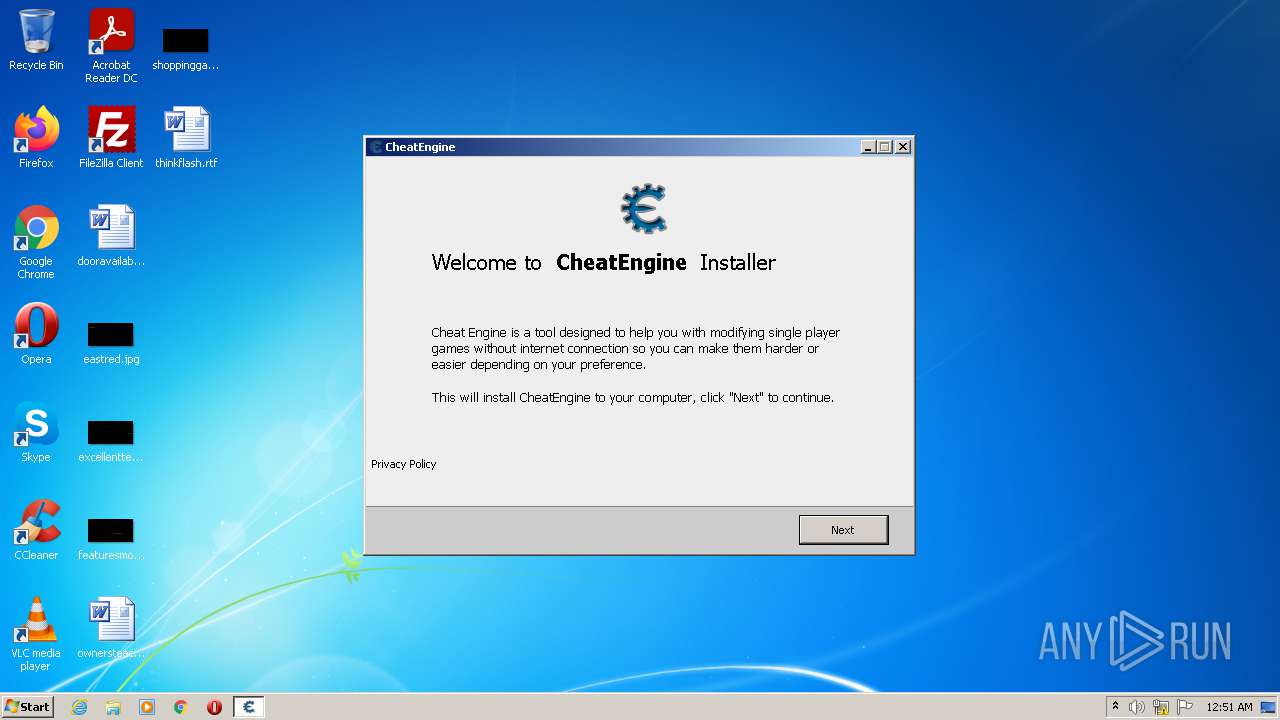
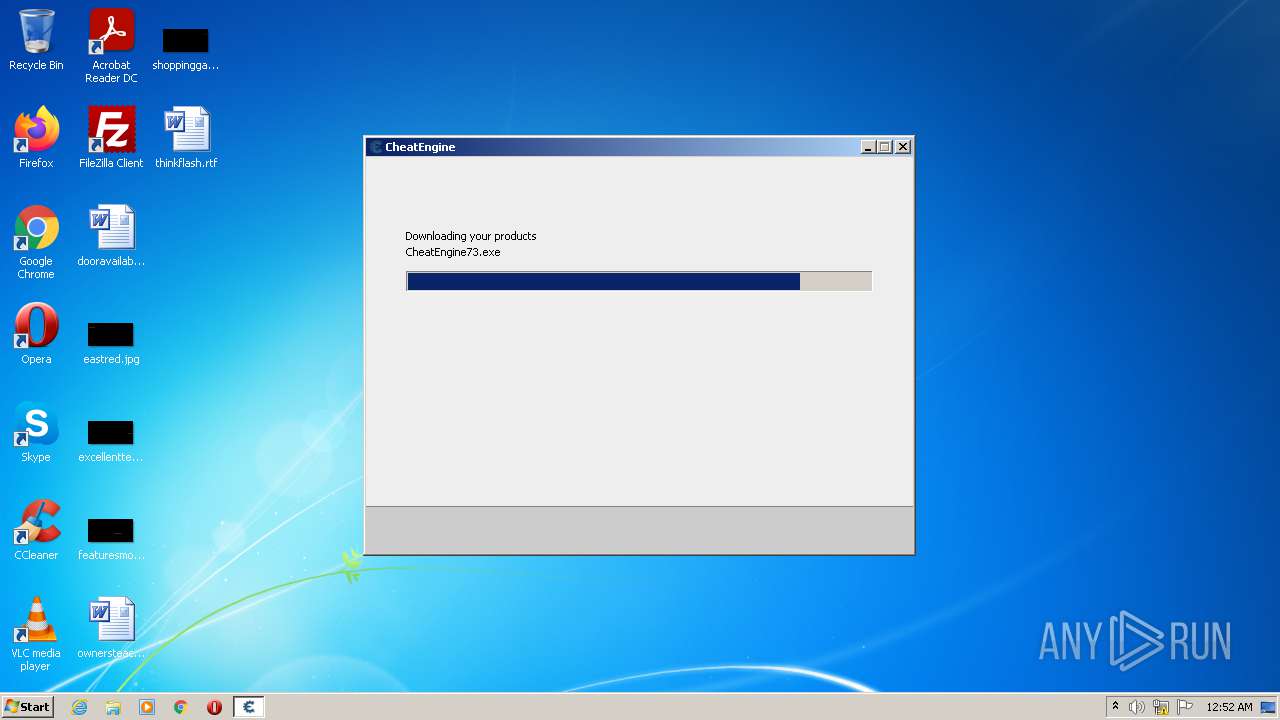
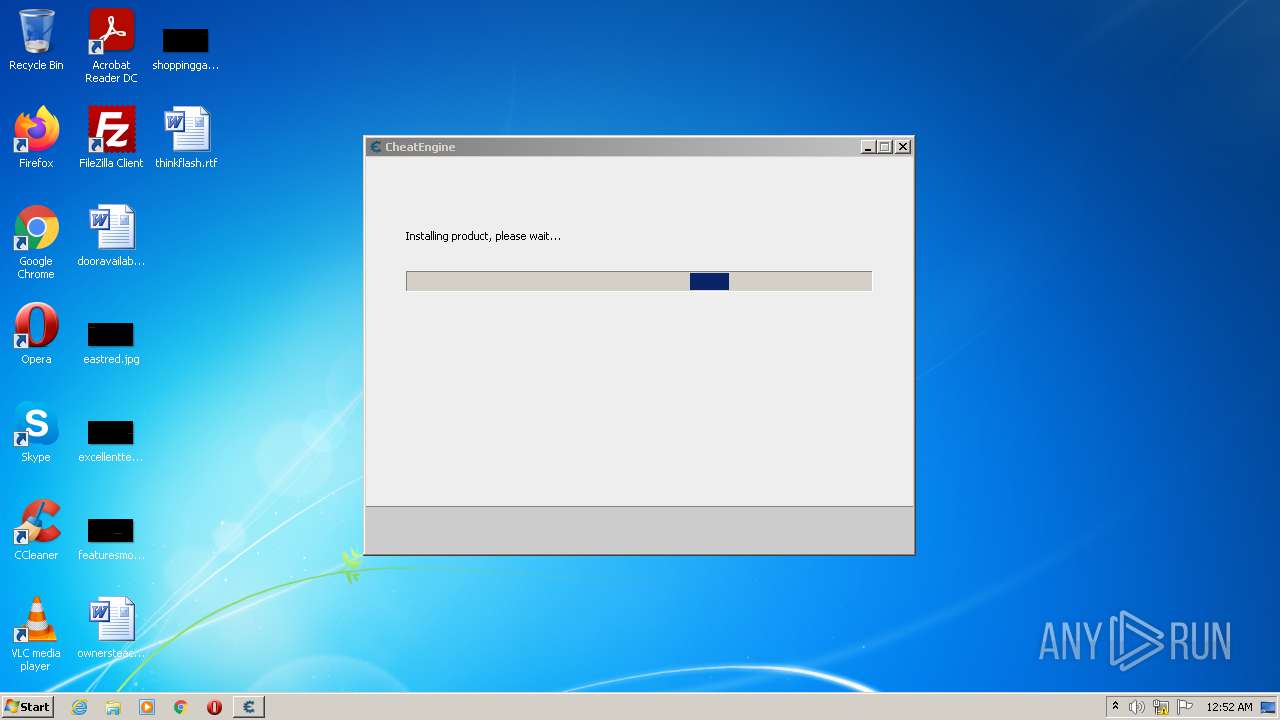
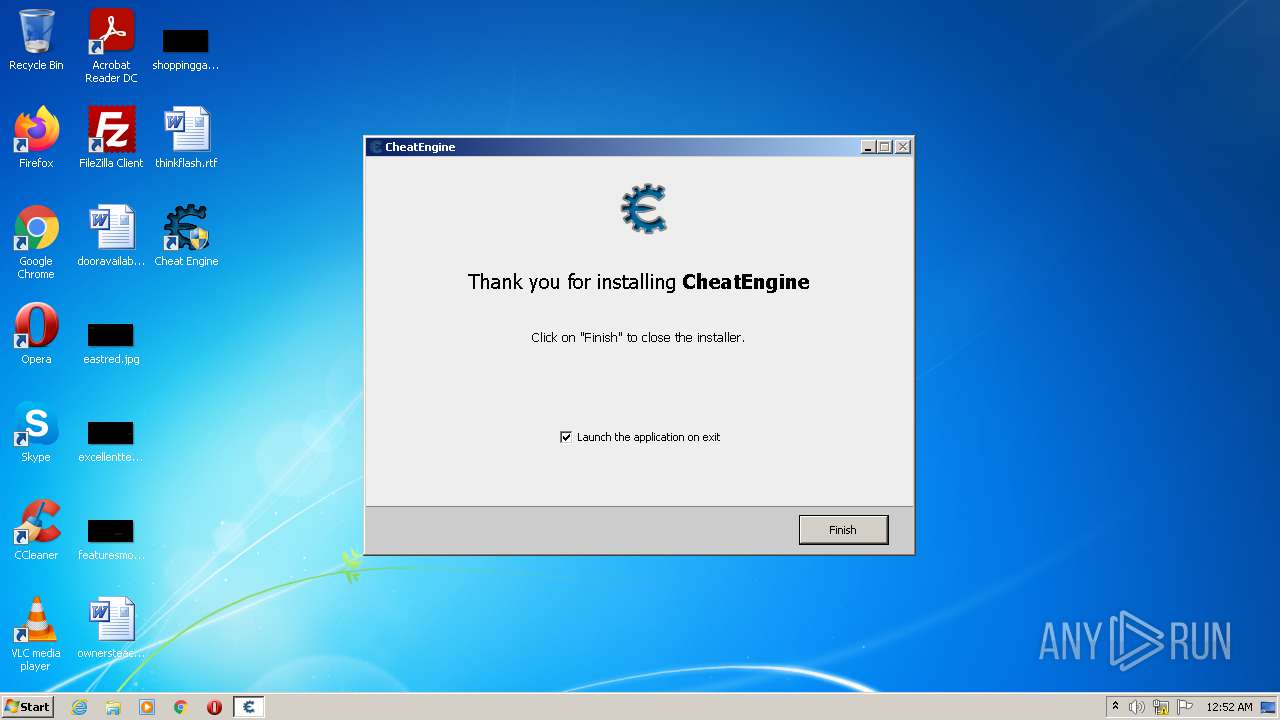
| File name: | CheatEngine73.exe |
| Full analysis: | https://app.any.run/tasks/57d44709-03b1-4aee-b20f-e547433f7840 |
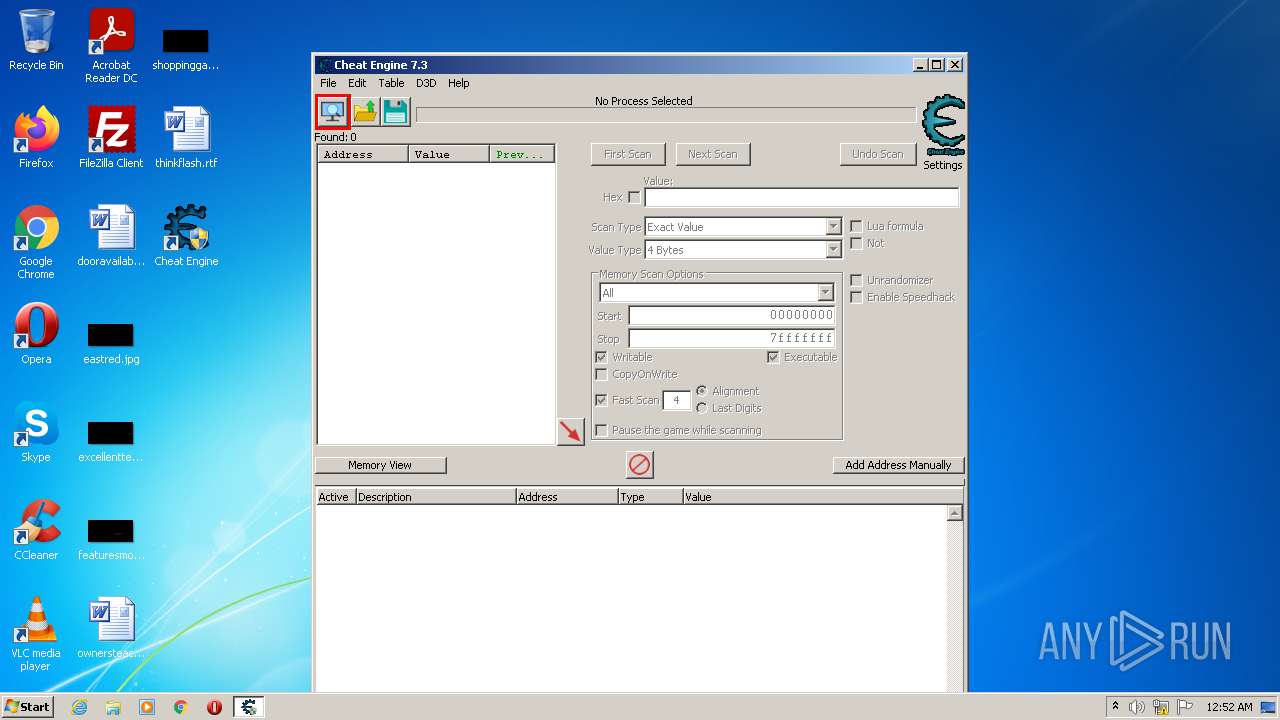
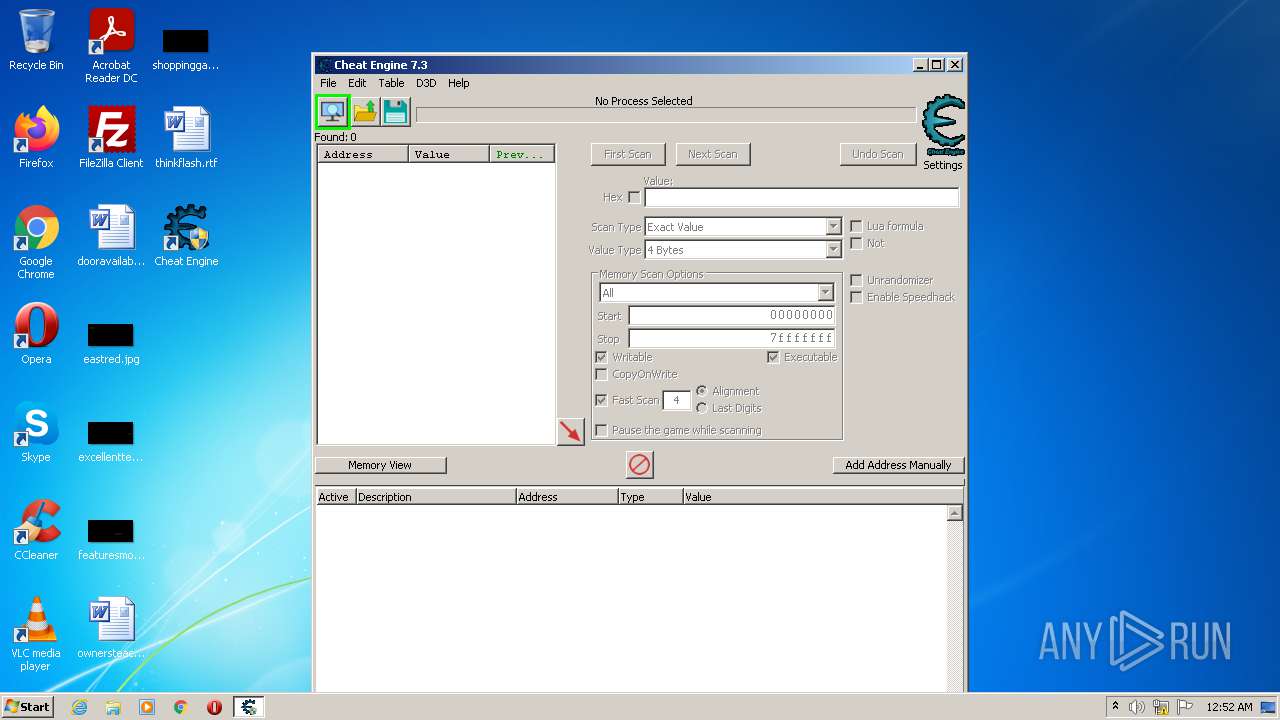
| Verdict: | Malicious activity |
| Analysis date: | September 09, 2021, 23:51:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7ED6B58360D0D7E033237F37DD314F47 |
| SHA1: | 6925AA78B2A1E18524BCBBE09611D079B7BDC9ED |
| SHA256: | 9B8480581FFD010C93C4504D0BB5DCD8C2EBA5C57812E399DA8C6C58024A4903 |
| SSDEEP: | 98304:6Sif4opH4opH4opuE9vBuN1EdKKBEXJhJJ:SDBDBDlDKKB2/ |
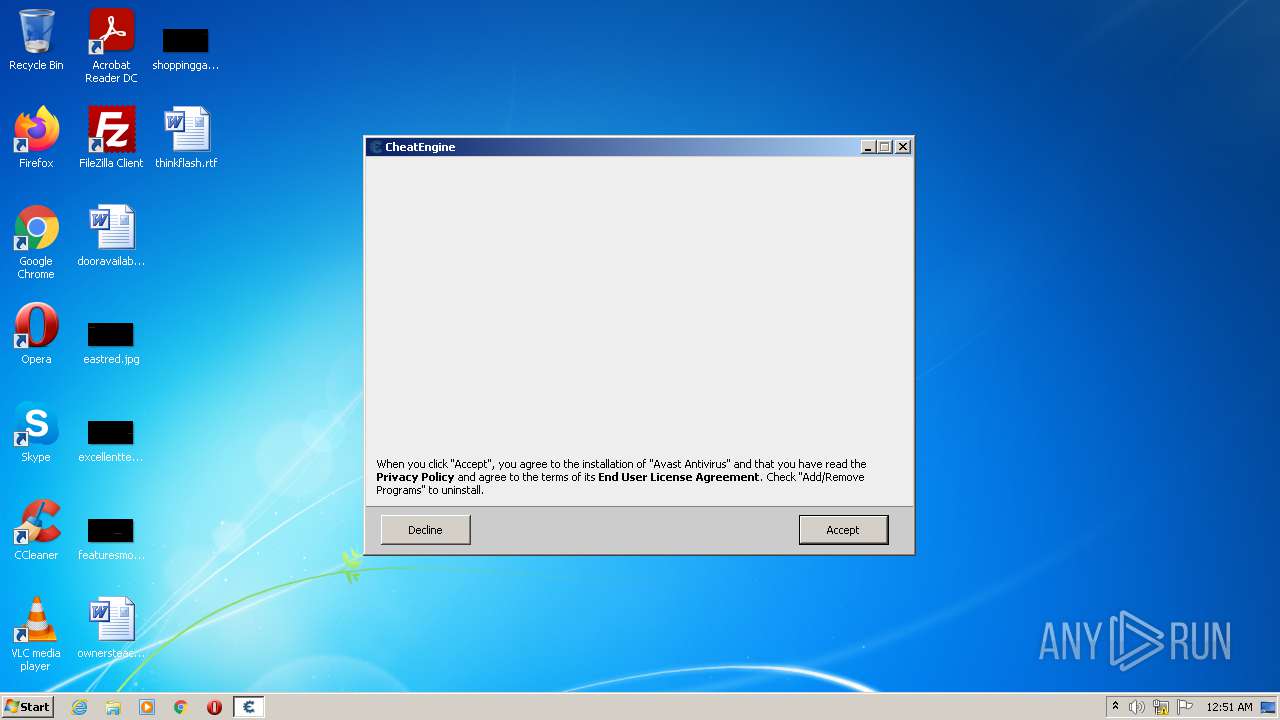
MALICIOUS
Drops executable file immediately after starts
- CheatEngine73.exe (PID: 3628)
- CheatEngine73.exe (PID: 2780)
- CheatEngine73.exe (PID: 3800)
- CheatEngine73.tmp (PID: 944)
Starts NET.EXE for service management
- CheatEngine73.tmp (PID: 944)
Application was dropped or rewritten from another process
- Kernelmoduleunloader.exe (PID: 3432)
- windowsrepair.exe (PID: 3904)
- Cheat Engine.exe (PID: 3452)
- Cheat Engine.exe (PID: 2244)
- cheatengine-i386.exe (PID: 2640)
Loads dropped or rewritten executable
- cheatengine-i386.exe (PID: 2640)
SUSPICIOUS
Executable content was dropped or overwritten
- CheatEngine73.exe (PID: 3628)
- CheatEngine73.tmp (PID: 2840)
- CheatEngine73.exe (PID: 2780)
- CheatEngine73.exe (PID: 3800)
- CheatEngine73.tmp (PID: 944)
Checks supported languages
- CheatEngine73.tmp (PID: 3956)
- CheatEngine73.exe (PID: 2780)
- CheatEngine73.tmp (PID: 2840)
- CheatEngine73.exe (PID: 3628)
- CheatEngine73.tmp (PID: 944)
- CheatEngine73.exe (PID: 3800)
- Kernelmoduleunloader.exe (PID: 3432)
- windowsrepair.exe (PID: 3904)
- Cheat Engine.exe (PID: 2244)
- cheatengine-i386.exe (PID: 2640)
Reads the computer name
- CheatEngine73.tmp (PID: 2840)
- CheatEngine73.tmp (PID: 3956)
- CheatEngine73.tmp (PID: 944)
- Kernelmoduleunloader.exe (PID: 3432)
- Cheat Engine.exe (PID: 2244)
- cheatengine-i386.exe (PID: 2640)
Reads Windows owner or organization settings
- CheatEngine73.tmp (PID: 2840)
- CheatEngine73.tmp (PID: 944)
Drops a file with too old compile date
- CheatEngine73.tmp (PID: 2840)
- CheatEngine73.tmp (PID: 944)
Drops a file that was compiled in debug mode
- CheatEngine73.tmp (PID: 2840)
- CheatEngine73.tmp (PID: 944)
Reads the Windows organization settings
- CheatEngine73.tmp (PID: 2840)
- CheatEngine73.tmp (PID: 944)
Drops a file with a compile date too recent
- CheatEngine73.tmp (PID: 2840)
Creates a directory in Program Files
- CheatEngine73.tmp (PID: 944)
Uses ICACLS.EXE to modify access control list
- CheatEngine73.tmp (PID: 944)
Starts SC.EXE for service management
- CheatEngine73.tmp (PID: 944)
Changes default file association
- CheatEngine73.tmp (PID: 944)
Creates files in the program directory
- cheatengine-i386.exe (PID: 2640)
INFO
Application was dropped or rewritten from another process
- CheatEngine73.tmp (PID: 2840)
- CheatEngine73.tmp (PID: 3956)
- CheatEngine73.exe (PID: 3800)
- CheatEngine73.tmp (PID: 944)
Reads settings of System Certificates
- CheatEngine73.tmp (PID: 2840)
- cheatengine-i386.exe (PID: 2640)
Loads dropped or rewritten executable
- CheatEngine73.tmp (PID: 2840)
Checks supported languages
- net.exe (PID: 2468)
- net.exe (PID: 704)
- net1.exe (PID: 2288)
- sc.exe (PID: 428)
- sc.exe (PID: 1040)
- icacls.exe (PID: 3096)
- net1.exe (PID: 904)
- icacls.exe (PID: 1620)
Reads the computer name
- net1.exe (PID: 904)
- net1.exe (PID: 2288)
- sc.exe (PID: 428)
- icacls.exe (PID: 3096)
- sc.exe (PID: 1040)
- icacls.exe (PID: 1620)
Creates files in the program directory
- CheatEngine73.tmp (PID: 944)
Creates a software uninstall entry
- CheatEngine73.tmp (PID: 944)
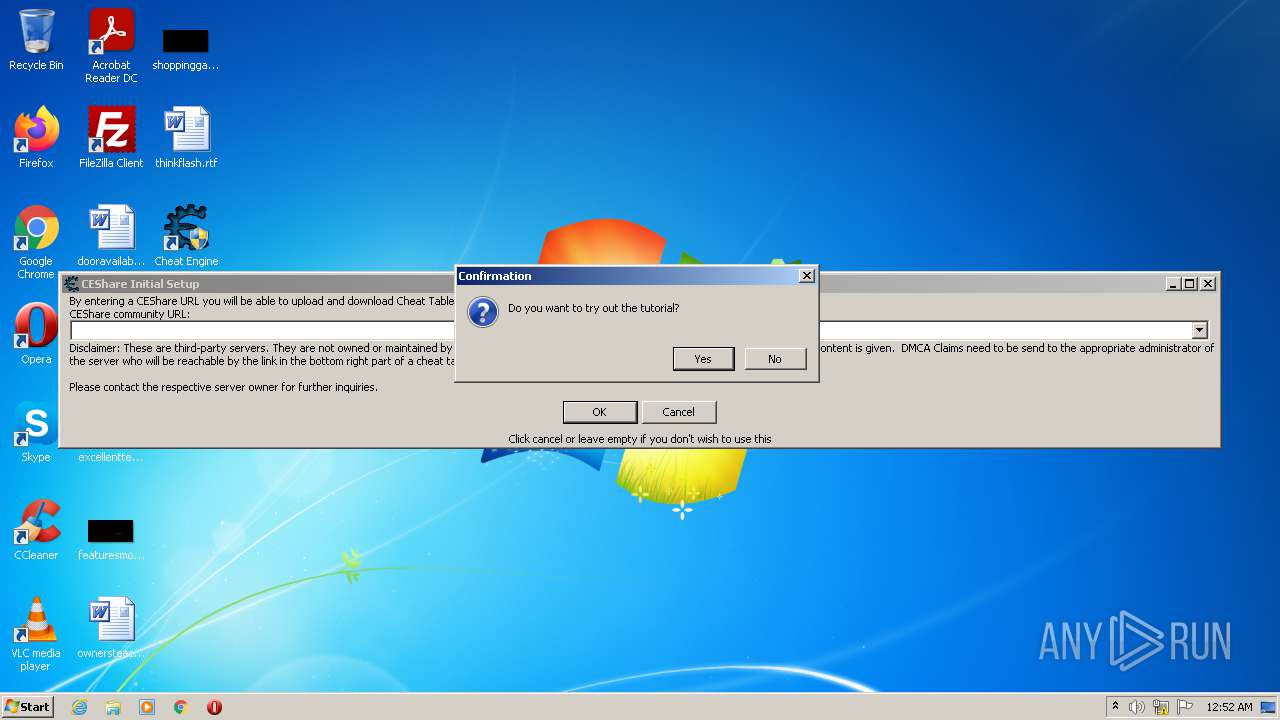
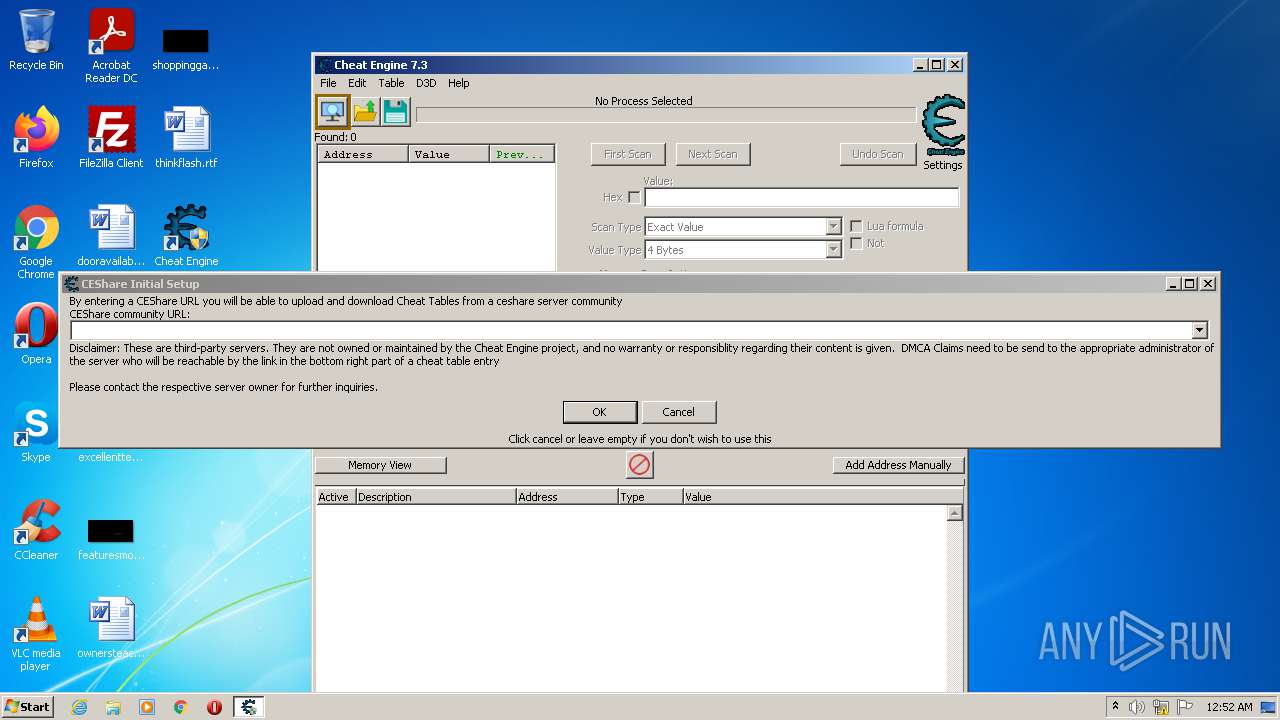
Manual execution by user
- Cheat Engine.exe (PID: 3452)
- Cheat Engine.exe (PID: 2244)
Checks Windows Trust Settings
- cheatengine-i386.exe (PID: 2640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| ProductVersion: | 7.3.0 |
|---|---|
| ProductName: | EngineGame |
| OriginalFileName: | |
| LegalCopyright: | |
| FileVersion: | 7.3.0 |
| FileDescription: | EngineGame Installer |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 7.3.0.0 |
| FileVersionNumber: | 7.3.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6 |
| OSVersion: | 6.1 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 102912 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2020:11:15 10:48:30+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2020 09:48:30 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | EngineGame Installer |
| FileVersion: | 7.3.0 |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | EngineGame |
| ProductVersion: | 7.3.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 15-Nov-2020 09:48:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x0001438C | 0x00014400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.12426 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.00833 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.56385 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.06349 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 7.9804 | 51953 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
Total processes
66
Monitored processes
19
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 428 | "sc" delete BadlionAntic | C:\Windows\system32\sc.exe | — | CheatEngine73.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 704 | "net" stop BadlionAntic | C:\Windows\system32\net.exe | — | CheatEngine73.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 904 | C:\Windows\system32\net1 stop BadlionAnticheat | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 944 | "C:\Users\admin\AppData\Local\Temp\is-SVFNJ.tmp\CheatEngine73.tmp" /SL5="$101AC,22981351,780800,C:\Users\admin\AppData\Local\Temp\is-U7GB1.tmp\CheatEngine73.exe" /VERYSILENT /ZBDIST | C:\Users\admin\AppData\Local\Temp\is-SVFNJ.tmp\CheatEngine73.tmp | CheatEngine73.exe | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1040 | "sc" delete BadlionAnticheat | C:\Windows\system32\sc.exe | — | CheatEngine73.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1620 | "icacls" "C:\Program Files\Cheat Engine 7.3" /grant *S-1-15-2-1:(OI)(CI)(RX) | C:\Windows\system32\icacls.exe | — | CheatEngine73.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 1332 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Cheat Engine 7.3\Cheat Engine.exe" | C:\Program Files\Cheat Engine 7.3\Cheat Engine.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 6.3.0.0 Modules
| |||||||||||||||
| 2288 | C:\Windows\system32\net1 stop BadlionAntic | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2468 | "net" stop BadlionAnticheat | C:\Windows\system32\net.exe | — | CheatEngine73.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
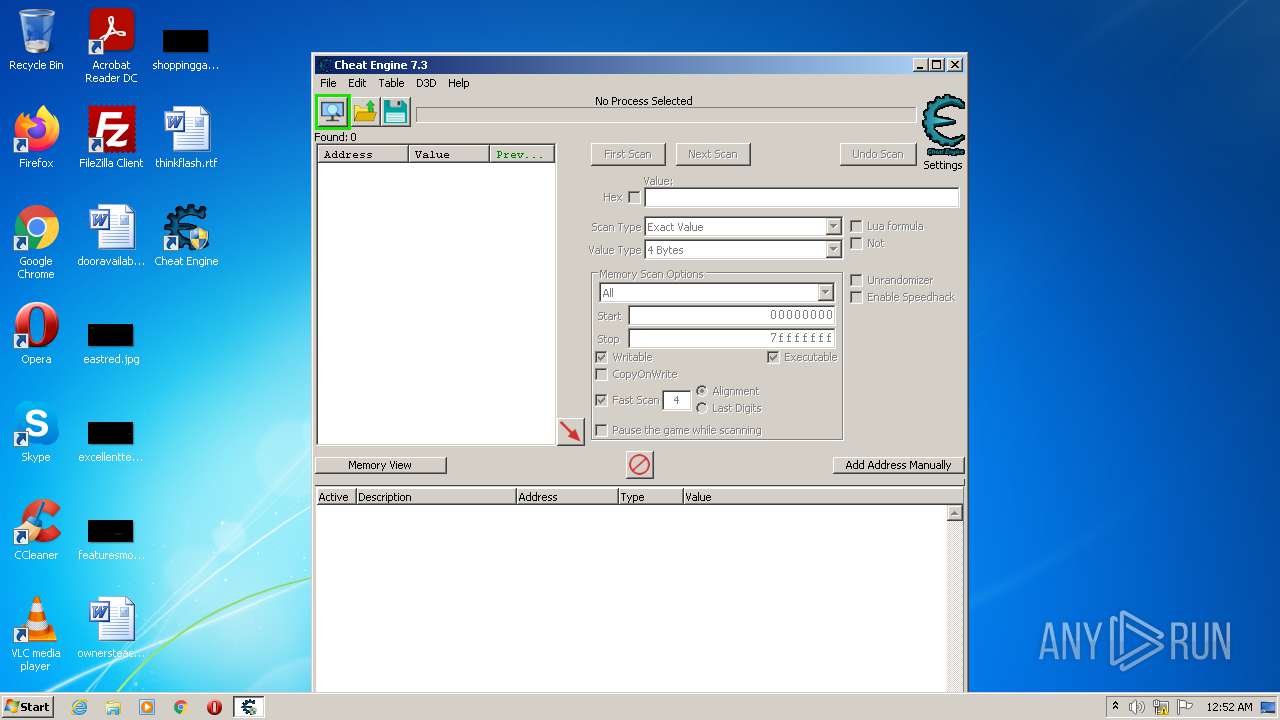
| 2640 | "C:\Program Files\Cheat Engine 7.3\cheatengine-i386.exe" | C:\Program Files\Cheat Engine 7.3\cheatengine-i386.exe | Cheat Engine.exe | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Cheat Engine Exit code: 0 Version: 7.3.0.7199 Modules
| |||||||||||||||
Total events
9 006
Read events
8 890
Write events
105
Delete events
11
Modification events
| (PID) Process: | (2840) CheatEngine73.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 180B0000DFC0499BD5A5D701 | |||
| (PID) Process: | (2840) CheatEngine73.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 376215EA6FDC672D6B60595BAC59BDF84DEA1C12960791BDBC18FDC3C9DFE84D | |||
| (PID) Process: | (2840) CheatEngine73.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2840) CheatEngine73.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (944) CheatEngine73.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: B0030000737A98B3D5A5D701 | |||
| (PID) Process: | (944) CheatEngine73.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: 139E7982F37A4A876249021CC06BC717065AD2E688D7D584ED8127D99C67792B | |||
| (PID) Process: | (944) CheatEngine73.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (944) CheatEngine73.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Cheat Engine 7.3\windowsrepair.exe | |||
| (PID) Process: | (944) CheatEngine73.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFilesHash |
Value: 1E41ABA0513DD822A2884BC613A3BF6FF13FAAA9439559485DC7E0F53D8CD756 | |||
| (PID) Process: | (944) CheatEngine73.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.CETRAINER |
| Operation: | write | Name: | (default) |
Value: CheatEngine | |||
Executable files
129
Suspicious files
16
Text files
415
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | CheatEngine73.tmp | C:\Users\admin\AppData\Local\Temp\is-U7GB1.tmp\is-NMOH8.tmp | image | |
MD5:— | SHA256:— | |||
| 2840 | CheatEngine73.tmp | C:\Users\admin\AppData\Local\Temp\is-U7GB1.tmp\WebAdvisor.png | image | |
MD5:— | SHA256:— | |||
| 2840 | CheatEngine73.tmp | C:\Users\admin\AppData\Local\Temp\is-U7GB1.tmp\is-HR22S.tmp | image | |
MD5:— | SHA256:— | |||
| 3628 | CheatEngine73.exe | C:\Users\admin\AppData\Local\Temp\is-F8K2N.tmp\CheatEngine73.tmp | executable | |
MD5:04F7929159C24D9D1A04E7771F285B57 | SHA256:2DDE2C775E7F549C63F95E6AAE533E61B1B4E33400C9034664F826B4A4EF6639 | |||
| 2840 | CheatEngine73.tmp | C:\Users\admin\AppData\Local\Temp\is-U7GB1.tmp\AVAST.png | image | |
MD5:— | SHA256:— | |||
| 2780 | CheatEngine73.exe | C:\Users\admin\AppData\Local\Temp\is-TSB7T.tmp\CheatEngine73.tmp | executable | |
MD5:04F7929159C24D9D1A04E7771F285B57 | SHA256:2DDE2C775E7F549C63F95E6AAE533E61B1B4E33400C9034664F826B4A4EF6639 | |||
| 2840 | CheatEngine73.tmp | C:\Users\admin\AppData\Local\Temp\is-U7GB1.tmp\zbShieldUtils.dll | executable | |
MD5:E1F18A22199C6F6AA5D87B24E5B39EF1 | SHA256:62C56C8CF2AC6521CE047B73AA99B6D3952CA53F11D34B00E98D17674A2FC10D | |||
| 2840 | CheatEngine73.tmp | C:\Users\admin\AppData\Local\Temp\is-U7GB1.tmp\logo.png | image | |
MD5:6B7CB2A5A8B301C788C3792802696FE8 | SHA256:3EED2E41BC6CA0AE9A5D5EE6D57CA727E5CBA6AC8E8C5234AC661F9080CEDADF | |||
| 2840 | CheatEngine73.tmp | C:\Users\admin\AppData\Local\Temp\is-U7GB1.tmp\error.png | image | |
MD5:6B7CB2A5A8B301C788C3792802696FE8 | SHA256:3EED2E41BC6CA0AE9A5D5EE6D57CA727E5CBA6AC8E8C5234AC661F9080CEDADF | |||
| 2840 | CheatEngine73.tmp | C:\Users\admin\AppData\Local\Temp\is-U7GB1.tmp\loader.gif | image | |
MD5:12D7FD91A06CEE2D0E76ABE0485036EE | SHA256:A6192B9A3FA5DB9917AEF72D651B7AD8FD8CCB9B53F3AD99D7C46701D00C78CB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2640 | cheatengine-i386.exe | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2e695053d14b703a | unknown | compressed | 4.70 Kb | whitelisted |
2640 | cheatengine-i386.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | cheatengine-i386.exe | 104.20.174.30:443 | cheatengine.org | Cloudflare Inc | US | shared |
2640 | cheatengine-i386.exe | 2.16.186.81:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2640 | cheatengine-i386.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2840 | CheatEngine73.tmp | 13.226.156.161:443 | d2oq4dwfbh6gxl.cloudfront.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d2oq4dwfbh6gxl.cloudfront.net |
| whitelisted |
cheatengine.org |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Kernelmoduleunloader.exe | Kernelmodule unloader |
Kernelmoduleunloader.exe | Setup. So do not show messages |
Kernelmoduleunloader.exe | attempting to unload |
Kernelmoduleunloader.exe | SCManager opened |
Kernelmoduleunloader.exe | count=0 |
Kernelmoduleunloader.exe | setup=true |
cheatengine-i386.exe | setDPIAware |
cheatengine-i386.exe | p3 |
cheatengine-i386.exe | DisassemblerThumb init |
cheatengine-i386.exe | arm disassembler |