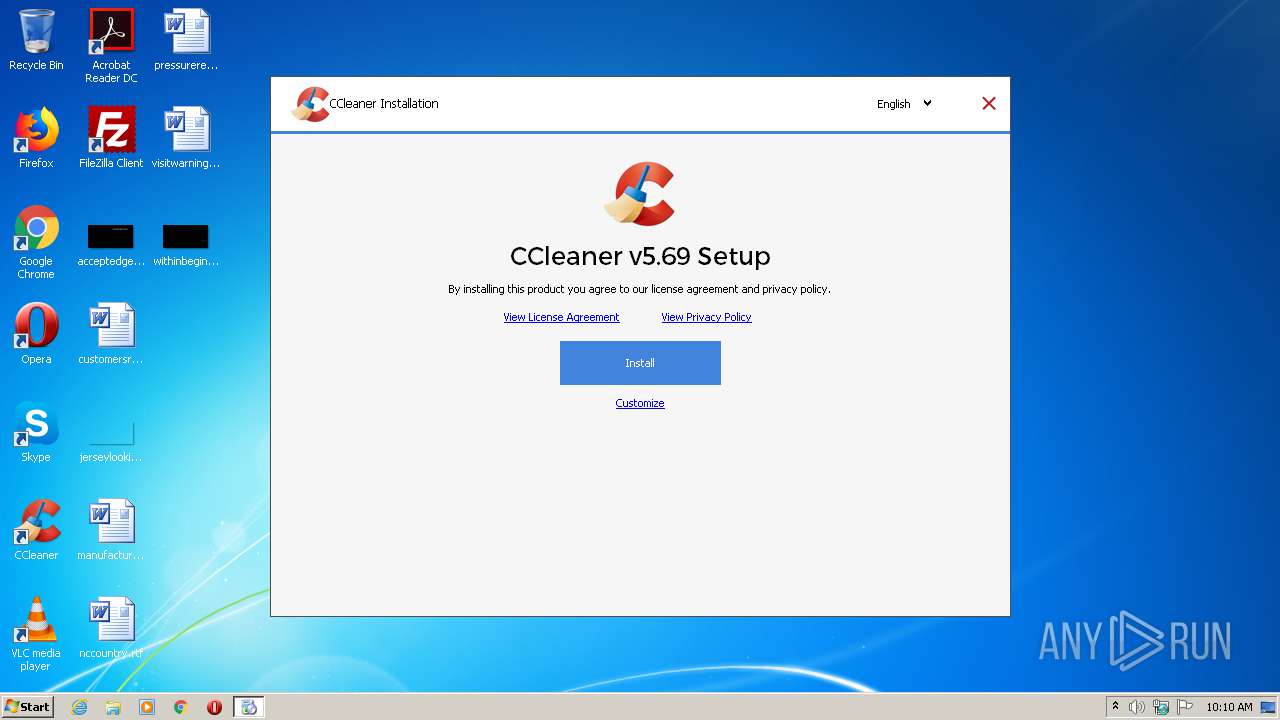
| download: | ccsetup569.exe |
| Full analysis: | https://app.any.run/tasks/a6648be3-5a27-45fe-a9f0-f896da8f2552 |
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2020, 09:10:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 1EE57823E03C286D48D7931E01FF2628 |
| SHA1: | A1374C52C8D65AE81B112D9AAE288BFF14966234 |
| SHA256: | 9B845E34C3F23DBE16B61BFBBFEB92194EDAFDE73299474B0A7B4AC9D733BE33 |
| SSDEEP: | 786432:2B4V4bjd2ESLvF6d5LtmSH3W/DuqntqDGlGMq:2B4Vih2JyJR3zay |
MALICIOUS
Changes settings of System certificates
- ccsetup569.exe (PID: 2172)
Actions looks like stealing of personal data
- ccsetup569.exe (PID: 2172)
Loads dropped or rewritten executable
- ccsetup569.exe (PID: 2172)
SUSPICIOUS
Low-level read access rights to disk partition
- ccsetup569.exe (PID: 2172)
Adds / modifies Windows certificates
- ccsetup569.exe (PID: 2172)
Starts application with an unusual extension
- ccsetup569.exe (PID: 2172)
Reads CPU info
- ccsetup569.exe (PID: 2172)
Reads the cookies of Mozilla Firefox
- ccsetup569.exe (PID: 2172)
Executable content was dropped or overwritten
- ccsetup569.exe (PID: 2172)
Creates files in the user directory
- ccsetup569.exe (PID: 2172)
Reads Environment values
- ccsetup569.exe (PID: 2172)
Reads internet explorer settings
- ccsetup569.exe (PID: 2172)
Reads the cookies of Google Chrome
- ccsetup569.exe (PID: 2172)
Reads Internet Cache Settings
- ccsetup569.exe (PID: 2172)
INFO
Reads settings of System Certificates
- ccsetup569.exe (PID: 2172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:29 22:34:49+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 29696 |
| InitializedDataSize: | 49664 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3a1c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.69.0.7865 |
| ProductVersionNumber: | 5.69.0.7865 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Piriform Software Ltd |
| FileDescription: | CCleaner Installer |
| FileVersion: | 5.69.0.7865 |
| LegalCopyright: | Copyright © 2005-2020 Piriform Software Ltd |
| ProductName: | CCleaner |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Dec-2015 21:34:49 |
| Detected languages: |
|
| CompanyName: | Piriform Software Ltd |
| FileDescription: | CCleaner Installer |
| FileVersion: | 5.69.0.7865 |
| LegalCopyright: | Copyright © 2005-2020 Piriform Software Ltd |
| ProductName: | CCleaner |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 29-Dec-2015 21:34:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00007250 | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46491 |
.rdata | 0x00009000 | 0x00002B38 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41939 |
.data | 0x0000C000 | 0x00067EDC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.89689 |
.ndata | 0x00074000 | 0x003CD000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00441000 | 0x000093B0 | 0x00009400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.89769 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27868 | 1212 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.62687 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.7389 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.91559 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.97397 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.89369 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
103 | 2.72033 | 90 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
105 | 2.704 | 688 | Latin 1 / Western European | English - United States | RT_DIALOG |
106 | 2.92897 | 344 | Latin 1 / Western European | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\nsACCE.tmp" C:\Windows\system32\ping.exe -n 1 -w 1000 www.ccleaner.com | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\nsACCE.tmp | — | ccsetup569.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2172 | "C:\Users\admin\AppData\Local\Temp\ccsetup569.exe" | C:\Users\admin\AppData\Local\Temp\ccsetup569.exe | explorer.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Installer Exit code: 0 Version: 5.69.0.7865 Modules
| |||||||||||||||
| 2812 | C:\Windows\system32\ping.exe -n 1 -w 1000 www.ccleaner.com | C:\Windows\system32\ping.exe | — | nsACCE.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3084 | "C:\Users\admin\AppData\Local\Temp\ccsetup569.exe" | C:\Users\admin\AppData\Local\Temp\ccsetup569.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Installer Exit code: 3221226540 Version: 5.69.0.7865 Modules
| |||||||||||||||
Total events
1 599
Read events
1 577
Write events
21
Delete events
1
Modification events
| (PID) Process: | (2172) ccsetup569.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Piriform\CCleaner |
| Operation: | delete value | Name: | GUID |
Value: 00000000-0000-4000-8000-d6f7f2be5127 | |||
| (PID) Process: | (2172) ccsetup569.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2172) ccsetup569.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\5FB7EE0633E259DBAD0C4C9AE6D38F1A61C7DC25 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000D474DE575C39B2D39C8583C5C065498A0F0000000100000014000000E35EF08D884F0A0ADE2F75E96301CE6230F213A80300000001000000140000005FB7EE0633E259DBAD0C4C9AE6D38F1A61C7DC251D00000001000000100000008F76B981D528AD4770088245E2031B630B0000000100000012000000440069006700690043006500720074000000140000000100000014000000B13EC36903F8BF4701D498261A0802EF63642BC36200000001000000200000007431E5F4C3C1CE4690774F0B61E05440883BA9A01ED00BA6ABD7806ED3B118CF5300000001000000230000003021301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0090000000100000034000000303206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308190000000100000010000000BA4F3972E7AED9DCCDC210DB59DA13C92000000001000000C9030000308203C5308202ADA003020102021002AC5C266A0B409B8F0B79F2AE462577300D06092A864886F70D0101050500306C310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312B30290603550403132244696769436572742048696768204173737572616E636520455620526F6F74204341301E170D3036313131303030303030305A170D3331313131303030303030305A306C310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312B30290603550403132244696769436572742048696768204173737572616E636520455620526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100C6CCE573E6FBD4BBE52D2D32A6DFE5813FC9CD2549B6712AC3D5943467A20A1CB05F69A640B1C4B7B28FD098A4A941593AD3DC94D63CDB7438A44ACC4D2582F74AA5531238EEF3496D71917E63B6ABA65FC3A484F84F6251BEF8C5ECDB3892E306E508910CC4284155FBCB5A89157E71E835BF4D72093DBE3A38505B77311B8DB3C724459AA7AC6D00145A04B7BA13EB510A984141224E656187814150A6795C89DE194A57D52EE65D1C532C7E98CD1A0616A46873D03404135CA171D35A7C55DB5E64E13787305604E511B4298012F1793988A202117C2766B788B778F2CA0AA838AB0A64C2BF665D9584C1A1251E875D1A500B2012CC41BB6E0B5138B84BCB0203010001A3633061300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E04160414B13EC36903F8BF4701D498261A0802EF63642BC3301F0603551D23041830168014B13EC36903F8BF4701D498261A0802EF63642BC3300D06092A864886F70D010105050003820101001C1A0697DCD79C9F3C886606085721DB2147F82A67AABF183276401057C18AF37AD911658E35FA9EFC45B59ED94C314BB891E8432C8EB378CEDBE3537971D6E5219401DA55879A2464F68A66CCDE9C37CDA834B1699B23C89E78222B7043E35547316119EF58C5852F4E30F6A0311623C8E7E2651633CBBF1A1BA03DF8CA5E8B318B6008892D0C065C52B7C4F90A98D1155F9F12BE7C366338BD44A47FE4262B0AC497690DE98CE2C01057B8C876129155F24869D8BC2A025B0F44D42031DBF4BA70265D90609EBC4B17092FB4CB1E4368C90727C1D25CF7EA21B968129C3C9CBF9EFC805C9B63CDEC47AA252767A037F300827D54D7A9F8E92E13A377E81F4A | |||
| (PID) Process: | (2172) ccsetup569.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2172) ccsetup569.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2172) ccsetup569.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2172) ccsetup569.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2172) ccsetup569.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2172) ccsetup569.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2172) ccsetup569.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
68
Suspicious files
14
Text files
7
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2172 | ccsetup569.exe | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\nsACCE.tmp | — | |
MD5:— | SHA256:— | |||
| 2172 | ccsetup569.exe | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\g\gcapi_dll.dll | executable | |
MD5:2973AF8515EFFD0A3BFC7A43B03B3FCC | SHA256:D0E4581210A22135CE5DEB47D9DF4D636A94B3813E0649AAB84822C9F08AF2A0 | |||
| 2172 | ccsetup569.exe | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\UserInfo.dll | executable | |
MD5:C1F778A6D65178D34BDE4206161A98E0 | SHA256:9CAF7A78F750713180CF64D18967A2B803B5580E636E59279DCAAF18BA0DAA87 | |||
| 2172 | ccsetup569.exe | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\ui\res\CC_Logo_40x96.png | image | |
MD5:D32B0460183056D3056D6DB89C992B88 | SHA256:B013039E32D2F8E54CFEBDBFDABC25F21AA0BBE9EF26A2A5319A20024961E9A7 | |||
| 2172 | ccsetup569.exe | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\a\AO.html | html | |
MD5:— | SHA256:— | |||
| 2172 | ccsetup569.exe | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\a\asdk.dll | executable | |
MD5:— | SHA256:— | |||
| 2172 | ccsetup569.exe | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\ui\res\lang-1027.dll | executable | |
MD5:— | SHA256:— | |||
| 2172 | ccsetup569.exe | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\ui\res\lang-1030.dll | executable | |
MD5:— | SHA256:— | |||
| 2172 | ccsetup569.exe | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\ui\res\lang-1028.dll | executable | |
MD5:— | SHA256:— | |||
| 2172 | ccsetup569.exe | C:\Users\admin\AppData\Local\Temp\nsg9916.tmp\ui\res\lang-1031.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
11
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2172 | ccsetup569.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2172 | ccsetup569.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDQ1xbKa56n3wIAAAAAcmxg | US | der | 472 b | whitelisted |
2172 | ccsetup569.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2172 | ccsetup569.exe | 72.247.226.62:443 | ipmcdn.avast.com | Akamai Technologies, Inc. | US | suspicious |
2172 | ccsetup569.exe | 172.217.22.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2172 | ccsetup569.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2172 | ccsetup569.exe | 5.62.40.213:443 | analytics.ff.avast.com | AVAST Software s.r.o. | DE | unknown |
2172 | ccsetup569.exe | 5.62.40.17:443 | ipm-provider.ff.avast.com | AVAST Software s.r.o. | DE | unknown |
2172 | ccsetup569.exe | 172.217.22.40:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
analytics.ff.avast.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
ipm-provider.ff.avast.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
ipmcdn.avast.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |