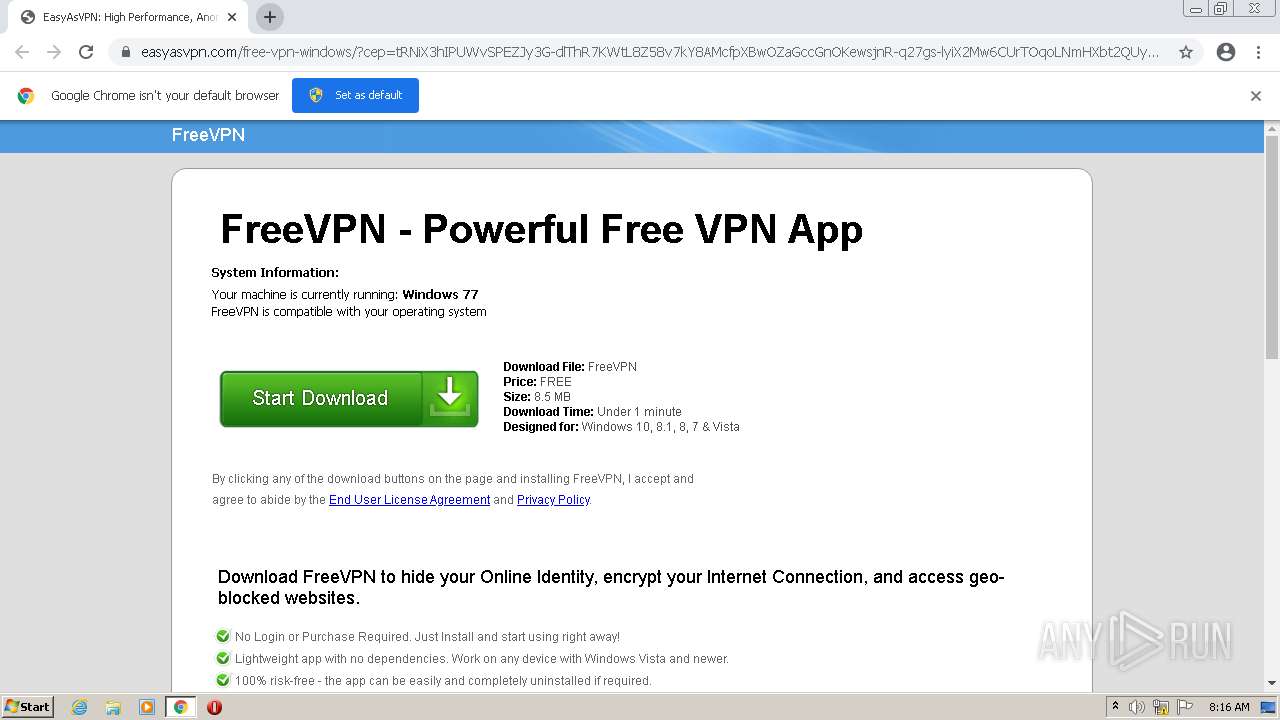
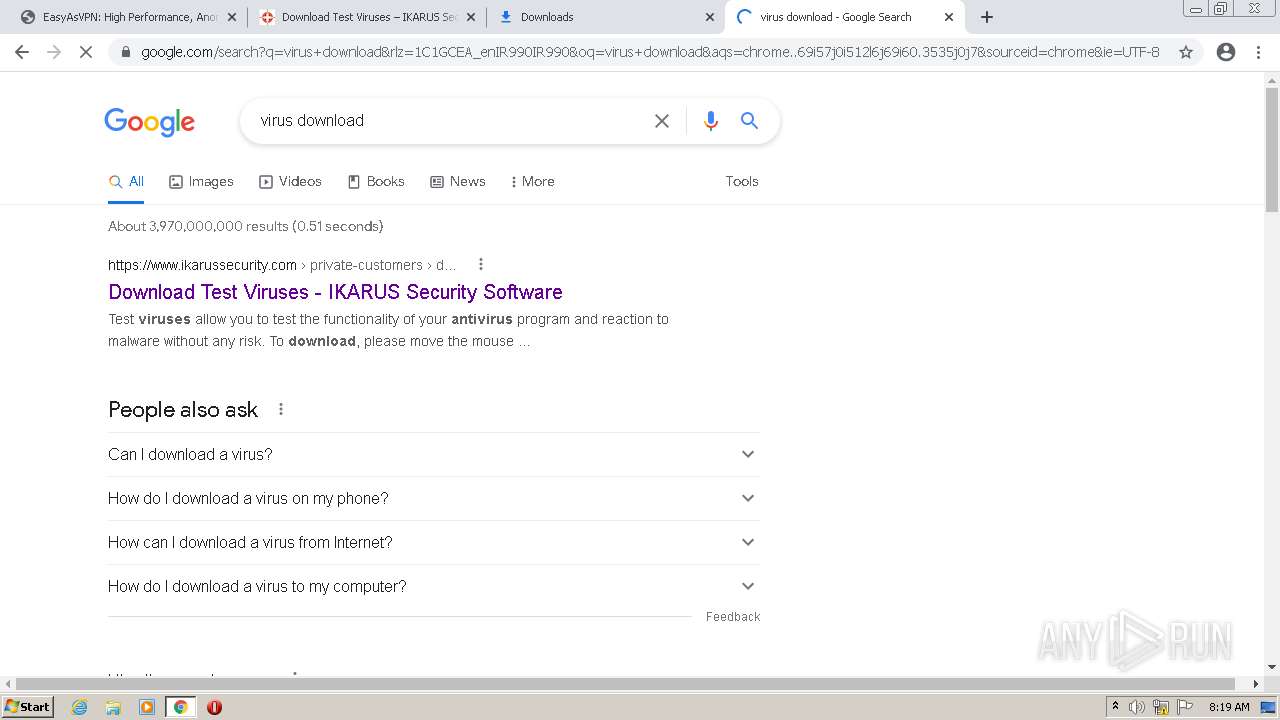
| URL: | https://easyasvpn.com/free-vpn-windows/?cep=tRNiX3hIPUWvSPEZJy3G-dlThR7KWtL8Z58v7kY8AMcfpXBwOZaGccGnOKewsjnR-q27gs-lyiX2Mw6CUrTOqoLNmHXbt2QUycGWP1lq3FUL1aJrDP1lW6s454phavqn9rW3lmj3nmaDInK_Ux5IdVuds-0dBu2OfT5YdjGJyXaZRQKcwti7ittSNozp7QzVjw1CvCRMo1tZdU0IZgVAVXSpC6omWvG_KQV6Sme4BlDJEiI_zUHXJTppik1XbMH0sD-YcSPQJb0ySXMzWSw6RmsgT-RP8QBZEiyZdPY85MWT4K0mIsF7WM2vj6776PV3TybpX0BRaEEBoAtXI4VxkoDJdwG-CmFmX9NKoPvDyrh3JQdReRnW874JGmmUbdicQbF3bcyba-Lh1Kqyr-8x7ZDW4oI9IU9yqp8rf6P-UTRKkfT-e3hduog6vTDB-HX-XjFtUfM-pIT7DKqXyb4GRFsFpOfyaEGiMwY-oTrdD6PBpoxMexnO5We7dIhIidj6eP_1-zx4BqIKEs7VvaSD30nFY1pNsYYAWRWLdtEOwhDBQF7YN4GGIhXvi6m7wgWkl18d3K8huEWofOqdCrEu0cqF-sX9DP1JVtuw9ptgwIq38JQIbr6P1vGJN8hW7N9msFB3Du1HmWq2oV-trXvE4TL-NPKt6SH98pdwzCuw2xC9C4y9ncKlRygrkgAs1YlBInoLsC4SW3viX2CcCPwJr31uH_fCT9vkbIA5KgVF57sfDIU6WZdhfC16YvAhR2skrHJXjAbojv02Vx1ir6dzsQ&lptoken=1605432109e196eb0875&zoneid=4732996&bannerid=10898377&browser=chrome&os=windows&device=desktop®ion=c&isp=asia+pacific+network+information+centre&useragent=Mozilla%2F5.0+%28Windows+NT+10.0%3B+Win64%3B+x64%29+AppleWebKit%2F537.36+%28KHTML%2C+like+Gecko%29+Chrome%2F97.0.4692.71+Safari%2F537.36&language=en&connectiontype=broadband&cost=0.000052&visitor_id=509751750727856290 |
| Full analysis: | https://app.any.run/tasks/a723df03-96c6-4dbb-a9d1-7f32331cbe26 |
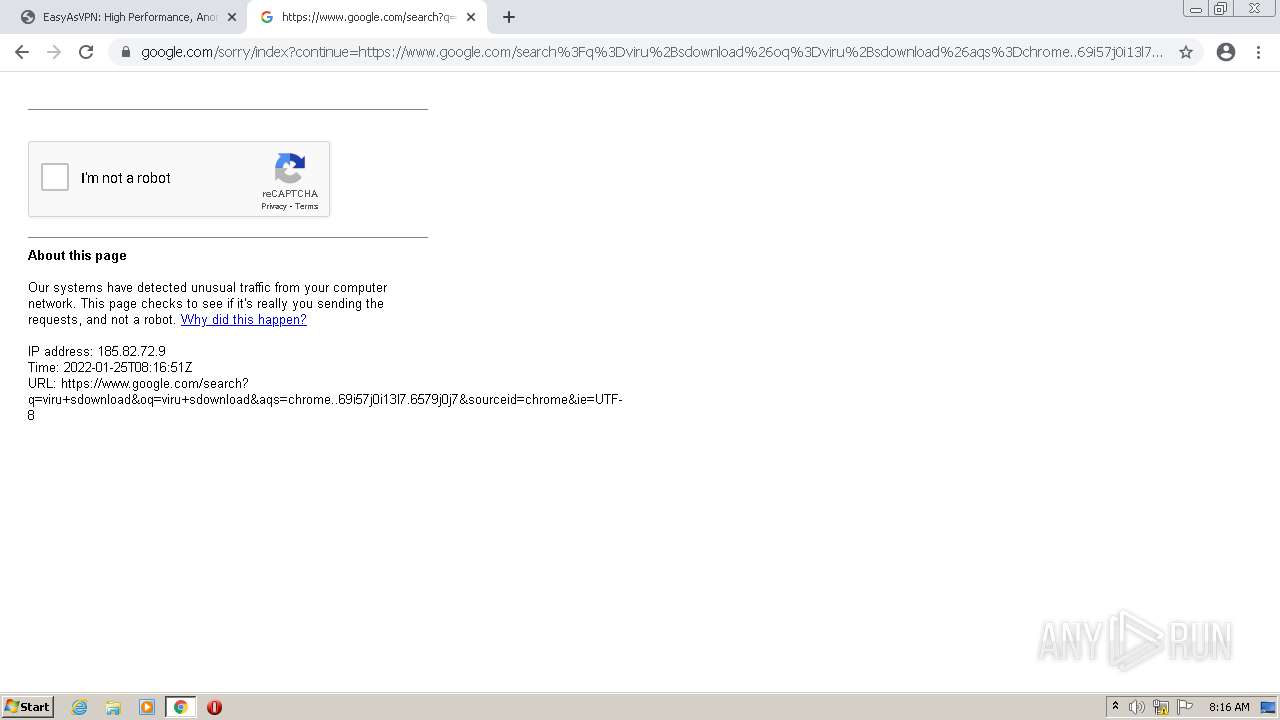
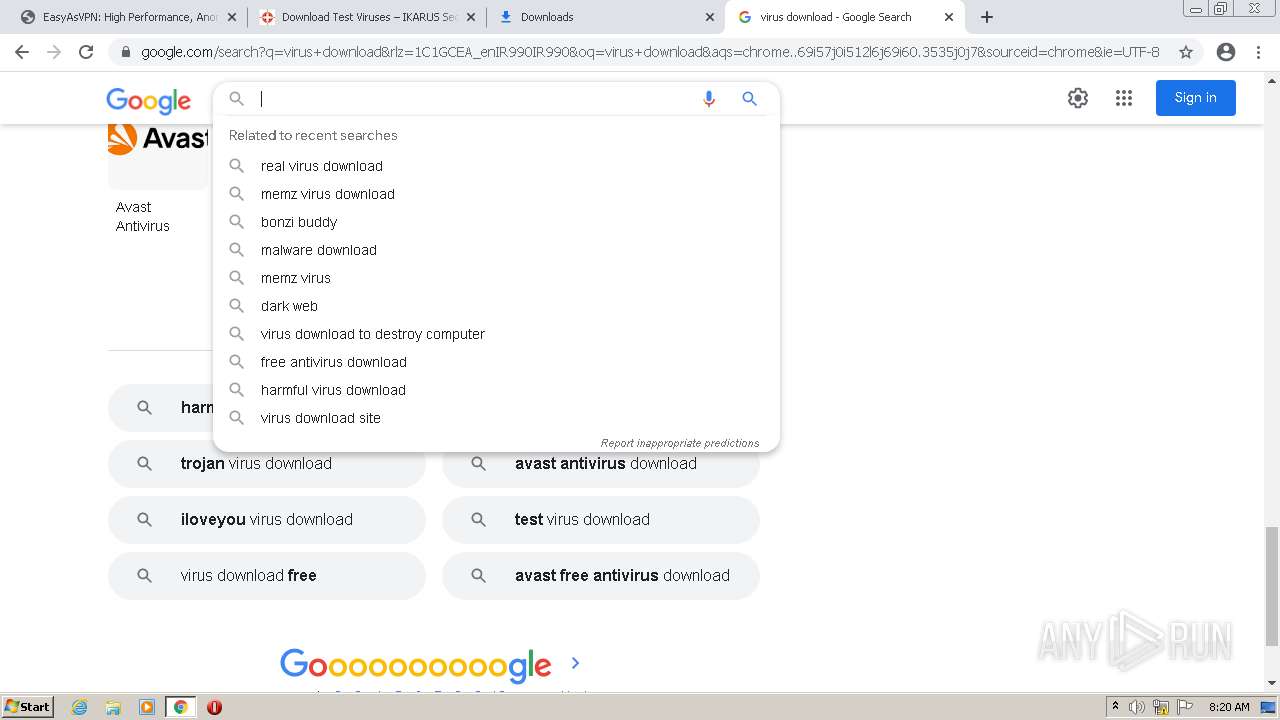
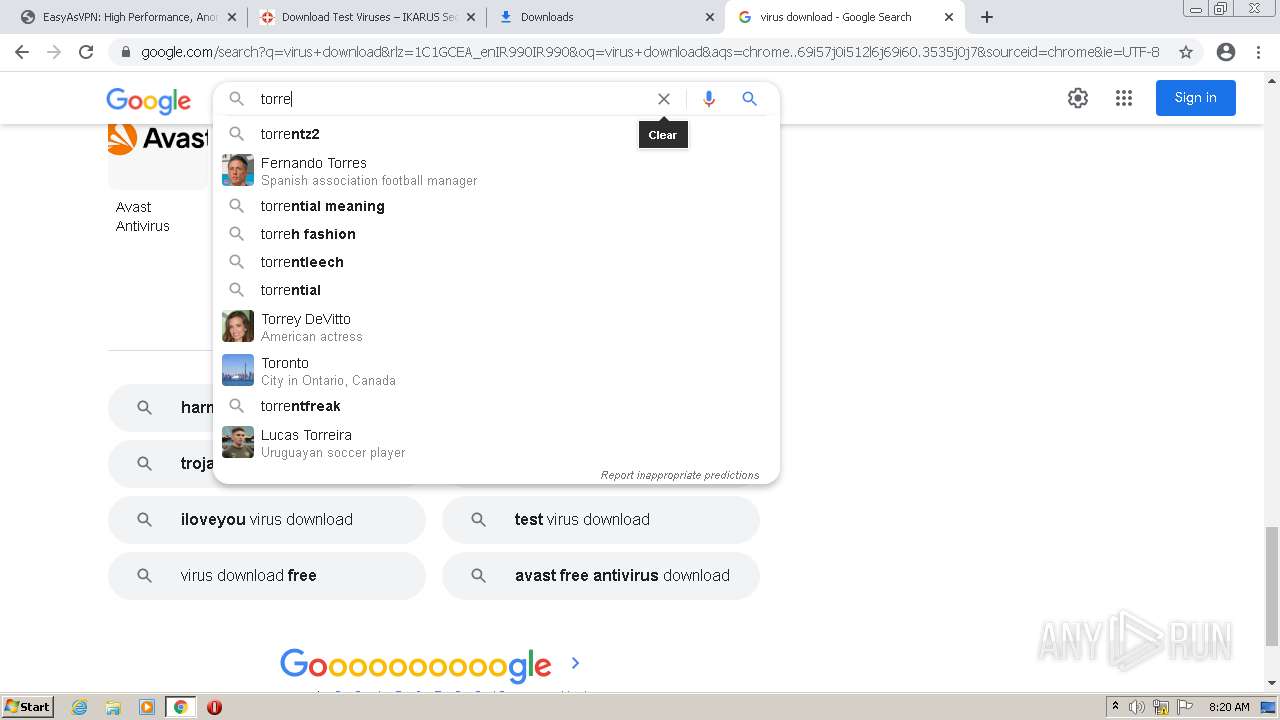
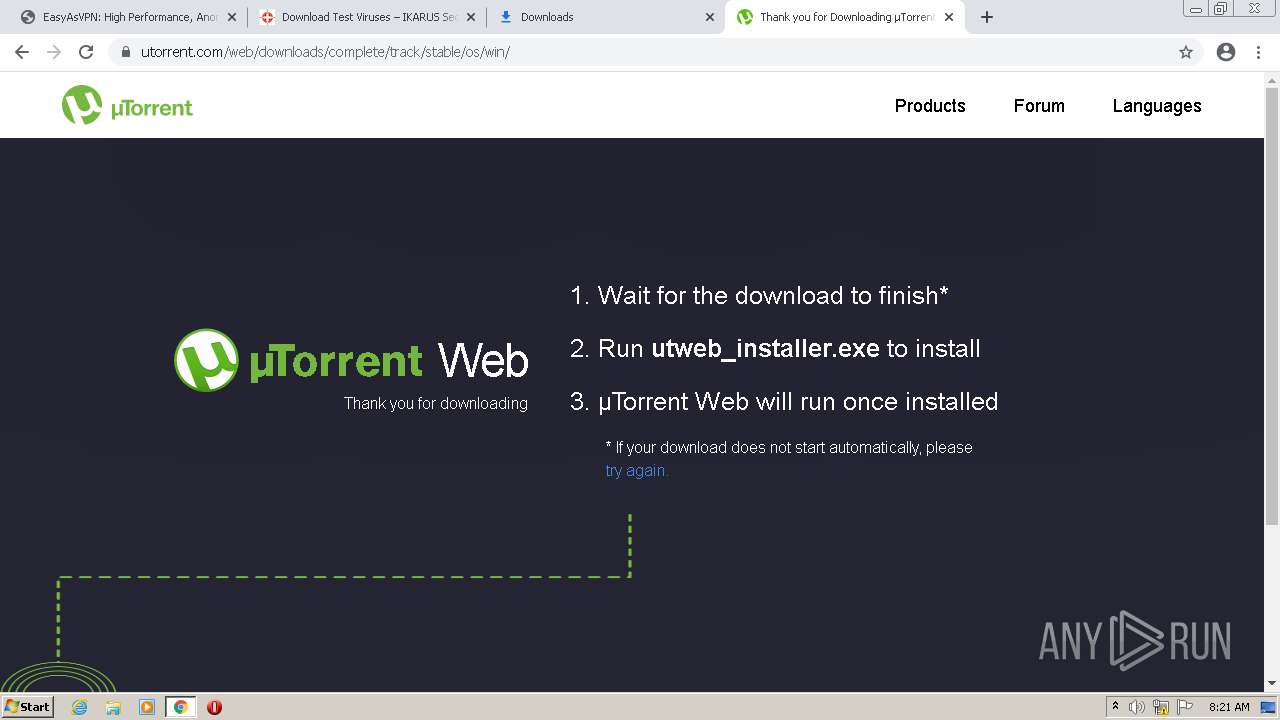
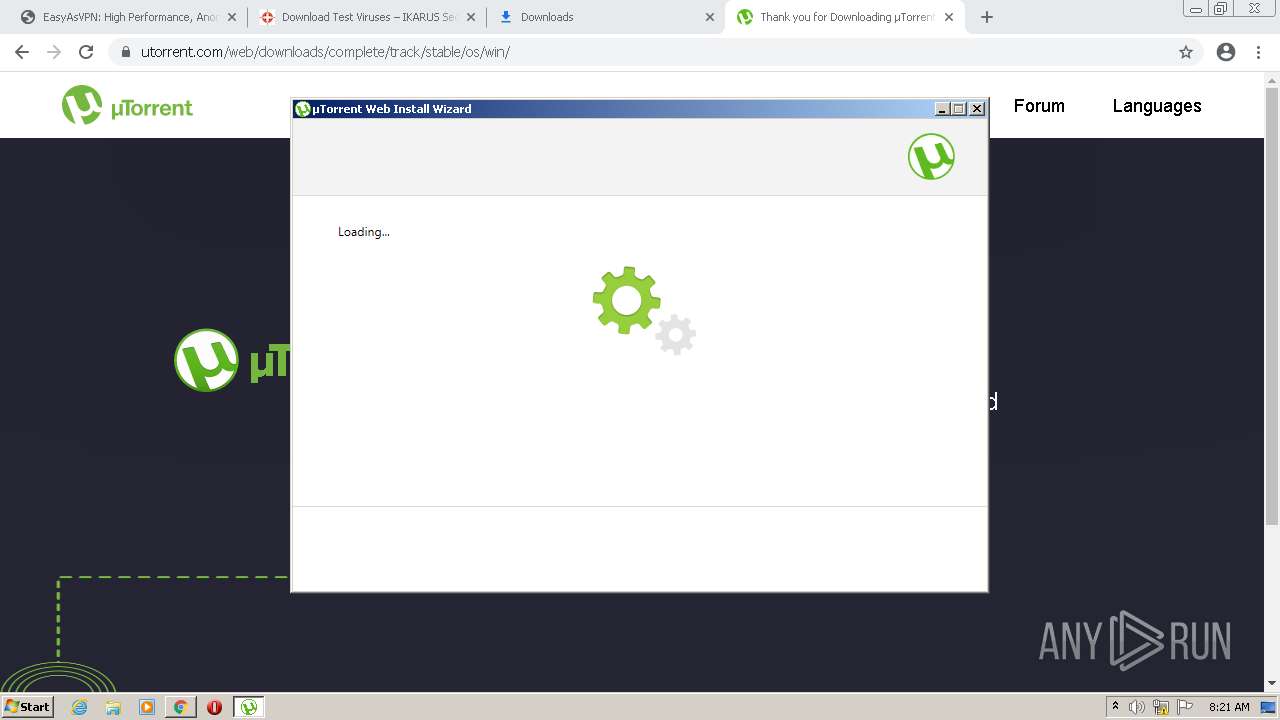
| Verdict: | Malicious activity |
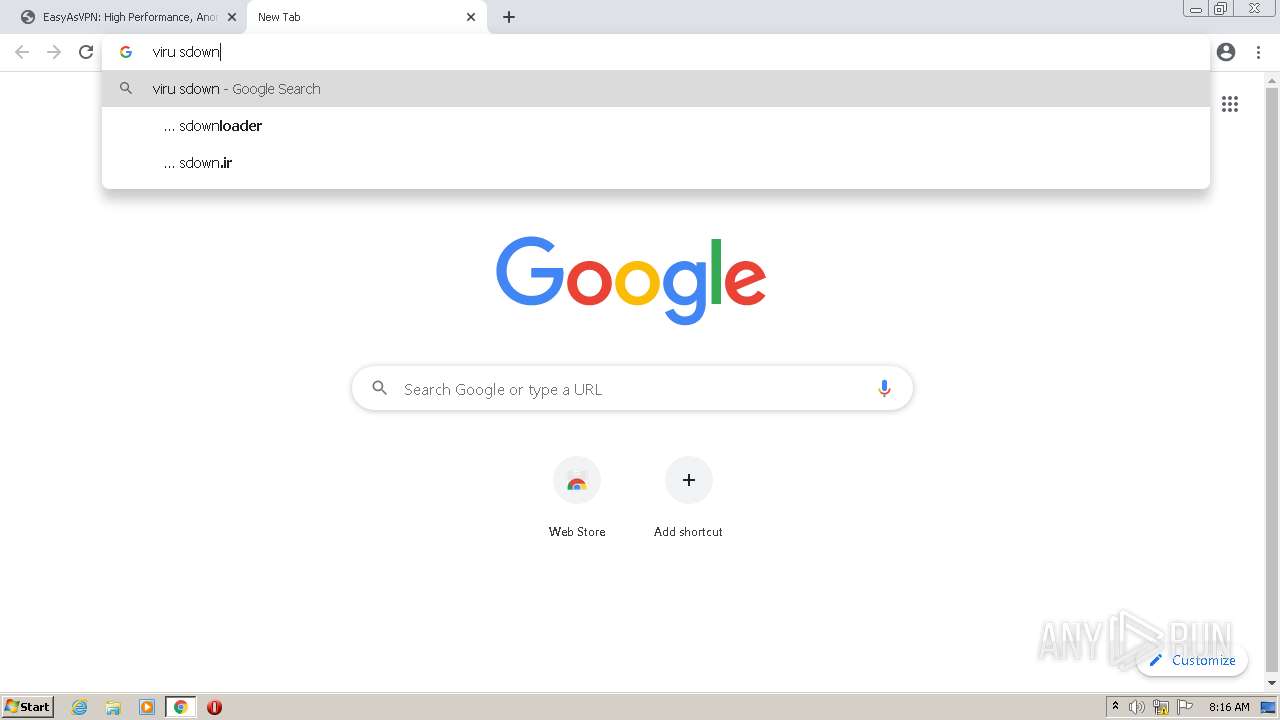
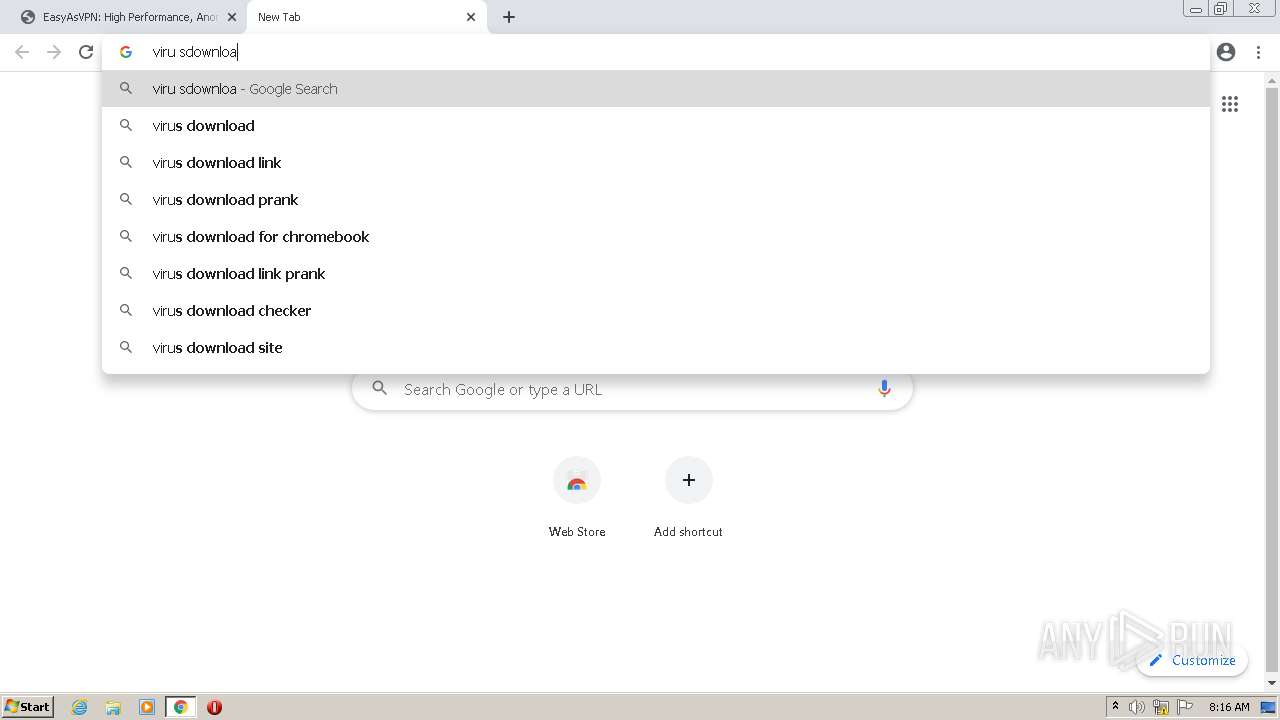
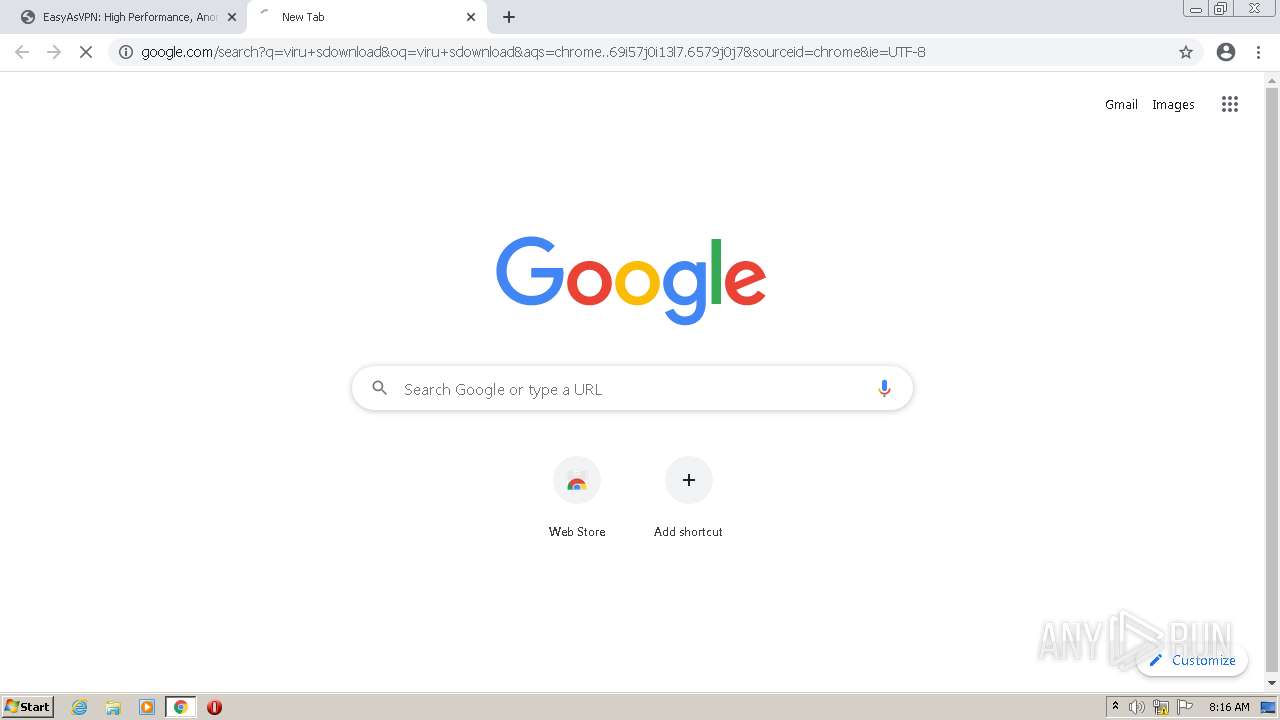
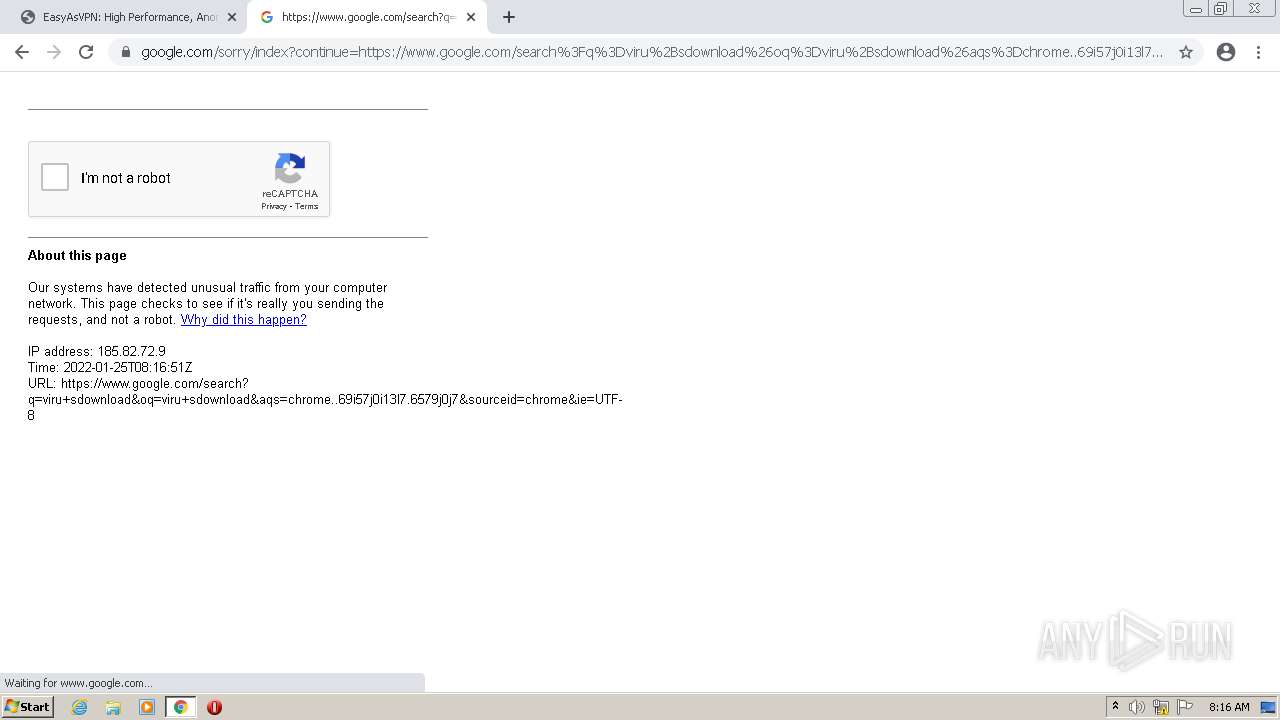
| Analysis date: | January 25, 2022, 08:16:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E9D0F2BC802E27121E08070229609342 |
| SHA1: | C99FDCF2A46406AF05B0032864BC710DF889C0F7 |
| SHA256: | 9BBC28543054268282074BB4284F6108C5A48FDFC31CC208924D869142C494EE |
| SSDEEP: | 24:2D6m8fWlYsalvle7m1JjtiLBJiW0cUu8OCEF5lL1W6iiBNOCV5SU:iKDdcm1/iLbiW0cUeblL06iiTOGx |
MALICIOUS
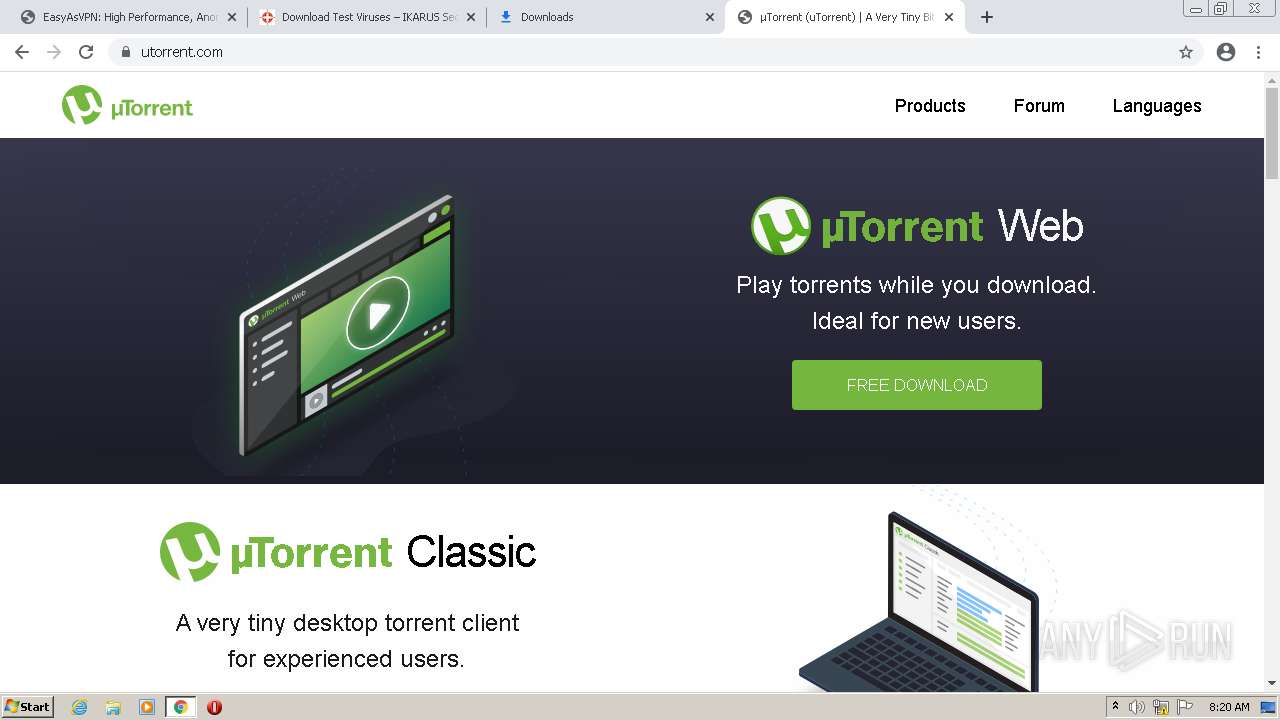
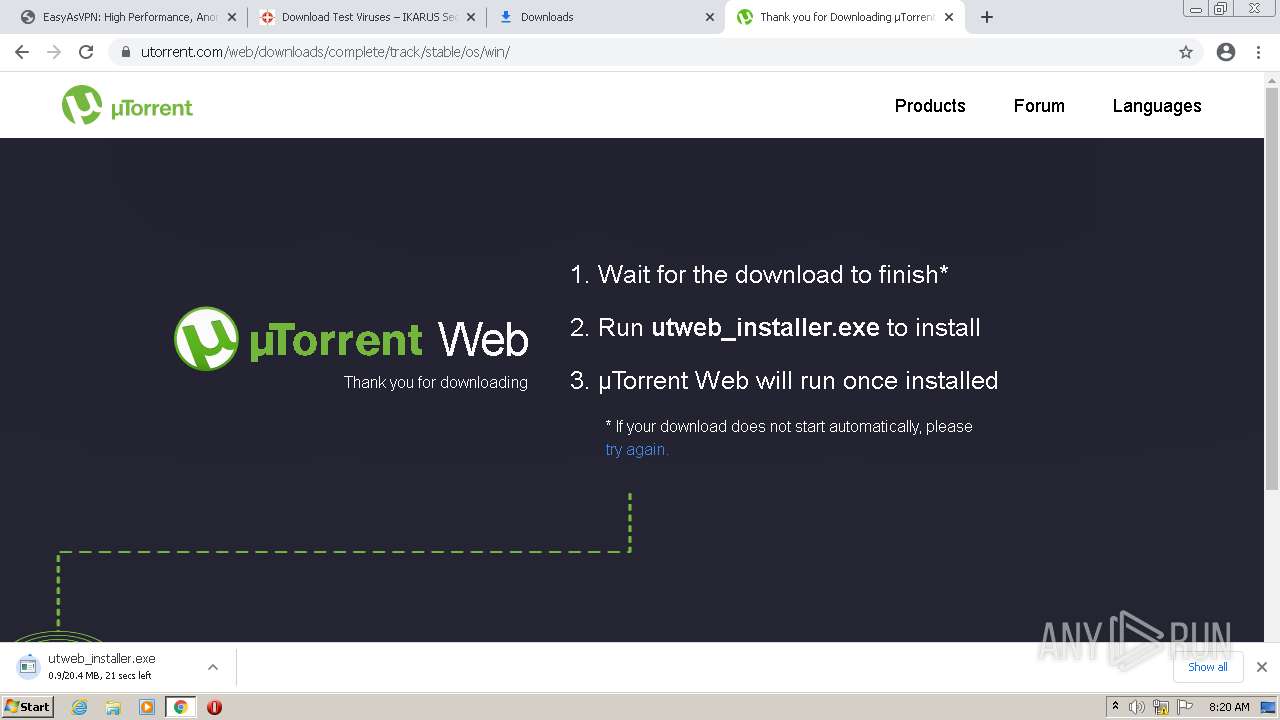
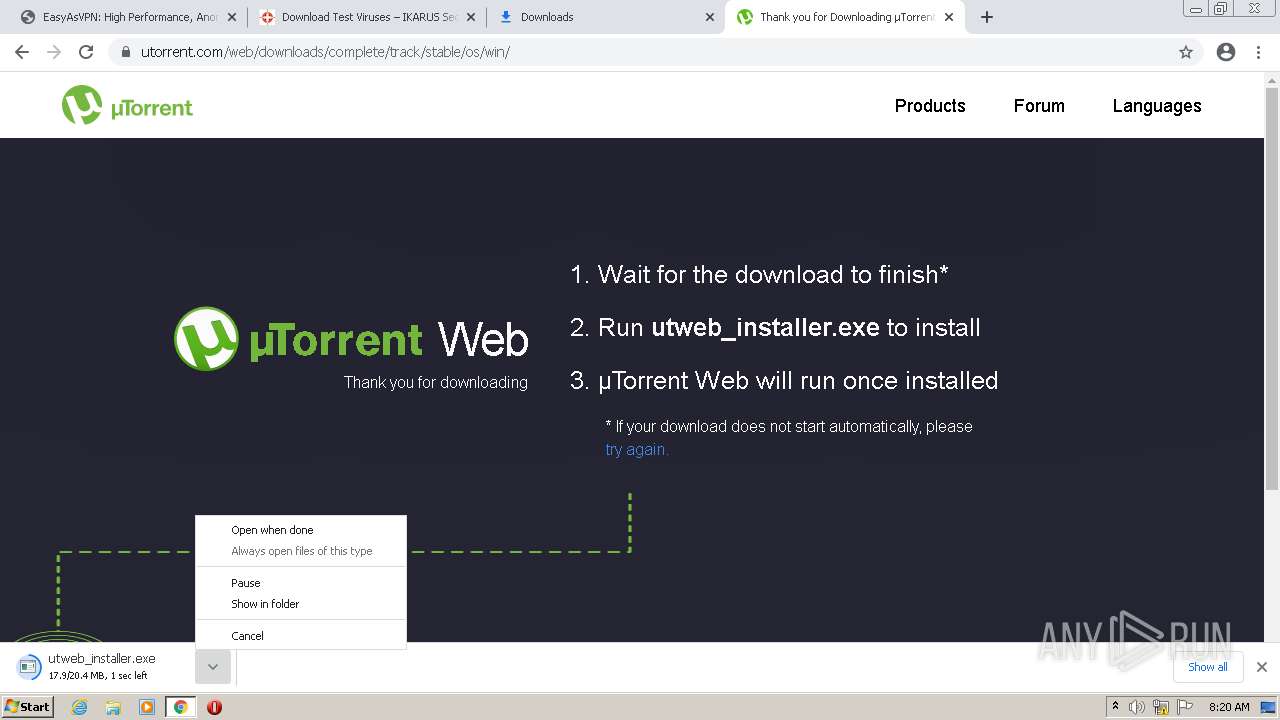
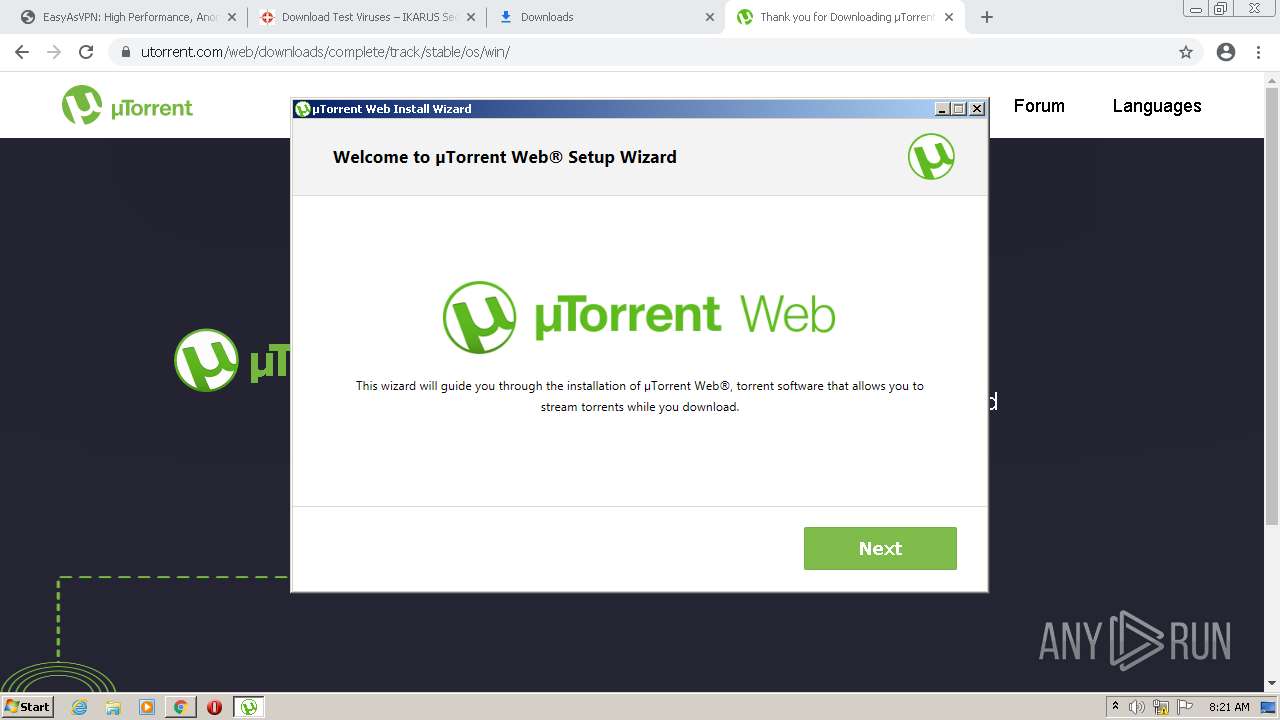
Drops executable file immediately after starts
- utweb_installer.exe (PID: 2444)
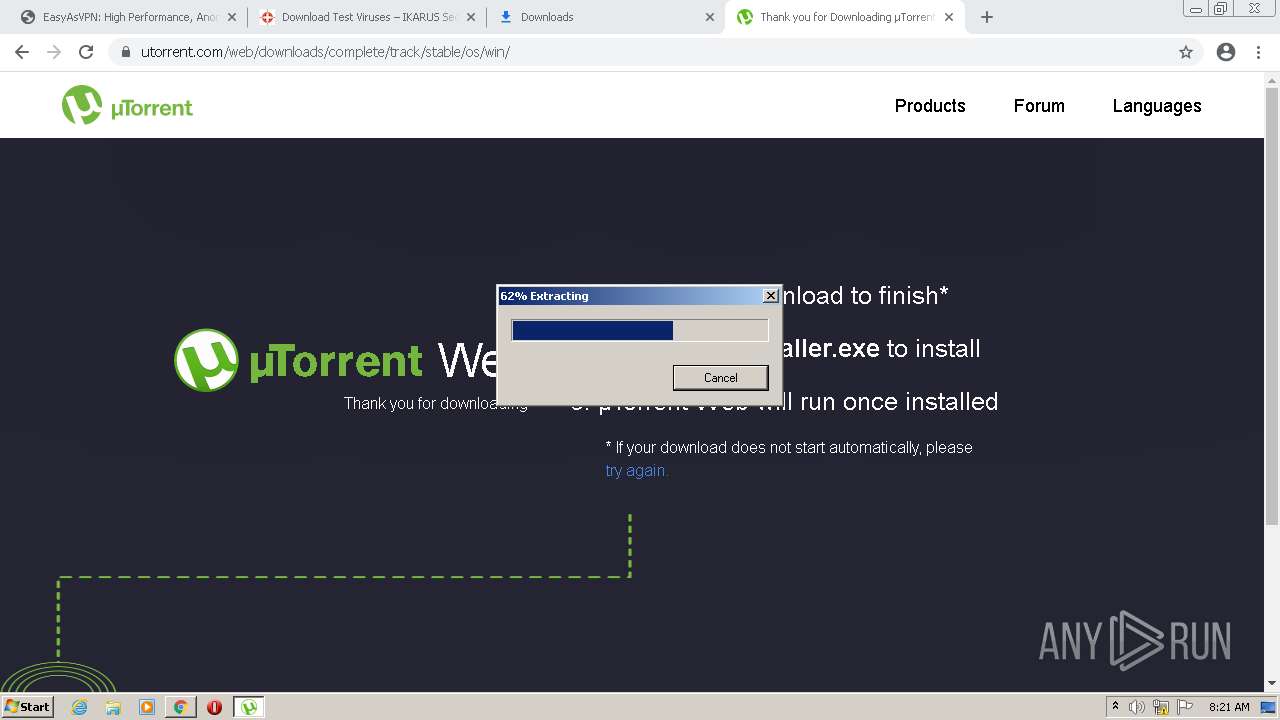
Application was dropped or rewritten from another process
- utweb_installer.exe (PID: 1536)
- utweb_installer.exe (PID: 2444)
- Carrier.exe (PID: 3392)
- GenericSetup.exe (PID: 2284)
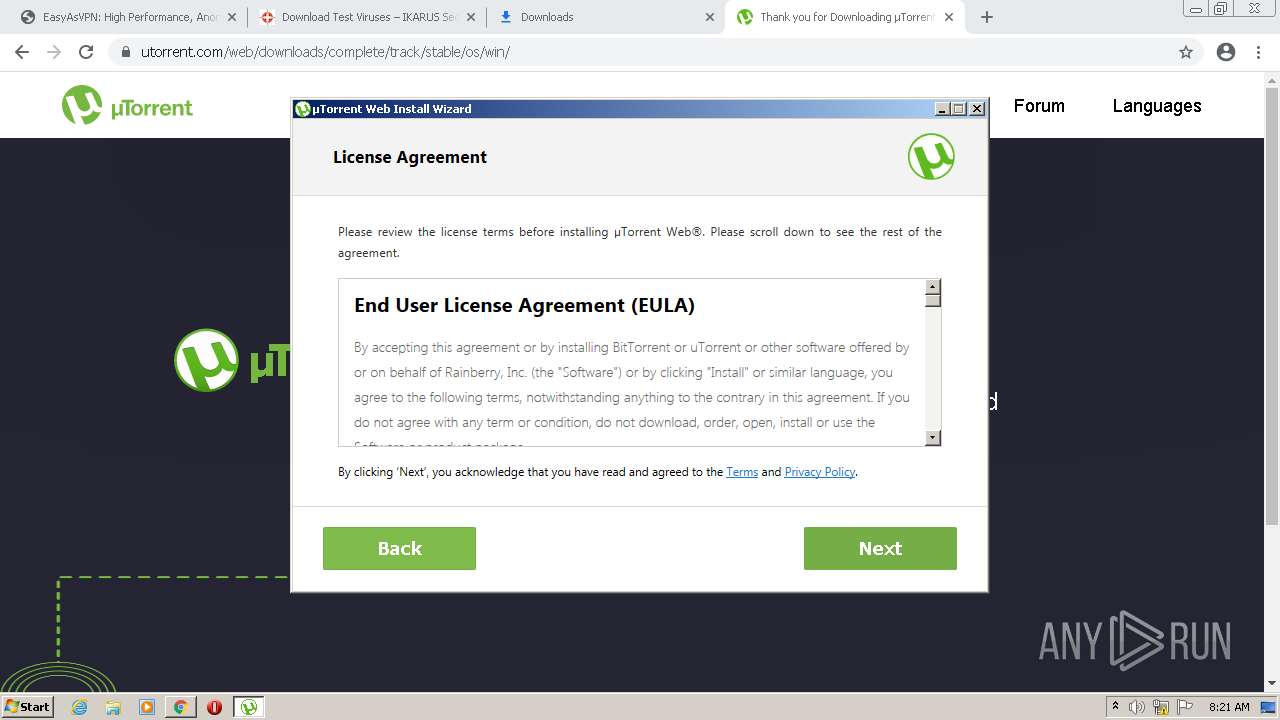
Loads dropped or rewritten executable
- GenericSetup.exe (PID: 2284)
Changes settings of System certificates
- GenericSetup.exe (PID: 2284)
Actions looks like stealing of personal data
- GenericSetup.exe (PID: 2284)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 1236)
- WinRAR.exe (PID: 1188)
- WinRAR.exe (PID: 3860)
- GenericSetup.exe (PID: 2284)
Checks supported languages
- WinRAR.exe (PID: 1236)
- WinRAR.exe (PID: 1188)
- WinRAR.exe (PID: 3860)
- utweb_installer.exe (PID: 2444)
- GenericSetup.exe (PID: 2284)
Executes application which crashes
- WinRAR.exe (PID: 1236)
Executable content was dropped or overwritten
- chrome.exe (PID: 3536)
- utweb_installer.exe (PID: 2444)
- GenericSetup.exe (PID: 2284)
Drops a file with a compile date too recent
- chrome.exe (PID: 3536)
- utweb_installer.exe (PID: 2444)
Drops a file that was compiled in debug mode
- utweb_installer.exe (PID: 2444)
- GenericSetup.exe (PID: 2284)
Reads the Windows organization settings
- GenericSetup.exe (PID: 2284)
Reads Environment values
- GenericSetup.exe (PID: 2284)
Reads Windows owner or organization settings
- GenericSetup.exe (PID: 2284)
Adds / modifies Windows certificates
- GenericSetup.exe (PID: 2284)
Searches for installed software
- GenericSetup.exe (PID: 2284)
INFO
Reads the computer name
- chrome.exe (PID: 3536)
- chrome.exe (PID: 2040)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 3816)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 3040)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 2392)
- chrome.exe (PID: 300)
- chrome.exe (PID: 2076)
Checks supported languages
- chrome.exe (PID: 2040)
- chrome.exe (PID: 2952)
- chrome.exe (PID: 3900)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 664)
- chrome.exe (PID: 3536)
- chrome.exe (PID: 3816)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 3992)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 2008)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 3040)
- ntvdm.exe (PID: 2868)
- ntvdm.exe (PID: 580)
- ntvdm.exe (PID: 2764)
- chrome.exe (PID: 2308)
- ntvdm.exe (PID: 2492)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 3944)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 2392)
- chrome.exe (PID: 1144)
- chrome.exe (PID: 1856)
- ntvdm.exe (PID: 2520)
- ntvdm.exe (PID: 1656)
- ntvdm.exe (PID: 1020)
- ntvdm.exe (PID: 2180)
- ntvdm.exe (PID: 2520)
- ntvdm.exe (PID: 3316)
- ntvdm.exe (PID: 3156)
- ntvdm.exe (PID: 3496)
- chrome.exe (PID: 2536)
- ntvdm.exe (PID: 3044)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2740)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 120)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 2088)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 148)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 2780)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 2952)
- chrome.exe (PID: 344)
- chrome.exe (PID: 2780)
- chrome.exe (PID: 1392)
- chrome.exe (PID: 300)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 3028)
Reads the hosts file
- chrome.exe (PID: 3536)
- chrome.exe (PID: 3816)
Reads settings of System Certificates
- chrome.exe (PID: 3816)
- chrome.exe (PID: 3536)
- GenericSetup.exe (PID: 2284)
Application launched itself
- chrome.exe (PID: 3536)
Reads the date of Windows installation
- chrome.exe (PID: 3012)
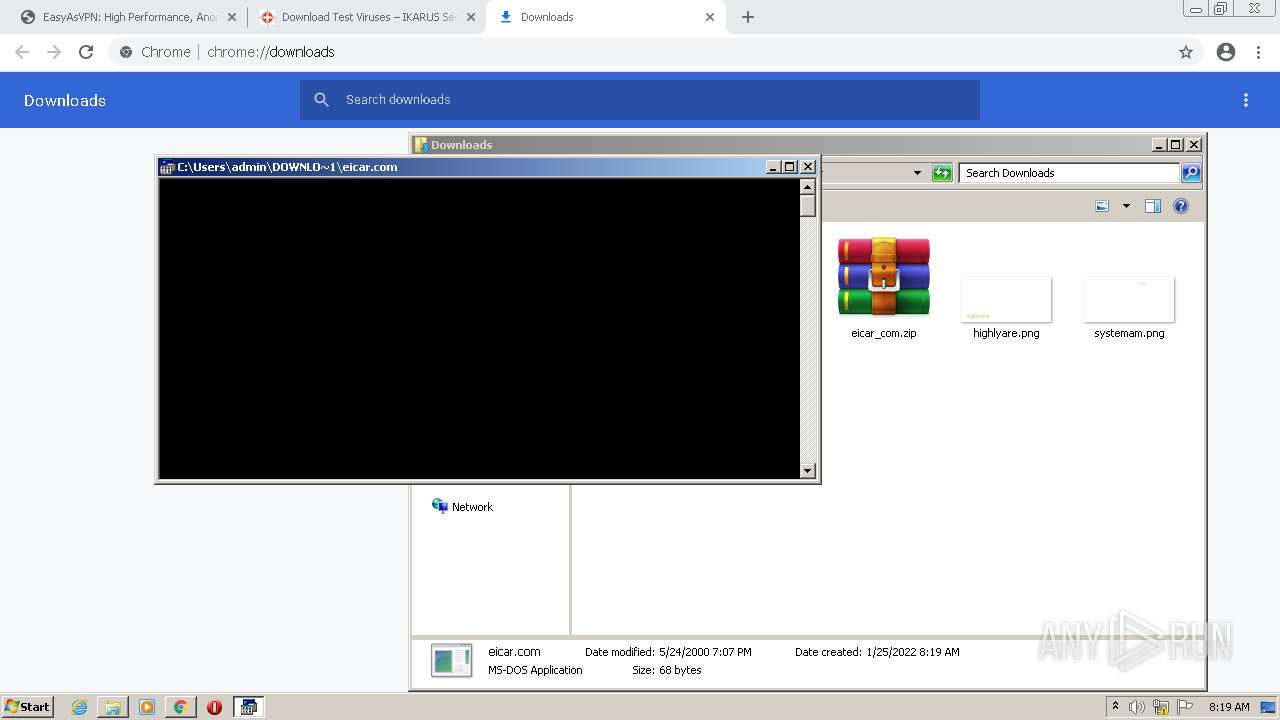
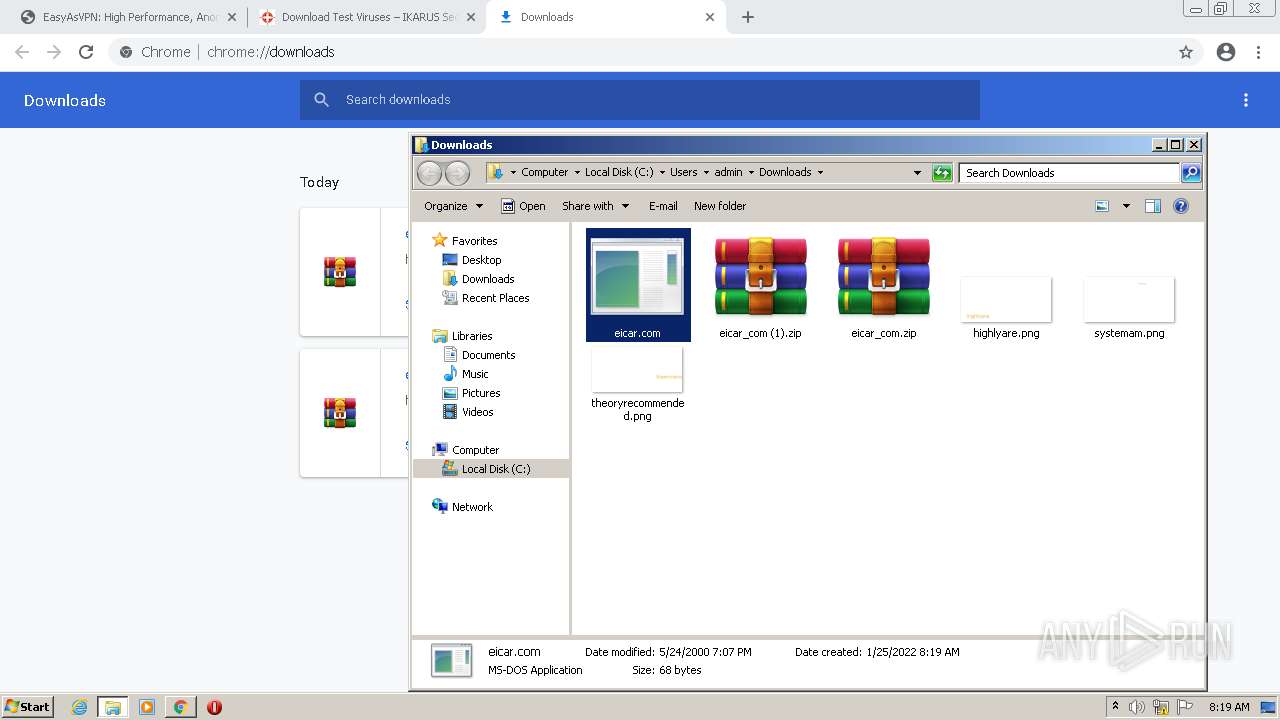
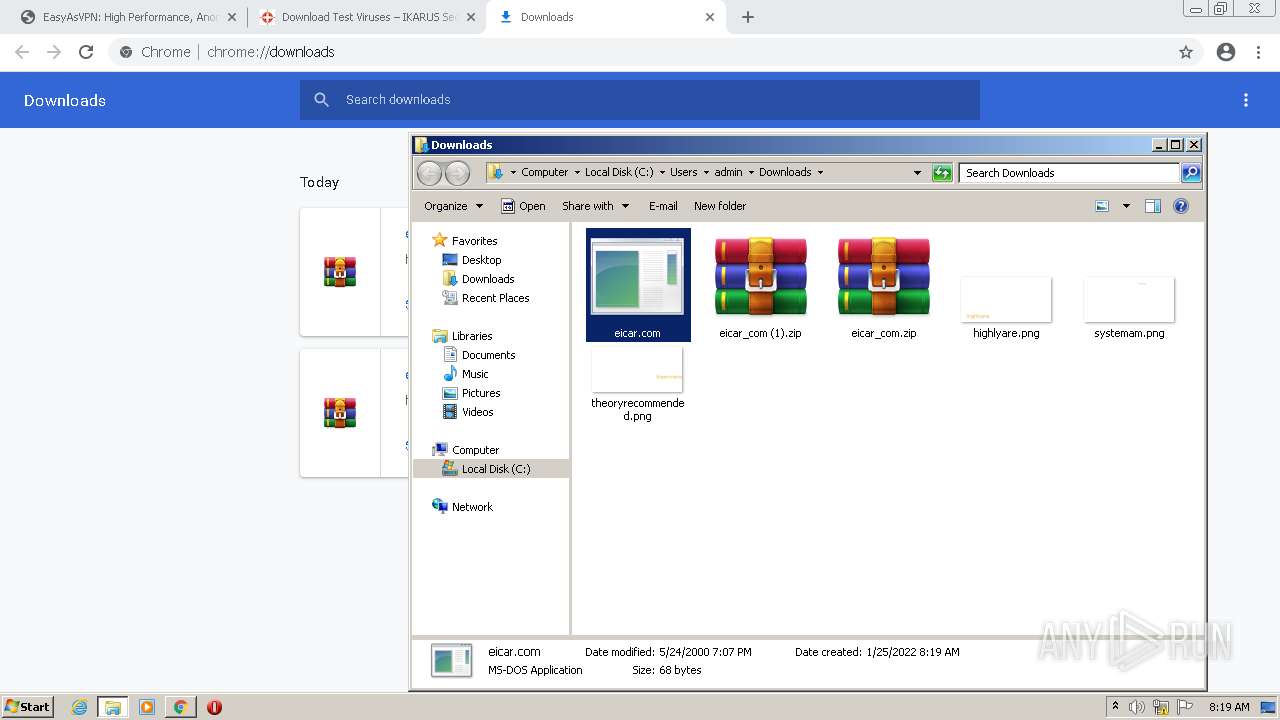
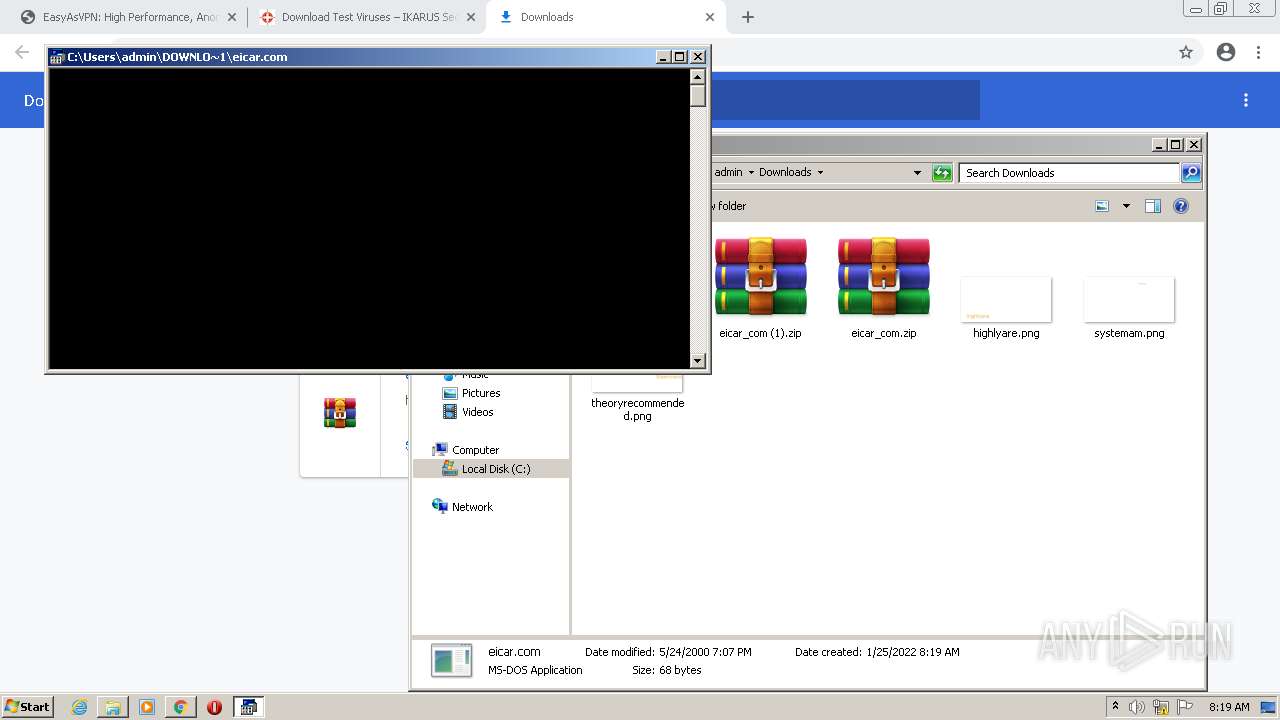
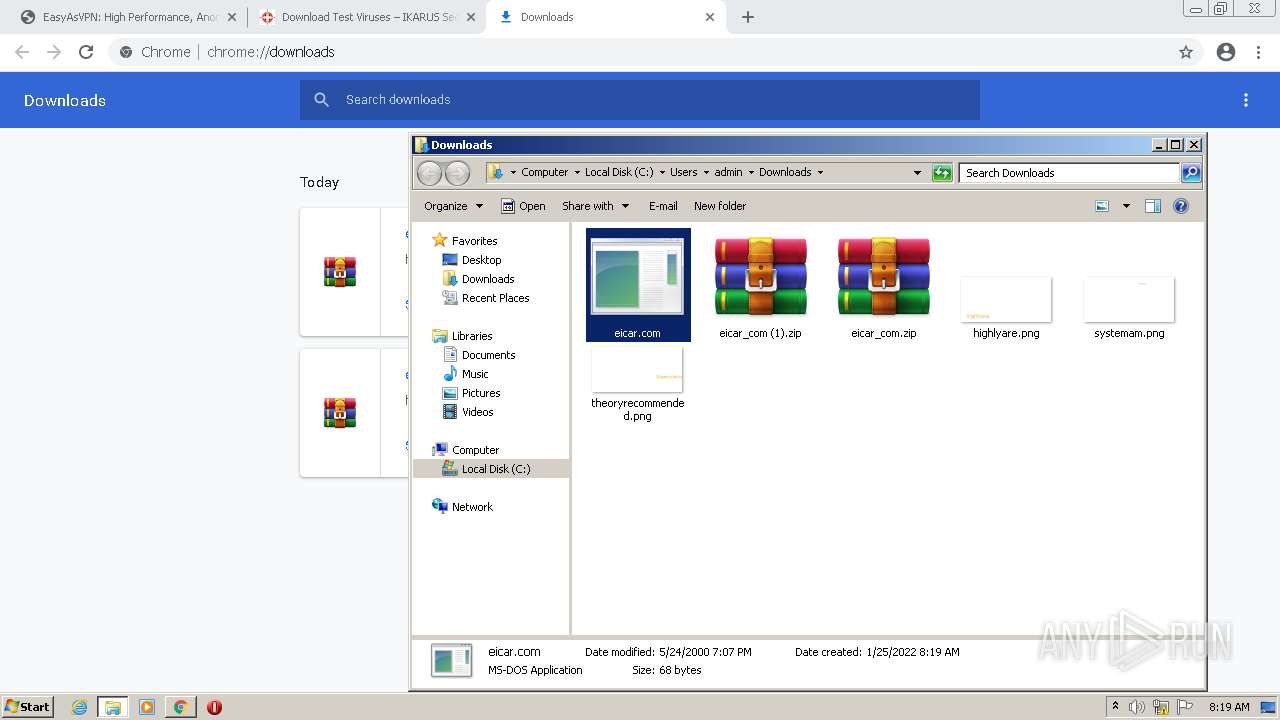
Manual execution by user
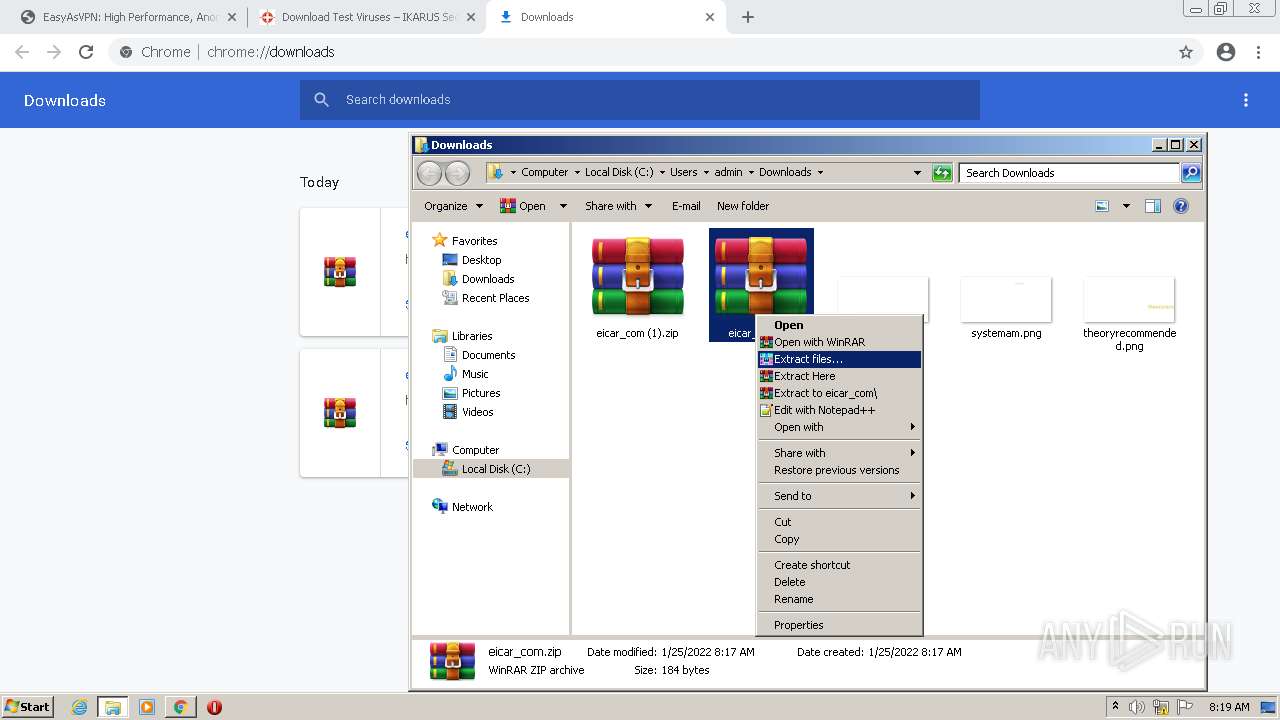
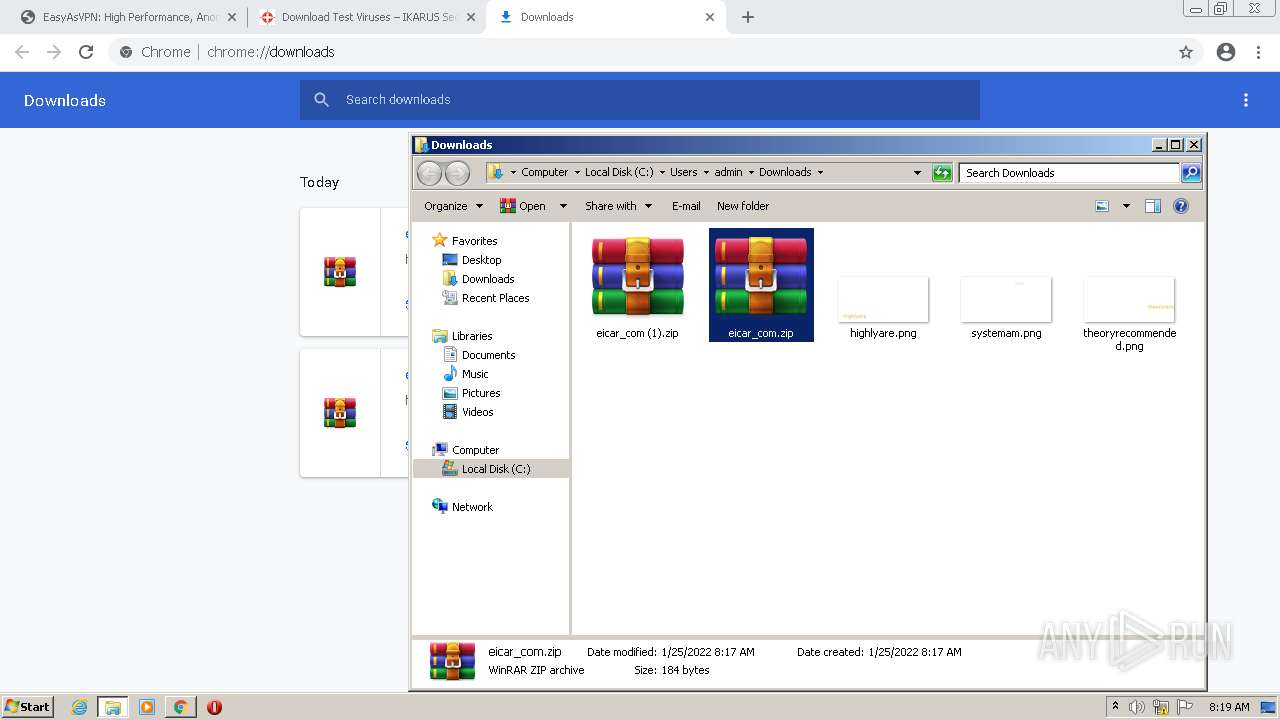
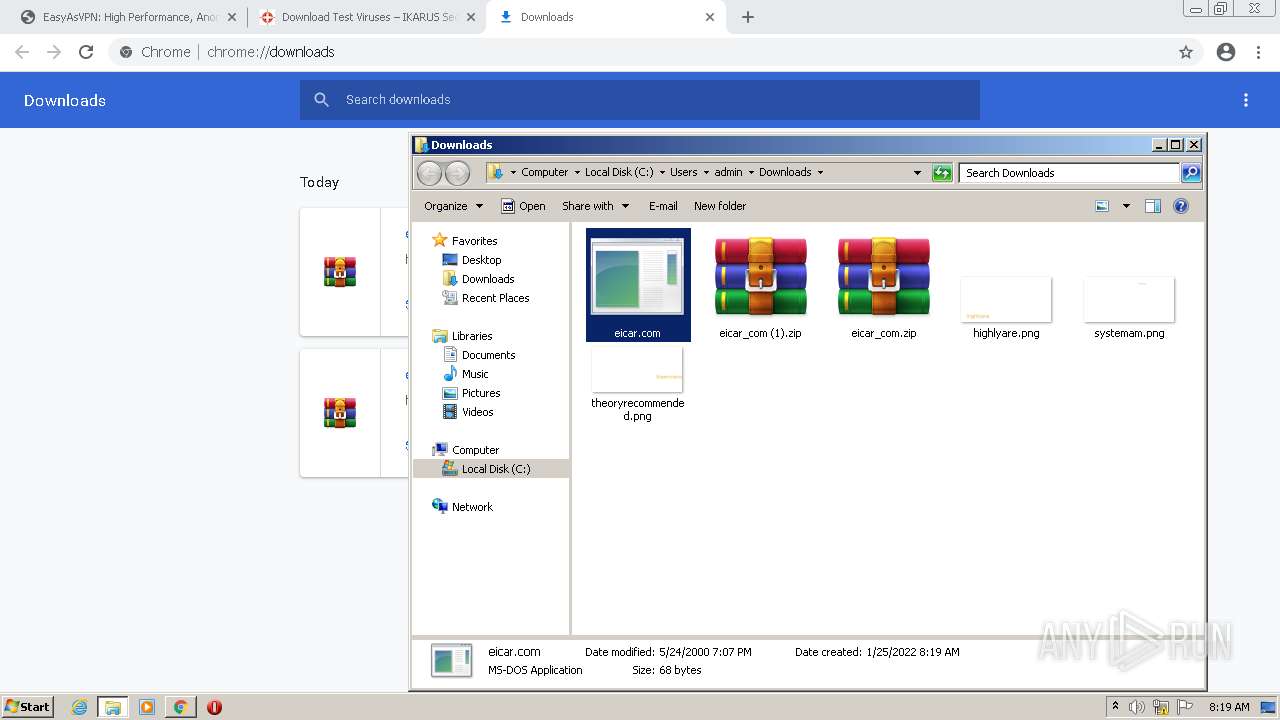
- WinRAR.exe (PID: 3860)
- ntvdm.exe (PID: 2520)
- ntvdm.exe (PID: 1656)
- ntvdm.exe (PID: 1020)
- ntvdm.exe (PID: 2180)
- ntvdm.exe (PID: 2520)
- ntvdm.exe (PID: 3316)
- ntvdm.exe (PID: 3156)
- ntvdm.exe (PID: 3496)
- ntvdm.exe (PID: 3044)
Checks Windows Trust Settings
- chrome.exe (PID: 3536)
- GenericSetup.exe (PID: 2284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
143
Monitored processes
84
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3156 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3420 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=56 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 580 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1020 | "C:\Windows\system32\ntvdm.exe" -i7 | C:\Windows\system32\ntvdm.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
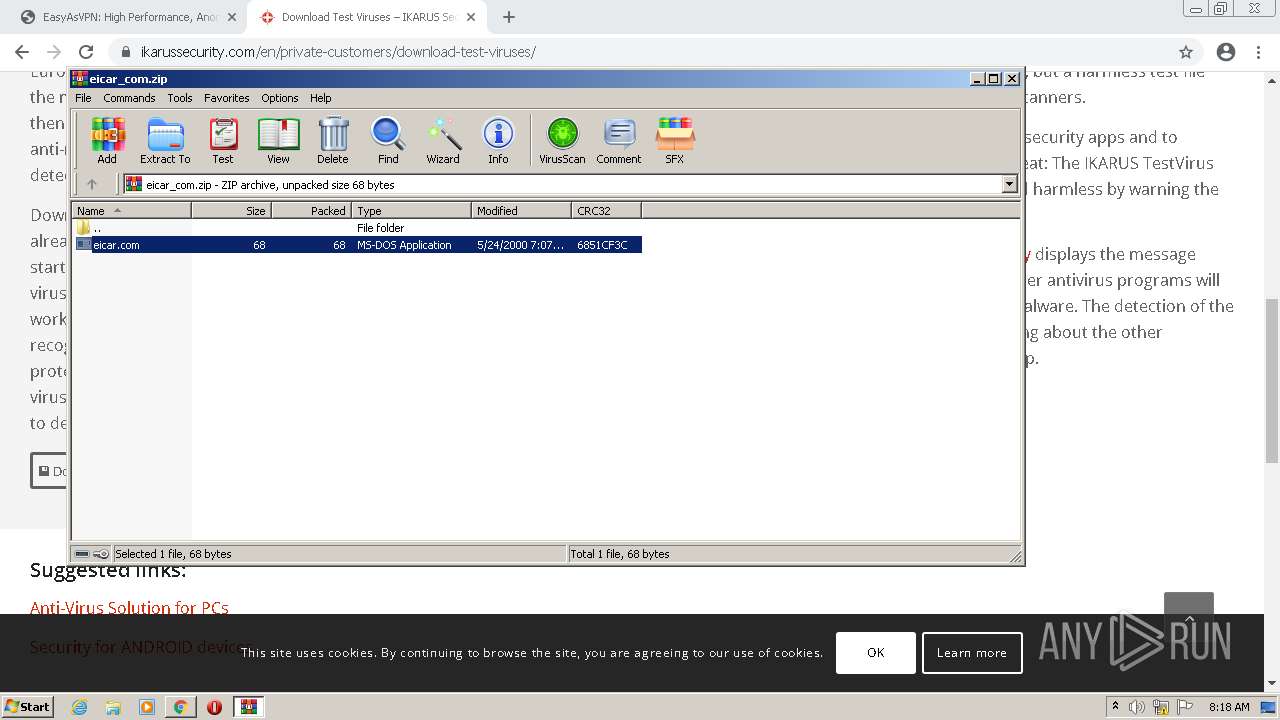
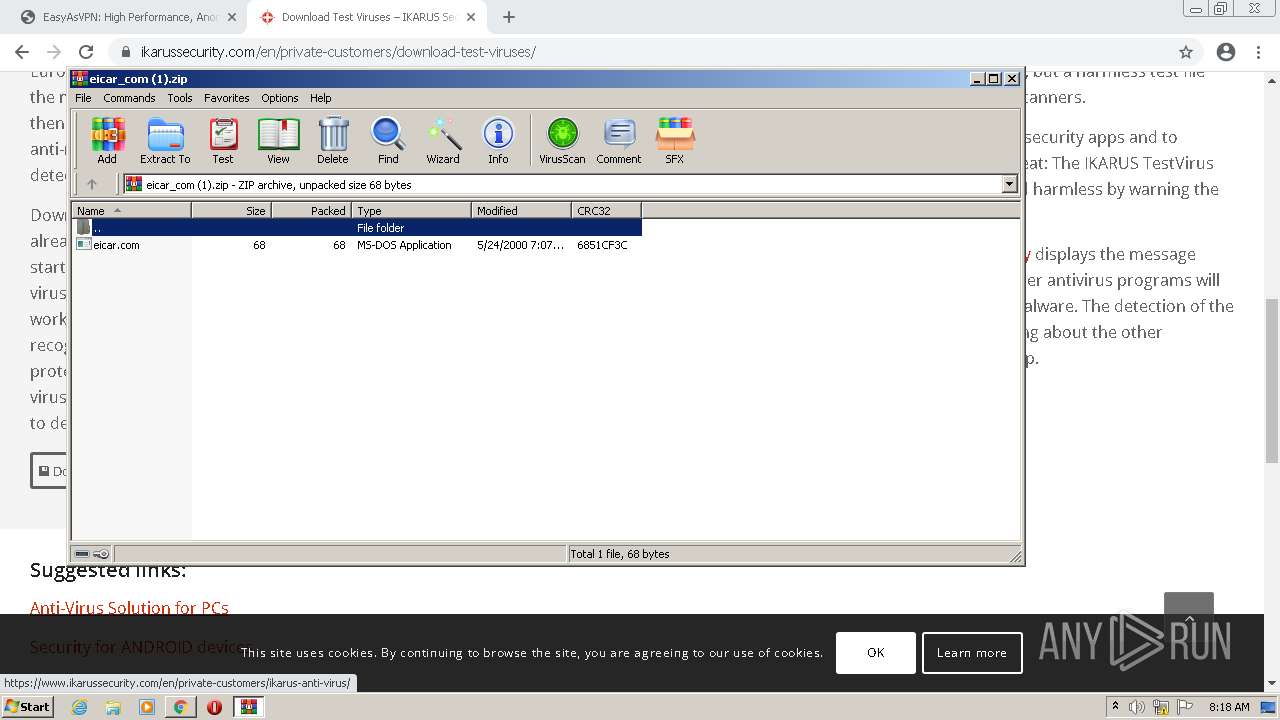
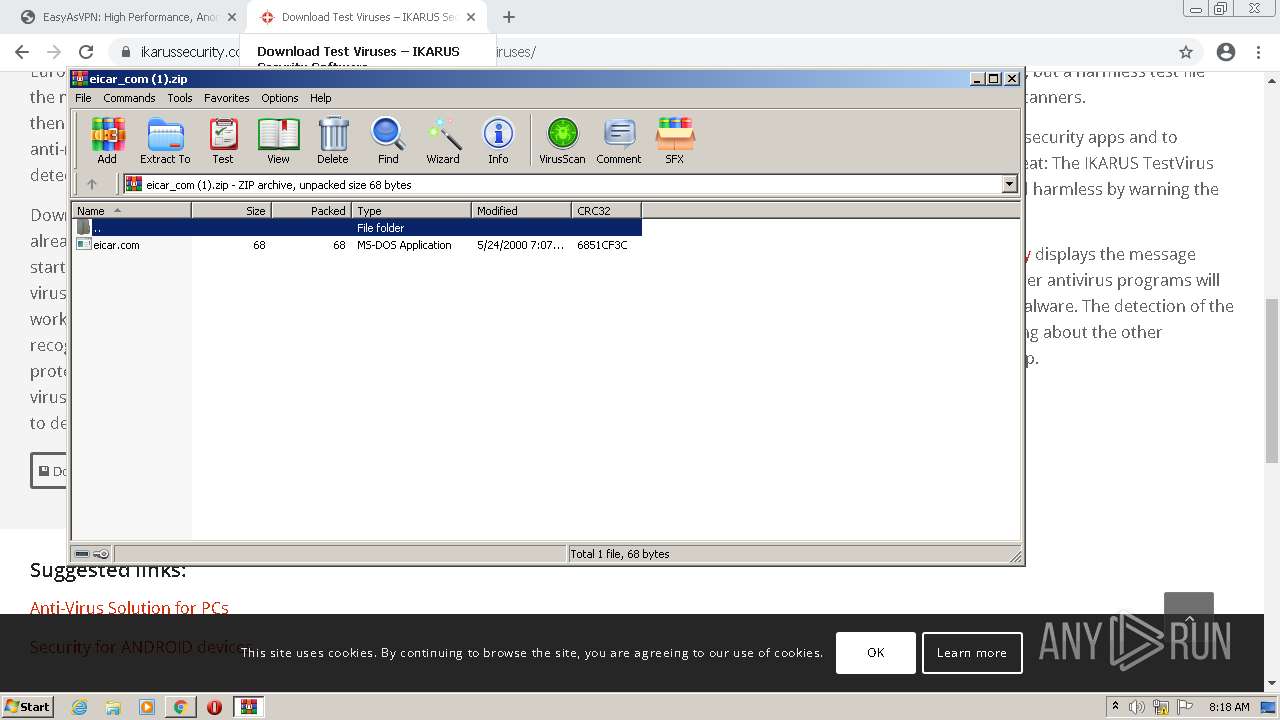
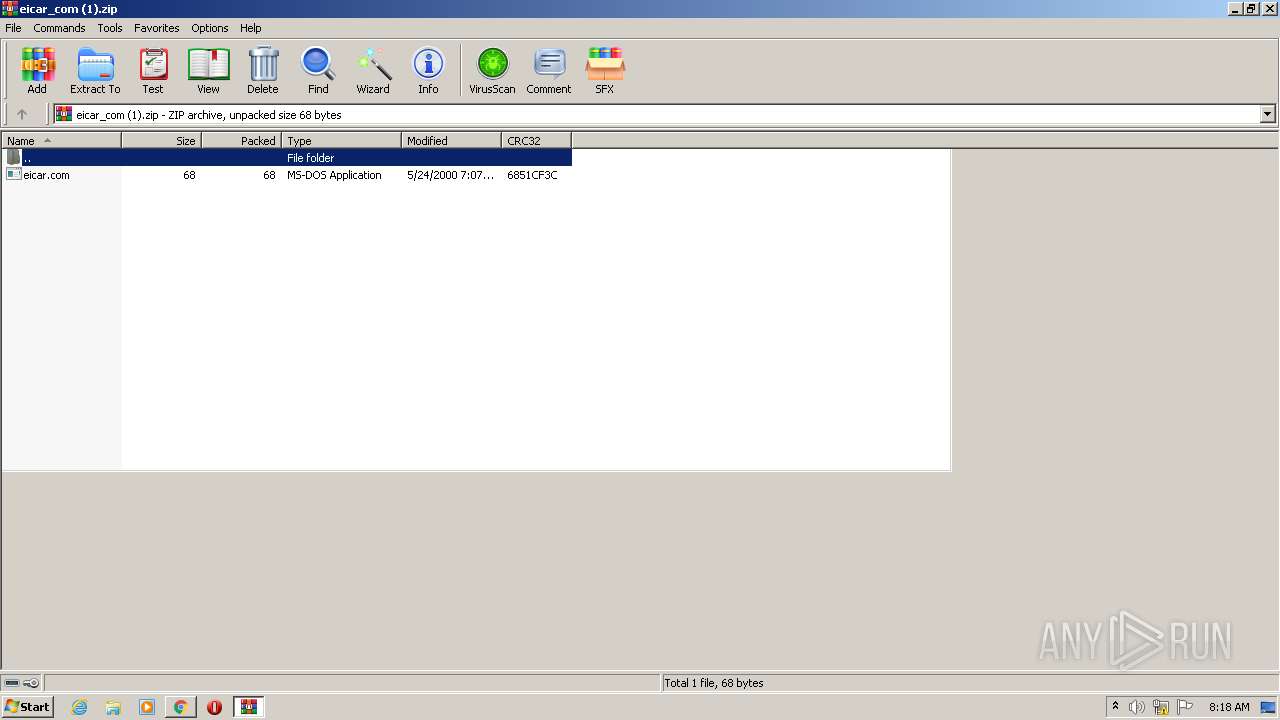
| 1188 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\eicar_com (1).zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,4081030515935642836,13687861013059722396,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
41 660
Read events
41 337
Write events
317
Delete events
6
Modification events
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
13
Suspicious files
76
Text files
250
Unknown types
4
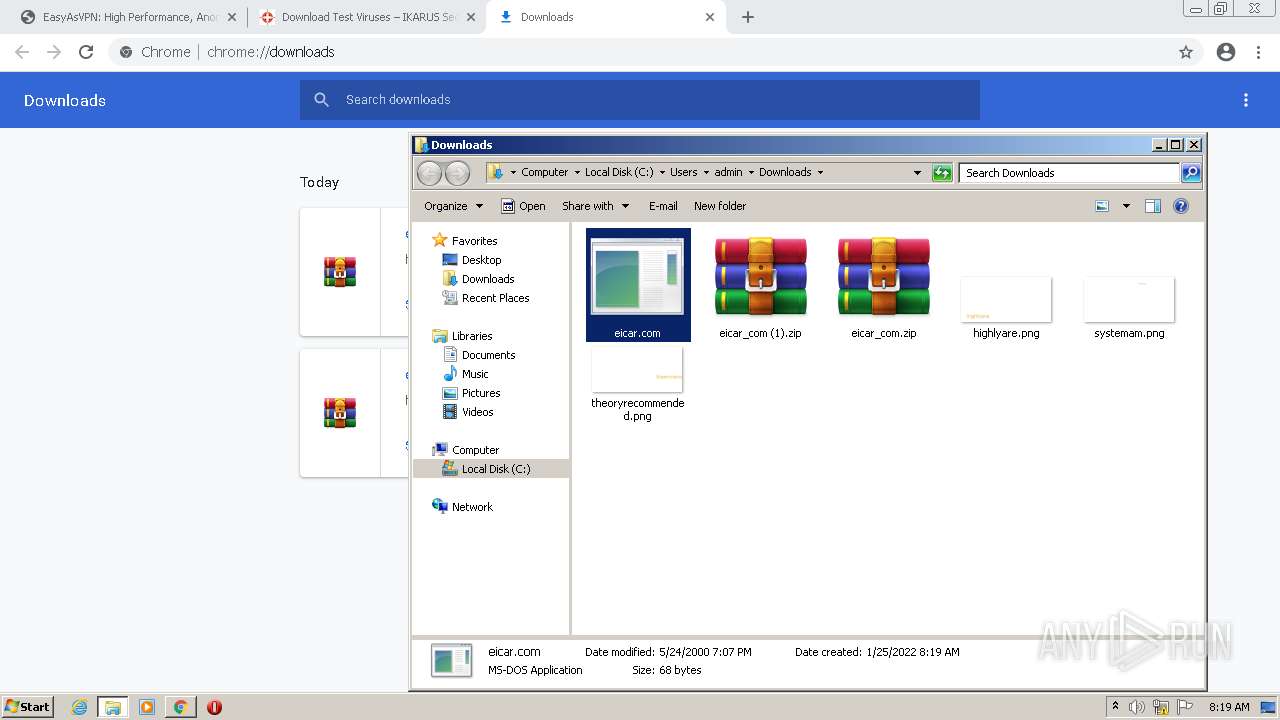
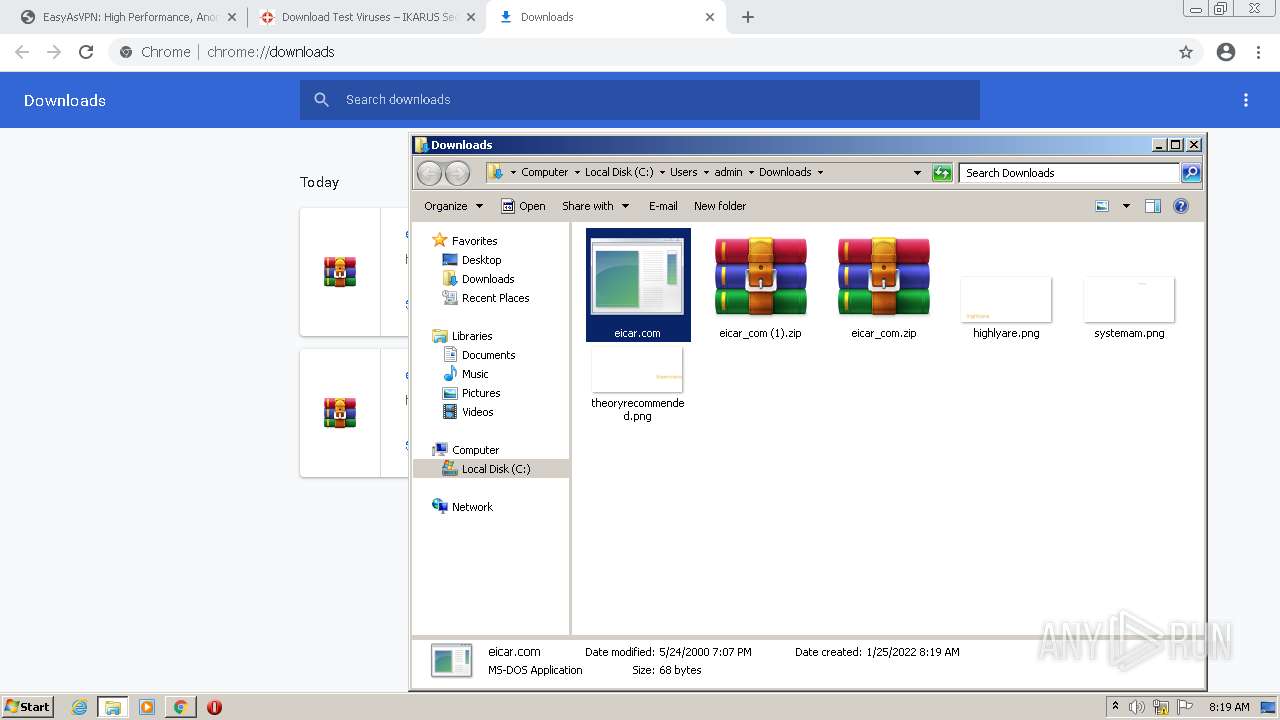
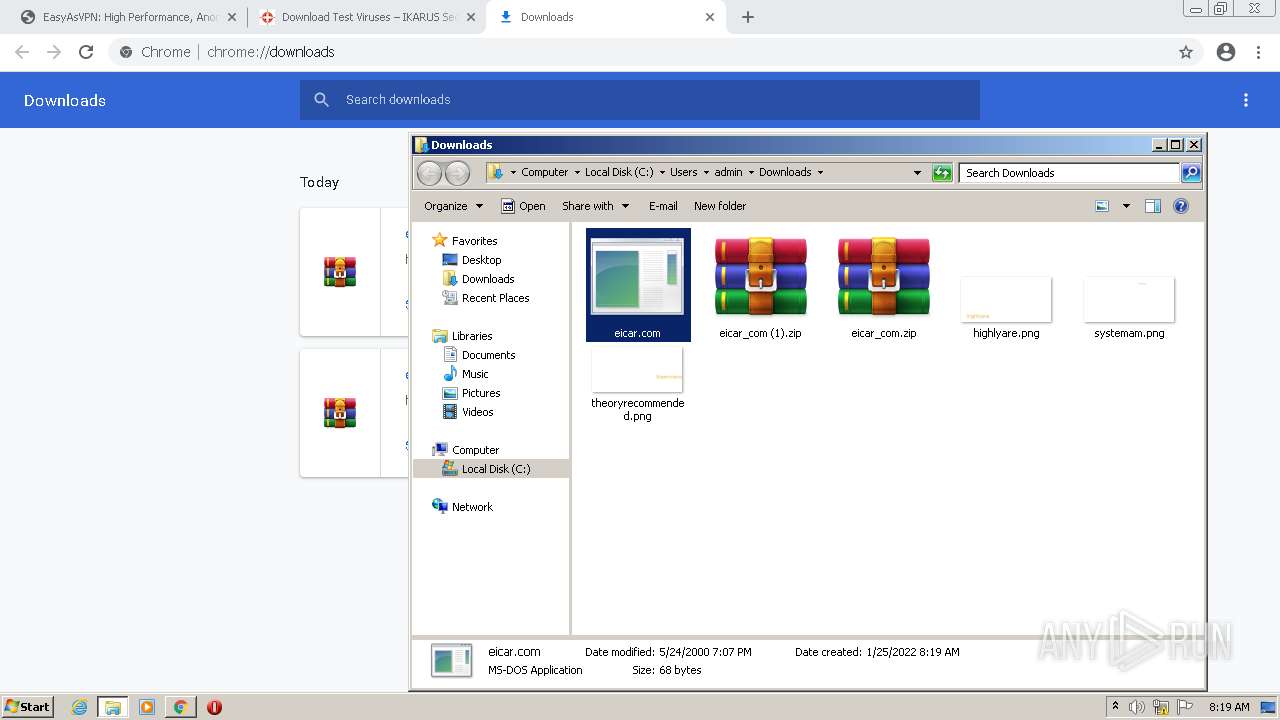
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EFB1DA-DD0.pma | — | |
MD5:— | SHA256:— | |||
| 3536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b5c81c1a-1806-45fa-9fba-27d91add8e37.tmp | text | |
MD5:— | SHA256:— | |||
| 3536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12c79e.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF12c7ad.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF12c8a7.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
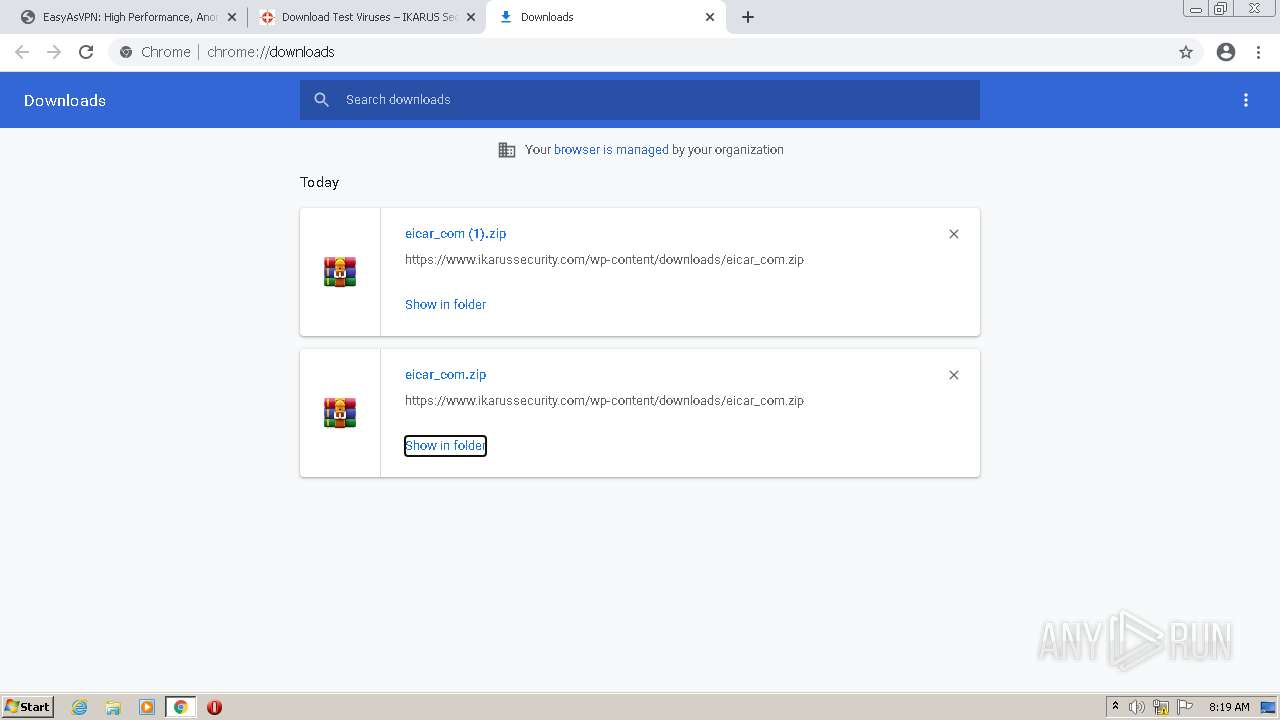
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
62
DNS requests
51
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mjpchtvxuzvmgs3kbhfbvsewiq_2766/jflookgnkcckhobaglndicnbbgbonegd_2766_all_ackzrb6mp2pobw3tsgfn2whb5ava.crx3 | US | — | — | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mjpchtvxuzvmgs3kbhfbvsewiq_2766/jflookgnkcckhobaglndicnbbgbonegd_2766_all_ackzrb6mp2pobw3tsgfn2whb5ava.crx3 | US | binary | 9.73 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 45.0 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 1.10 Mb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mjpchtvxuzvmgs3kbhfbvsewiq_2766/jflookgnkcckhobaglndicnbbgbonegd_2766_all_ackzrb6mp2pobw3tsgfn2whb5ava.crx3 | US | binary | 9.75 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 89.1 Kb | whitelisted |
3816 | chrome.exe | GET | 200 | 23.53.43.50:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDFotP2600ZPBepCqOKKW5U | NL | der | 1.54 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mjpchtvxuzvmgs3kbhfbvsewiq_2766/jflookgnkcckhobaglndicnbbgbonegd_2766_all_ackzrb6mp2pobw3tsgfn2whb5ava.crx3 | US | abr | 127 b | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 720 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mjpchtvxuzvmgs3kbhfbvsewiq_2766/jflookgnkcckhobaglndicnbbgbonegd_2766_all_ackzrb6mp2pobw3tsgfn2whb5ava.crx3 | US | binary | 5.66 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
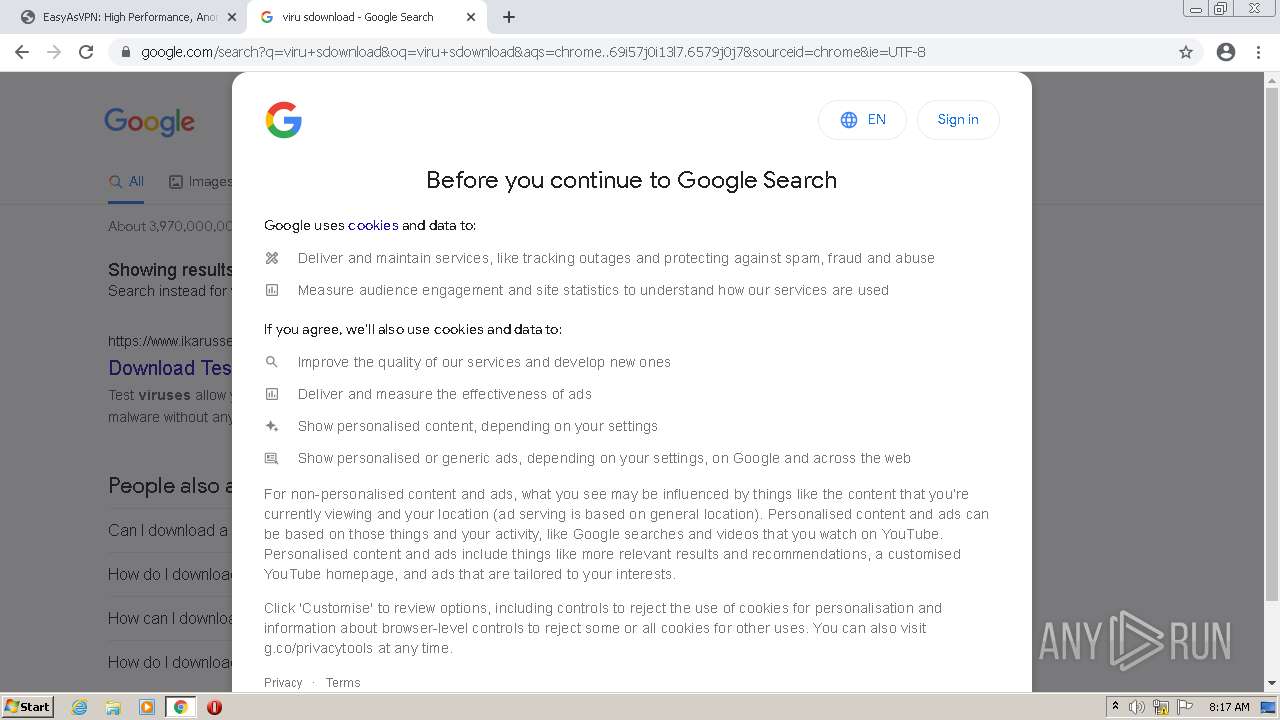
3816 | chrome.exe | 142.250.186.45:443 | accounts.google.com | Google Inc. | US | suspicious |
3816 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 142.250.185.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 142.250.186.78:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 142.250.184.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 142.250.74.142:443 | consent.google.com | Google Inc. | US | whitelisted |
3816 | chrome.exe | 142.250.185.138:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
easyasvpn.com |
| suspicious |
accounts.google.com |
| shared |
turninted-suradios.icu |
| suspicious |
a.nel.cloudflare.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
3816 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
5 ETPRO signatures available at the full report
Process | Message |
|---|---|
GenericSetup.exe | Error: File not found - genericsetup.wrappers.sciter:console.tis
|
GenericSetup.exe | at sciter:init-script.tis
|
GenericSetup.exe | |
GenericSetup.exe | |
GenericSetup.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|
GenericSetup.exe | Error: File not found - genericsetup.wrappers.sciter:console.tis
|
GenericSetup.exe | at sciter:init-script.tis
|
GenericSetup.exe | |
GenericSetup.exe | |
GenericSetup.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|