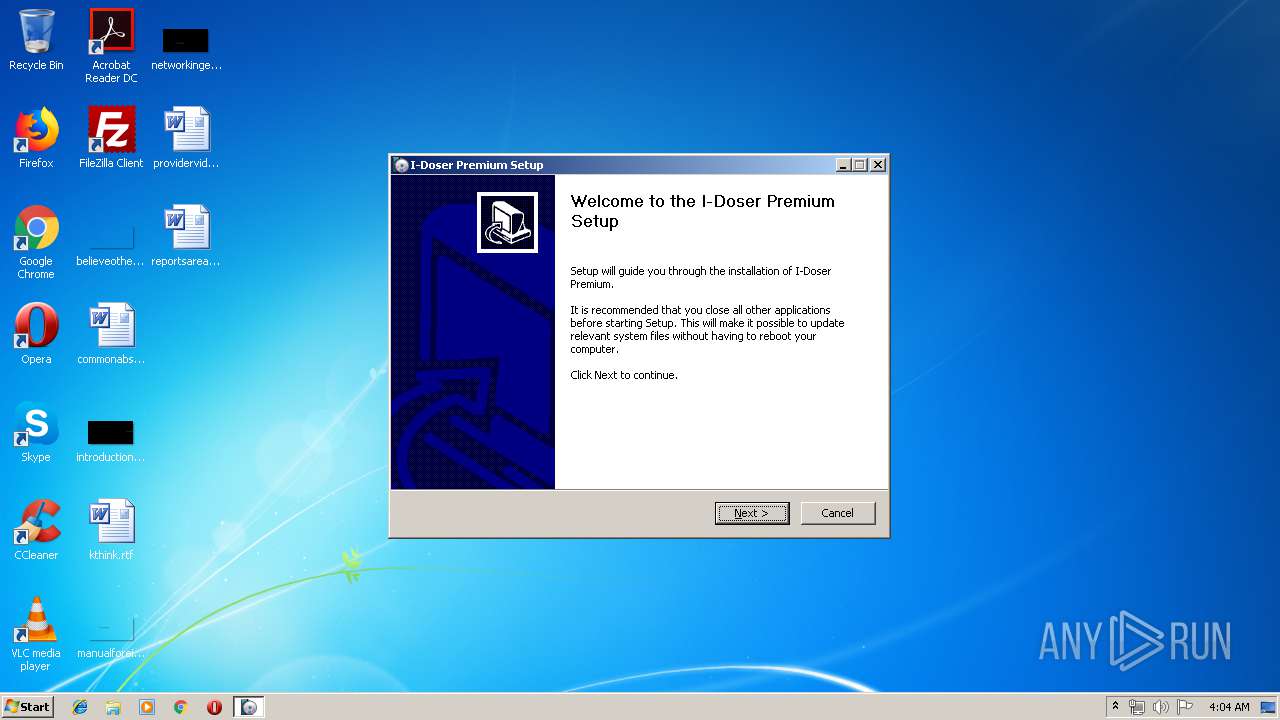
| File name: | IDoserPremiumSetup.exe |
| Full analysis: | https://app.any.run/tasks/f621bea9-41b8-4852-b855-021bd23fede3 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 03:04:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | DA4416AFE409D5EE5FF1588F66534FDD |
| SHA1: | 3184E3B73C68E97B02791F6C56D986C98E3AE3F0 |
| SHA256: | 9B91A426C323E22EB3CB82CB42B7A77FC8A70DEB354CF7AD68B2C23477CD99F5 |
| SSDEEP: | 196608:rDggsP9ZgWLsdqzI+zOwps7z+kukwrRdk5rAhMp3JZ:rDKejqceOwcStkw05rAsz |
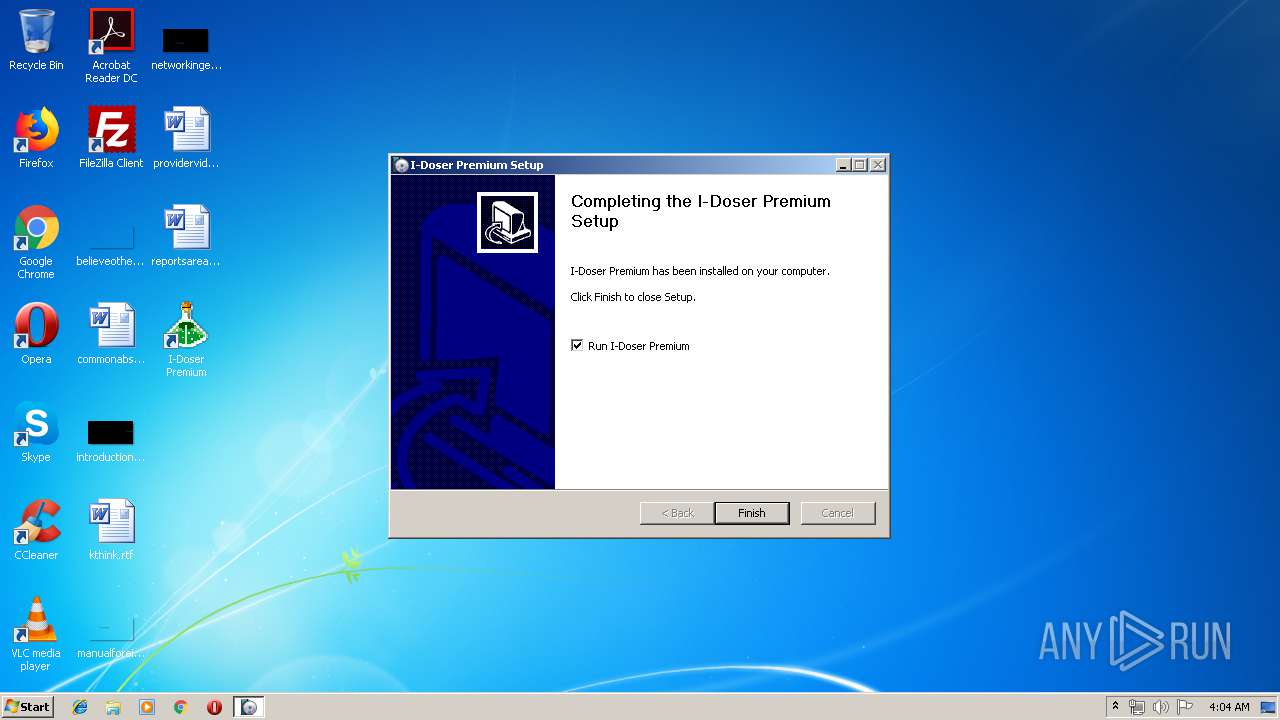
MALICIOUS
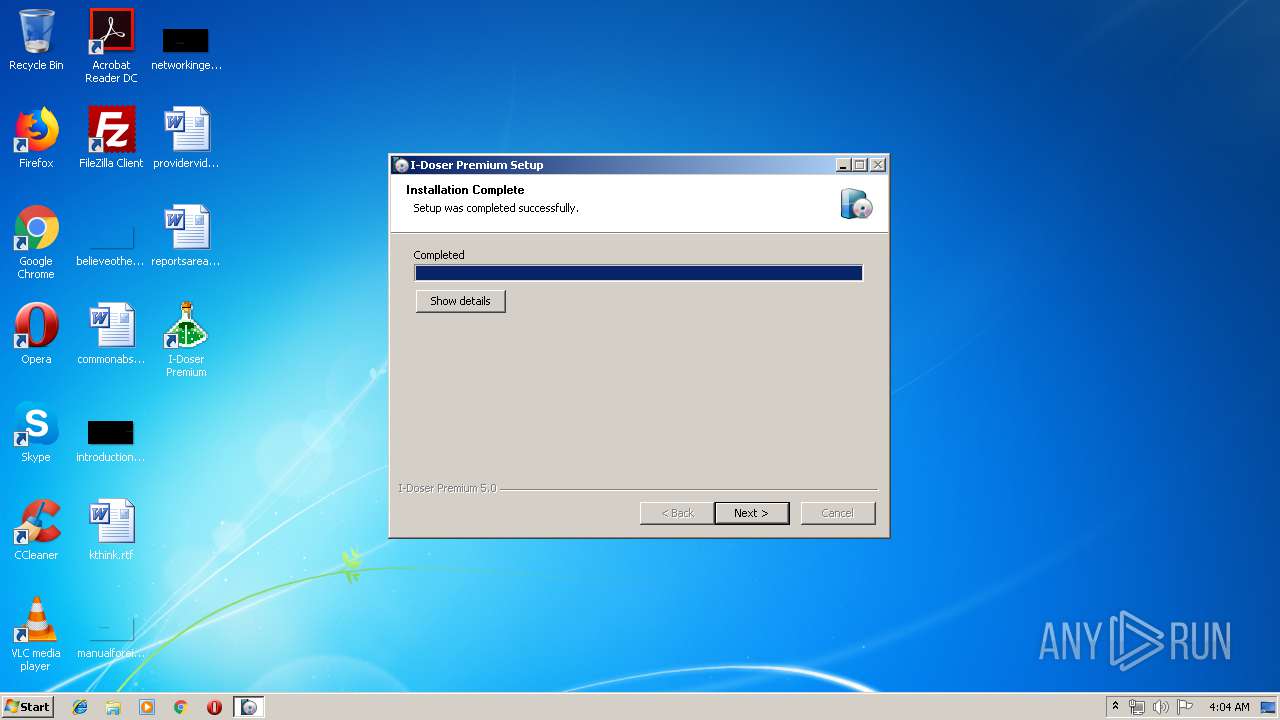
Application was dropped or rewritten from another process
- IDoser.exe (PID: 3604)
Loads dropped or rewritten executable
- IDoserPremiumSetup.exe (PID: 3640)
- IDoser.exe (PID: 3604)
SUSPICIOUS
Creates files in the program directory
- IDoserPremiumSetup.exe (PID: 3640)
Executable content was dropped or overwritten
- IDoserPremiumSetup.exe (PID: 3640)
Creates a software uninstall entry
- IDoserPremiumSetup.exe (PID: 3640)
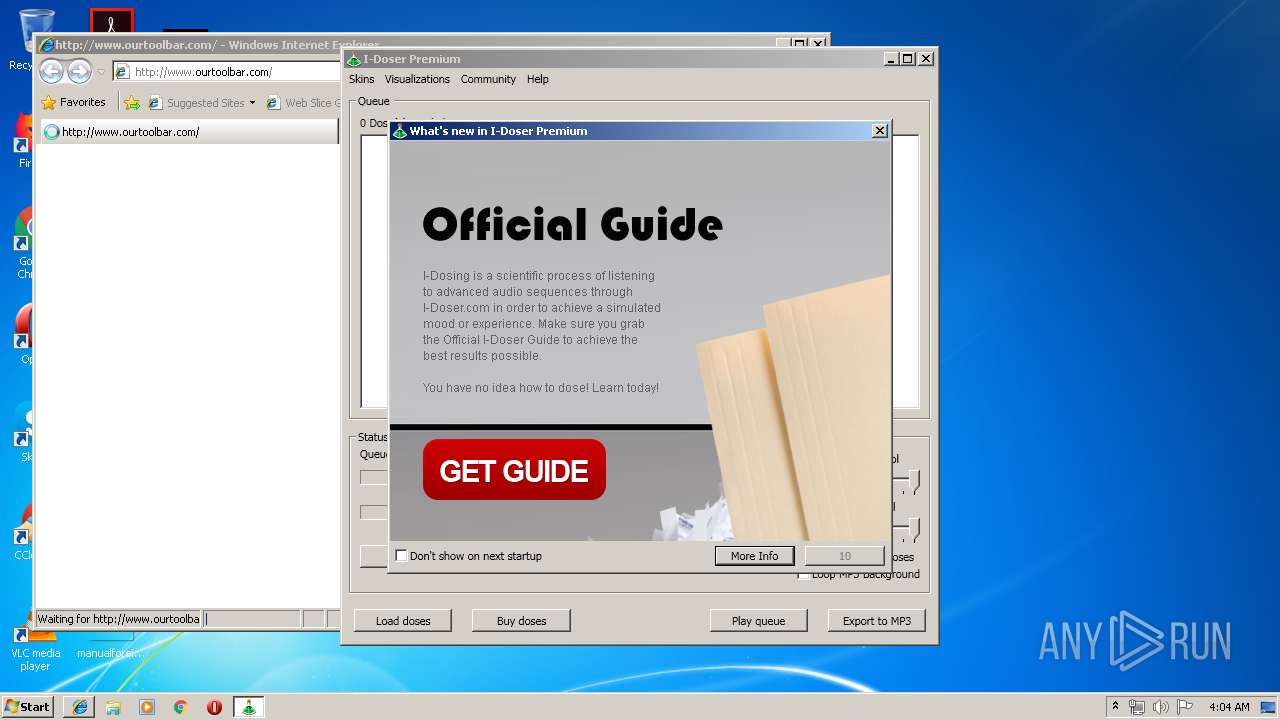
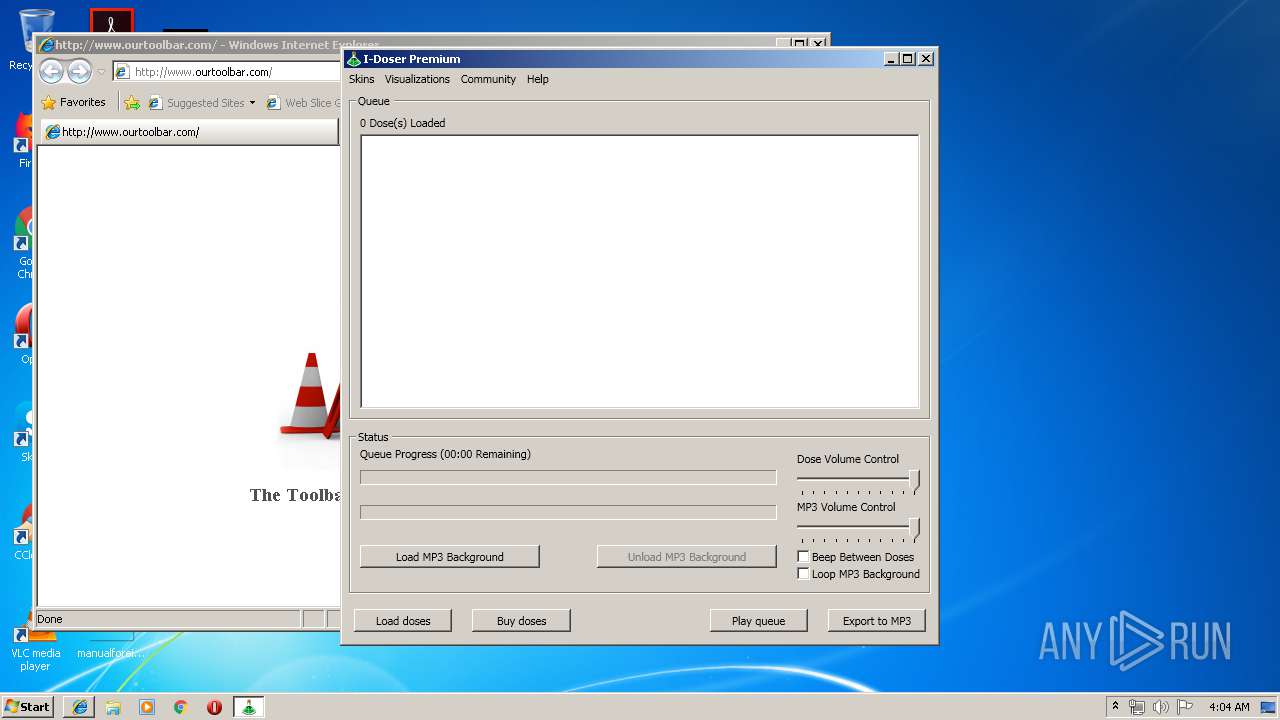
Starts Internet Explorer
- IDoserPremiumSetup.exe (PID: 3640)
Modifies the open verb of a shell class
- IDoser.exe (PID: 3604)
Creates files in the user directory
- IDoser.exe (PID: 3604)
