| download: | upwork1 |
| Full analysis: | https://app.any.run/tasks/1cd7e117-c6cc-4d42-a582-90fc1ee38e0a |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 22:55:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with CRLF line terminators |
| MD5: | B8DD5BBB5B79D1CBE0350452574F155A |
| SHA1: | 3E60BF86E873E03D6C65E2BEAE8D32668562359B |
| SHA256: | 9BAE55F07001A9268E1C4F8612671D19594BB31D699C6813A3206FA6A7808770 |
| SSDEEP: | 6:h4QboY+oMOO2Rg9AtJav1uZKaoJTwMGNAFKUYUHPGb:hPQofRgitoao5cUVPGb |
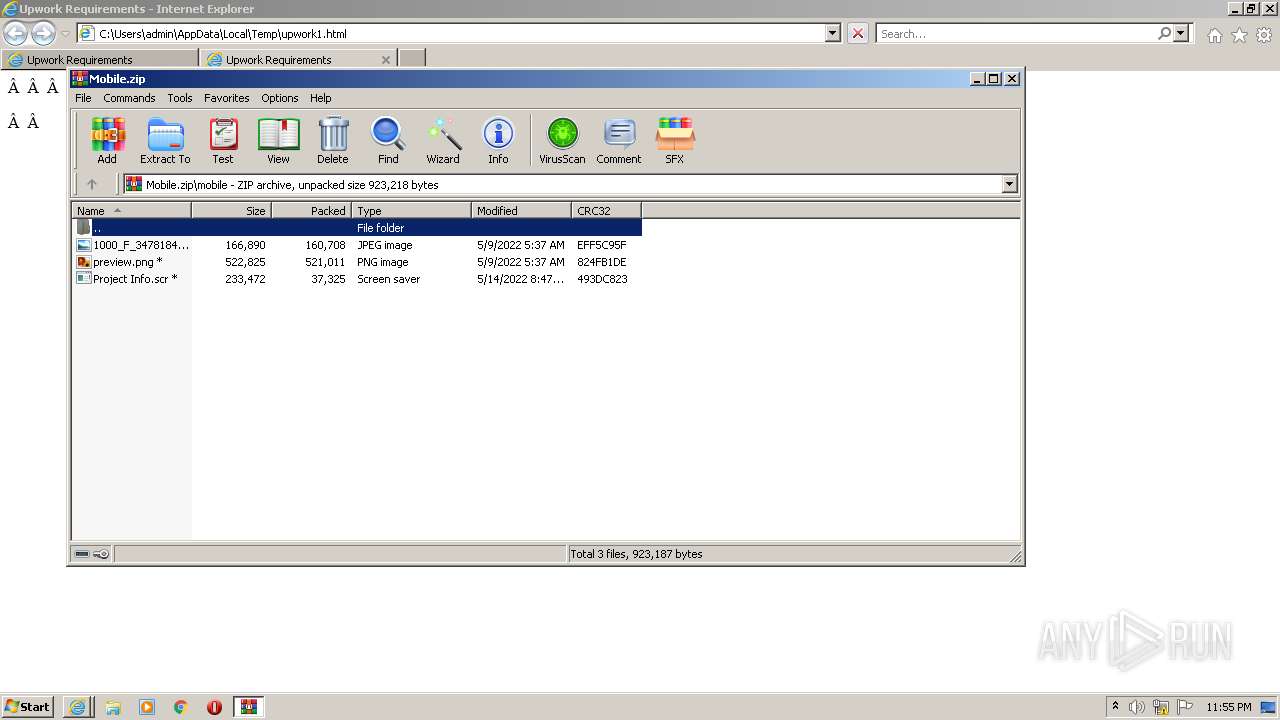
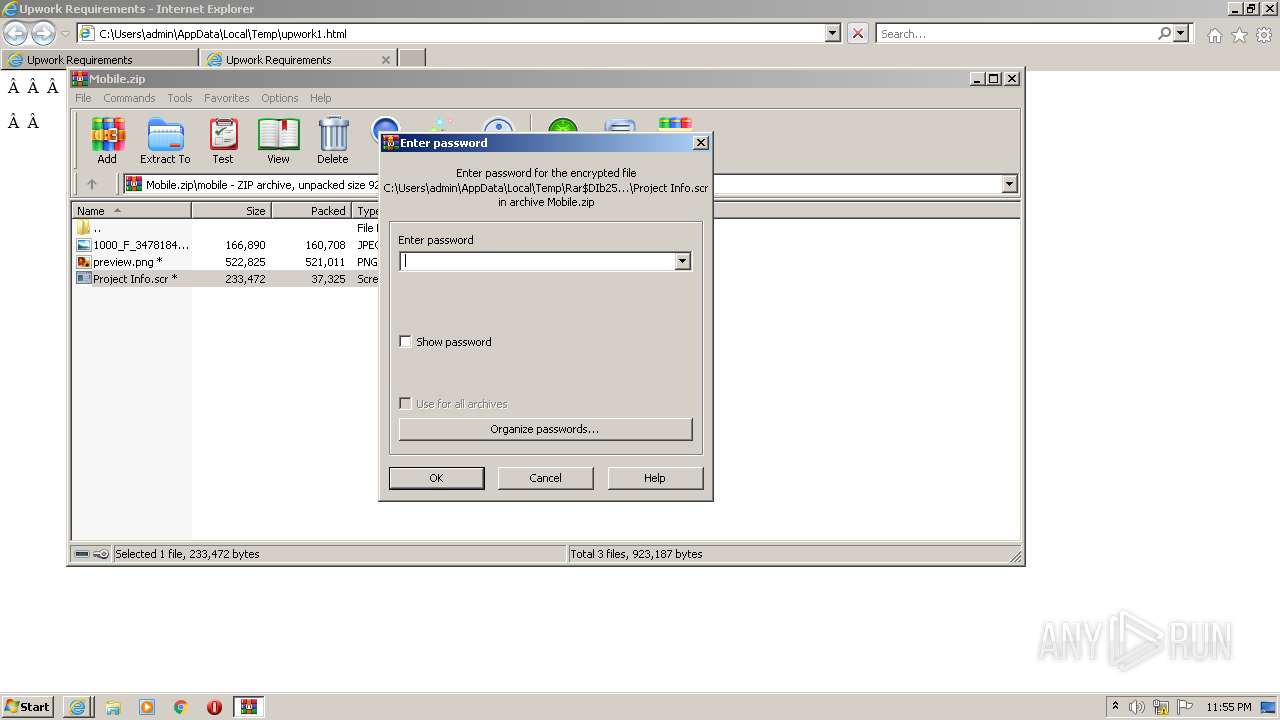
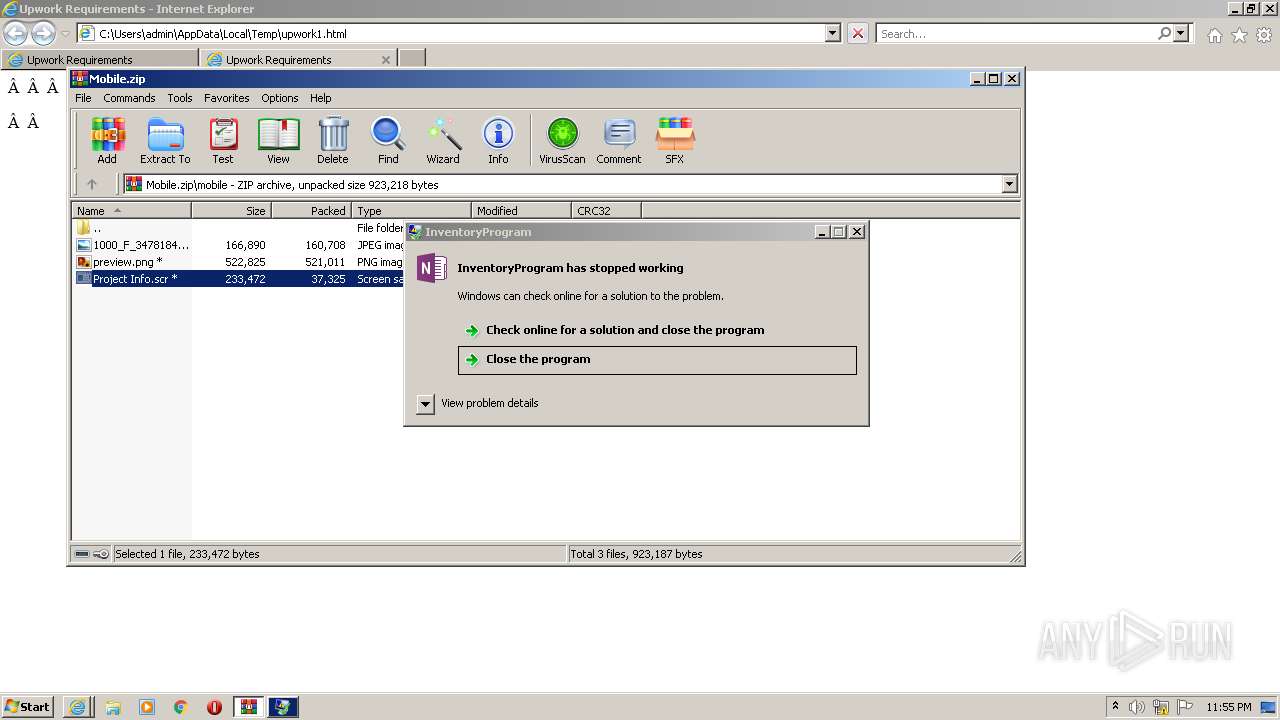
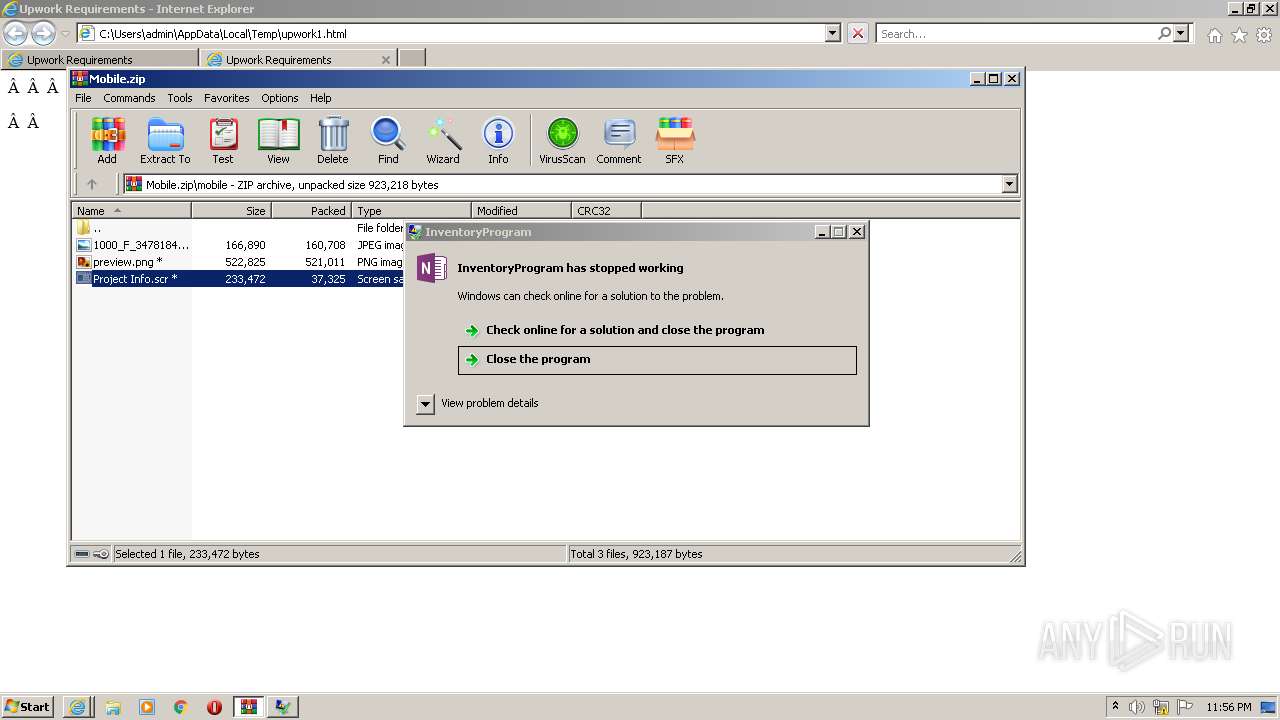
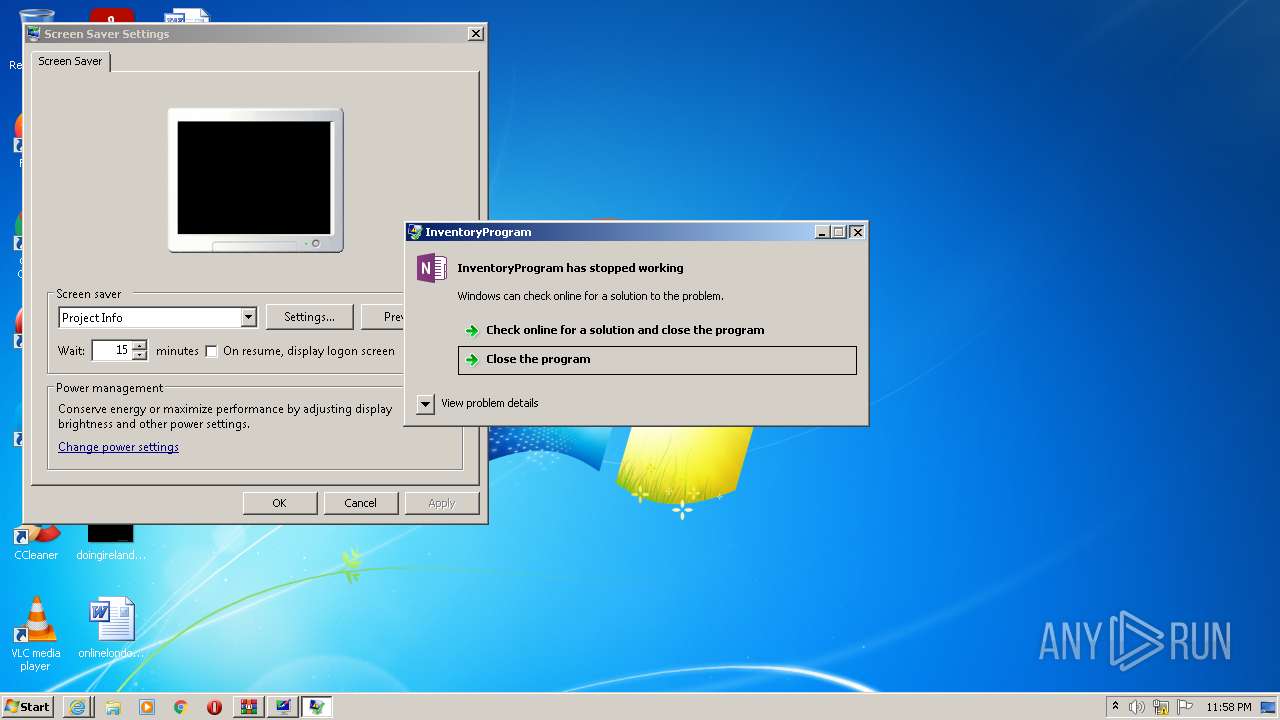
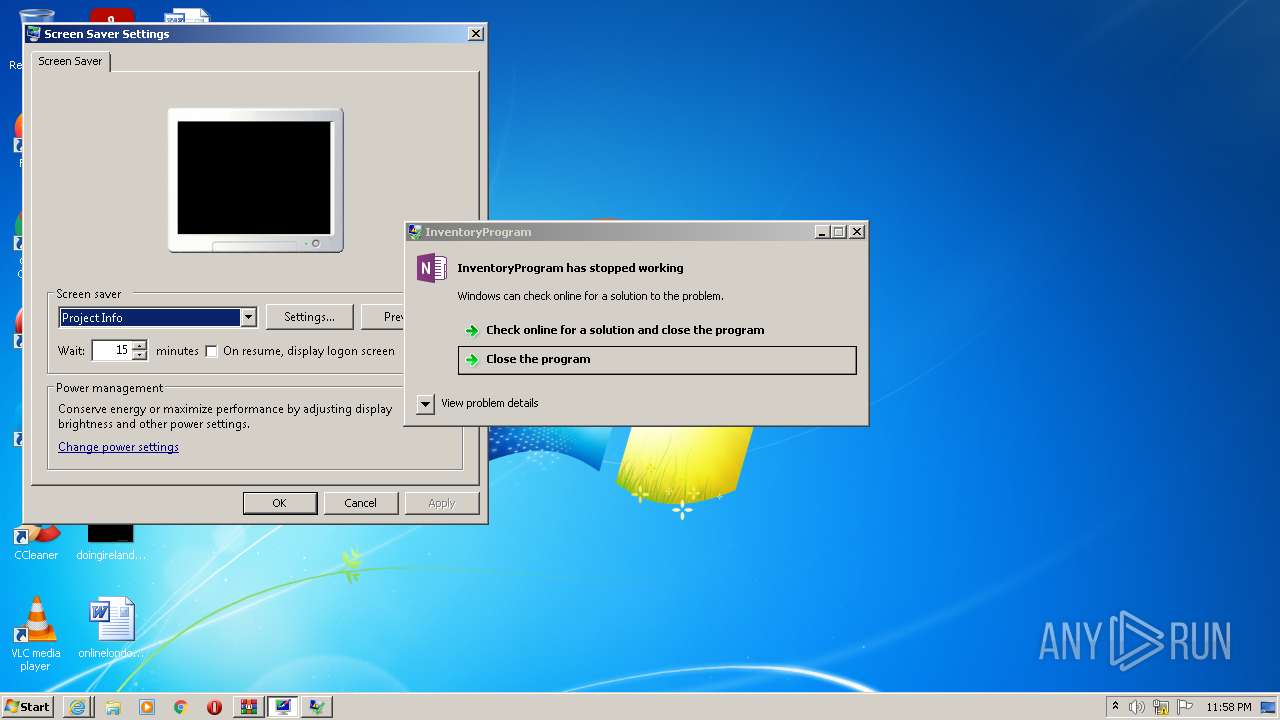
MALICIOUS
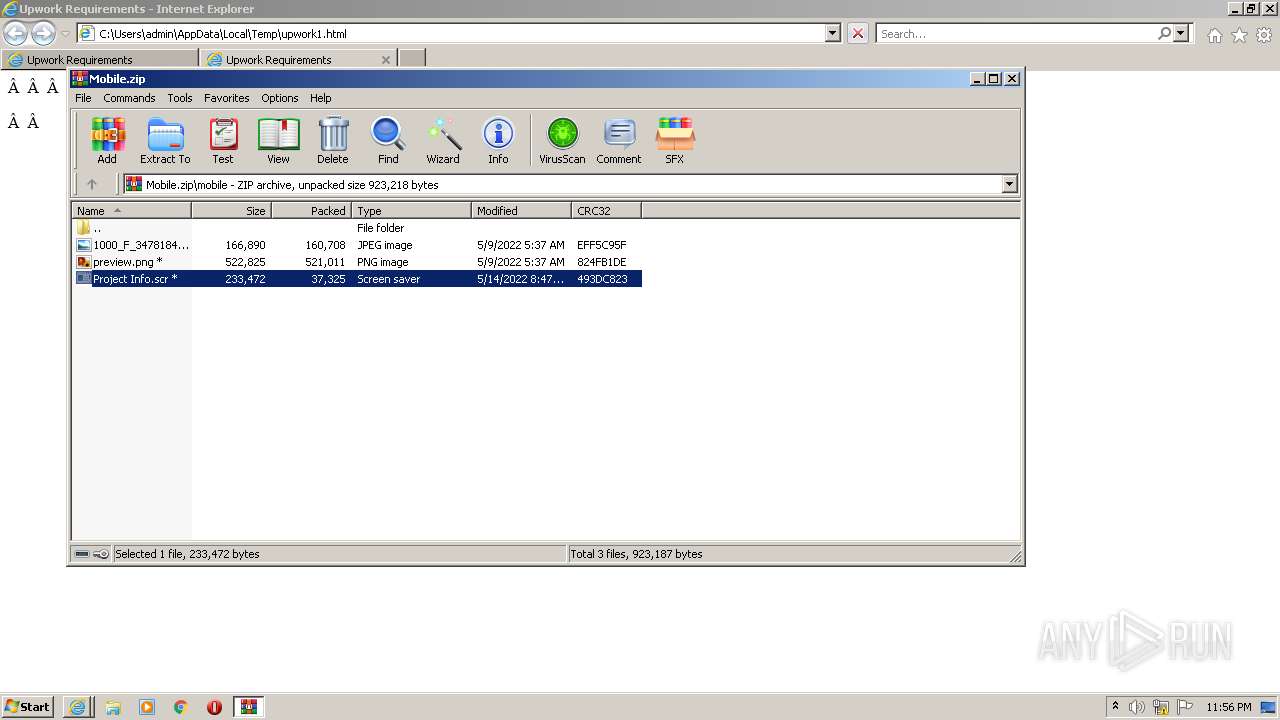
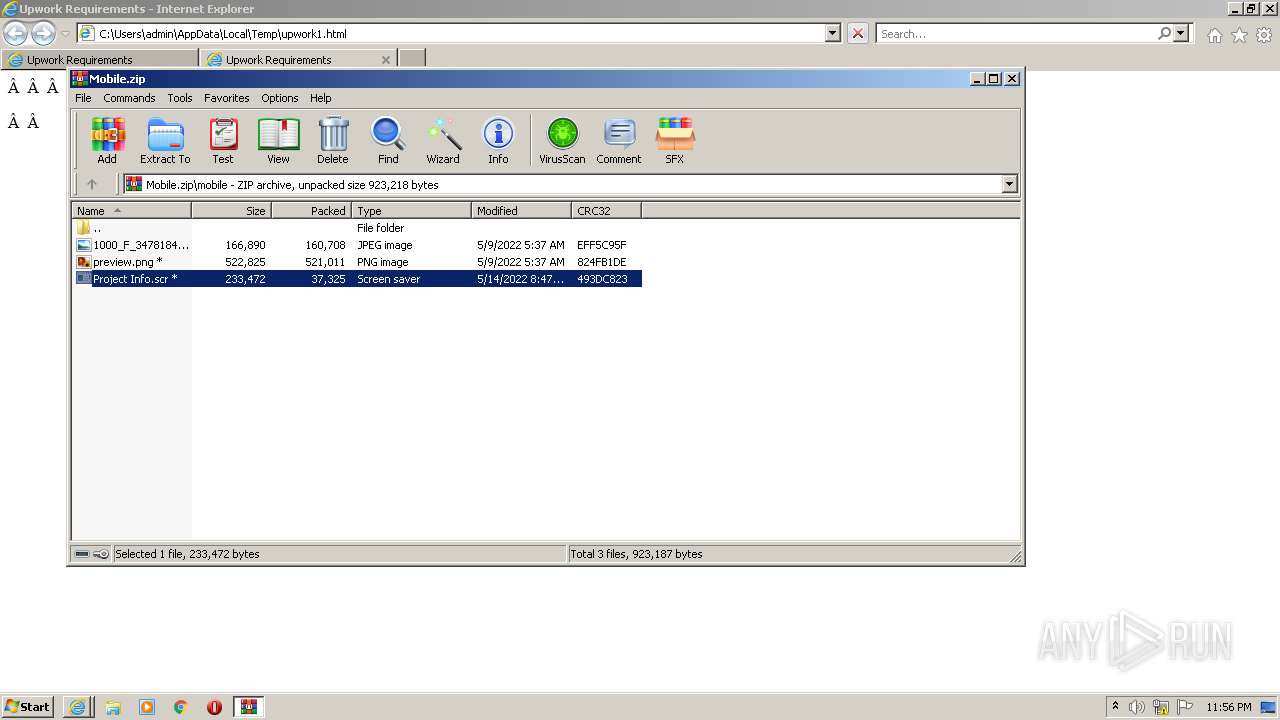
Drops executable file immediately after starts
- WinRAR.exe (PID: 2504)
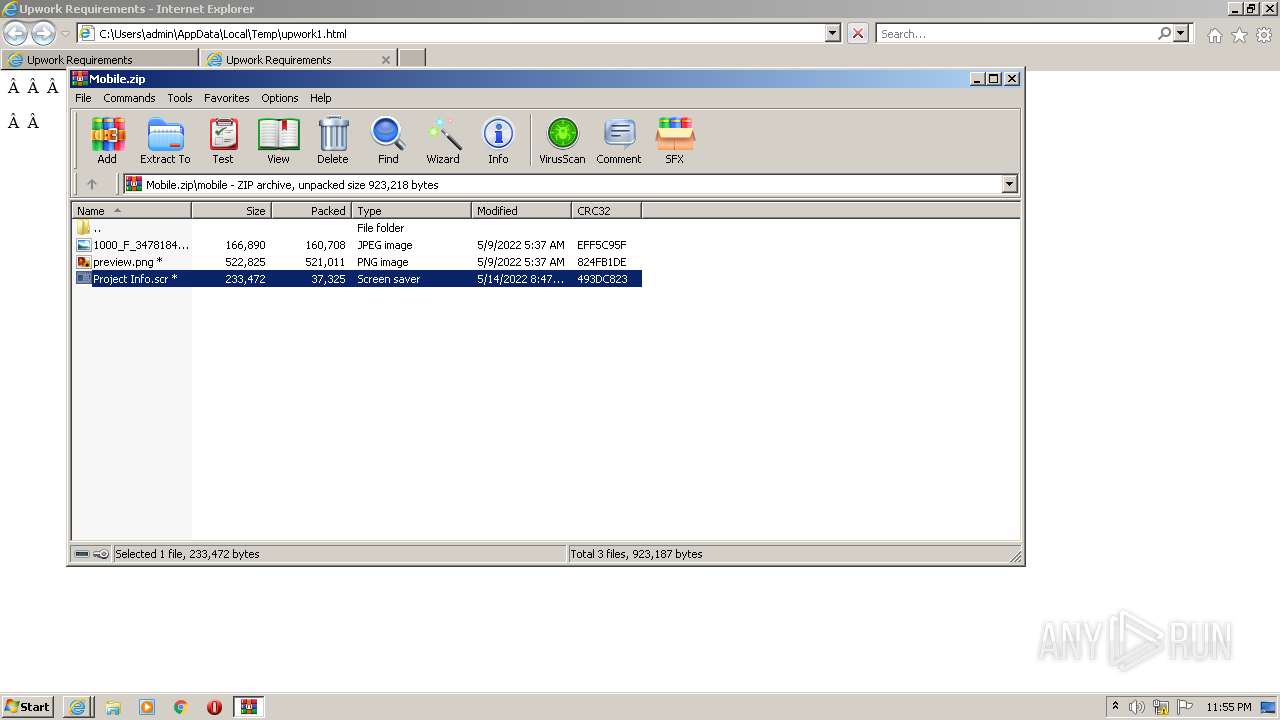
Application was dropped or rewritten from another process
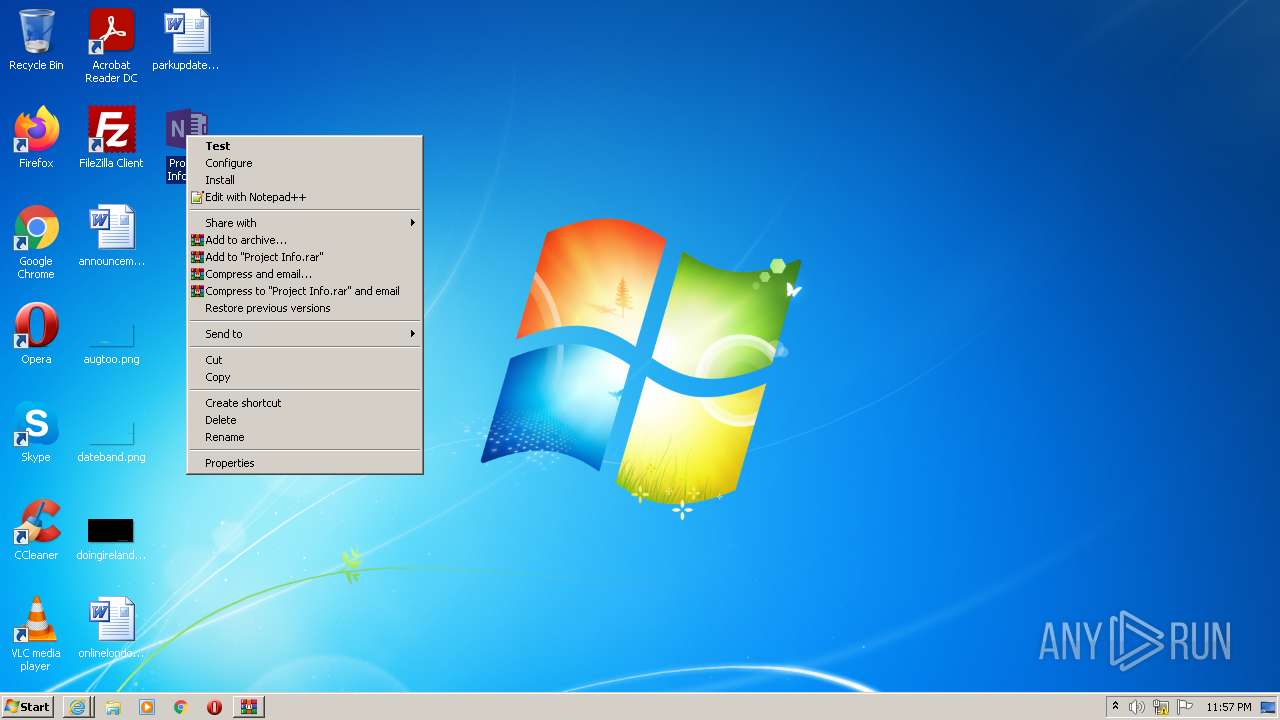
- Project Info.scr (PID: 1740)
- Project Info.scr (PID: 4068)
- Project Info.scr (PID: 2384)
- Project Info.scr (PID: 2184)
