| download: | version5b0ee404c2d18.exe |
| Full analysis: | https://app.any.run/tasks/15b39022-a708-49e5-9fd6-697b6d90a54f |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2018, 07:27:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A790834EE22574EFE8E70CE537FD5BF8 |
| SHA1: | 400BB993923D8821CDA777A849E96356D4CA467A |
| SHA256: | 9B932351C7EEAC24EF089C2907283C4D61C0974224FC0A6C5814B8B2B3E536C8 |
| SSDEEP: | 393216:cHFkbrDjtCte6fGAOq//9xo1xll4Y/cPQgCaNni0Z1hJD4mRbcY1fsuTEvz4Af5n:o4rn8kUGD29xOLEPXzzTRbf1fsuLiF |
MALICIOUS
Loads dropped or rewritten executable
- version5b0ee404c2d18.exe (PID: 3072)
Loads the Task Scheduler COM API
- version5b0ee404c2d18.exe (PID: 3072)
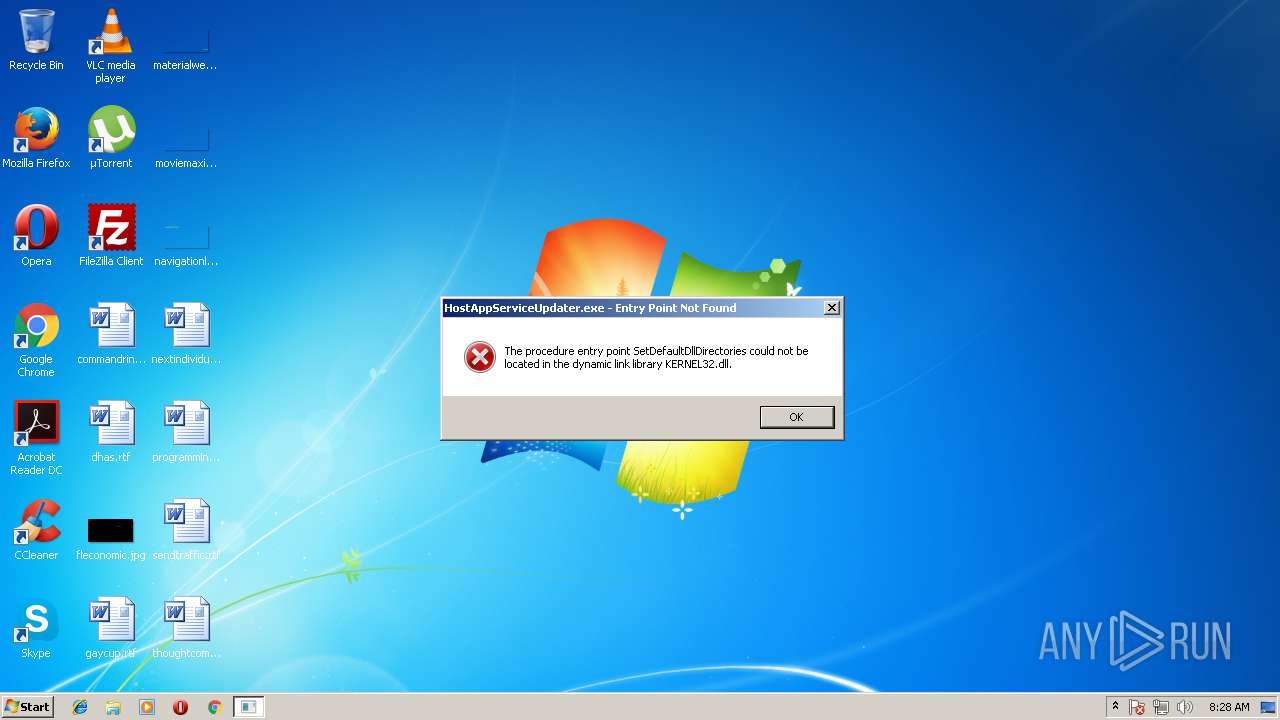
Application was dropped or rewritten from another process
- HostAppServiceUpdater.exe (PID: 3032)
SUSPICIOUS
Changes IE settings (feature browser emulation)
- version5b0ee404c2d18.exe (PID: 3072)
Executable content was dropped or overwritten
- version5b0ee404c2d18.exe (PID: 3072)
Creates a software uninstall entry
- version5b0ee404c2d18.exe (PID: 3072)
INFO
Dropped object may contain URL's
- version5b0ee404c2d18.exe (PID: 3072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:25 02:55:51+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 57856 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x33b6 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.273.2.777 |
| ProductVersionNumber: | 0.273.2.777 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | SweetLabs,Inc. |
| FileDescription: | App Explorer |
| FileVersion: | 0.0.0.0 |
| LegalCopyright: | © SweetLabs,Inc. |
| ProductName: | App Explorer |
| ProductVersion: | v0.273.2.777 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jul-2016 00:55:51 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | SweetLabs,Inc. |
| FileDescription: | App Explorer |
| FileVersion: | 0.0.0.0 |
| LegalCopyright: | © SweetLabs,Inc. |
| ProductName: | App Explorer |
| ProductVersion: | v0.273.2.777 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Jul-2016 00:55:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000615D | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45023 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.163 |
.data | 0x0000A000 | 0x00020338 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9824 |
.ndata | 0x0002B000 | 0x0002B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00056000 | 0x0000C750 | 0x0000C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.28227 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06488 | 1589 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.52489 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.65614 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.17423 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.68031 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.09695 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.0117 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.18158 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 2.03281 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.32052 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3032 | "C:\Users\admin\AppData\Local\Host App Service\Engine\HostAppServiceUpdater.exe" /LOGON | C:\Users\admin\AppData\Local\Host App Service\Engine\HostAppServiceUpdater.exe | — | explorer.exe | |||||||||||
User: admin Company: SweetLabs, Inc Integrity Level: MEDIUM Description: Host App Service Updater Exit code: 3221225785 Version: 0.273.2.777 Modules
| |||||||||||||||
| 3072 | "C:\Users\admin\AppData\Local\Temp\version5b0ee404c2d18.exe" | C:\Users\admin\AppData\Local\Temp\version5b0ee404c2d18.exe | explorer.exe | ||||||||||||
User: admin Company: SweetLabs,Inc. Integrity Level: MEDIUM Description: App Explorer Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
369
Read events
348
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3072) version5b0ee404c2d18.exe | Key: | HKEY_CURRENT_USER\Software\Host App Service |
| Operation: | write | Name: | ClientId |
Value: 80563094-a62d-47da-a319-c15a1159bf53 | |||
| (PID) Process: | (3072) version5b0ee404c2d18.exe | Key: | HKEY_CURRENT_USER\Software\Host App Service |
| Operation: | write | Name: | InstallDate |
Value: 2018-06-21 | |||
| (PID) Process: | (3072) version5b0ee404c2d18.exe | Key: | HKEY_CURRENT_USER\Software\Host App Service |
| Operation: | write | Name: | InstallDate2 |
Value: 7E532B5B00000000 | |||
| (PID) Process: | (3072) version5b0ee404c2d18.exe | Key: | HKEY_CURRENT_USER\Software\Host App Service\Sideload\Apps |
| Operation: | write | Name: | App Explorer |
Value: 32643404c9763e5e50dbcbb85d1ee63a23897ed0 | |||
| (PID) Process: | (3072) version5b0ee404c2d18.exe | Key: | HKEY_CURRENT_USER\Software\Host App Service |
| Operation: | write | Name: | InstallDir |
Value: %LOCALAPPDATA%\Host App Service | |||
| (PID) Process: | (3072) version5b0ee404c2d18.exe | Key: | HKEY_CURRENT_USER\Software\Host App Service |
| Operation: | write | Name: | Version |
Value: 0.273.2.777 | |||
| (PID) Process: | (3072) version5b0ee404c2d18.exe | Key: | HKEY_CURRENT_USER\Software\Host App Service\WebApps |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (3072) version5b0ee404c2d18.exe | Key: | HKEY_CURRENT_USER\Software\Host App Service |
| Operation: | write | Name: | InstallFresh |
Value: 1 | |||
| (PID) Process: | (3072) version5b0ee404c2d18.exe | Key: | HKEY_CURRENT_USER\Software\Host App Service |
| Operation: | write | Name: | InstallAppOrigin |
Value: | |||
| (PID) Process: | (3072) version5b0ee404c2d18.exe | Key: | HKEY_CURRENT_USER\Software\Host App Service |
| Operation: | write | Name: | InstallCampaign |
Value: | |||
Executable files
12
Suspicious files
1
Text files
26
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3072 | version5b0ee404c2d18.exe | C:\Users\admin\AppData\Local\Temp\nscB345.tmp | — | |
MD5:— | SHA256:— | |||
| 3072 | version5b0ee404c2d18.exe | C:\Users\admin\AppData\Local\Host App Service\Engine\HostAppServiceUpdaterMetrics.exe | executable | |
MD5:— | SHA256:— | |||
| 3072 | version5b0ee404c2d18.exe | C:\Users\admin\AppData\Local\Temp\App Explorer-2018-06-21.log | text | |
MD5:— | SHA256:— | |||
| 3072 | version5b0ee404c2d18.exe | C:\Users\admin\AppData\Local\Host App Service\Engine\HostAppServiceInterface.exe | executable | |
MD5:— | SHA256:— | |||
| 3072 | version5b0ee404c2d18.exe | C:\Users\admin\AppData\Local\Temp\nscB346.tmp\___aensis.dll | executable | |
MD5:— | SHA256:— | |||
| 3072 | version5b0ee404c2d18.exe | C:\Users\admin\AppData\Local\Host App Service\Engine\HostAppServiceUpdater.exe | executable | |
MD5:— | SHA256:— | |||
| 3072 | version5b0ee404c2d18.exe | C:\Users\admin\AppData\Local\Host App Service\Engine\WebAppHelper.exe | executable | |
MD5:— | SHA256:— | |||
| 3072 | version5b0ee404c2d18.exe | C:\Users\admin\AppData\Local\Host App Service\Engine\SLToolWrapper.dll | executable | |
MD5:— | SHA256:— | |||
| 3072 | version5b0ee404c2d18.exe | C:\Users\admin\AppData\Local\Host App Service\Engine\HostAppServiceUpdateManager.exe | executable | |
MD5:— | SHA256:— | |||
| 3072 | version5b0ee404c2d18.exe | C:\Users\admin\AppData\Local\Host App Service\Engine\SLTool.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report