Reads Environment values
- IDoser.exe (PID: 3604)
Check for Java to be installed
- iexplore.exe (PID: 2292)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2292)
Application launched itself
- iexplore.exe (PID: 2292)
Dropped object may contain Bitcoin addresses
- IDoserPremiumSetup.exe (PID: 3640)
- IDoser.exe (PID: 3604)
Reads Internet Cache Settings
- iexplore.exe (PID: 3032)
- iexplore.exe (PID: 2292)
Reads internet explorer settings
- iexplore.exe (PID: 3032)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3032)
Changes settings of System certificates
- iexplore.exe (PID: 3032)
Creates files in the user directory
- iexplore.exe (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:10 14:19:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 25600 |
| InitializedDataSize: | 431104 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x354b |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Apr-2010 12:19:31 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Apr-2010 12:19:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000063A2 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48045 |
.rdata | 0x00008000 | 0x000018F2 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.88829 |
.data | 0x0000A000 | 0x0006669C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.42988 |
.ndata | 0x00071000 | 0x00131000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x001A2000 | 0x00017C68 | 0x00017E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.73194 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10572 | 541 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9375 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.96544 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.89278 | 2440 | UNKNOWN | English - United States | RT_ICON |
5 | 5.78939 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.67841 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2292 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | IDoserPremiumSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2292 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3460 | "C:\Users\admin\AppData\Local\Temp\IDoserPremiumSetup.exe" | C:\Users\admin\AppData\Local\Temp\IDoserPremiumSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
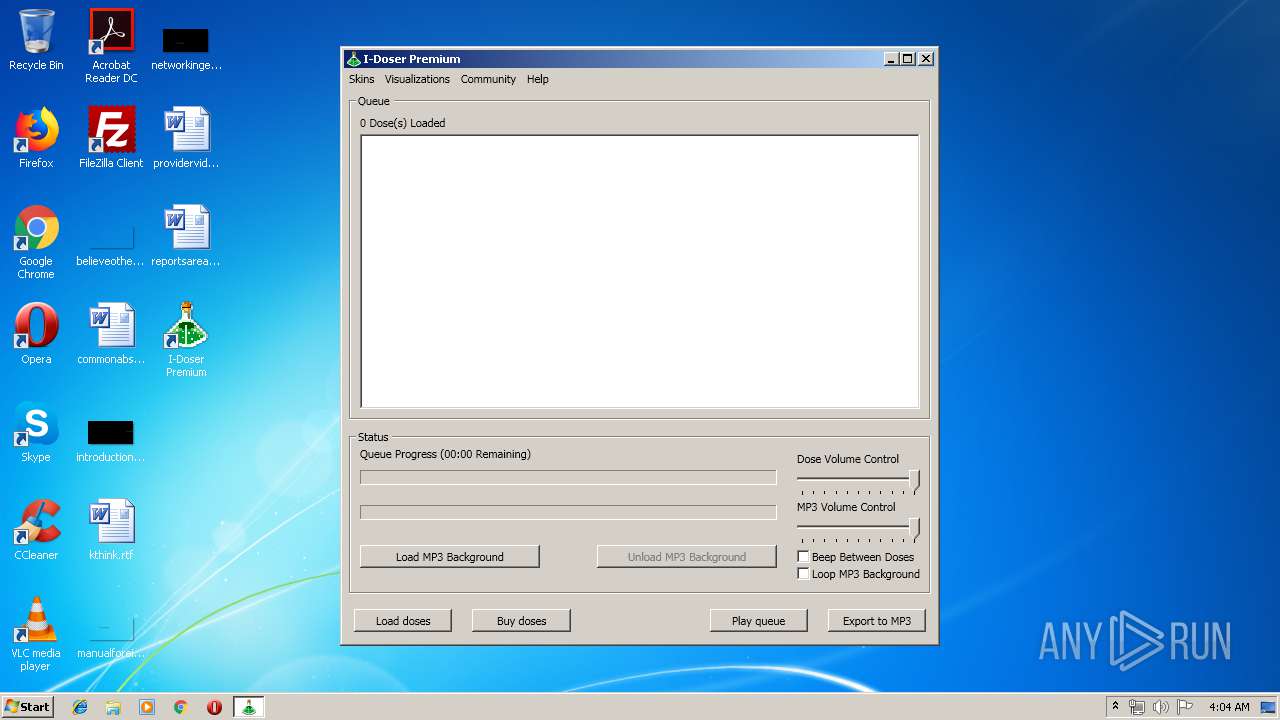
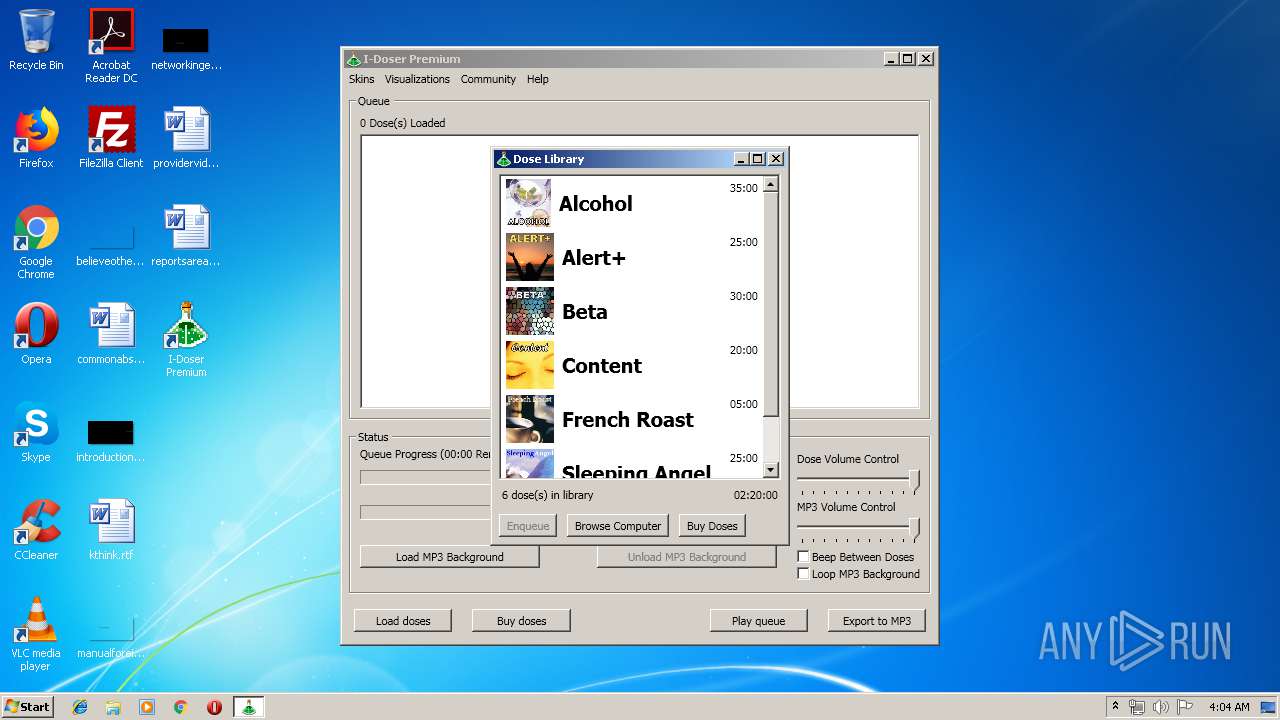
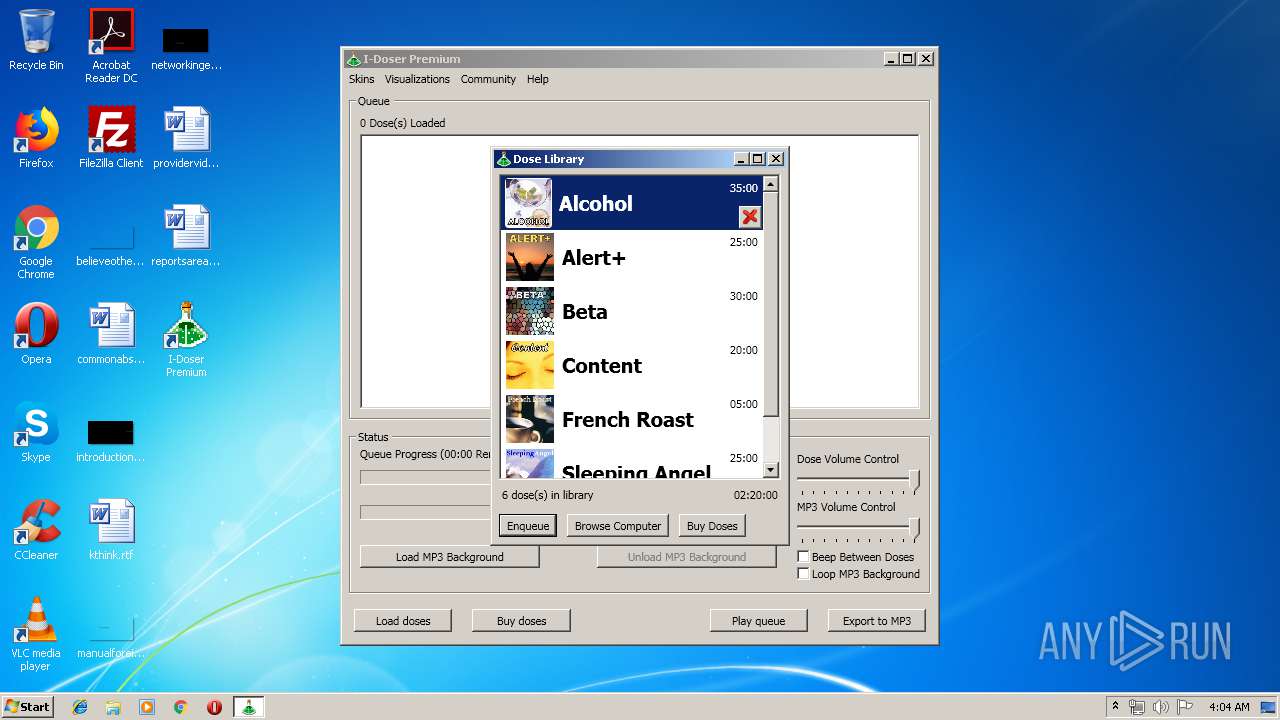
| 3604 | "C:\Program Files\I-Doser Premium\IDoser.exe" | C:\Program Files\I-Doser Premium\IDoser.exe | IDoserPremiumSetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: IDoser Exit code: 0 Version: 5.0.* Modules
| |||||||||||||||
| 3640 | "C:\Users\admin\AppData\Local\Temp\IDoserPremiumSetup.exe" | C:\Users\admin\AppData\Local\Temp\IDoserPremiumSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
851
Read events
731
Write events
118
Delete events
2
Modification events
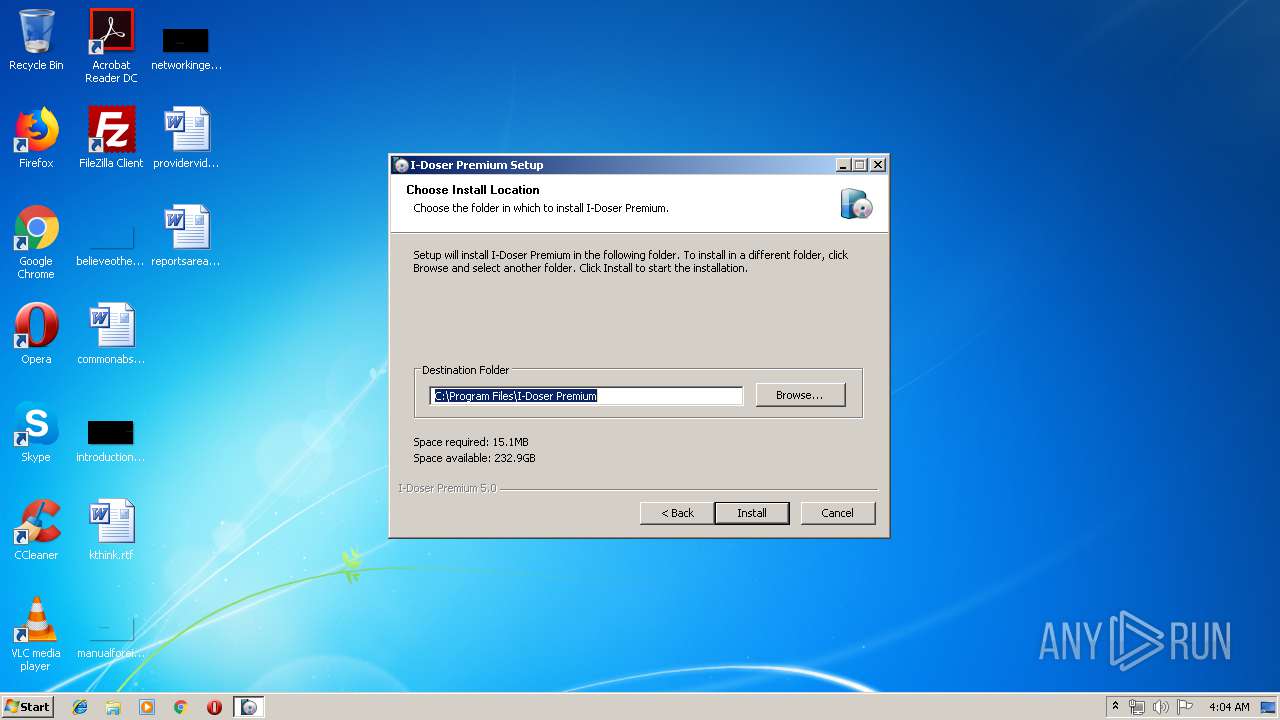
| (PID) Process: | (3640) IDoserPremiumSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\I-Doser |
| Operation: | write | Name: | Install_Dir |
Value: C:\Program Files\I-Doser Premium | |||
| (PID) Process: | (3640) IDoserPremiumSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\I-Doser |
| Operation: | write | Name: | Edition |
Value: Premium | |||
| (PID) Process: | (3640) IDoserPremiumSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\I-Doser |
| Operation: | write | Name: | DisplayName |
Value: I-Doser Premium | |||
| (PID) Process: | (3640) IDoserPremiumSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\I-Doser |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\I-Doser Premium\Uninstall.exe" | |||
| (PID) Process: | (3640) IDoserPremiumSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\I-Doser |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\I-Doser Premium\Uninstall.exe" /S | |||
| (PID) Process: | (3640) IDoserPremiumSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\I-Doser |
| Operation: | write | Name: | Publisher |
Value: I-Doser.com | |||
| (PID) Process: | (3640) IDoserPremiumSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\I-Doser |
| Operation: | write | Name: | InstallLocation |
Value: "C:\Program Files\I-Doser Premium" | |||
| (PID) Process: | (3640) IDoserPremiumSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\I-Doser |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Program Files\I-Doser Premium\IDoser.exe" | |||
| (PID) Process: | (3640) IDoserPremiumSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\I-Doser |
| Operation: | write | Name: | DisplayVersion |
Value: 5.0 | |||
| (PID) Process: | (3640) IDoserPremiumSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\I-Doser |
| Operation: | write | Name: | EstimatedSize |
Value: 4825 | |||
Executable files
8
Suspicious files
3
Text files
46
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3640 | IDoserPremiumSetup.exe | C:\Program Files\I-Doser Premium\Skins\Expression Light.xaml | html | |
MD5:17F8F6AF69ED7E092C85AE7B7FD61CAB | SHA256:2E1E8243611709DE06E27A2B2A0CD68E77212CDF61F020A0009E8C2E585ABACE | |||
| 3640 | IDoserPremiumSetup.exe | C:\Users\admin\AppData\Local\Temp\nsd521D.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3640 | IDoserPremiumSetup.exe | C:\Users\admin\AppData\Local\Temp\nsd521D.tmp\UserInfo.dll | executable | |
MD5:D16E06C5DE8FB8213A0464568ED9852F | SHA256:728472BA312AE8AF7F30D758AB473E0772477A68FCD1D2D547DAFE6D8800D531 | |||
| 3640 | IDoserPremiumSetup.exe | C:\Program Files\I-Doser Premium\IDoser.exe | executable | |
MD5:630B4939D6232D37EE16A81DFD460565 | SHA256:A10943B60EBD5919E5C340303249878881E8F7158BFF2FB3A3C037A1C1C76DB5 | |||
| 3640 | IDoserPremiumSetup.exe | C:\Program Files\I-Doser Premium\SbaGen.dll | executable | |
MD5:3EE76D93D90E07F67A47B5660AA577BF | SHA256:2EA846D0EBEF6F521A5909DA92E46E7EE5181FE88C5C3FFB61310B6683178B2F | |||
| 3640 | IDoserPremiumSetup.exe | C:\Program Files\I-Doser Premium\SbaGen.zip | compressed | |
MD5:3ED890A10D087FEAE92EB229F74A5160 | SHA256:380C449219598C6F09EA1C490D989255465C944D1F2EA85D583FAB0BBCF95508 | |||
| 3640 | IDoserPremiumSetup.exe | C:\Program Files\I-Doser Premium\Skins\Bubble Creme.xaml | html | |
MD5:69B408150F769B24930684B6DA9253F3 | SHA256:99F6972CA7087E9A60B70113FE214144979F41325B2AF4851ED5B058C49AC132 | |||
| 3640 | IDoserPremiumSetup.exe | C:\Program Files\I-Doser Premium\lame_enc.dll | executable | |
MD5:83D6E37130F8F0F2D9829F528E53DD5D | SHA256:A2E312305EC6BA7AD2E65C5B6141326247C27DD1AF6789AC3498E958D685EE85 | |||
| 3640 | IDoserPremiumSetup.exe | C:\Program Files\I-Doser Premium\whatsnew.jpg | image | |
MD5:1E812D8EF51FE81EA33582DB2000C436 | SHA256:61A9DB101E6D03066A6B2A29D4C4C96EAC43F2BC235A44DCC58C3D72295CD4BF | |||
| 3640 | IDoserPremiumSetup.exe | C:\Program Files\I-Doser Premium\Skins\Bureau Blue.xaml | text | |
MD5:A4F14ADFA00C931F4D167CEA0786EEA7 | SHA256:AC9024B42ACD860A156776FB19F0687E52907E874B4EBDEB32A357349A6CA348 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
13
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3604 | IDoser.exe | GET | — | 64.50.176.93:80 | http://www.i-doser.com/pcapp_whatsnew/whatsnew_newsletter.jpg | US | — | — | unknown |
3604 | IDoser.exe | GET | 200 | 64.50.176.93:80 | http://www.i-doser.com/pcapp_whatsnew/whatsnew_premiumupgrade.jpg | US | image | 71.8 Kb | unknown |
3604 | IDoser.exe | GET | 200 | 64.50.176.93:80 | http://www.i-doser.com/pcapp_whatsnew/whatsnew_youtube.jpg | US | image | 165 Kb | unknown |
3604 | IDoser.exe | GET | 200 | 64.50.176.93:80 | http://www.i-doser.com/pcapp_whatsnew/whatsnew_saleofcentury.jpg | US | image | 62.7 Kb | unknown |
3604 | IDoser.exe | GET | 200 | 64.50.176.93:80 | http://www.i-doser.com/pcapp_whatsnew/whatsnew_mobile.jpg | US | image | 189 Kb | unknown |
3604 | IDoser.exe | GET | 200 | 64.50.176.93:80 | http://www.i-doser.com/pcapp_whatsnew/whatsnew_merch.jpg | US | image | 201 Kb | unknown |
3604 | IDoser.exe | GET | 200 | 64.50.176.93:80 | http://www.i-doser.com/pcapp_whatsnew/whatsnew_freedoses.jpg | US | image | 126 Kb | unknown |
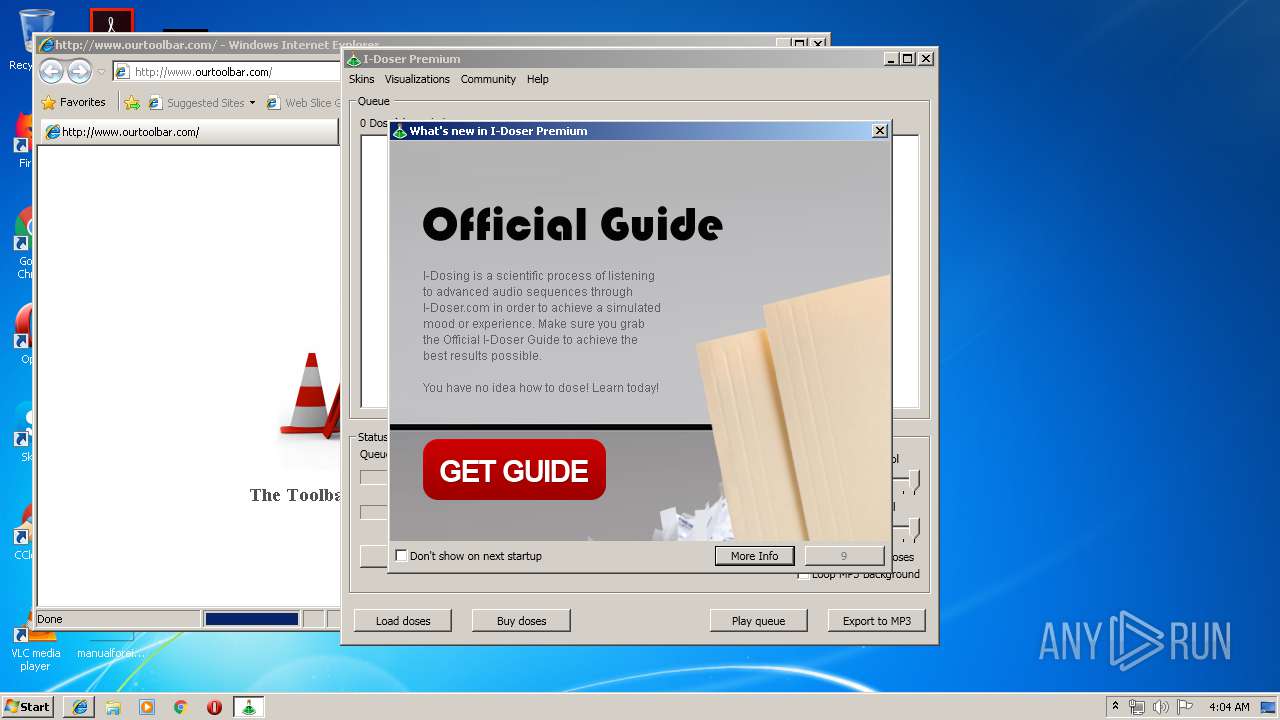
3032 | iexplore.exe | GET | 302 | 216.146.46.11:80 | http://idosercom.ourtoolbar.com/ | US | html | 161 b | malicious |
3032 | iexplore.exe | GET | 200 | 52.216.145.98:80 | http://www.ourtoolbar.com/ | US | html | 733 b | suspicious |
3032 | iexplore.exe | GET | 200 | 52.216.145.98:80 | http://www.ourtoolbar.com/pic.jpg | US | image | 18.8 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3032 | iexplore.exe | 216.146.46.11:80 | idosercom.ourtoolbar.com | Dynamic Network Services, Inc. | US | malicious |
2292 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3032 | iexplore.exe | 52.216.145.98:80 | www.ourtoolbar.com | Amazon.com, Inc. | US | unknown |
3032 | iexplore.exe | 216.58.208.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3032 | iexplore.exe | 172.217.16.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3604 | IDoser.exe | 64.50.176.93:80 | www.i-doser.com | Lunar Pages | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
idosercom.ourtoolbar.com |
| malicious |
www.bing.com |
| whitelisted |
www.ourtoolbar.com |
| suspicious |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.i-doser.com |
| unknown |