| File name: | 2020-06-09-soub1.cab-from-xsiv7v4qzjq6rdmpp.com.bin |
| Full analysis: | https://app.any.run/tasks/9dc4700a-6907-4646-b7a3-a797b5268180 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 07:19:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | D717A41516AC54155B362B4D0D923F49 |
| SHA1: | 9569C2C3CCC11D23C05C62089DEEE08E568697EA |
| SHA256: | 9BB9BE7AF6B4FBEDB52CC47AC640E4B96F49DAC76CDB7E28C4DD06A70139D7D0 |
| SSDEEP: | 6144:Abn3wL9n85k46vl/3LUYODnu6EwNjSqZU0g5tkUASBY9kIJfKF5:63s9n6k469mtFqtkVqUKF5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
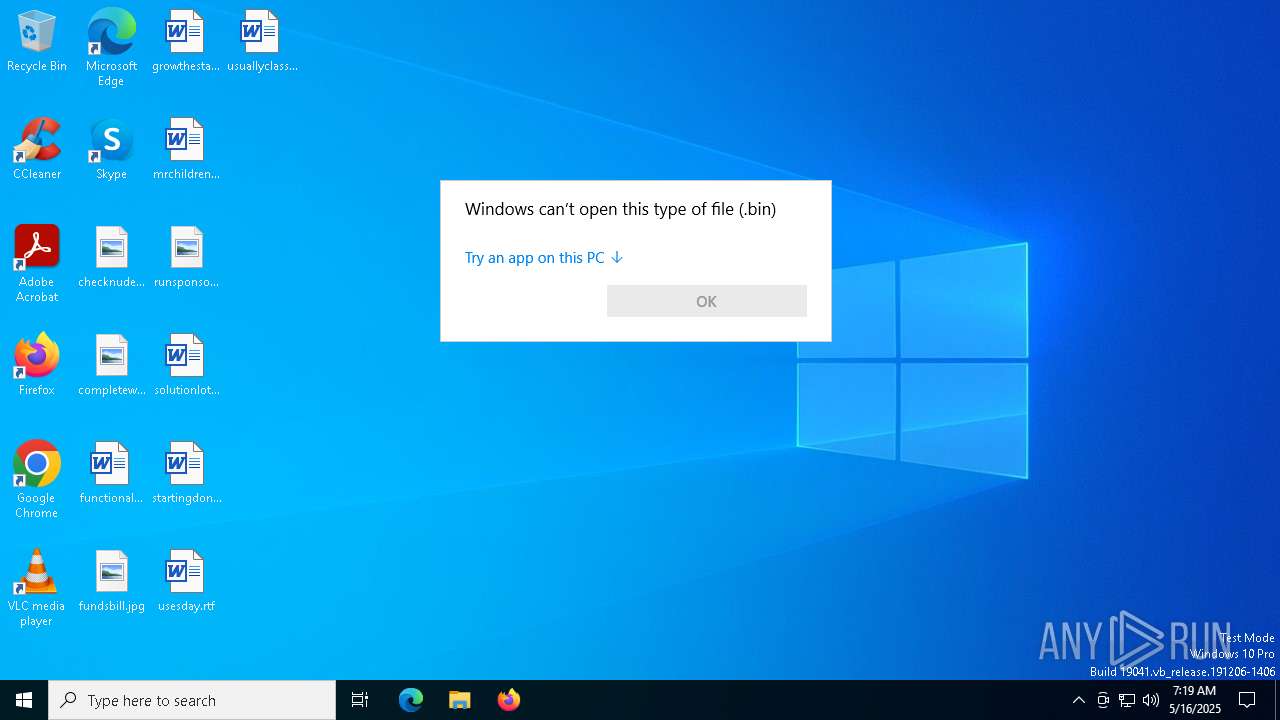
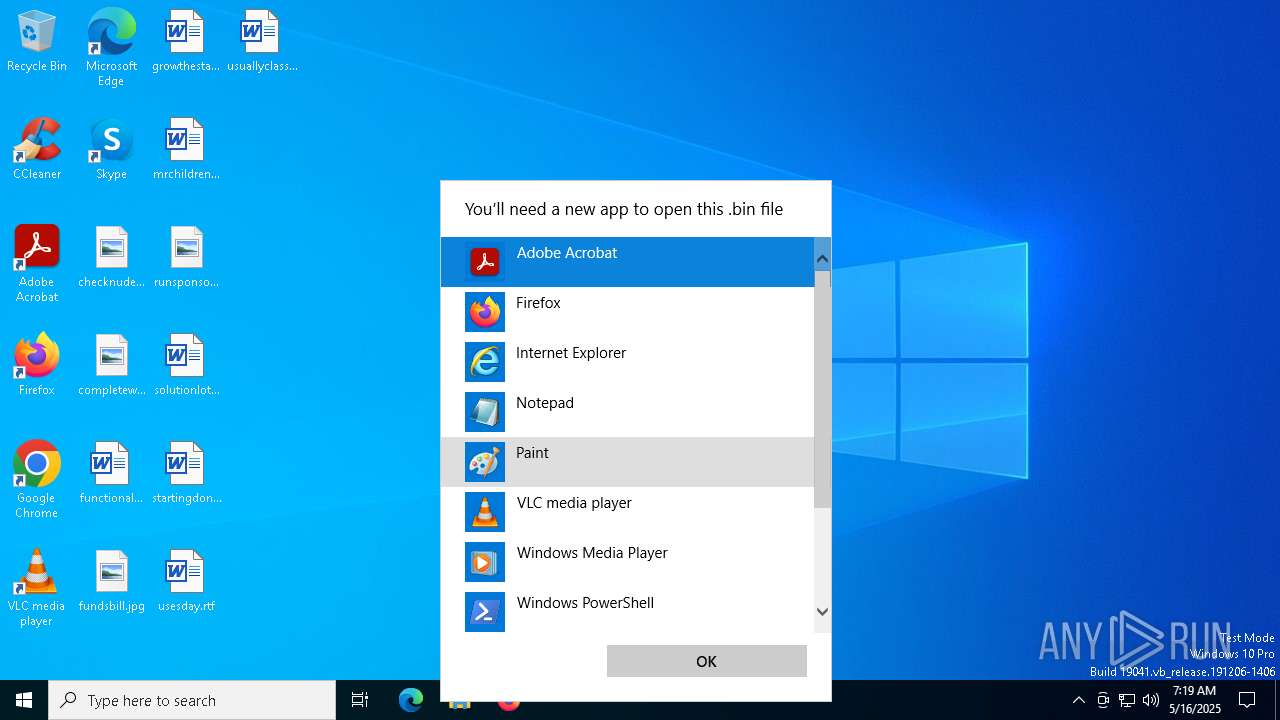
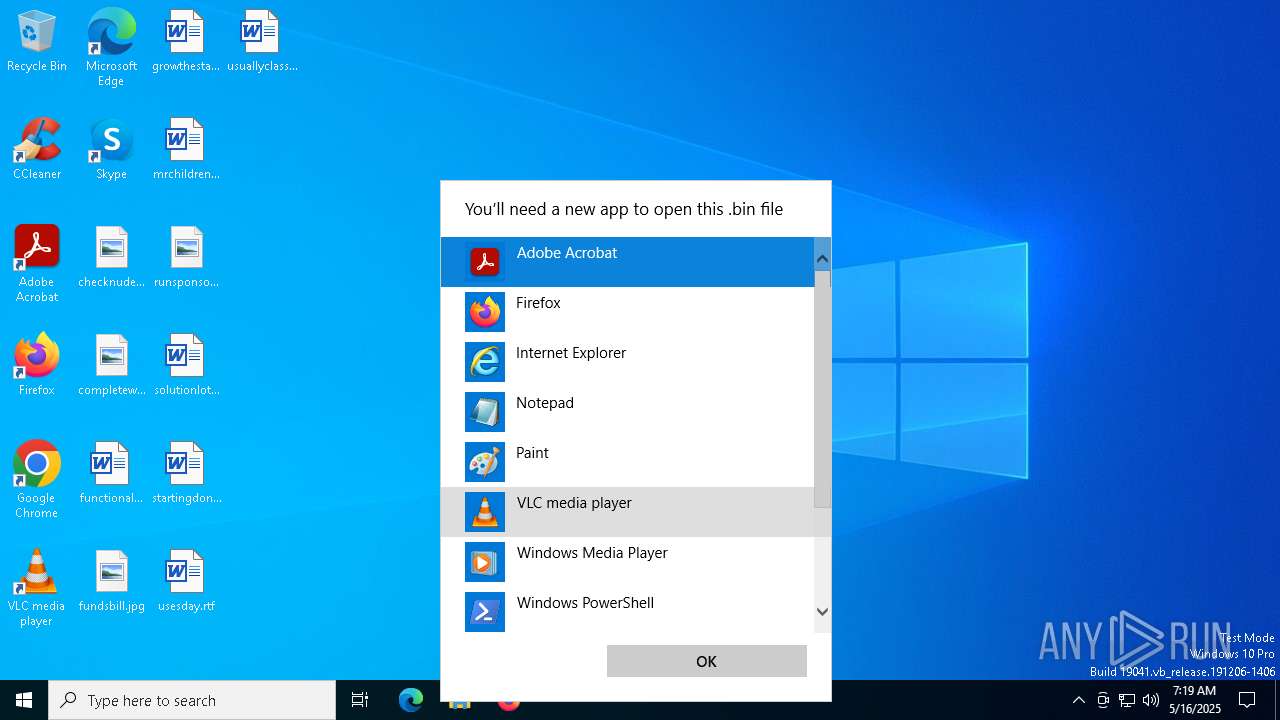
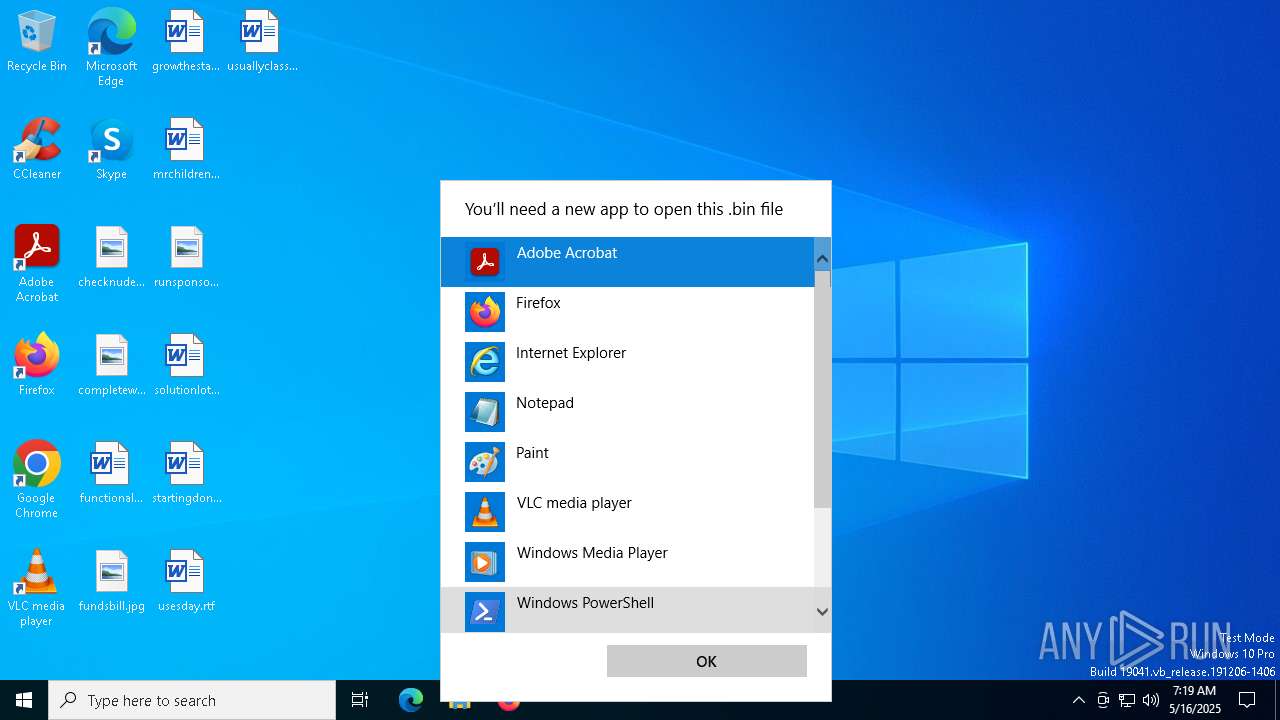
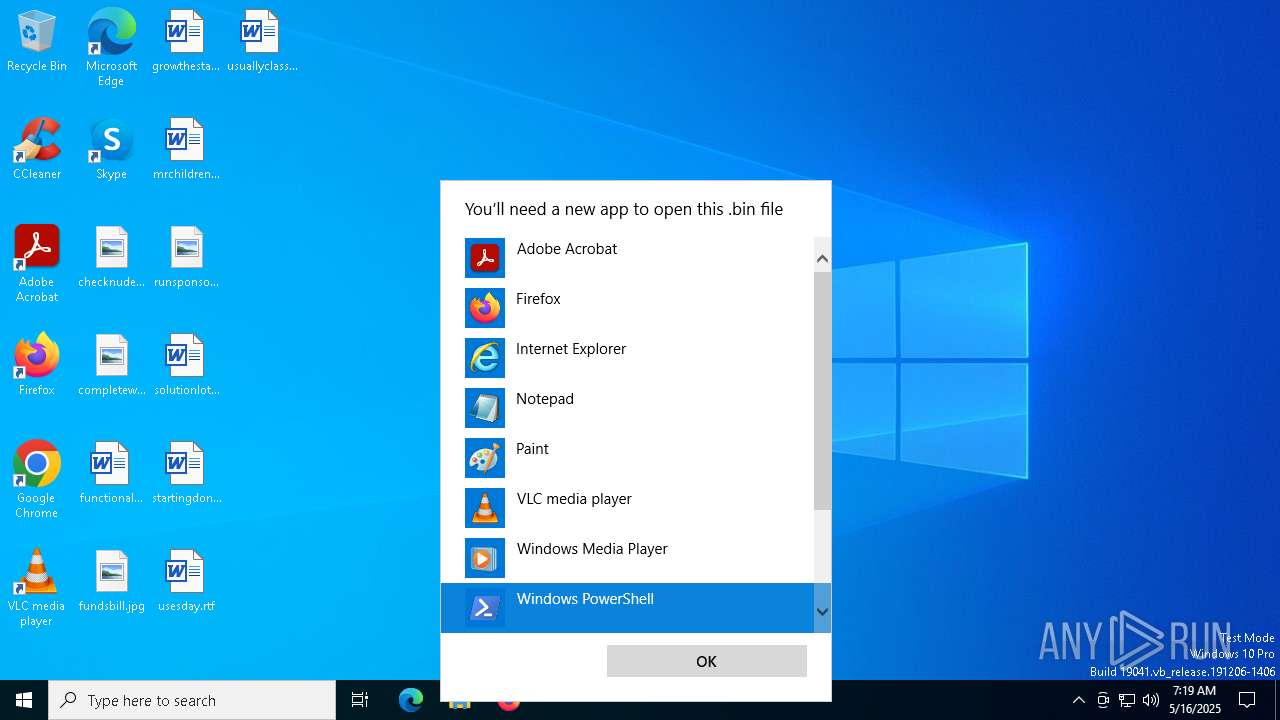
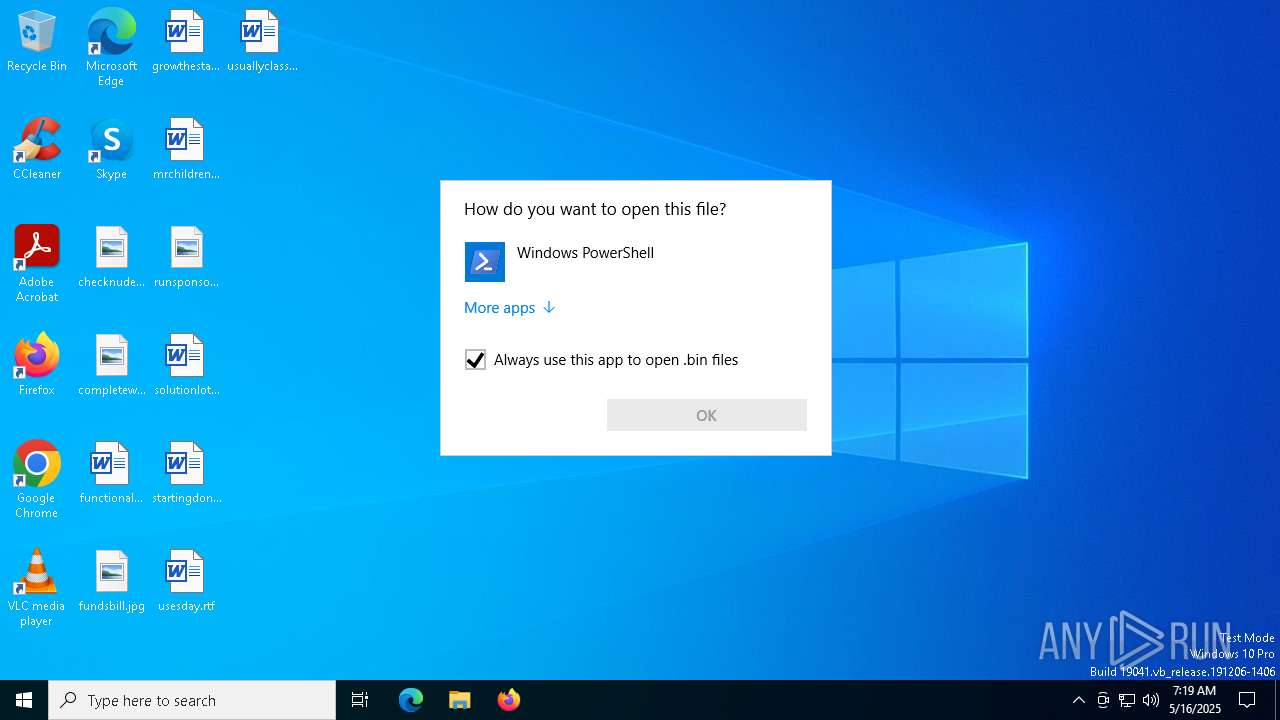
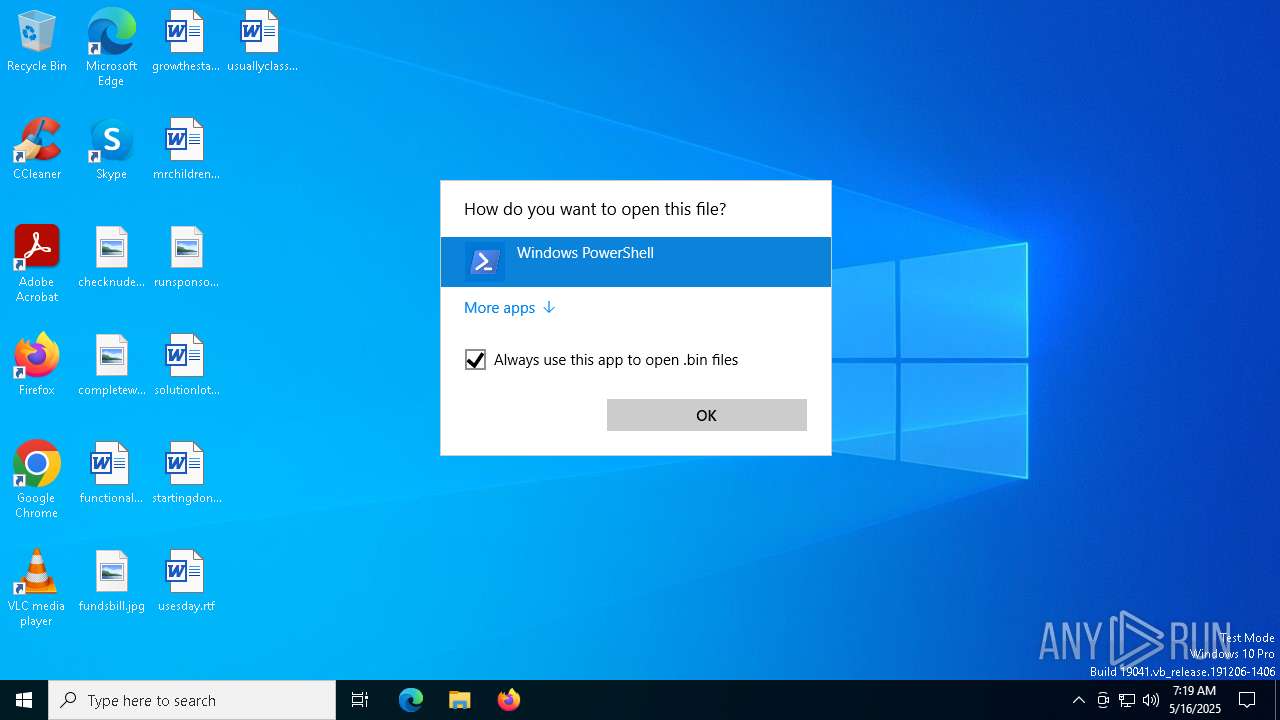
Starts POWERSHELL.EXE for commands execution
- OpenWith.exe (PID: 4380)
- OpenWith.exe (PID: 4980)
- powershell.exe (PID: 5608)
- powershell.exe (PID: 1012)
- powershell.exe (PID: 5156)
- powershell.exe (PID: 6372)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 728)
- powershell.exe (PID: 900)
- powershell.exe (PID: 5408)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 3008)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 1348)
- powershell.exe (PID: 4284)
- powershell.exe (PID: 856)
- powershell.exe (PID: 4728)
- powershell.exe (PID: 5776)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 4008)
- powershell.exe (PID: 4696)
- powershell.exe (PID: 5232)
- powershell.exe (PID: 960)
- powershell.exe (PID: 5156)
- powershell.exe (PID: 4608)
- powershell.exe (PID: 1184)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 668)
- powershell.exe (PID: 2852)
- powershell.exe (PID: 1628)
- powershell.exe (PID: 864)
- powershell.exe (PID: 5176)
- powershell.exe (PID: 6068)
- powershell.exe (PID: 3976)
- powershell.exe (PID: 856)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 6652)
- powershell.exe (PID: 4268)
- powershell.exe (PID: 4608)
- powershell.exe (PID: 1164)
- powershell.exe (PID: 6148)
- powershell.exe (PID: 4488)
- powershell.exe (PID: 4528)
- powershell.exe (PID: 1196)
- powershell.exe (PID: 2148)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6824)
- powershell.exe (PID: 1600)
- powershell.exe (PID: 1240)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 2392)
- powershell.exe (PID: 5020)
- powershell.exe (PID: 5216)
- powershell.exe (PID: 4268)
- powershell.exe (PID: 3008)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 3124)
- powershell.exe (PID: 4408)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 1388)
- powershell.exe (PID: 5188)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 1020)
- powershell.exe (PID: 7144)
- powershell.exe (PID: 5304)
- powershell.exe (PID: 6944)
- powershell.exe (PID: 1244)
- powershell.exe (PID: 5384)
- powershell.exe (PID: 3976)
- powershell.exe (PID: 4164)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 6972)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 5428)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 5964)
- powershell.exe (PID: 5036)
- powershell.exe (PID: 4304)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 6564)
- powershell.exe (PID: 920)
- powershell.exe (PID: 4428)
- powershell.exe (PID: 5364)
- powershell.exe (PID: 856)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 5608)
- powershell.exe (PID: 4652)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 5740)
- powershell.exe (PID: 3176)
- powershell.exe (PID: 5332)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 4212)
- powershell.exe (PID: 6468)
- powershell.exe (PID: 4188)
- powershell.exe (PID: 5304)
- powershell.exe (PID: 2992)
- powershell.exe (PID: 7136)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 6652)
- powershell.exe (PID: 1628)
- powershell.exe (PID: 900)
- powershell.exe (PID: 3992)
- powershell.exe (PID: 6156)
- powershell.exe (PID: 6612)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 6072)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 4652)
- powershell.exe (PID: 5176)
- powershell.exe (PID: 4348)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 2664)
- powershell.exe (PID: 2104)
- powershell.exe (PID: 5056)
- powershell.exe (PID: 4348)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 3976)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 232)
- powershell.exe (PID: 456)
- powershell.exe (PID: 3748)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 2776)
- powershell.exe (PID: 4476)
- powershell.exe (PID: 1244)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 808)
- powershell.exe (PID: 3164)
- powershell.exe (PID: 1704)
- powershell.exe (PID: 5244)
- powershell.exe (PID: 2416)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 3264)
- powershell.exe (PID: 2148)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 5332)
- powershell.exe (PID: 6780)
- powershell.exe (PID: 2432)
Application launched itself
- powershell.exe (PID: 1012)
- powershell.exe (PID: 5608)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 6372)
- powershell.exe (PID: 5156)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 5408)
- powershell.exe (PID: 3008)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 728)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 4284)
- powershell.exe (PID: 856)
- powershell.exe (PID: 4728)