- Project Info.scr (PID: 3752)
- Project Info.scr (PID: 3156)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1048)
- iexplore.exe (PID: 3464)
- iexplore.exe (PID: 740)
Reads the computer name
- WinRAR.exe (PID: 2504)
- Project Info.scr (PID: 2384)
- Project Info.scr (PID: 1740)
- Project Info.scr (PID: 2184)
- Project Info.scr (PID: 3752)
- Project Info.scr (PID: 4068)
- Project Info.scr (PID: 3156)
Checks supported languages
- WinRAR.exe (PID: 2504)
- Project Info.scr (PID: 2384)
- Project Info.scr (PID: 1740)
- Project Info.scr (PID: 2184)
- Project Info.scr (PID: 3752)
- Project Info.scr (PID: 4068)
- Project Info.scr (PID: 3156)
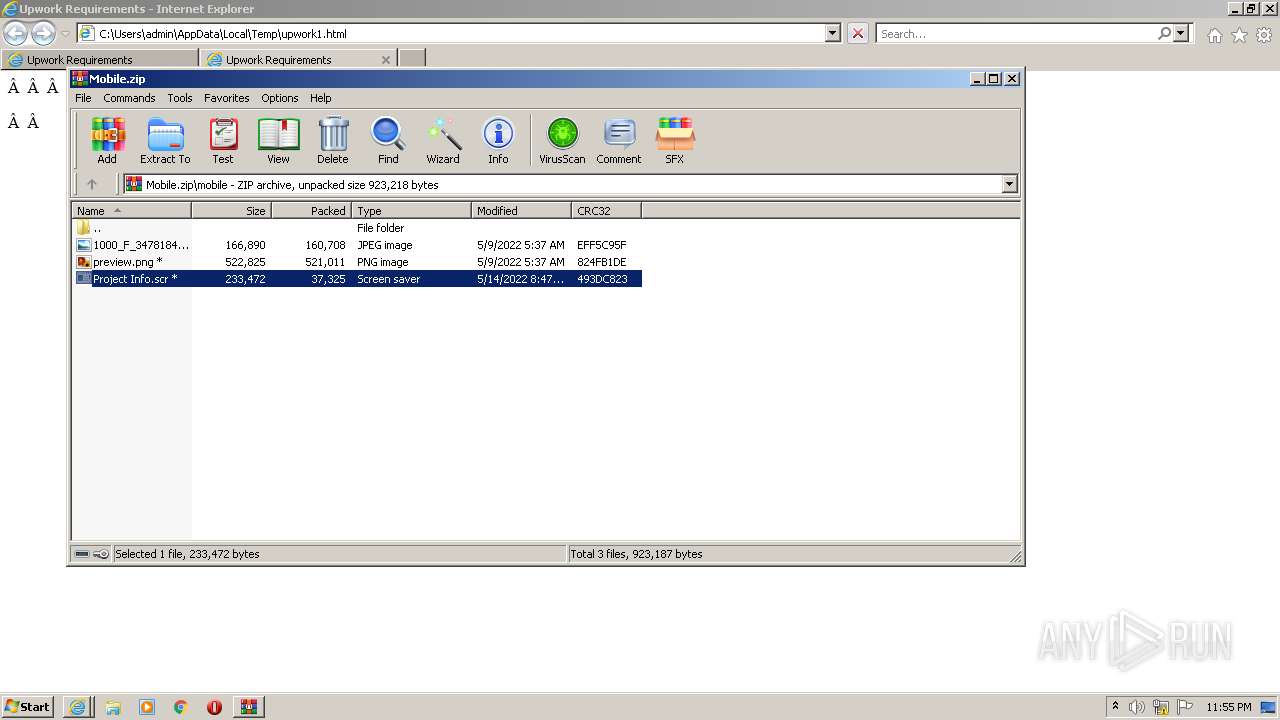
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2504)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2504)
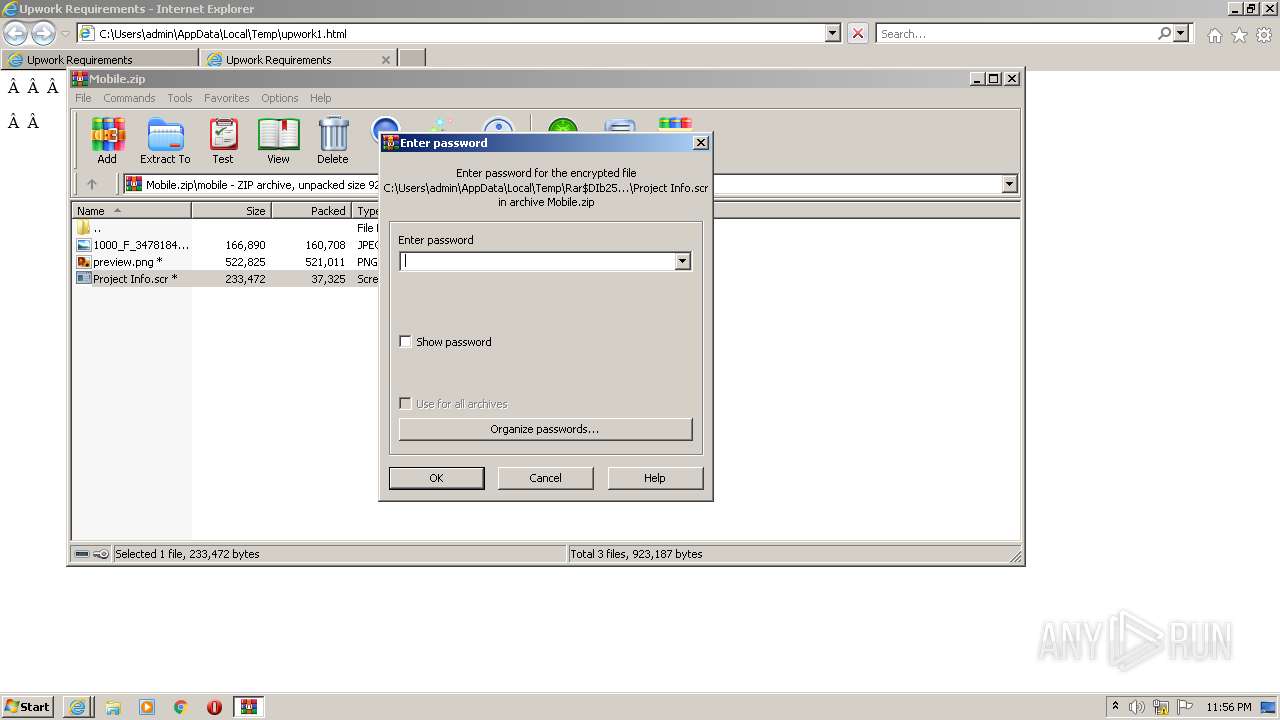
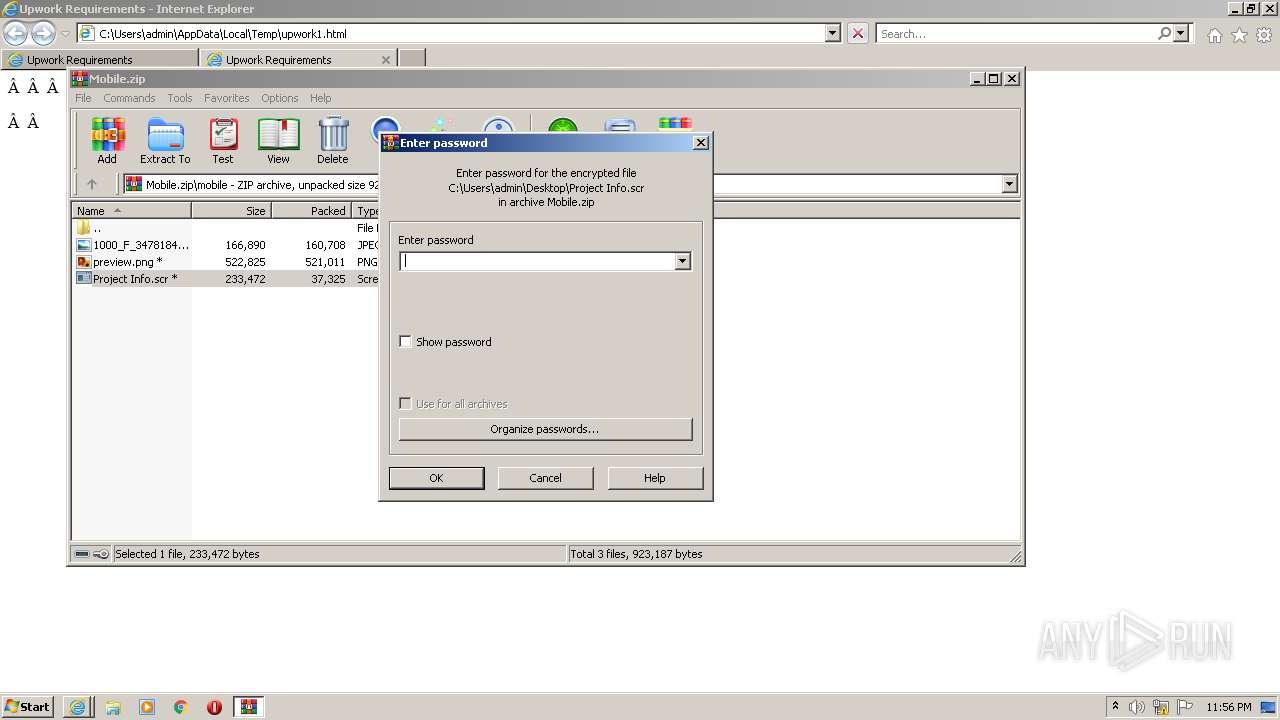
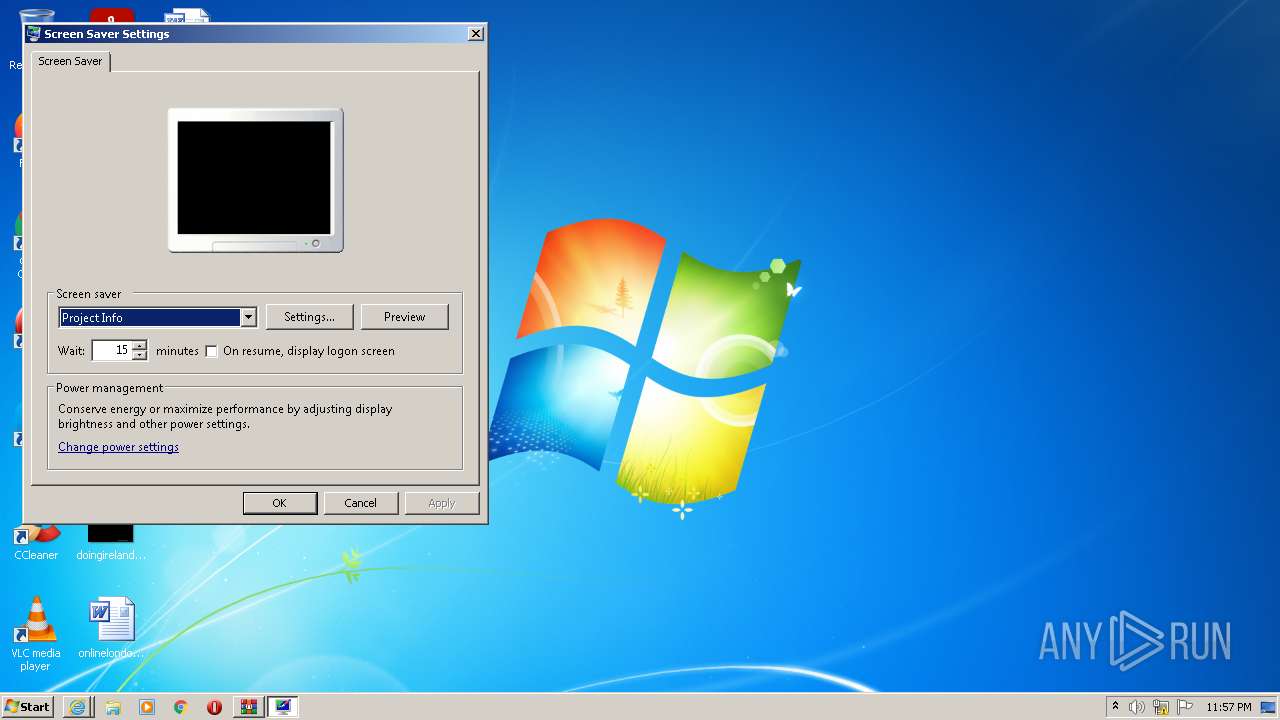
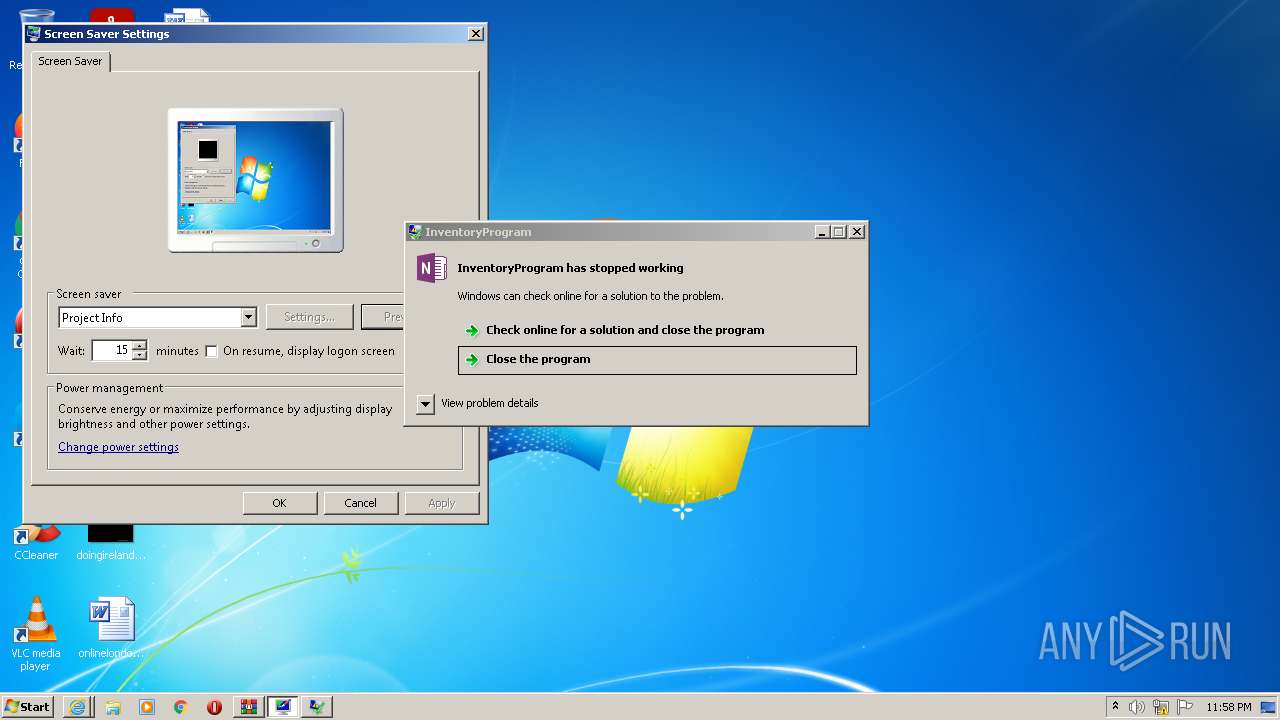
Starts application with an unusual extension
- WinRAR.exe (PID: 2504)
- rundll32.exe (PID: 3356)
Reads Environment values
- Project Info.scr (PID: 1740)
- Project Info.scr (PID: 2384)
- Project Info.scr (PID: 2184)
