: 6016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable PowerBASIC/Win 9.x (51.2) |
|---|---|---|
| .exe | | | Inno Setup installer (37.9) |
| .exe | | | Win32 Executable Delphi generic (4.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.2) |
| .exe | | | Win32 Executable (generic) (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37376 |
| InitializedDataSize: | 16896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x991c |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.7.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Magic Video,Inc |
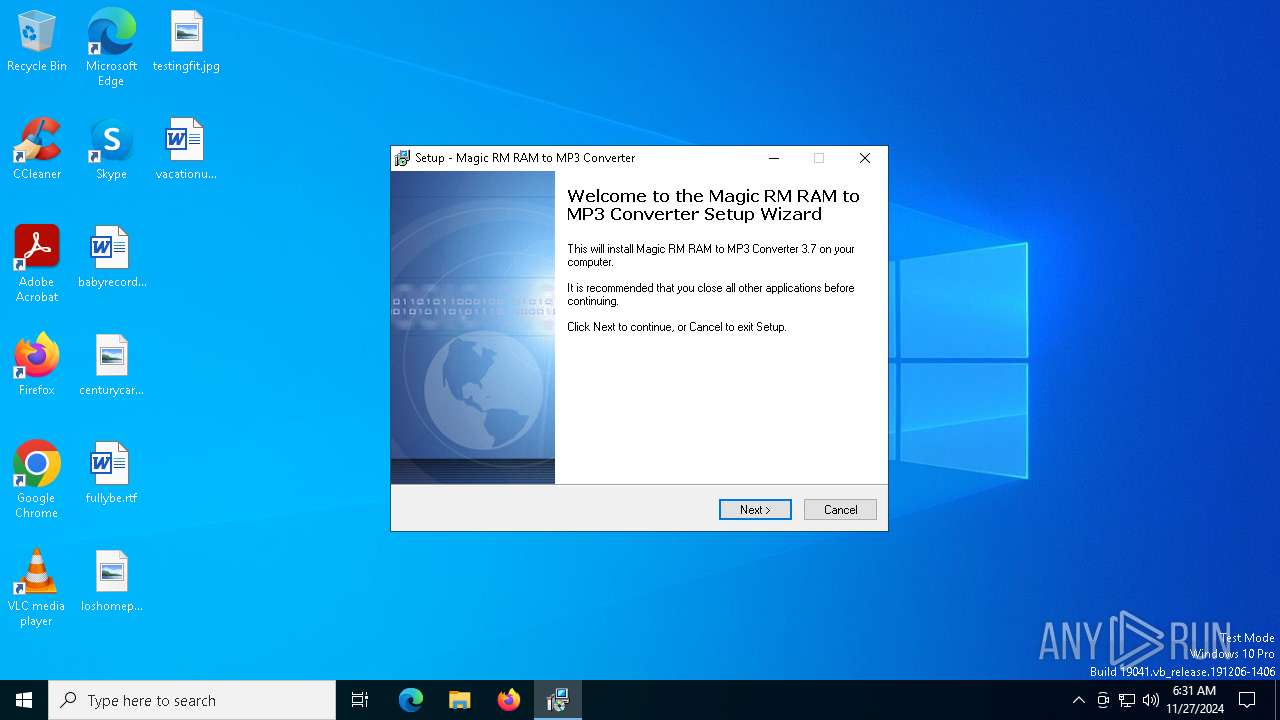
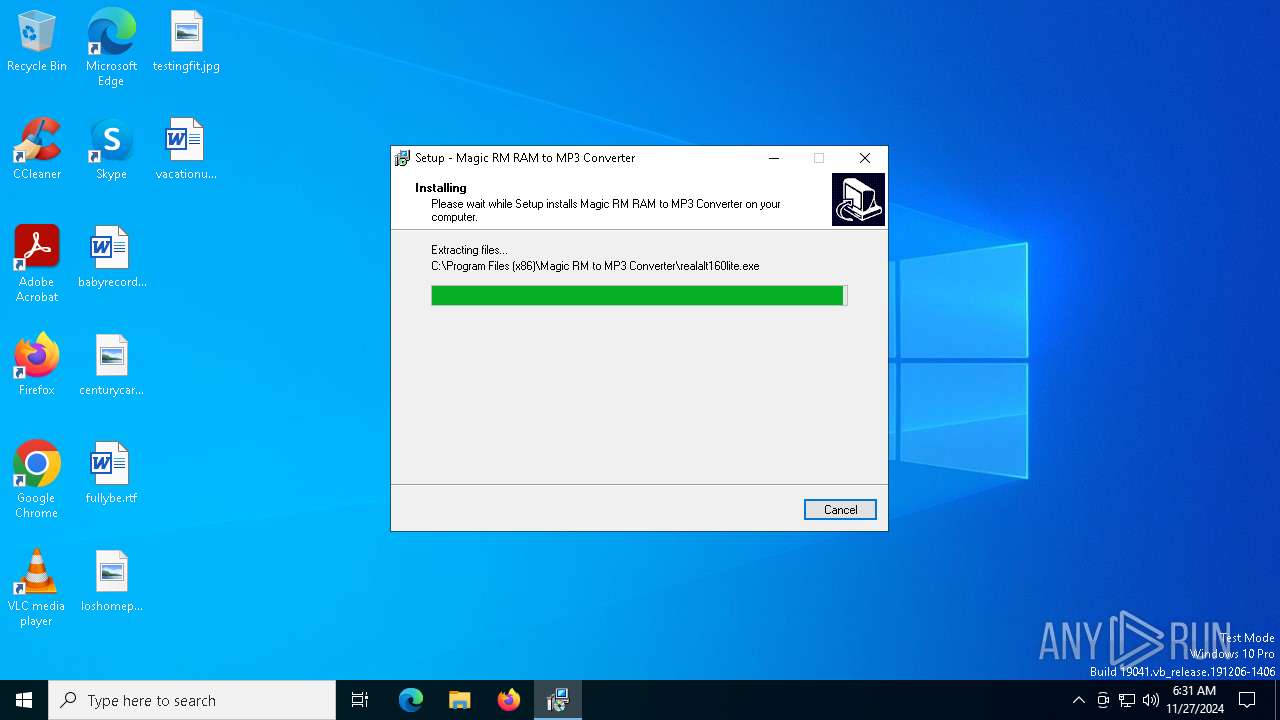
| FileDescription: | Magic RM RAM to MP3 Converter Setup |
| FileVersion: | 3.7 |
| LegalCopyright: |
Total processes
142
Monitored processes
13
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\AppData\Local\Temp\rmtomp3converter.exe" | C:\Users\admin\AppData\Local\Temp\rmtomp3converter.exe | explorer.exe | ||||||||||||
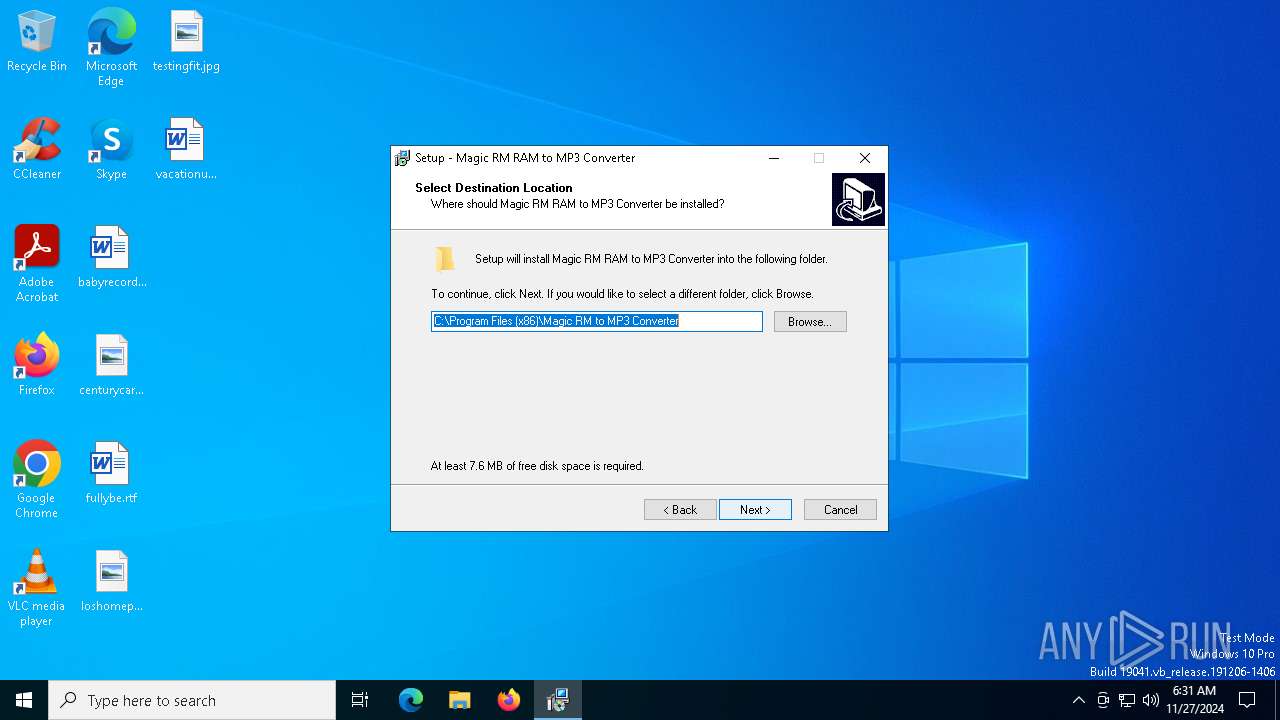
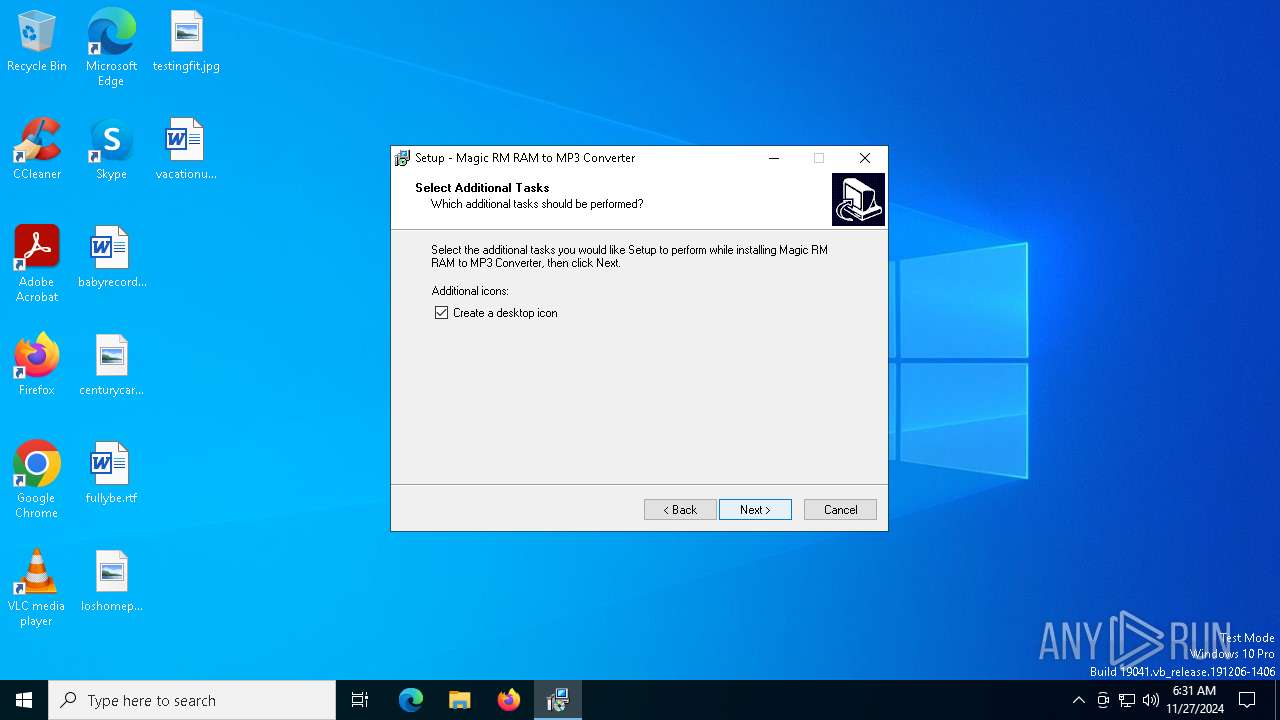
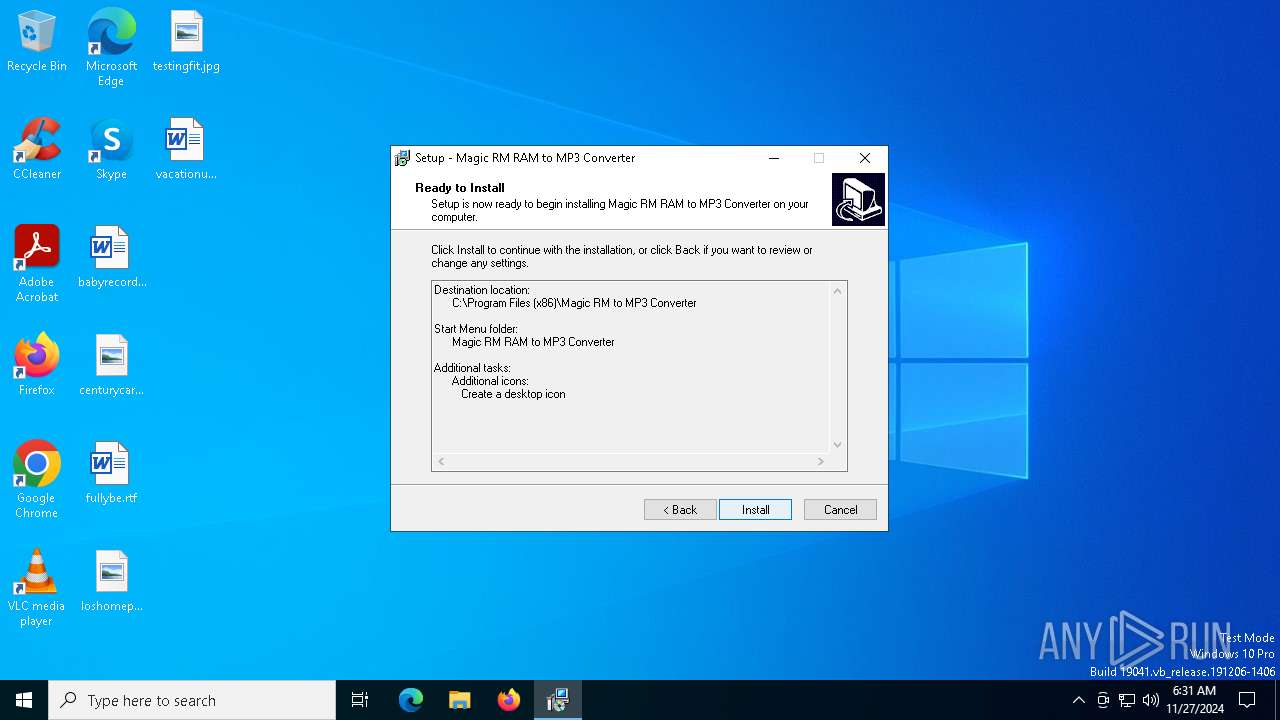
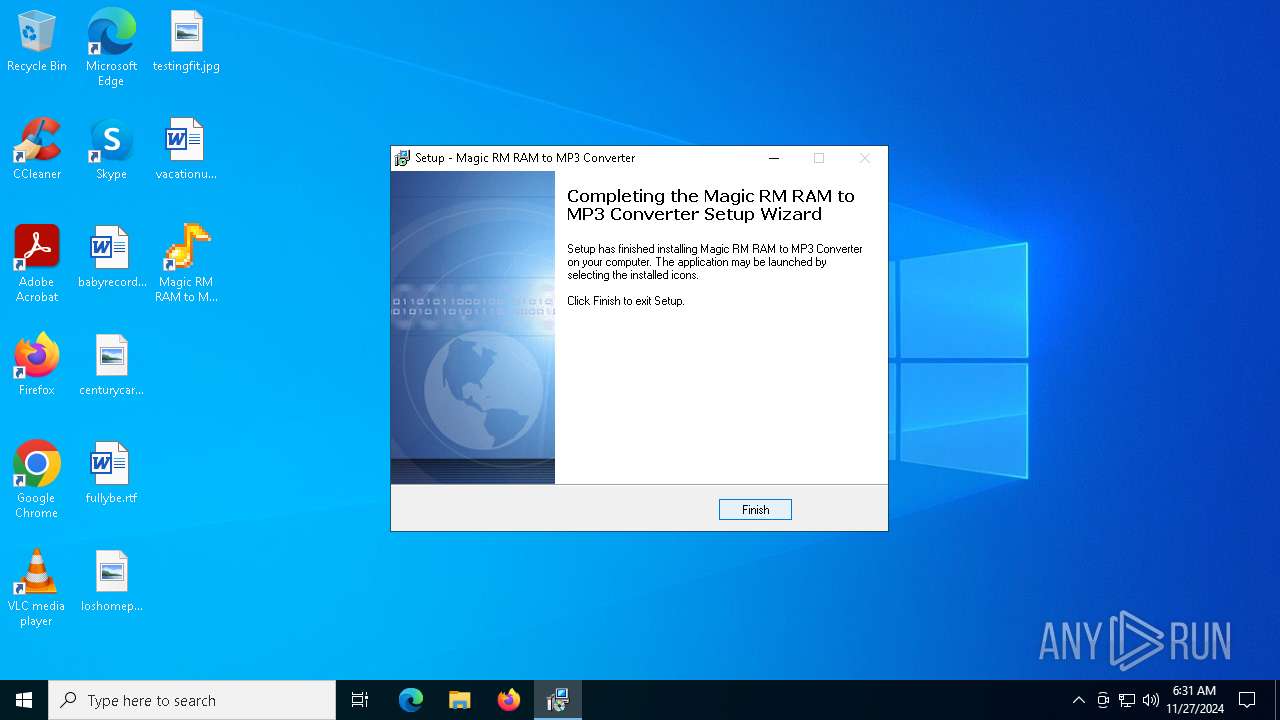
User: admin Company: Magic Video,Inc Integrity Level: HIGH Description: Magic RM RAM to MP3 Converter Setup Exit code: 0 Version: 3.7 Modules
| |||||||||||||||
| 4136 | "C:\Users\admin\AppData\Local\Temp\is-70QCP.tmp\is-R9H91.tmp" /SL4 $5020E "C:\Users\admin\AppData\Local\Temp\rmtomp3converter.exe" 6054022 52736 | C:\Users\admin\AppData\Local\Temp\is-70QCP.tmp\is-R9H91.tmp | rmtomp3converter.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.46.0.0 Modules
| |||||||||||||||
| 4976 | "C:\Users\admin\AppData\Local\Temp\rmtomp3converter.exe" | C:\Users\admin\AppData\Local\Temp\rmtomp3converter.exe | — | explorer.exe | |||||||||||
User: admin Company: Magic Video,Inc Integrity Level: MEDIUM Description: Magic RM RAM to MP3 Converter Setup Exit code: 3221226540 Version: 3.7 Modules
| |||||||||||||||
| 6016 | "C:\Program Files (x86)\Magic RM to MP3 Converter\all2mp3.exe" | C:\Program Files (x86)\Magic RM to MP3 Converter\all2mp3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 3.6.0.6 Modules
| |||||||||||||||
| 6872 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files (x86)\Magic RM to MP3 Converter\lame.ax" | C:\Windows\SysWOW64\regsvr32.exe | — | is-R9H91.