- powershell.exe (PID: 900)
- powershell.exe (PID: 5436)
- powershell.exe (PID: 1348)
- powershell.exe (PID: 5776)
- powershell.exe (PID: 4696)
- powershell.exe (PID: 1184)
- powershell.exe (PID: 5156)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 4608)
- powershell.exe (PID: 4008)
- powershell.exe (PID: 5232)
- powershell.exe (PID: 960)
- powershell.exe (PID: 1628)
- powershell.exe (PID: 6068)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 668)
- powershell.exe (PID: 2852)
- powershell.exe (PID: 5176)
- powershell.exe (PID: 864)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 856)
- powershell.exe (PID: 3976)
- powershell.exe (PID: 6652)
- powershell.exe (PID: 4268)
- powershell.exe (PID: 4608)
- powershell.exe (PID: 1164)
- powershell.exe (PID: 6148)
- powershell.exe (PID: 4528)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 1196)
- powershell.exe (PID: 2148)
- powershell.exe (PID: 4488)
- powershell.exe (PID: 6824)
- powershell.exe (PID: 1600)
- powershell.exe (PID: 1240)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 2392)
- powershell.exe (PID: 5020)
- powershell.exe (PID: 5216)
- powershell.exe (PID: 3008)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 1388)
- powershell.exe (PID: 4408)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 4268)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 5188)
- powershell.exe (PID: 7144)
- powershell.exe (PID: 5304)
- powershell.exe (PID: 1020)
- powershell.exe (PID: 6944)
- powershell.exe (PID: 1244)
- powershell.exe (PID: 3124)
- powershell.exe (PID: 5384)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 3300)
- powershell.exe (PID: 4164)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 6972)
- powershell.exe (PID: 3976)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 5428)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 4304)
- powershell.exe (PID: 5964)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 3176)
- powershell.exe (PID: 6564)
- powershell.exe (PID: 920)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 5036)
- powershell.exe (PID: 5364)
- powershell.exe (PID: 856)
- powershell.exe (PID: 5608)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 5740)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 4652)
- powershell.exe (PID: 4428)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 6468)
- powershell.exe (PID: 4212)
- powershell.exe (PID: 5304)
- powershell.exe (PID: 4188)
- powershell.exe (PID: 2992)
- powershell.exe (PID: 5332)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 7136)
- powershell.exe (PID: 6072)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 6652)
- powershell.exe (PID: 900)
- powershell.exe (PID: 3992)
- powershell.exe (PID: 6156)
- powershell.exe (PID: 6612)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 1628)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 4652)
- powershell.exe (PID: 5176)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 4348)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 3976)
- powershell.exe (PID: 2664)
- powershell.exe (PID: 2104)
- powershell.exe (PID: 232)
- powershell.exe (PID: 5056)
- powershell.exe (PID: 4348)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 808)
- powershell.exe (PID: 3748)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 2776)
- powershell.exe (PID: 4476)
- powershell.exe (PID: 1244)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 456)
- powershell.exe (PID: 1704)
- powershell.exe (PID: 3264)
- powershell.exe (PID: 2416)
- powershell.exe (PID: 5244)
- powershell.exe (PID: 6780)
- powershell.exe (PID: 2148)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 3164)
- powershell.exe (PID: 5332)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 2432)
INFO
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 4380)
- OpenWith.exe (PID: 4980)
The sample compiled with english language support
- OpenWith.exe (PID: 4380)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4380)
- OpenWith.exe (PID: 4980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:06:09 09:06:26+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, DLL |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 105472 |
| InitializedDataSize: | 188416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1009f |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.2.0.304 |
| ProductVersionNumber: | 8.2.0.304 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Region LegQuart Corporation |
| FileVersion: | 8.2.0.304 fo-349259 |
| InternalName: | Area connect |
| LegalCopyright: | © Region LegQuart Corporation. All rights reserved. |
| OriginalFileName: | Area connect.DLL |
| ProductName: | Region LegQuart® LotRing® wife make |
| ProductVersion: | 8.2.0.304 |
Total processes
443
Monitored processes
313
Malicious processes
1
Suspicious processes
71
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\AppData\Local\Temp\2020-06-09-soub1.cab-from-xsiv7v4qzjq6rdmpp.com.bin" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\AppData\Local\Temp\2020-06-09-soub1.cab-from-xsiv7v4qzjq6rdmpp.com.bin" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\AppData\Local\Temp\2020-06-09-soub1.cab-from-xsiv7v4qzjq6rdmpp.com.bin" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\AppData\Local\Temp\2020-06-09-soub1.cab-from-xsiv7v4qzjq6rdmpp.com.bin" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
718 324
Read events
718 165
Write events
159
Delete events
0
Modification events
| (PID) Process: | (4980) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.bin\UserChoice |
| Operation: | write | Name: | ProgId |
Value: Applications\powershell.exe | |||
| (PID) Process: | (4980) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.bin\UserChoice |
| Operation: | write | Name: | Hash |
Value: LJZaJloqabo= | |||
| (PID) Process: | (4980) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.bin\OpenWithProgids |
| Operation: | write | Name: | bin_auto_file |
Value: | |||
| (PID) Process: | (4980) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.bin\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
| (PID) Process: | (4980) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 114 | |||
| (PID) Process: | (1012) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.bin\OpenWithProgids |
| Operation: | write | Name: | bin_auto_file |
Value: | |||
| (PID) Process: | (5608) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.bin\OpenWithProgids |
| Operation: | write | Name: | bin_auto_file |
Value: | |||
| (PID) Process: | (5156) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.bin\OpenWithProgids |
| Operation: | write | Name: | bin_auto_file |
Value: | |||
| (PID) Process: | (4560) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.bin\OpenWithProgids |
| Operation: | write | Name: | bin_auto_file |
Value: | |||
| (PID) Process: | (5408) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.bin\OpenWithProgids |
| Operation: | write | Name: | bin_auto_file |
Value: | |||
Executable files
0
Suspicious files
463
Text files
306
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4UU5VRS0K8JZX3SSG1N2.temp | binary | |
MD5:C6627855CC94F749191AA67F0B67C54E | SHA256:983E806CEC1A0FE0B974C30777EBCBE1597264AAEE6EB5871A65EA83BB9D9DD3 | |||
| 1196 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:8EE2F3FCA7A9D5E8407932FD7824F29E | SHA256:327C23BAEAB1306C15597D2001531C879FEC8493105D830D920C2110767EFCC9 | |||
| 1196 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ONQAPGZSDE4ENZA3ZQW4.temp | binary | |
MD5:8EE2F3FCA7A9D5E8407932FD7824F29E | SHA256:327C23BAEAB1306C15597D2001531C879FEC8493105D830D920C2110767EFCC9 | |||
| 1196 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:50A81914AD669191BFF11635A3A34D09 | SHA256:64FD9E3D223A1033F95BBAE95DE3BB1D746C81762A01C7D226AAAFF7A46DCE74 | |||
| 1196 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iocwsu2k.gkq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1012 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_seorasbi.hyk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1196 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_j01vw5mf.3qb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF111f0e.TMP | binary | |
MD5:8EE2F3FCA7A9D5E8407932FD7824F29E | SHA256:327C23BAEAB1306C15597D2001531C879FEC8493105D830D920C2110767EFCC9 | |||
| 1012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:C6627855CC94F749191AA67F0B67C54E | SHA256:983E806CEC1A0FE0B974C30777EBCBE1597264AAEE6EB5871A65EA83BB9D9DD3 | |||
| 1012 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tq42tk4v.gyc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
29
DNS requests
14
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5576 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3268 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
171.39.242.20.in-addr.arpa |
| unknown |
d.3.0.0.0.0.0.0.0.0.0.0.0.0.0.0.7.0.0.0.8.0.4.0.0.3.0.1.3.0.6.2.ip6.arpa |
| unknown |