- Project Info.scr (PID: 3752)
- Project Info.scr (PID: 4068)
- Project Info.scr (PID: 3156)
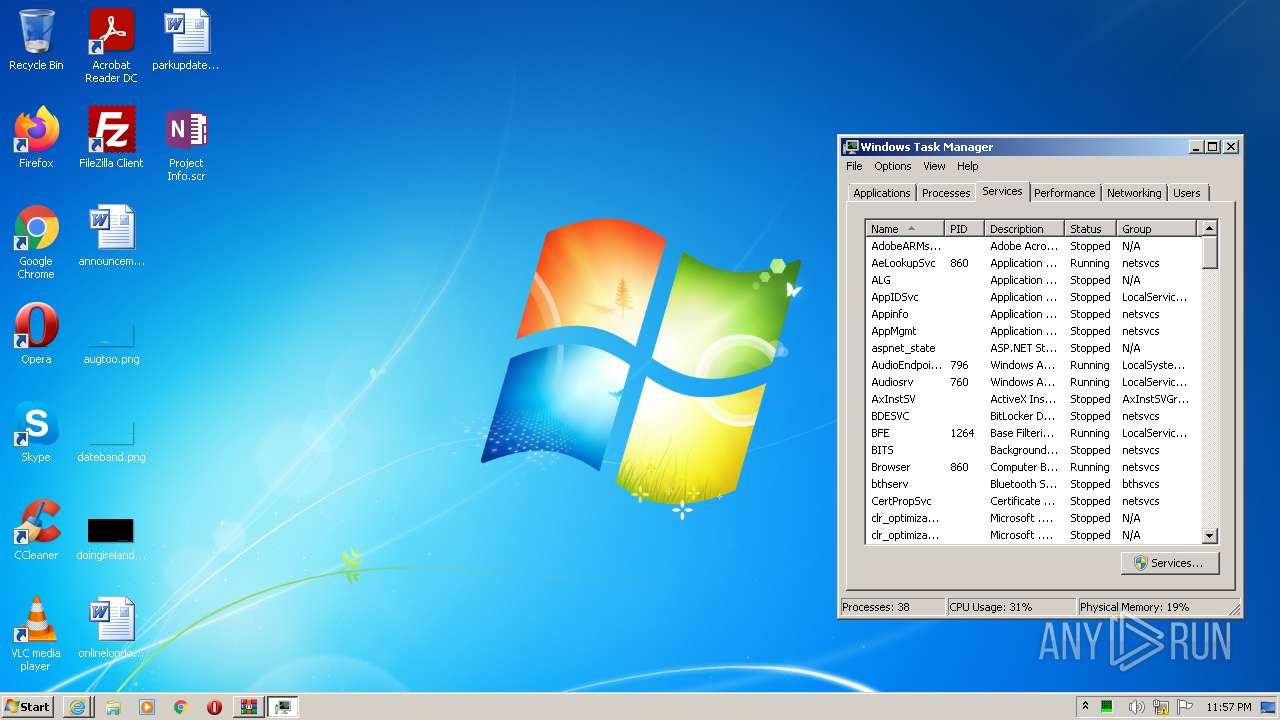
INFO
Application launched itself
- iexplore.exe (PID: 1636)
- iexplore.exe (PID: 1048)
Checks supported languages
- iexplore.exe (PID: 1636)
- iexplore.exe (PID: 1048)
- iexplore.exe (PID: 740)
- iexplore.exe (PID: 3464)
- taskmgr.exe (PID: 2296)
- rundll32.exe (PID: 3356)
Changes internet zones settings
- iexplore.exe (PID: 1636)
Reads the computer name
- iexplore.exe (PID: 1636)
- iexplore.exe (PID: 1048)
- iexplore.exe (PID: 740)
- iexplore.exe (PID: 3464)
- taskmgr.exe (PID: 2296)
- rundll32.exe (PID: 3356)
Reads internet explorer settings
- iexplore.exe (PID: 1048)
- iexplore.exe (PID: 3464)
Checks Windows Trust Settings
- iexplore.exe (PID: 740)
- iexplore.exe (PID: 1636)
- iexplore.exe (PID: 3464)
- iexplore.exe (PID: 1048)
Reads settings of System Certificates
- iexplore.exe (PID: 740)
- iexplore.exe (PID: 1636)
- Project Info.scr (PID: 2384)
- iexplore.exe (PID: 1048)
- Project Info.scr (PID: 1740)
- iexplore.exe (PID: 3464)
- Project Info.scr (PID: 2184)
- Project Info.scr (PID: 4068)
- Project Info.scr (PID: 3156)
- Project Info.scr (PID: 3752)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1636)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1636)
Creates files in the user directory
- iexplore.exe (PID: 1636)
Changes settings of System certificates
- iexplore.exe (PID: 1636)
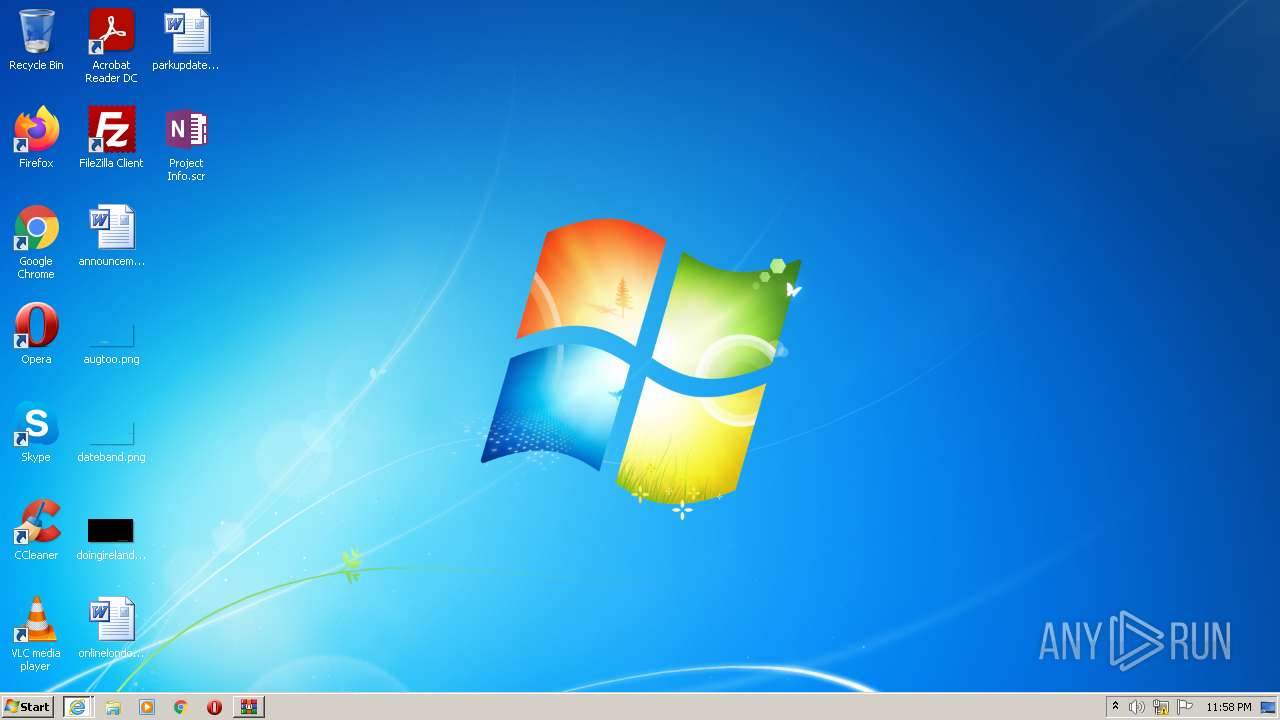
Manual execution by user
- Project Info.scr (PID: 4068)
- rundll32.exe (PID: 3356)
- taskmgr.exe (PID: 2296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
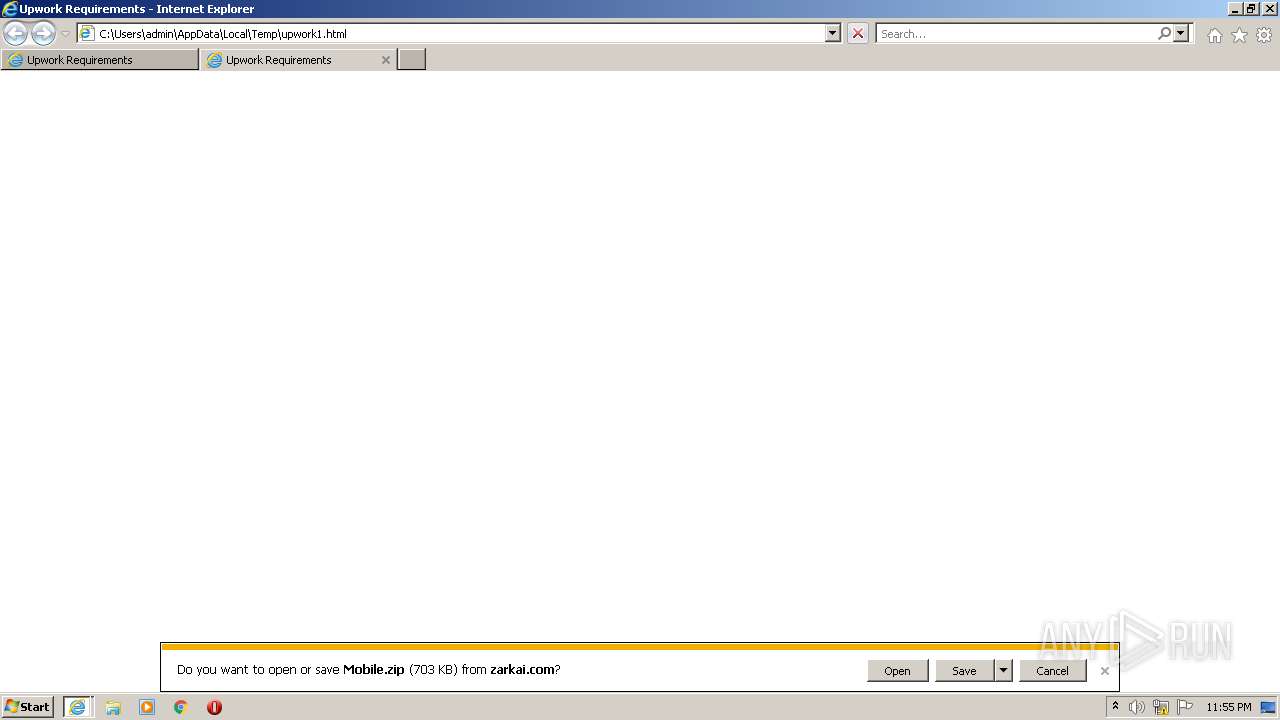
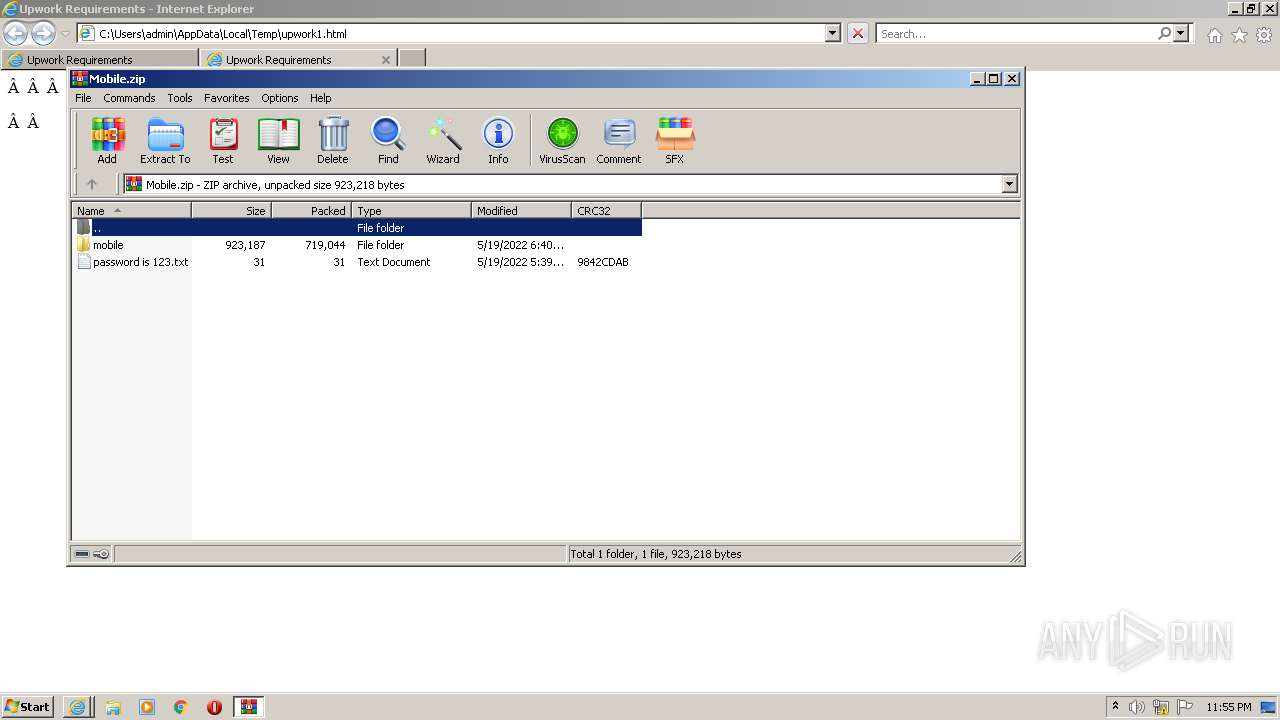
| Refresh: | 2; url = https://zarkai.com/upwork1/Mobile.zip |
|---|---|
| Title: | Upwork Requirements |
Total processes
57
Monitored processes
13
Malicious processes
5
Suspicious processes
4
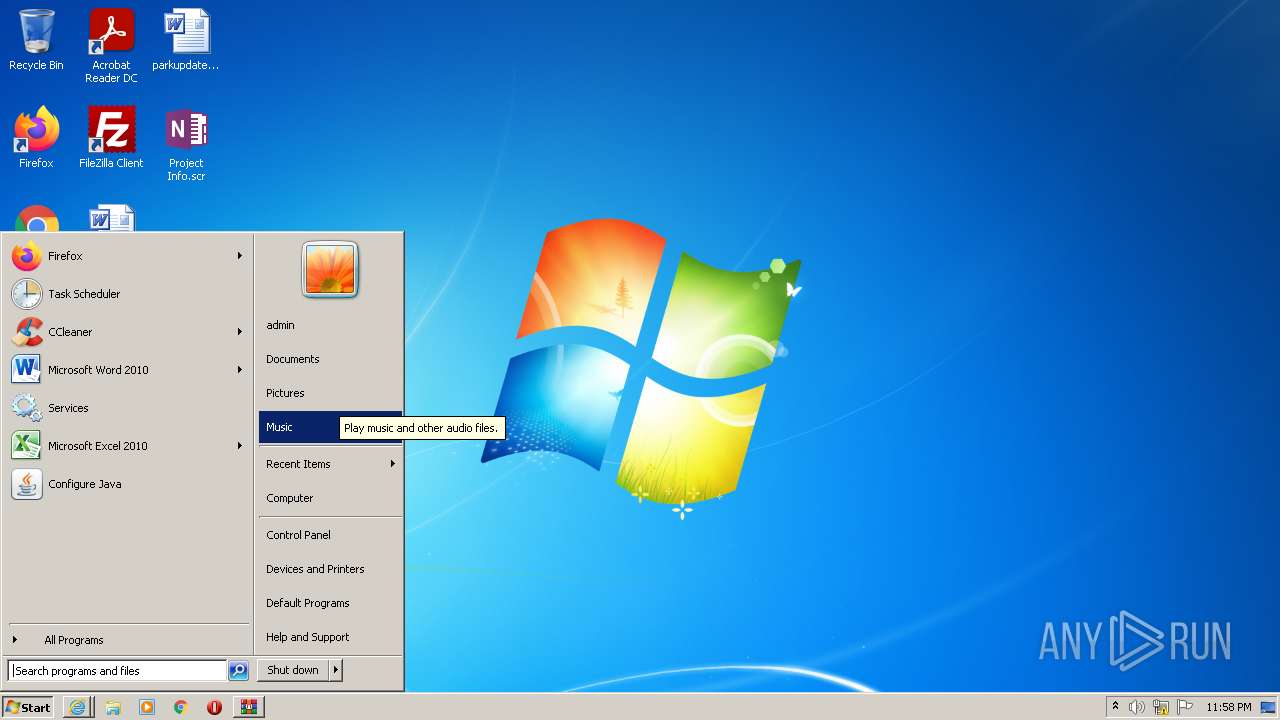
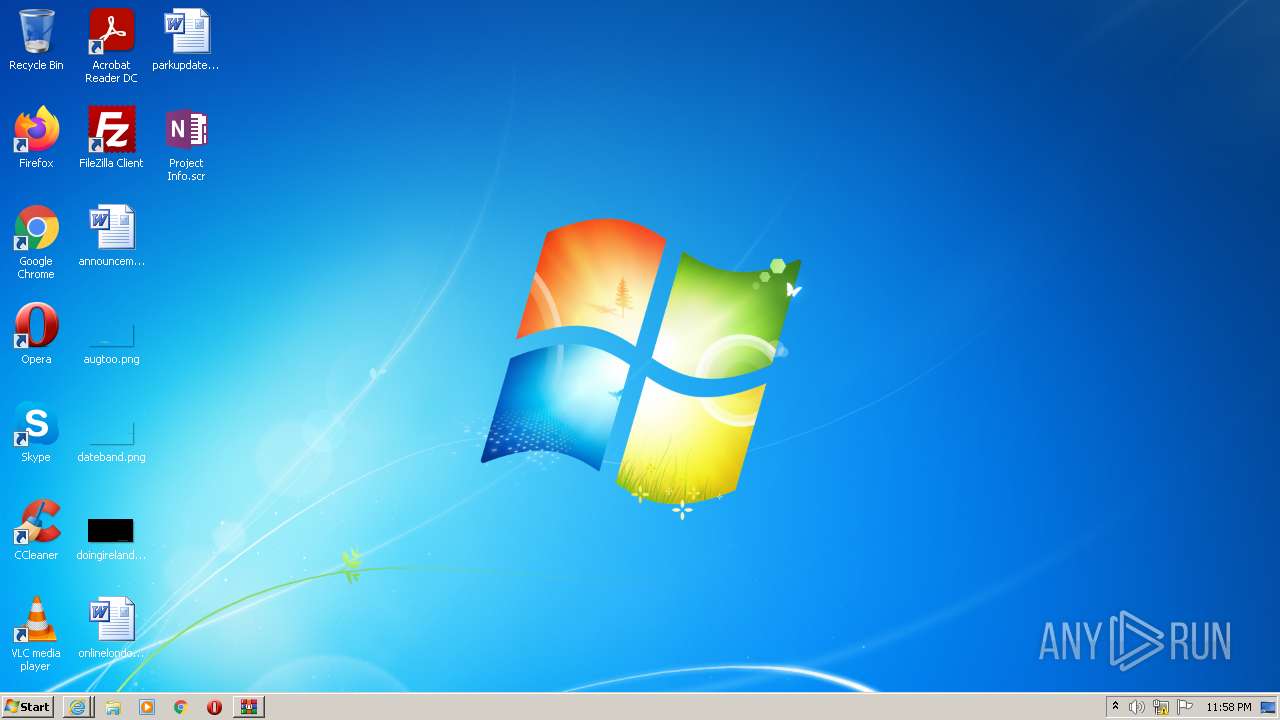
Behavior graph
Click at the process to see the details
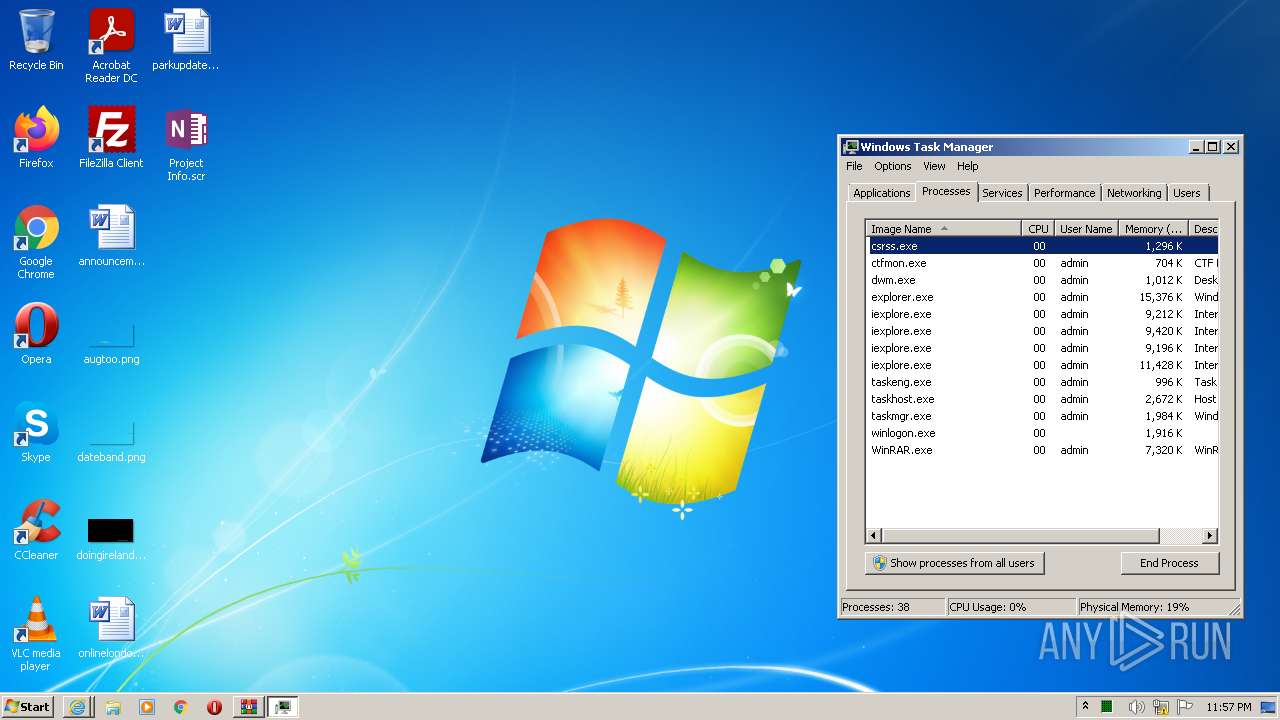
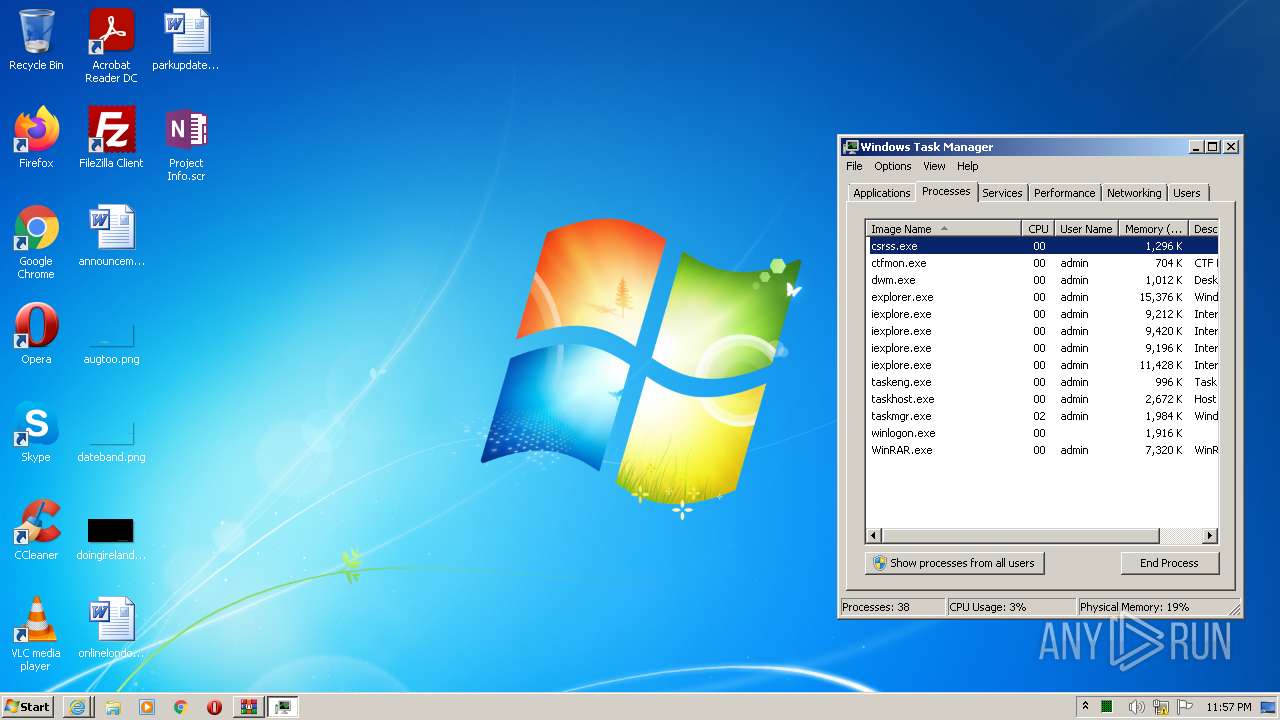
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 740 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1636 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1636 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\AppData\Local\Temp\upwork1.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
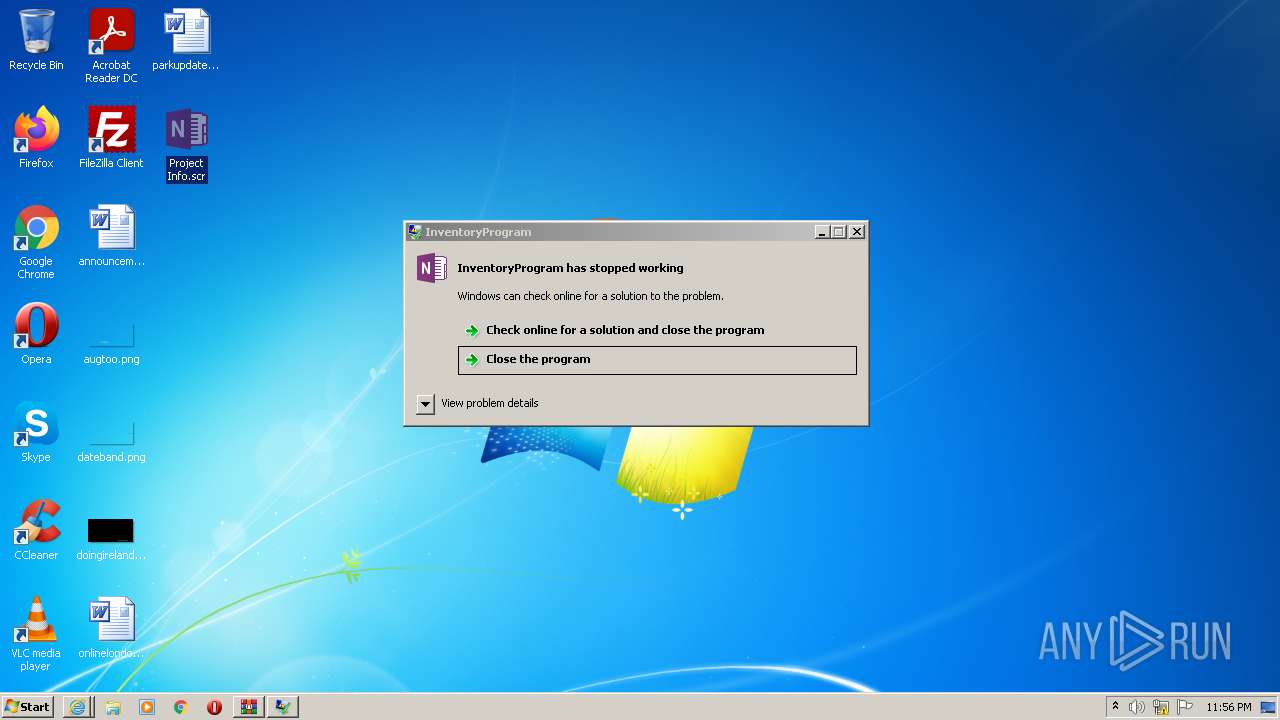
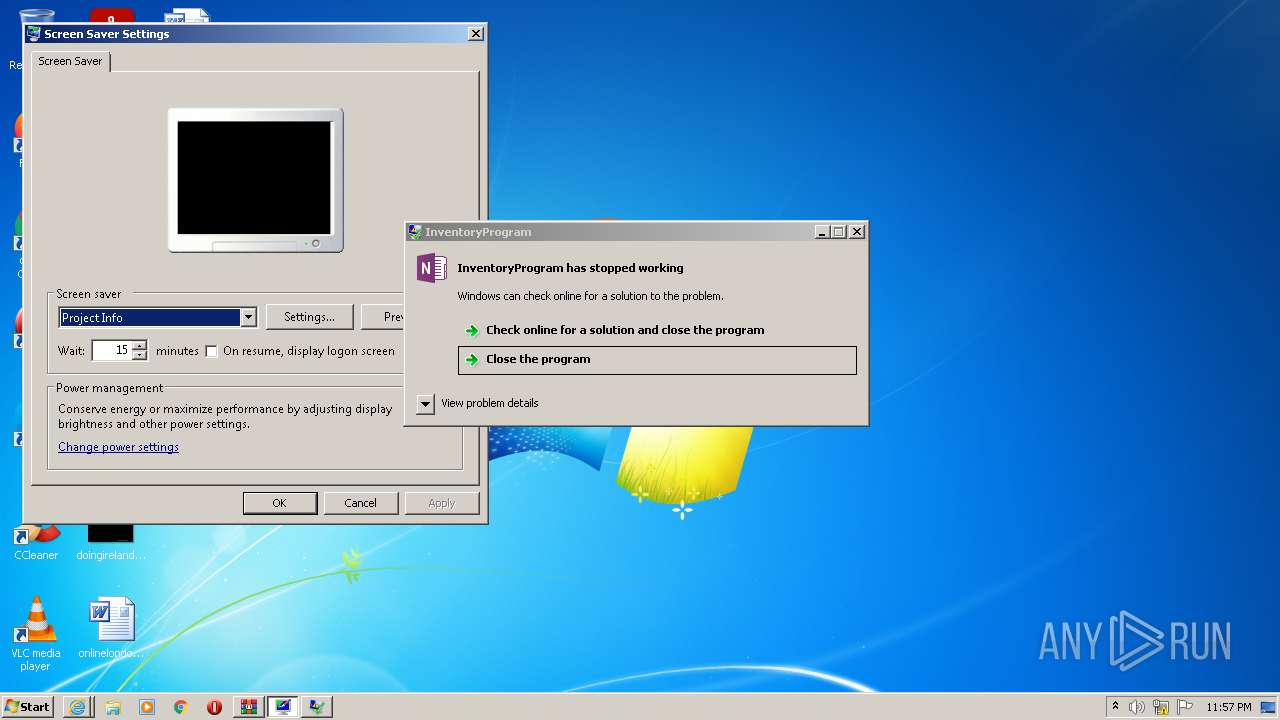
| 1740 | "C:\Users\admin\AppData\Local\Temp\Rar$DIb2504.2136\Project Info.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIb2504.2136\Project Info.scr | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: InventoryProgram Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2184 | "C:\Users\admin\Desktop\Project Info.scr" /p 131806 | C:\Users\admin\Desktop\Project Info.scr | rundll32.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: InventoryProgram Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2296 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\Rar$DIb2504.49539\Project Info.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIb2504.49539\Project Info.scr | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: InventoryProgram Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
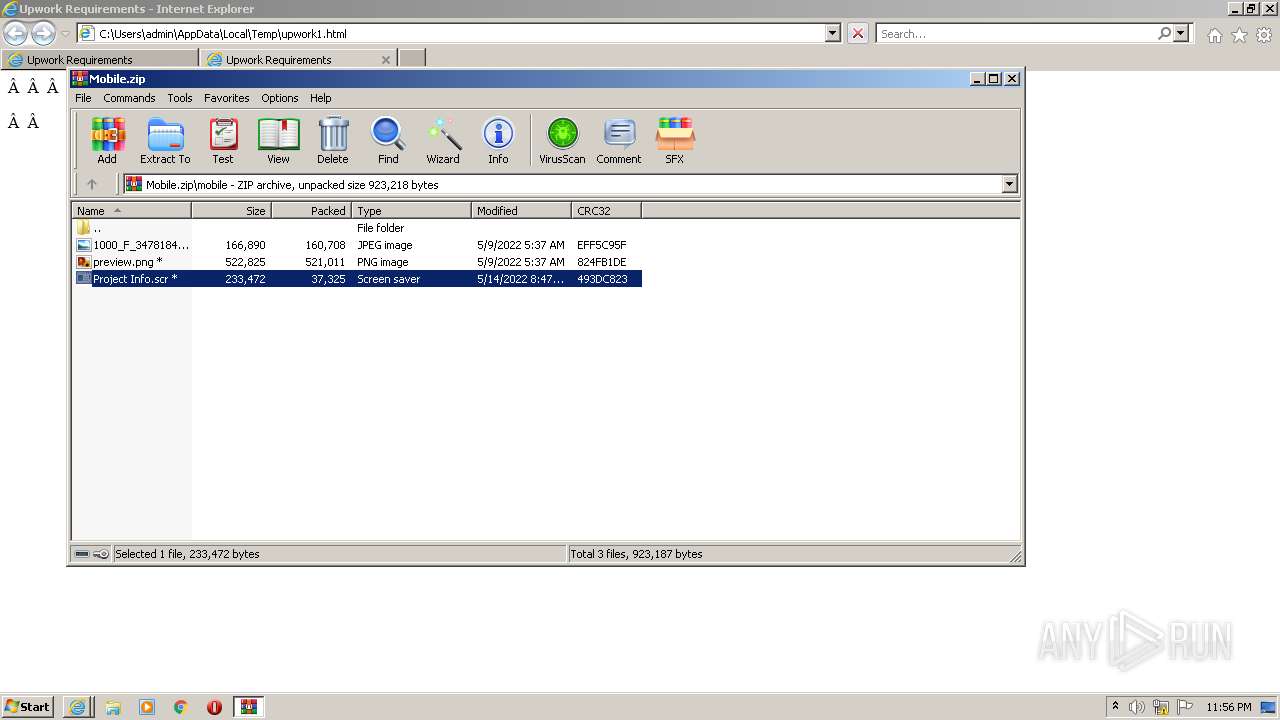
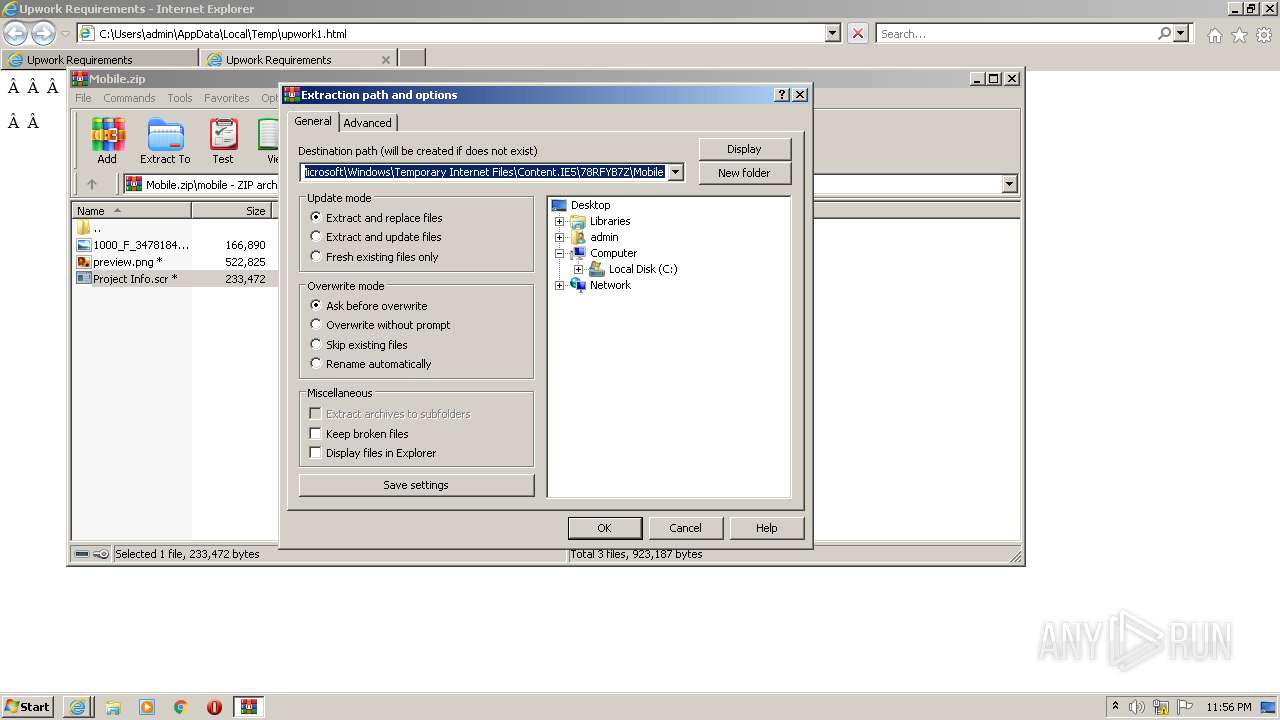
| 2504 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Mobile.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3156 | "C:\Users\admin\Desktop\Project Info.scr" /p 131806 | C:\Users\admin\Desktop\Project Info.scr | rundll32.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: InventoryProgram Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3356 | "rundll32.exe" desk.cpl,InstallScreenSaver C:\Users\admin\Desktop\Project Info.scr | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
42 506
Read events
42 071
Write events
433
Delete events
2
Modification events
| (PID) Process: | (1636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960796 | |||
| (PID) Process: | (1636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960796 | |||
| (PID) Process: | (1636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
18
Text files
19
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 740 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_2DBE917624E9880FE0C7C5570D56E691 | binary | |
MD5:— | SHA256:— | |||
| 740 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Mobile[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 740 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5080DC7A65DB6A5960ECD874088F3328_862BA1770B2FEE013603D2FF9ABEAFDA | binary | |
MD5:— | SHA256:— | |||
| 740 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 740 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_2DBE917624E9880FE0C7C5570D56E691 | der | |
MD5:— | SHA256:— | |||
| 740 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5080DC7A65DB6A5960ECD874088F3328_862BA1770B2FEE013603D2FF9ABEAFDA | der | |
MD5:— | SHA256:— | |||
| 1636 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFF8B7C2796720A54.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{EB3FC759-D88F-11EC-B7B7-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 740 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Mobile[2].zip | compressed | |
MD5:— | SHA256:— | |||
| 1636 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7151732EBE8BB8E5.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
27
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
740 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEQDwHUvue3yjezwFZqwFlyRY | US | der | 728 b | whitelisted |
740 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
1636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
1636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
740 | iexplore.exe | GET | 200 | 2.16.107.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?441bcdd83adb9857 | unknown | compressed | 4.70 Kb | whitelisted |
740 | iexplore.exe | GET | 200 | 2.16.107.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?167c331ed0f98cfa | unknown | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
740 | iexplore.exe | 95.111.231.140:443 | zarkai.com | Intertelecom Ltd | UA | unknown |
740 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
1636 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1636 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1636 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2384 | Project Info.scr | 180.188.192.80:443 | burgercircus.com.hk | i-System Technology Limited | HK | unknown |
1048 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1740 | Project Info.scr | 180.188.192.80:443 | burgercircus.com.hk | i-System Technology Limited | HK | unknown |
3464 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1636 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zarkai.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
burgercircus.com.hk |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |