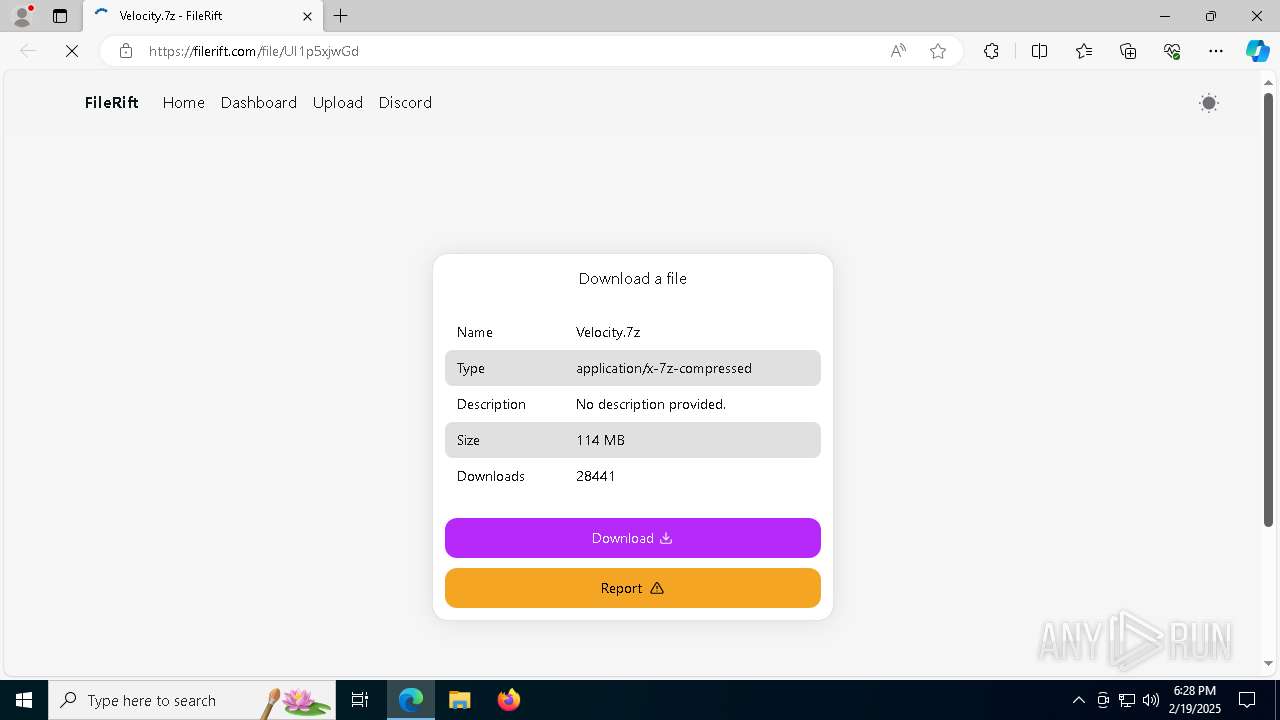
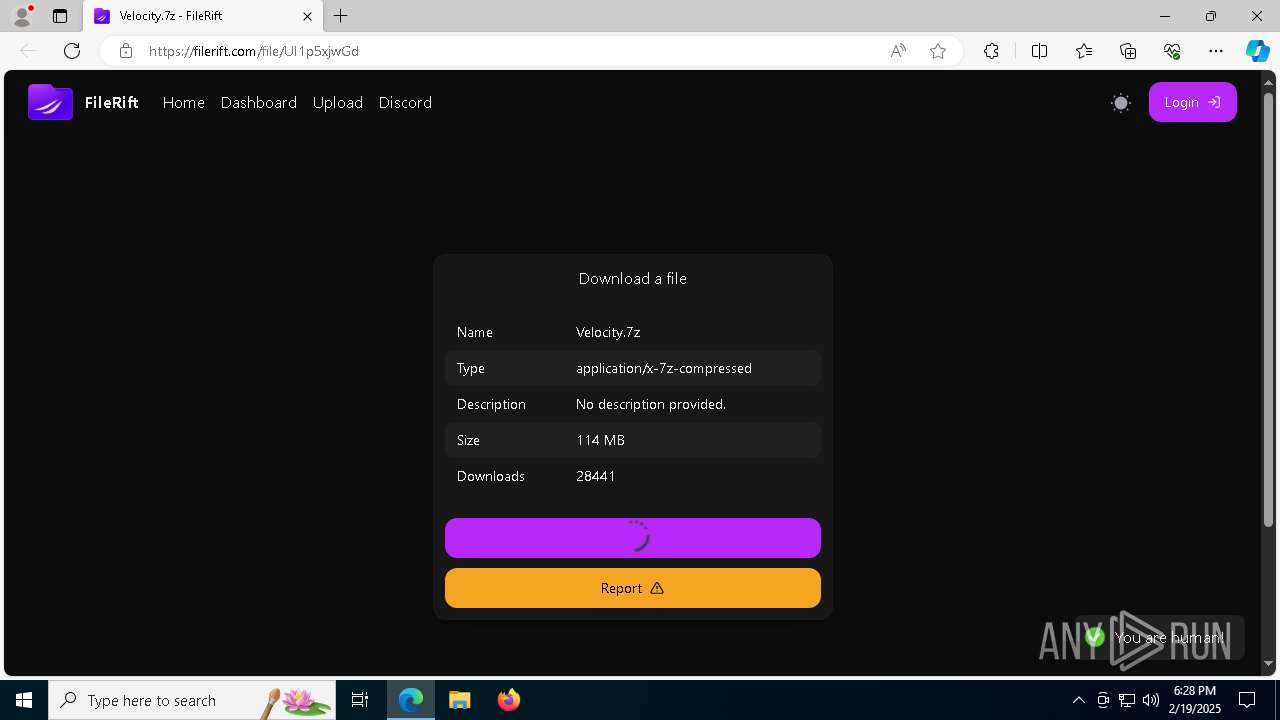
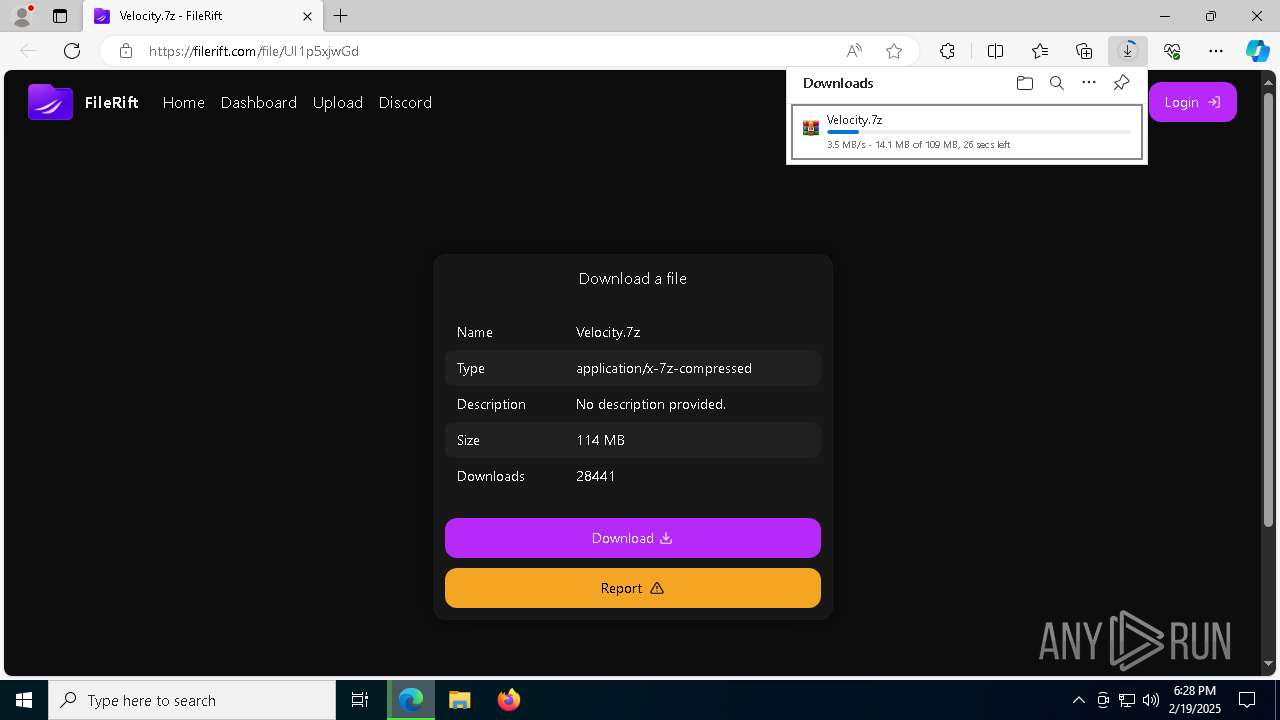
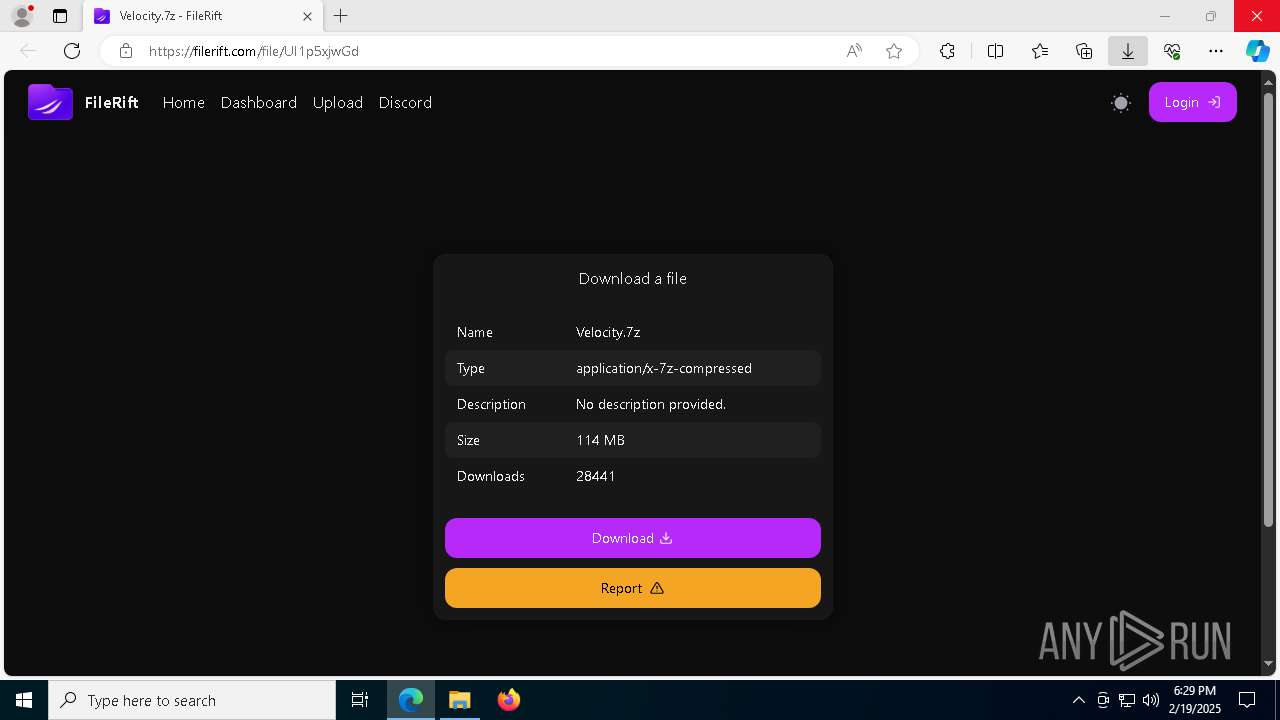
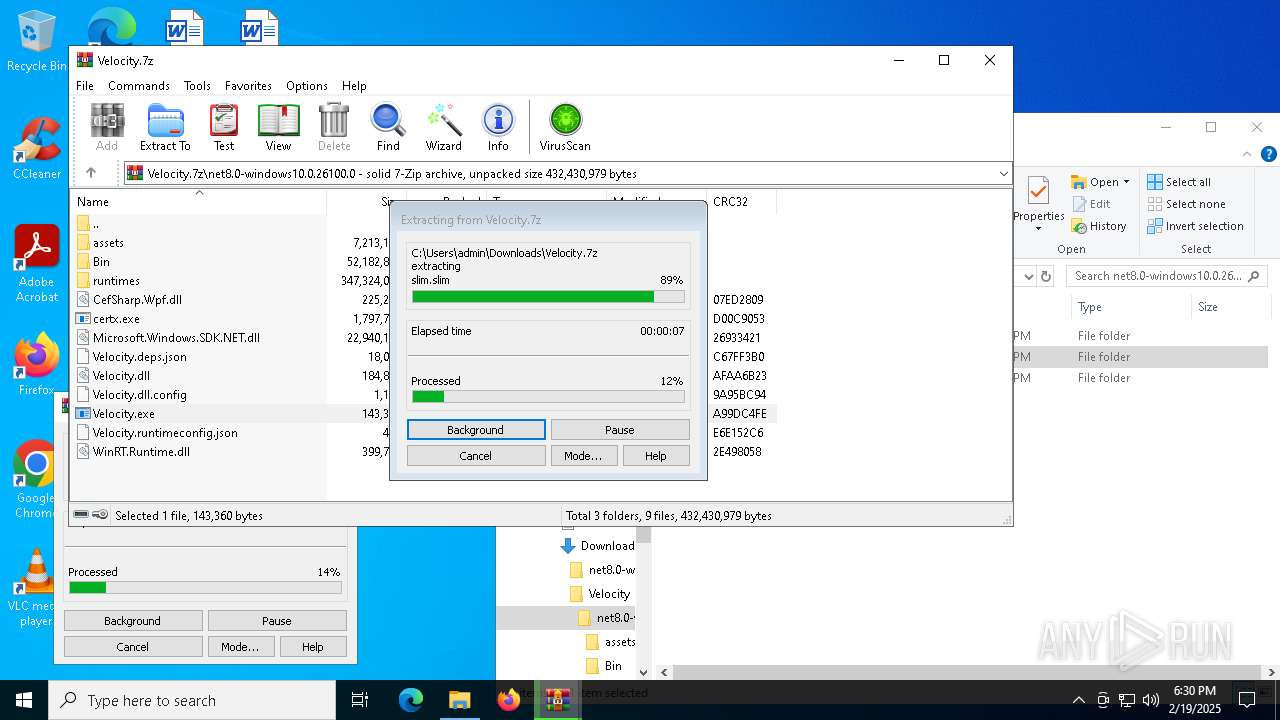
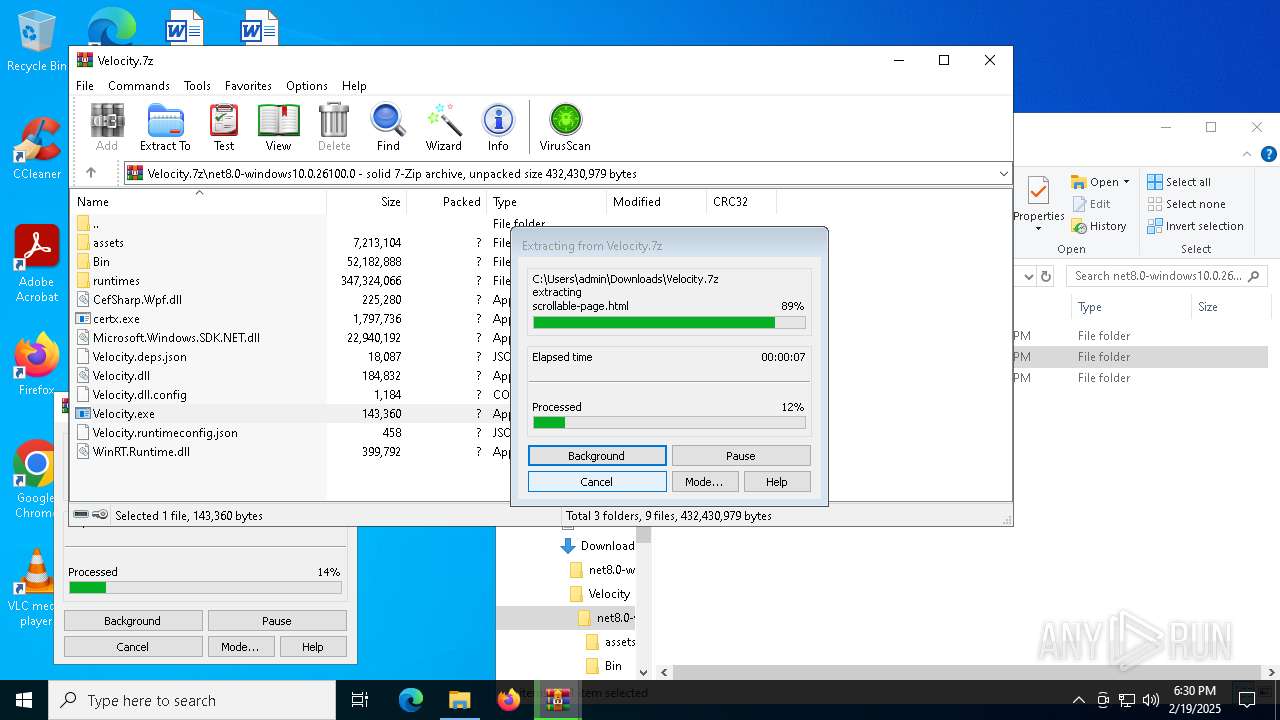
| URL: | https://filerift.com/file/UI1p5xjwGd |
| Full analysis: | https://app.any.run/tasks/6f839b18-36d9-4bb3-9895-92329e912bb6 |
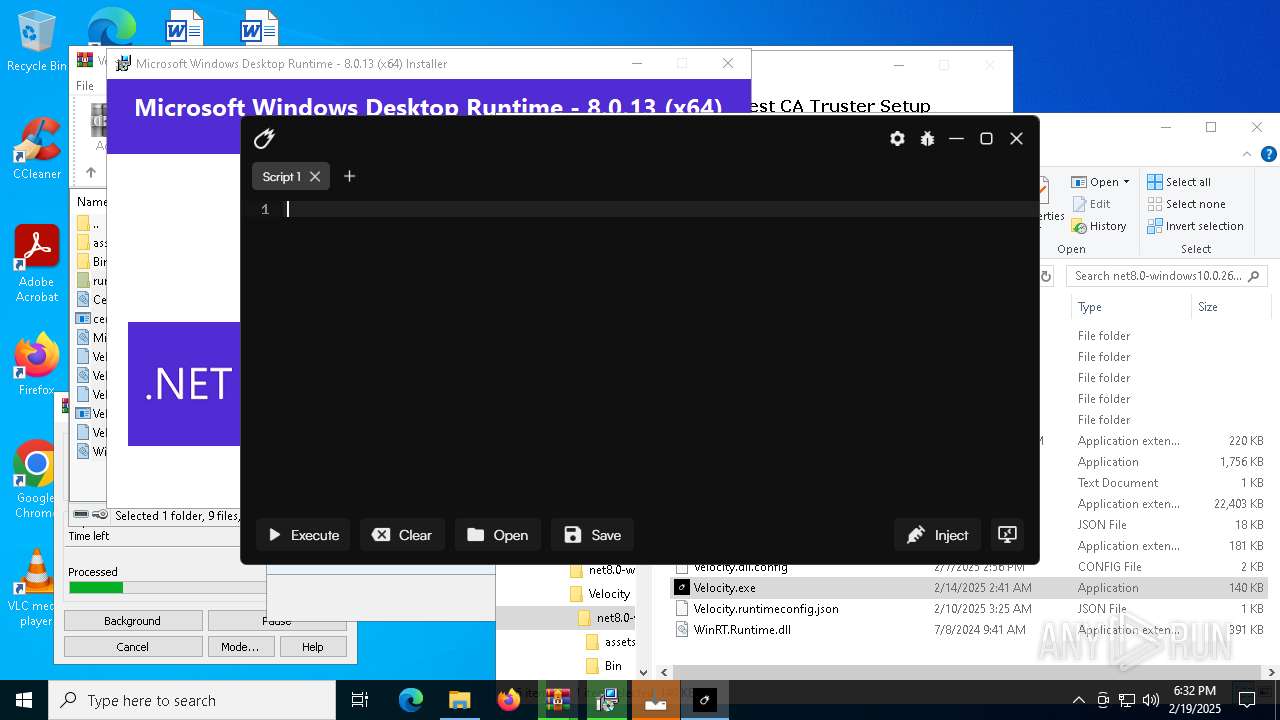
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2025, 18:28:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 74E02AC178466B0A0C0A510614DDC45F |
| SHA1: | FE679064A2DF07EE6071B4DA8E9CF65262F92F2A |
| SHA256: | 9B9D21F2AA906D750A8CF875AFCE0C6B1390AF35D518CEC43A544A28D0223E1B |
| SSDEEP: | 3:N8yDMZMIPnn:2yDNIPn |
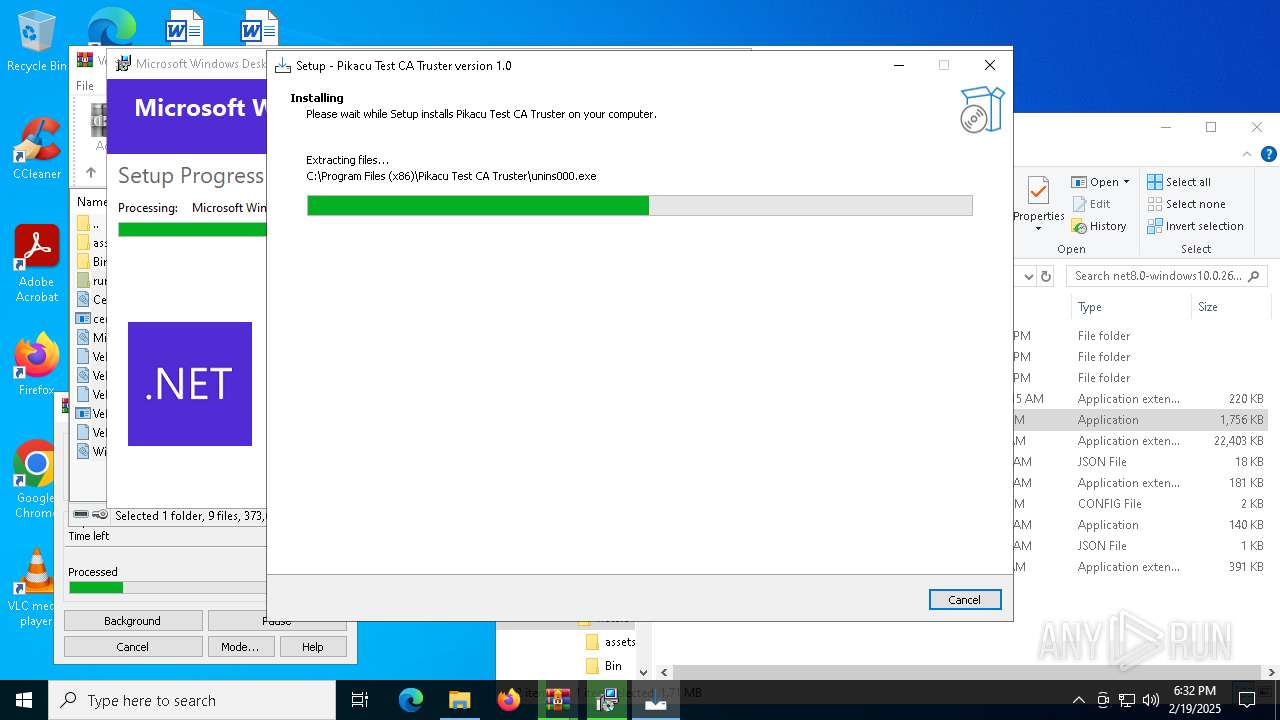
MALICIOUS
Changes the autorun value in the registry
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
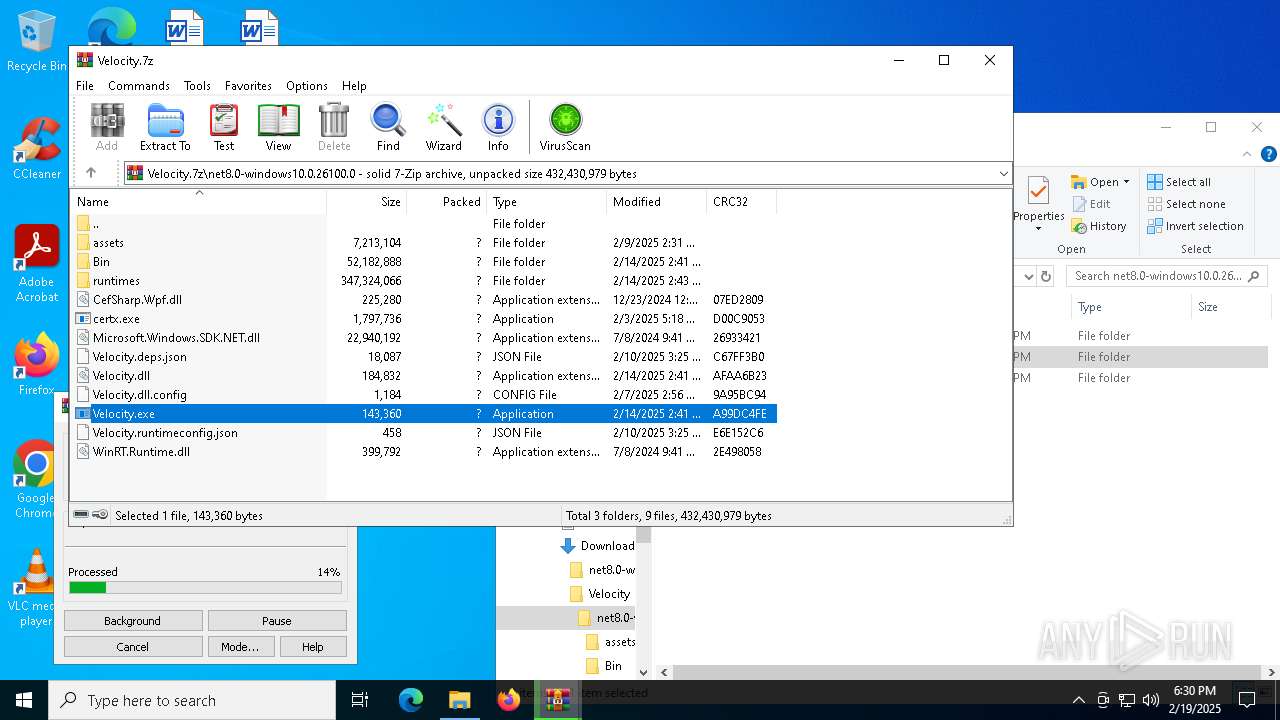
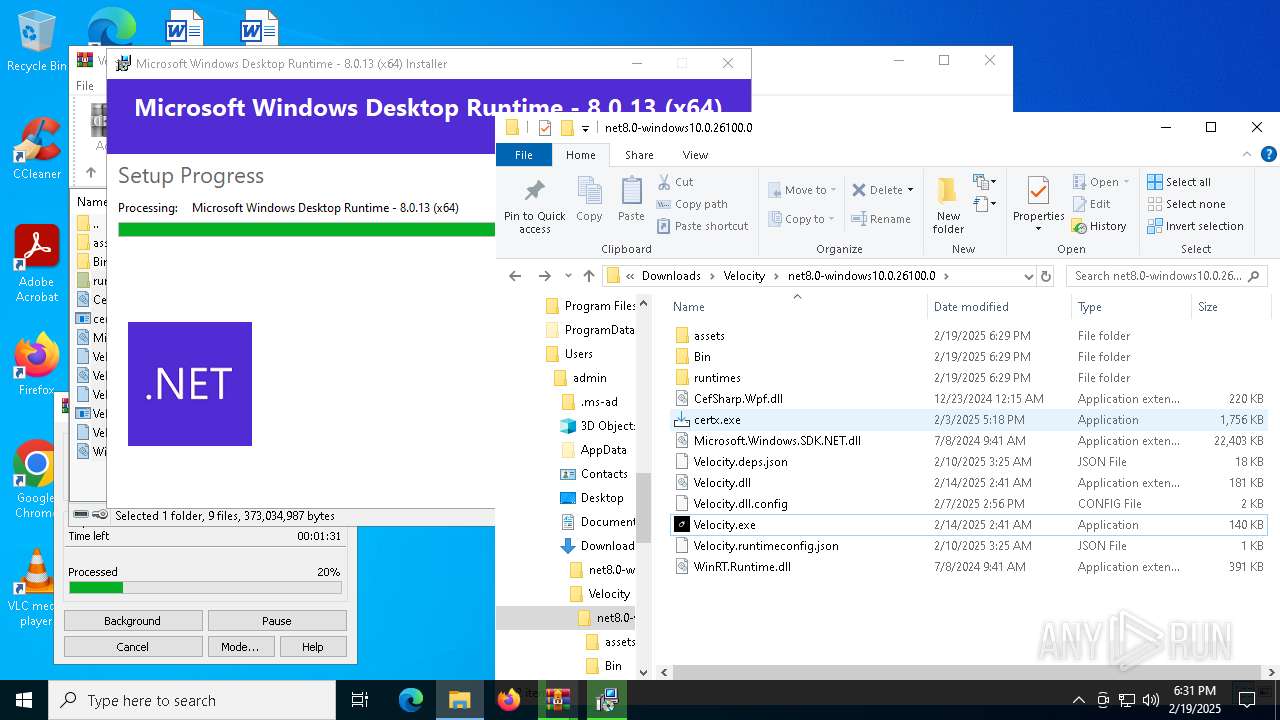
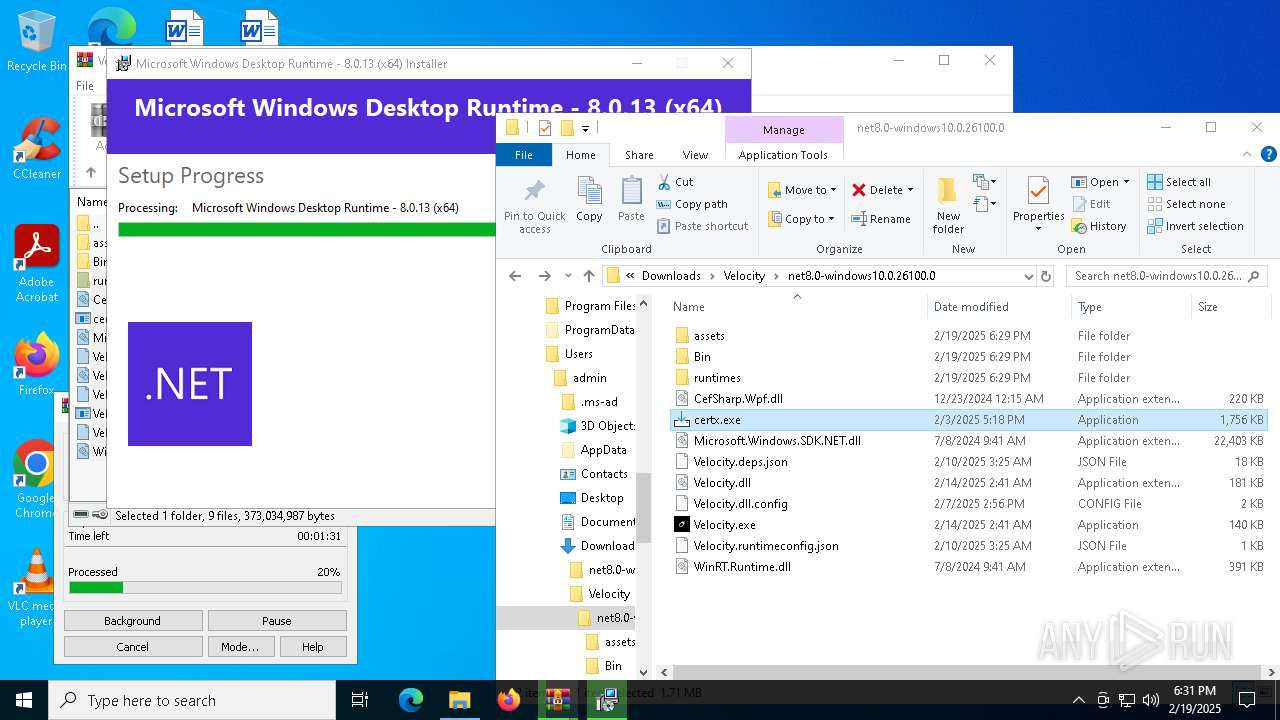
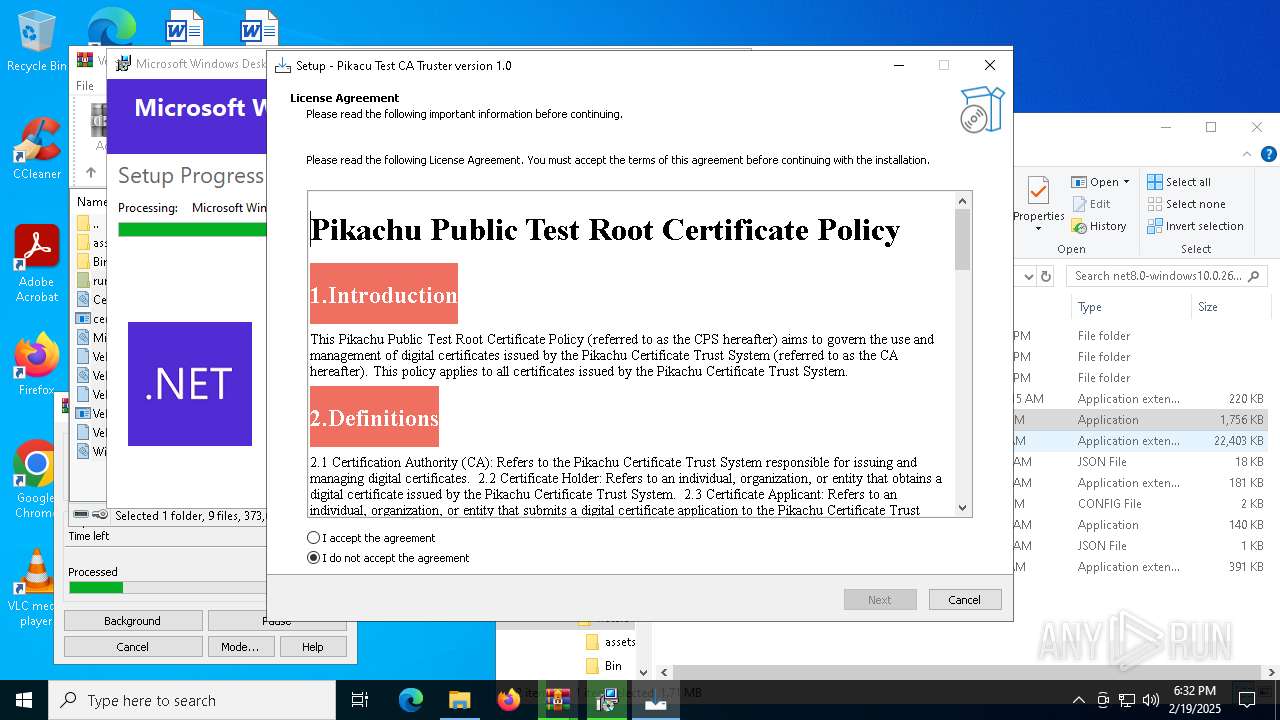
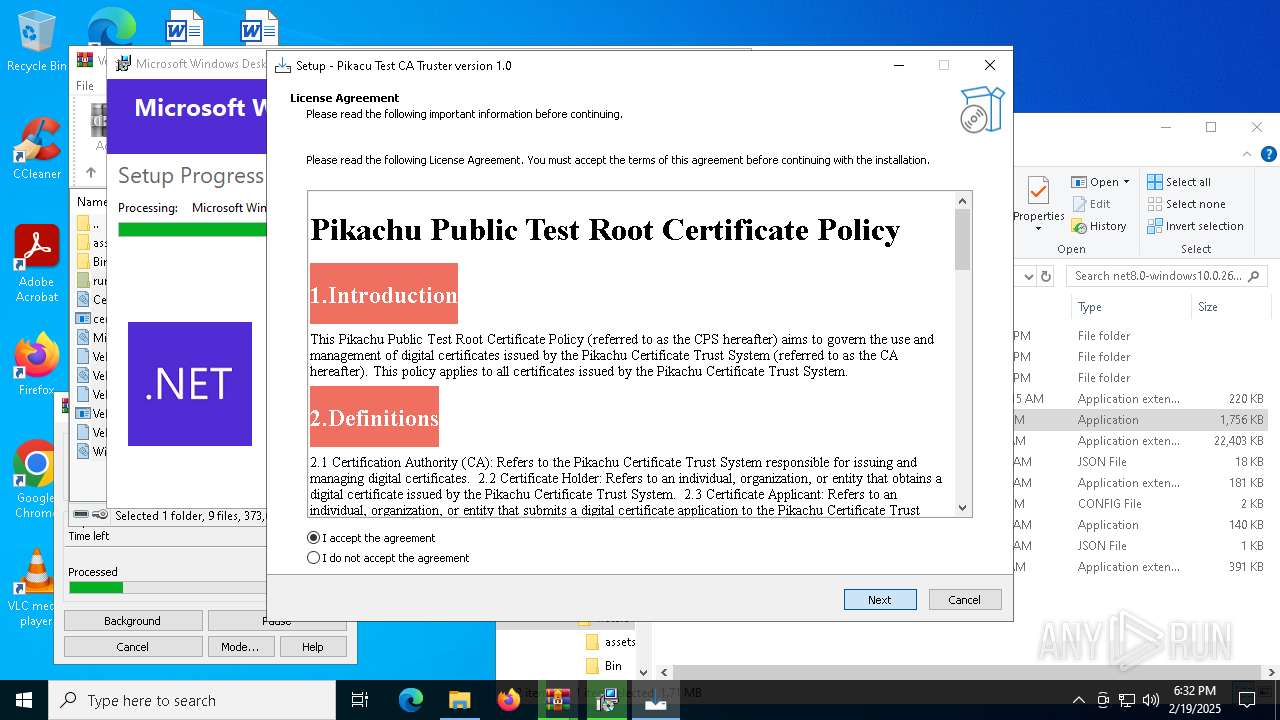
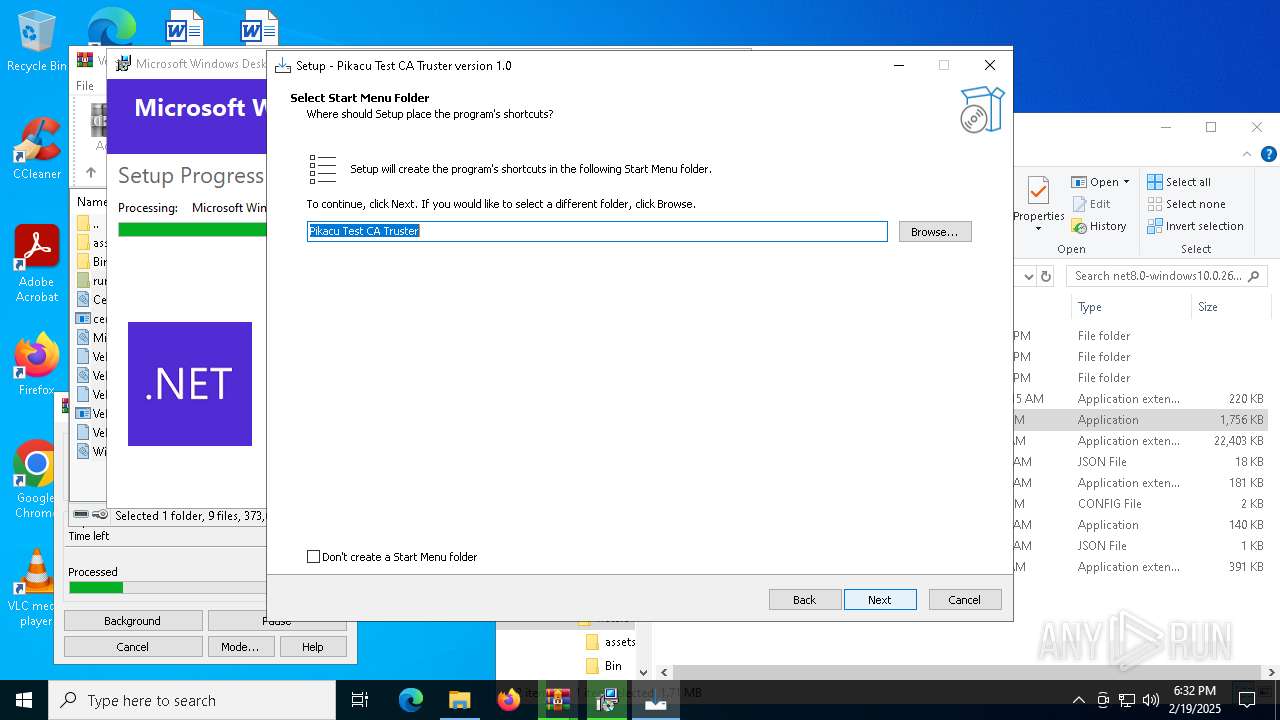
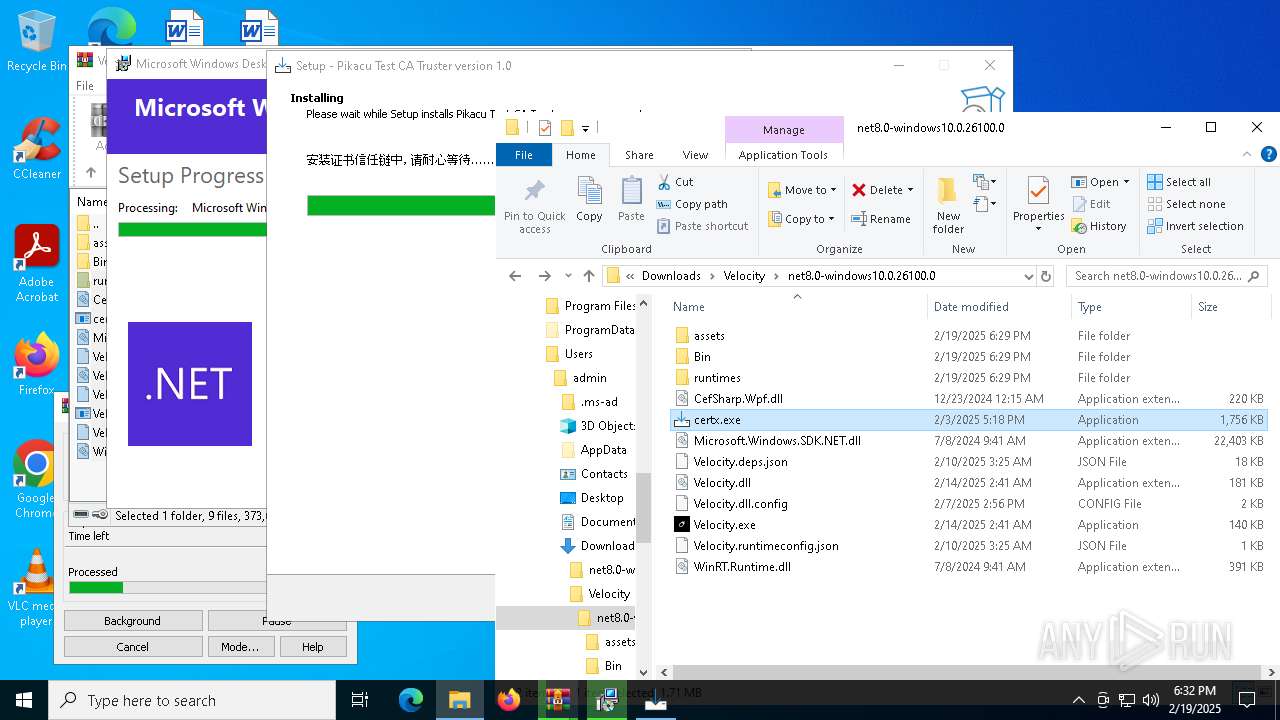
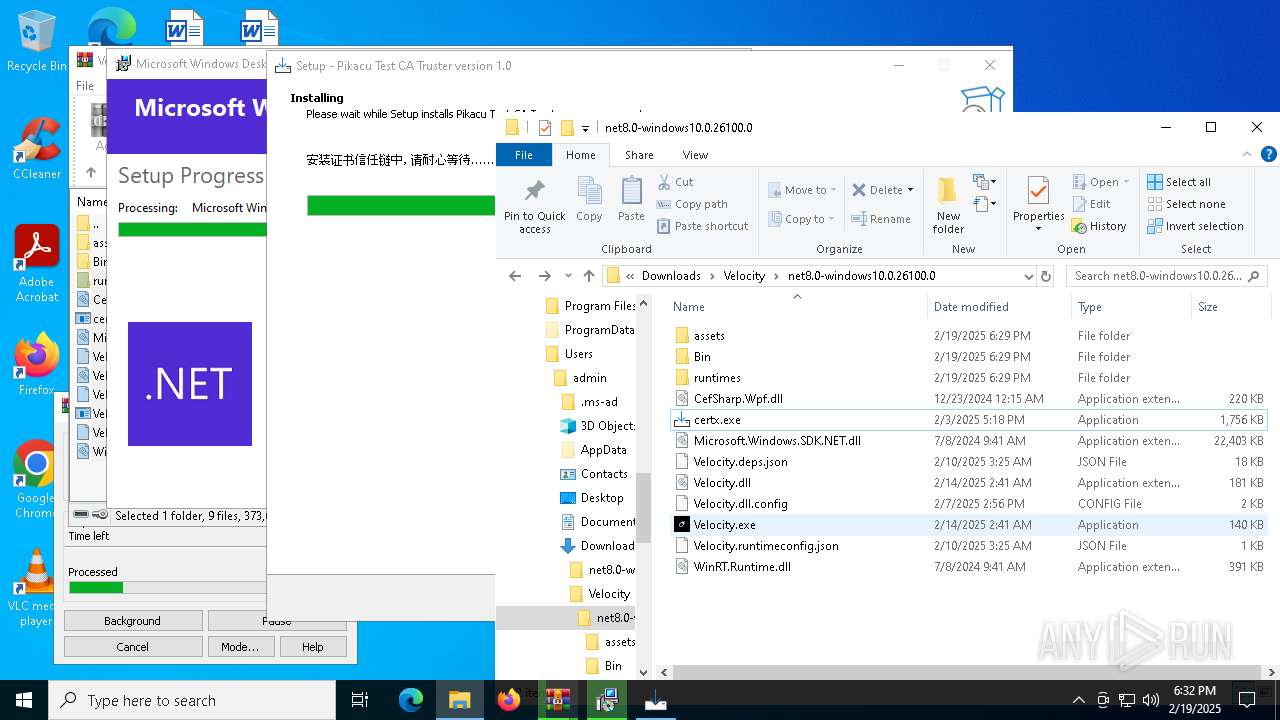
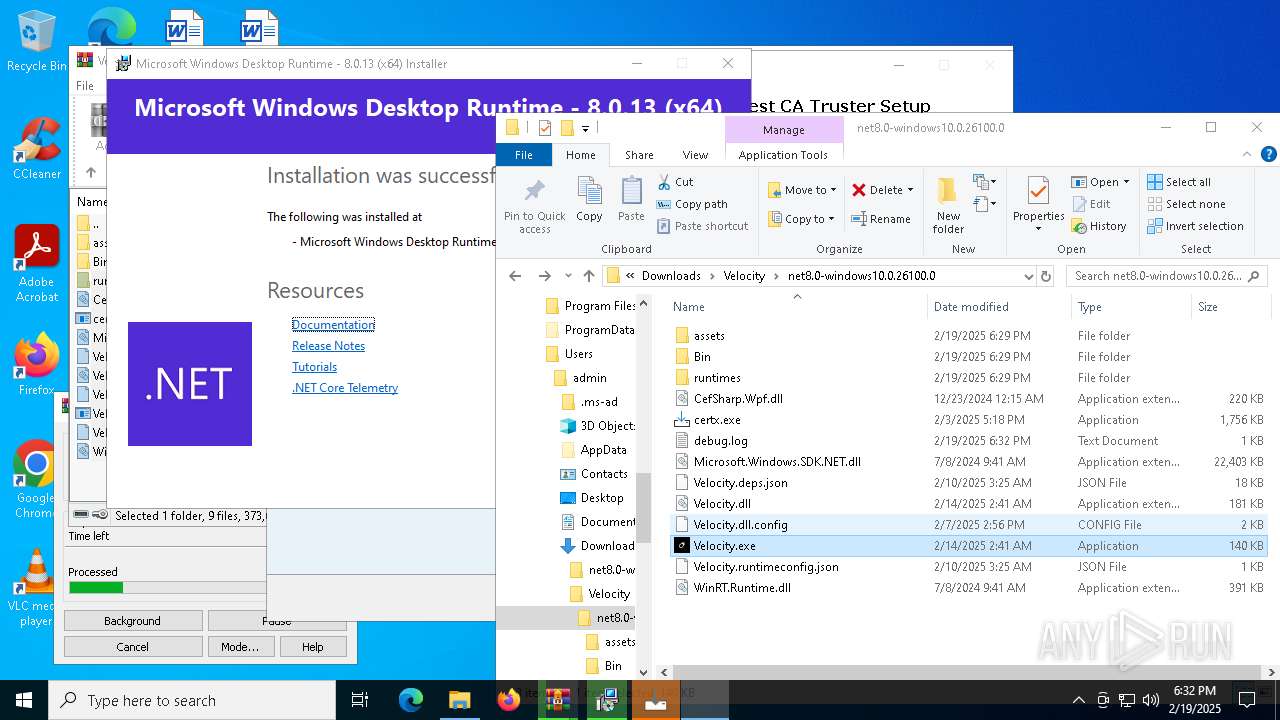
Executing a file with an untrusted certificate
- certx.exe (PID: 5200)
- certx.exe (PID: 7396)
- Certmgr.exe (PID: 7924)
- Certmgr.exe (PID: 2972)
- Certmgr.exe (PID: 7676)
- Certmgr.exe (PID: 1200)
- Certmgr.exe (PID: 7748)
- Certmgr.exe (PID: 2312)
- Certmgr.exe (PID: 6512)
- Certmgr.exe (PID: 4824)
- Certmgr.exe (PID: 3952)
- Certmgr.exe (PID: 6072)
- Certmgr.exe (PID: 7724)
- Certmgr.exe (PID: 5548)
- Certmgr.exe (PID: 7136)
- Certmgr.exe (PID: 5308)
- Certmgr.exe (PID: 6096)
- Certmgr.exe (PID: 7404)
- Certmgr.exe (PID: 3288)
- Certmgr.exe (PID: 7256)
- Certmgr.exe (PID: 5208)
- Certmgr.exe (PID: 7512)
- Certmgr.exe (PID: 7440)
- Certmgr.exe (PID: 6292)
- Certmgr.exe (PID: 7916)
- Certmgr.exe (PID: 4968)
- Certmgr.exe (PID: 6520)
- Certmgr.exe (PID: 1804)
- Certmgr.exe (PID: 6296)
- Certmgr.exe (PID: 6892)
- Certmgr.exe (PID: 2160)
- Certmgr.exe (PID: 4908)
- Certmgr.exe (PID: 628)
- Certmgr.exe (PID: 2940)
- Certmgr.exe (PID: 1796)
- Certmgr.exe (PID: 6056)
- Certmgr.exe (PID: 6720)
- Certmgr.exe (PID: 5444)
- Certmgr.exe (PID: 3436)
- Certmgr.exe (PID: 6380)
- Certmgr.exe (PID: 6236)
- Certmgr.exe (PID: 4144)
- Certmgr.exe (PID: 6460)
- Certmgr.exe (PID: 8076)
- Certmgr.exe (PID: 6332)
- Certmgr.exe (PID: 1868)
- Certmgr.exe (PID: 1988)
- Certmgr.exe (PID: 5968)
- Certmgr.exe (PID: 3996)
- Certmgr.exe (PID: 7884)
- Certmgr.exe (PID: 7760)
- Certmgr.exe (PID: 7632)
- Certmgr.exe (PID: 5540)
- Certmgr.exe (PID: 2312)
- Certmgr.exe (PID: 6868)
- Certmgr.exe (PID: 3052)
SUSPICIOUS
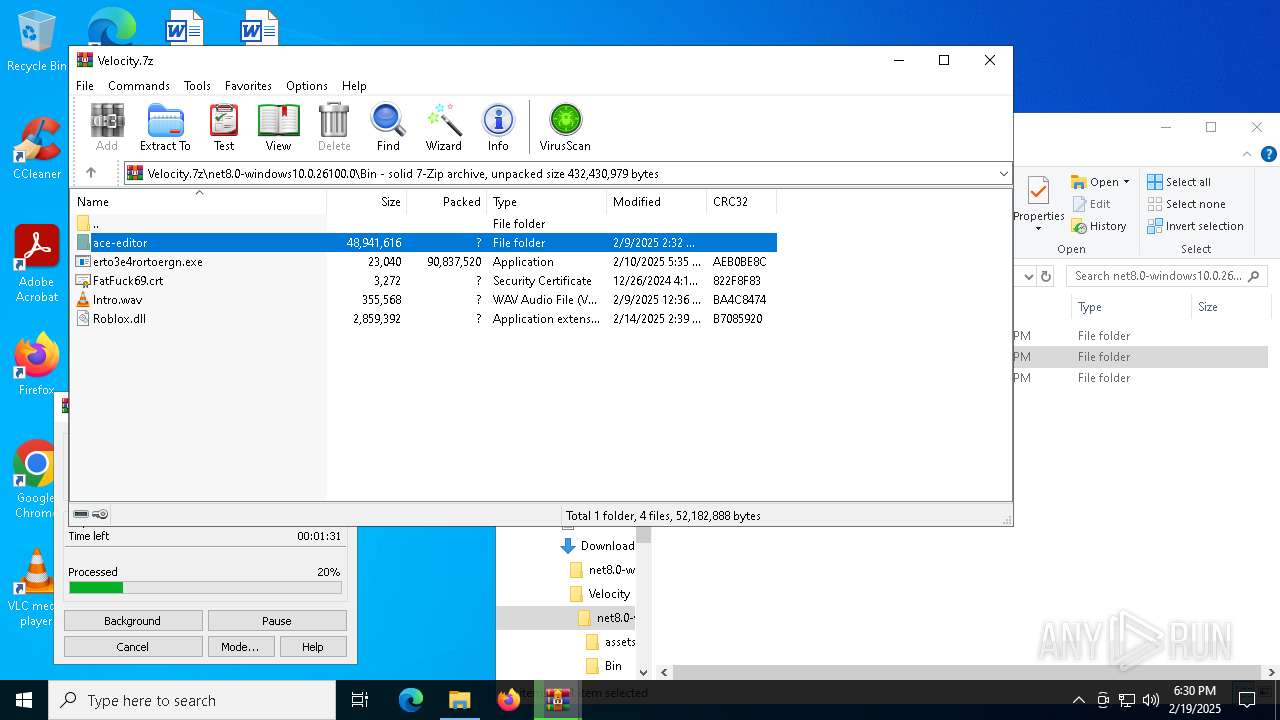
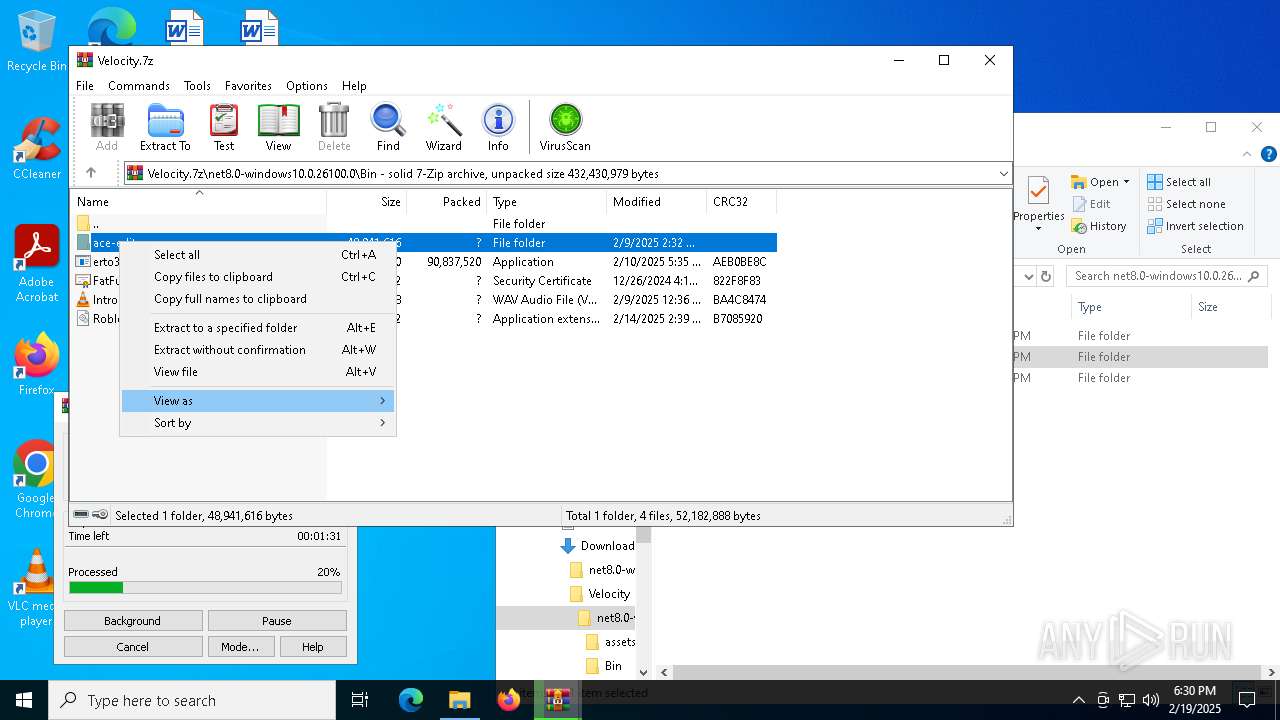
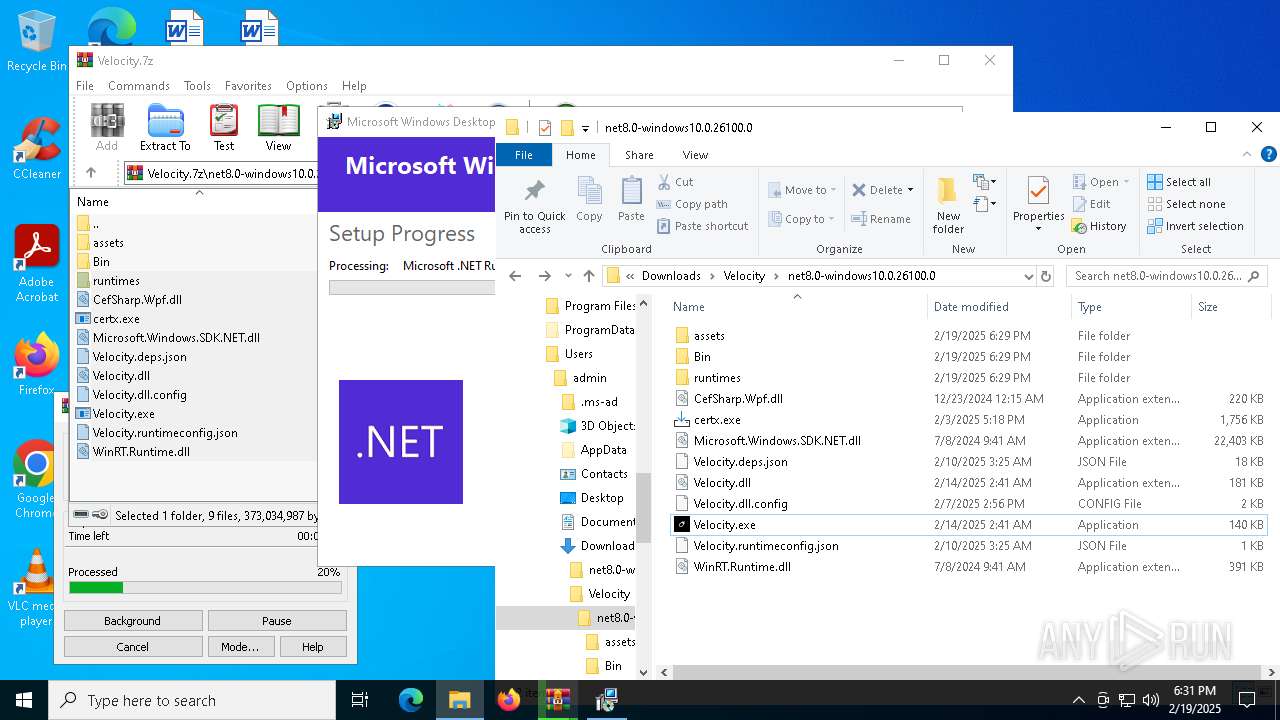
The process creates files with name similar to system file names
- WinRAR.exe (PID: 7944)
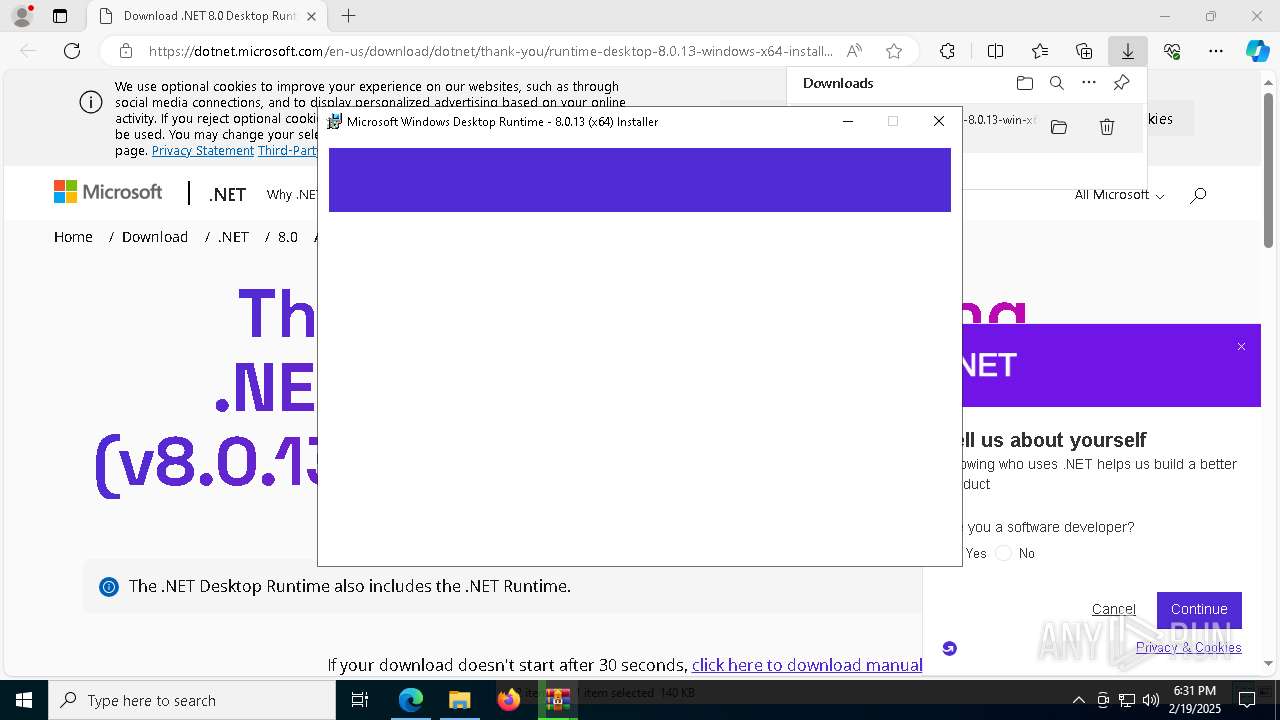
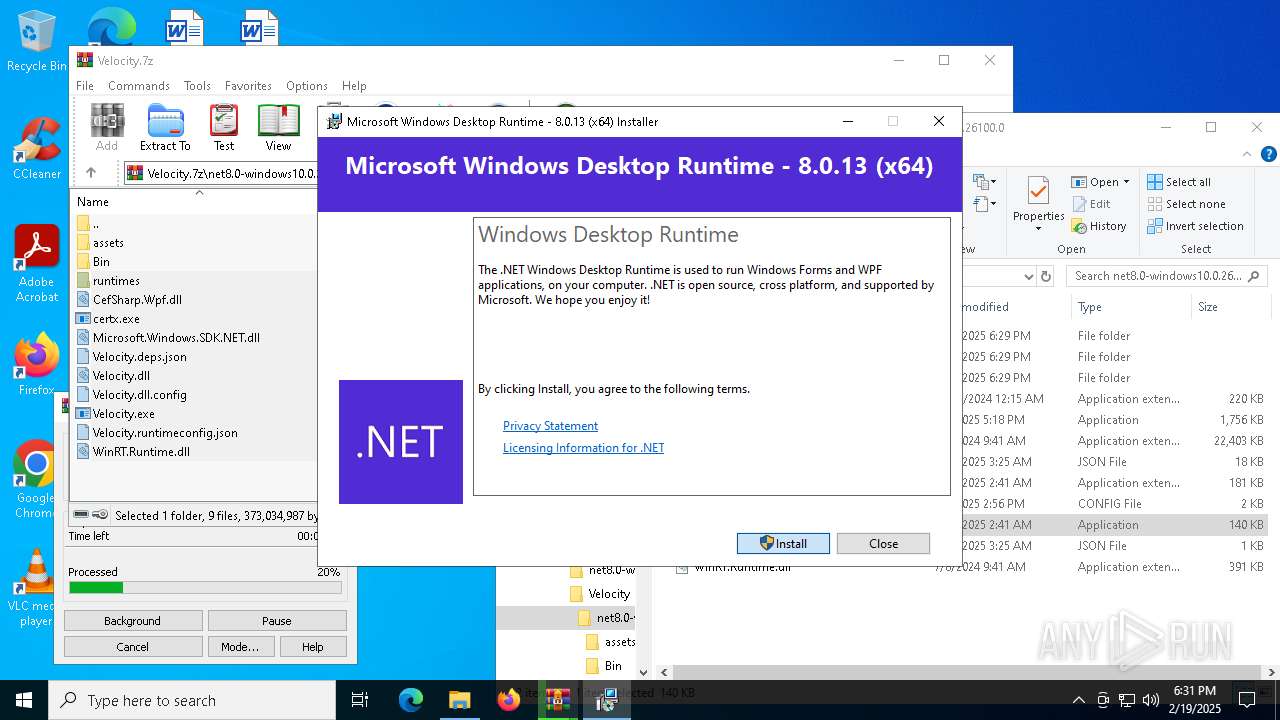
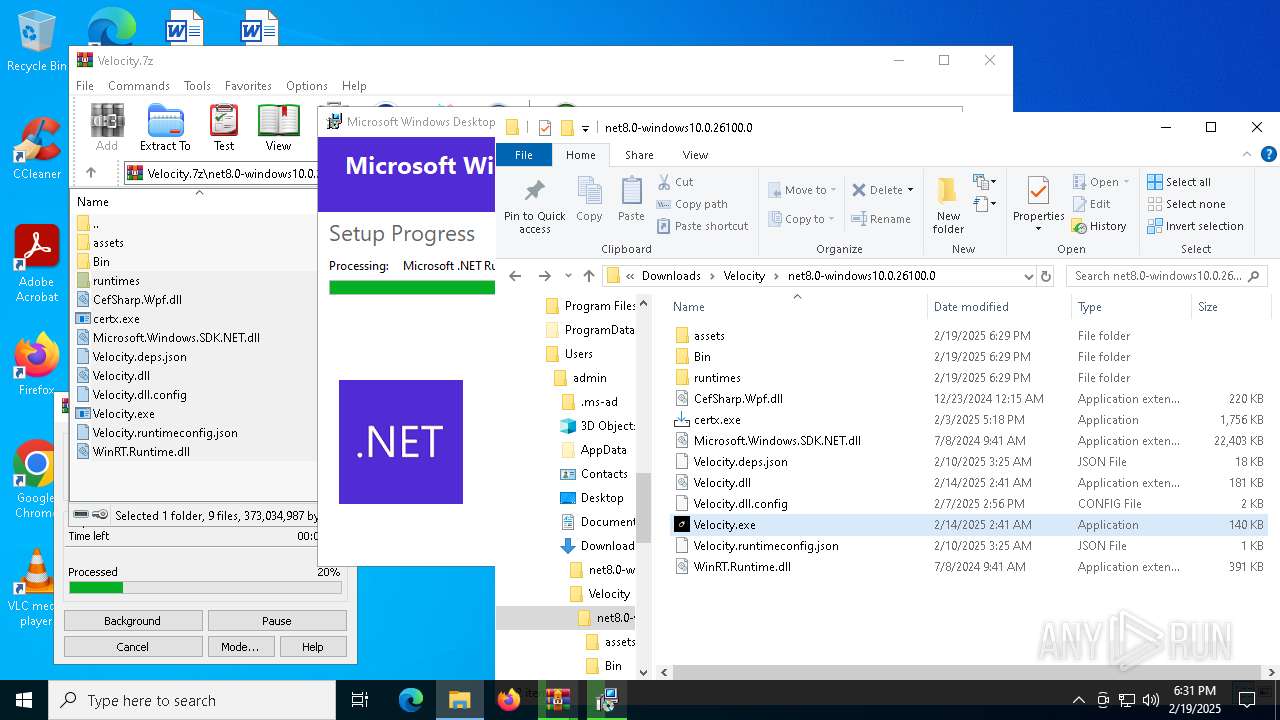
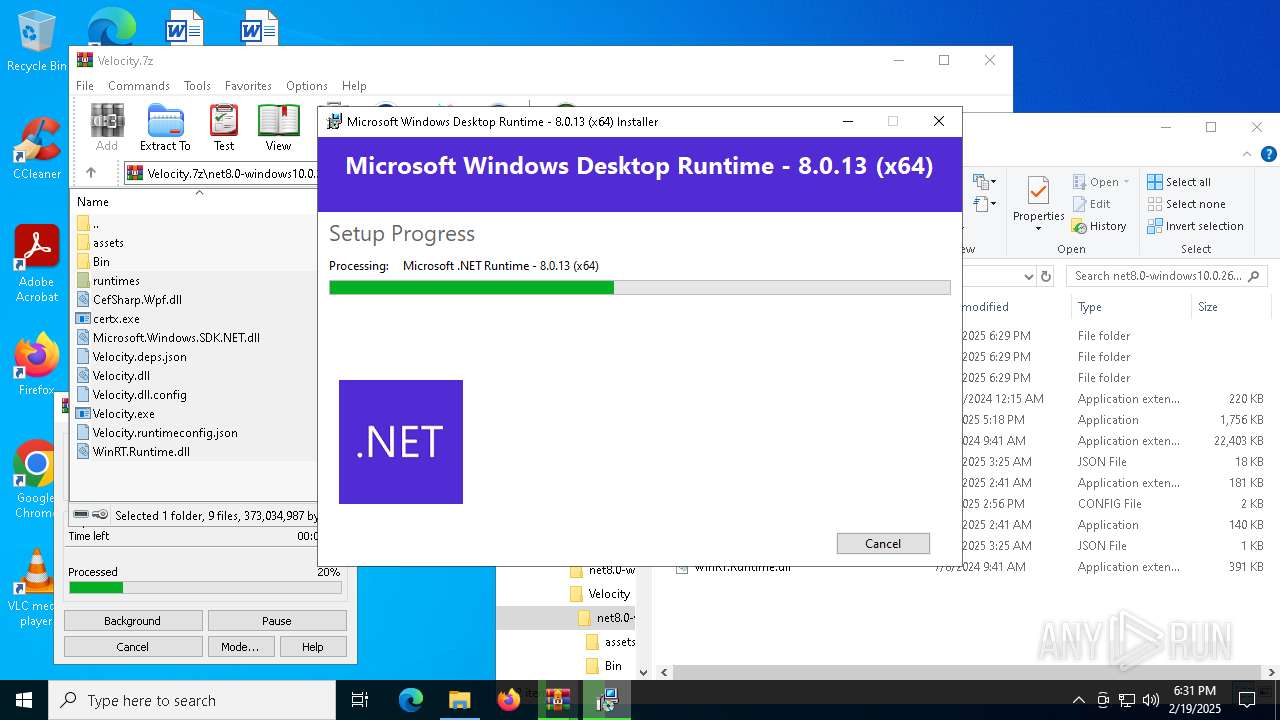
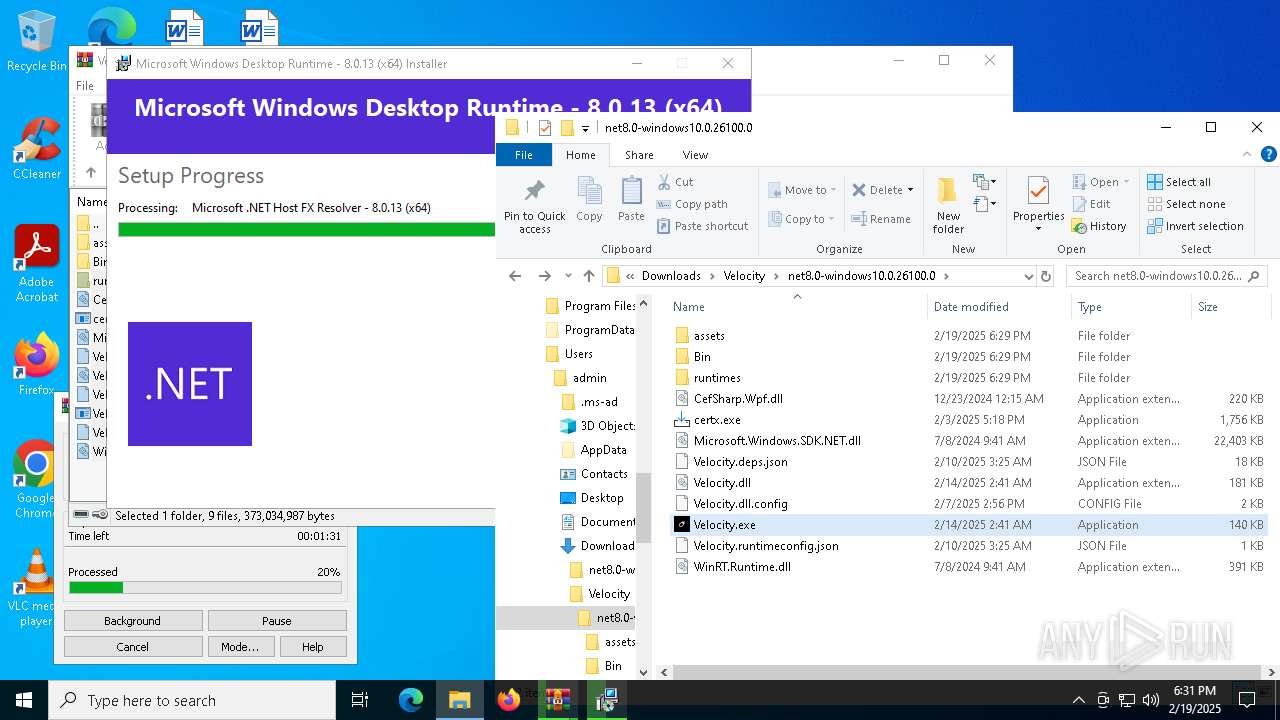
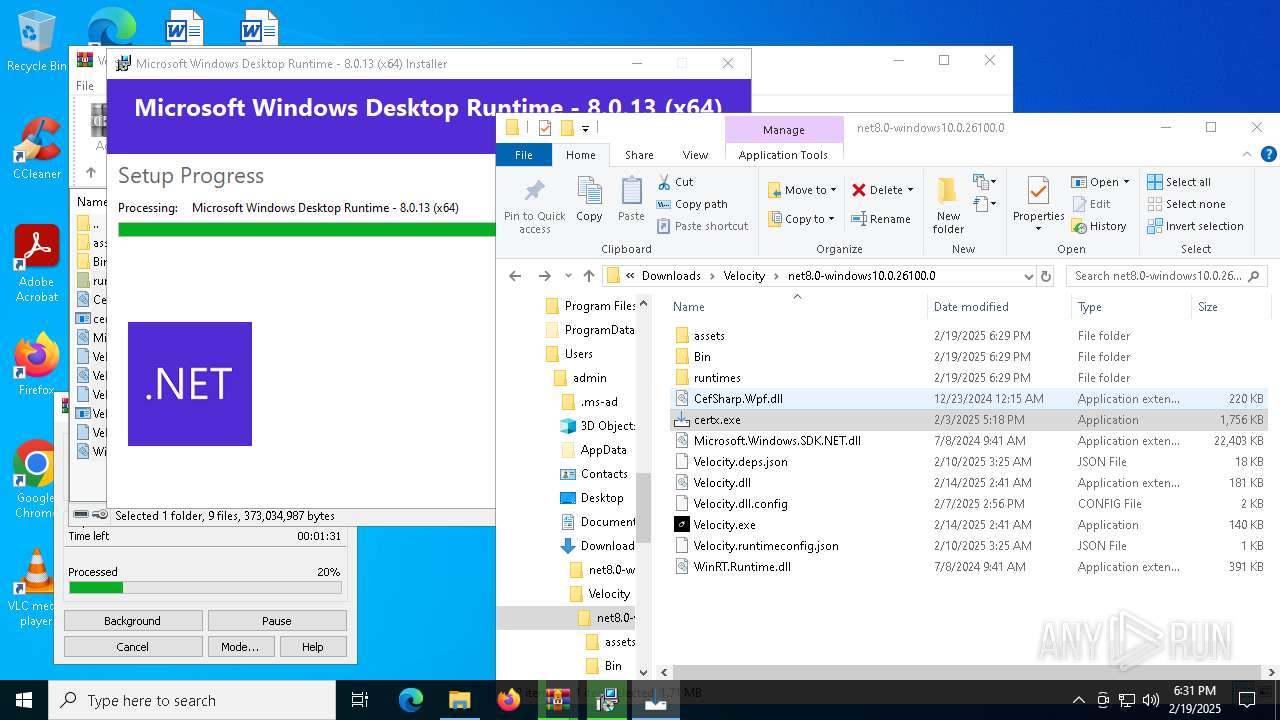
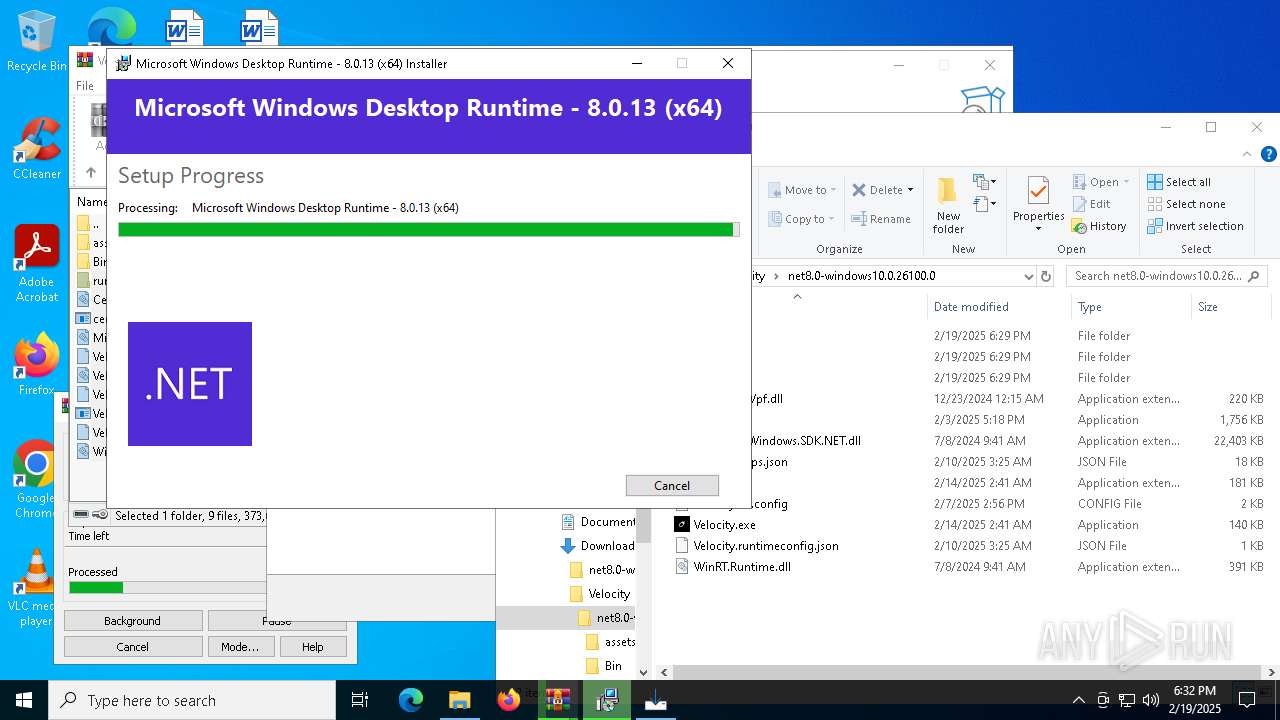
Process drops legitimate windows executable
- WinRAR.exe (PID: 7944)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 1920)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 7456)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
- msiexec.exe (PID: 7356)
- certx.tmp (PID: 5828)
Reads security settings of Internet Explorer
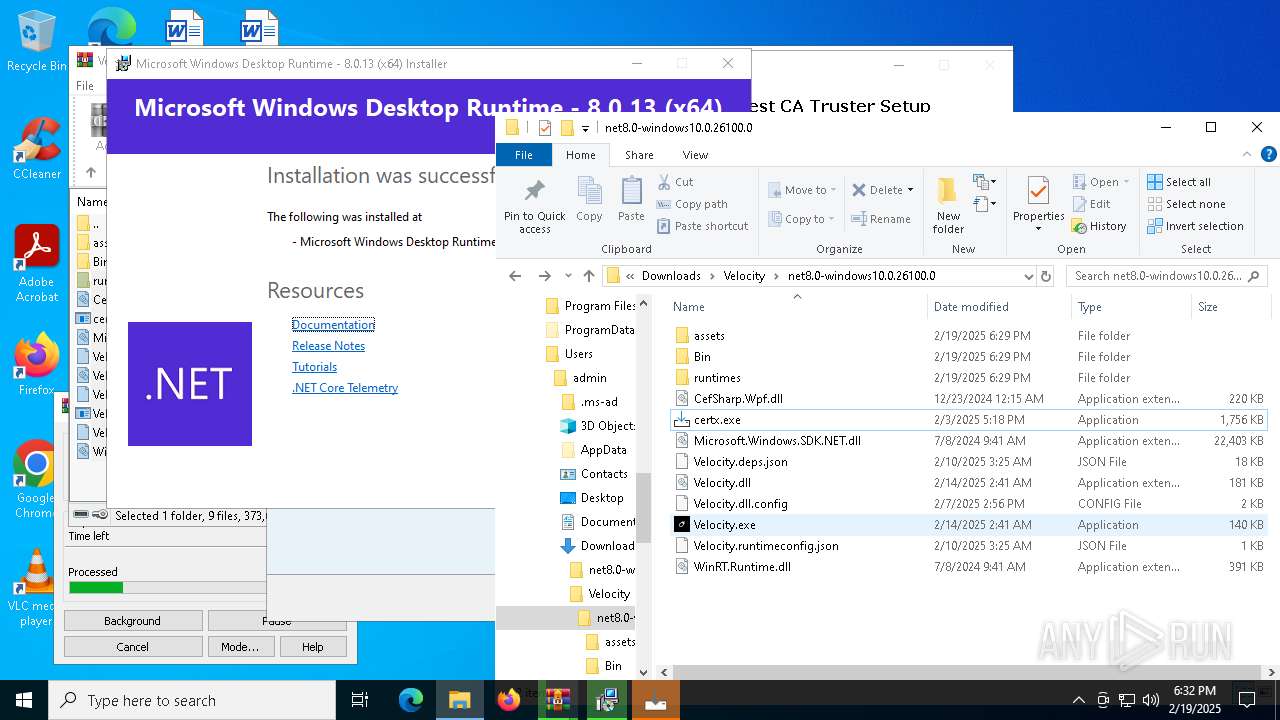
- Velocity.exe (PID: 6420)
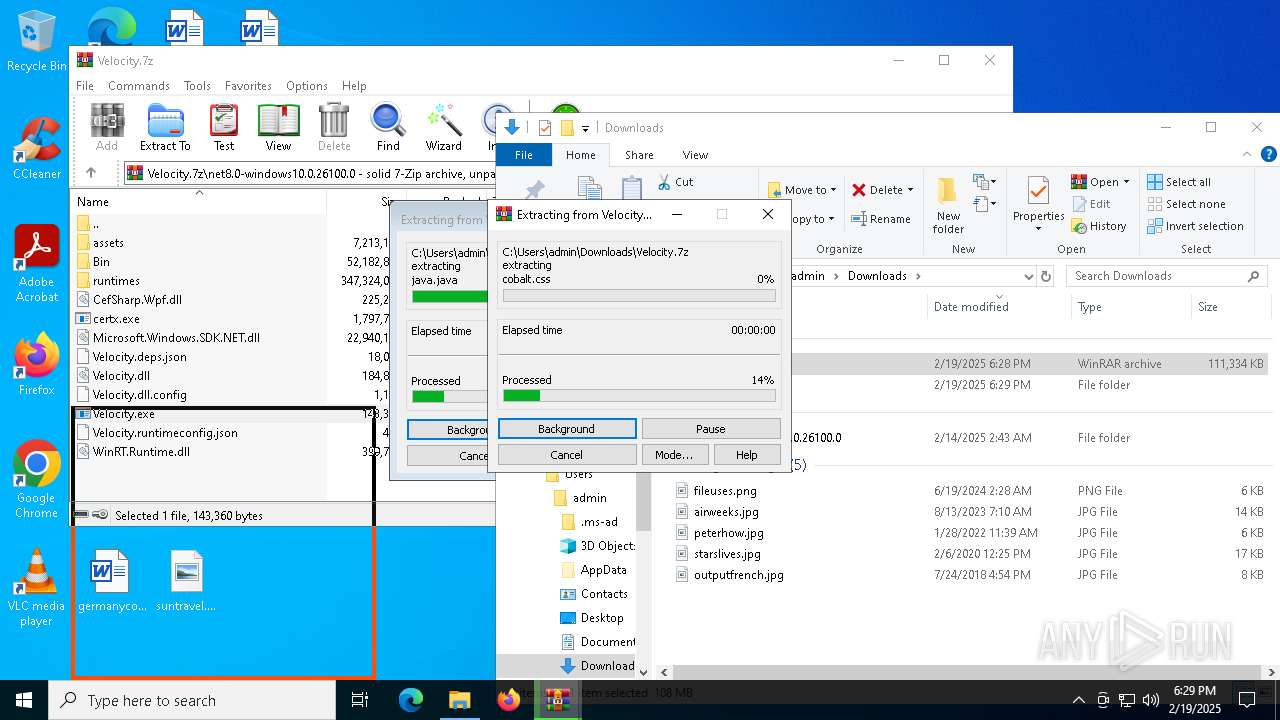
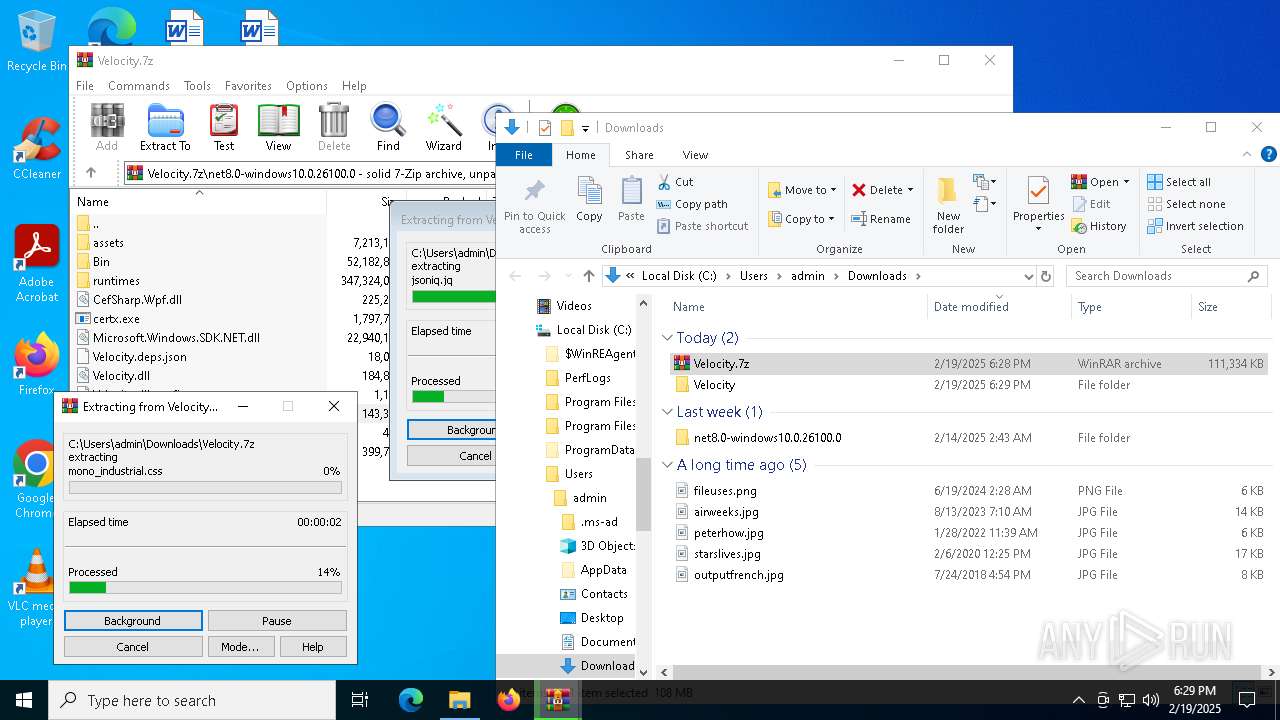
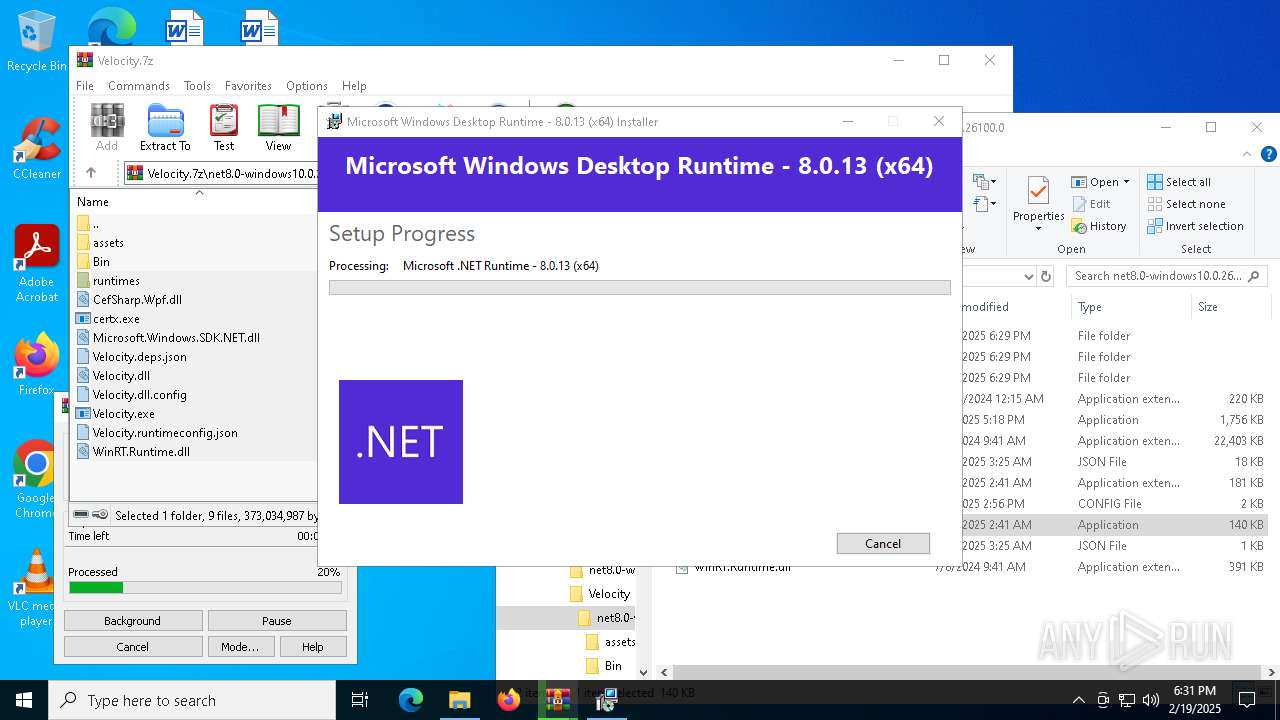
Executable content was dropped or overwritten
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 1920)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 7456)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
- certx.exe (PID: 5200)
- certx.exe (PID: 7396)
- certx.tmp (PID: 5828)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 7456)
Searches for installed software
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 7456)
Starts itself from another location
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 7456)
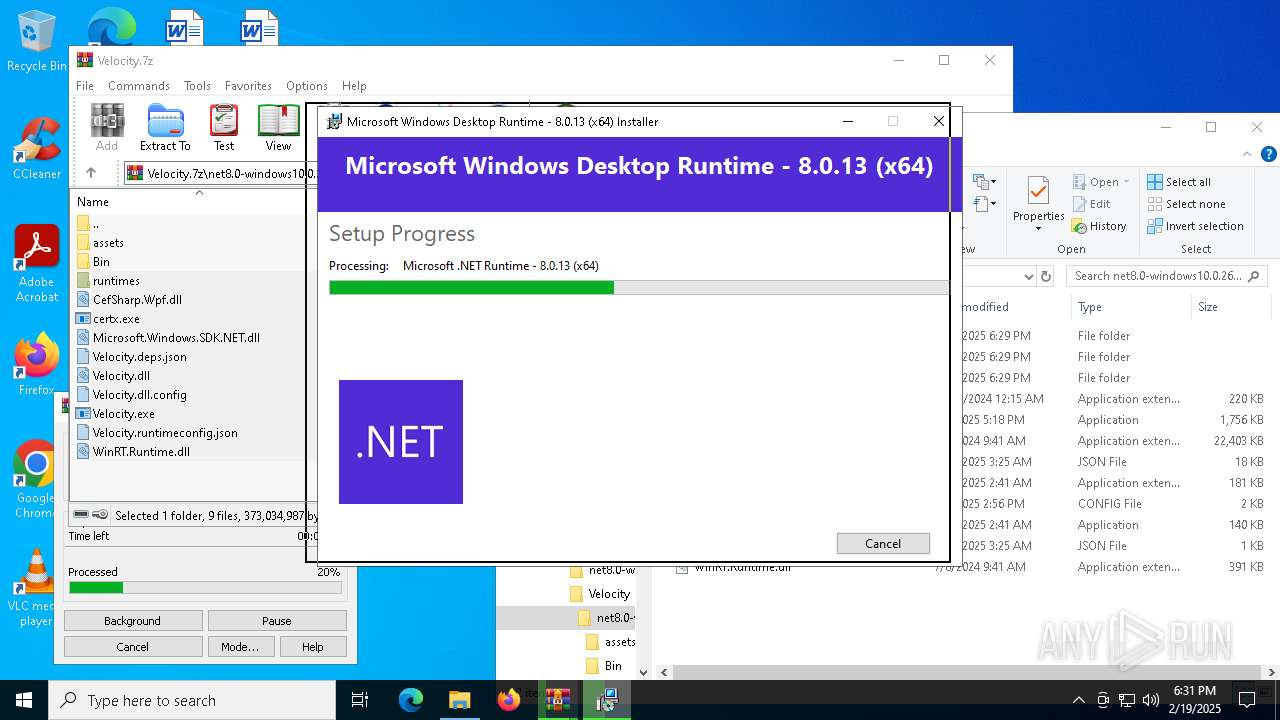
Creates a software uninstall entry
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7356)
- certx.tmp (PID: 5828)
Checks Windows Trust Settings
- msiexec.exe (PID: 7356)
The process drops C-runtime libraries
- msiexec.exe (PID: 7356)
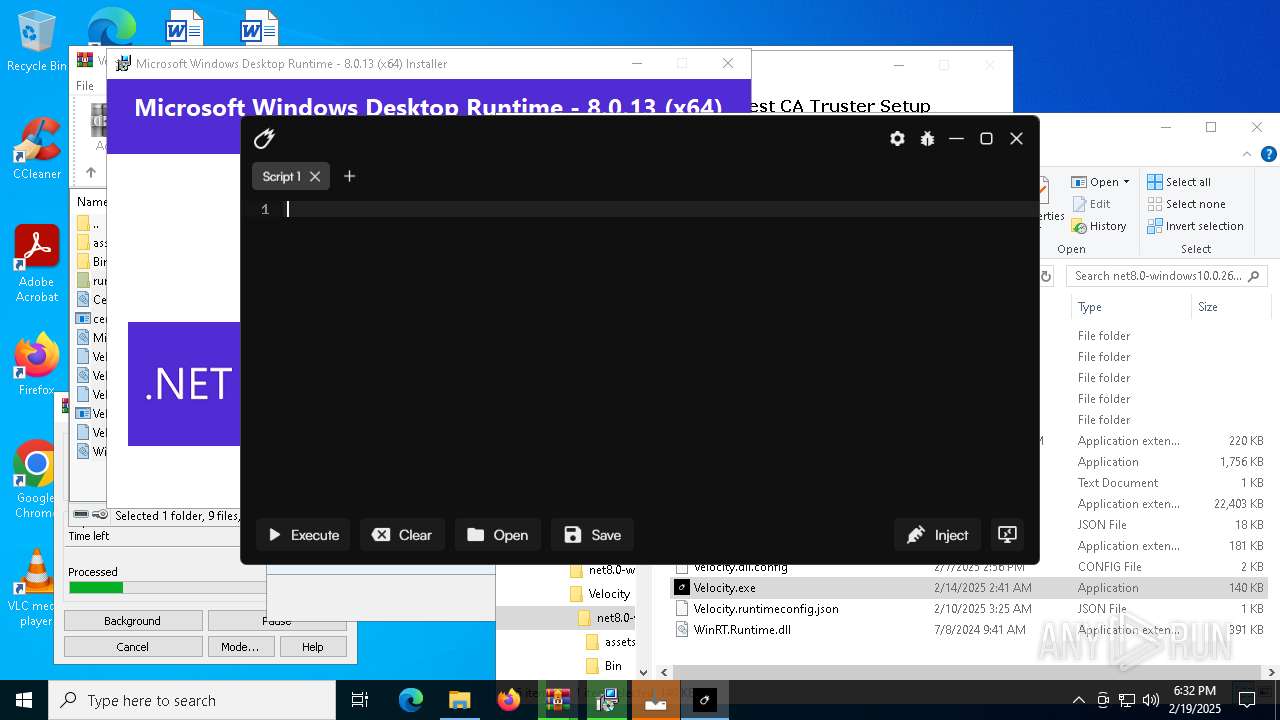
Starts CMD.EXE for commands execution
- certx.tmp (PID: 5828)
- Velocity.exe (PID: 7380)
Executing commands from a ".bat" file
- certx.tmp (PID: 5828)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7940)
Changes settings of the software policy
- regedit.exe (PID: 7532)
Adds/modifies Windows certificates
- Certmgr.exe (PID: 7676)
- regedit.exe (PID: 7532)
- Certmgr.exe (PID: 1200)
- Certmgr.exe (PID: 7512)
- Certmgr.exe (PID: 7256)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7668)
INFO
Application launched itself
- msedge.exe (PID: 6256)
- msedge.exe (PID: 8112)
- msedge.exe (PID: 2008)
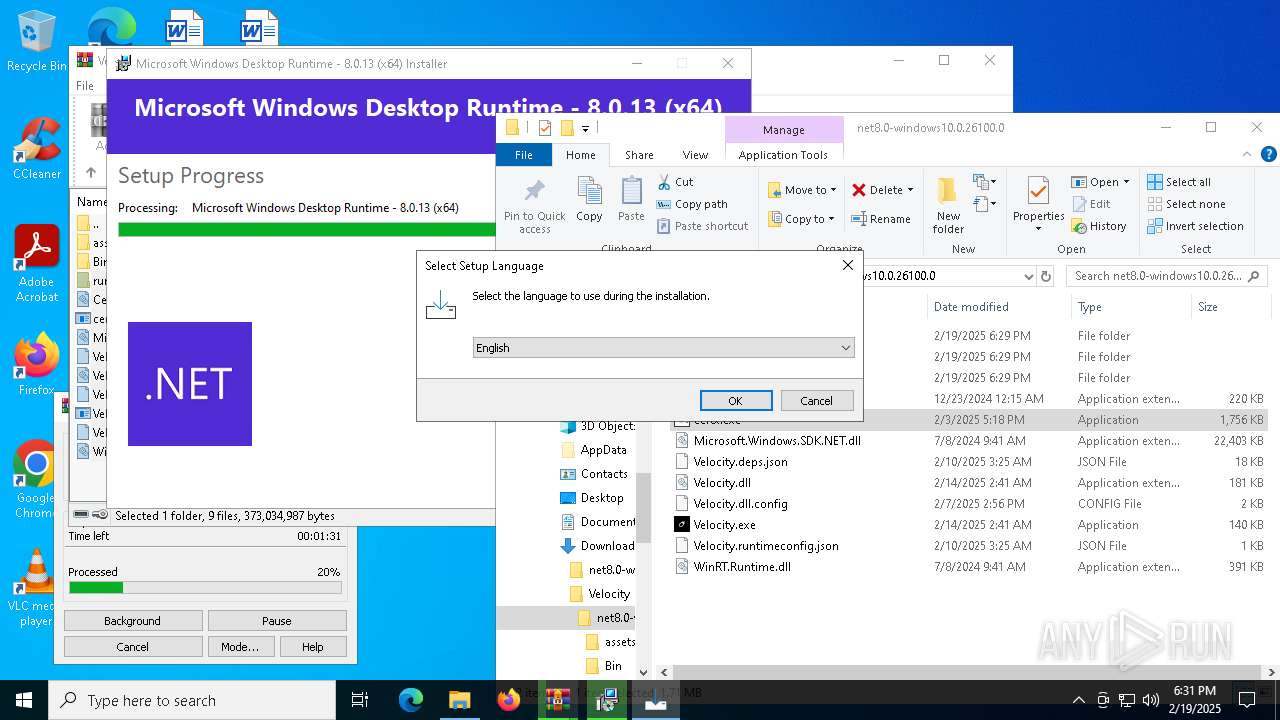
Checks supported languages
- identity_helper.exe (PID: 3224)
- identity_helper.exe (PID: 7548)
- Velocity.exe (PID: 6420)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 7456)
- identity_helper.exe (PID: 6372)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 1920)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
- msiexec.exe (PID: 2448)
- msiexec.exe (PID: 7356)
- msiexec.exe (PID: 7500)
- msiexec.exe (PID: 1328)
- msiexec.exe (PID: 1876)
- certx.exe (PID: 5200)
- certx.tmp (PID: 1468)
- certx.exe (PID: 7396)
- certx.tmp (PID: 5828)
- Certmgr.exe (PID: 7924)
- Certmgr.exe (PID: 7676)
- Certmgr.exe (PID: 7748)
- Certmgr.exe (PID: 3952)
- Certmgr.exe (PID: 2312)
- Certmgr.exe (PID: 4824)
- Certmgr.exe (PID: 6072)
- Certmgr.exe (PID: 7724)
- Certmgr.exe (PID: 5548)
- Certmgr.exe (PID: 5308)
- Certmgr.exe (PID: 4968)
- Certmgr.exe (PID: 6460)
Reads the computer name
- identity_helper.exe (PID: 3224)
- identity_helper.exe (PID: 7548)
- Velocity.exe (PID: 6420)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 7456)
- identity_helper.exe (PID: 6372)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
- msiexec.exe (PID: 1876)
- certx.tmp (PID: 1468)
- certx.tmp (PID: 5828)
- msiexec.exe (PID: 7500)
Reads Environment values
- identity_helper.exe (PID: 3224)
- identity_helper.exe (PID: 7548)
- identity_helper.exe (PID: 6372)
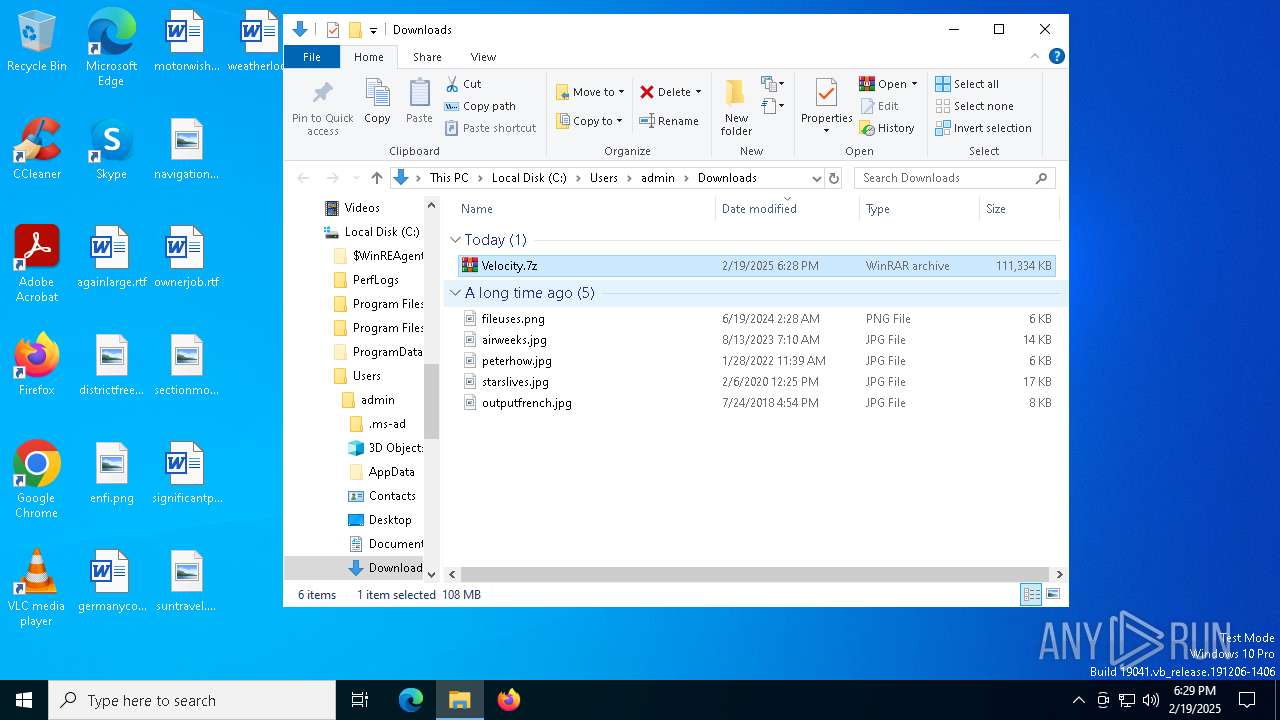
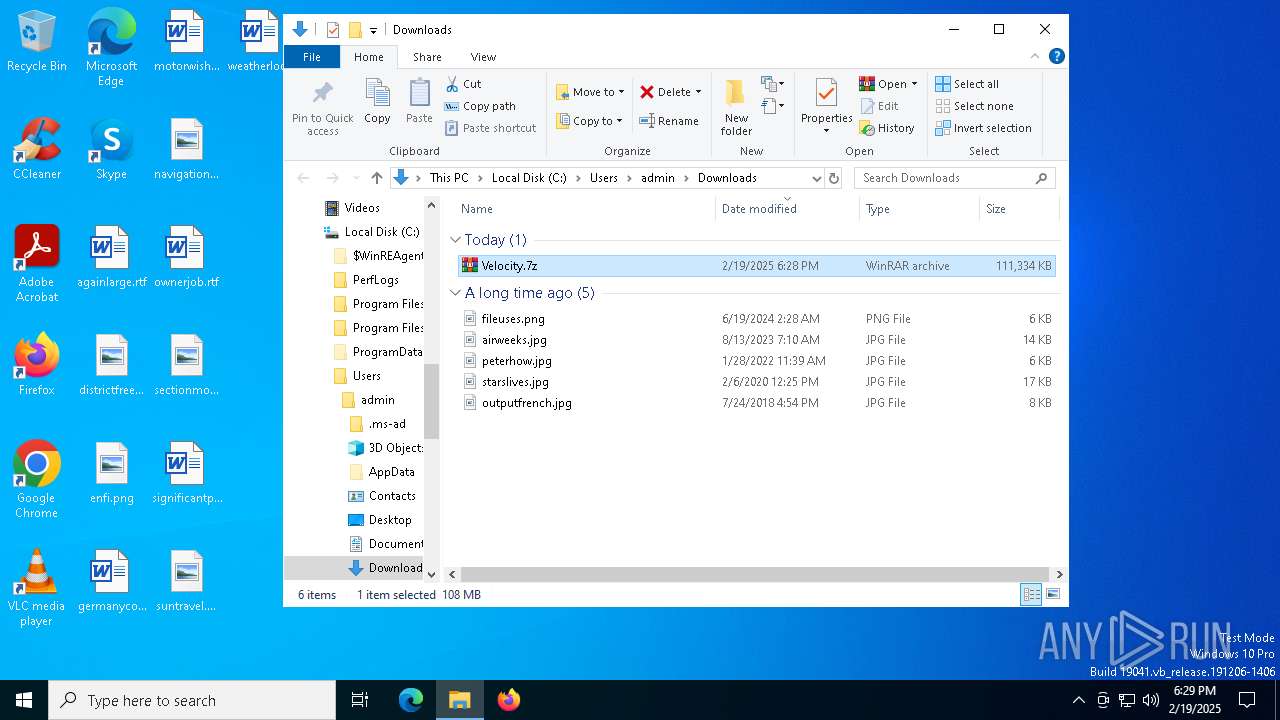
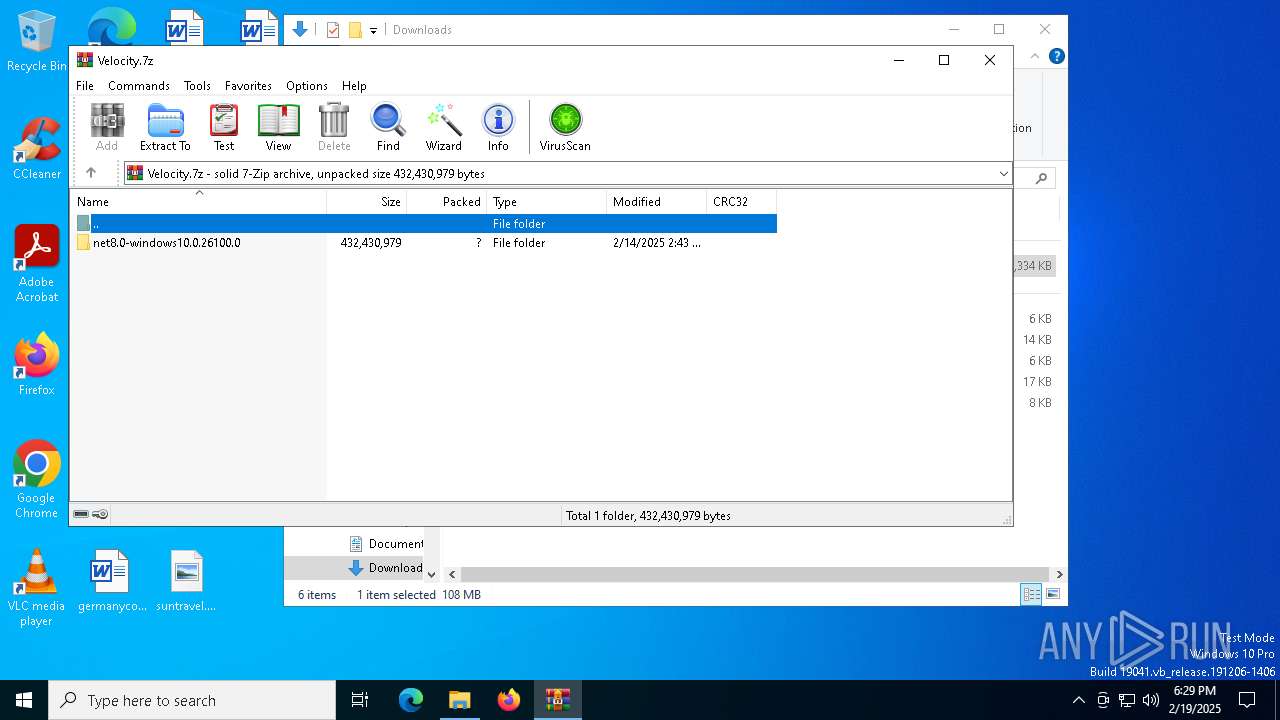
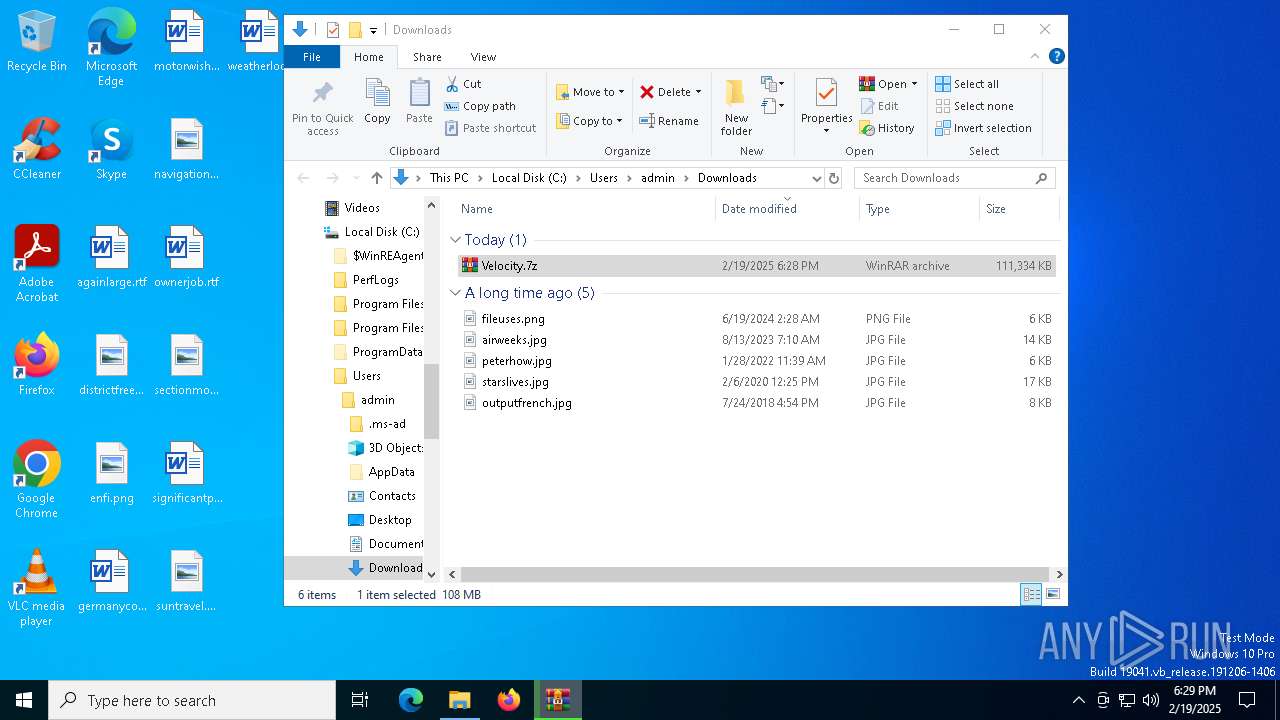
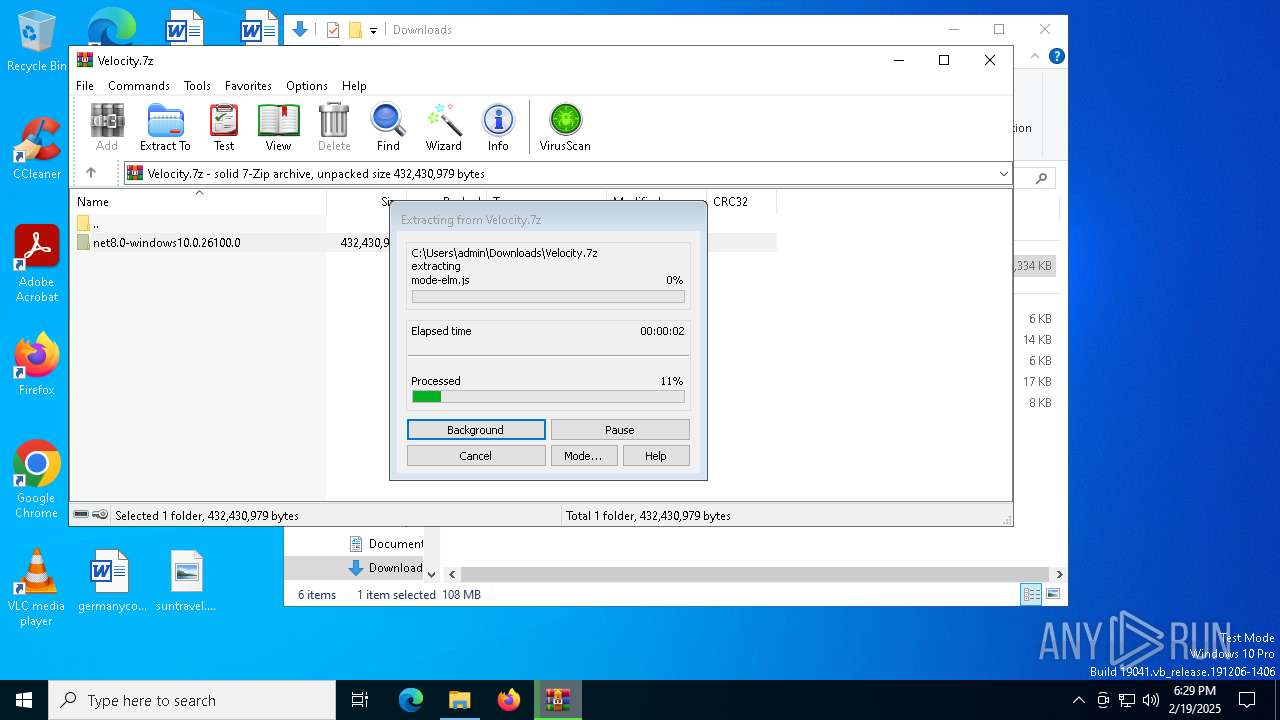
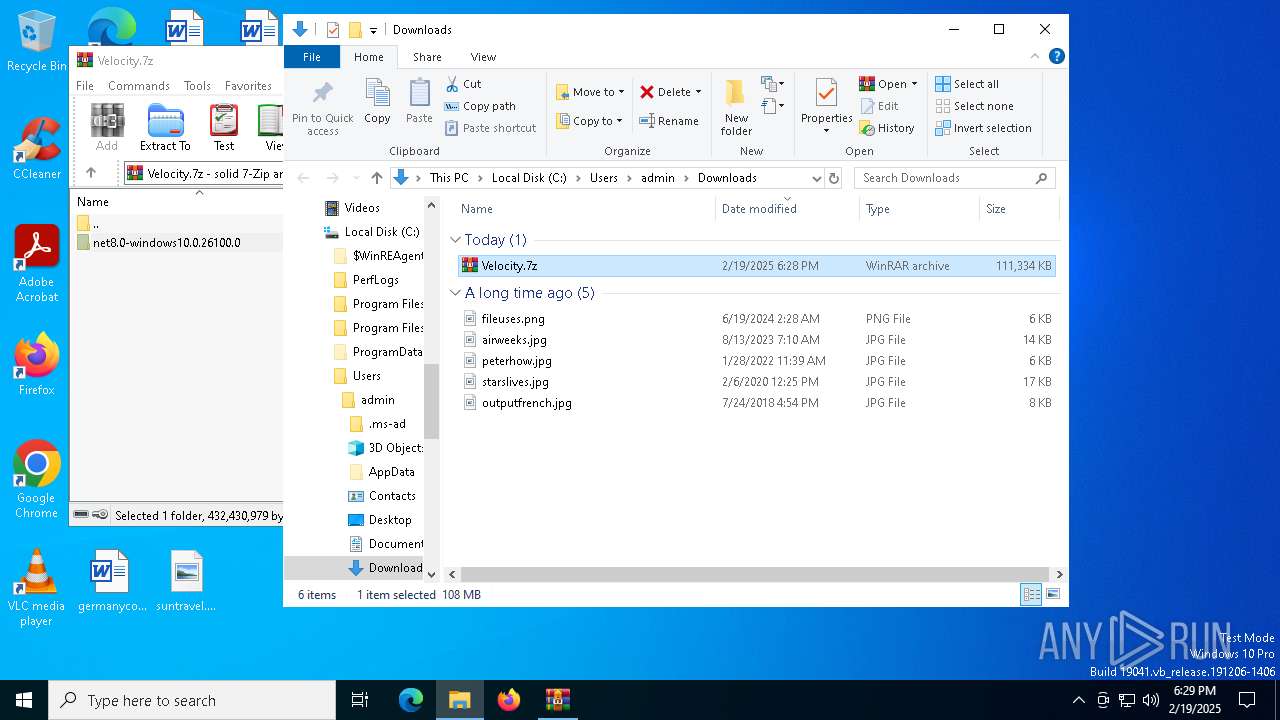
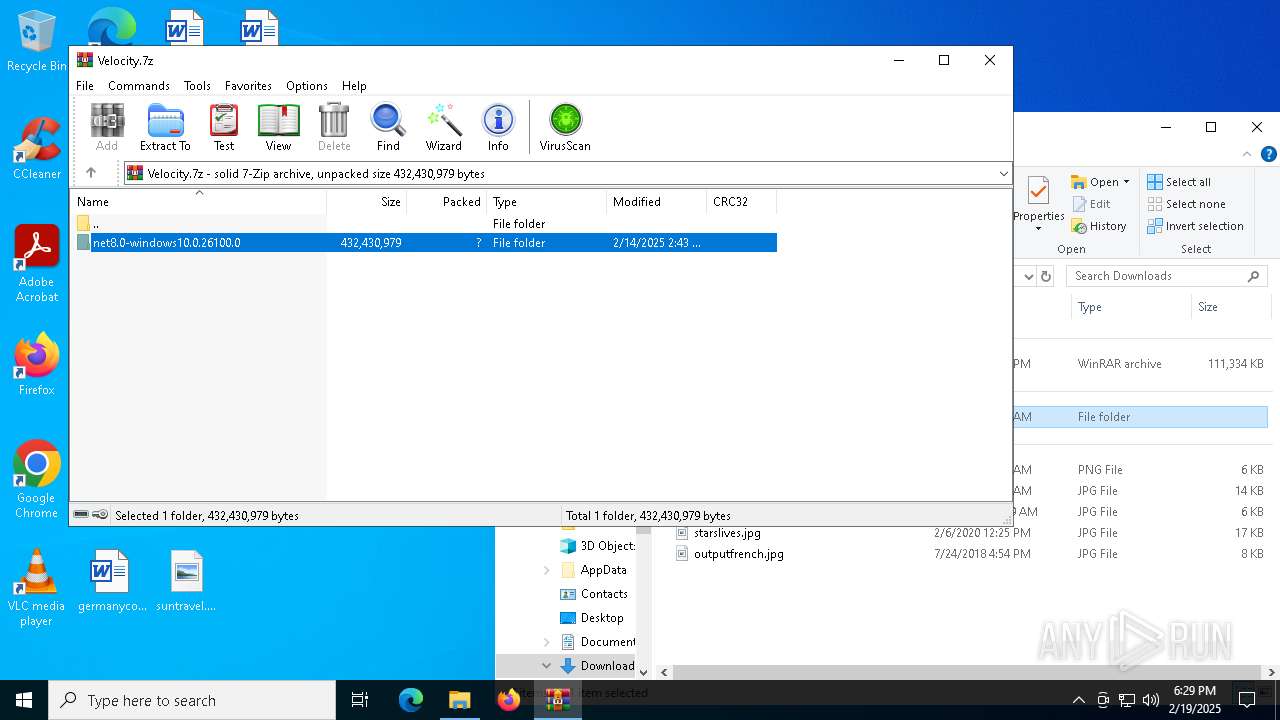
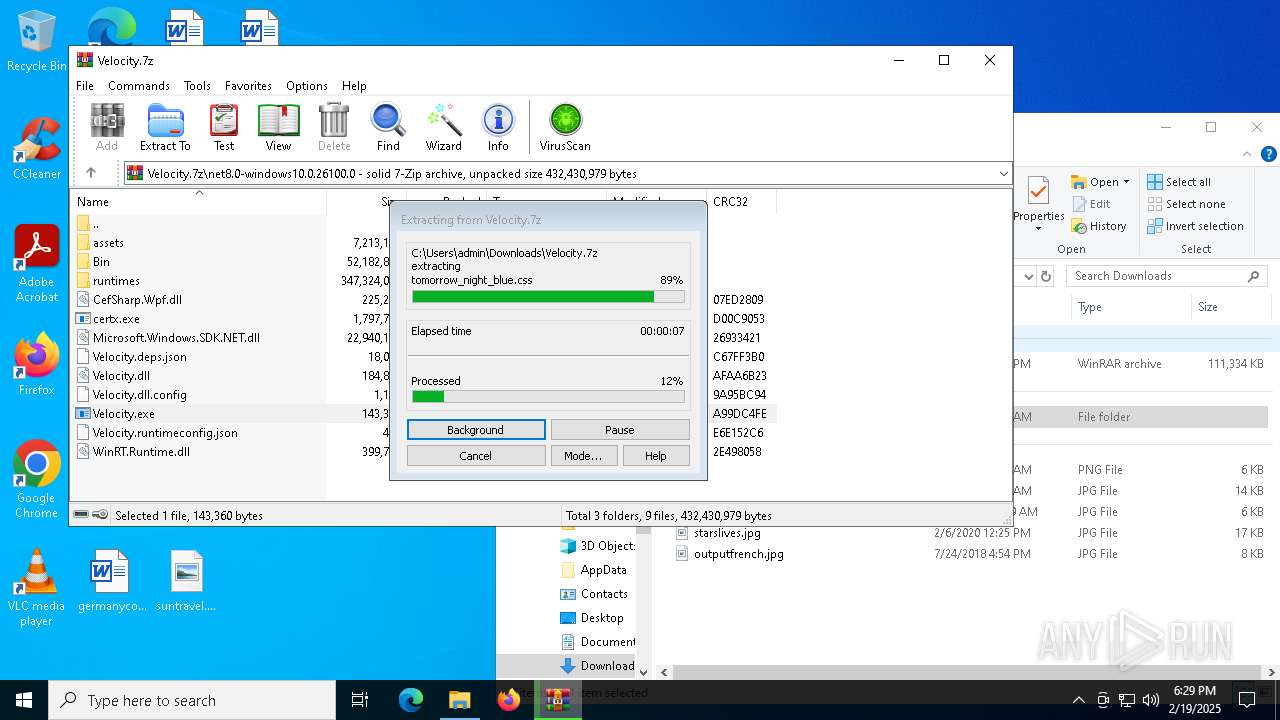
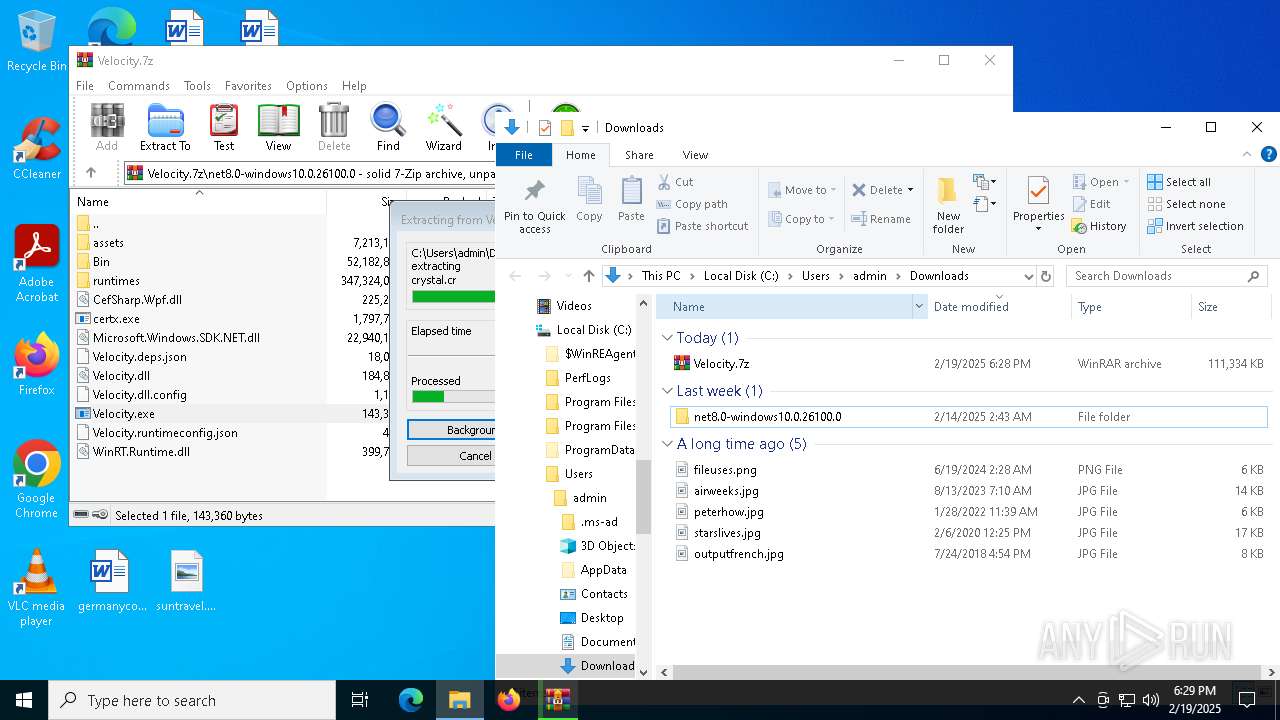
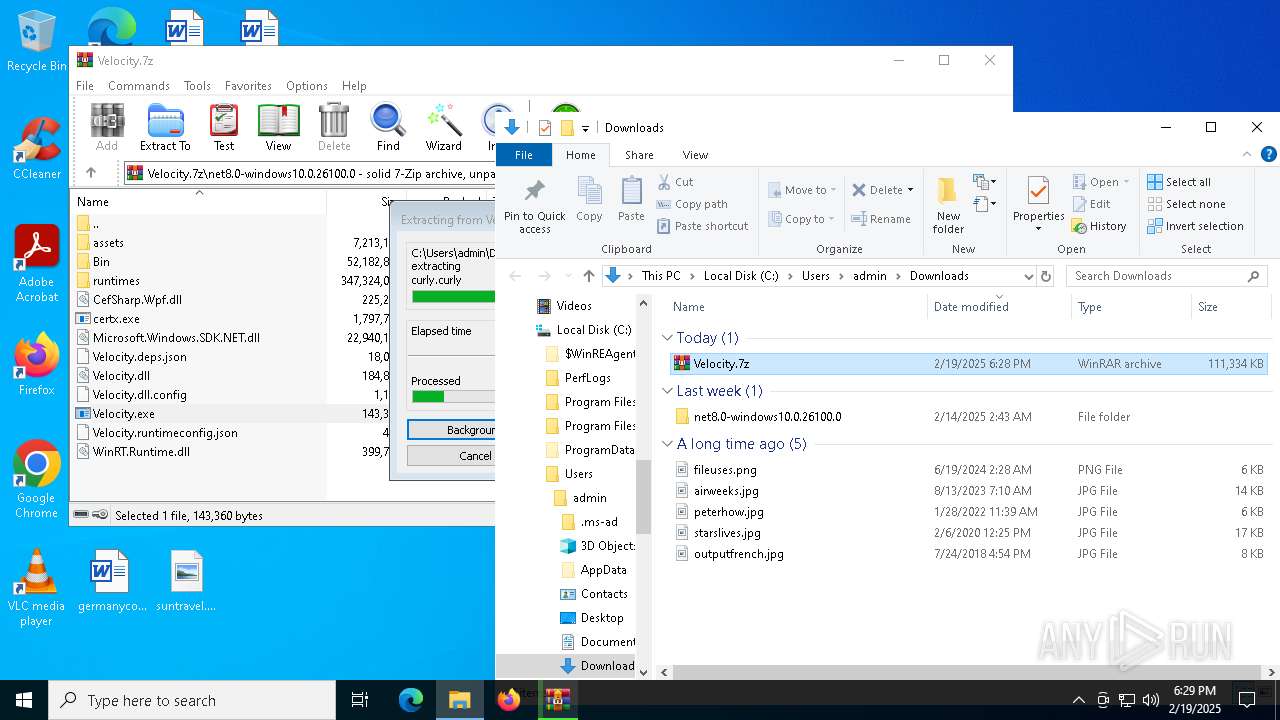
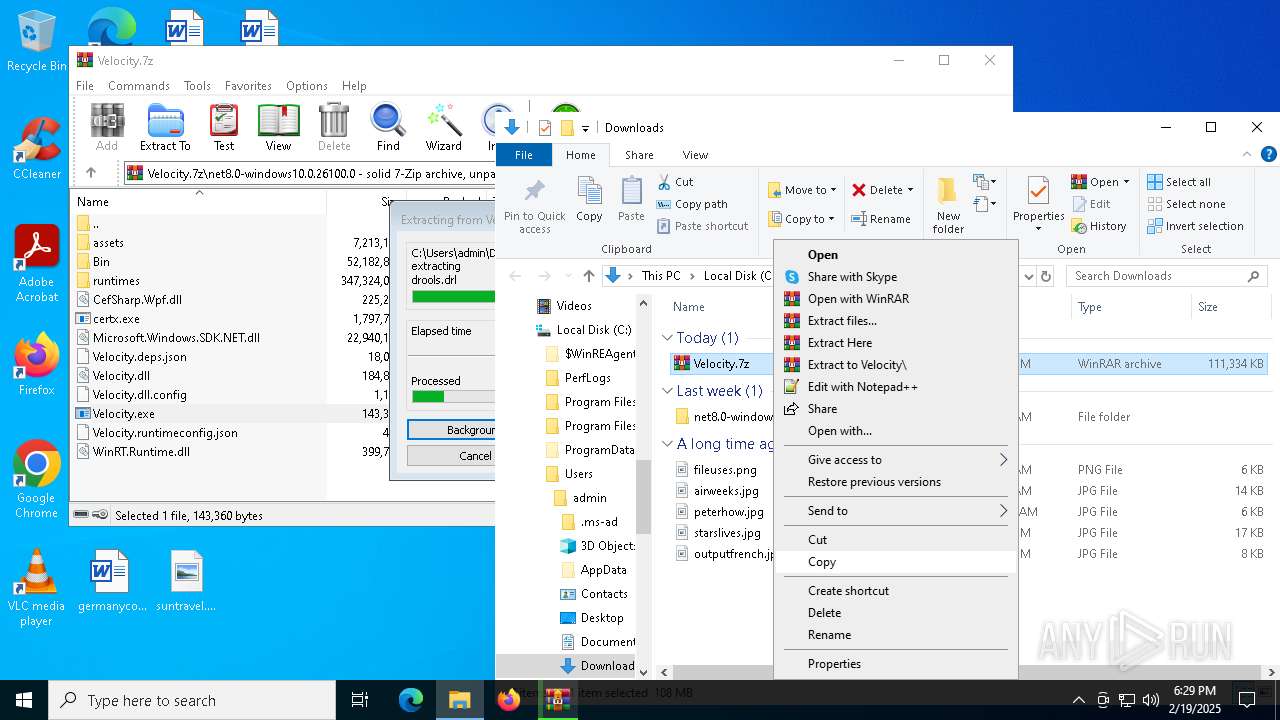
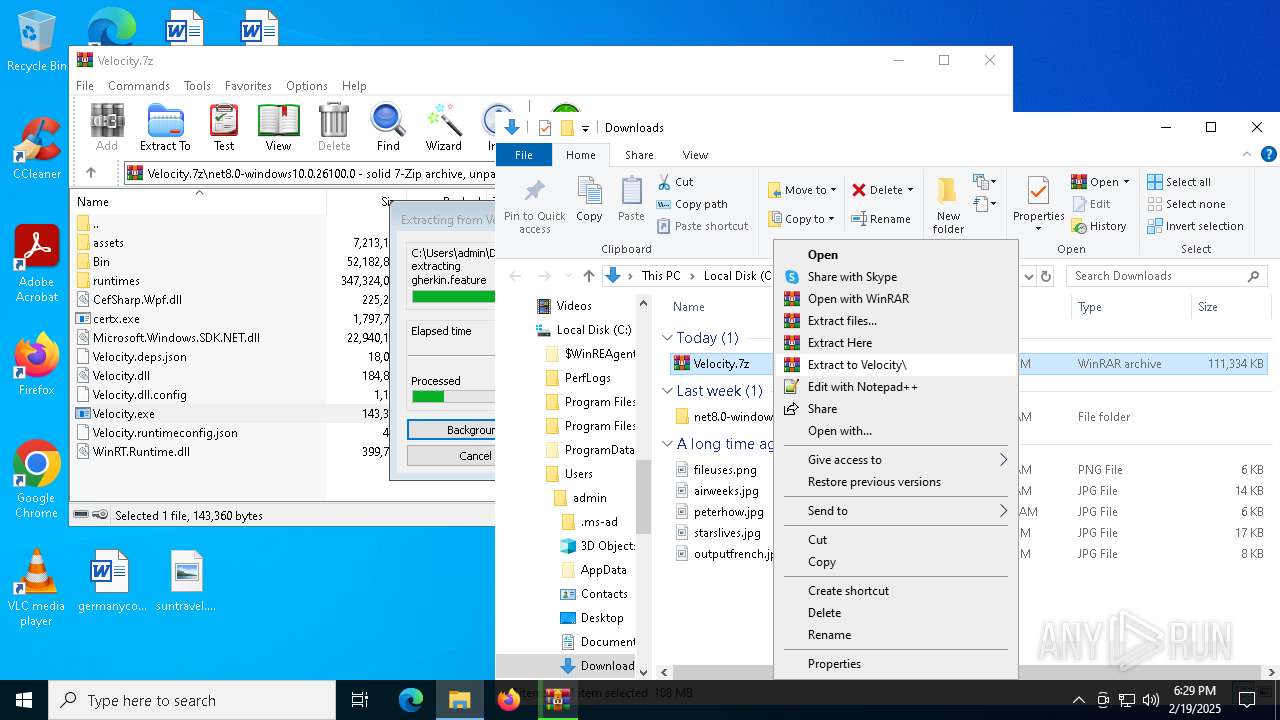
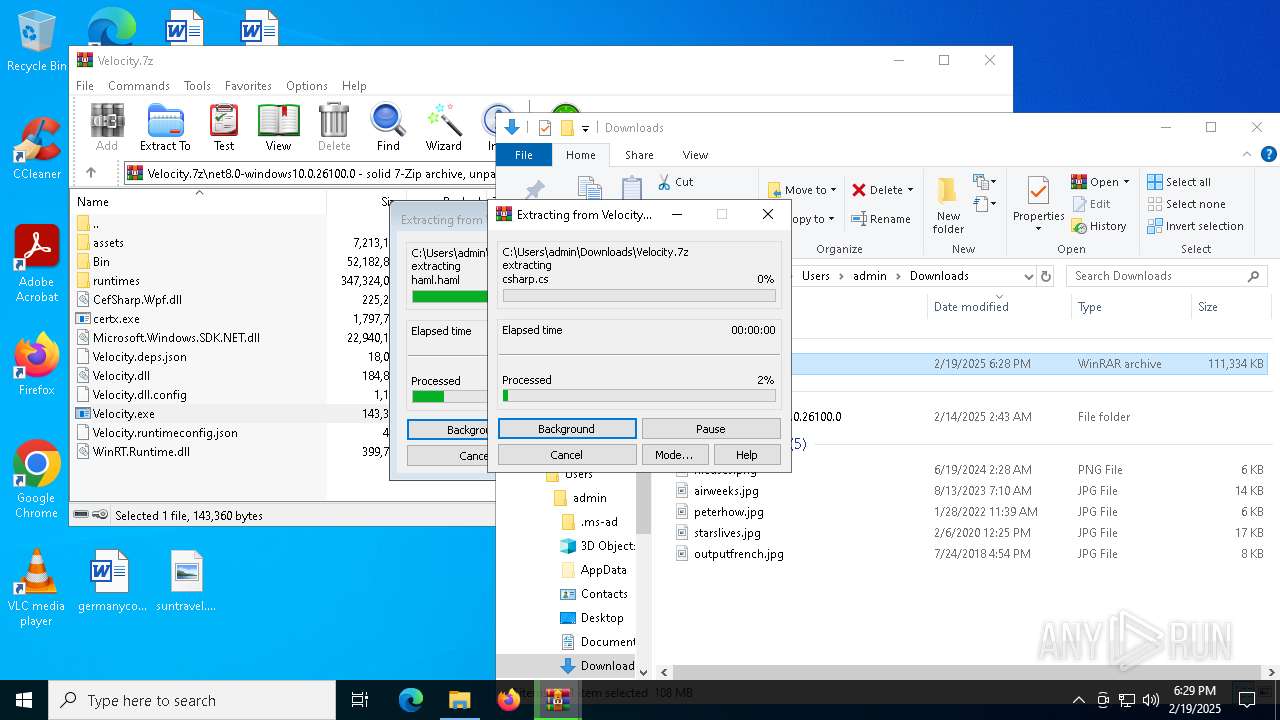
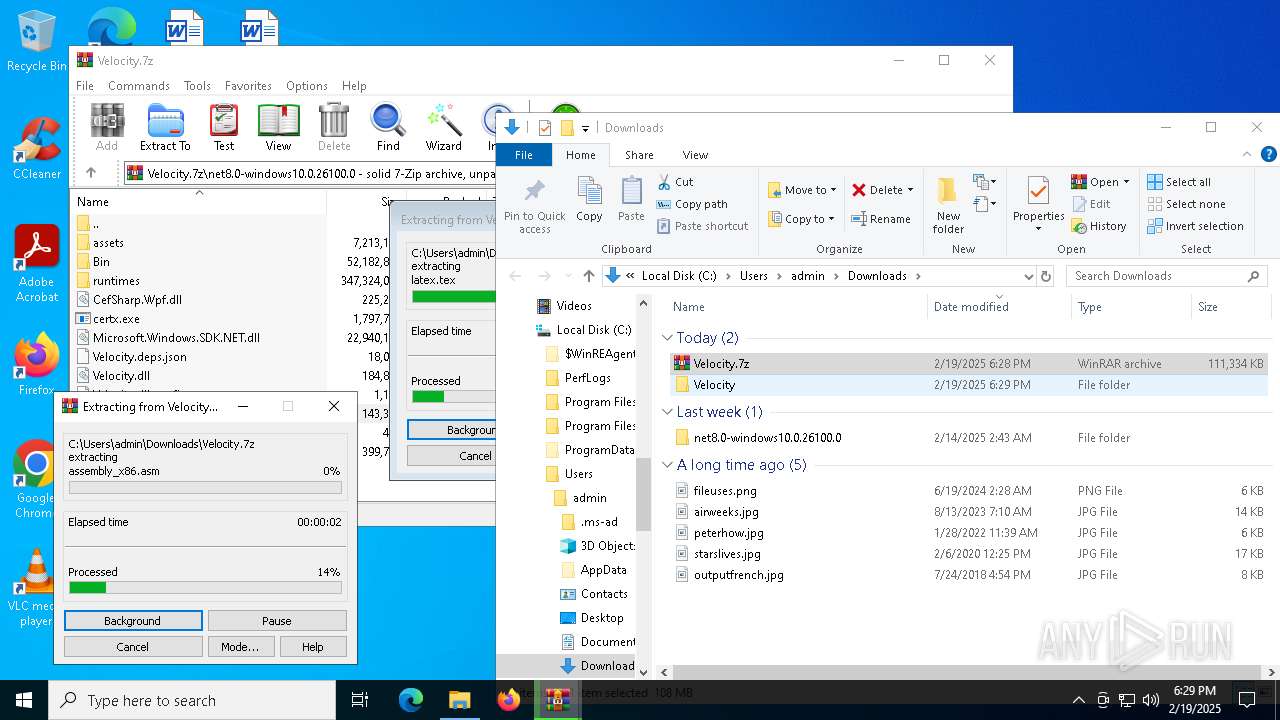
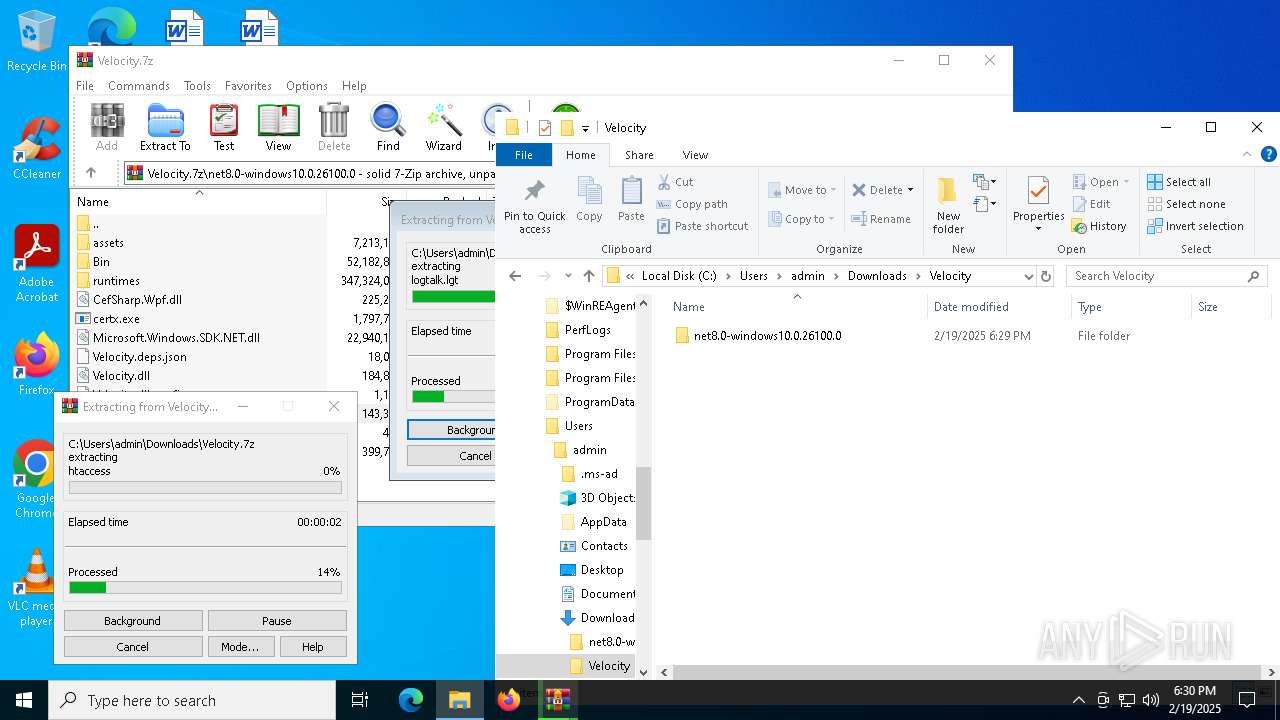
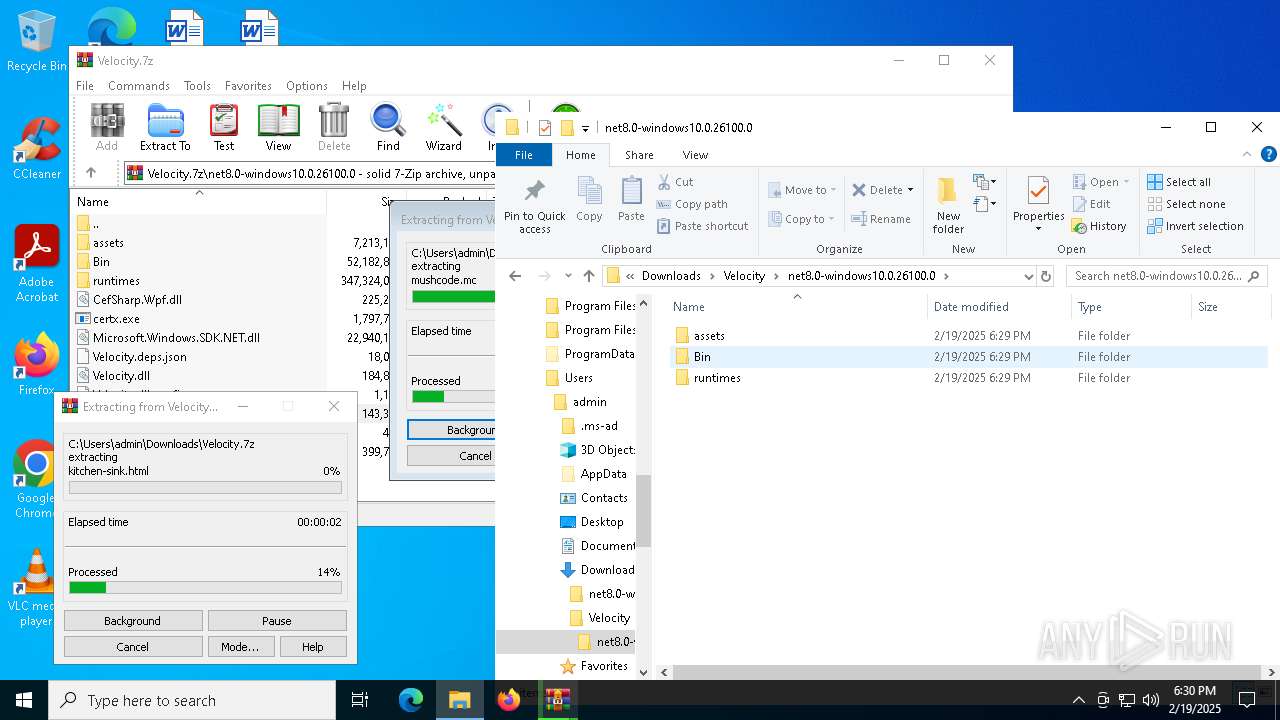
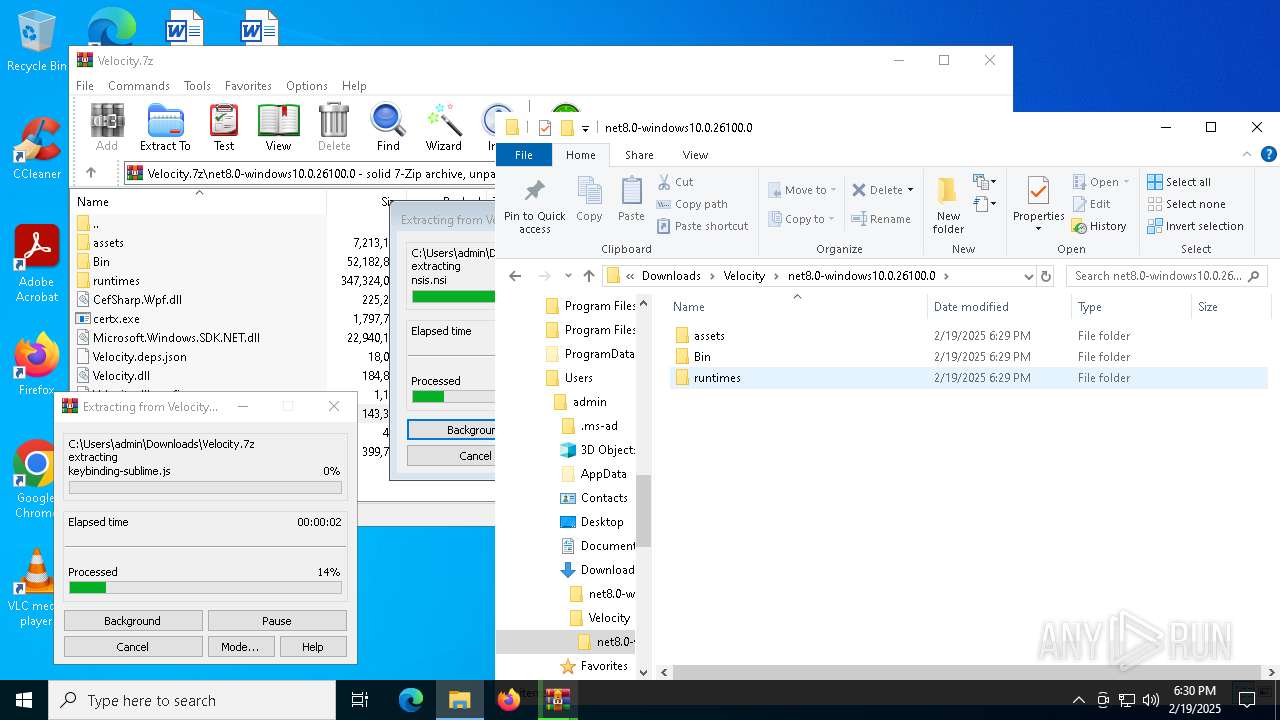
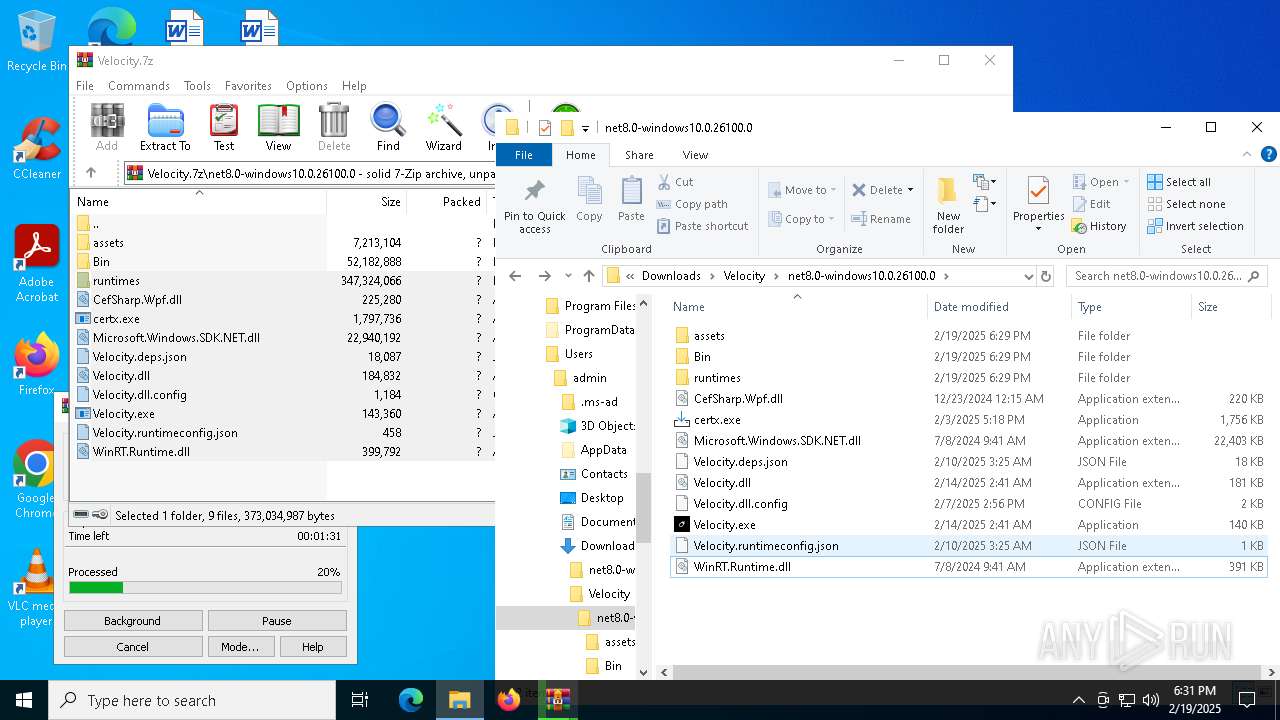
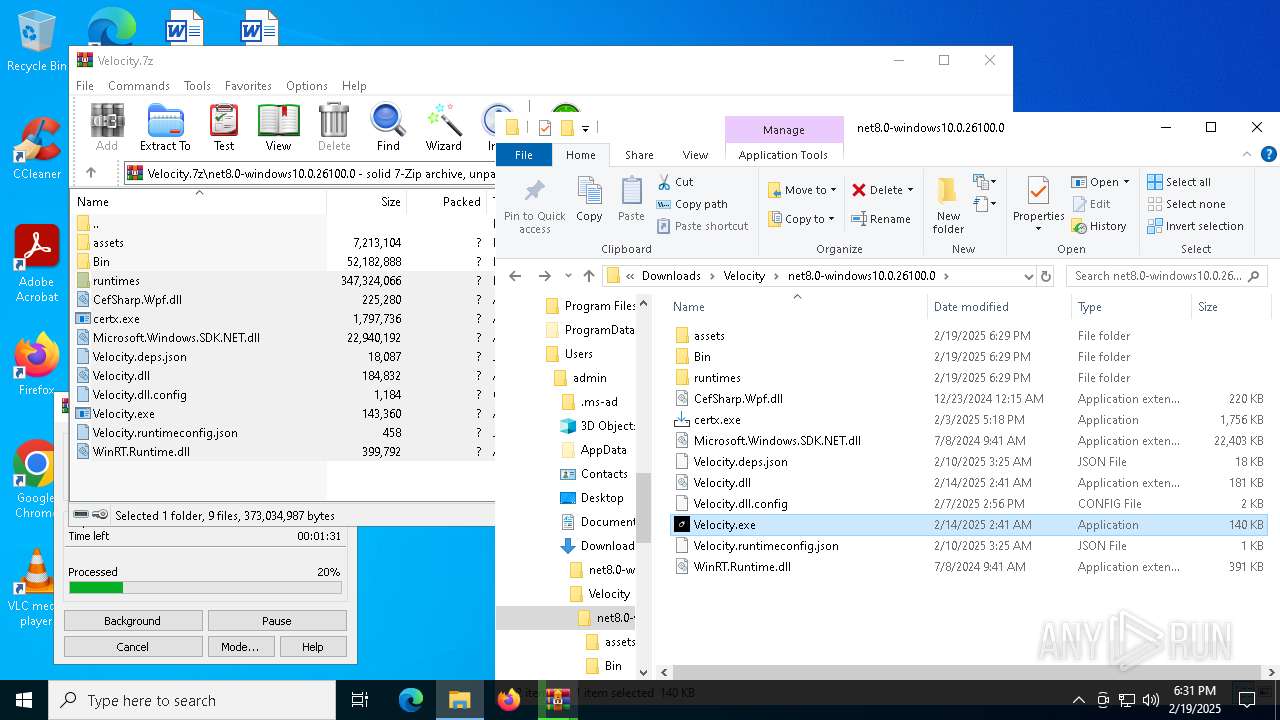
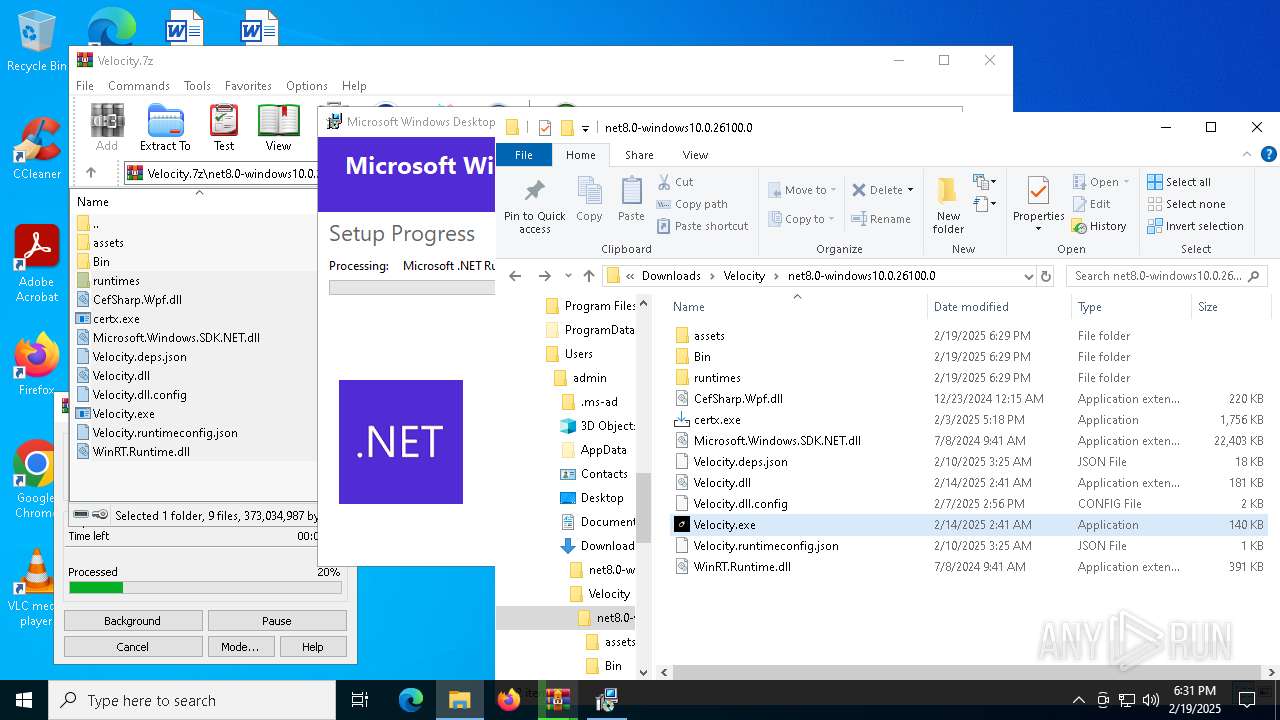
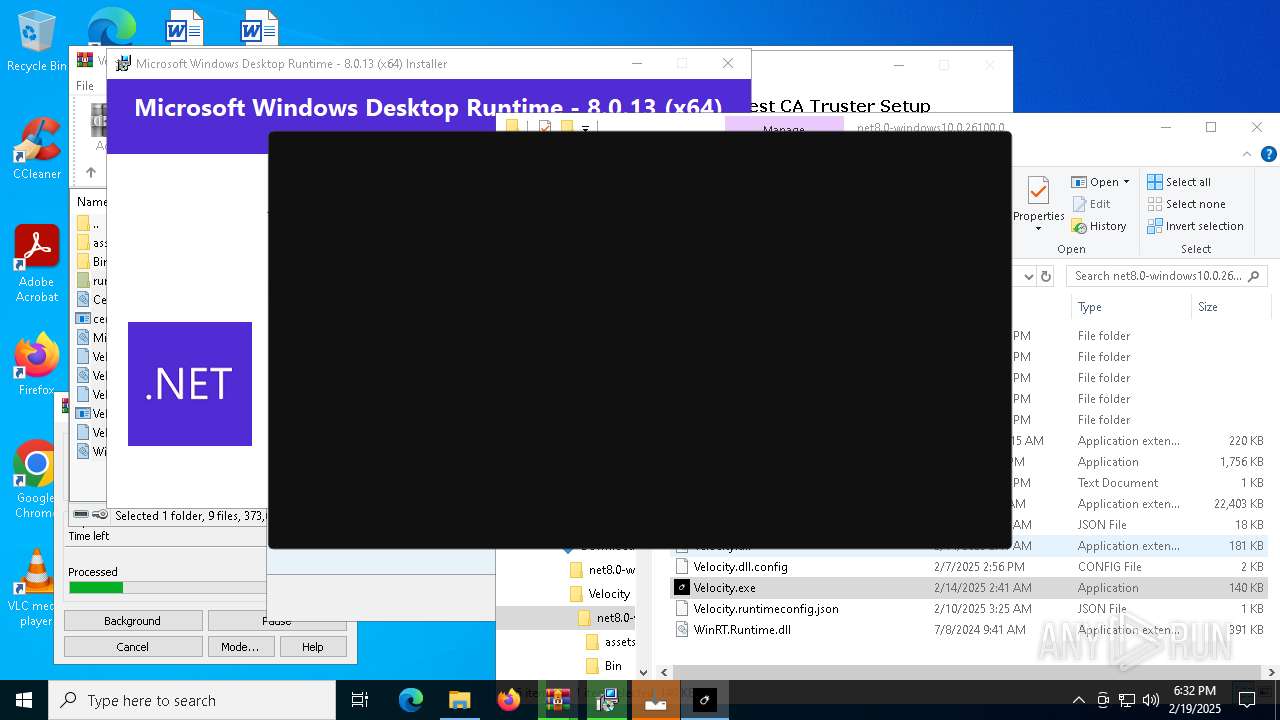
Manual execution by a user
- WinRAR.exe (PID: 7944)
- WinRAR.exe (PID: 7348)
- Velocity.exe (PID: 6420)
- certx.exe (PID: 5200)
- Velocity.exe (PID: 7380)
The sample compiled with english language support
- WinRAR.exe (PID: 7944)
- msedge.exe (PID: 6644)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 1920)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 7456)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
- msiexec.exe (PID: 7356)
- certx.tmp (PID: 5828)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7944)
- msedge.exe (PID: 6644)
- msedge.exe (PID: 8112)
- msiexec.exe (PID: 7356)
Create files in a temporary directory
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 7456)
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
Process checks computer location settings
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 7456)
- certx.tmp (PID: 1468)
Reads the machine GUID from the registry
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
- msiexec.exe (PID: 7356)
- Certmgr.exe (PID: 7924)
- Certmgr.exe (PID: 7676)
- Certmgr.exe (PID: 7748)
- Certmgr.exe (PID: 2312)
- Certmgr.exe (PID: 6512)
- Certmgr.exe (PID: 6072)
- Certmgr.exe (PID: 7724)
- Certmgr.exe (PID: 4824)
- Certmgr.exe (PID: 5548)
- Certmgr.exe (PID: 5308)
- Certmgr.exe (PID: 4968)
Creates files in the program directory
- windowsdesktop-runtime-8.0.13-win-x64.exe (PID: 6272)
Reads the software policy settings
- msiexec.exe (PID: 7356)
Creates a software uninstall entry
- msiexec.exe (PID: 7356)
- certx.tmp (PID: 5828)
Starts MODE.COM to configure console settings
- mode.com (PID: 3420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
330
Monitored processes
188
Malicious processes
9
Suspicious processes
56
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5036 --field-trial-handle=2268,i,15449151998908296298,889257713808170185,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 628 | certmgr.exe -crl -add /all .\6-Pikachu_File_Sub_CA-G1.crl -s -r currentUser AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 4294967295 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=6964 --field-trial-handle=2256,i,13608460910372678245,6531924695338984296,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1172 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6380 --field-trial-handle=2352,i,1429504241378497055,3243666095275031895,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | certmgr.exe -crl -add /all .\0-Pikachu_Test_CA_RSA-G2.crl -s -r localMachine AuthRoot | C:\Program Files (x86)\Pikacu Test CA Truster\Scripts\Certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 10.0.14393.795 (rs1_release_sec.170105-1850) Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --mojo-platform-channel-handle=7016 --field-trial-handle=2352,i,1429504241378497055,3243666095275031895,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | C:\Windows\syswow64\MsiExec.exe -Embedding 2EC958437CF6DE77E9C38E5AAD901975 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5504 --field-trial-handle=2352,i,1429504241378497055,3243666095275031895,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\AppData\Local\Temp\is-2CTA4.tmp\certx.tmp" /SL5="$5043E,908493,832512,C:\Users\admin\Downloads\Velocity\net8.0-windows10.0.26100.0\certx.exe" | C:\Users\admin\AppData\Local\Temp\is-2CTA4.tmp\certx.tmp | — | certx.exe | |||||||||||
User: admin Company: Pikachu Software Integrity Level: MEDIUM Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
101 262
Read events
100 147
Write events
1 030
Delete events
85
Modification events
| (PID) Process: | (5464) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5464) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5464) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5464) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5464) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5464) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6256) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
547
Suspicious files
2 694
Text files
1 195
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF136574.TMP | — | |
MD5:— | SHA256:— | |||
| 6256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF136564.TMP | — | |
MD5:— | SHA256:— | |||
| 6256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136574.TMP | — | |
MD5:— | SHA256:— | |||
| 6256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF136574.TMP | — | |
MD5:— | SHA256:— | |||
| 6256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF136593.TMP | — | |
MD5:— | SHA256:— | |||
| 6256 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
131
DNS requests
149
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7528 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7528 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3524 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1740402680&P2=404&P3=2&P4=M7UUpHfOl6XifksaqZAICo6103VmKyzx2A2NV0qk8P4EbsTm1ukTlZagMwmhjpHeK7i5dvZ6IySw8xZSFvhv5w%3d%3d | unknown | — | — | whitelisted |
1668 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3524 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1740402680&P2=404&P3=2&P4=M7UUpHfOl6XifksaqZAICo6103VmKyzx2A2NV0qk8P4EbsTm1ukTlZagMwmhjpHeK7i5dvZ6IySw8xZSFvhv5w%3d%3d | unknown | — | — | whitelisted |
3524 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1740402680&P2=404&P3=2&P4=M7UUpHfOl6XifksaqZAICo6103VmKyzx2A2NV0qk8P4EbsTm1ukTlZagMwmhjpHeK7i5dvZ6IySw8xZSFvhv5w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6092 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 92.123.104.40:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.158:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6256 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6488 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
filerift.com |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
6488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
6488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
6488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
3128 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
3128 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
3128 | CefSharp.BrowserSubprocess.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
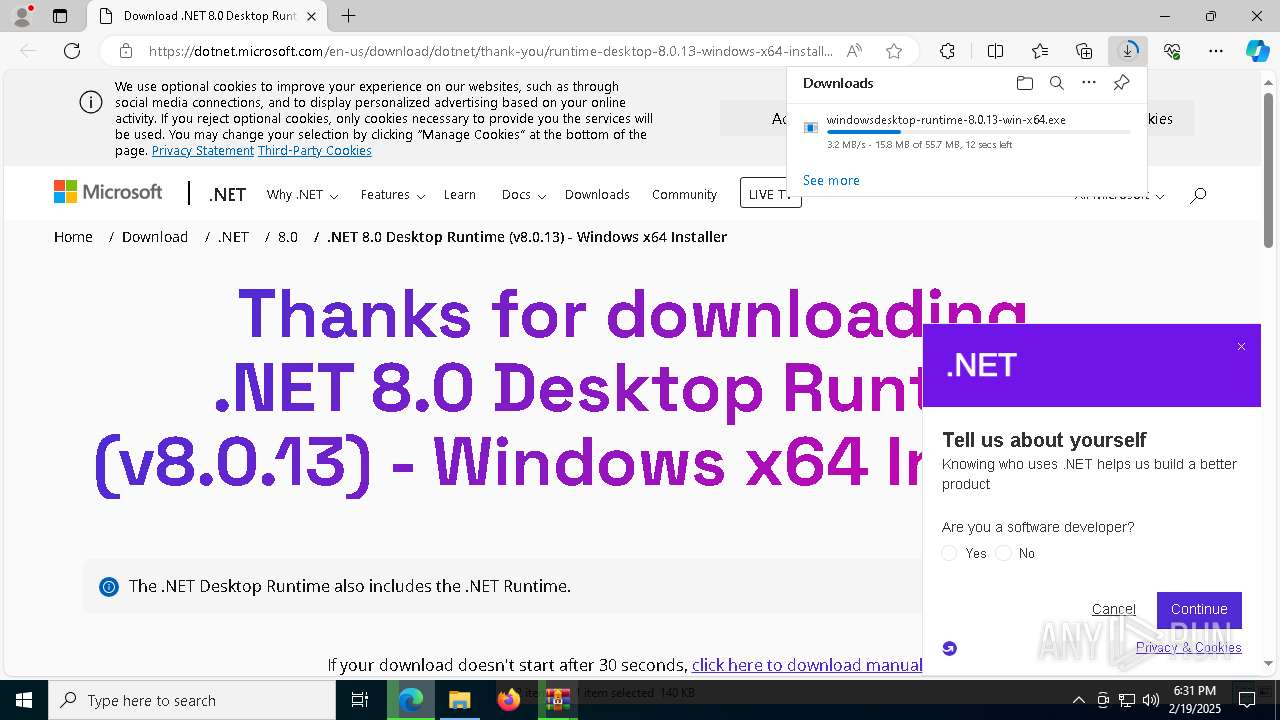
Process | Message |
|---|---|
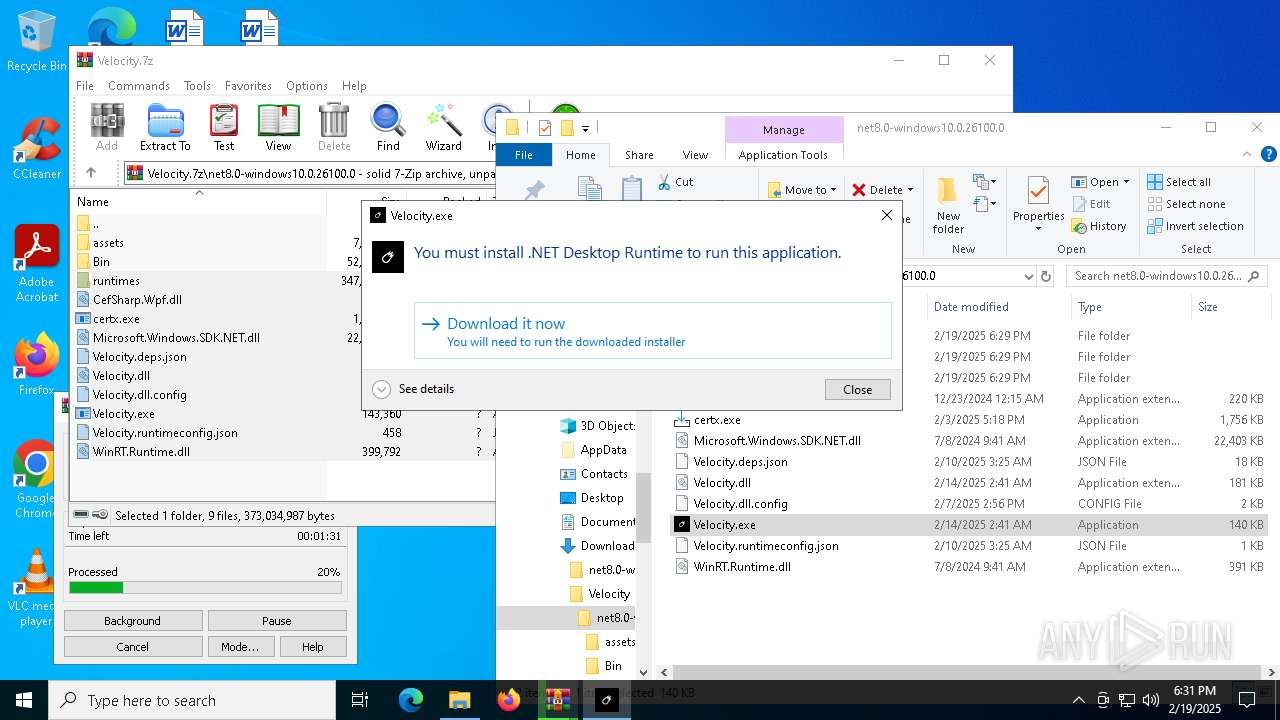
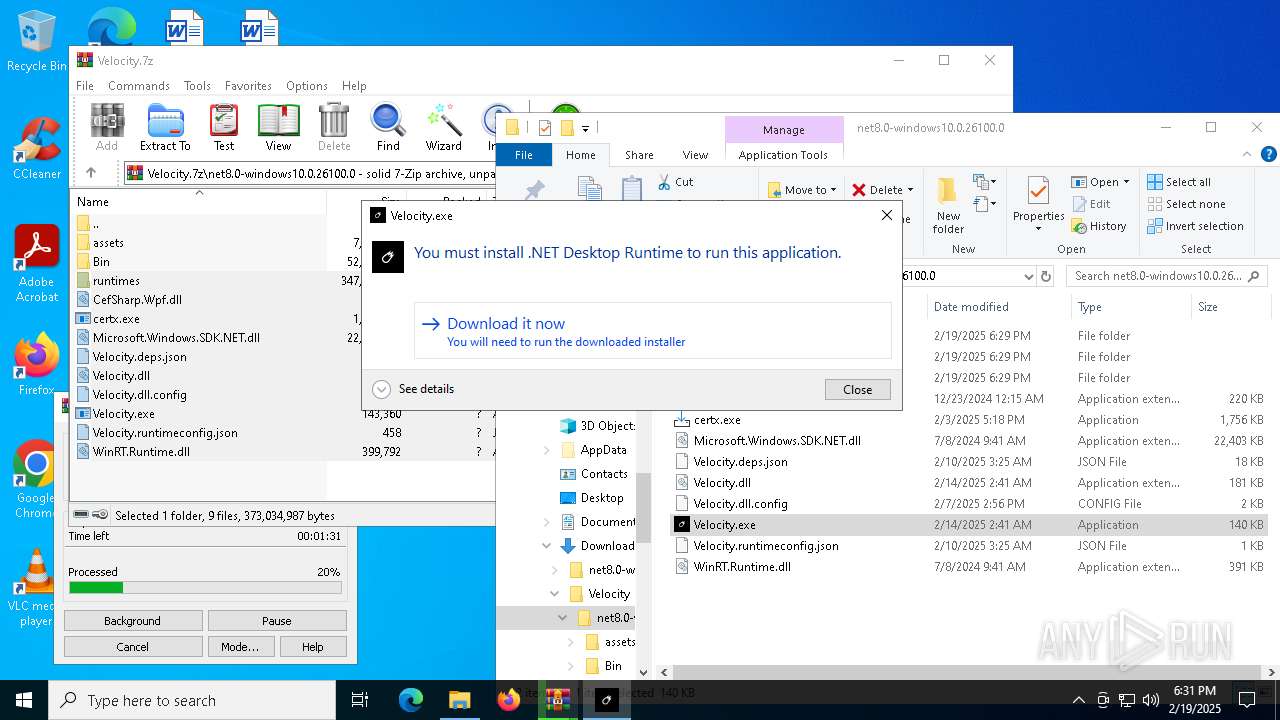
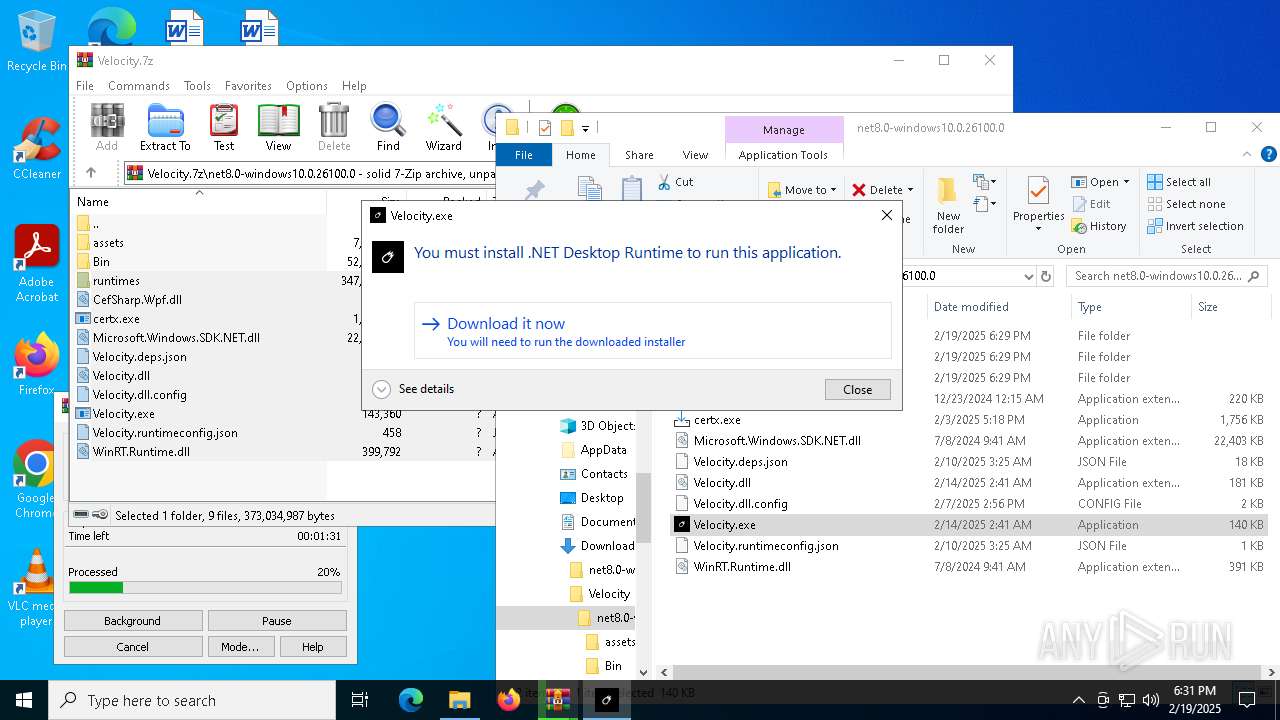
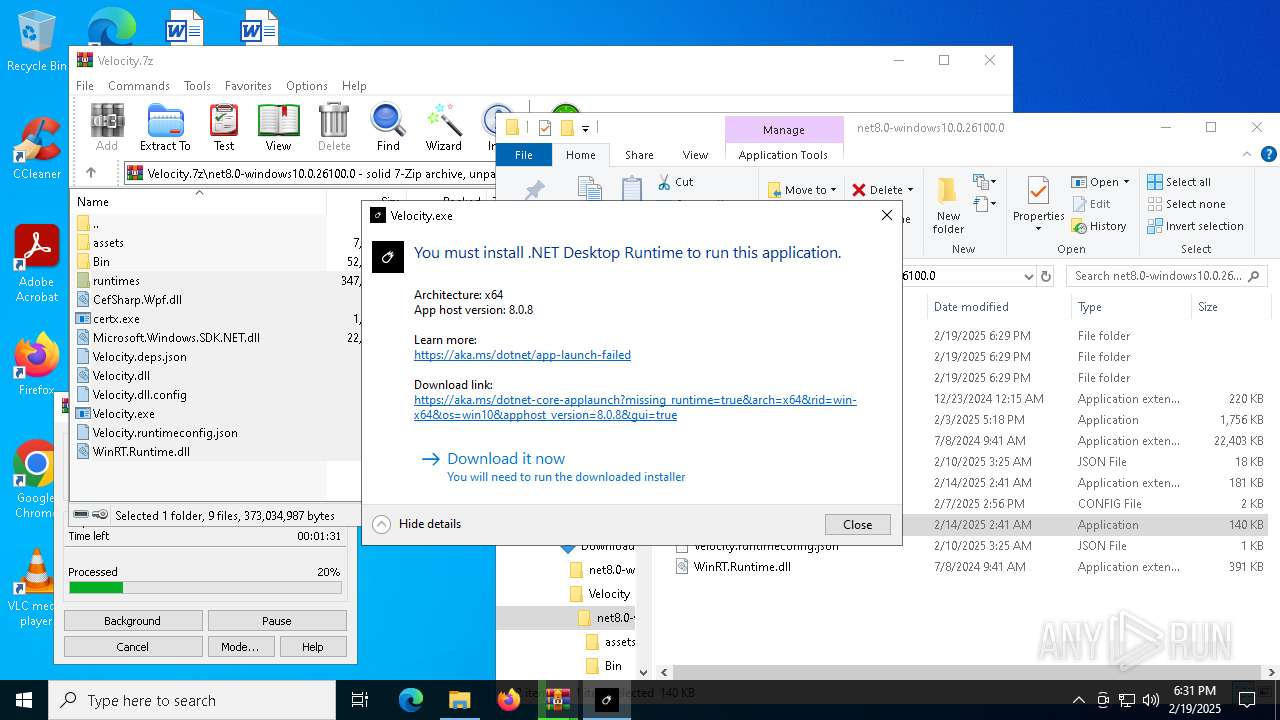
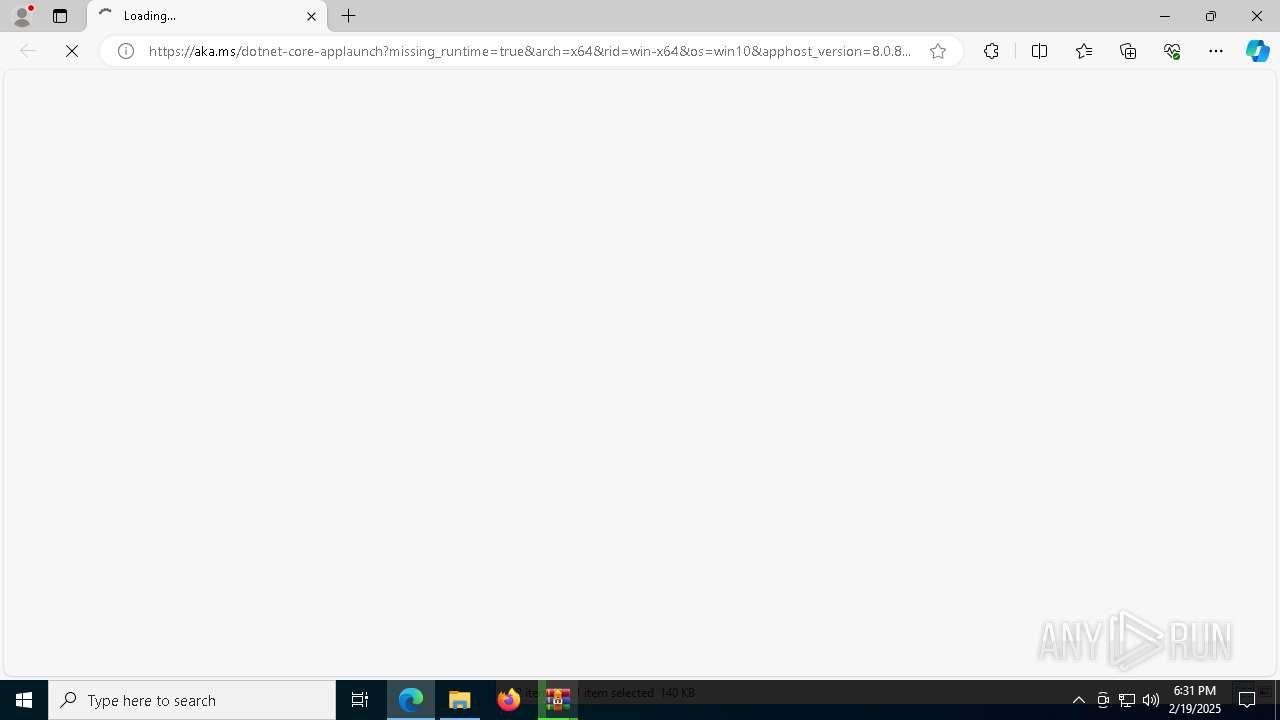
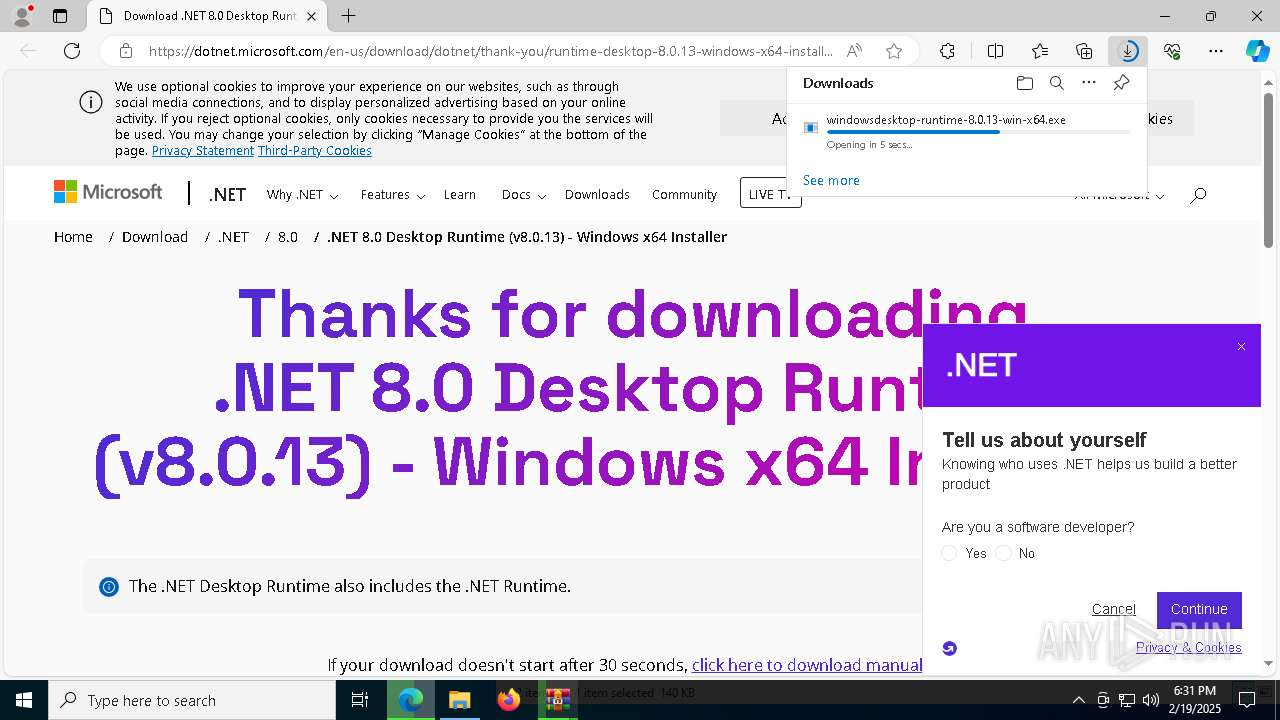
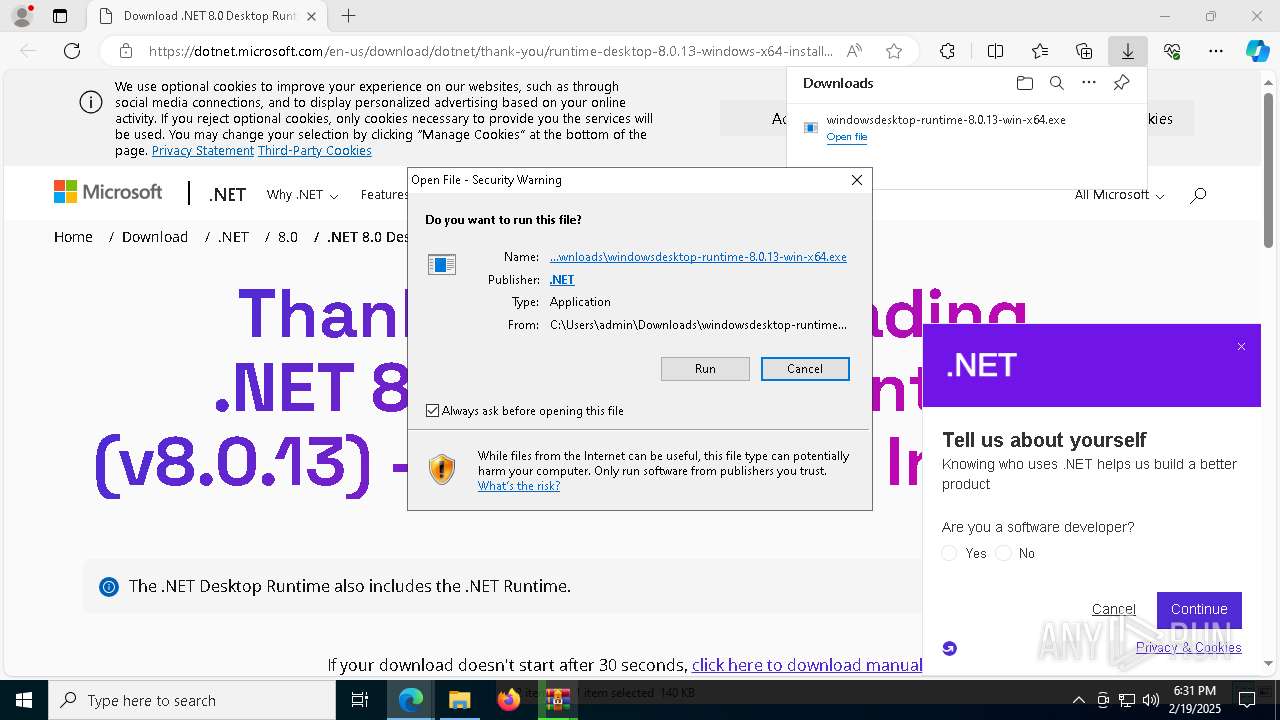
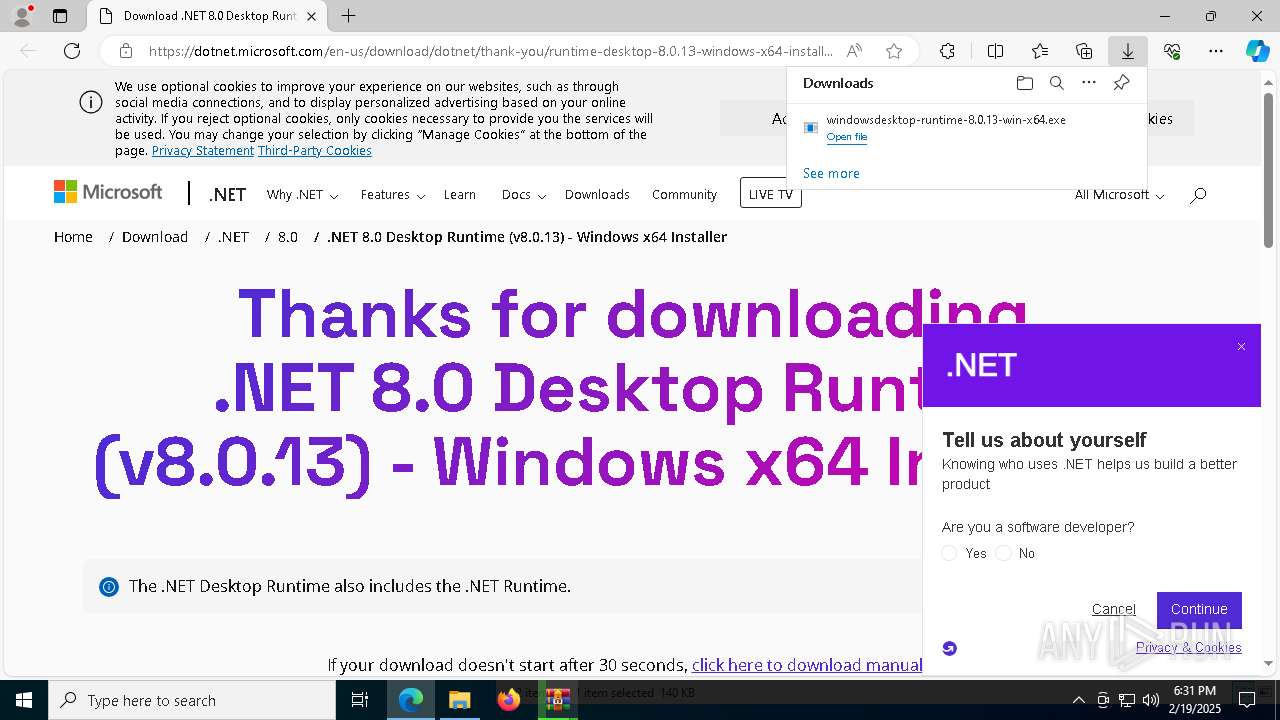
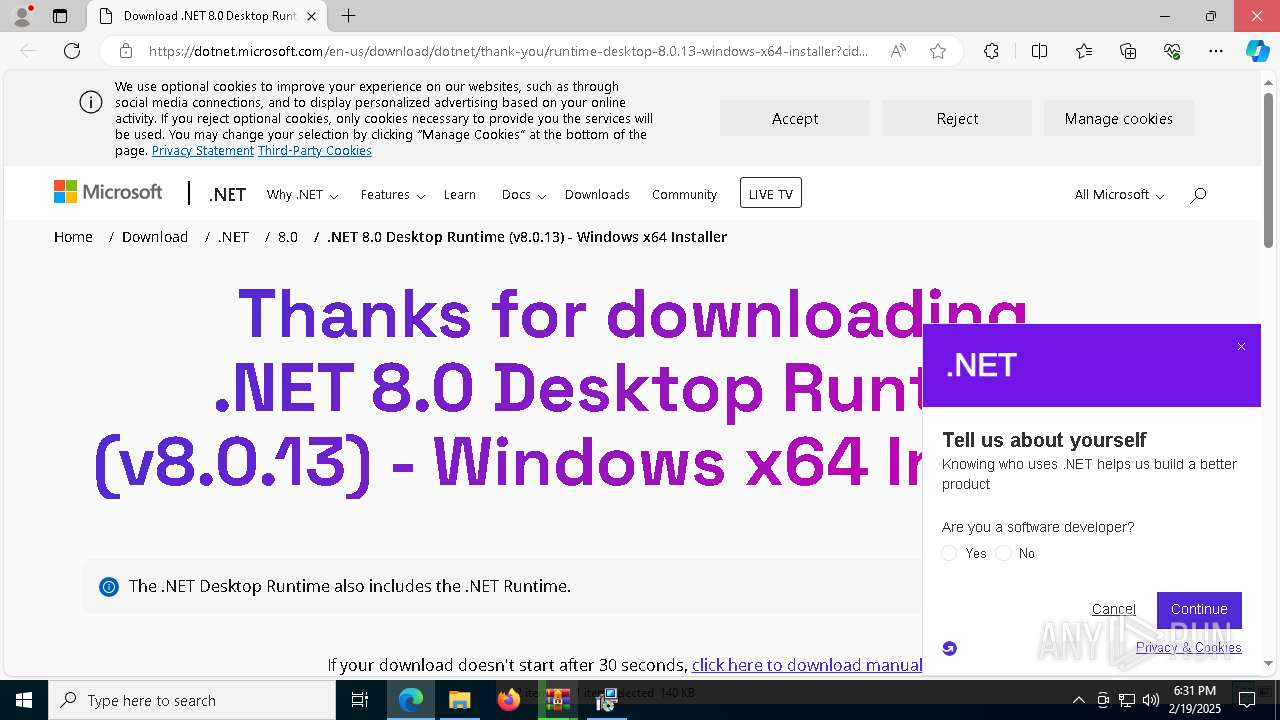
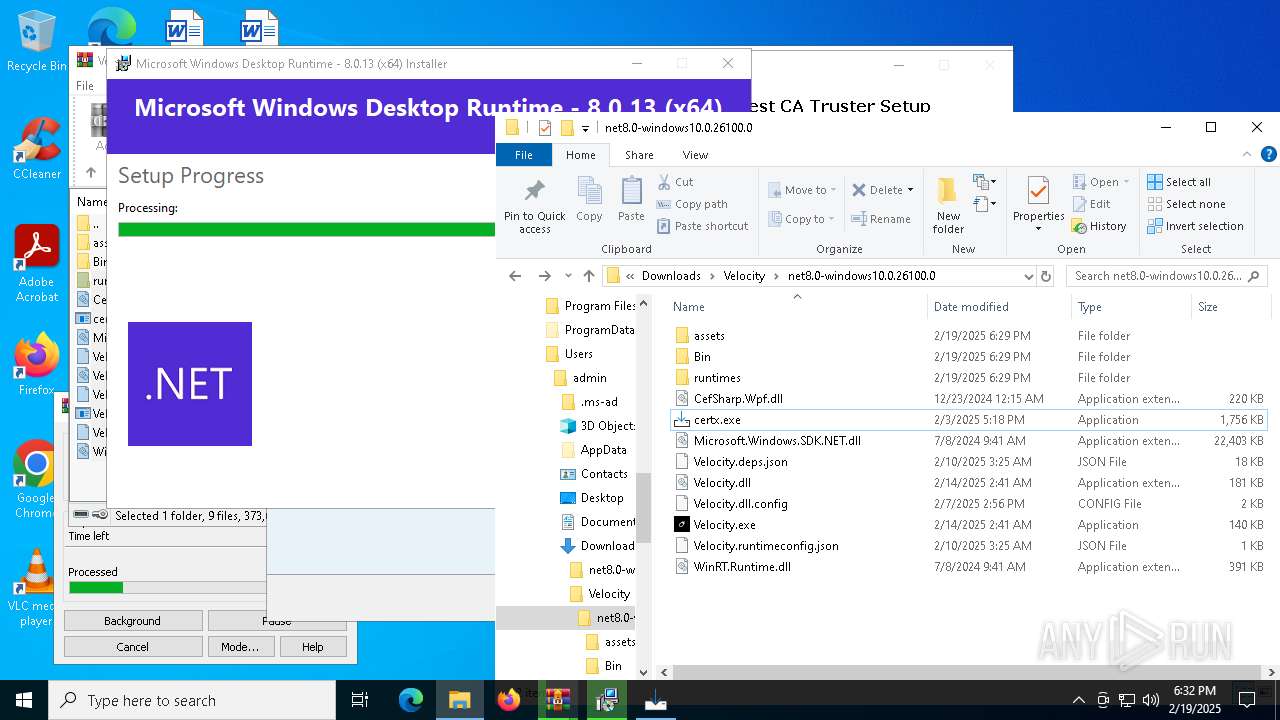
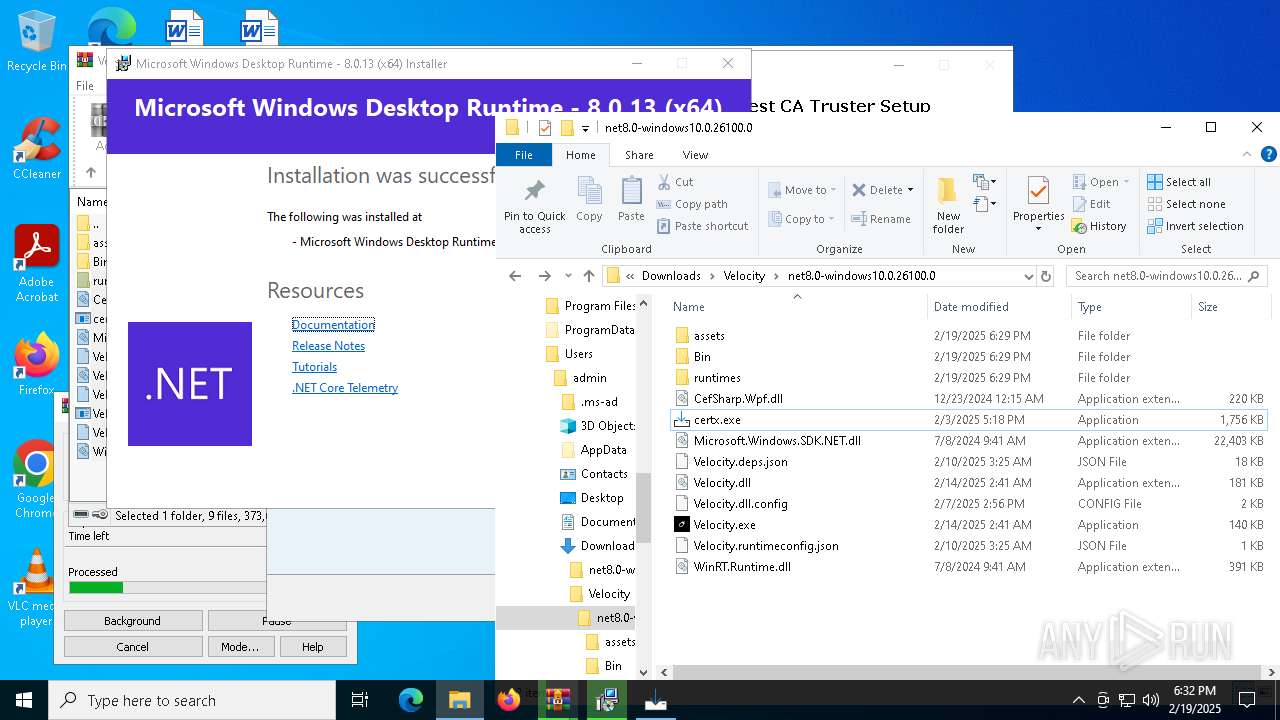
Velocity.exe | You must install .NET to run this application.
App: C:\Users\admin\Downloads\Velocity\net8.0-windows10.0.26100.0\Velocity.exe
Architecture: x64
App host version: 8.0.8
.NET location: Not found
Learn more:
https://aka.ms/dotnet/app-launch-failed
Download the .NET runtime:
https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win-x64&os=win10&apphost_version=8.0.8 |