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6896 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files (x86)\Magic RM to MP3 Converter\write.ax" | C:\Windows\SysWOW64\regsvr32.exe | — | is-R9H91.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6920 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files (x86)\Magic RM to MP3 Converter\wav.ax" | C:\Windows\SysWOW64\regsvr32.exe | — | is-R9H91.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6960 | "C:\WINDOWS\system32\cmd.exe" /C ""C:\Program Files (x86)\Magic RM to MP3 Converter\realalt.bat"" | C:\Windows\SysWOW64\cmd.exe | — | is-R9H91.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
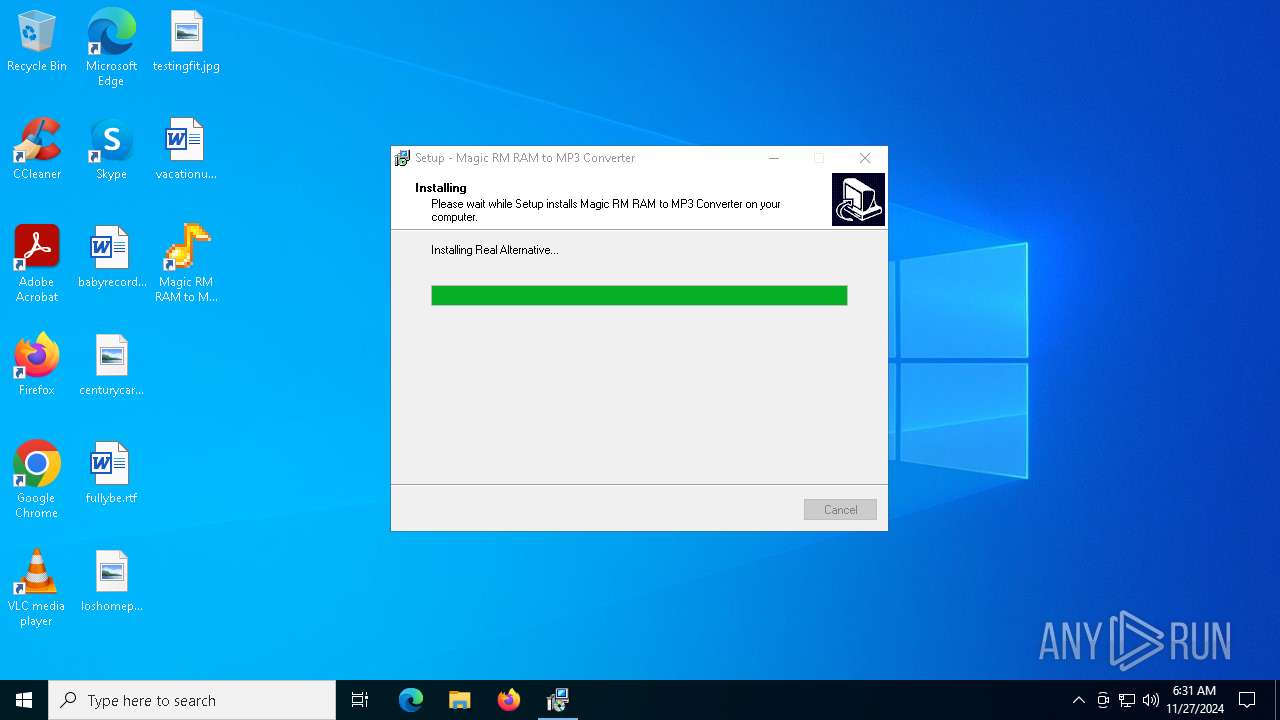
| 7036 | realalt160lite.exe /verysilent /norestart /LoadInf=".\realalt.ini" | C:\Program Files (x86)\Magic RM to MP3 Converter\realalt160lite.exe | cmd.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Real Alternative Exit code: 0 Version: 1.6.0.0 Modules
| |||||||||||||||
Total events
4 186
Read events
3 972
Write events
212
Delete events
2
Modification events
| (PID) Process: | (4136) is-R9H91.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\Real\Codecs\cook.dll |
Value: 1 | |||
| (PID) Process: | (6872) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{B8D27088-FF5F-4B7C-98DC-0E91A1696286}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6872) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{B8D27089-FF5F-4B7C-98DC-0E91A1696286}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6872) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{B8D2708A-FF5F-4B7C-98DC-0E91A1696286}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6872) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{FE69EDD1-F4CB-11D5-994A-000021D1FE2F}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6872) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{083863F1-70DE-11D0-BD40-00A0C911CE86}\Instance\{B8D27088-FF5F-4B7C-98DC-0E91A1696286} |
| Operation: | write | Name: | FriendlyName |
Value: LAME Audio Encoder | |||
| (PID) Process: | (6872) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{083863F1-70DE-11D0-BD40-00A0C911CE86}\Instance\{B8D27088-FF5F-4B7C-98DC-0E91A1696286} |
| Operation: | write | Name: | CLSID |
Value: {B8D27088-FF5F-4B7C-98DC-0E91A1696286} | |||
| (PID) Process: | (6872) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{083863F1-70DE-11D0-BD40-00A0C911CE86}\Instance\{B8D27088-FF5F-4B7C-98DC-0E91A1696286} |
| Operation: | write | Name: | FilterData |
Value: 0200000000001000030000000000000030706933000000000000000001000000000000000000000030747933000000008800000098000000317069330800000000000000020000000000000000000000307479330000000088000000A8000000317479330000000088000000B80000003270693300000000000000000000000000000000000000006175647300001000800000AA00389B710100000000001000800000AA00389B715000000000001000800000AA00389B712B806DE046DBCF11B4D100805F6CBBEA | |||
| (PID) Process: | (6896) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{36A5F770-FE4C-11CE-A8ED-00AA002FEAB5}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6896) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{083863F1-70DE-11D0-BD40-00A0C911CE86}\Instance\{36A5F770-FE4C-11CE-A8ED-00AA002FEAB5} |
| Operation: | write | Name: | FriendlyName |
Value: Dump | |||
Executable files
198
Suspicious files
18
Text files
18
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4136 | is-R9H91.tmp | C:\Program Files (x86)\Magic RM to MP3 Converter\is-D6H5V.tmp | executable | |
MD5:F771D46617A46D6640A58207F6403D9F | SHA256:CC6294E9A1B13293E7FEAE1D8F530E0BDFE9BDAF4ED002606C0D7C556CE87750 | |||
| 128 | rmtomp3converter.exe | C:\Users\admin\AppData\Local\Temp\is-70QCP.tmp\is-R9H91.tmp | executable | |
MD5:3DAFB498BB15D5260CB2C12B391A0D48 | SHA256:C5D5F5F814C5BC4989D691442051E5E78CF1971EB9B773A7A26B438E58A73D7A | |||
| 4136 | is-R9H91.tmp | C:\Users\admin\AppData\Local\Temp\is-D176B.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 4136 | is-R9H91.tmp | C:\Program Files (x86)\Magic RM to MP3 Converter\is-08GOR.tmp | image | |
MD5:8B0B8A02AB3EC936FBBC10DE2AE5D694 | SHA256:E320B14714F42BED4248F1BF1C6CA767E2291586BC12C1B17234F465883D2B11 | |||
| 4136 | is-R9H91.tmp | C:\Program Files (x86)\Magic RM to MP3 Converter\unins000.exe | executable | |
MD5:F771D46617A46D6640A58207F6403D9F | SHA256:CC6294E9A1B13293E7FEAE1D8F530E0BDFE9BDAF4ED002606C0D7C556CE87750 | |||
| 4136 | is-R9H91.tmp | C:\Program Files (x86)\Magic RM to MP3 Converter\is-5VG89.tmp | executable | |
MD5:68557856C6851353C1578B7CB5B4E71E | SHA256:E62EEA6B342443B075FE1CEDEBF2EBA82448524197ABCE17263D2D00CC0AED61 | |||
| 4136 | is-R9H91.tmp | C:\Program Files (x86)\Magic RM to MP3 Converter\is-EKMMB.tmp | html | |
MD5:78ED995520610DB2F4262910558ECCDE | SHA256:9FBED2E589CFA6DB2A3BF78C9650A2E1EEB0E394745B8E41C919909D1F0516A5 | |||
| 4136 | is-R9H91.tmp | C:\Program Files (x86)\Magic RM to MP3 Converter\Help.htm | html | |
MD5:78ED995520610DB2F4262910558ECCDE | SHA256:9FBED2E589CFA6DB2A3BF78C9650A2E1EEB0E394745B8E41C919909D1F0516A5 | |||
| 4136 | is-R9H91.tmp | C:\Program Files (x86)\Magic RM to MP3 Converter\ArmAccess.dll | executable | |
MD5:68557856C6851353C1578B7CB5B4E71E | SHA256:E62EEA6B342443B075FE1CEDEBF2EBA82448524197ABCE17263D2D00CC0AED61 | |||
| 4136 | is-R9H91.tmp | C:\Program Files (x86)\Magic RM to MP3 Converter\is-MH45A.tmp | executable | |
MD5:C8F3668DF2C490FBC8A4B27AC2F6A0FC | SHA256:FE6196F21FE933A7DB42B3C598ABD505B9D88E523FC14D9E4564BD2B1A9D6D7A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
624 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
624 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6216 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
640 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3976 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.16.204.144:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
all2mp3.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
all2mp3.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |