| File name: | setup_3544811250.exe |
| Full analysis: | https://app.any.run/tasks/d9150b79-776a-4df5-94e4-cbcad869400f |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 00:29:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DCF010124C8FA738C2A859E829FD70E1 |
| SHA1: | 85085569CC4AB05D13640E8F732725D9DB3CEC37 |
| SHA256: | 9BA6AC61D927A8C13F207EBE46465E9BB3318A43EDD3AC52E72BF75489619F34 |
| SSDEEP: | 49152:ZGp1QMaJqiHnYN8bwEvKq8oTgdttARFU+RzO0+HZ6L:aQLIICqN4jAzU+hO0qM |
MALICIOUS
Loads dropped or rewritten executable
- setup_3544811250.exe (PID: 2544)
SUSPICIOUS
Reads Environment values
- setup_3544811250.exe (PID: 2544)
Application launched itself
- setup_3544811250.exe (PID: 3896)
Executable content was dropped or overwritten
- setup_3544811250.exe (PID: 2544)
Reads internet explorer settings
- setup_3544811250.exe (PID: 2544)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:09 10:48:22+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 60416 |
| InitializedDataSize: | 52736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf3bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.7.4.6 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Hosubom Setup |
| FileVersion: | 2.7.4.6 |
| LegalCopyright: | |
| ProductName: | Hosubom |
| ProductVersion: | 1.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Oct-2012 08:48:22 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Hosubom Setup |
| FileVersion: | 2.7.4.6 |
| LegalCopyright: | - |
| ProductName: | Hosubom |
| ProductVersion: | 1.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 09-Oct-2012 08:48:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000DE64 | 0x0000E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45507 |
.itext | 0x0000F000 | 0x00000B2C | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.68265 |
.data | 0x00010000 | 0x00000C84 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.23598 |
.bss | 0x00011000 | 0x000056B0 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00017000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.89082 |
.tls | 0x00018000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00019000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001A000 | 0x0000B000 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14243 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08452 | 1444 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2544 | "C:\Users\admin\AppData\Local\Temp\setup_3544811250.exe" RSF /ppn:YyhwYgxaFRAiP211FM5W /mnl | C:\Users\admin\AppData\Local\Temp\setup_3544811250.exe | setup_3544811250.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Hosubom Setup Exit code: 0 Version: 2.7.4.6 Modules
| |||||||||||||||
| 3896 | "C:\Users\admin\AppData\Local\Temp\setup_3544811250.exe" | C:\Users\admin\AppData\Local\Temp\setup_3544811250.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Hosubom Setup Exit code: 0 Version: 2.7.4.6 Modules
| |||||||||||||||
Total events
497
Read events
470
Write events
27
Delete events
0
Modification events
| (PID) Process: | (3896) setup_3544811250.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3896) setup_3544811250.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2544) setup_3544811250.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2544) setup_3544811250.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2544) setup_3544811250.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2544) setup_3544811250.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2544) setup_3544811250.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2544) setup_3544811250.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2544) setup_3544811250.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: setup_3544811250.exe | |||
| (PID) Process: | (2544) setup_3544811250.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: 1349772502 | |||
Executable files
2
Suspicious files
8
Text files
79
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2544 | setup_3544811250.exe | C:\Users\admin\AppData\Local\Temp\00A6778A.log | — | |
MD5:— | SHA256:— | |||
| 2544 | setup_3544811250.exe | C:\Users\admin\AppData\Local\Temp\inH1090957831107\csshover3.htc | html | |
MD5:52FA0DA50BF4B27EE625C80D36C67941 | SHA256:E37E99DDFC73AC7BA774E23736B2EF429D9A0CB8C906453C75B14C029BDD5493 | |||
| 2544 | setup_3544811250.exe | C:\Users\admin\AppData\Local\Temp\inH1090957831107\css\main.scss | text | |
MD5:A85DEB7E401725C73E02464106F6501F | SHA256:3B5A044EF2BFF26A7D09AF66A3B8E102CF669BEDEEE65C127B46C4DC21EC344D | |||
| 2544 | setup_3544811250.exe | C:\Users\admin\AppData\Local\Temp\inH1090957831107\css\_helpers.scss | text | |
MD5:5F158DBBD9FC4594A2F6C13854501916 | SHA256:BF12B79F67F1CB9988797F7D81F6F504C8DFE0F0435482E64819A140DBC8DA14 | |||
| 2544 | setup_3544811250.exe | C:\Users\admin\AppData\Local\Temp\inH1090957831107\form.bmp.Mask | binary | |
MD5:D2FC989F9C2043CD32332EC0FAD69C70 | SHA256:27DD029405CBFB0C3BF8BAC517BE5DB9AA83E981B1DC2BD5C5D6C549FA514101 | |||
| 2544 | setup_3544811250.exe | C:\Users\admin\AppData\Local\Temp\inH1090957831107\css\main.css | text | |
MD5:CD50C111BCB785F12306BB72C5E926E2 | SHA256:86DD1310F16A1DAF0DCF0A05FE0C7937432A889B43D440BC1548C49314F9F05F | |||
| 2544 | setup_3544811250.exe | C:\Users\admin\AppData\Local\Temp\inH1090957831107\css\ie6_main.scss | text | |
MD5:D10348D17ADF8A90670696728F54562D | SHA256:E8A3D15CF32009B01B9145B6E62FF6CAA9C2981F81CE063578C73C7ADFF08DFC | |||
| 2544 | setup_3544811250.exe | C:\Users\admin\AppData\Local\Temp\inH1090957831107\css\_variables.scss | text | |
MD5:07922410C30F0117CBC3C140F14AEA88 | SHA256:AF1999B49C03F5DCBB19466466FAC2D8172C684C0FF18931B85A8D0A06332C73 | |||
| 2544 | setup_3544811250.exe | C:\Users\admin\AppData\Local\Temp\inH1090957831107\css\ie6_main.css | text | |
MD5:AD234E6A62580F62019C78B2A718DE00 | SHA256:C4F2684F16C8E4553CC29C604A2F505399039638A34E652A7A1ACDEB157A0861 | |||
| 2544 | setup_3544811250.exe | C:\Users\admin\AppData\Local\Temp\inH1090957831107\css\_functions.scss | text | |
MD5:8F7259DE64F6DDF352BF461F44D34A81 | SHA256:80EDC9D67172BC830D68D33F4547735FB072CADF3EF25AAB37A10B50DB87A069 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
15
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2544 | setup_3544811250.exe | HEAD | 200 | 192.96.201.161:80 | http://ww42.seginefmino.com/ofr/Niniwic/YL/Niniwic_Tefenece_12Apr16 | US | — | — | malicious |
2544 | setup_3544811250.exe | POST | 200 | 52.215.31.191:80 | http://bbs.seginefmino.com/ | IE | — | — | malicious |
2544 | setup_3544811250.exe | POST | 200 | 52.16.29.135:80 | http://www3.seginefmino.com/ | IE | text | 1.15 Kb | malicious |
2544 | setup_3544811250.exe | POST | 200 | 52.215.31.191:80 | http://bbs.seginefmino.com/ | IE | — | — | malicious |
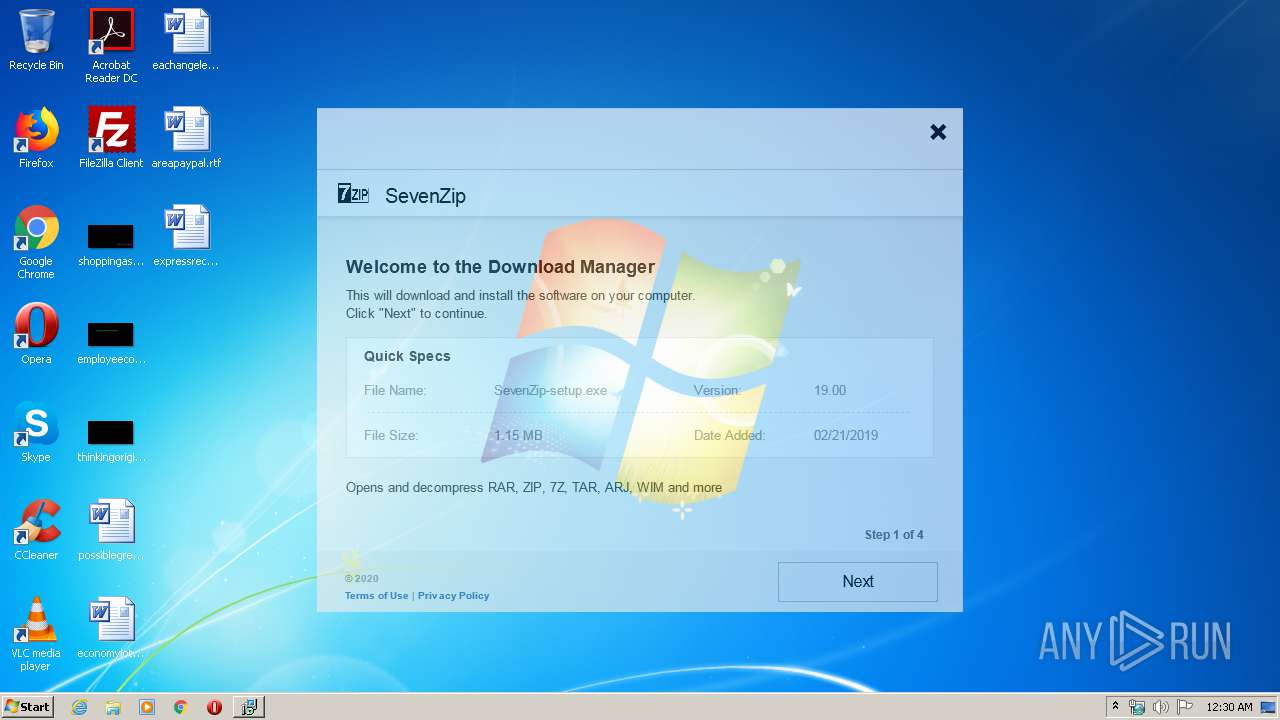
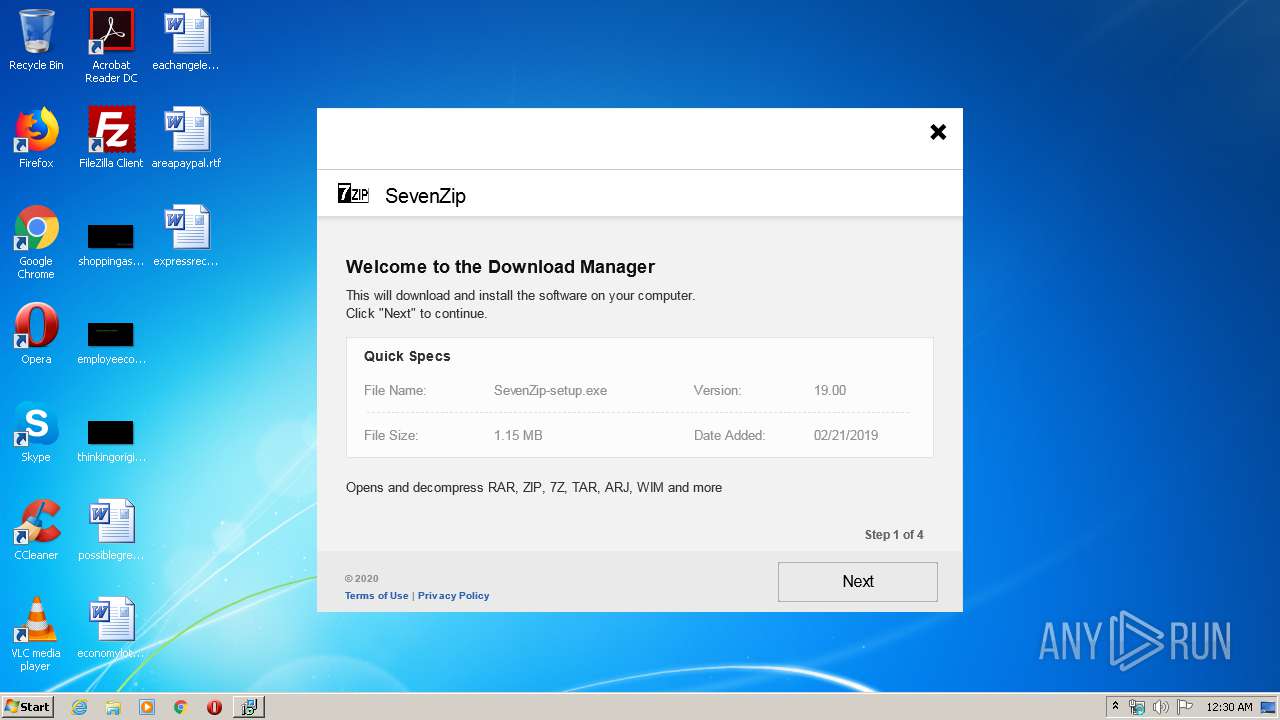
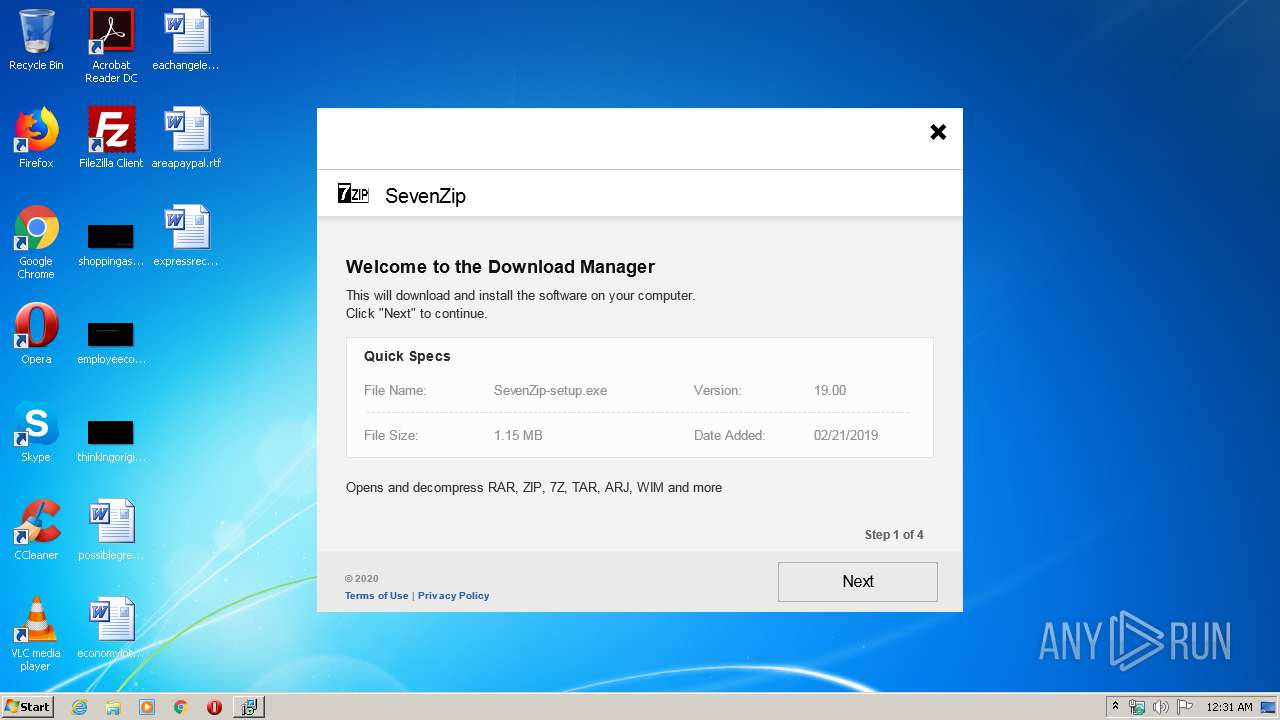
2544 | setup_3544811250.exe | GET | 200 | 46.21.100.252:80 | http://sevenzip.net/img/sevenzip.png | US | image | 12.7 Kb | malicious |
2544 | setup_3544811250.exe | POST | 200 | 52.212.215.62:80 | http://api.seginefmino.com/ | IE | binary | 860 Kb | malicious |
2544 | setup_3544811250.exe | GET | 200 | 192.96.201.161:80 | http://ww42.seginefmino.com/img/Sibarasawi/bg_comp.png | US | image | 25.2 Kb | malicious |
2544 | setup_3544811250.exe | GET | 200 | 192.96.201.161:80 | http://ww42.seginefmino.com/img/Tavasat/15Feb17/v2/EN.png | US | image | 43.9 Kb | malicious |
2544 | setup_3544811250.exe | GET | 200 | 192.96.201.161:80 | http://ww42.seginefmino.com/ofr/Niniwic/YL/Niniwic_Tefenece_12Apr16 | US | binary | 8.93 Kb | malicious |
2544 | setup_3544811250.exe | POST | 200 | 52.215.31.191:80 | http://bbs.seginefmino.com/ | IE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2544 | setup_3544811250.exe | 52.215.31.191:80 | bbs.seginefmino.com | Amazon.com, Inc. | IE | malicious |
— | — | 52.16.29.135:80 | www3.seginefmino.com | Amazon.com, Inc. | IE | malicious |
— | — | 46.21.100.252:80 | sevenzip.net | GleSYS Internet Services AB | US | malicious |
2544 | setup_3544811250.exe | 52.212.215.62:80 | api.seginefmino.com | Amazon.com, Inc. | IE | malicious |
2544 | setup_3544811250.exe | 192.96.201.161:80 | ww42.seginefmino.com | Leaseweb USA, Inc. | US | malicious |
2544 | setup_3544811250.exe | 85.159.237.103:80 | www4.seginefmino.com | NForce Entertainment B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bbs.seginefmino.com |
| malicious |
www3.seginefmino.com |
| malicious |
sevenzip.net |
| malicious |
api.seginefmino.com |
| malicious |
ww42.seginefmino.com |
| malicious |
www4.seginefmino.com |
| malicious |